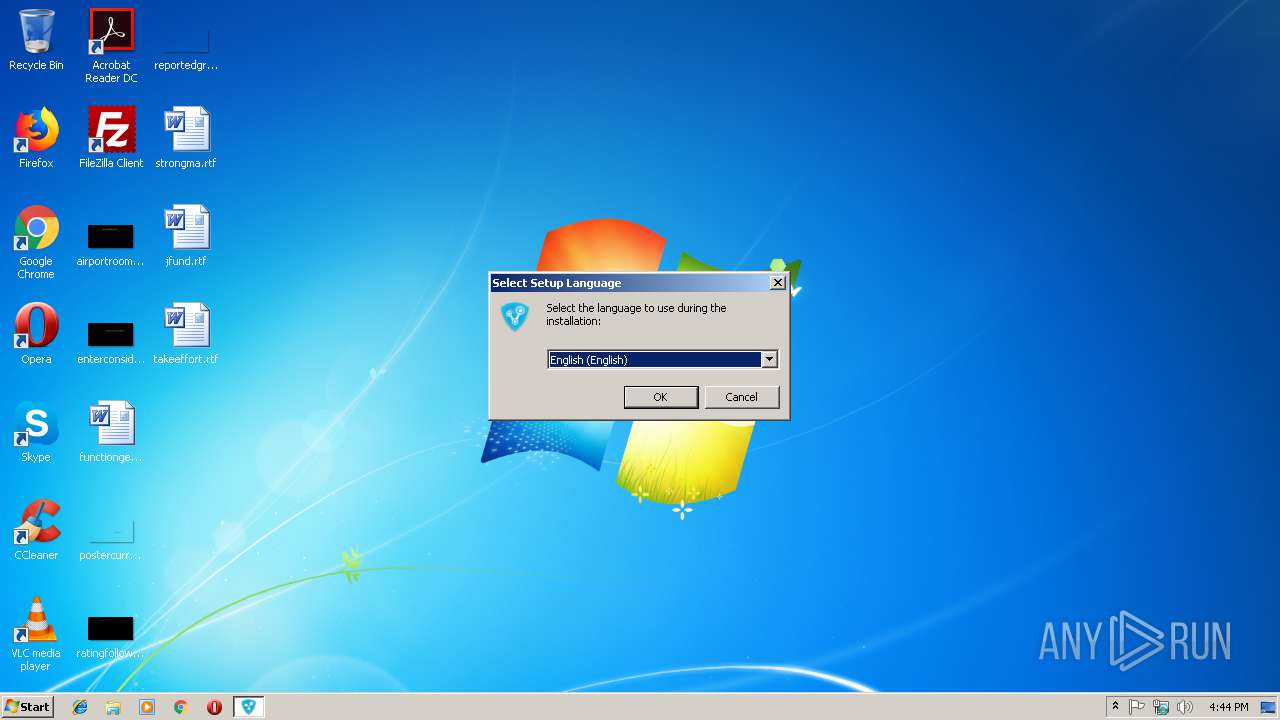
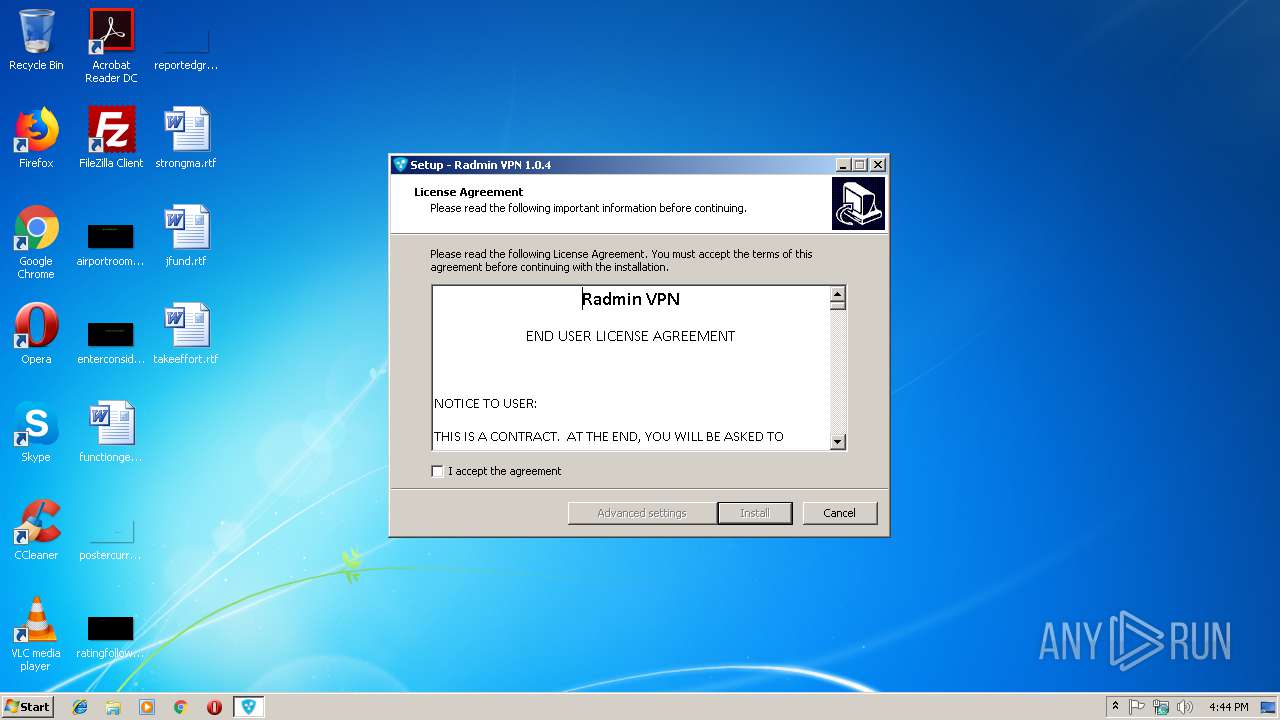
| download: | Radmin_VPN_1.0.3722.4.exe |
| Full analysis: | https://app.any.run/tasks/96a73462-a837-4dc5-81bb-a63daa993273 |
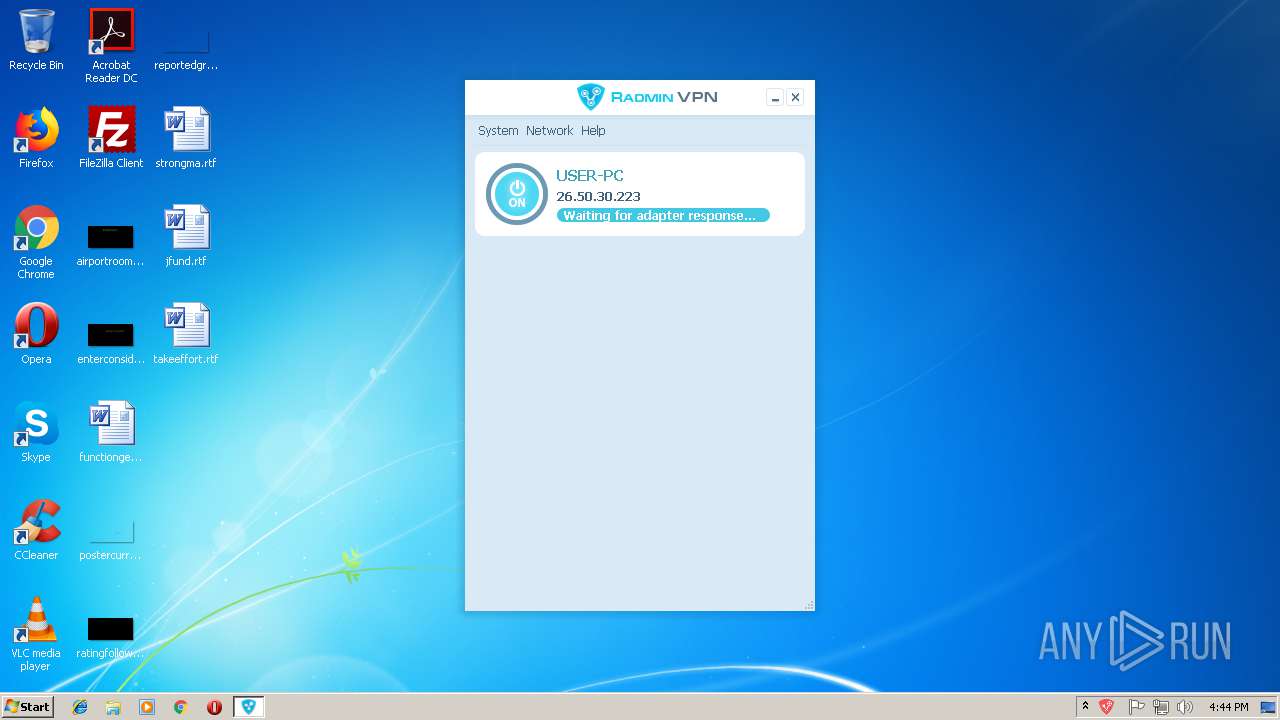
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2019, 16:43:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 34DDD00A9CE649B4CFCC5E589D791527 |
| SHA1: | 36D6B0B50AB7A5095A9ACDB6CB91E1712A2BE80C |
| SHA256: | C82B4A4416F2F4006B4A504CA5865C8EB99A07D3A0790B53C8601B7D33202AC9 |
| SSDEEP: | 393216:5h3mpRe755T5vLljuoxrHQTAyywF8hAKiXwl2xG12la6KDHLJhZiI:5h3mpRAntRuoxrwUlN4c2lmrLJXD |
MALICIOUS
Loads dropped or rewritten executable
- RvControlSvc.exe (PID: 2564)
- RvRvpnGui.exe (PID: 3440)
Application was dropped or rewritten from another process
- RvControlSvc.exe (PID: 2564)
- RvRvpnGui.exe (PID: 3440)
SUSPICIOUS
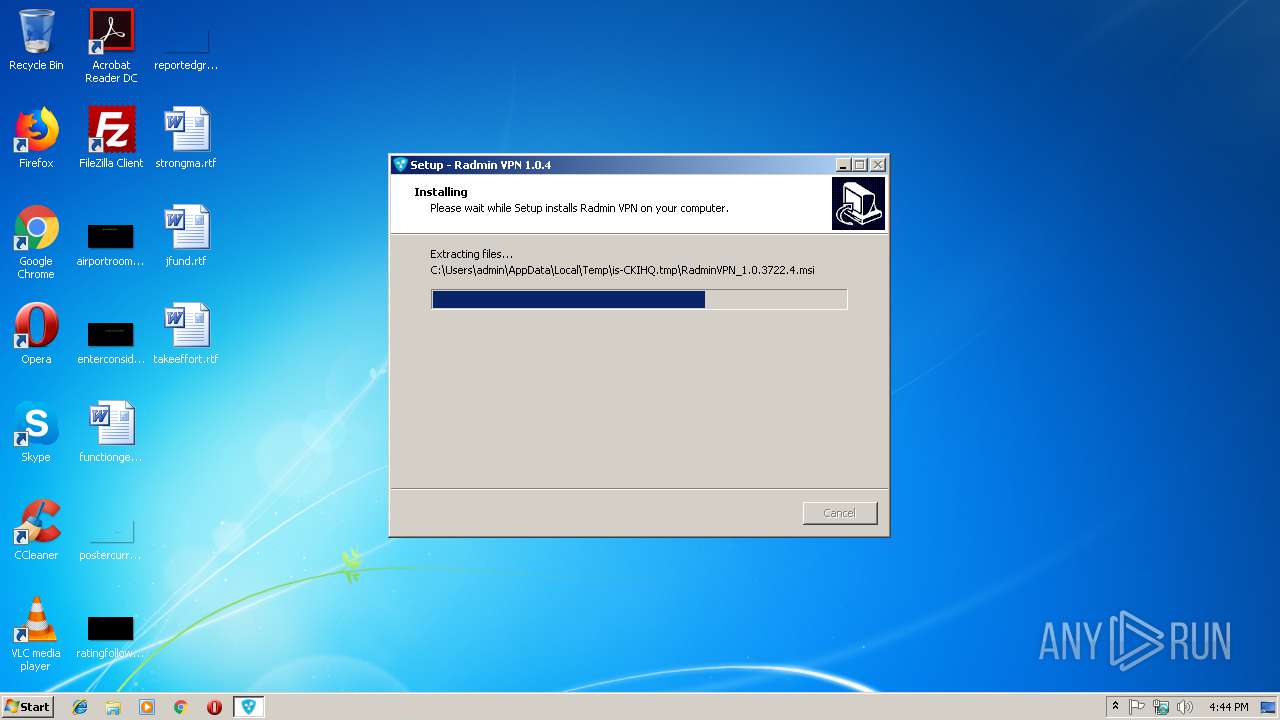
Executable content was dropped or overwritten
- Radmin_VPN_1.0.3722.4.exe (PID: 3572)
- Radmin_VPN_1.0.3722.4.exe (PID: 3820)
- Radmin_VPN_1.0.3722.4.tmp (PID: 2124)
- msiexec.exe (PID: 2672)
- DrvInst.exe (PID: 3908)
Reads Windows owner or organization settings
- Radmin_VPN_1.0.3722.4.tmp (PID: 2124)
Reads the Windows organization settings
- Radmin_VPN_1.0.3722.4.tmp (PID: 2124)
Changes the autorun value in the registry
- msiexec.exe (PID: 2672)
Creates files in the Windows directory
- MSI31BD.tmp (PID: 3236)
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3908)
Creates files in the driver directory
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3908)
Removes files from Windows directory
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3908)
Uses NETSH.EXE for network configuration
- MsiExec.exe (PID: 3124)
- RvControlSvc.exe (PID: 2564)
Creates files in the program directory
- RvControlSvc.exe (PID: 2564)
Creates or modifies windows services
- DrvInst.exe (PID: 3908)
Connects to unusual port
- RvControlSvc.exe (PID: 2564)
INFO
Application was dropped or rewritten from another process
- Radmin_VPN_1.0.3722.4.tmp (PID: 2124)
- Radmin_VPN_1.0.3722.4.tmp (PID: 2180)
- MSI31BD.tmp (PID: 3236)
Loads dropped or rewritten executable
- Radmin_VPN_1.0.3722.4.tmp (PID: 2124)
- MsiExec.exe (PID: 3124)
- MsiExec.exe (PID: 2844)
Application launched itself
- msiexec.exe (PID: 2672)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2672)
Creates files in the program directory
- msiexec.exe (PID: 2672)
Starts application with an unusual extension
- msiexec.exe (PID: 2672)
Creates a software uninstall entry
- msiexec.exe (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:01:30 15:21:56+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 122880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.3722.4 |
| ProductVersionNumber: | 1.0.3722.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Famatech Corp. |
| FileDescription: | Radmin VPN Setup |
| FileVersion: | 1.0.3722.4 |
| LegalCopyright: | Copyright © 2017-2019 Famatech Corp. and its licensors. All rights reserved. |
| ProductName: | Radmin VPN |
| ProductVersion: | 1.0.3722.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2013 14:21:56 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Famatech Corp. |
| FileDescription: | Radmin VPN Setup |
| FileVersion: | 1.0.3722.4 |
| LegalCopyright: | Copyright © 2017-2019 Famatech Corp. and its licensors. All rights reserved. |
| ProductName: | Radmin VPN |
| ProductVersion: | 1.0.3722.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 30-Jan-2013 14:21:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F12C | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39148 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.73207 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24631 |
.bss | 0x00013000 | 0x000056B4 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0001C1FC | 0x0001C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.46107 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08452 | 1444 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.17328 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.4747 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.26122 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.44613 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.81232 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 7.92159 | 49353 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.0953 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.2715 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 6.0551 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
62
Monitored processes
21
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1640 | netsh advfirewall firewall add rule name="Radmin VPN Control Service" dir=in action=allow program="C:\Program Files\Radmin VPN\RvControlSvc.exe" enable=yes profile=any | C:\Windows\system32\netsh.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Temp\is-9TST2.tmp\Radmin_VPN_1.0.3722.4.tmp" /SL5="$3011E,21000555,188928,C:\Users\admin\AppData\Local\Temp\Radmin_VPN_1.0.3722.4.exe" /SPAWNWND=$20116 /NOTIFYWND=$2011C | C:\Users\admin\AppData\Local\Temp\is-9TST2.tmp\Radmin_VPN_1.0.3722.4.tmp | Radmin_VPN_1.0.3722.4.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2180 | "C:\Users\admin\AppData\Local\Temp\is-59SM2.tmp\Radmin_VPN_1.0.3722.4.tmp" /SL5="$2011C,21000555,188928,C:\Users\admin\AppData\Local\Temp\Radmin_VPN_1.0.3722.4.exe" | C:\Users\admin\AppData\Local\Temp\is-59SM2.tmp\Radmin_VPN_1.0.3722.4.tmp | — | Radmin_VPN_1.0.3722.4.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Radmin VPN\RvControlSvc.exe" /service | C:\Program Files\Radmin VPN\RvControlSvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin VPN Control Service Exit code: 0 Version: 1.0.3722.4 Modules
| |||||||||||||||
| 2584 | netsh interface ip delete route prefix=0.0.0.0/0 interface="Radmin VPN" nexthop=26.0.0.1 | C:\Windows\system32\netsh.exe | — | RvControlSvc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2672 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | C:\Windows\system32\MsiExec.exe -Embedding 5059FCDBA49631C2F3C0DCAA121DA1EC | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3048 | netsh interface set interface name="Local Area Connection" newname="Radmin VPN" | C:\Windows\system32\netsh.exe | — | RvControlSvc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3116 | netsh interface ipv6 add address interface="Radmin VPN" address=fdfd::1a32:1edf | C:\Windows\system32\netsh.exe | — | RvControlSvc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3124 | C:\Windows\system32\MsiExec.exe -Embedding D9F862A7C1DC05153124C186919ED05C M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 949
Read events
972
Write events
906
Delete events
71
Modification events
| (PID) Process: | (2124) Radmin_VPN_1.0.3722.4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 4C0800000891DEDF84CFD401 | |||
| (PID) Process: | (2124) Radmin_VPN_1.0.3722.4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C7FA676ABD85EF0A591AD3F9ABE54AF23591630B550CEF0EABDAAC53BA53250E | |||
| (PID) Process: | (2124) Radmin_VPN_1.0.3722.4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2672) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2672) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: 700A0000DECF8DE484CFD401 | |||
| (PID) Process: | (2672) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: B35A590A76057A698CEA8F7C7F8B50465D72DDA8A41C55C6AF6C9B7C2AADB6C8 | |||
| (PID) Process: | (2672) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2672) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | |
Value: C:\Windows\Installer\1b2ba2.ipi | |||
| (PID) Process: | (2672) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\1b2ba3.rbs |
Value: 30723972 | |||
| (PID) Process: | (2672) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\1b2ba3.rbsLow |
Value: 3844810288 | |||
Executable files
70
Suspicious files
17
Text files
26
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | Radmin_VPN_1.0.3722.4.tmp | C:\Users\admin\AppData\Local\Temp\is-CKIHQ.tmp\is-0EEH1.tmp | — | |
MD5:— | SHA256:— | |||
| 2124 | Radmin_VPN_1.0.3722.4.tmp | C:\Users\admin\AppData\Local\Temp\is-CKIHQ.tmp\RadminVPN_1.0.3722.4.msi | — | |
MD5:— | SHA256:— | |||
| 2672 | msiexec.exe | C:\Windows\Installer\1b2ba0.msi | — | |
MD5:— | SHA256:— | |||
| 2672 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF9A7B6025D192E8E1.TMP | — | |
MD5:— | SHA256:— | |||
| 2672 | msiexec.exe | C:\Program Files\Radmin VPN\rserv35ml.msi | — | |
MD5:— | SHA256:— | |||
| 2672 | msiexec.exe | C:\Windows\Installer\1b2ba2.ipi | binary | |
MD5:B85AA3718FAA322D7F85CC1472F33867 | SHA256:D2A4513512A4B759467014C6B8D99F0596EB54389B0AA389B1D11BB44DF60F07 | |||
| 2672 | msiexec.exe | C:\Windows\Installer\MSI2E30.tmp | binary | |
MD5:78C68AD0907D3B99BD771755AF2B81DE | SHA256:568D3DE80F1ADFFBEEADD5768C6F7A536411FDFF2D4271F8914F453D52FFC5A8 | |||
| 2672 | msiexec.exe | C:\Program Files\Radmin VPN\NetMP60.cat | cat | |
MD5:A24D05BDFC34972ACBD3D884E1459CE9 | SHA256:CE0BF211741C9351A70F5A0AFE8CB6CEF39FCD4D1E42088A25FB9680EE858CC1 | |||
| 2124 | Radmin_VPN_1.0.3722.4.tmp | C:\Users\admin\AppData\Local\Temp\is-CKIHQ.tmp\Rvis_install_dll.dll | executable | |
MD5:C013FA5920E8585E38980751100F613A | SHA256:A5552C6FC01291238D005A610F9B97DDB83324C646FB6649A3C8B297F26CE024 | |||
| 3572 | Radmin_VPN_1.0.3722.4.exe | C:\Users\admin\AppData\Local\Temp\is-59SM2.tmp\Radmin_VPN_1.0.3722.4.tmp | executable | |
MD5:EC5312E06DA51691D2E26820F3C93ECE | SHA256:421CB7E48E3063D927EEFE28940E119FB1309A3990BC7325C7F7052A2B286A09 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
18
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | RvControlSvc.exe | 5.63.147.60:17301 | fail468.rol.famatech.com | Hosting Services Inc | GB | unknown |
2564 | RvControlSvc.exe | 67.212.229.52:17301 | — | WestHost, Inc. | US | unknown |
2564 | RvControlSvc.exe | 184.173.146.60:17301 | fail490.rol.famatech.com | SoftLayer Technologies Inc. | US | unknown |
2564 | RvControlSvc.exe | 199.195.196.140:17301 | fail491.rol.famatech.com | WestHost, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
r714.z714.rol.famatech.com |
| unknown |
fail468.rol.famatech.com |
| unknown |
r3117563.z941.rol.famatech.com |
| unknown |
fail490.rol.famatech.com |
| unknown |
fail491.rol.famatech.com |
| unknown |
teredo.ipv6.microsoft.com |
| whitelisted |
r564.z564.rol.famatech.com |
| unknown |
Threats
Process | Message |
|---|---|
RvRvpnGui.exe | CPipeThread()
|
RvRvpnGui.exe | Country: "ar-sa" id: 1025
|
RvRvpnGui.exe | Country: "bg-bg" id: 1026
|
RvRvpnGui.exe | Country: "ca-es" id: 1027
|
RvRvpnGui.exe | Country: "zh-tw" id: 1028
|
RvRvpnGui.exe | Country: "cs-cz" id: 1029
|
RvRvpnGui.exe | Country: "da-dk" id: 1030
|
RvRvpnGui.exe | Country: "de-de" id: 1031
|
RvRvpnGui.exe | Country: "el-gr" id: 1032
|
RvRvpnGui.exe | Country: "en-us" id: 1033
|