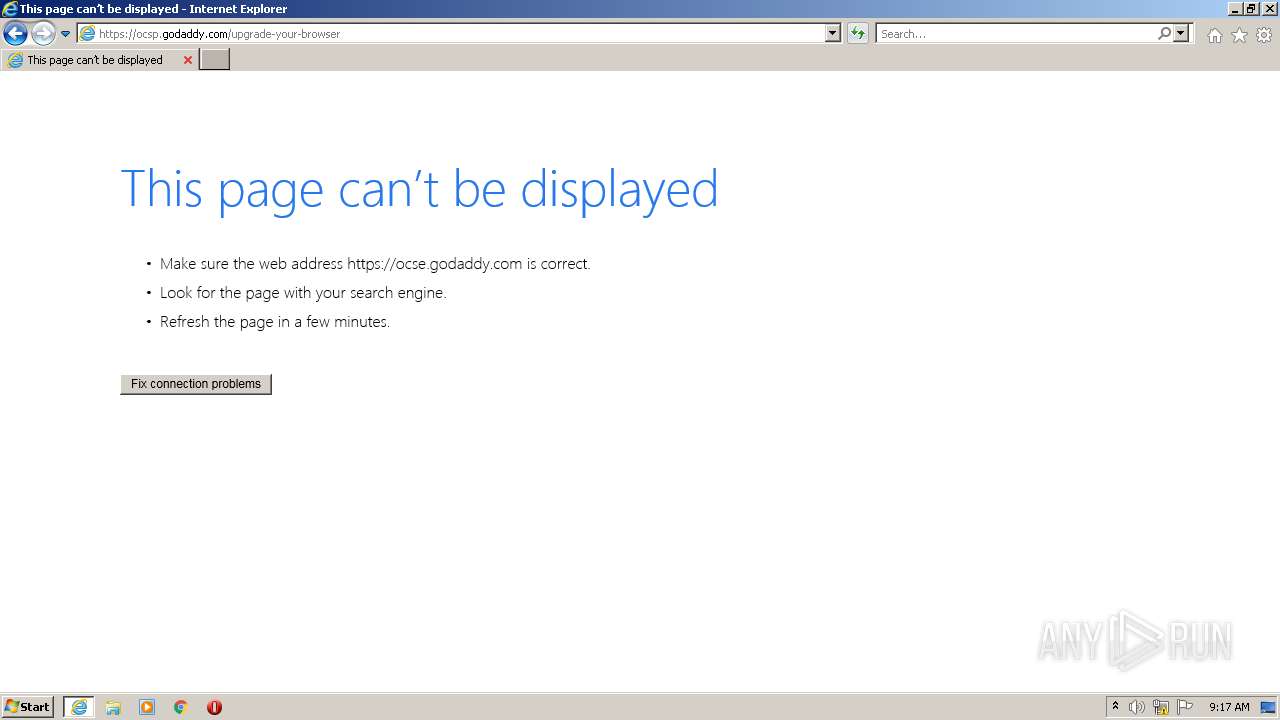
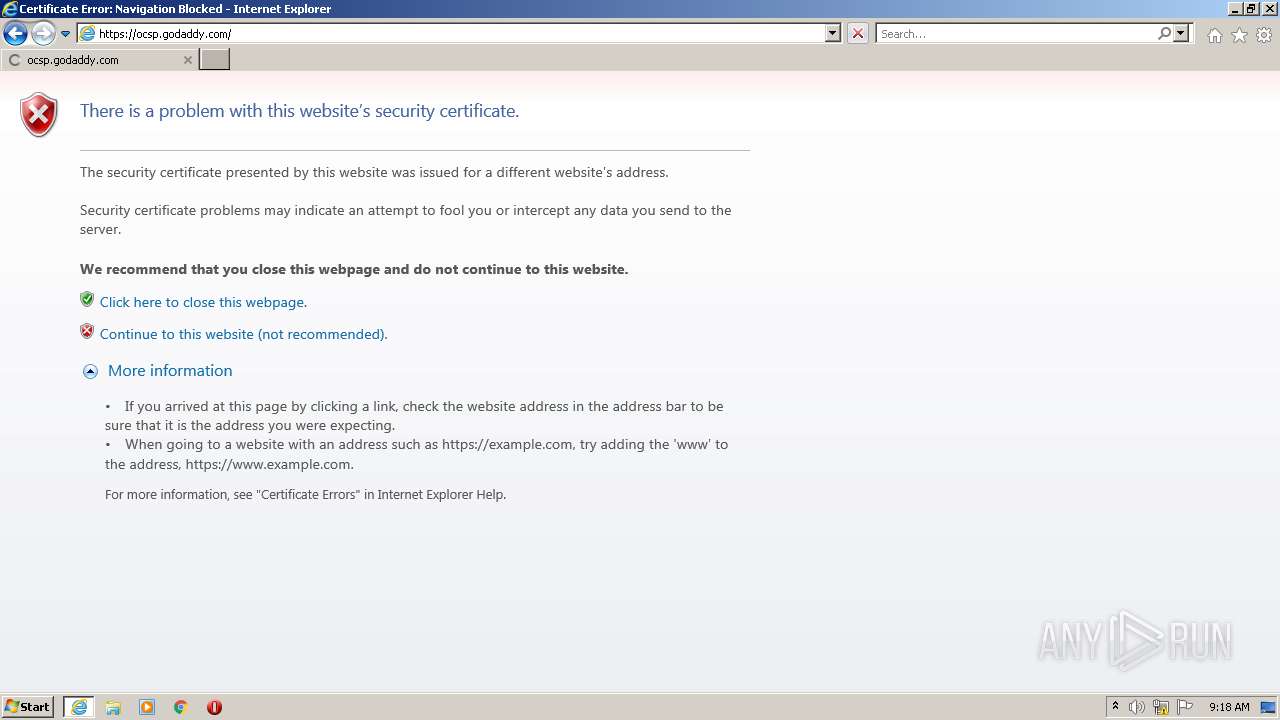
| URL: | http://ocsp.godaddy.com |
| Full analysis: | https://app.any.run/tasks/0fecde62-8682-468e-9c30-3a9c66db4cb3 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2022, 08:16:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 967055BD2D1AC790FEA56D4D12B80AD4 |
| SHA1: | A375E80D6E6F266463E20E5CCA97E252D30E5477 |
| SHA256: | C80FE3C58C5193E3125BC80C805B1C60C272B81E3DE887F6C5EDE9EA11E77ED7 |
| SSDEEP: | 3:N1KRGWVwcZI:CgWVwcZI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 900)
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 3060)
Reads the date of Windows installation
- rundll32.exe (PID: 3300)
- rundll32.exe (PID: 3800)
INFO
Reads the computer name
- iexplore.exe (PID: 3060)
- iexplore.exe (PID: 900)
- rundll32.exe (PID: 3300)
- rundll32.exe (PID: 3800)
Changes internet zones settings
- iexplore.exe (PID: 3060)
Checks supported languages
- iexplore.exe (PID: 3060)
- rundll32.exe (PID: 3300)
- rundll32.exe (PID: 3800)
- NOTEPAD.EXE (PID: 2788)
- iexplore.exe (PID: 900)
Checks Windows Trust Settings
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 3060)
- rundll32.exe (PID: 3300)
- rundll32.exe (PID: 3800)
Creates files in the user directory
- iexplore.exe (PID: 900)
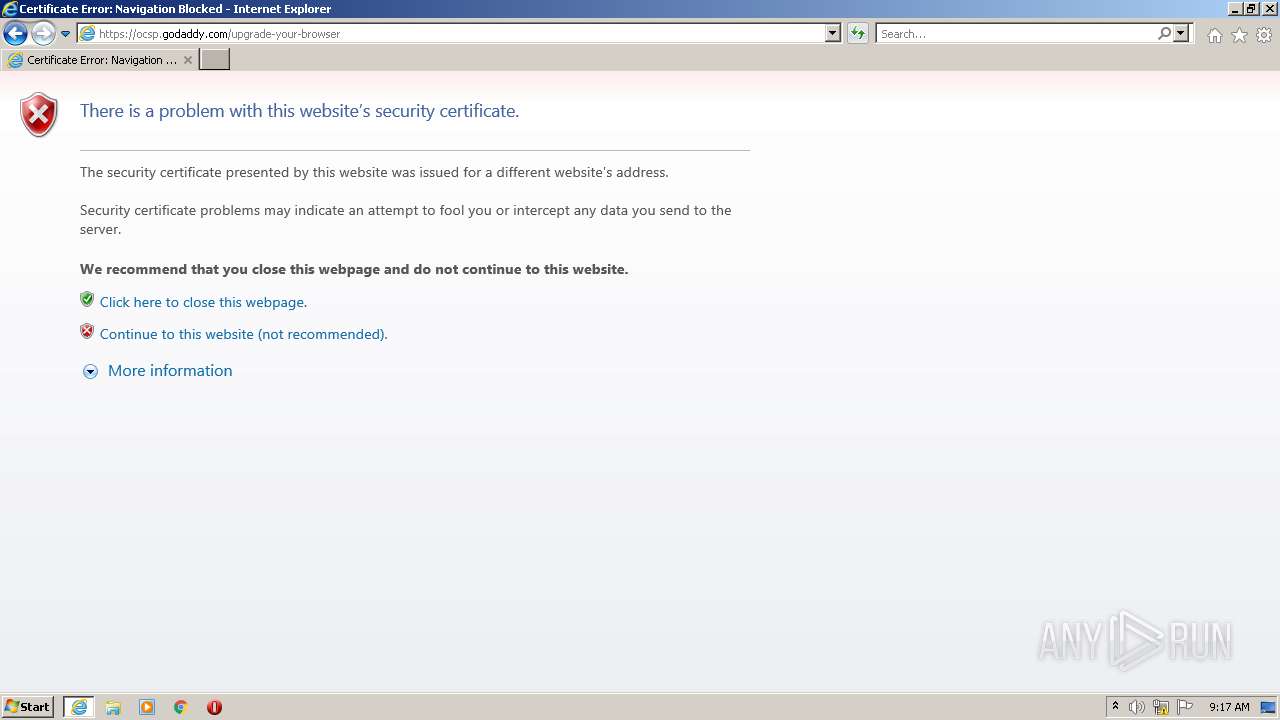
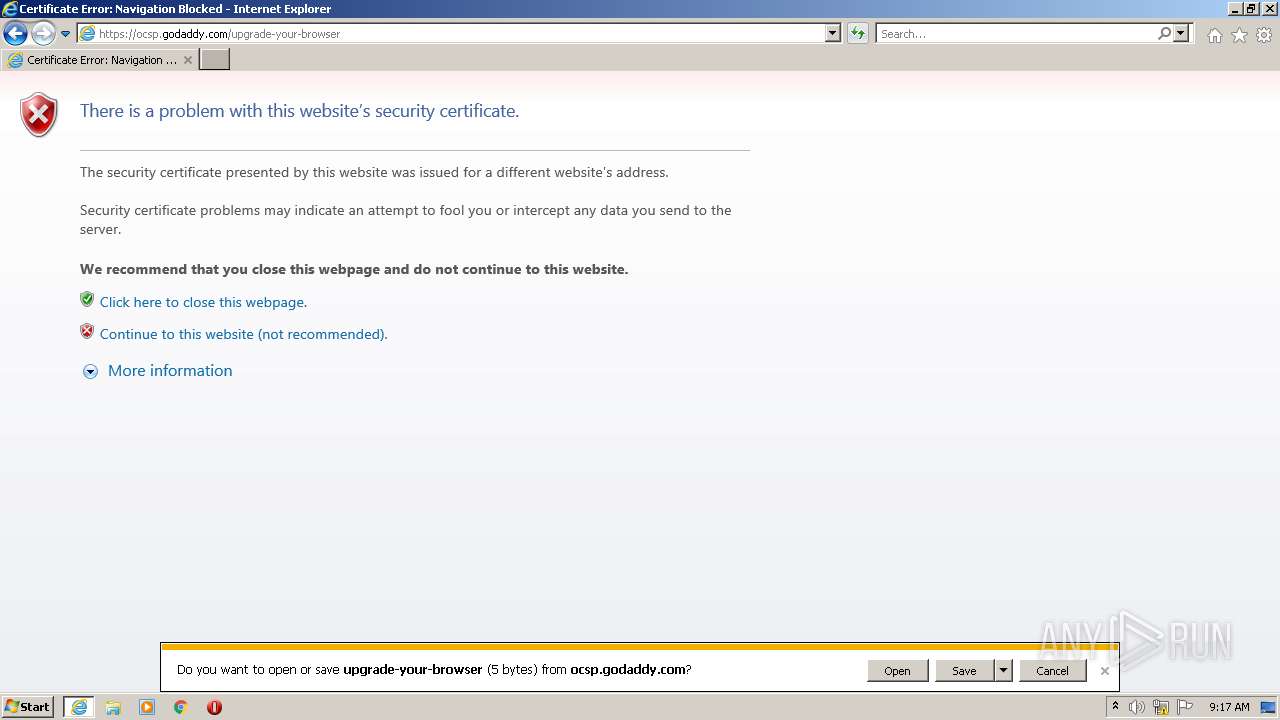
Changes settings of System certificates
- iexplore.exe (PID: 3060)
Application launched itself
- iexplore.exe (PID: 3060)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3060)
Reads internet explorer settings
- iexplore.exe (PID: 900)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3060)
Reads settings of System Certificates
- iexplore.exe (PID: 3060)
- iexplore.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3060 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
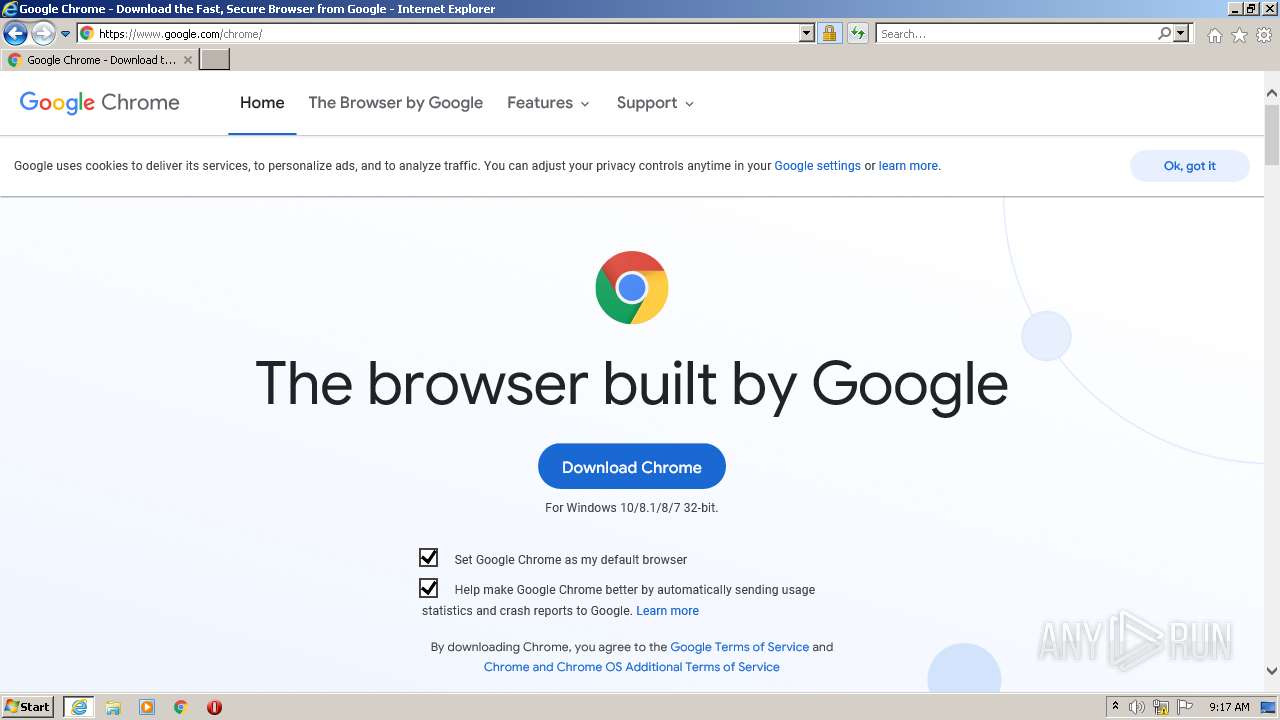
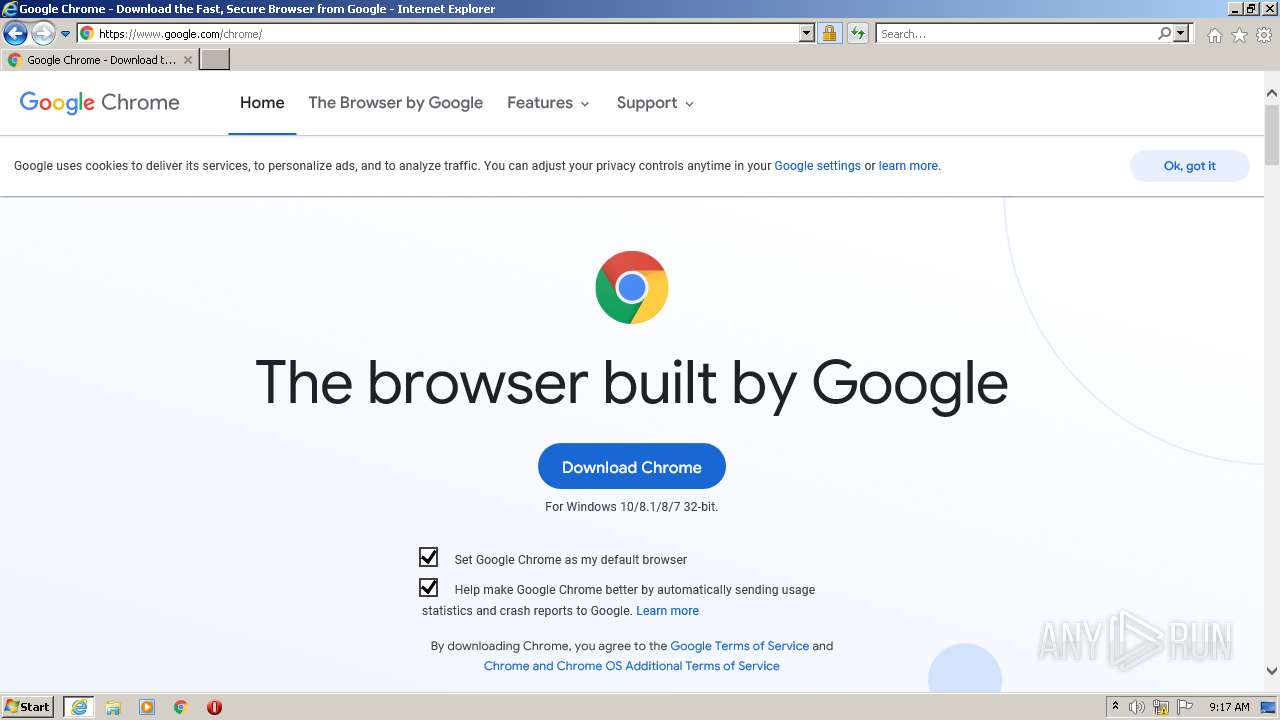
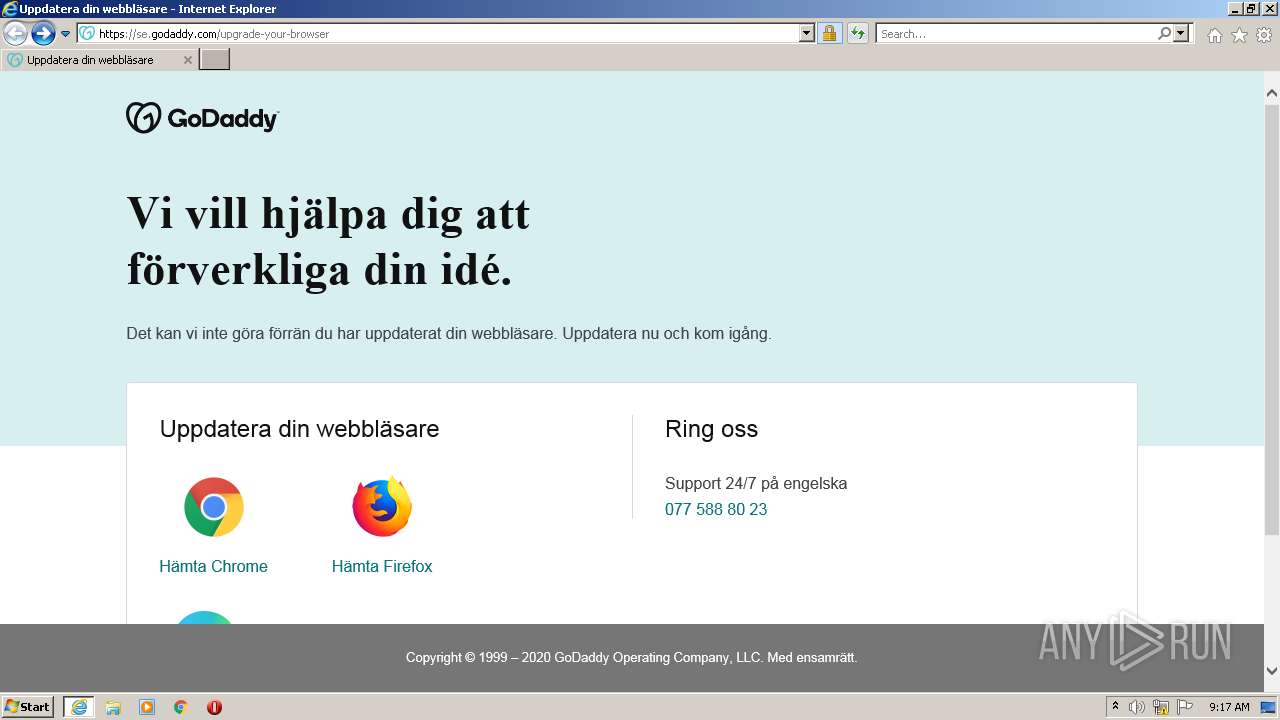
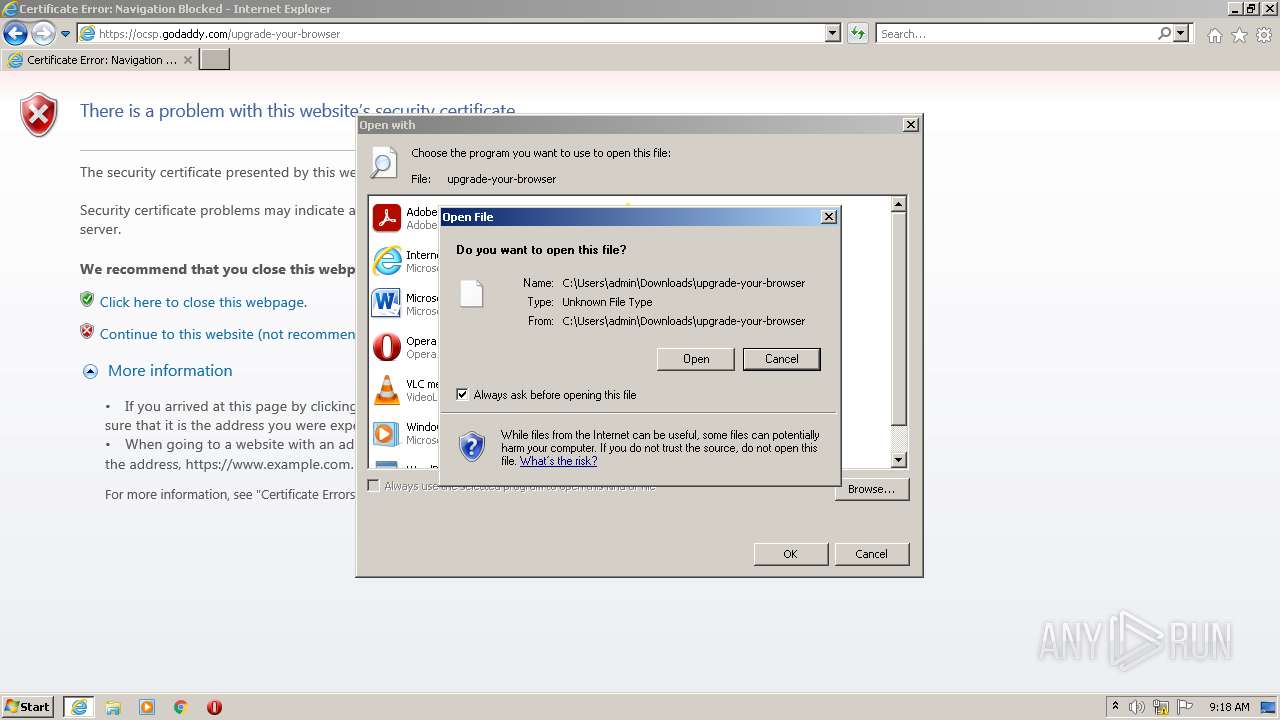
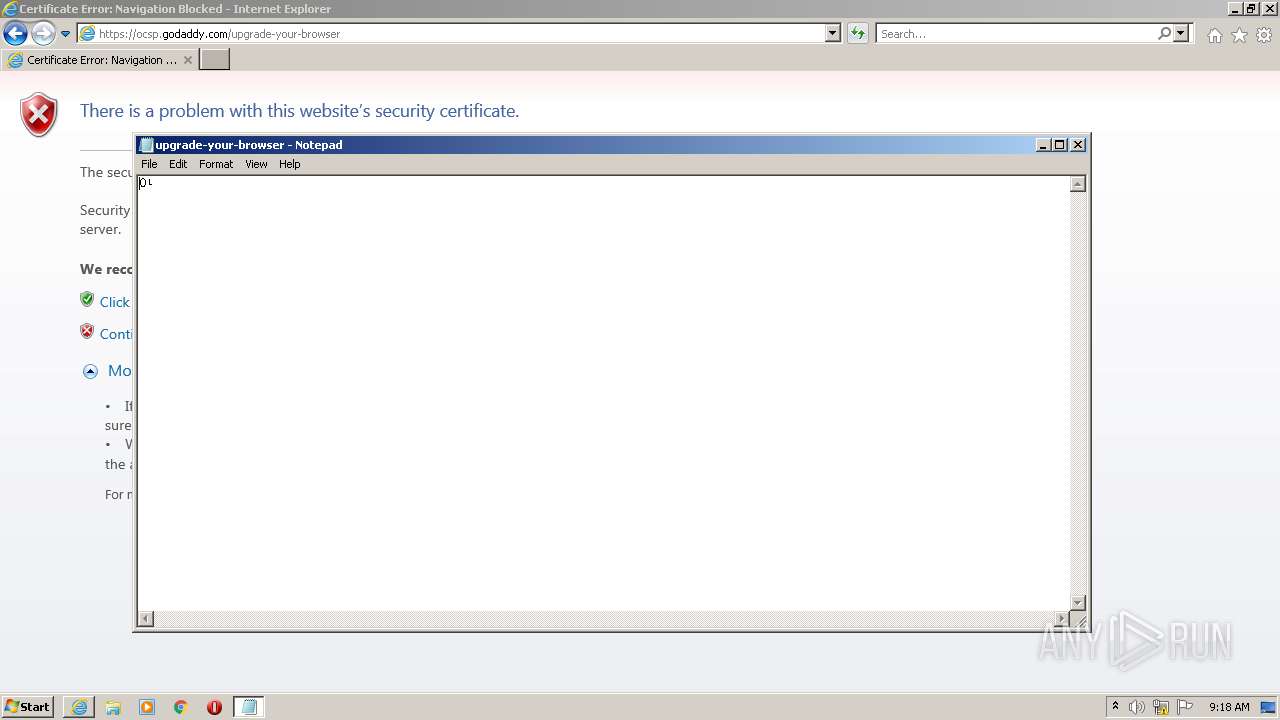
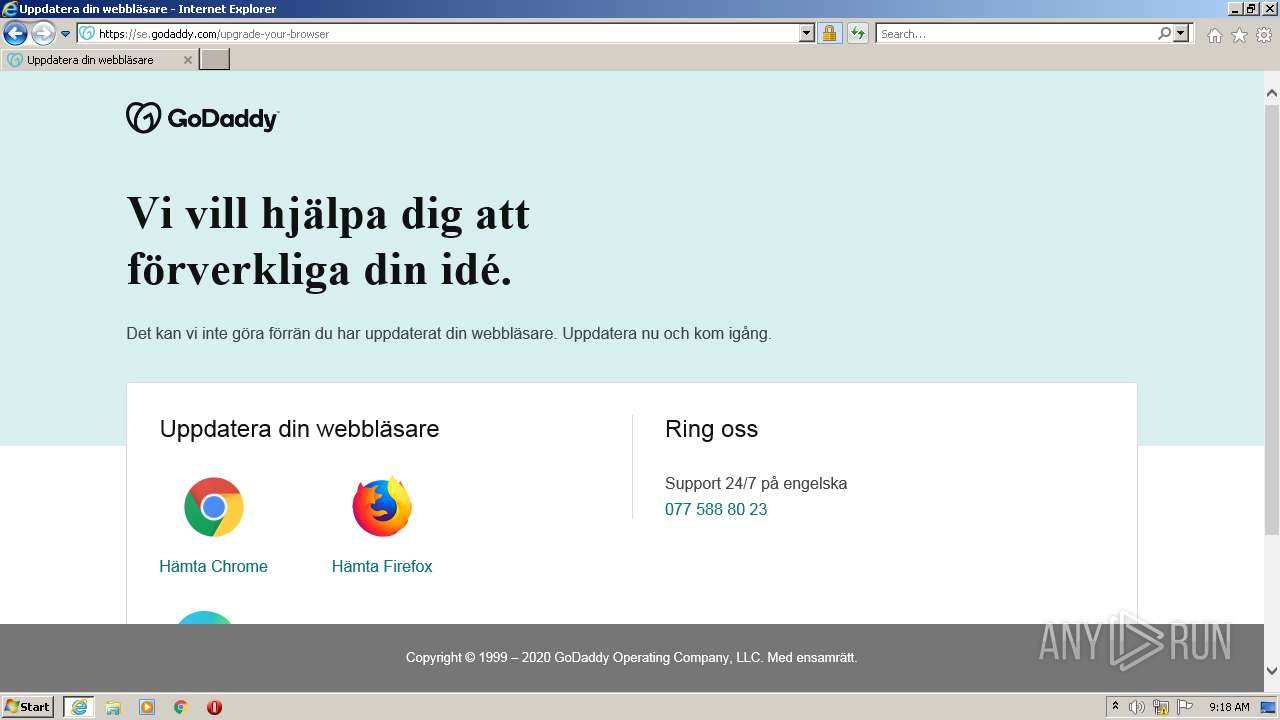
| 2788 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\upgrade-your-browser | C:\Windows\system32\NOTEPAD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
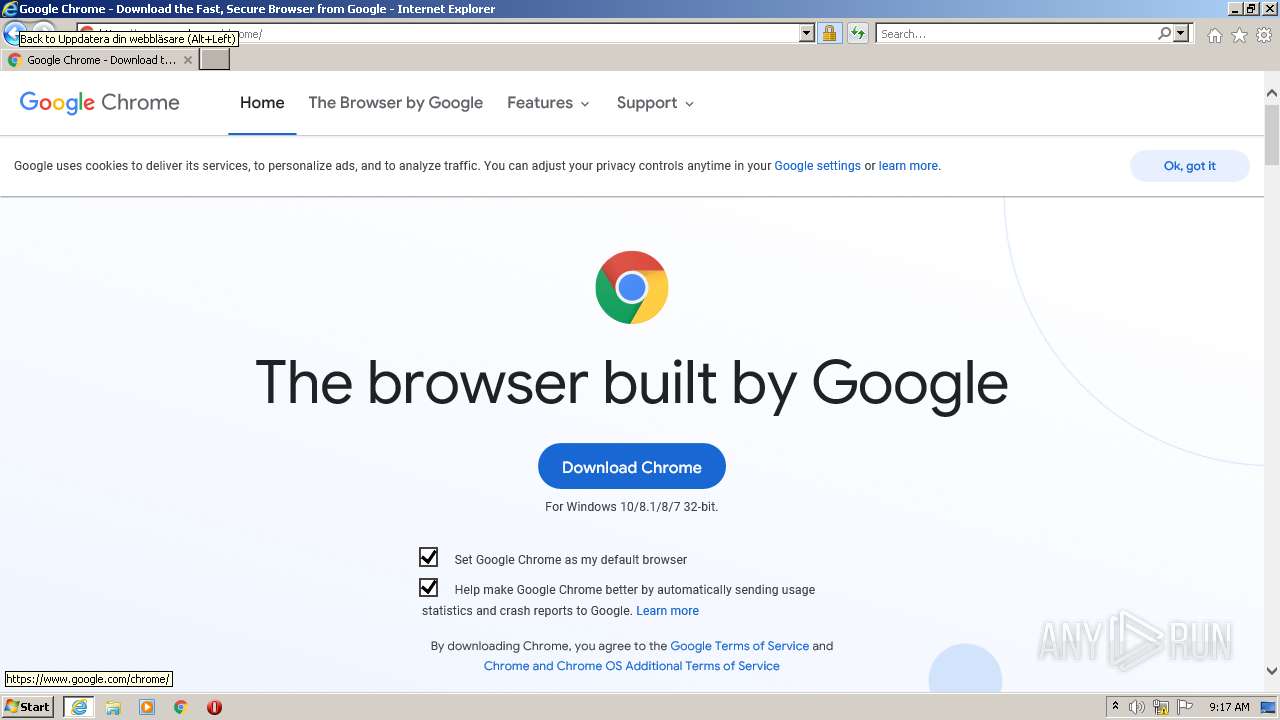
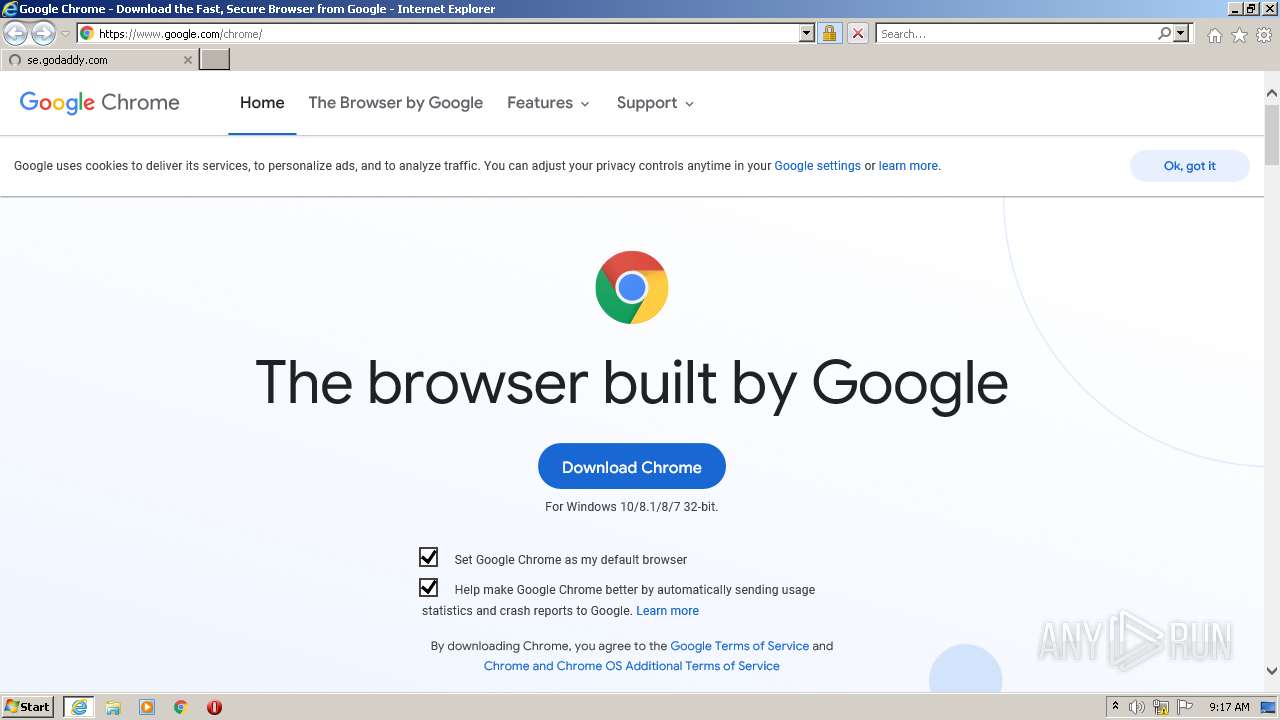
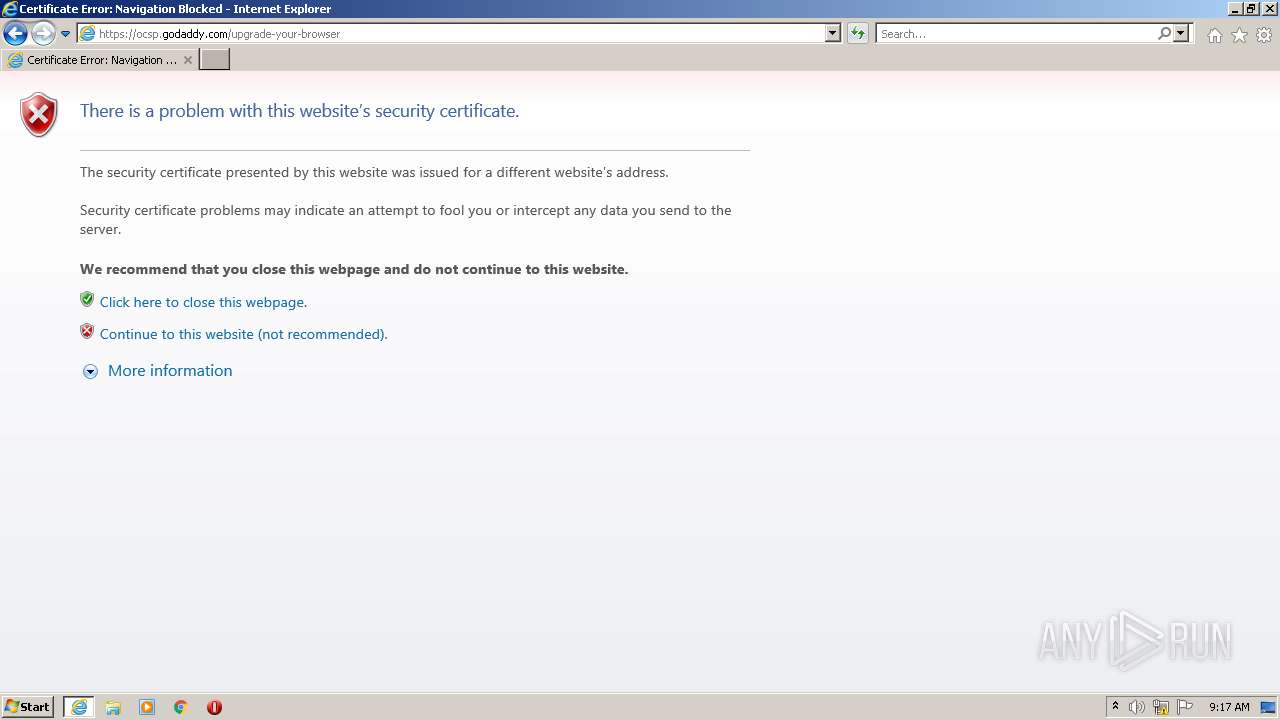
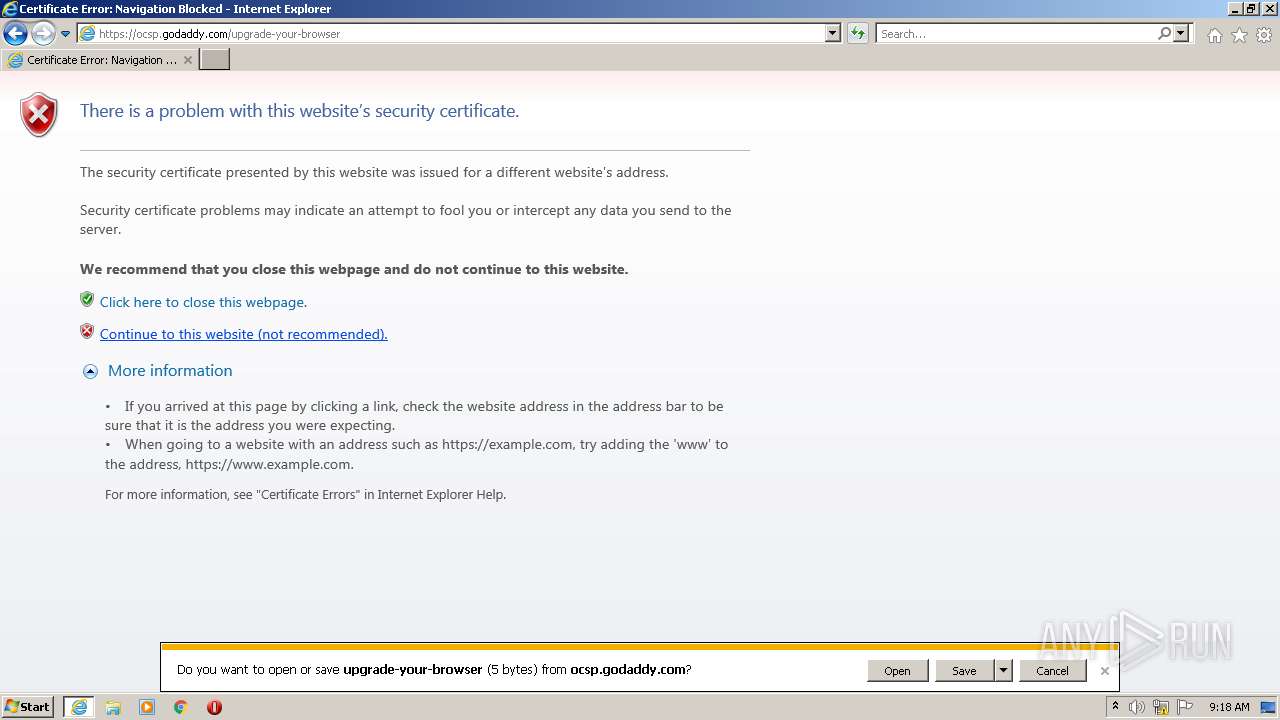
| 3060 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://ocsp.godaddy.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
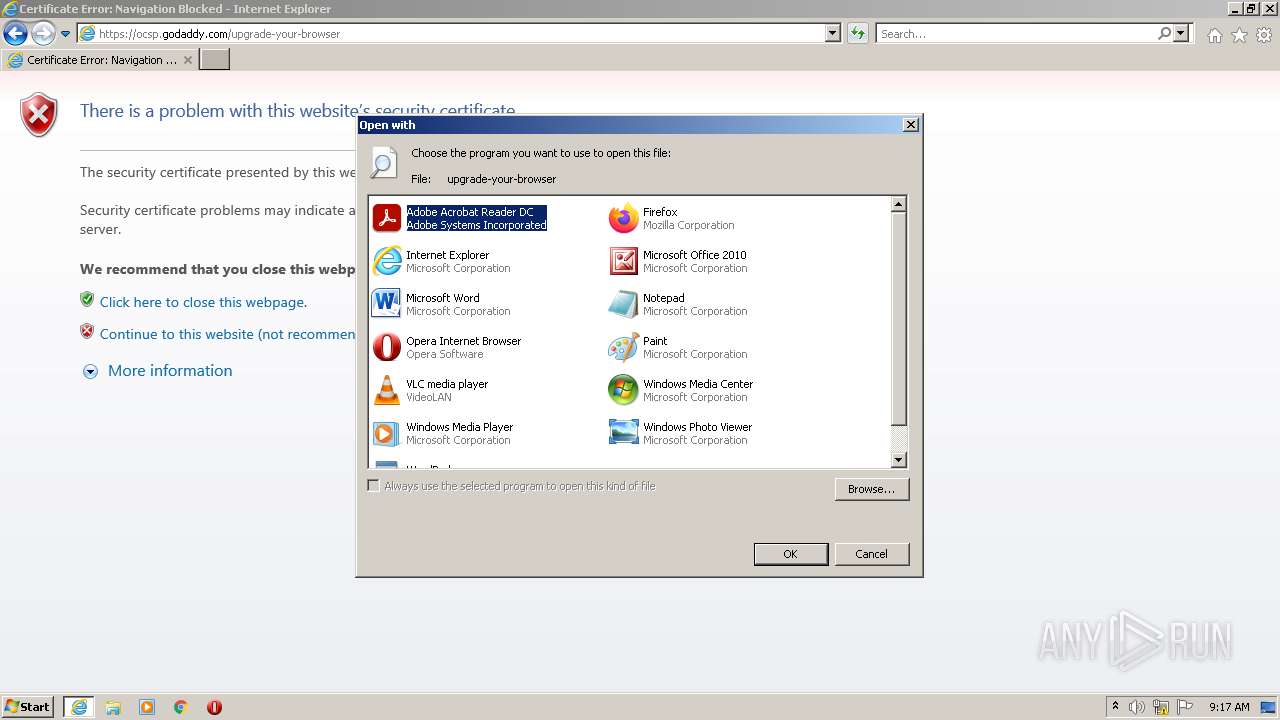
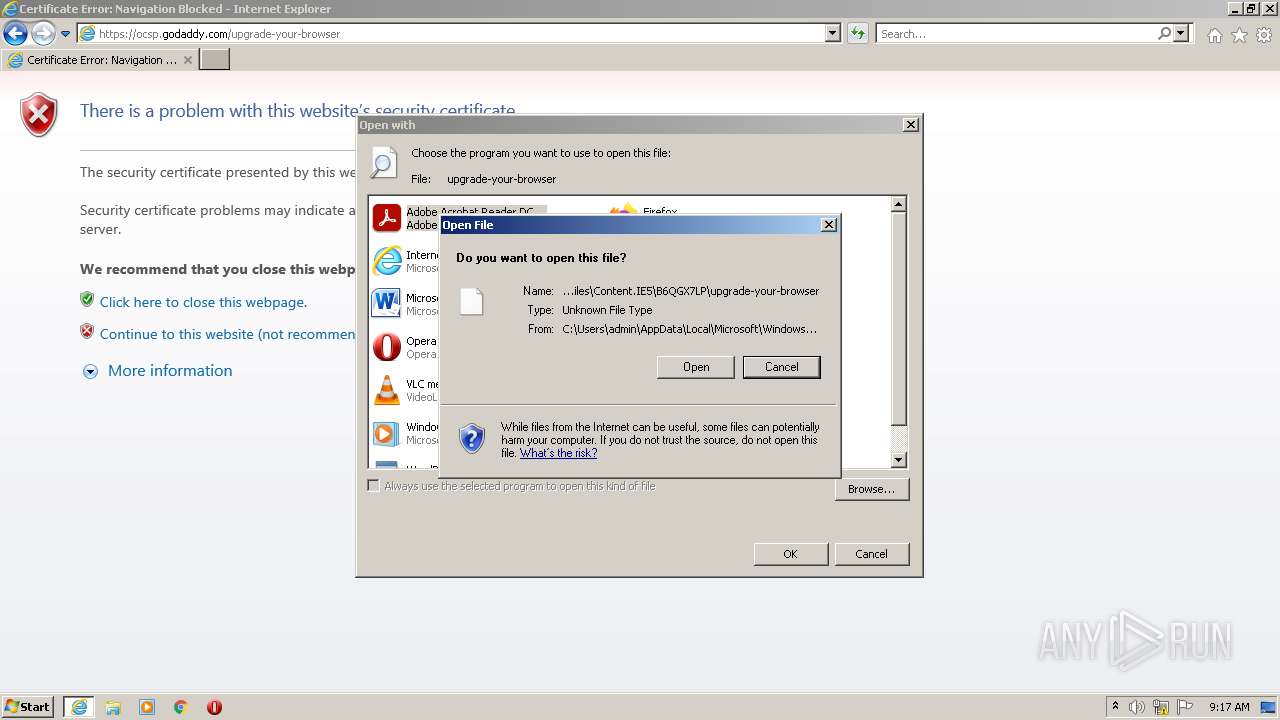
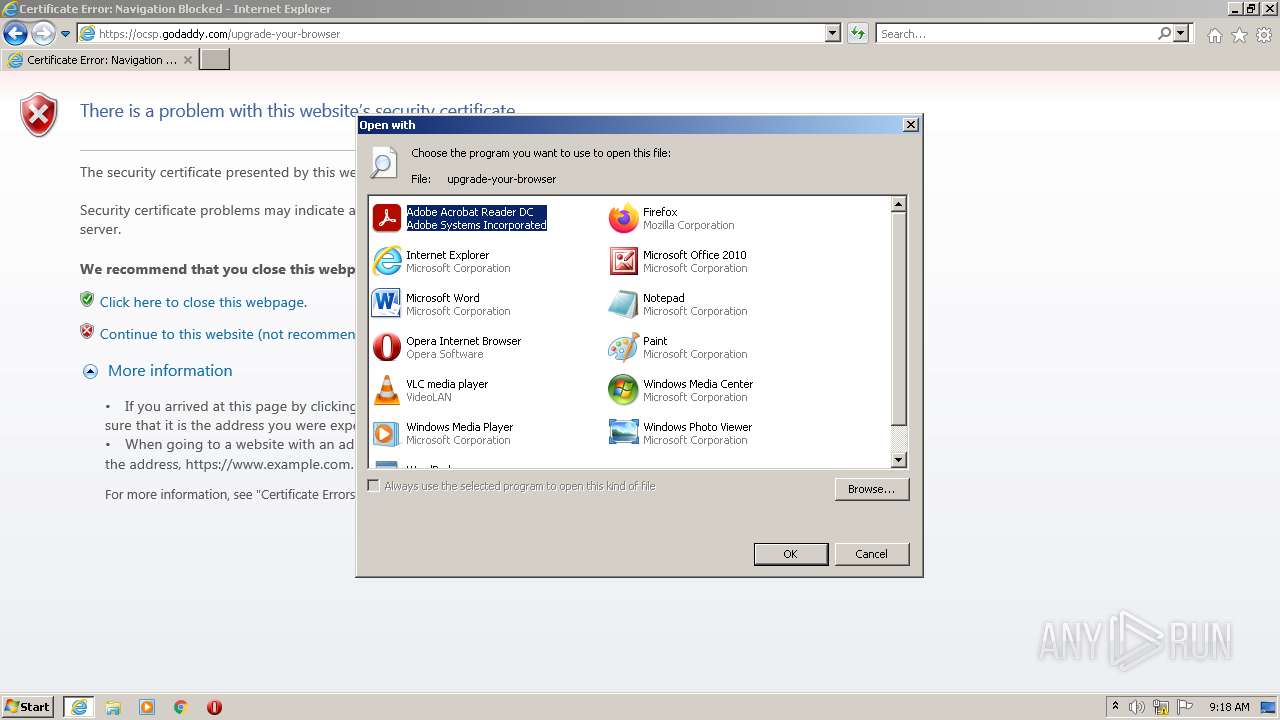
| 3300 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\upgrade-your-browser | C:\Windows\system32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3800 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\upgrade-your-browser | C:\Windows\system32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
19 915
Read events
19 558
Write events
352
Delete events
5
Modification events
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30972341 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30972341 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
25
Text files
84
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6XG8NENJ.txt | text | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\IFMXGSTY.txt | text | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5RW2ABMP.txt | text | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\19QM0T9V.txt | text | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\MLCSRHS7.txt | text | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\84AFE219AEC53B0C9251F5E19EF019BD_2C9D5E6D83DF507CBE6C15521D5D3562 | der | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BC2602F5489CFE3E69F81C6328A4C17C_849A9AE095E451B9FFDF6A58F3A98E26 | binary | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BC2602F5489CFE3E69F81C6328A4C17C_849A9AE095E451B9FFDF6A58F3A98E26 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
87
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
900 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | der | 1.74 Kb | whitelisted |
900 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
900 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.starfieldtech.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCAzkUhA%3D%3D | US | der | 1.70 Kb | whitelisted |
900 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
900 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFEXqDlk0KpHEjSOBz6OhEI%3D | US | der | 471 b | whitelisted |
3060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
900 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCdCo7SwE91lQqnx3AQwRaw | US | der | 472 b | whitelisted |
900 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECcV7e3Q9jc%2BEjjW9IbWOFg%3D | US | der | 471 b | whitelisted |
900 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECCuIlKRrBB3Eo8mqCoQqTs%3D | US | der | 471 b | whitelisted |
900 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC8LbKC6DMw9BLG%2BP%2FsrywD | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
900 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
900 | iexplore.exe | 2.16.241.86:443 | img6.wsimg.com | Akamai International B.V. | — | suspicious |
900 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
900 | iexplore.exe | 192.124.249.36:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
900 | iexplore.exe | 104.89.27.138:443 | www.godaddy.com | Akamai Technologies, Inc. | NL | suspicious |
3060 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3060 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3060 | iexplore.exe | 2.16.241.86:443 | img6.wsimg.com | Akamai International B.V. | — | suspicious |
900 | iexplore.exe | 142.250.186.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
900 | iexplore.exe | 142.250.185.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.godaddy.com |
| whitelisted |
www.godaddy.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
se.godaddy.com |
| unknown |
img6.wsimg.com |
| whitelisted |
ocsp.starfieldtech.com |
| whitelisted |
img1.wsimg.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |