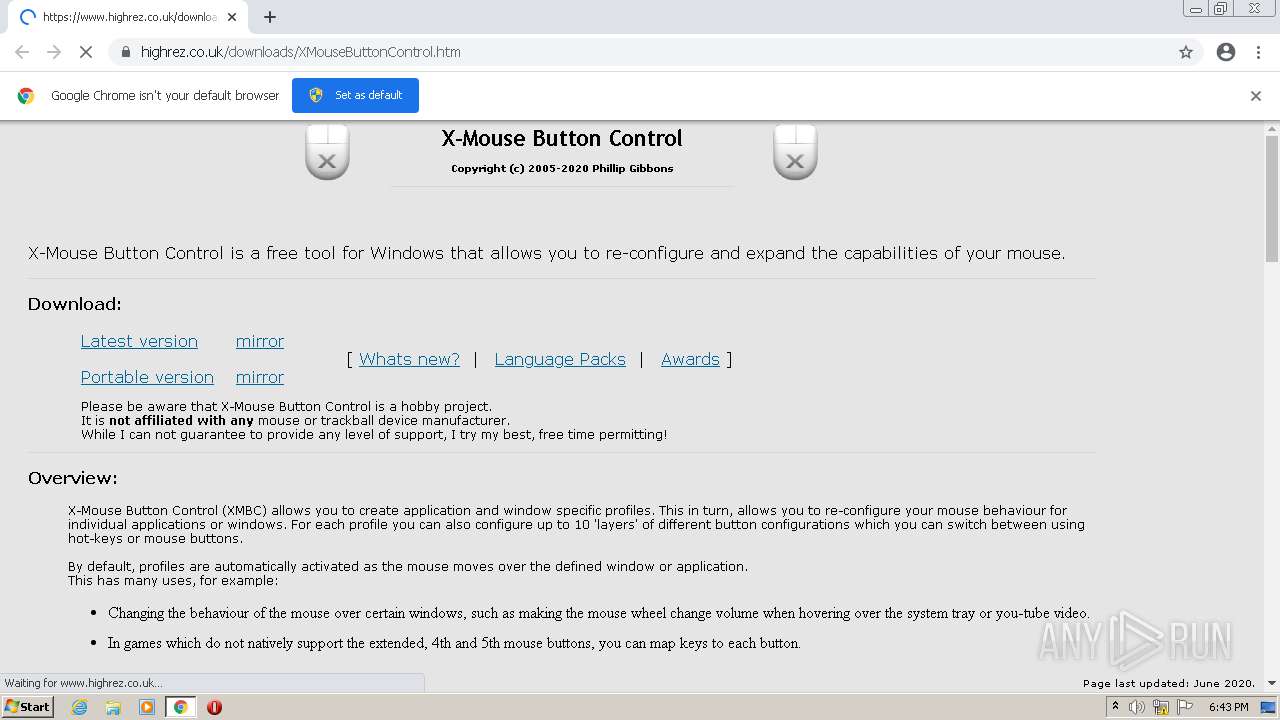
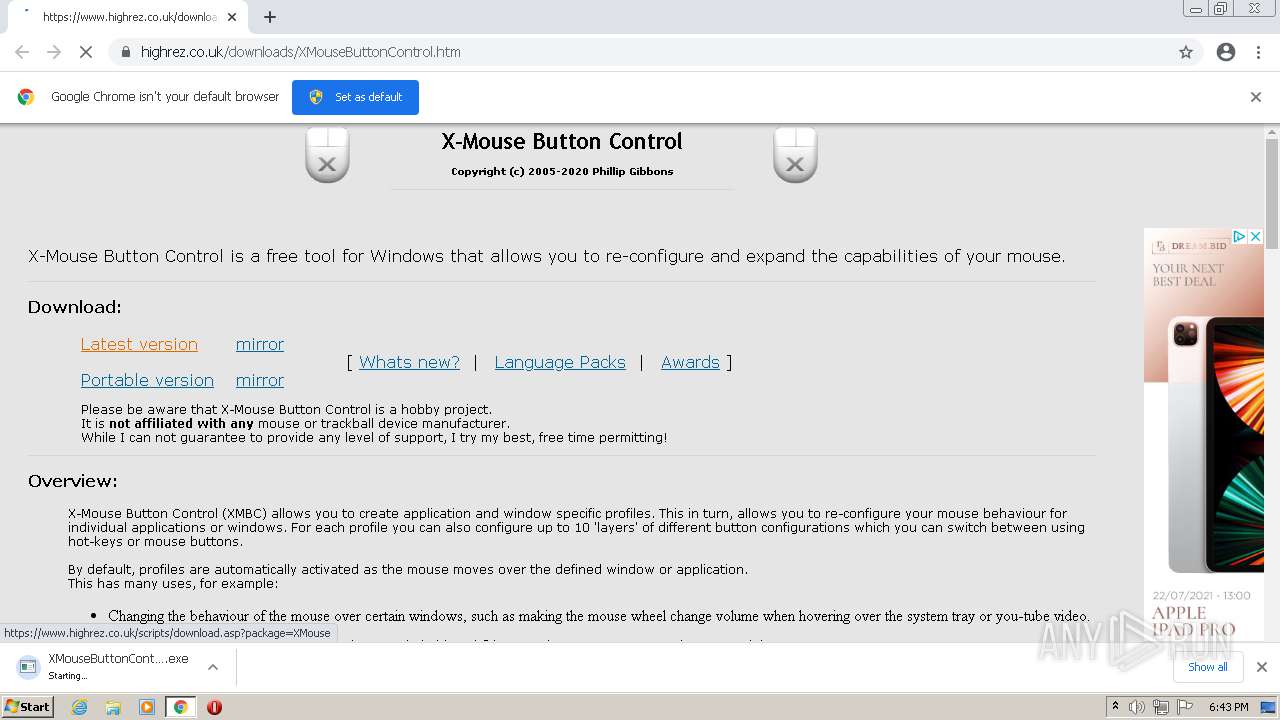
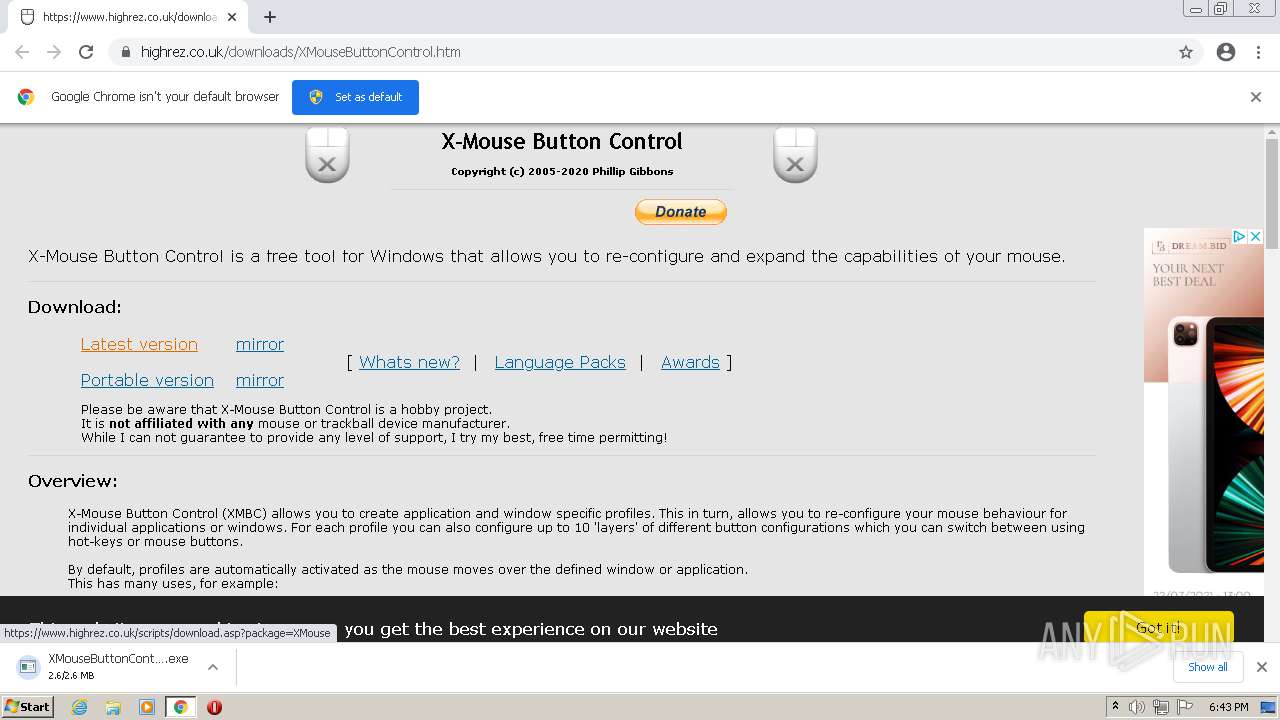
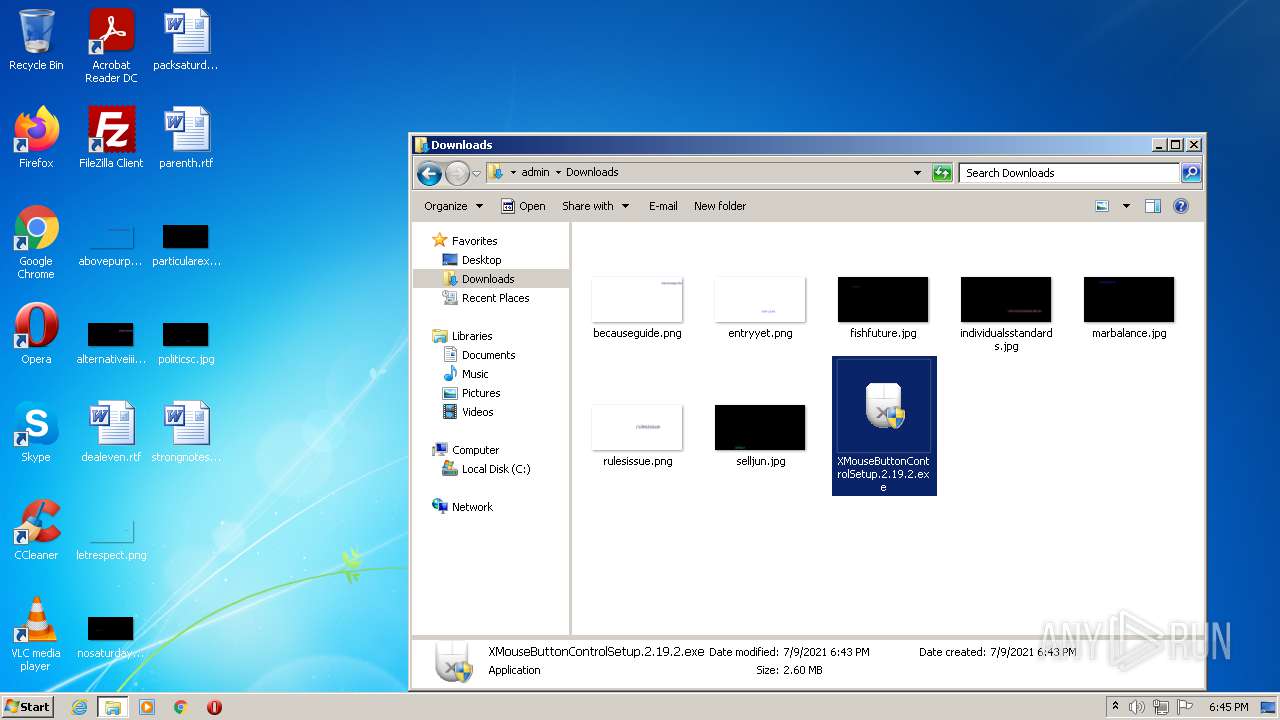
| URL: | https://www.highrez.co.uk/downloads/XMouseButtonControl.htm |
| Full analysis: | https://app.any.run/tasks/10301cdf-11a2-4af1-bc31-65d3eeb7ada9 |
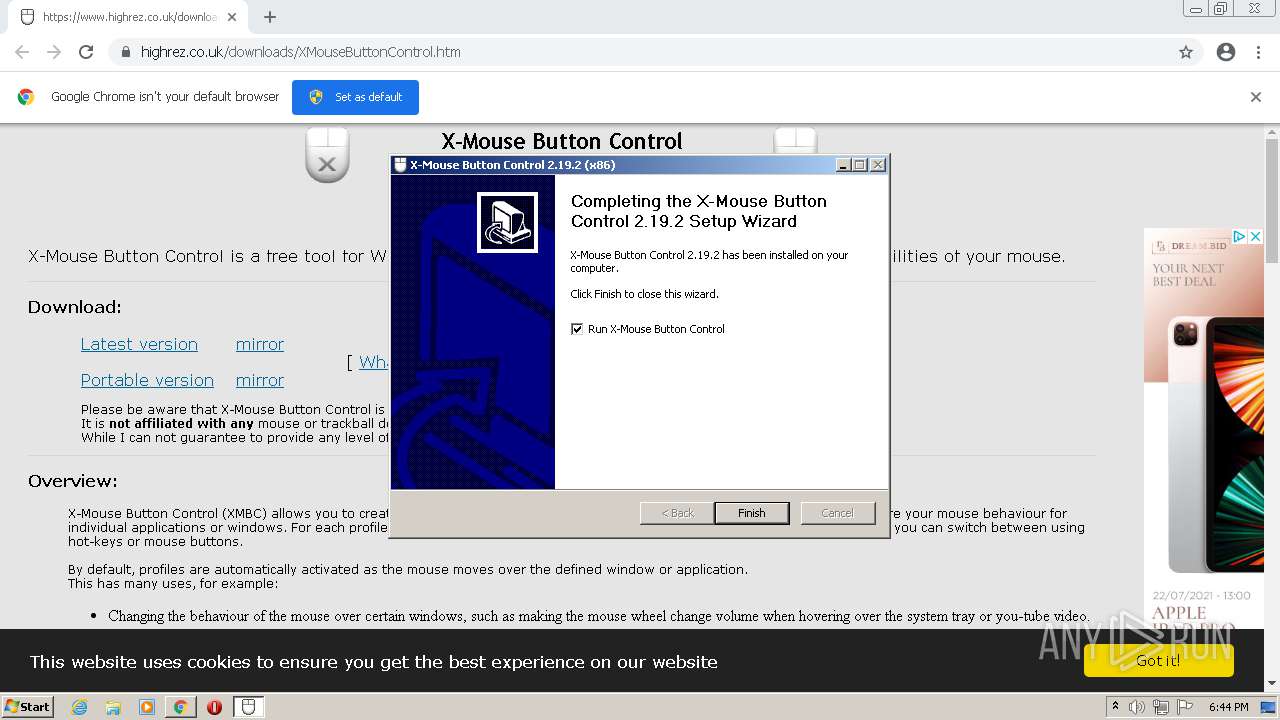
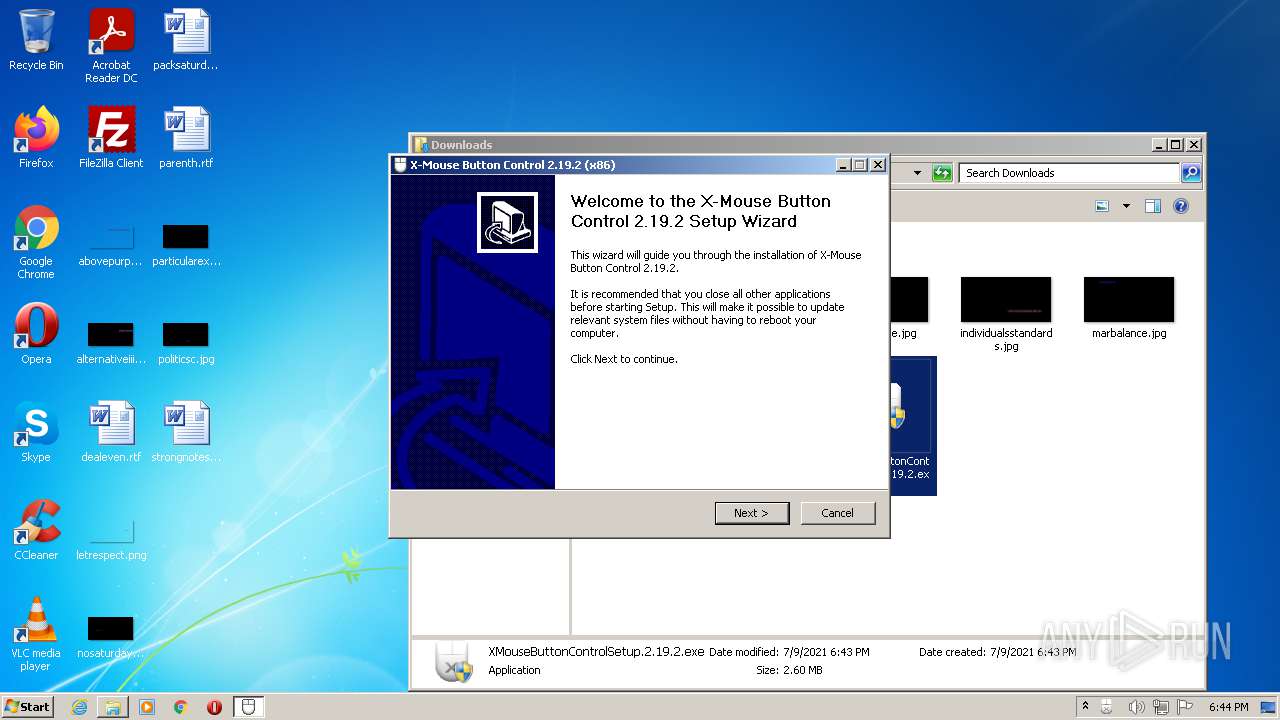
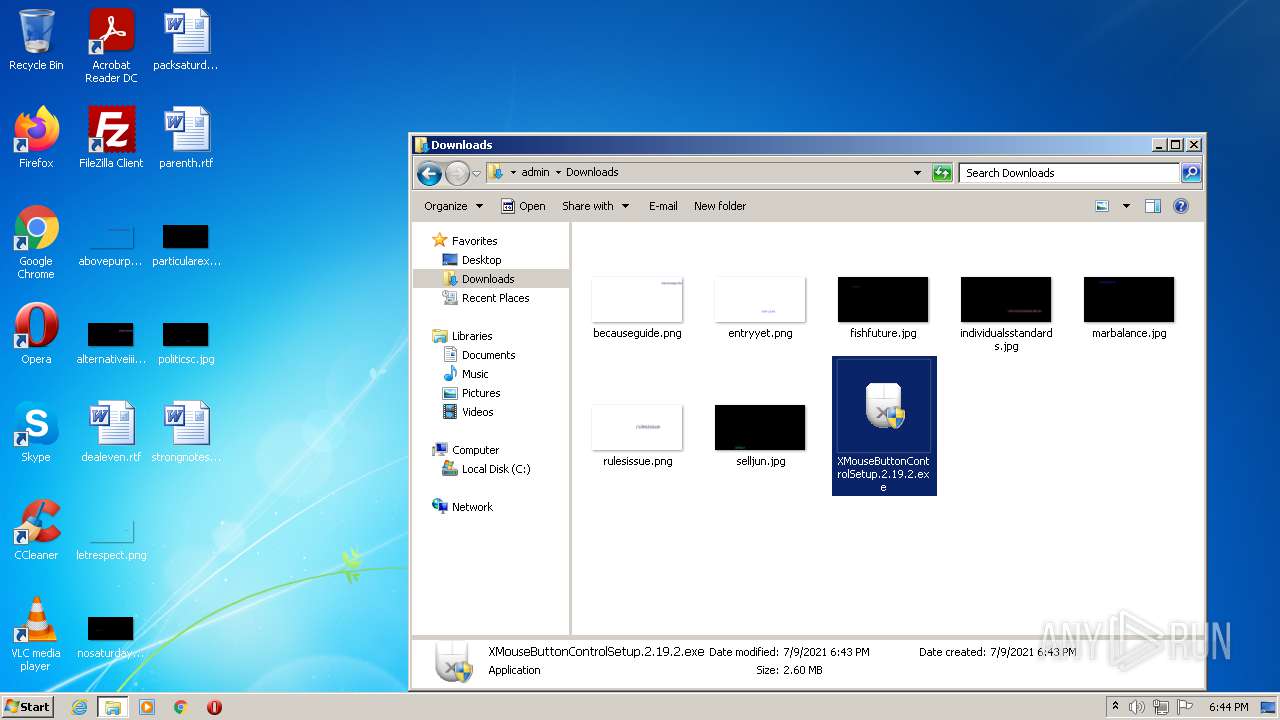
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2021, 17:42:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8C6A6477A00819F1FE9B5F4907CE5E28 |
| SHA1: | CF7F7030D66661E2F0161B87969BEA7FE23756D2 |
| SHA256: | C8377E256C7A05A5FDF581241676C331312B041FD04D26E77B6AD0017AA691AB |
| SSDEEP: | 3:N8DSLPK0KE4KGnQg9N0In:2OLZDGnQg9Nx |
MALICIOUS
Application was dropped or rewritten from another process
- XMouseButtonControlSetup.2.19.2.exe (PID: 2616)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControl.exe (PID: 3808)
- XMouseButtonControl.exe (PID: 436)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3356)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
- XMouseButtonControl.exe (PID: 1932)
- XMouseButtonControl.exe (PID: 2468)
- XMouseButtonControl.exe (PID: 2076)
- XMouseButtonControl.exe (PID: 336)
- XMouseButtonControl.exe (PID: 2408)
- XMouseButtonControl.exe (PID: 3480)
- XMouseButtonControl.exe (PID: 1448)
Loads dropped or rewritten executable
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControl.exe (PID: 436)
- XMouseButtonControl.exe (PID: 2076)
- XMouseButtonControl.exe (PID: 2408)
- XMouseButtonControl.exe (PID: 1448)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
Drops executable file immediately after starts
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
Changes the autorun value in the registry
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2816)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
Reads the computer name
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControl.exe (PID: 436)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
- XMouseButtonControl.exe (PID: 2076)
- cmd.exe (PID: 3540)
- XMouseButtonControl.exe (PID: 2408)
- javaw.exe (PID: 444)
- jucheck.exe (PID: 2844)
- jucheck.exe (PID: 3852)
- XMouseButtonControl.exe (PID: 1448)
Checks supported languages
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- nsED8C.tmp (PID: 2920)
- XMouseButtonControl.exe (PID: 436)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
- XMouseButtonControl.exe (PID: 2076)
- cmd.exe (PID: 3540)
- ns9016.tmp (PID: 464)
- XMouseButtonControl.exe (PID: 2408)
- javacpl.exe (PID: 3036)
- javaw.exe (PID: 444)
- jucheck.exe (PID: 2844)
- XMouseButtonControl.exe (PID: 1448)
- jucheck.exe (PID: 3852)
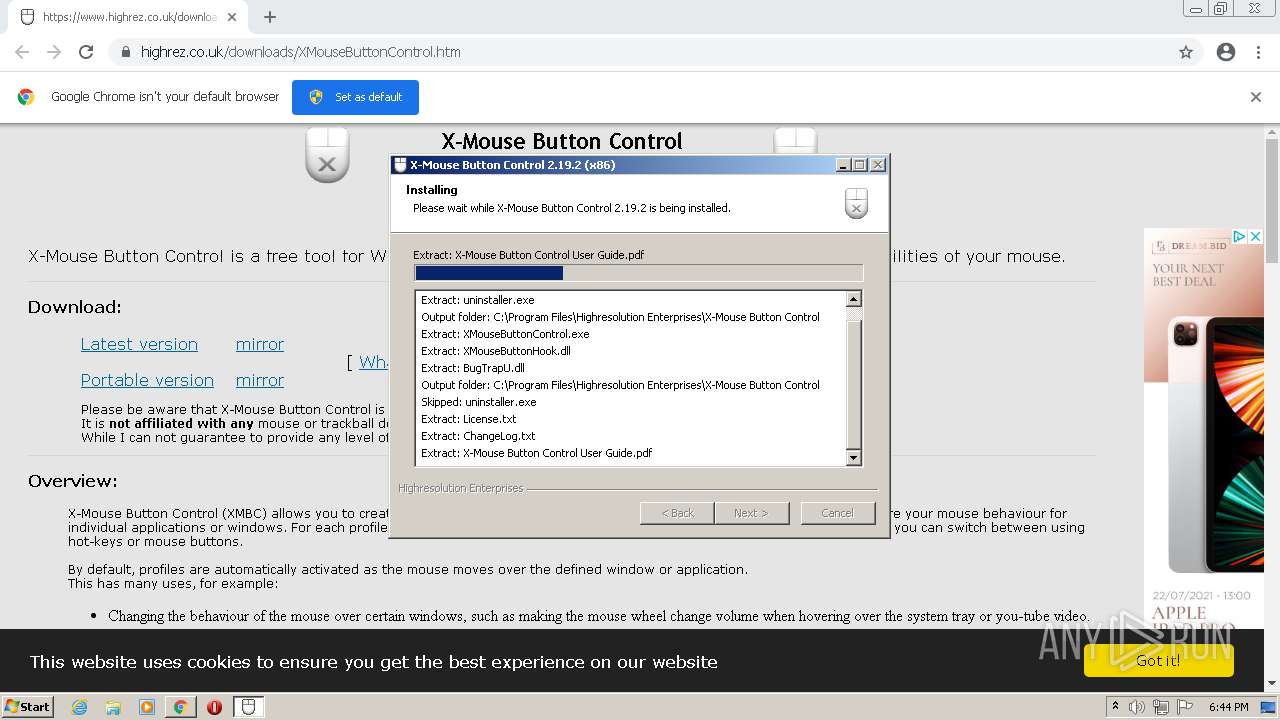
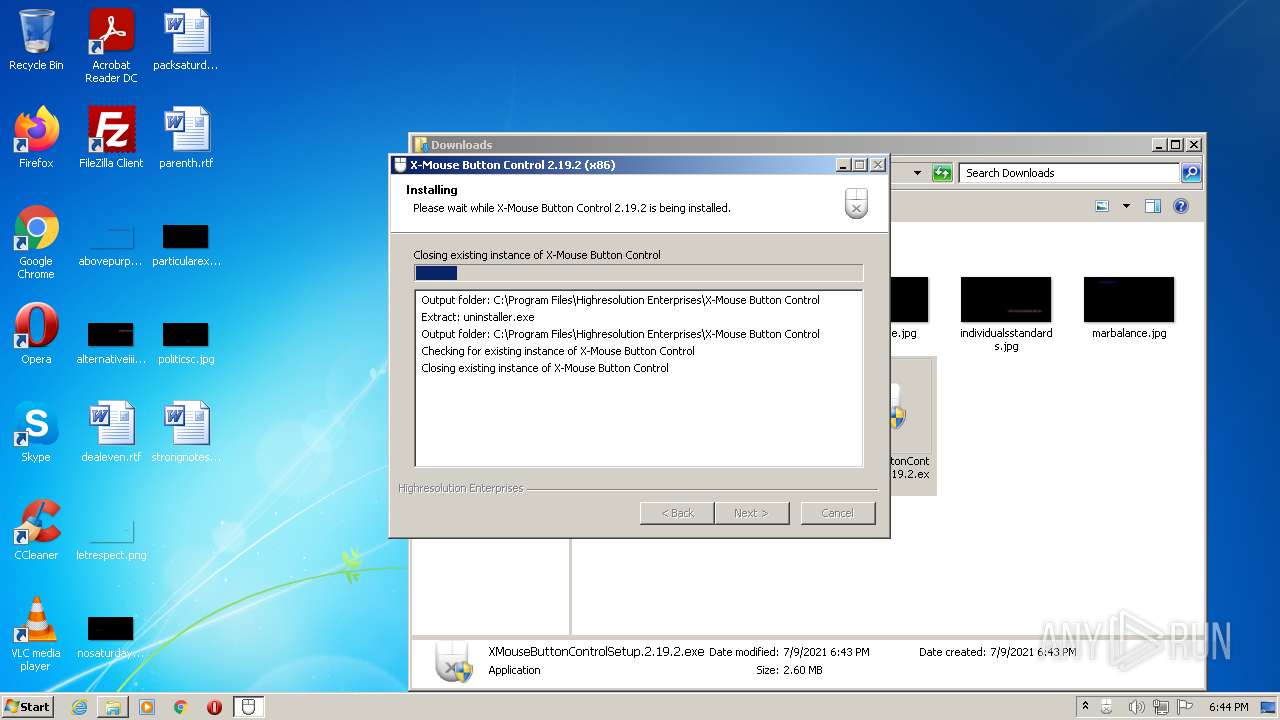
Creates a directory in Program Files
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
Starts application with an unusual extension
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
Creates files in the program directory
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
Removes files from Windows directory
- certutil.exe (PID: 3780)
- certutil.exe (PID: 3880)
Creates files in the Windows directory
- certutil.exe (PID: 3780)
- certutil.exe (PID: 3880)
Drops a file that was compiled in debug mode
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
Changes default file association
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
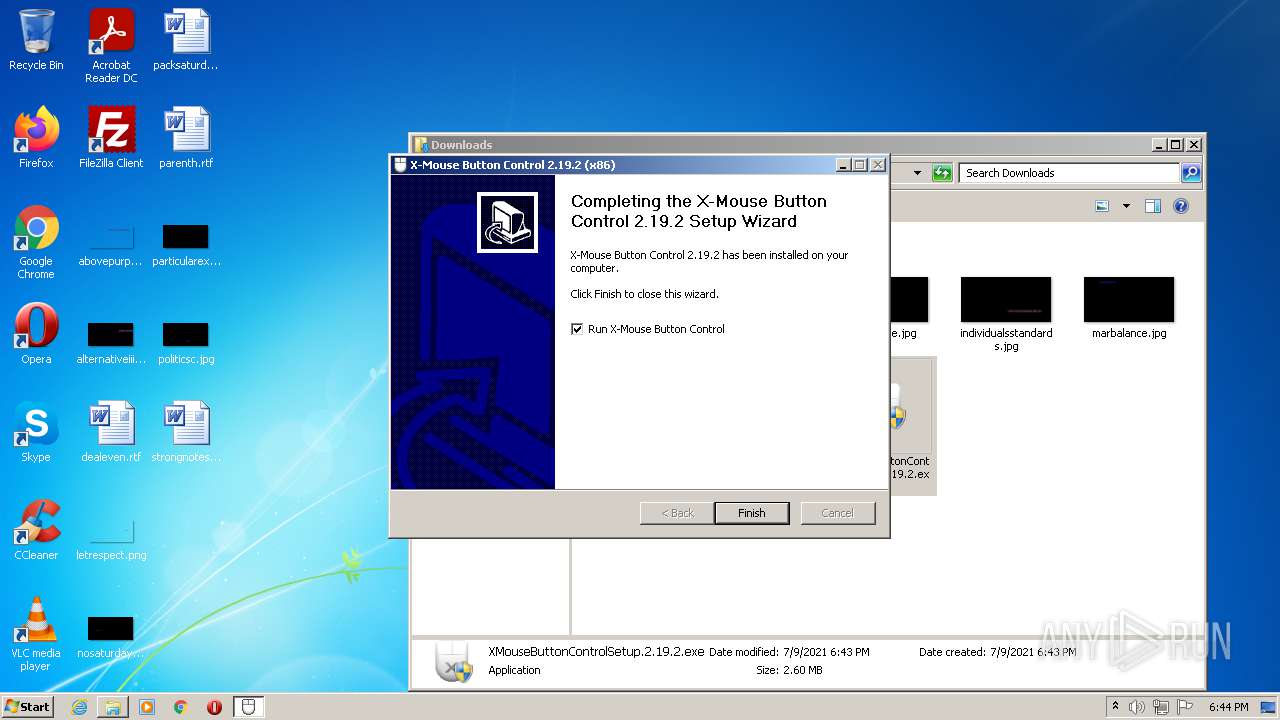
Creates a software uninstall entry
- XMouseButtonControlSetup.2.19.2.exe (PID: 3428)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
Creates files in the user directory
- XMouseButtonControl.exe (PID: 436)
- XMouseButtonControl.exe (PID: 2076)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3324)
Drops a file with too old compile date
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
Starts CMD.EXE for commands execution
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
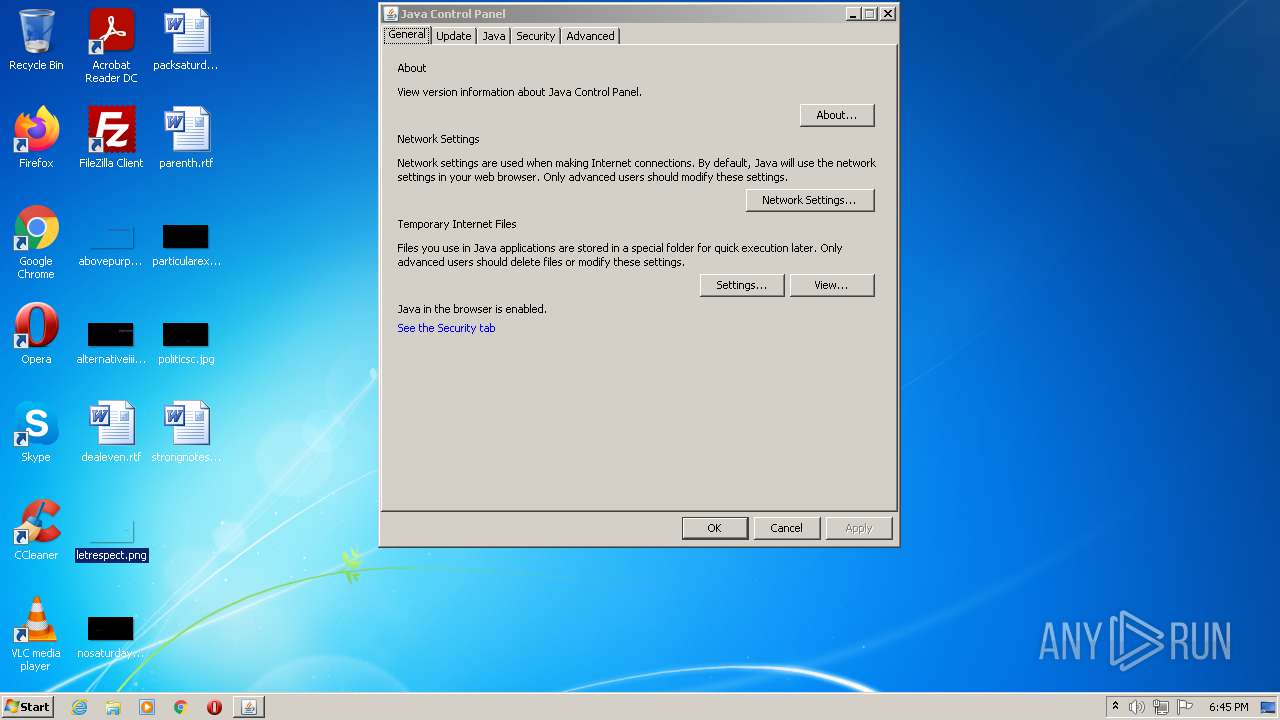
Executes JAVA applets
- javacpl.exe (PID: 3036)
Check for Java to be installed
- javaw.exe (PID: 444)
- jucheck.exe (PID: 2844)
- jucheck.exe (PID: 3852)
INFO
Checks supported languages
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 2528)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 492)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 1348)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 1428)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 3432)
- certutil.exe (PID: 3780)
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 3388)
- explorer.exe (PID: 2968)
- certutil.exe (PID: 3880)
- iexplore.exe (PID: 3392)
- iexplore.exe (PID: 3324)
Application launched itself
- chrome.exe (PID: 2816)
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 3392)
Reads the hosts file
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2844)
Reads the computer name
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 1348)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 3432)
- certutil.exe (PID: 3780)
- iexplore.exe (PID: 3388)
- chrome.exe (PID: 2560)
- explorer.exe (PID: 2968)
- iexplore.exe (PID: 1764)
- certutil.exe (PID: 3880)
- iexplore.exe (PID: 3392)
- iexplore.exe (PID: 3324)
Reads settings of System Certificates
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2816)
- certutil.exe (PID: 3780)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 1764)
- certutil.exe (PID: 3880)
- iexplore.exe (PID: 3324)
Checks Windows Trust Settings
- chrome.exe (PID: 2816)
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 3324)
Reads the date of Windows installation
- chrome.exe (PID: 4072)
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 3392)
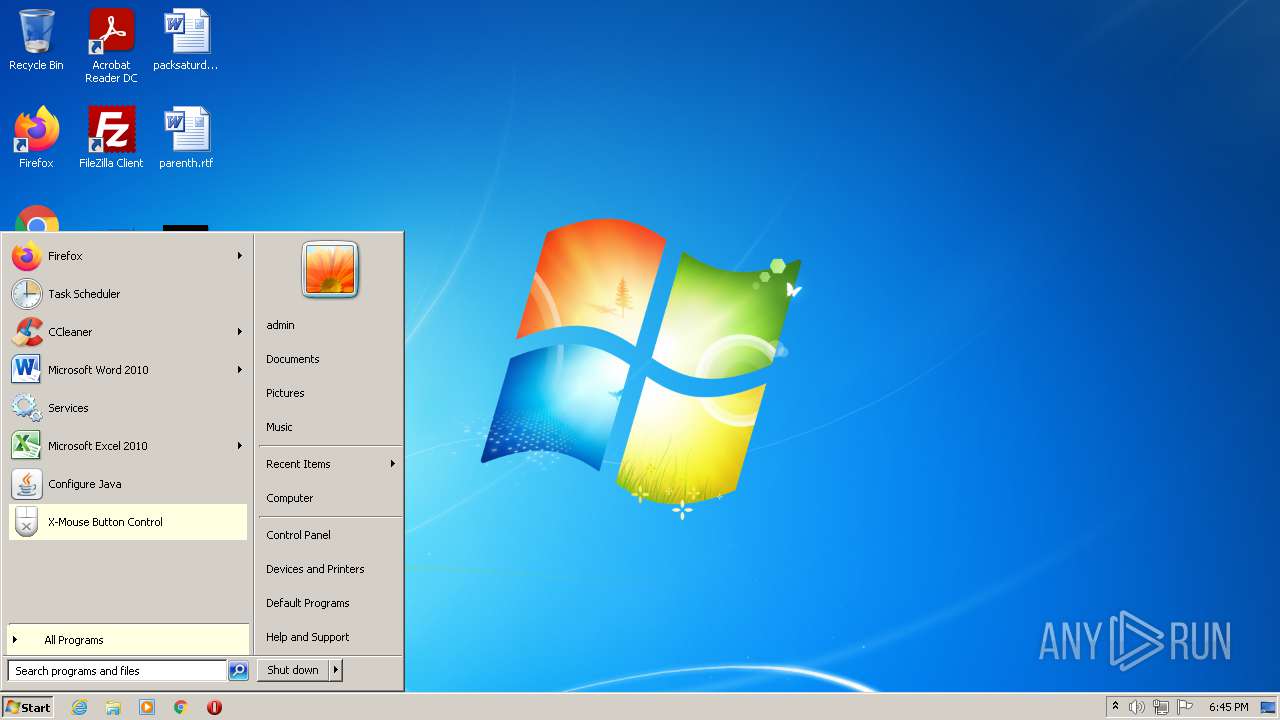
Manual execution by user
- XMouseButtonControl.exe (PID: 3808)
- iexplore.exe (PID: 1764)
- XMouseButtonControl.exe (PID: 436)
- explorer.exe (PID: 2968)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3356)
- iexplore.exe (PID: 3392)
- XMouseButtonControl.exe (PID: 336)
- XMouseButtonControl.exe (PID: 2408)
- XMouseButtonControlSetup.2.19.2.exe (PID: 3396)
- javacpl.exe (PID: 3036)
- XMouseButtonControl.exe (PID: 1448)
- XMouseButtonControl.exe (PID: 3480)
Changes internet zones settings
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 3392)
Changes settings of System certificates
- iexplore.exe (PID: 1764)
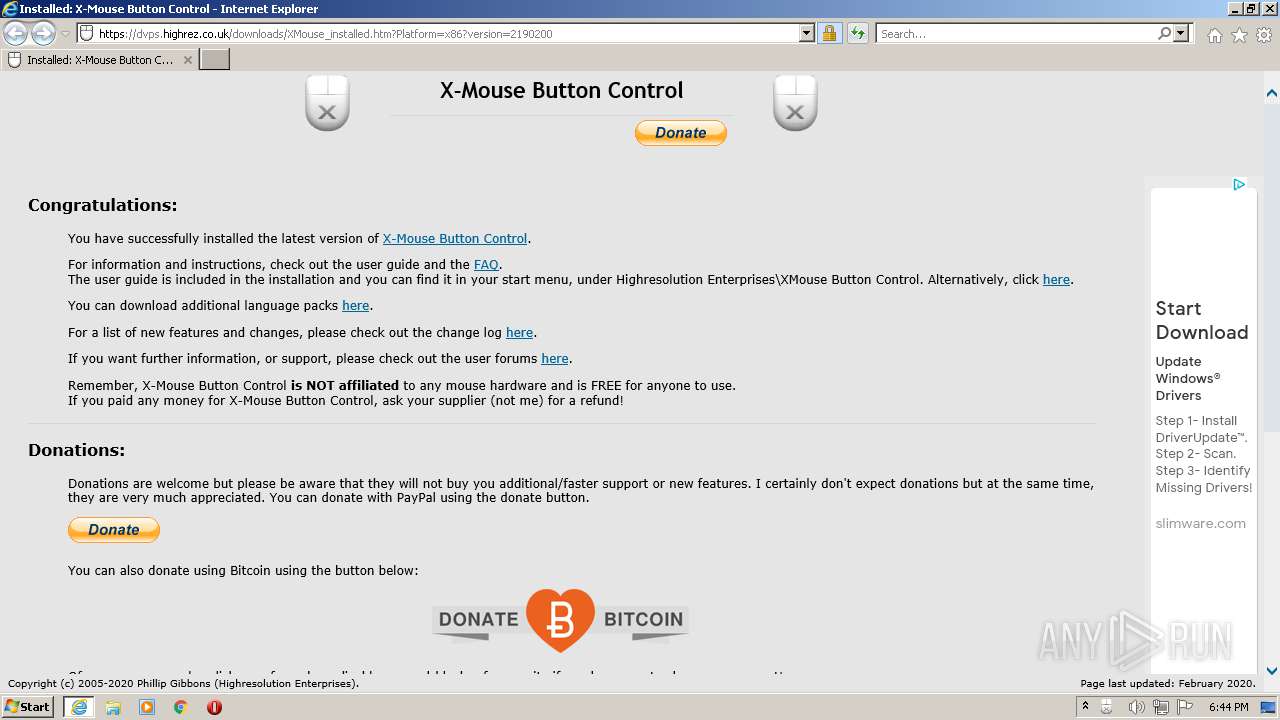
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3388)
Reads internet explorer settings
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3324)
Creates files in the user directory
- iexplore.exe (PID: 3388)
- iexplore.exe (PID: 3324)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
50
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Program Files\Highresolution Enterprises\X-Mouse Button Control\XMouseButtonControl.exe" /Installed /notportable | C:\Program Files\Highresolution Enterprises\X-Mouse Button Control\XMouseButtonControl.exe | — | Explorer.EXE | |||||||||||
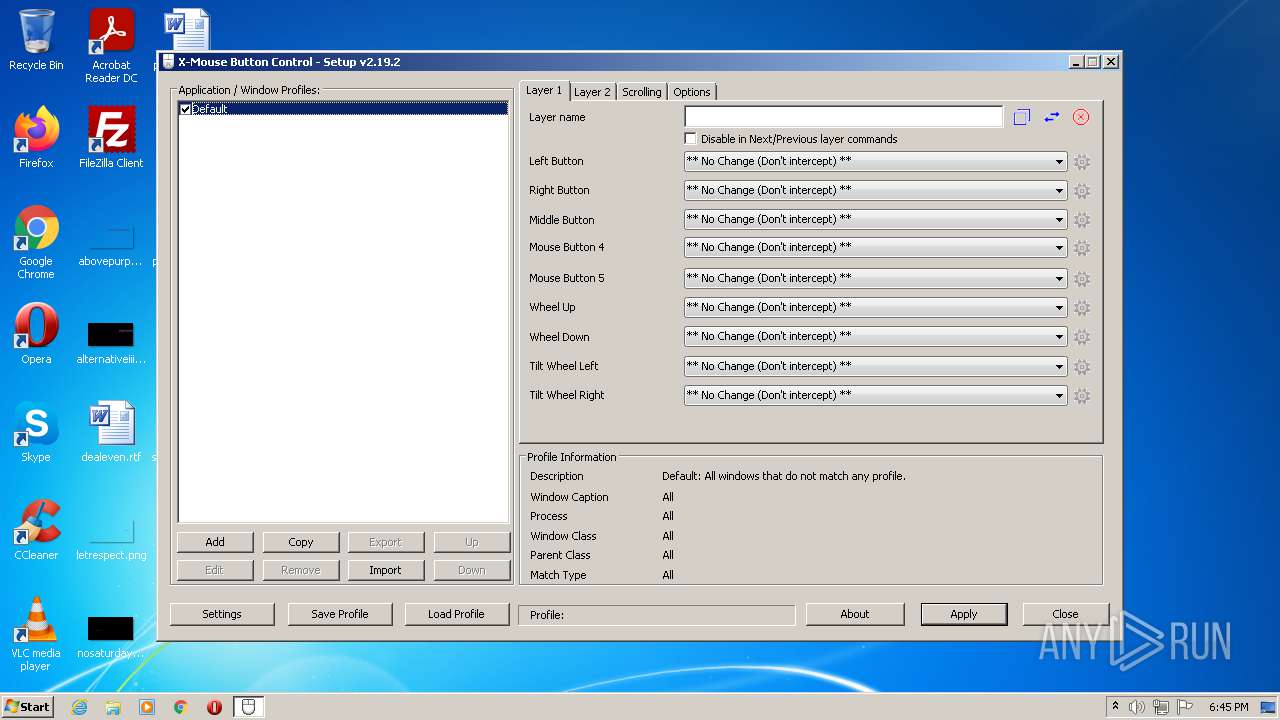
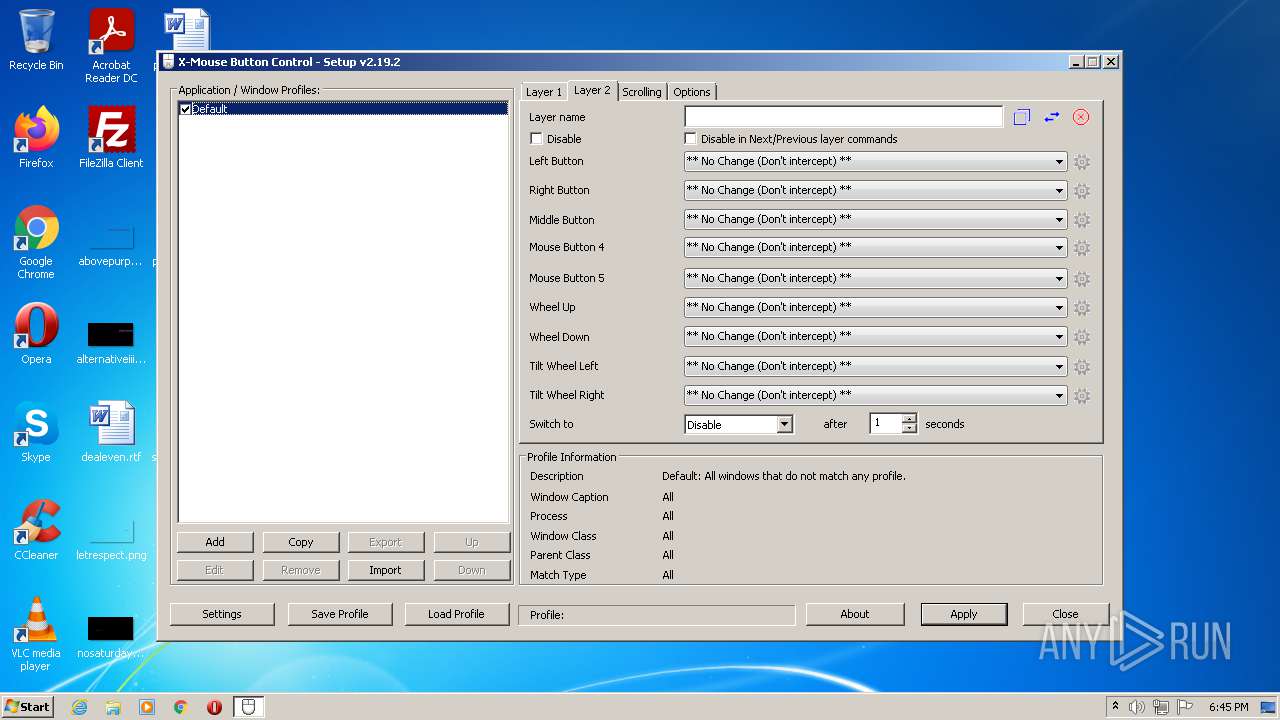
User: admin Company: Highresolution Enterprises Integrity Level: MEDIUM Description: X-Mouse Button Control Exit code: 3221226540 Version: 2.19.2 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Highresolution Enterprises\X-Mouse Button Control\XMouseButtonControl.exe" /Installed /notportable | C:\Program Files\Highresolution Enterprises\X-Mouse Button Control\XMouseButtonControl.exe | Explorer.EXE | ||||||||||||
User: admin Company: Highresolution Enterprises Integrity Level: HIGH Description: X-Mouse Button Control Exit code: 3221225547 Version: 2.19.2 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Xbootclasspath/a:"C:\Program Files\Java\jre1.8.0_271\bin\..\lib\deploy.jar" -Djava.locale.providers=HOST,JRE,SPI -Djdk.disableLastUsageTracking -Dsun.java2d.dpiaware=true -Duser.home="C:\Users\admin" com.sun.deploy.panel.ControlPanel | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javacpl.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 464 | "C:\Users\admin\AppData\Local\Temp\nst49B5.tmp\ns9016.tmp" certutil -delstore root "82 53 30 f1 fa 00 53 f0 03 5a 19 83 63 cd f3 78 22 1d d7 7f" | C:\Users\admin\AppData\Local\Temp\nst49B5.tmp\ns9016.tmp | — | XMouseButtonControlSetup.2.19.2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13794870373888100710,10493350133130491856,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1036,13794870373888100710,10493350133130491856,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4032 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13794870373888100710,10493350133130491856,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Highresolution Enterprises\X-Mouse Button Control\XMouseButtonControl.exe" /notportable | C:\Program Files\Highresolution Enterprises\X-Mouse Button Control\XMouseButtonControl.exe | Explorer.EXE | ||||||||||||
User: admin Company: Highresolution Enterprises Integrity Level: HIGH Description: X-Mouse Button Control Exit code: 0 Version: 2.19.2 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.highrez.co.uk/scripts/postinstall.asp?package=XMouse&major=2&minor=19&build=2&revision=0&platform=x86 | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Highresolution Enterprises\X-Mouse Button Control\XMouseButtonControl.exe" /exit | C:\Program Files\Highresolution Enterprises\X-Mouse Button Control\XMouseButtonControl.exe | — | cmd.exe | |||||||||||
User: admin Company: Highresolution Enterprises Integrity Level: HIGH Description: X-Mouse Button Control Exit code: 3221226540 Version: 2.19.2 Modules
| |||||||||||||||
Total events
45 695
Read events
45 172
Write events
515
Delete events
8
Modification events
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
23
Suspicious files
90
Text files
256
Unknown types
64
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60E88A9F-B00.pma | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5a760aaa-d1f0-40ca-a2b9-1dd443fc999e.tmp | text | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF10b9ad.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\34d644f4-6070-4613-b064-068f19555952.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF10ba78.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10b98e.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF10bac6.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
189
DNS requests
84
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2844 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEEPADVwzSh7mAwAAAADMUdQ%3D | US | der | 471 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDklLiDhjNkMCgAAAADoMj8%3D | US | der | 471 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDklLiDhjNkMCgAAAADoMj8%3D | US | der | 471 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPh2xhM2DwYKKbfQtcy5UWRCw%3D%3D | unknown | der | 503 b | shared |
3388 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDEmZ%2BFi9JBWQMAAAAAzFGq | US | der | 472 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFS9lWfFTtEyCgAAAADoPas%3D | US | der | 471 b | whitelisted |
3388 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCCOr8WKmKZfQoAAAAA6D2u | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | chrome.exe | 142.250.185.170:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 142.250.185.66:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2844 | chrome.exe | 104.21.7.178:443 | lab.subinsb.com | Cloudflare Inc | US | unknown |
2844 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2844 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
2844 | chrome.exe | 142.250.185.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2844 | chrome.exe | 142.250.128.155:443 | partner.googleadservices.com | Google Inc. | US | unknown |
2844 | chrome.exe | 142.250.185.194:443 | adservice.google.com | Google Inc. | US | suspicious |
2844 | chrome.exe | 142.250.184.194:443 | adservice.google.co.uk | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.highrez.co.uk |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.paypalobjects.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
lab.subinsb.com |
| malicious |
Threats
Process | Message |
|---|---|
XMouseButtonControlSetup.2.19.2.exe | ExecShellAsUser: DLL_PROCESS_ATTACH |
XMouseButtonControlSetup.2.19.2.exe | ExecShellAsUser: got desktop |
XMouseButtonControlSetup.2.19.2.exe | ExecShellAsUser: elevated process detected |
XMouseButtonControlSetup.2.19.2.exe | ExecShellAsUser: NSPIM_UNLOAD wait... |
XMouseButtonControlSetup.2.19.2.exe | ExecShellAsUser: thread finished |
XMouseButtonControlSetup.2.19.2.exe | ExecShellAsUser: NSPIM_UNLOAD |
XMouseButtonControlSetup.2.19.2.exe | ExecShellAsUser: DLL_PROCESS_DETACH |
XMouseButtonControl.exe | 09-07-2021 18:44:56.028> CXButtonControllApp: Constructing Main Application Class
|
XMouseButtonControl.exe | 09-07-2021 18:44:56.028> InitInstance: XMBC is starting
|
XMouseButtonControl.exe | 09-07-2021 18:44:56.028> MultInstance: Sending commandline to an existing instance of X-Mouse Button Control
|