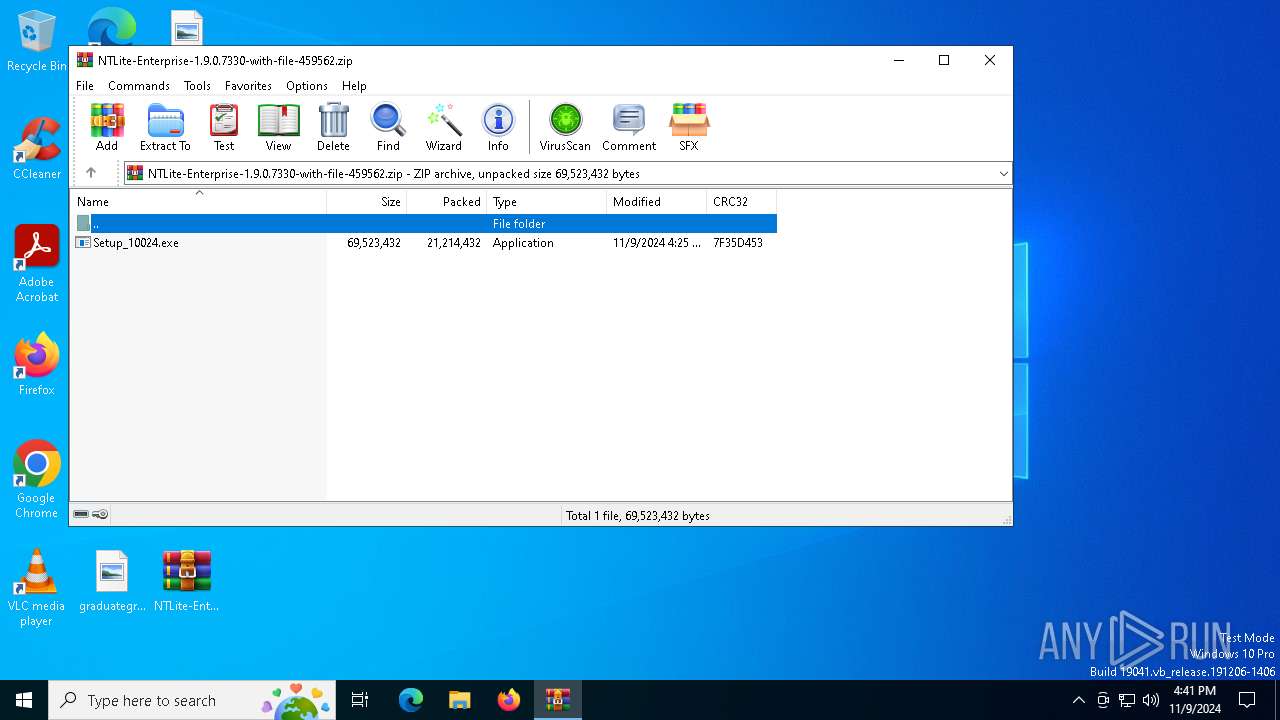
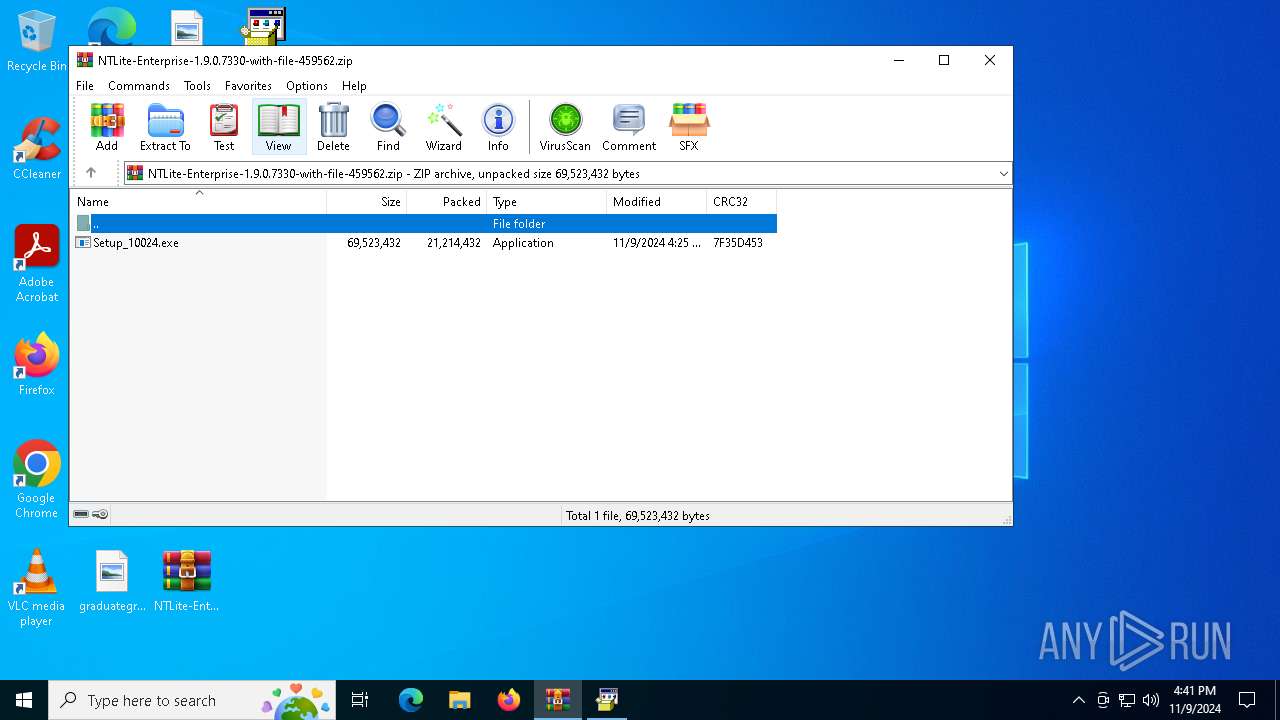
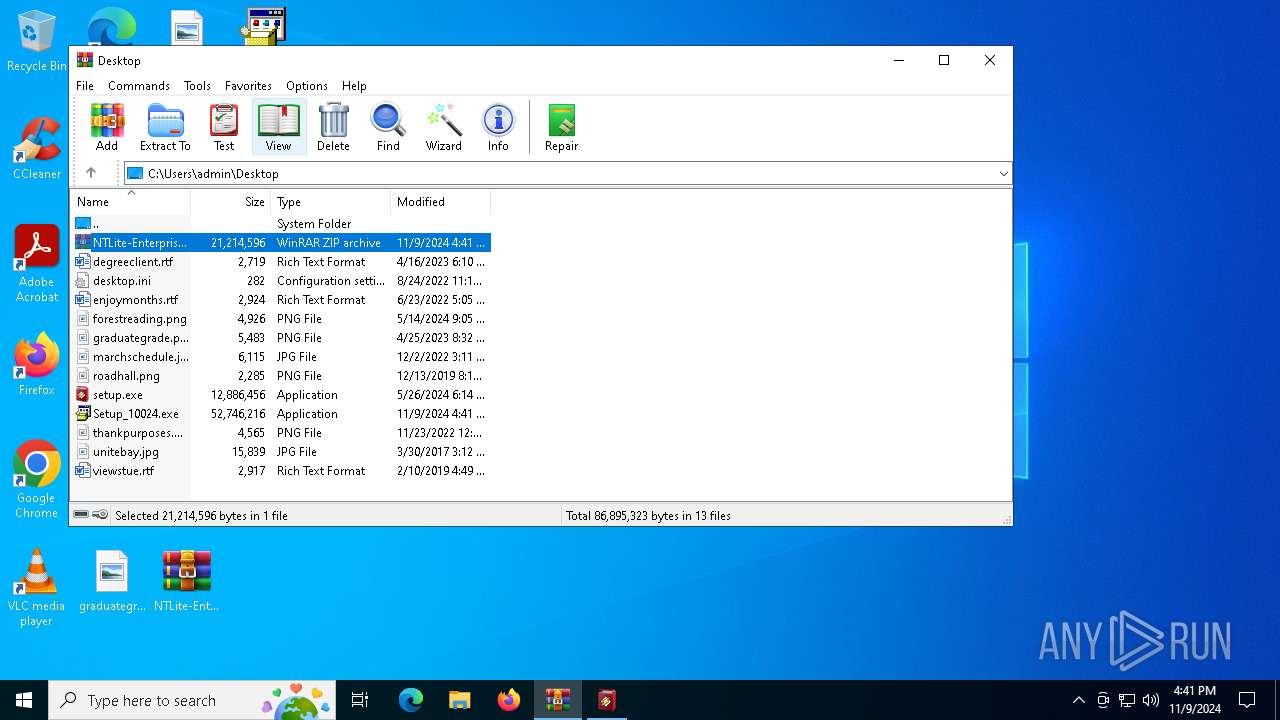
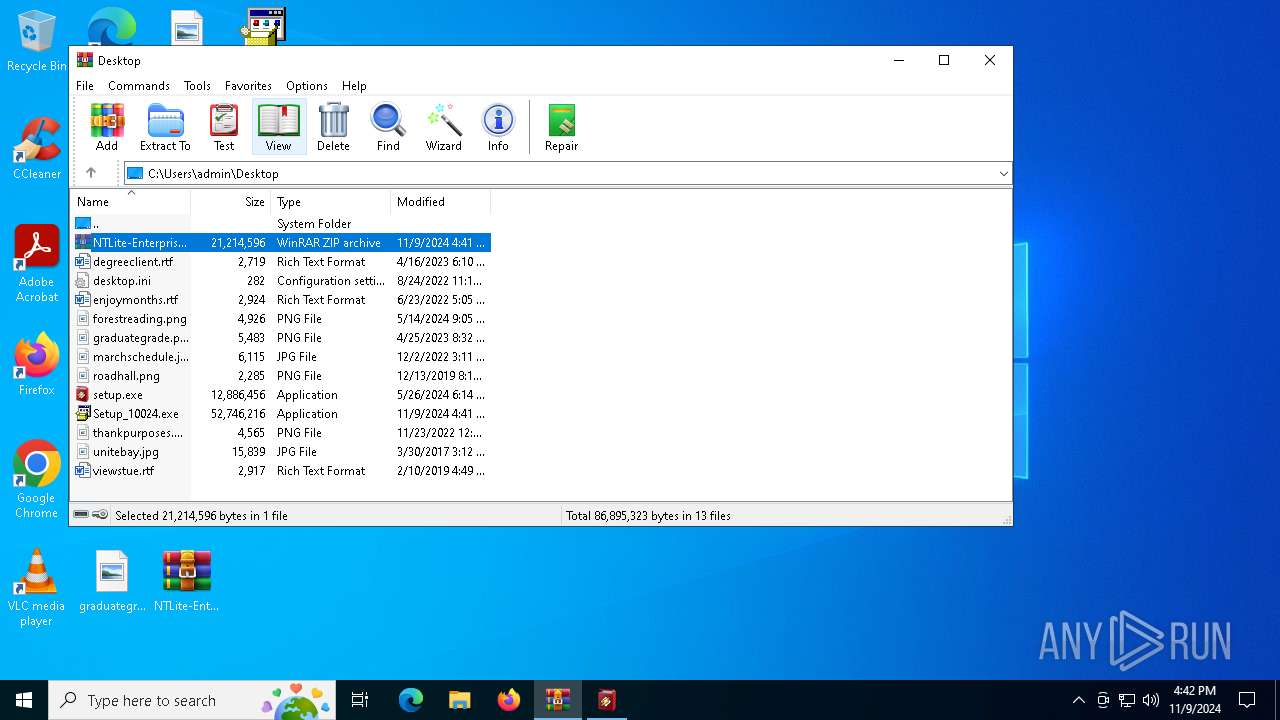
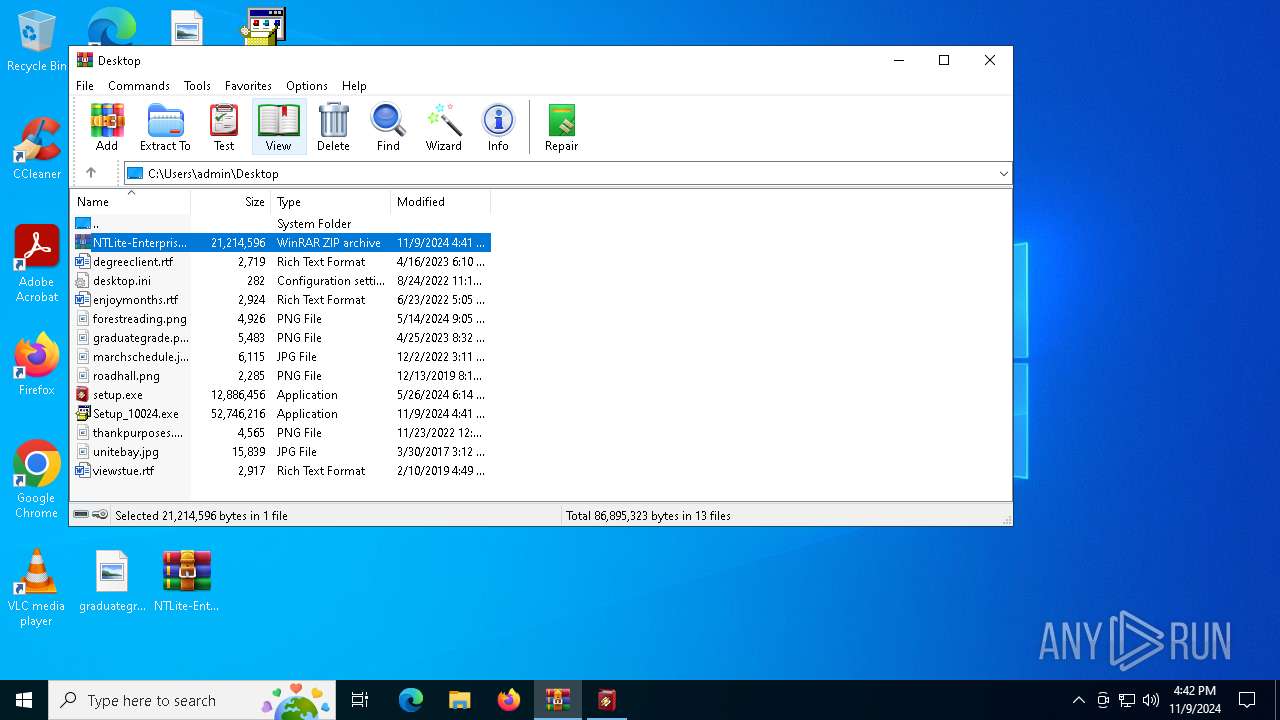
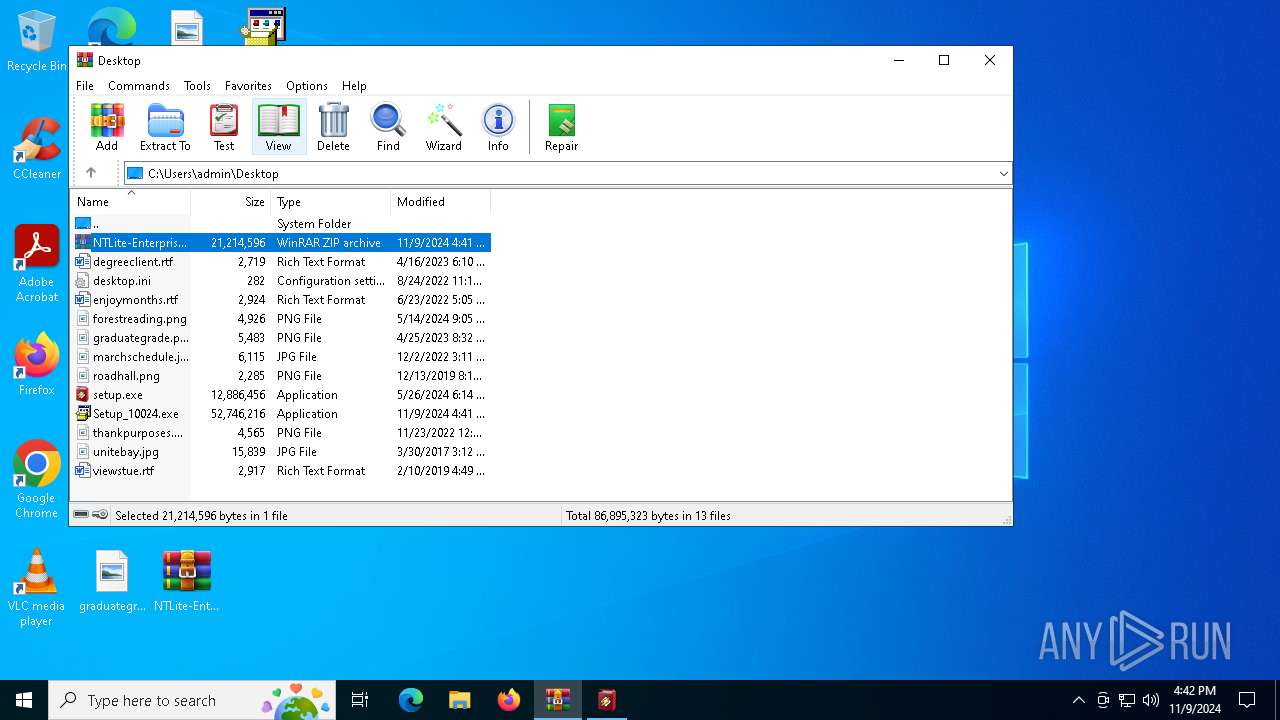
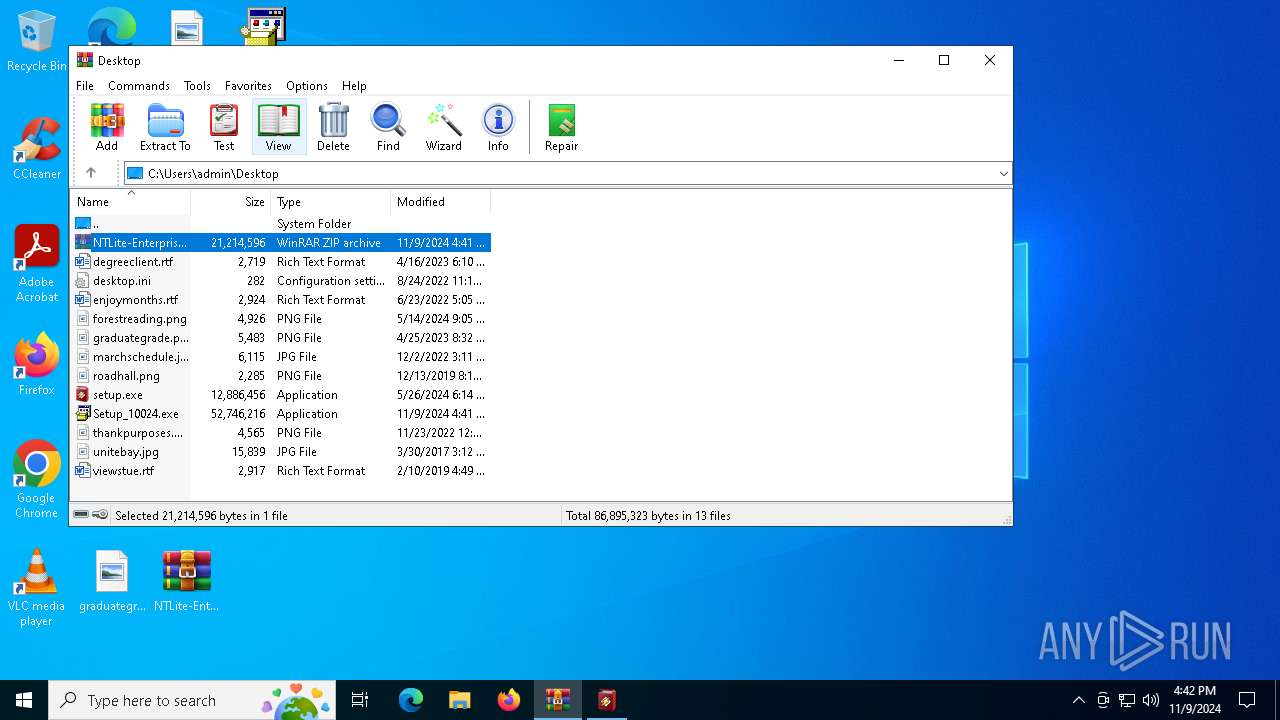
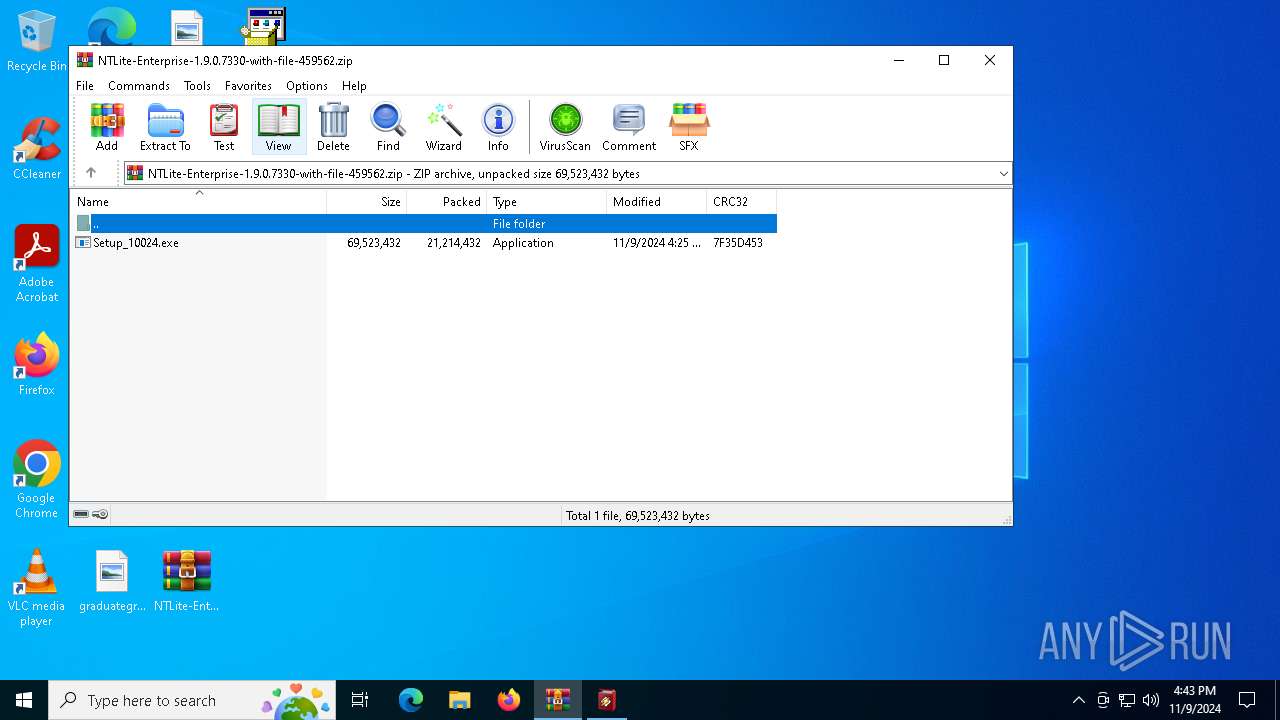
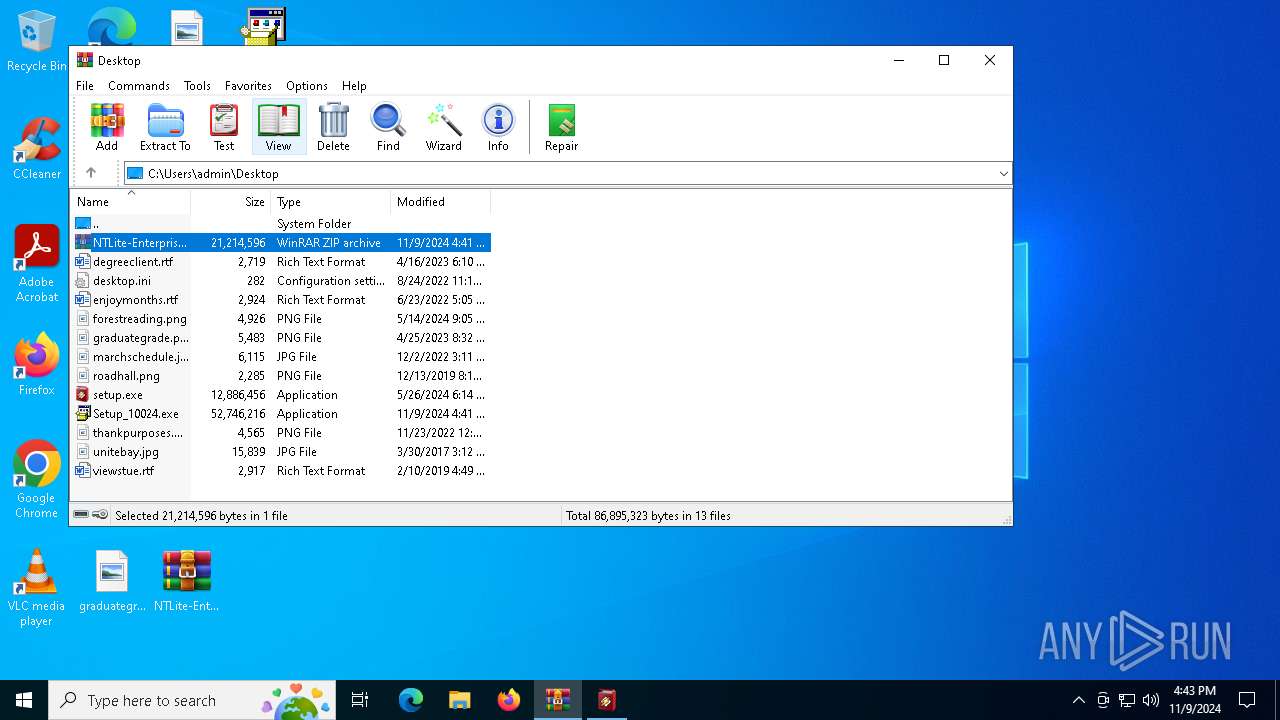
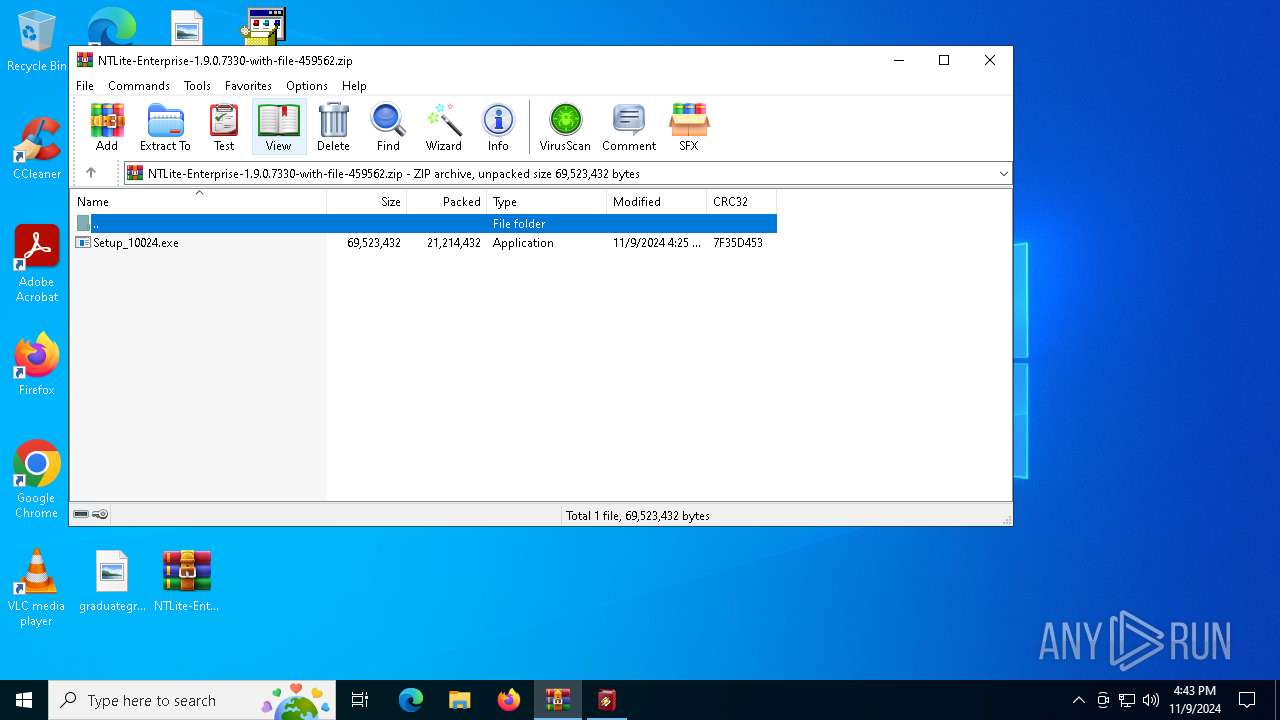
| File name: | NTLite-Enterprise-1.9.0.7330-with-file-459562.zip |
| Full analysis: | https://app.any.run/tasks/e3df0e8f-ab96-430f-b764-777abc164d00 |
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2024, 16:40:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.1 to extract, compression method=deflate64 |
| MD5: | 2806E7B3057B6E2439B036C69FD4D045 |
| SHA1: | 4D6645849FCFCA0BF923755F7D0C7405F879E614 |
| SHA256: | C801CEE5E5DC6465A1F8DF1E7C755D6B407760E14CC8F0855E97C7A7A3D46A1C |
| SSDEEP: | 196608:lNde7BhPHAC3BebkI0Jz0rwTAx/dkSUTJFdTWMbT7m:lNde7BhP73BirwUxSSiLTWsfm |
MALICIOUS
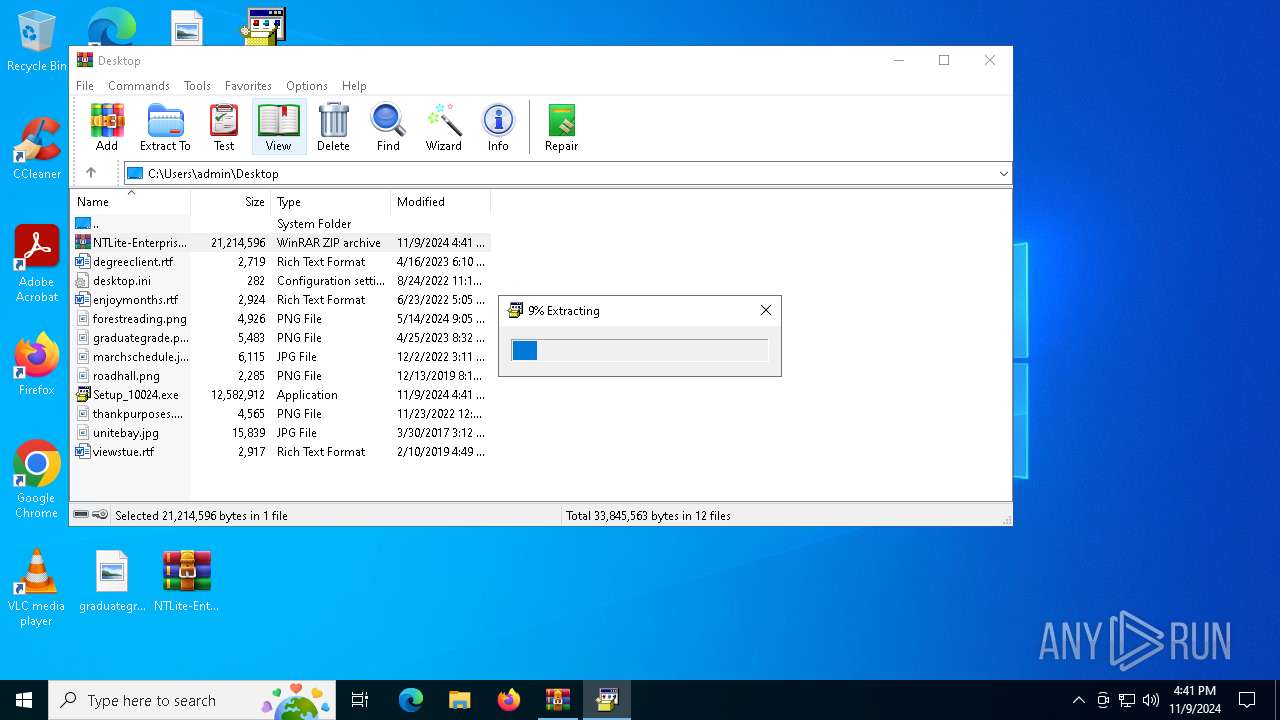
Generic archive extractor
- WinRAR.exe (PID: 6688)
SUSPICIOUS
Reads security settings of Internet Explorer
- Setup_10024.exe (PID: 1584)
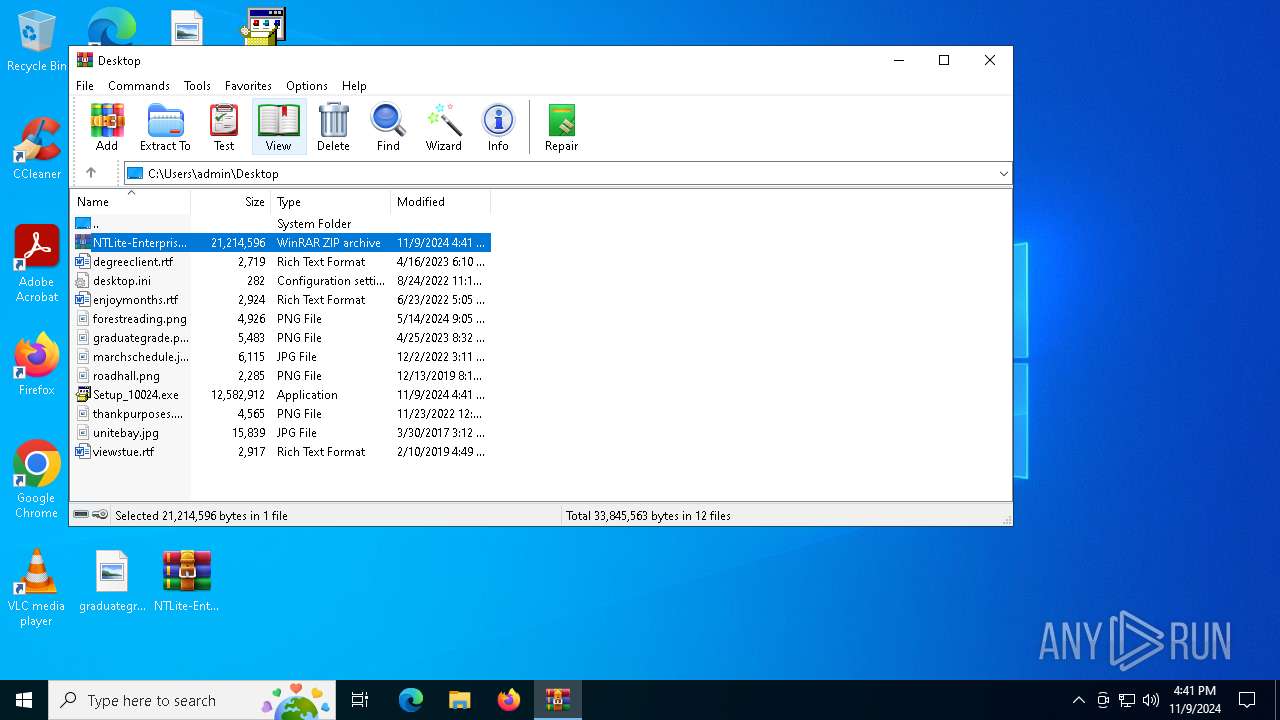
Executable content was dropped or overwritten
- Setup_10024.exe (PID: 1584)
- setup.exe (PID: 5892)
Creates file in the systems drive root
- Setup_10024.exe (PID: 1584)
The process creates files with name similar to system file names
- setup.exe (PID: 5892)
Malware-specific behavior (creating "System.dll" in Temp)
- setup.exe (PID: 5892)
Creates a software uninstall entry
- setup.exe (PID: 5892)
Searches for installed software
- setup.exe (PID: 5892)
INFO
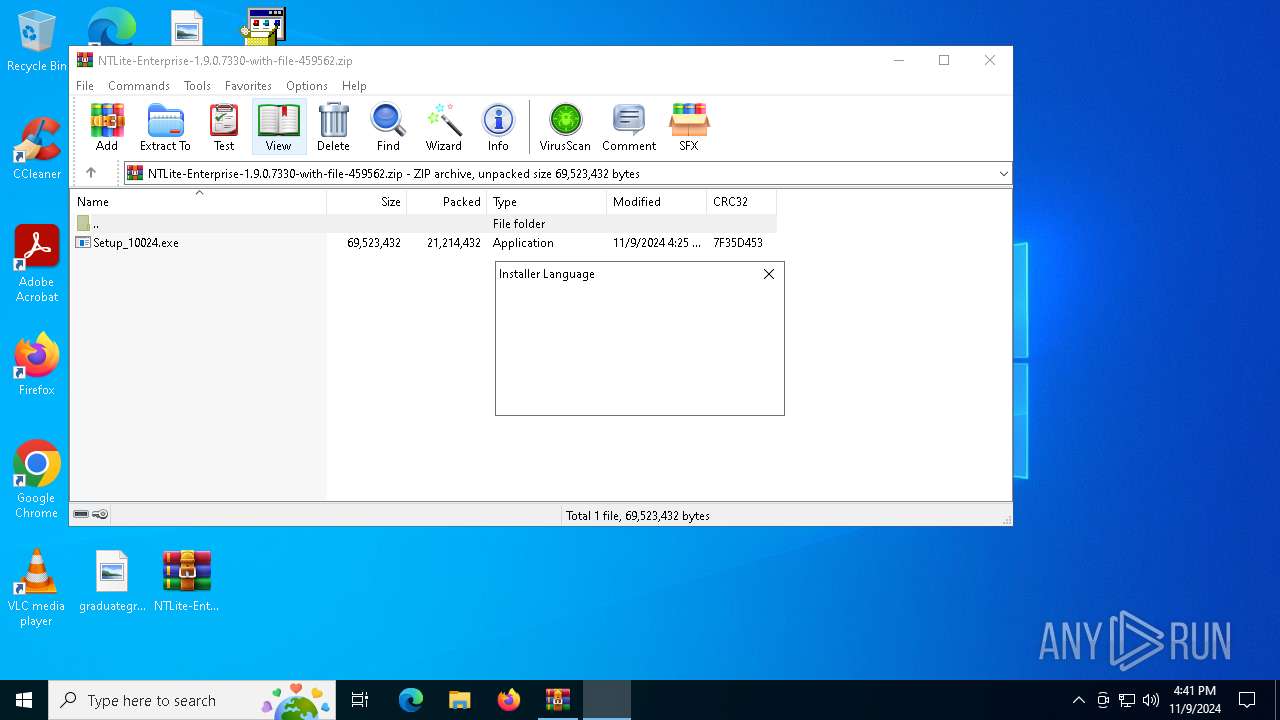
Manual execution by a user
- Setup_10024.exe (PID: 1584)
Reads the computer name
- Setup_10024.exe (PID: 1584)
- setup.exe (PID: 5892)
The process uses the downloaded file
- Setup_10024.exe (PID: 1584)
Process checks computer location settings
- Setup_10024.exe (PID: 1584)
Checks supported languages
- Setup_10024.exe (PID: 1584)
- setup.exe (PID: 5892)
Create files in a temporary directory
- setup.exe (PID: 5892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
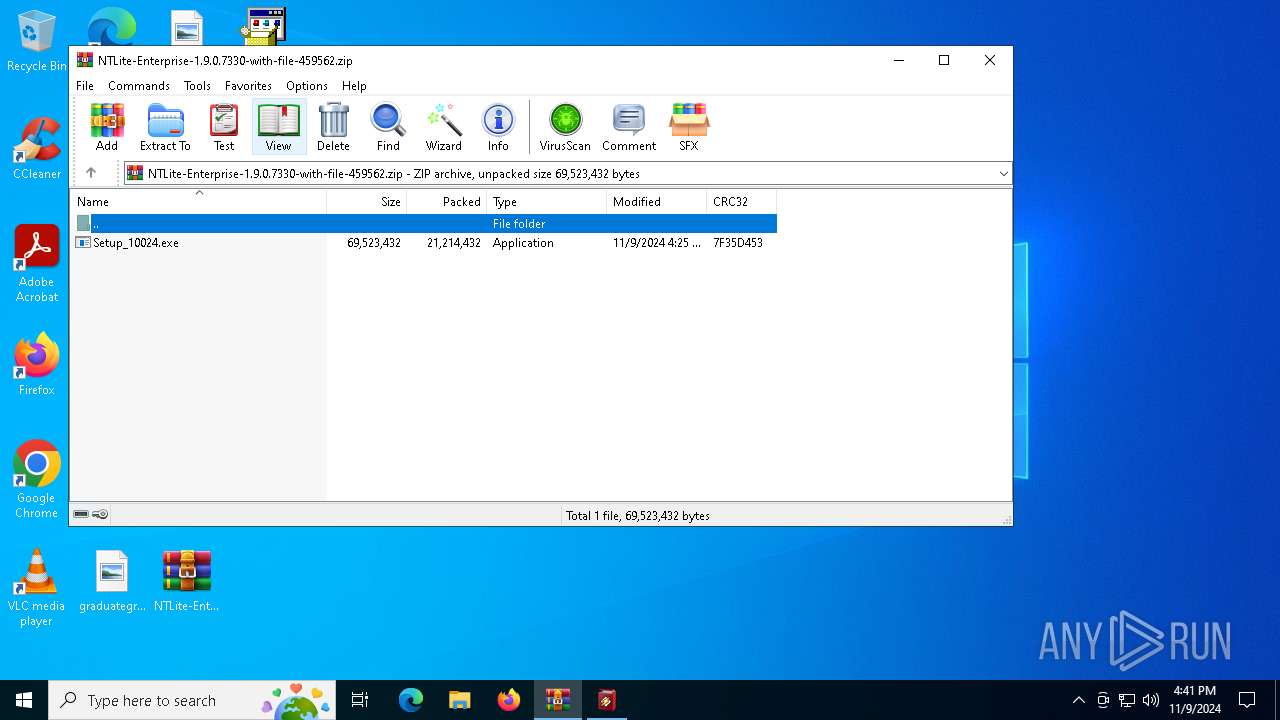
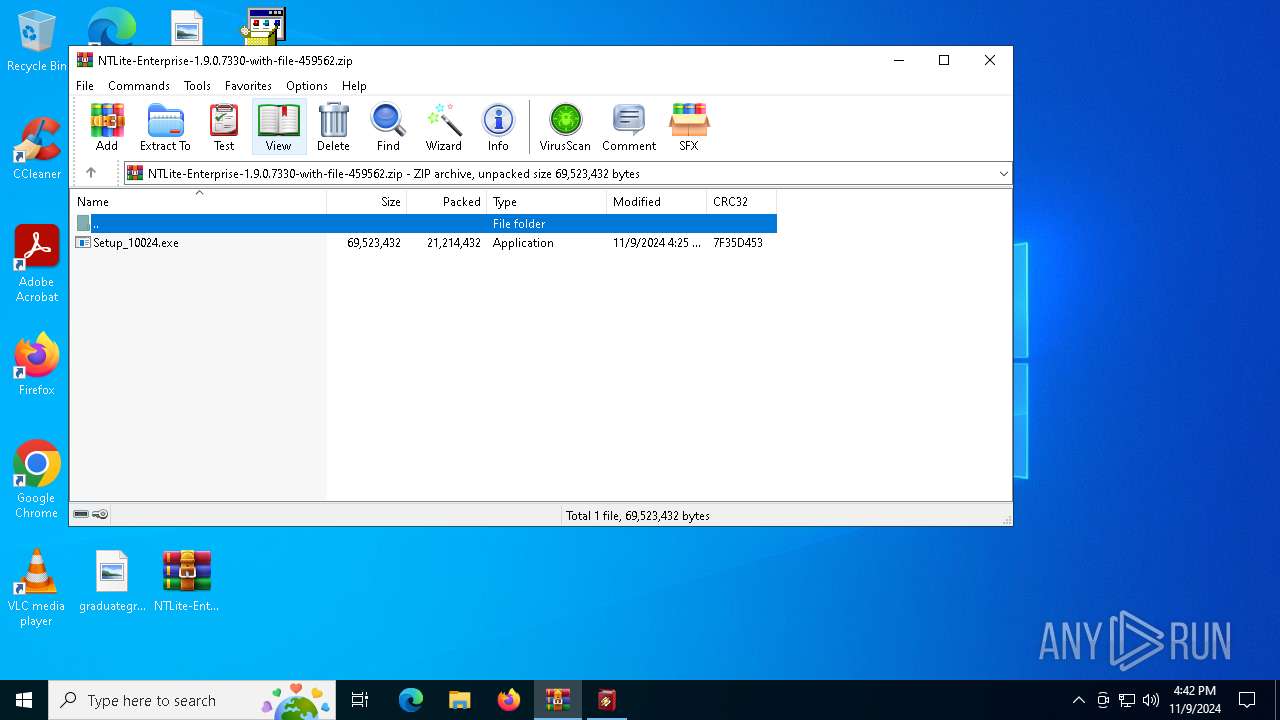
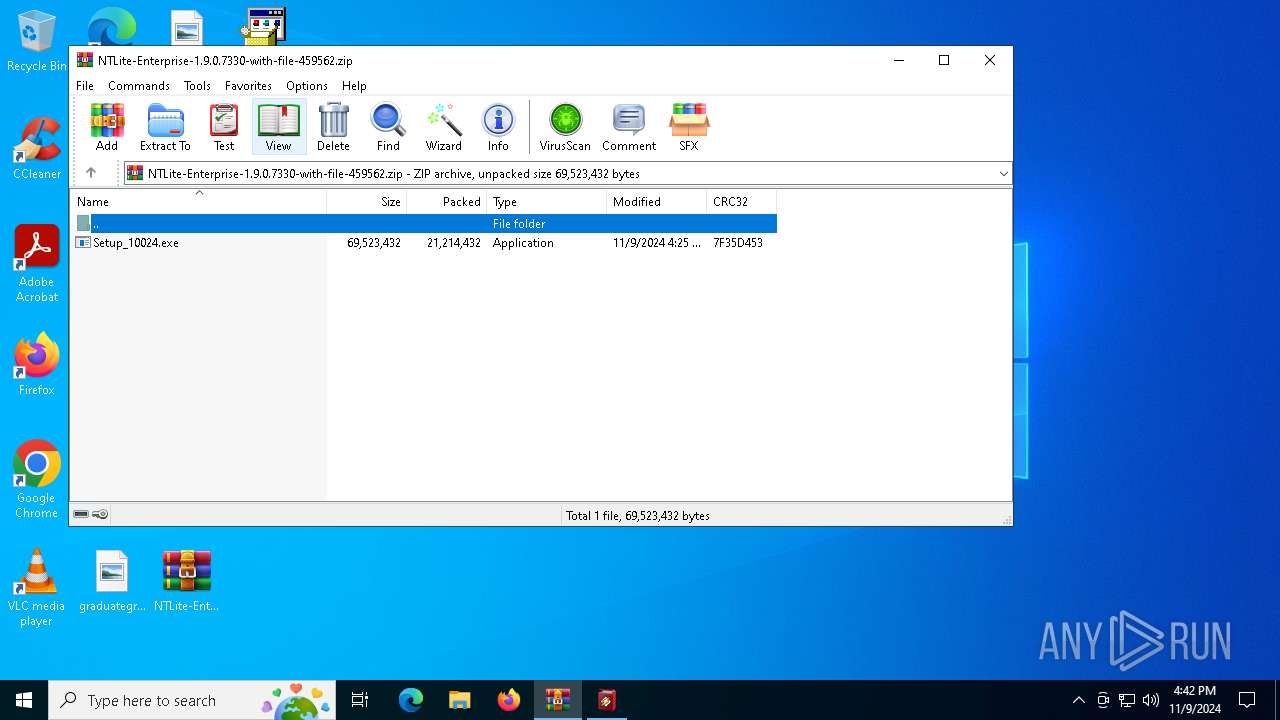
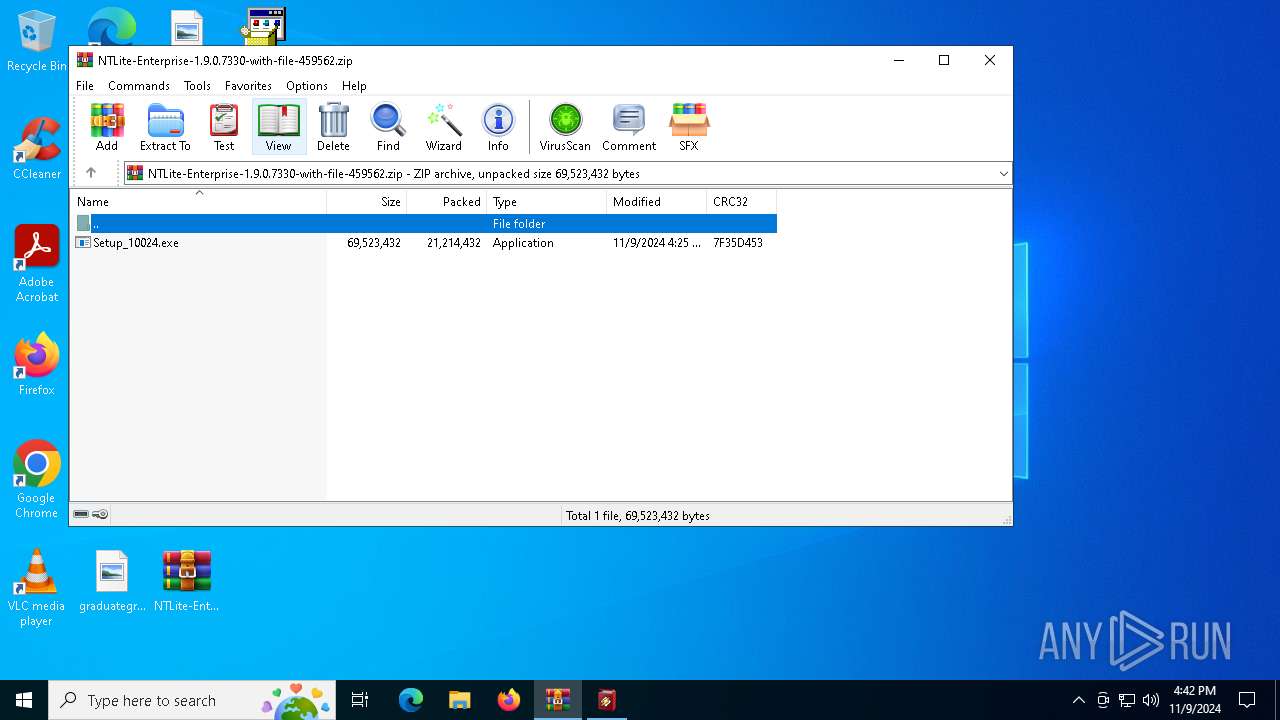
| ZipRequiredVersion: | 789 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Enhanced Deflate using Deflate64(tm) |
| ZipModifyDate: | 2024:11:09 11:25:34 |
| ZipCRC: | 0x7f35d453 |
| ZipCompressedSize: | 21214432 |
| ZipUncompressedSize: | 69523432 |
| ZipFileName: | Setup_10024.exe |
Total processes
126
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1584 | "C:\Users\admin\Desktop\Setup_10024.exe" | C:\Users\admin\Desktop\Setup_10024.exe | explorer.exe | ||||||||||||
User: admin Company: Agreement Tool Tools Integrity Level: MEDIUM Description: 7-zip Agreement Tool Tools Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4032 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\setup.exe | — | Setup_10024.exe | |||||||||||
User: admin Company: Nullsoft, Inc. Integrity Level: MEDIUM Description: Winamp Installer Exit code: 3221226540 Version: 5.6.6.3507 Modules
| |||||||||||||||
| 5892 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\setup.exe | Setup_10024.exe | ||||||||||||
User: admin Company: Nullsoft, Inc. Integrity Level: HIGH Description: Winamp Installer Version: 5.6.6.3507 Modules
| |||||||||||||||
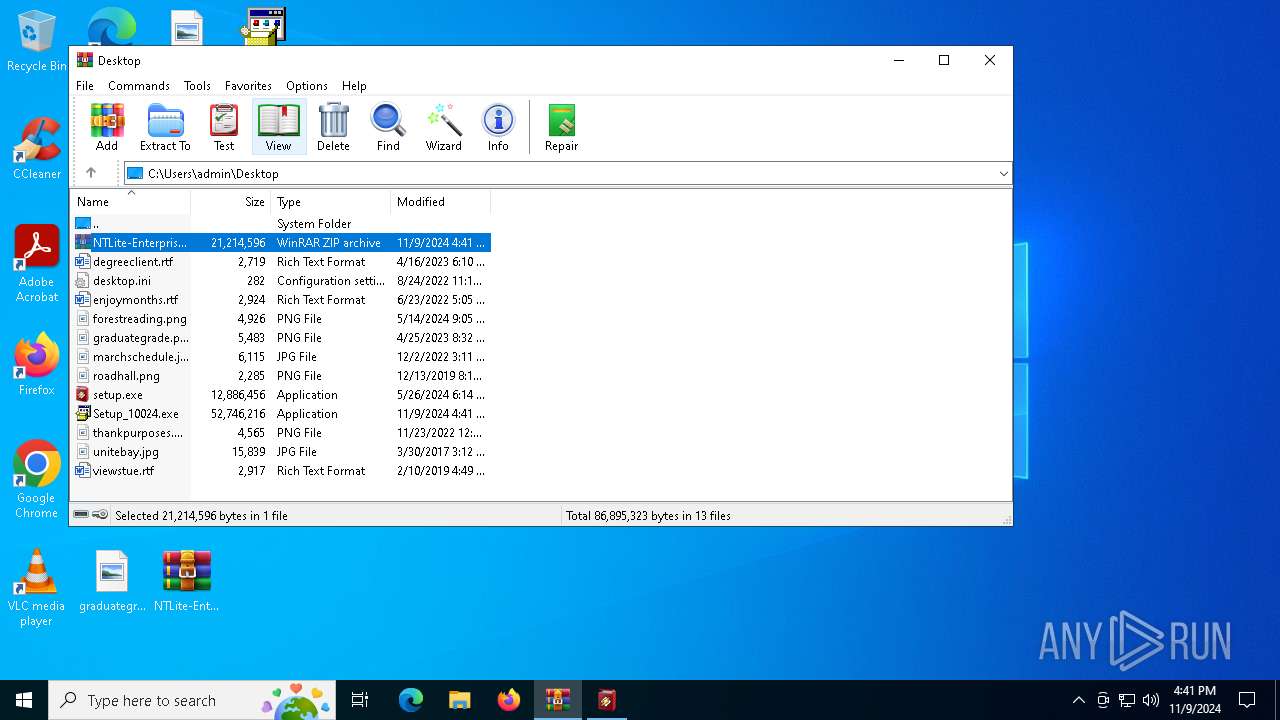
| 6688 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\NTLite-Enterprise-1.9.0.7330-with-file-459562.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 999
Read events
2 904
Write events
95
Delete events
0
Modification events
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\NTLite-Enterprise-1.9.0.7330-with-file-459562.zip | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (6688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1584 | Setup_10024.exe | C:\Users\admin\Desktop\setup.exe | executable | |
MD5:76954D7DBF005D6DB5E38D64F25A8C20 | SHA256:E9E2EB114941F9F9157B4FB139E5588665FB89B709DF82D4A8346AE66CCF03E1 | |||
| 5892 | setup.exe | C:\Users\admin\AppData\Local\Temp\nscBBE.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
| 5892 | setup.exe | C:\Users\admin\AppData\Local\Temp\nscBBE.tmp\LangDLL.dll | executable | |
MD5:A1CD3F159EF78D9ACE162F067B544FD9 | SHA256:47B9E251C9C90F43E3524965AECC07BD53C8E09C5B9F9862B44C306667E2B0B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.43.61.127:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.43.61.127:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.26.12.40:443 | https://businesssetupapp.com/1B518AB85F055085/15389572801/12DAE81DDA8AD3D5/73117048416?452C35B06B6068001731170484 | unknown | text | 32 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7060 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 23.43.61.127:80 | www.microsoft.com | Akamai International B.V. | US | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.43.61.127:80 | www.microsoft.com | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
businesssetupapp.com |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report