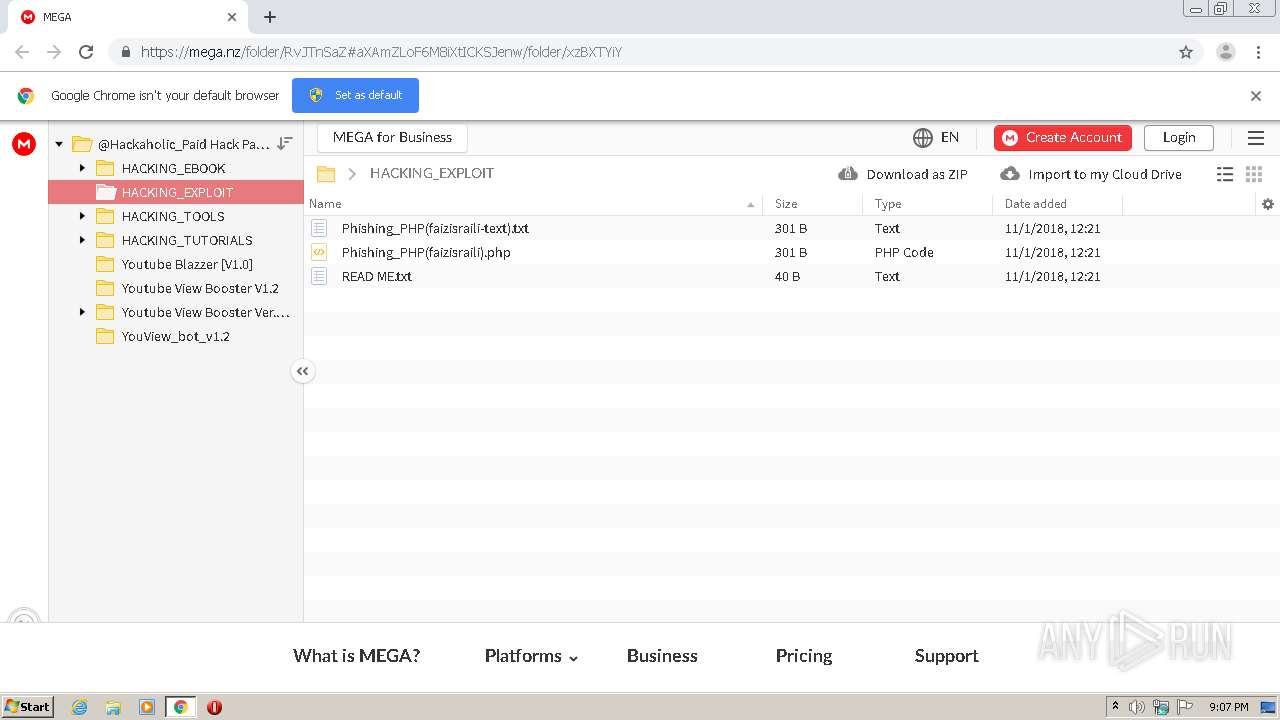
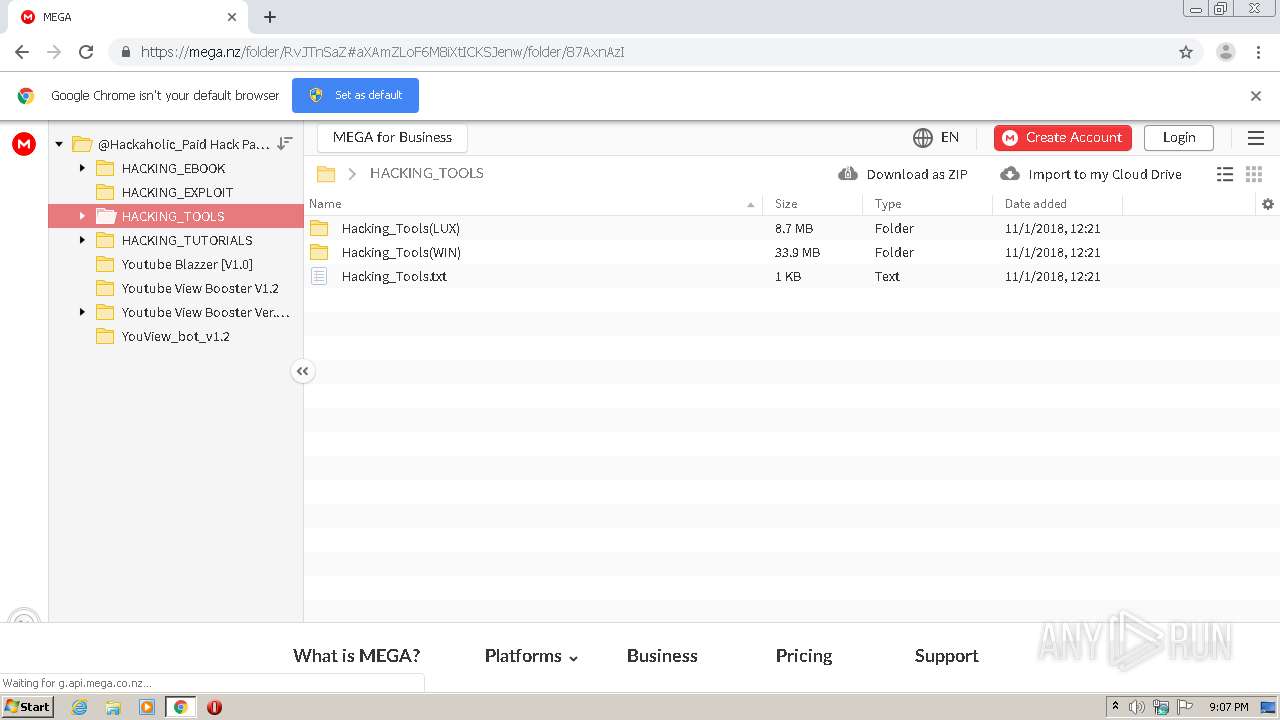
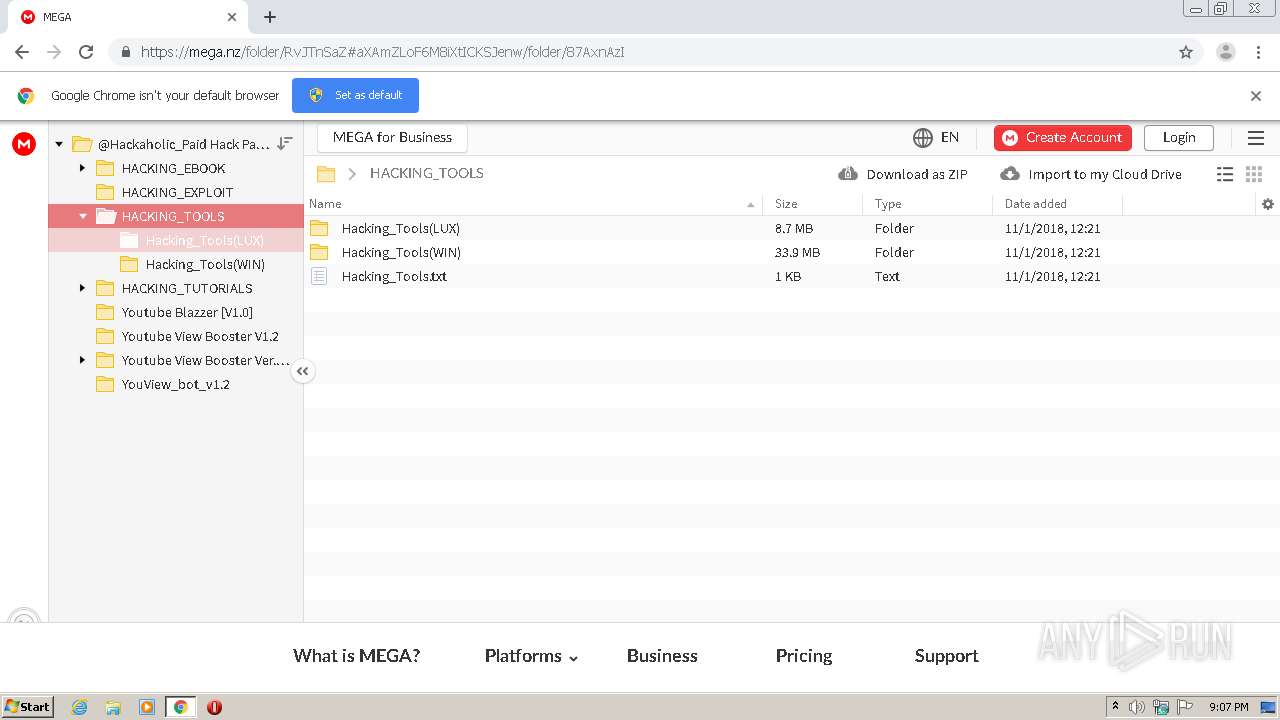
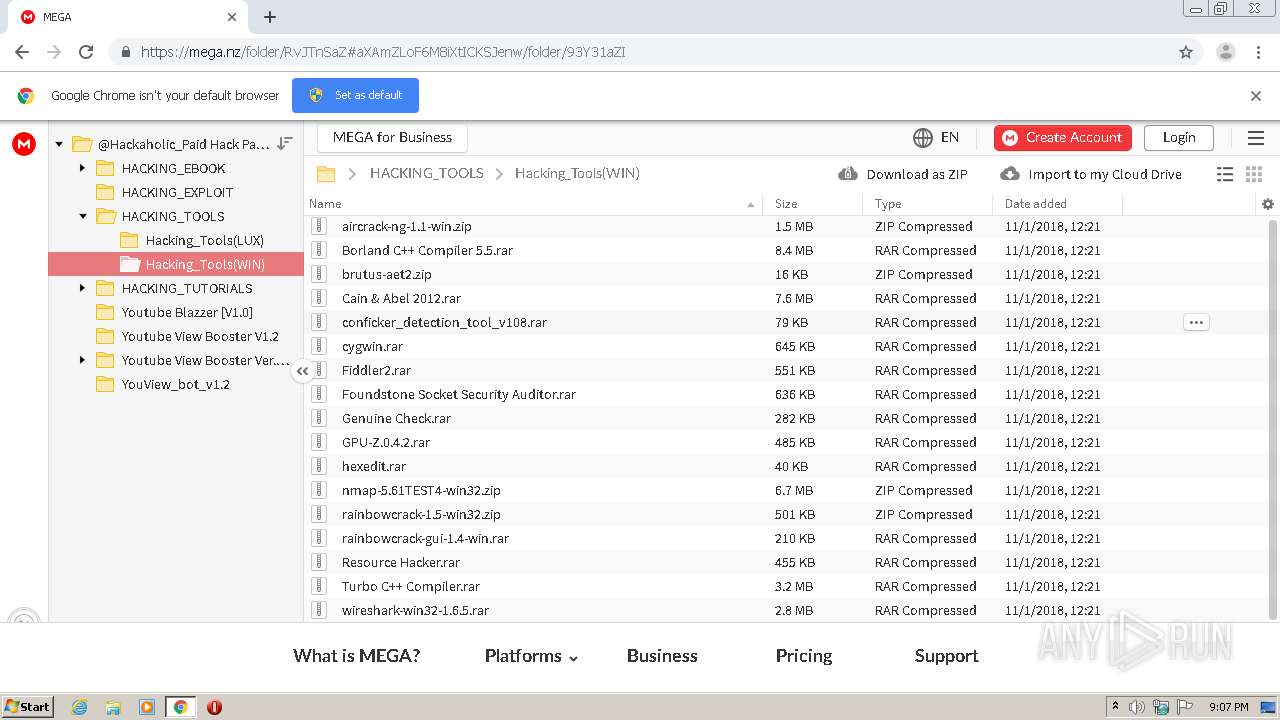
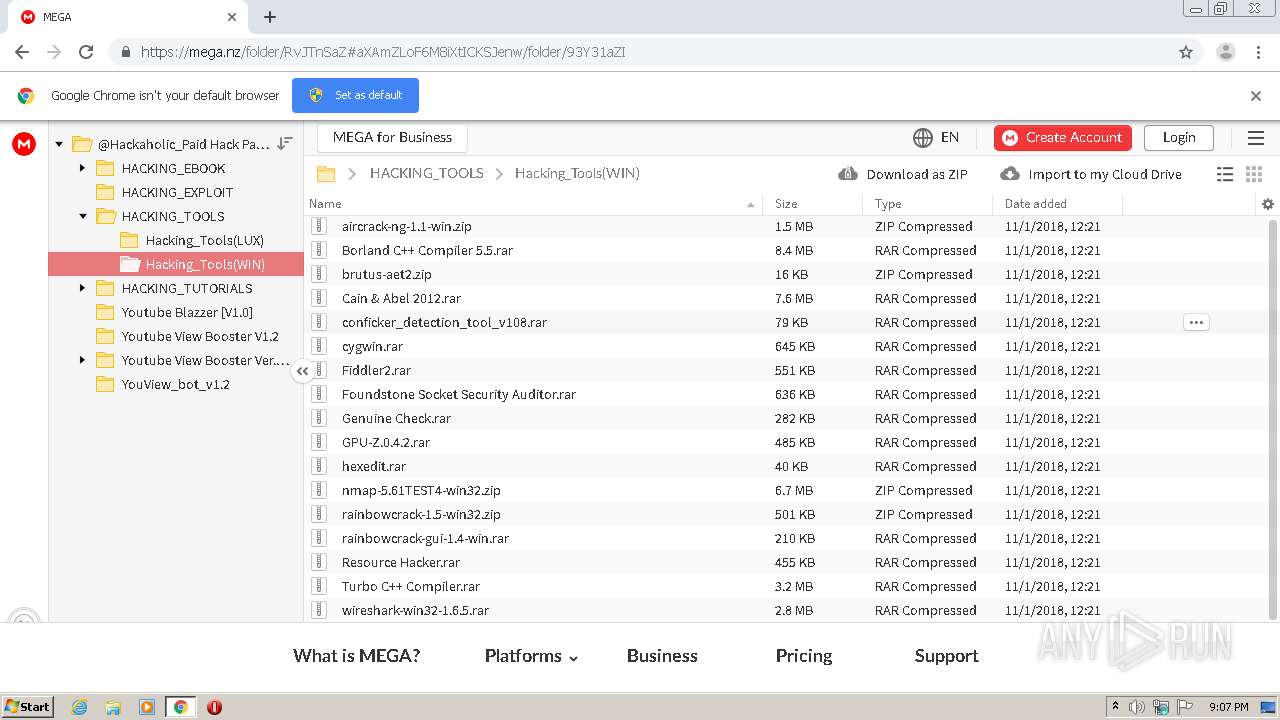
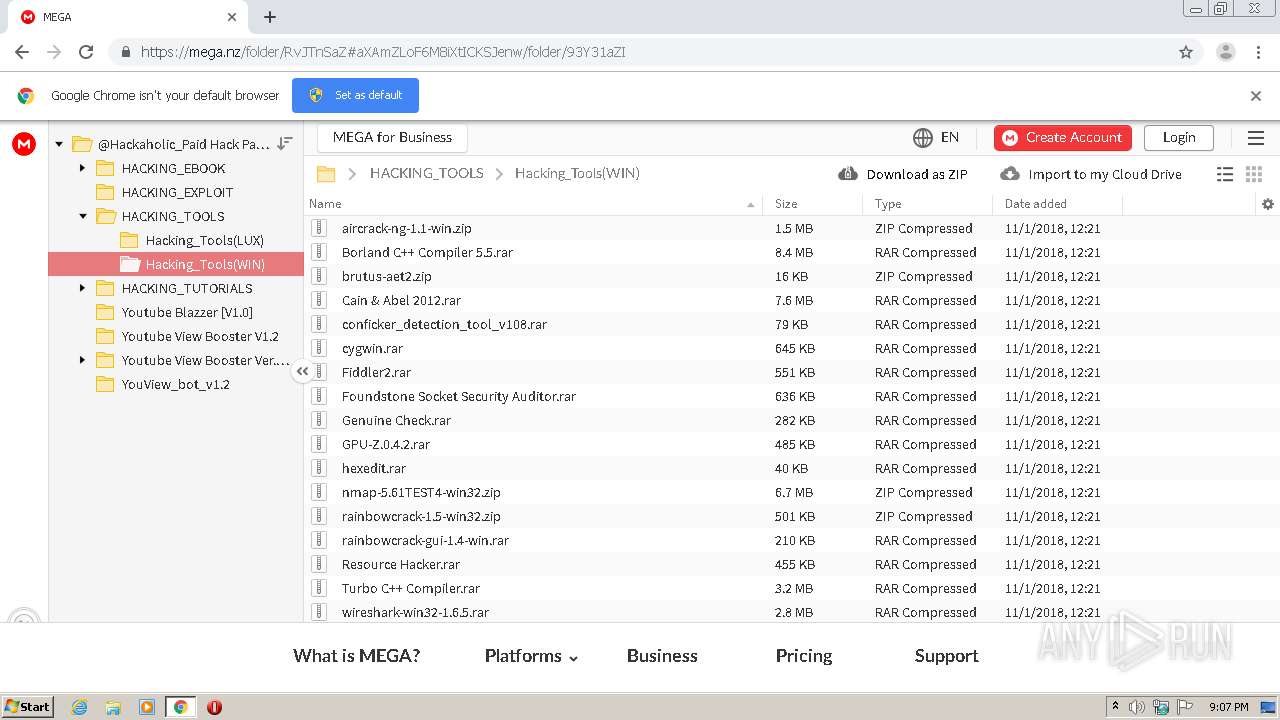
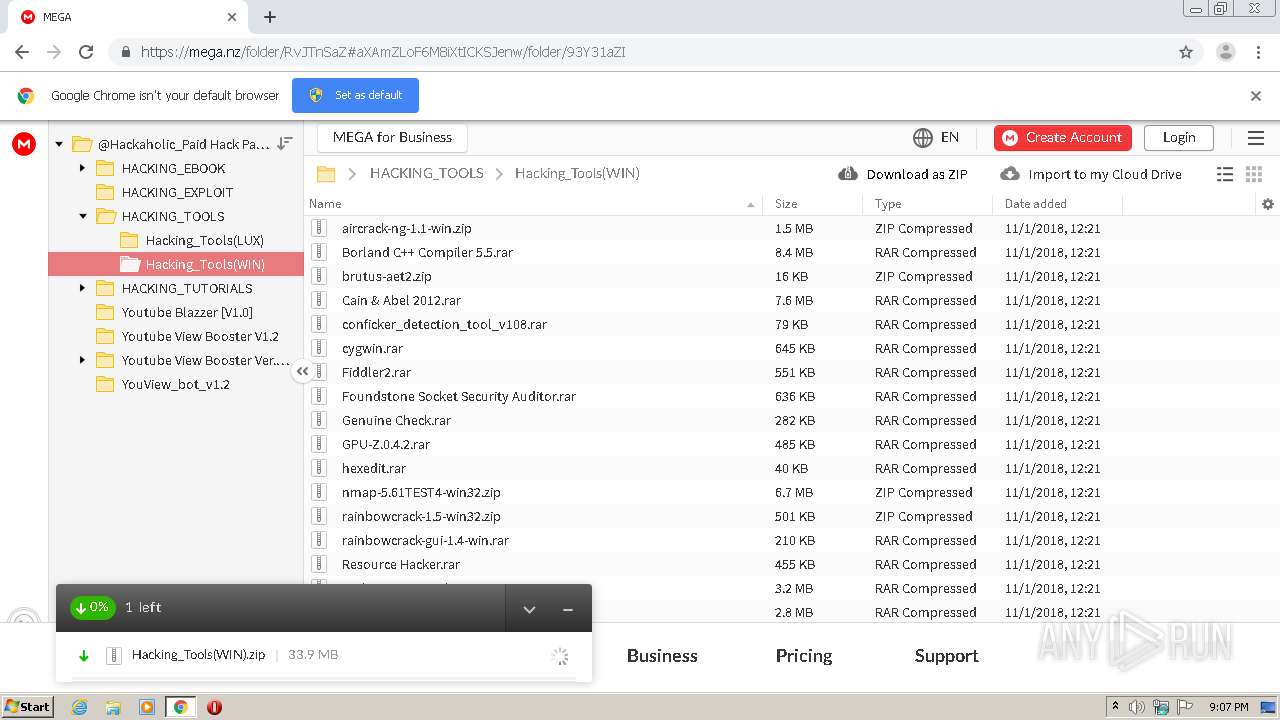
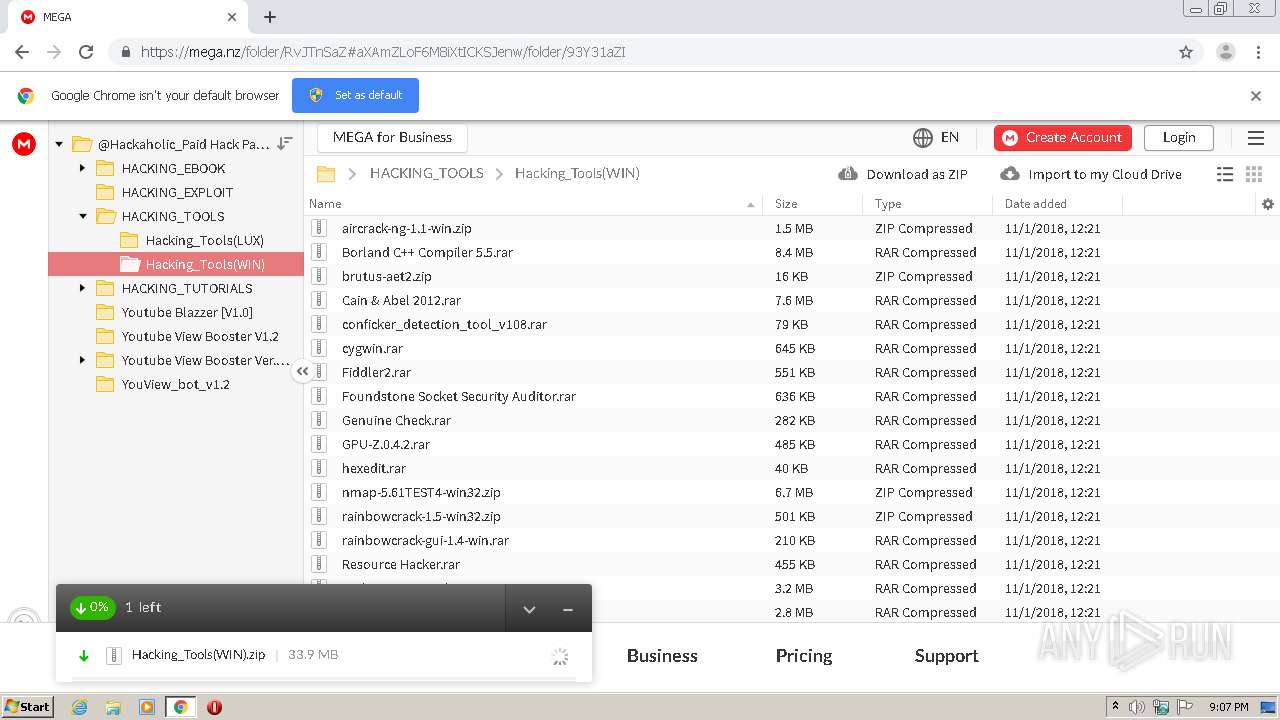
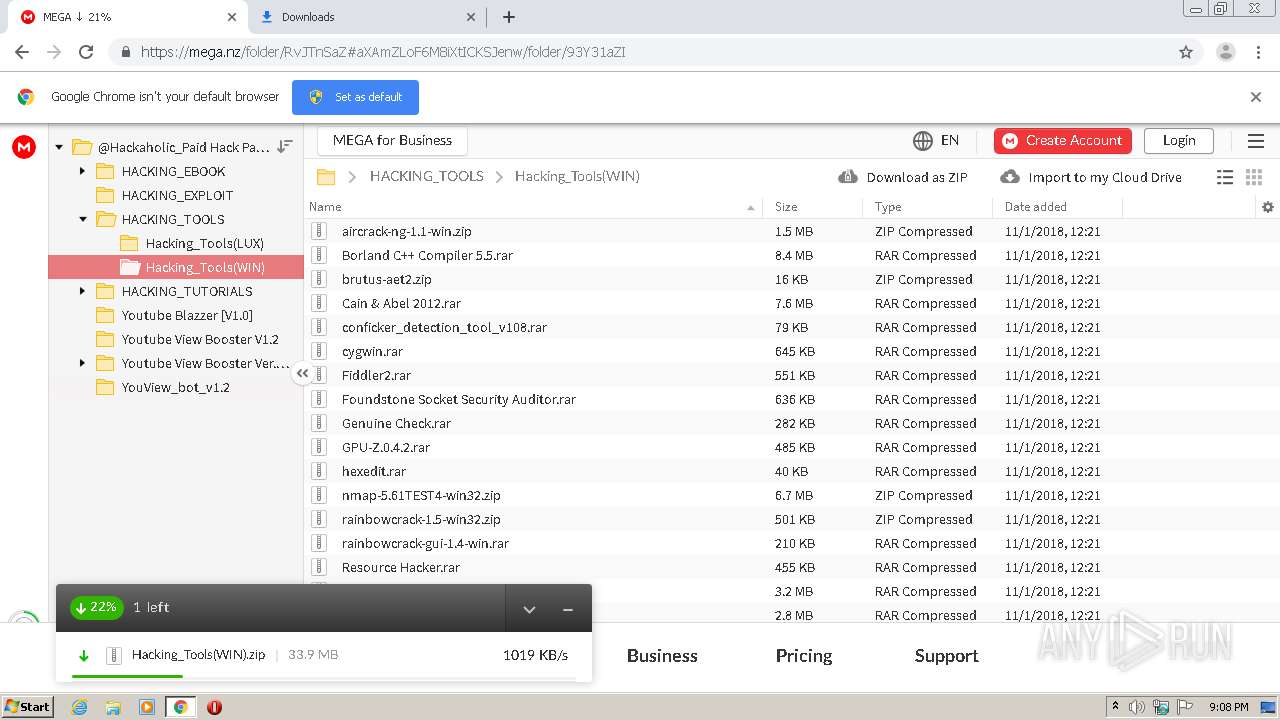
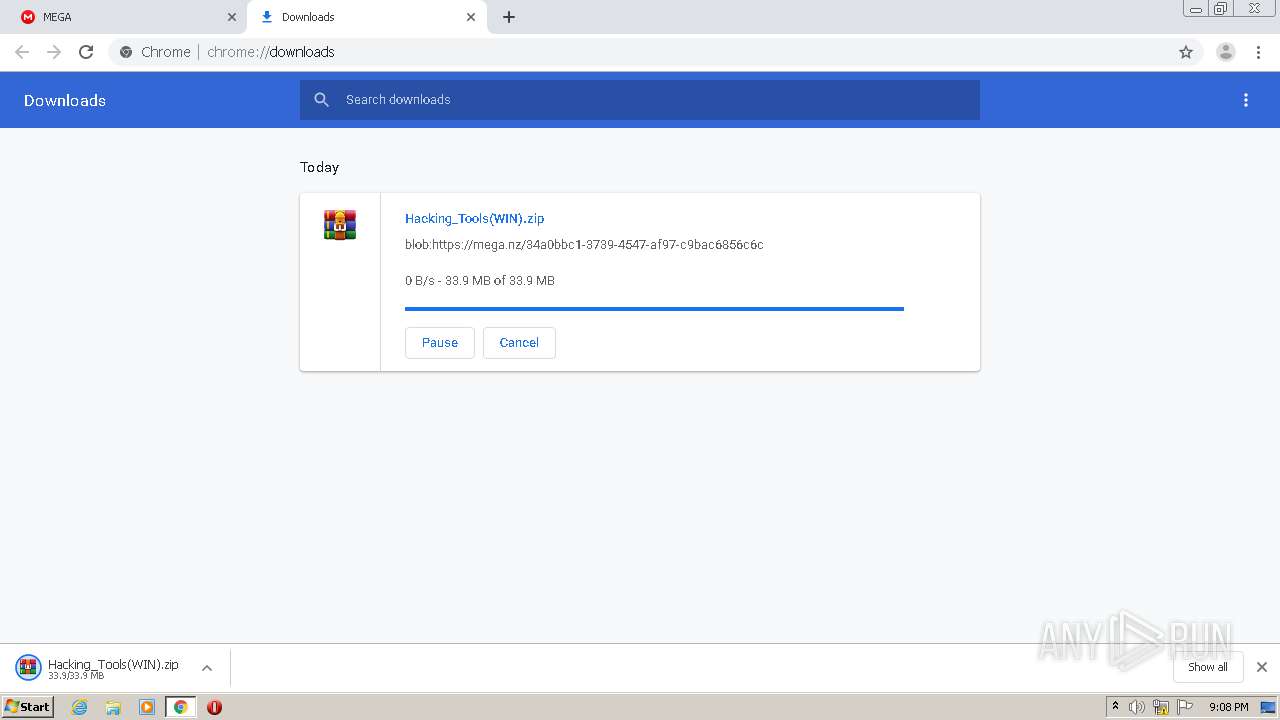
| URL: | https://mega.nz/folder/RvJTnSaZ#aXAmZLoF6M8iXtICKSJenw/folder/xzBXTYiY |
| Full analysis: | https://app.any.run/tasks/ce66c2a8-015f-4682-8406-d05e1d143717 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2020, 20:07:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 851697CF2EDDC4BEA3B4AF8E3C28767B |
| SHA1: | 61ACE5F93990C3D62432CE60EE1CA042636F0CBF |
| SHA256: | C7F7669F05331C884BD6B2611FB9AD74F6ED649709B1ECC9AAC55F340888C2CF |
| SSDEEP: | 3:N8X/iuyKp2Bqhv5O2XKlT+n:26O2ctNXW+ |
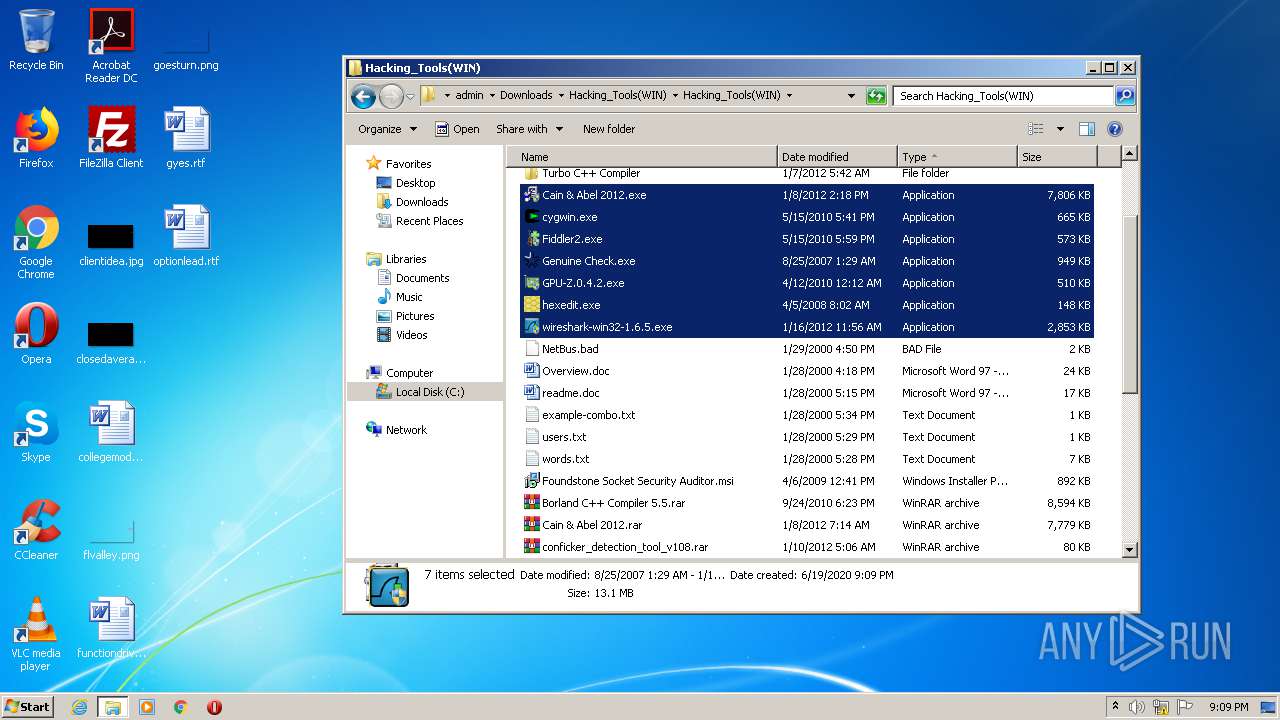
MALICIOUS
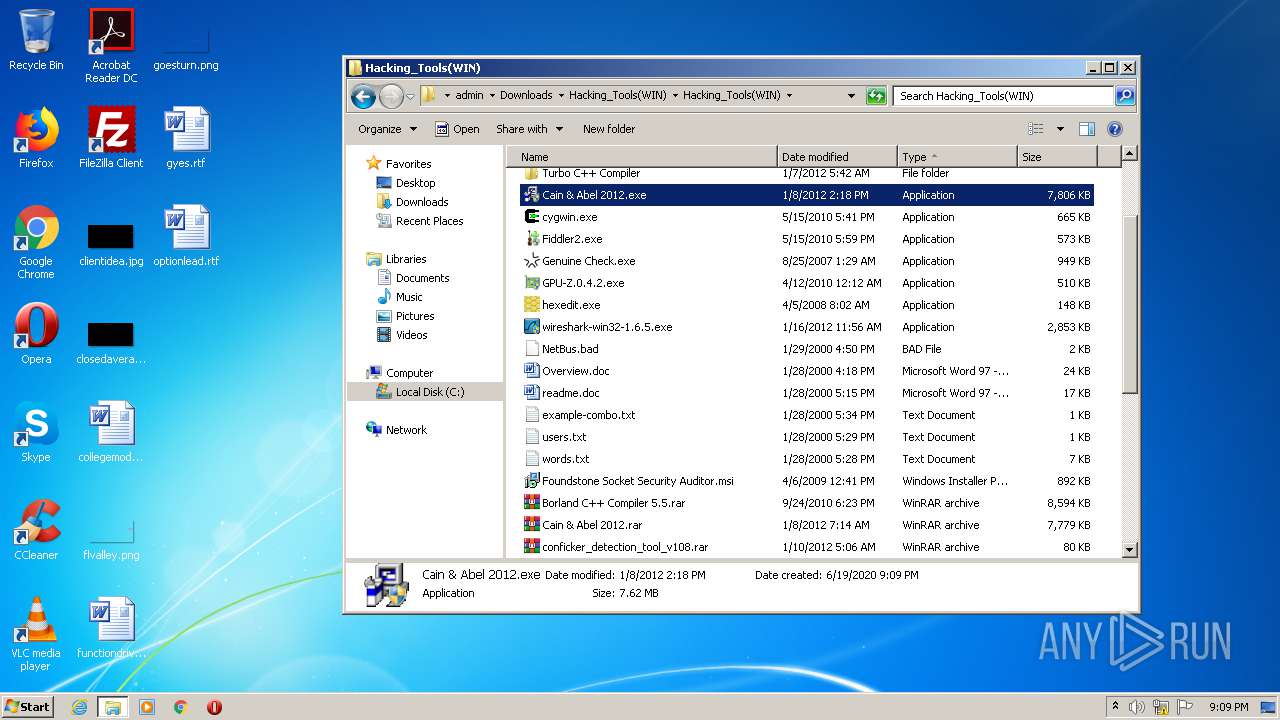
Application was dropped or rewritten from another process
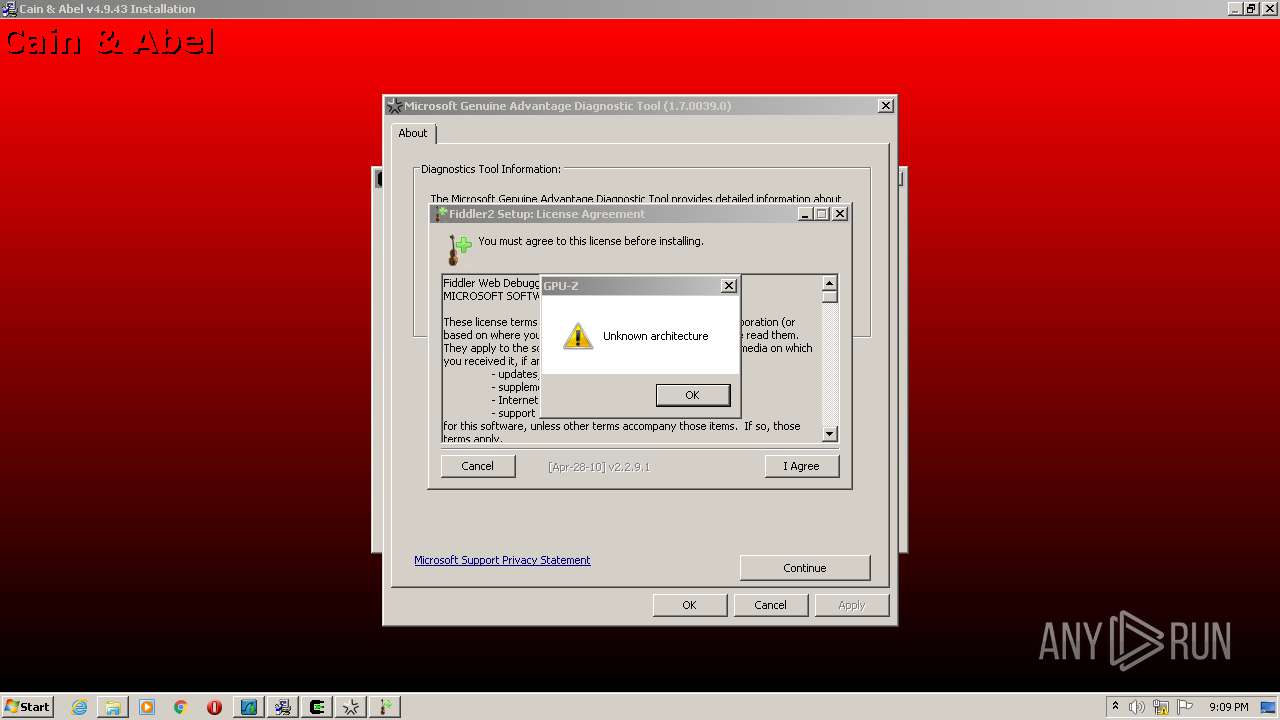
- Cain & Abel 2012.exe (PID: 3704)
- Cain & Abel 2012.exe (PID: 2844)
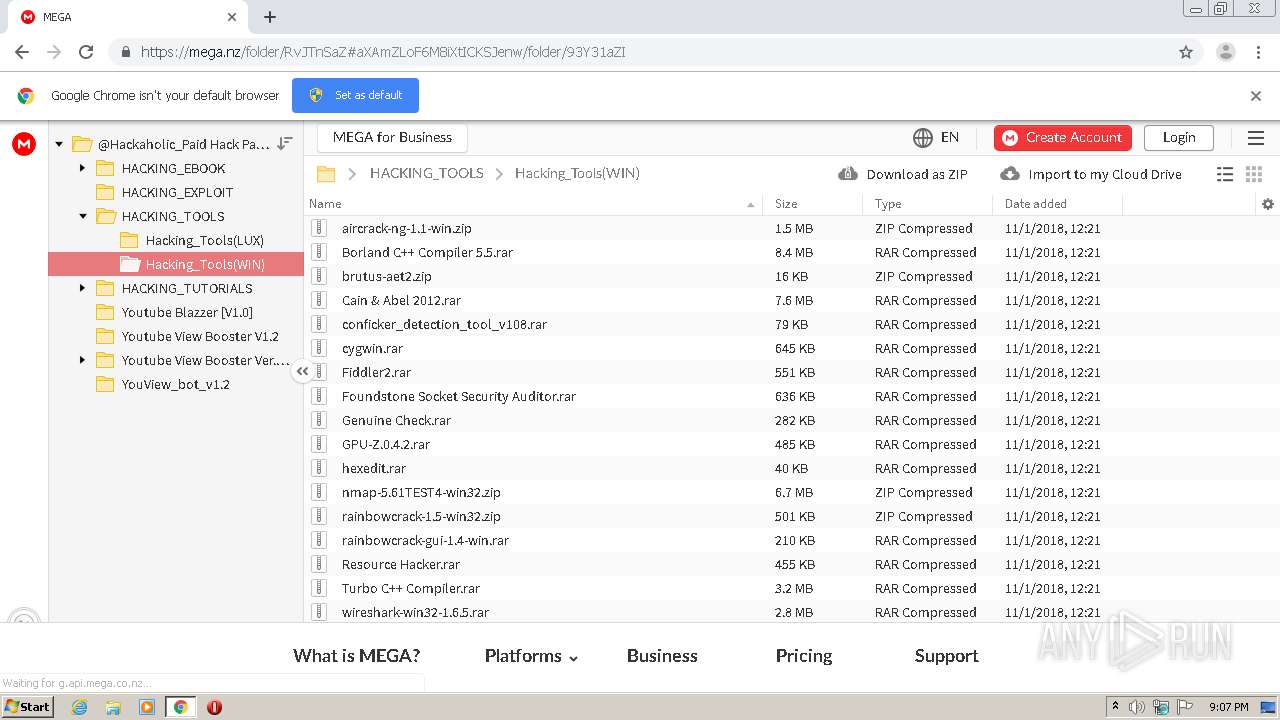
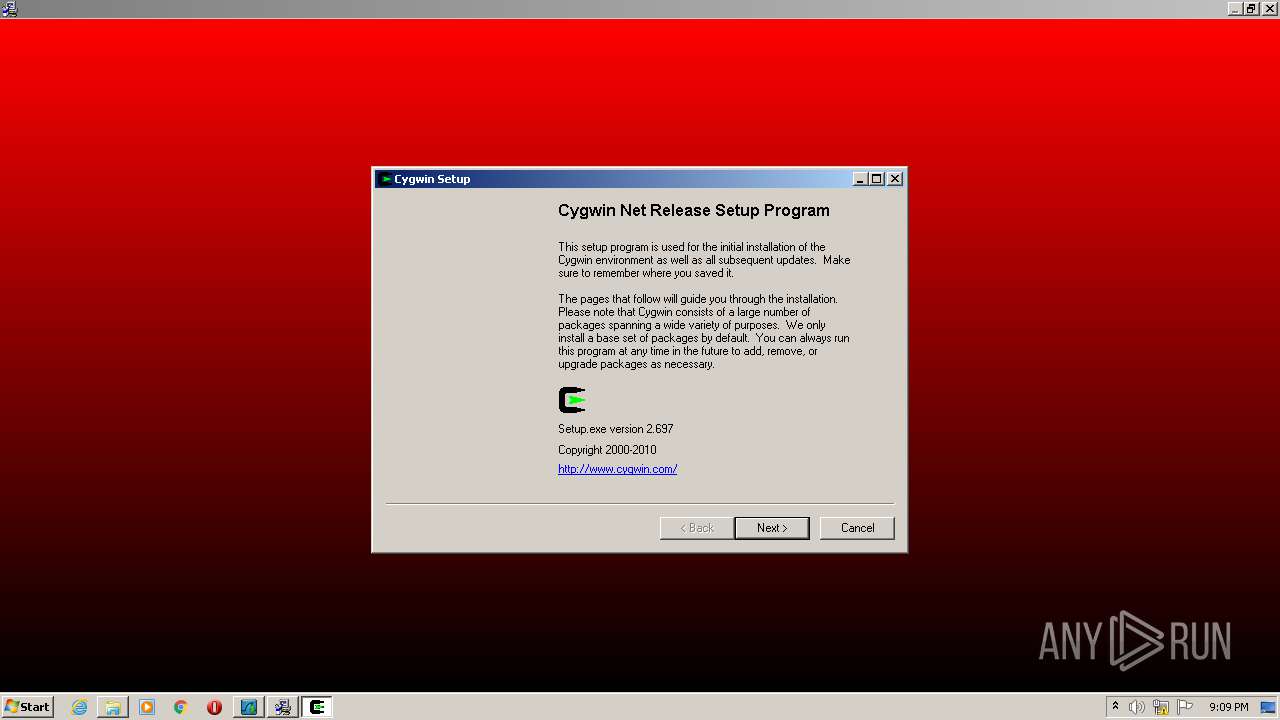
- cygwin.exe (PID: 1908)
- wireshark-win32-1.6.5.exe (PID: 3892)
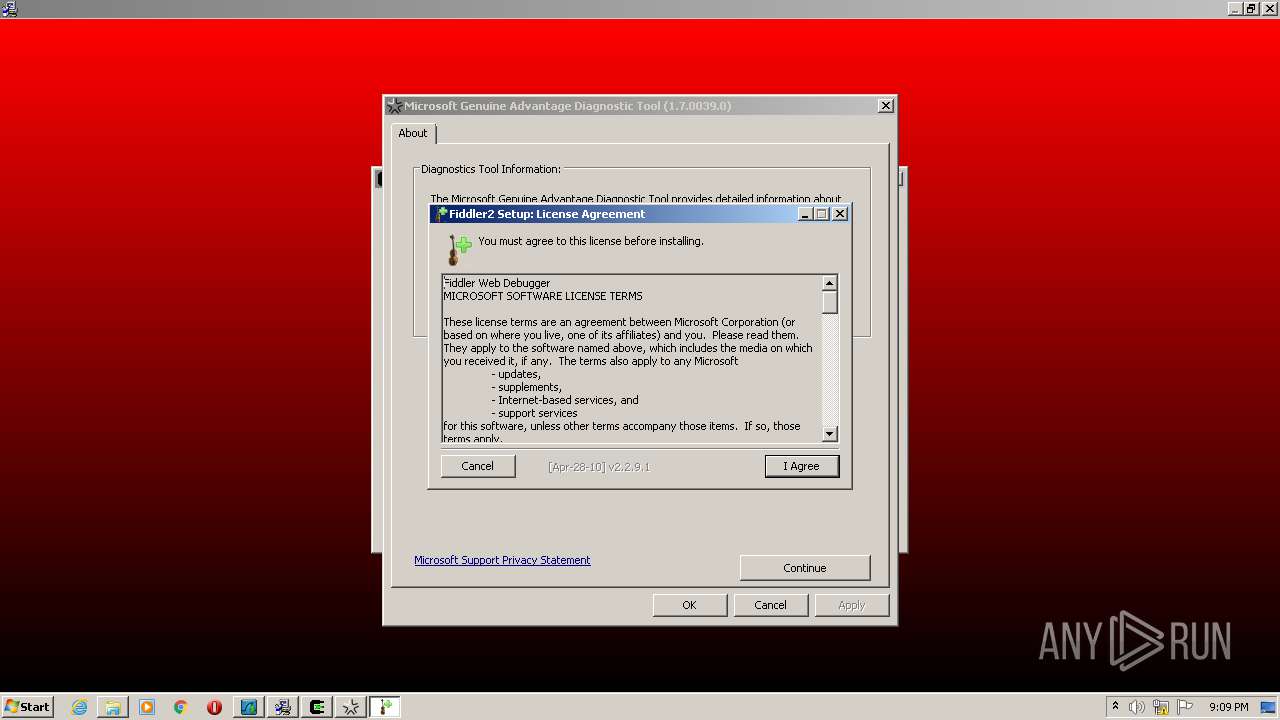
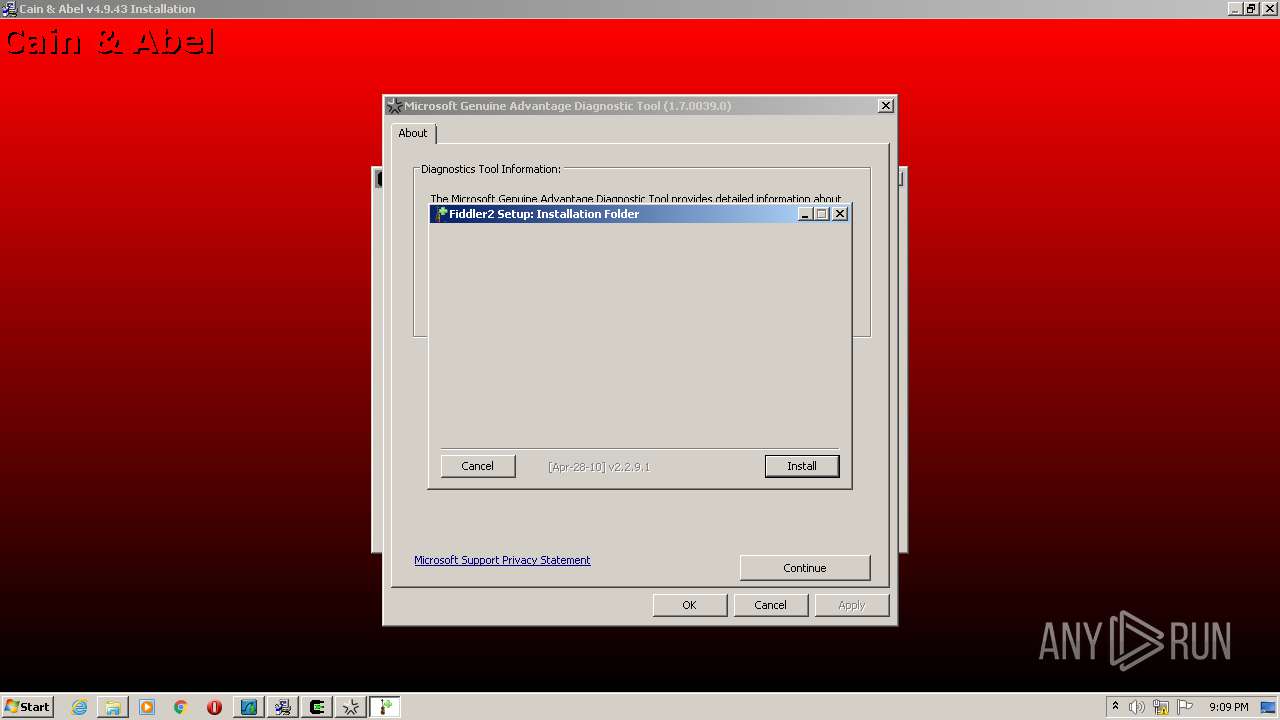
- Fiddler2.exe (PID: 3304)
- wireshark-win32-1.6.5.exe (PID: 3064)
- Genuine Check.exe (PID: 2204)
- GPU-Z.0.4.2.exe (PID: 3140)
- hexedit.exe (PID: 2780)
- GPU-Z.0.4.2.exe (PID: 2280)
- Fiddler2.exe (PID: 3436)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3300)
SUSPICIOUS
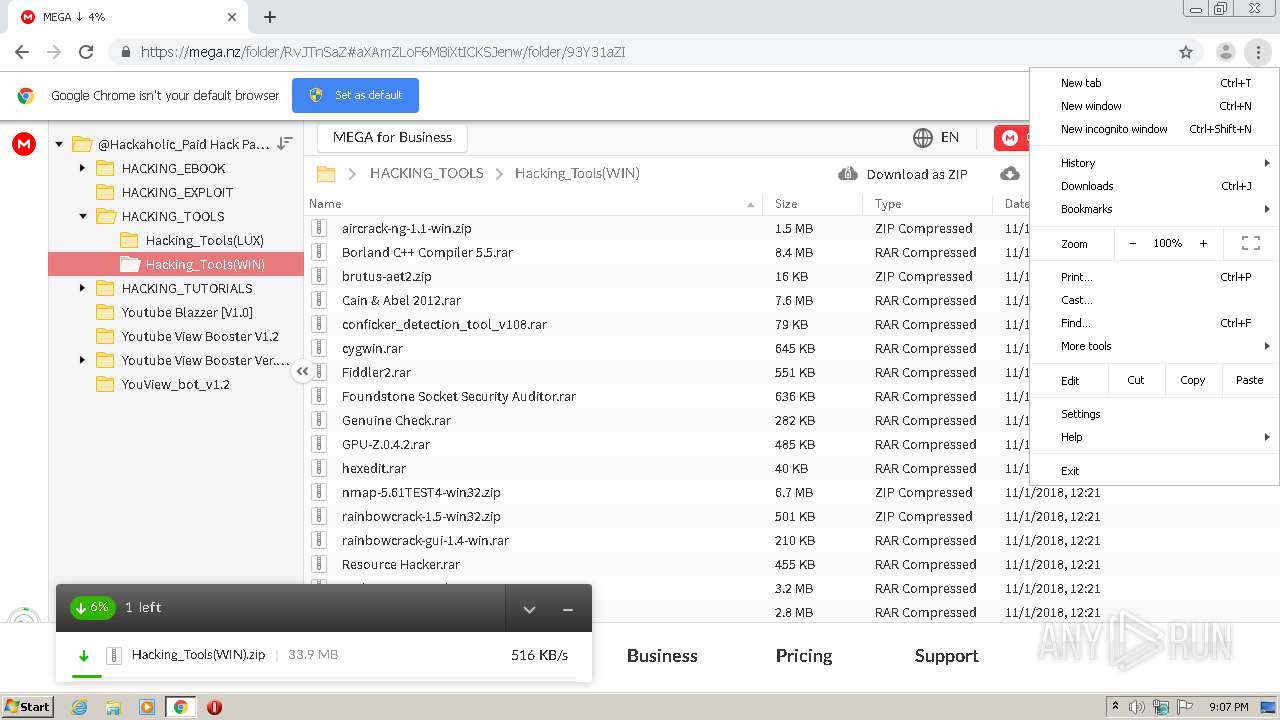
Modifies files in Chrome extension folder
- chrome.exe (PID: 1856)
Executable content was dropped or overwritten
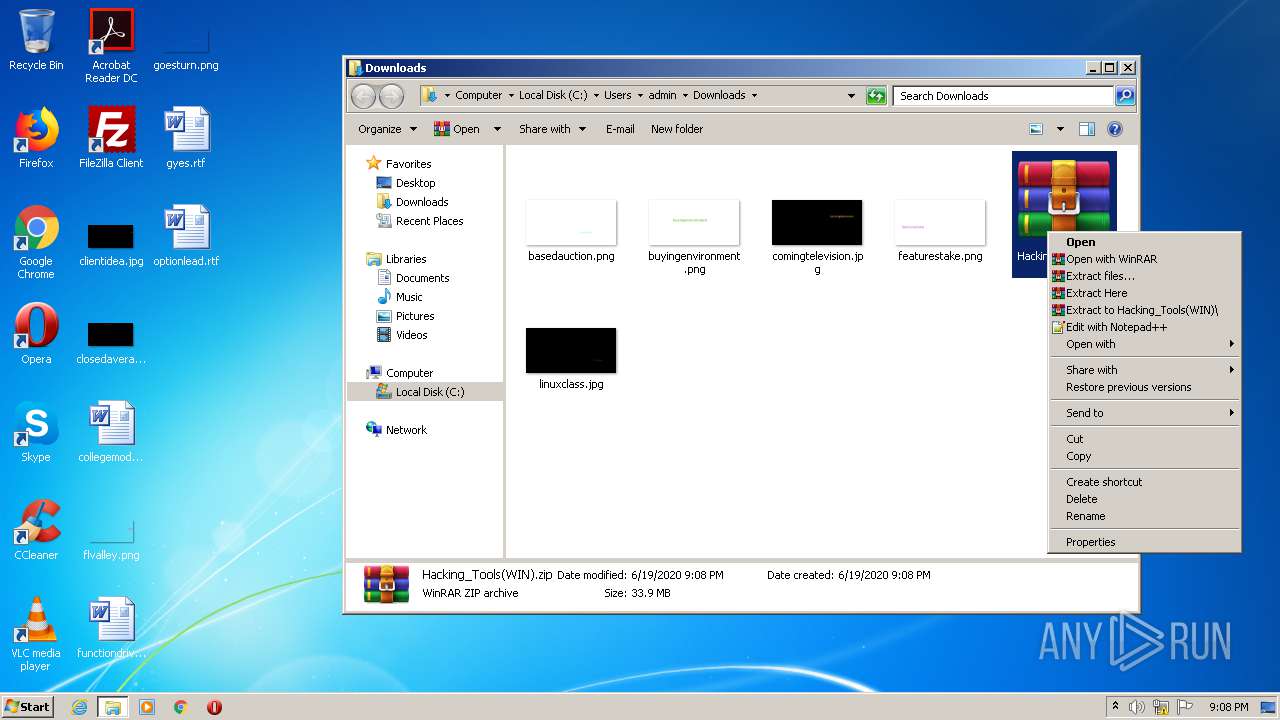
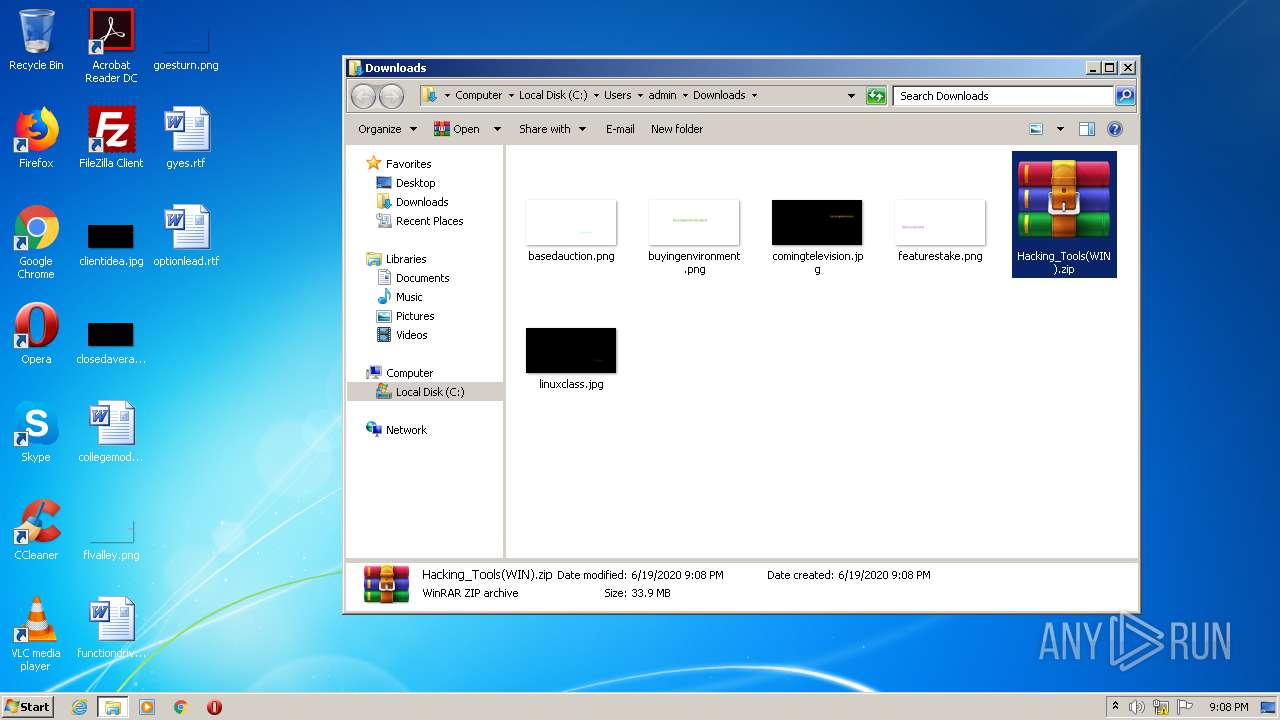
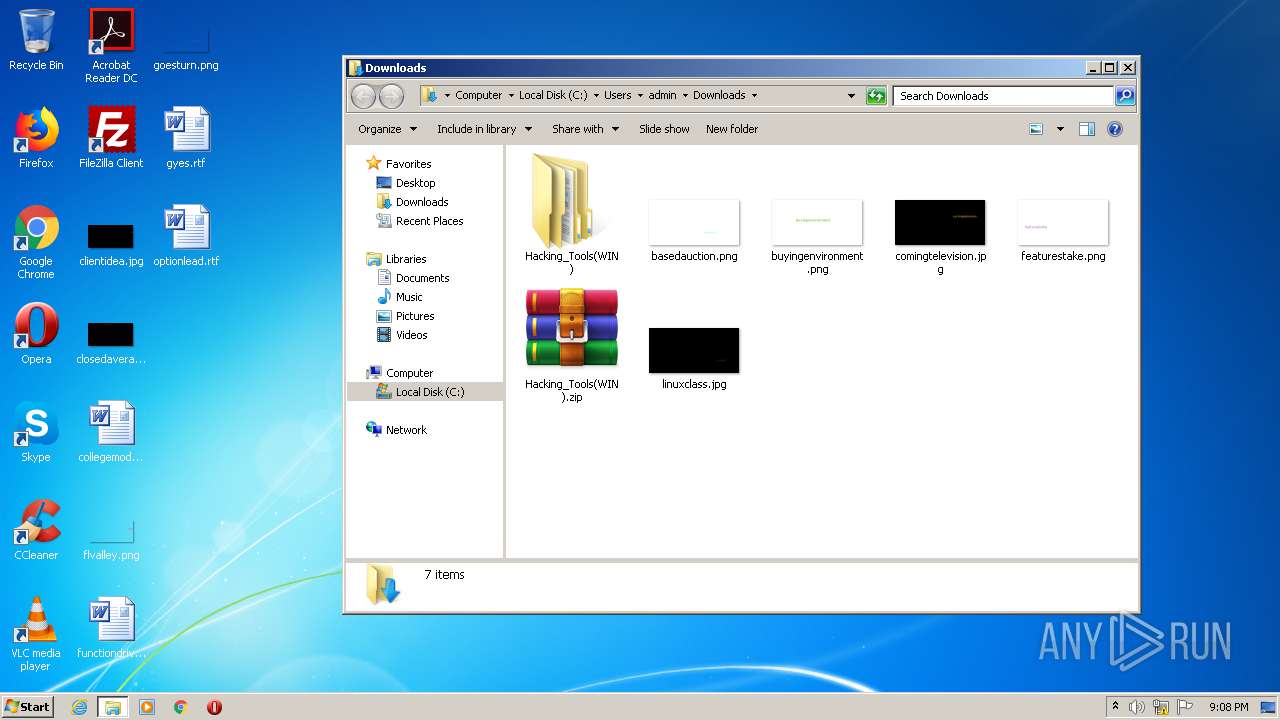
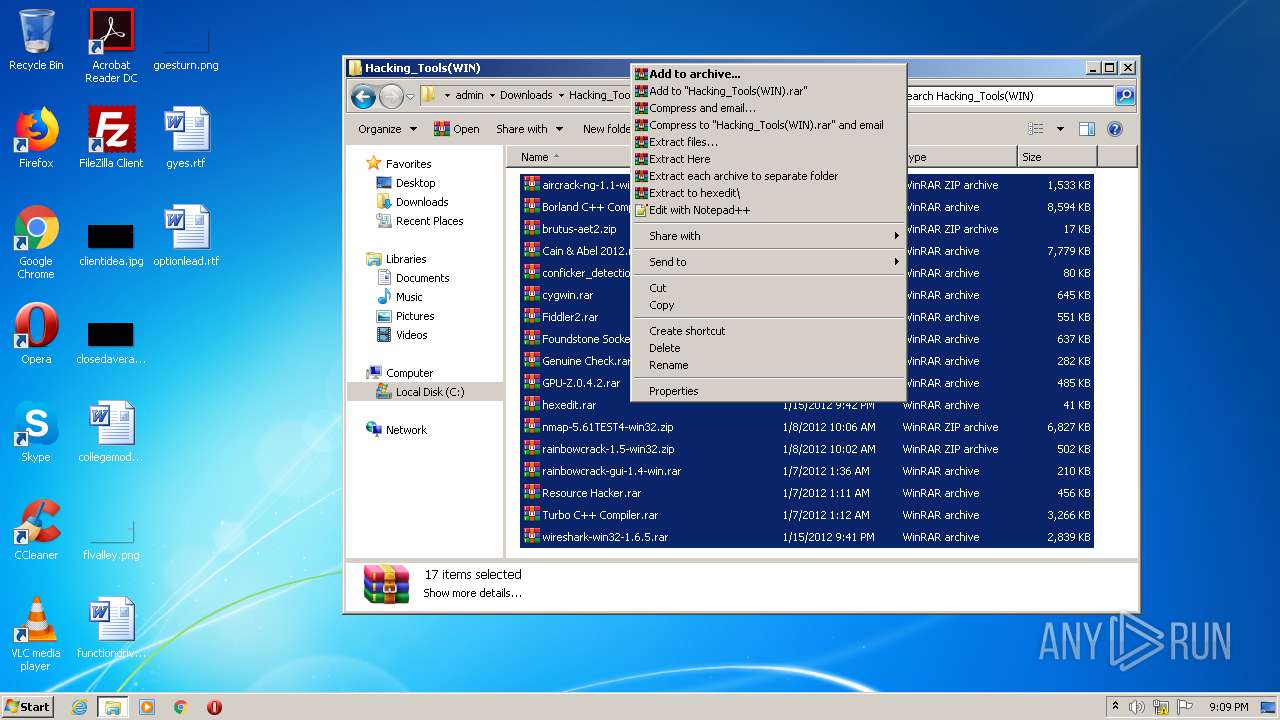
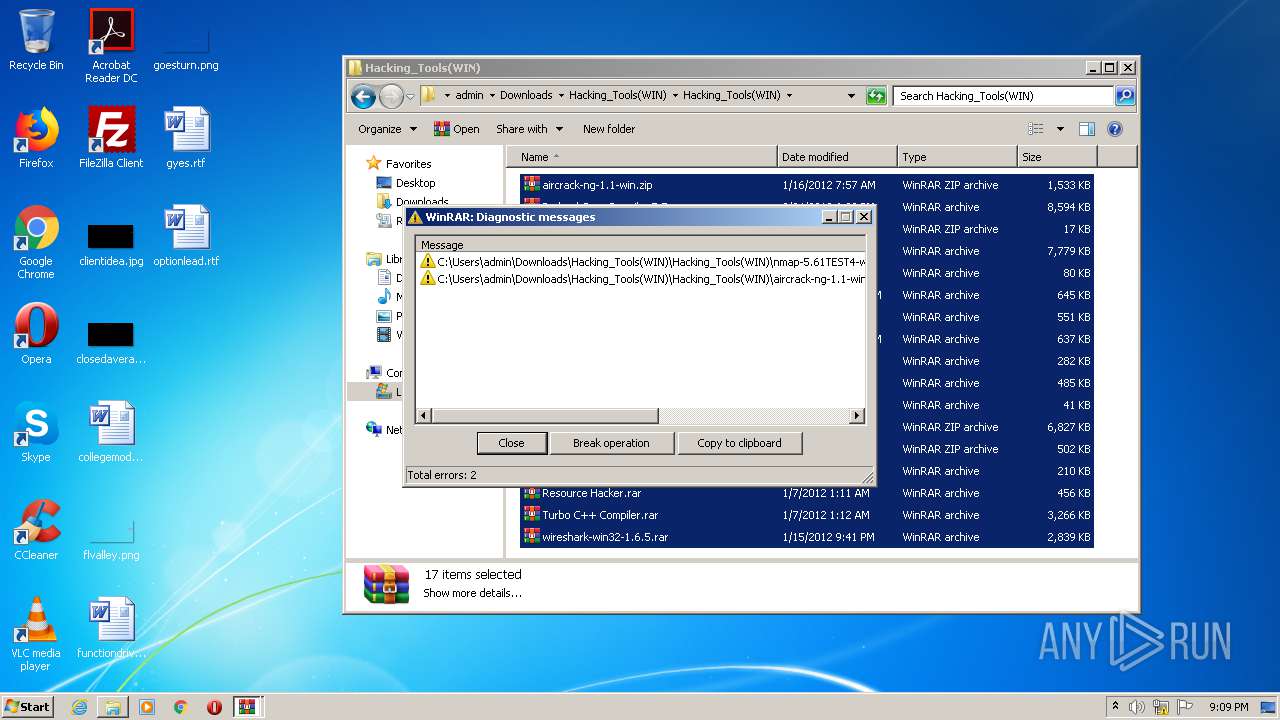
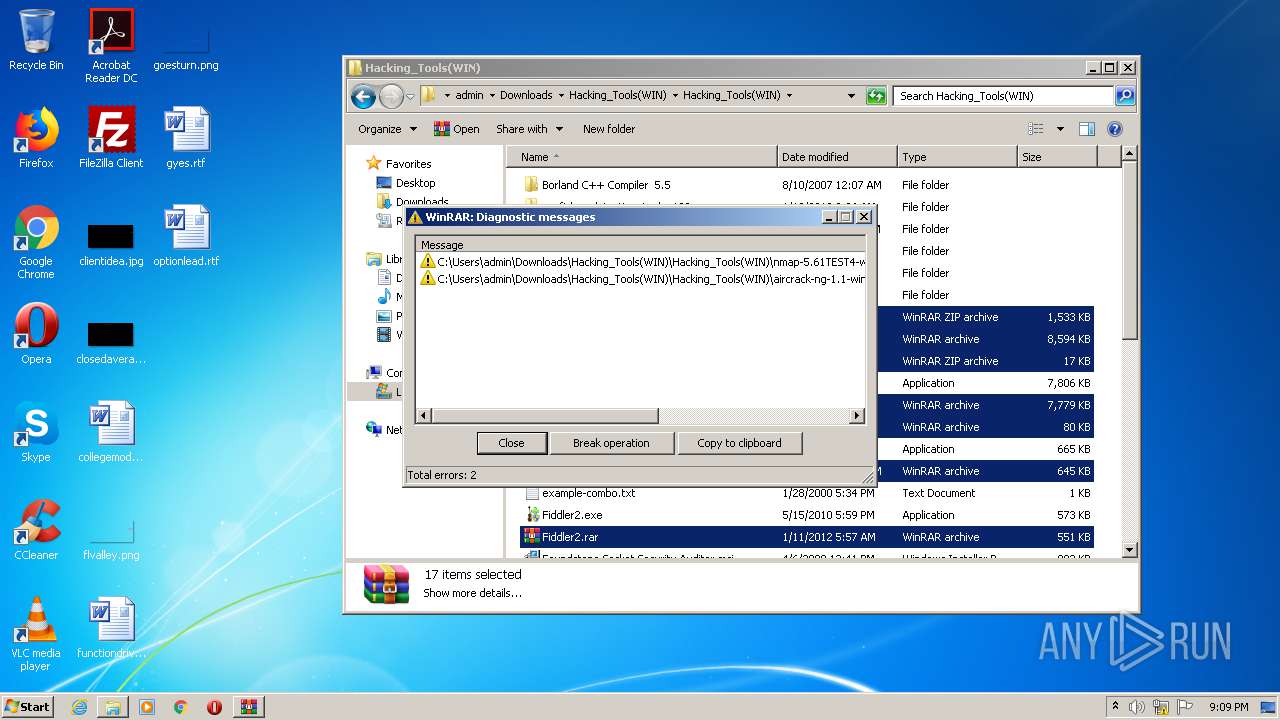
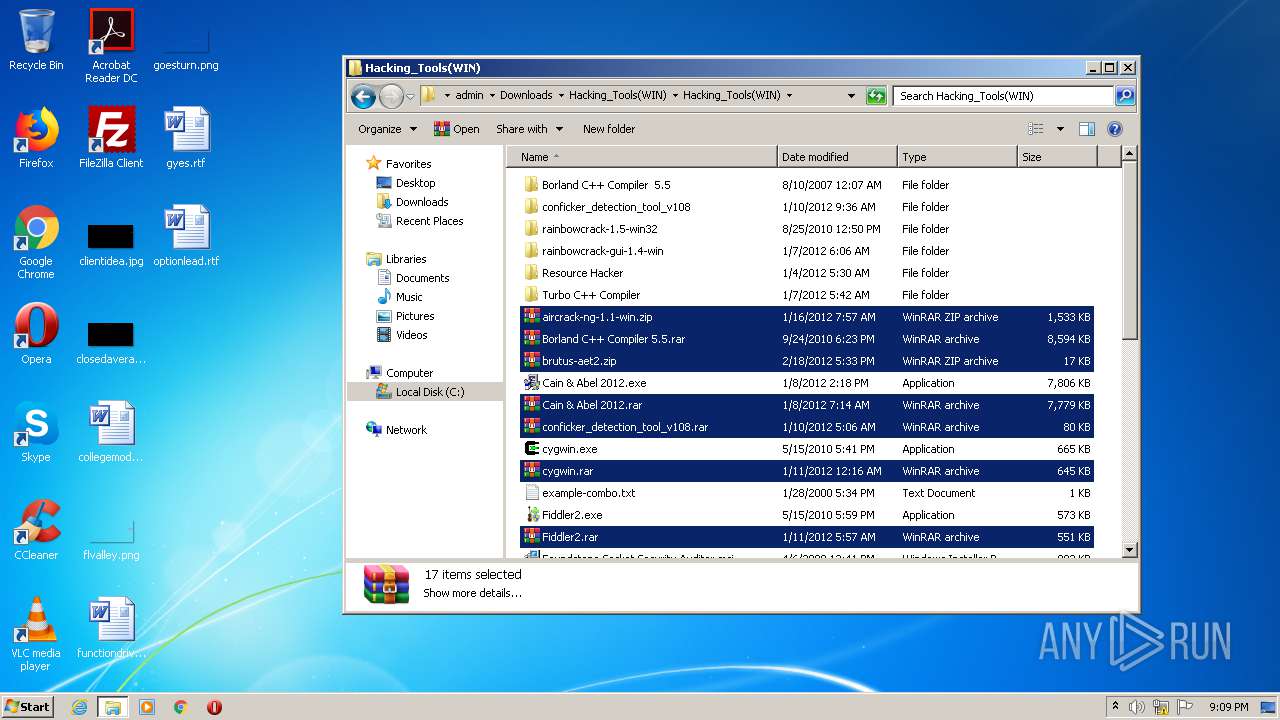
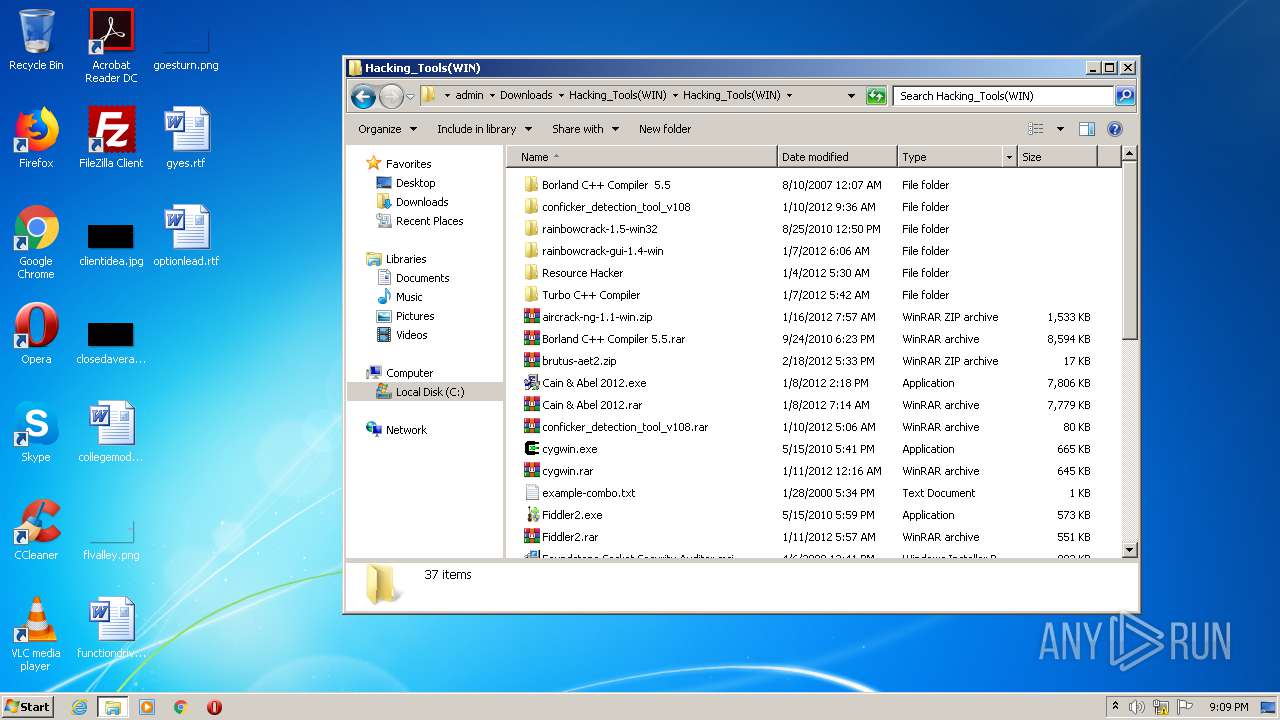
- WinRAR.exe (PID: 4020)
- Cain & Abel 2012.exe (PID: 3704)
Creates files in the Windows directory
- Cain & Abel 2012.exe (PID: 3704)
Removes files from Windows directory
- Cain & Abel 2012.exe (PID: 3704)
INFO
Application launched itself
- chrome.exe (PID: 1856)
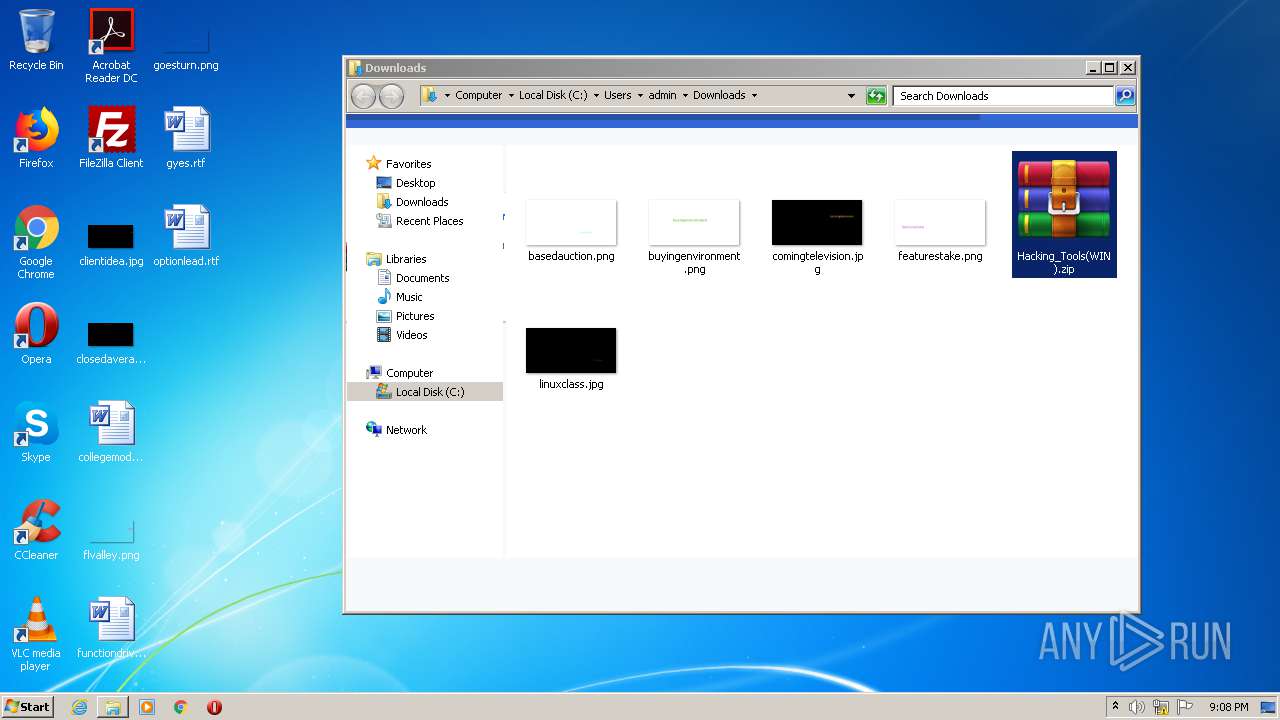
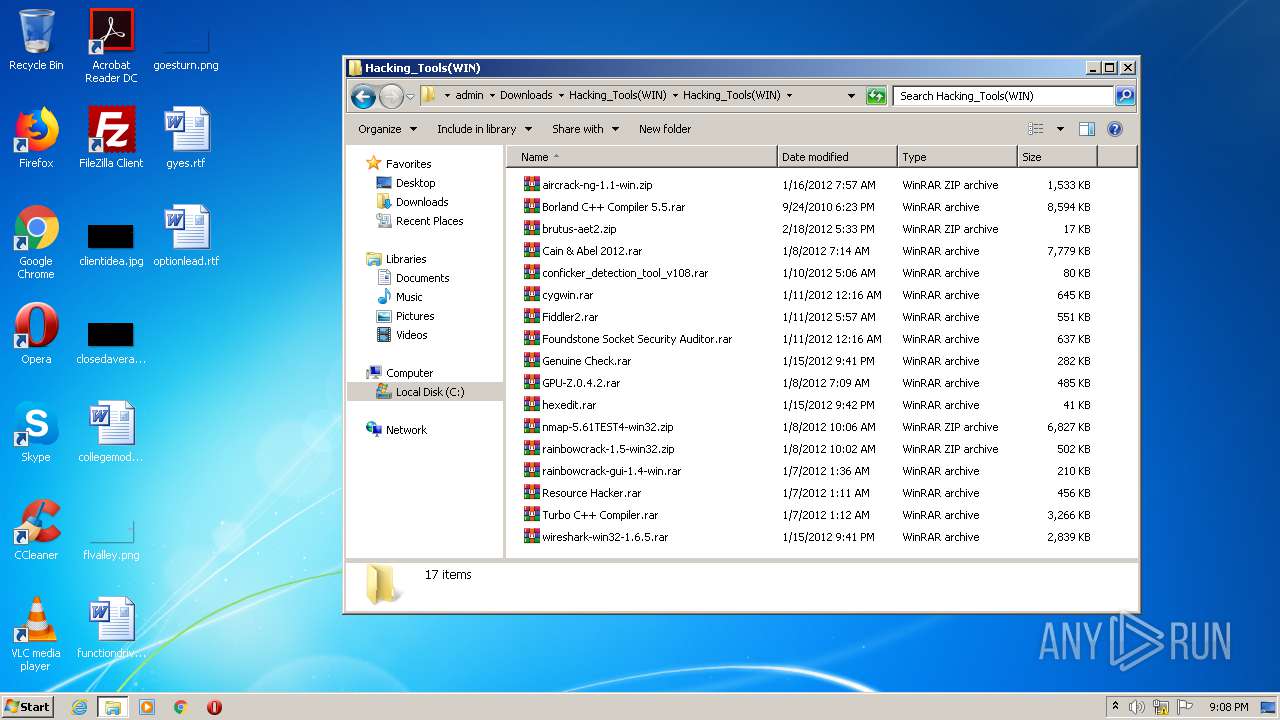
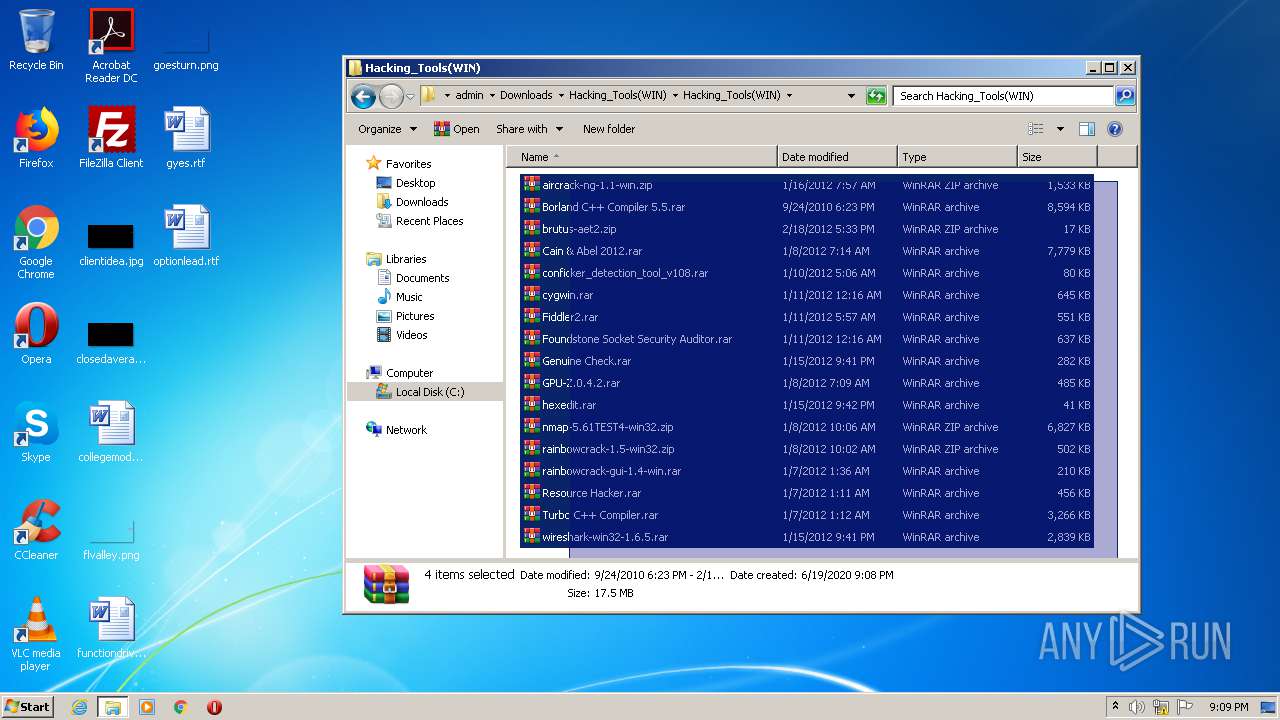
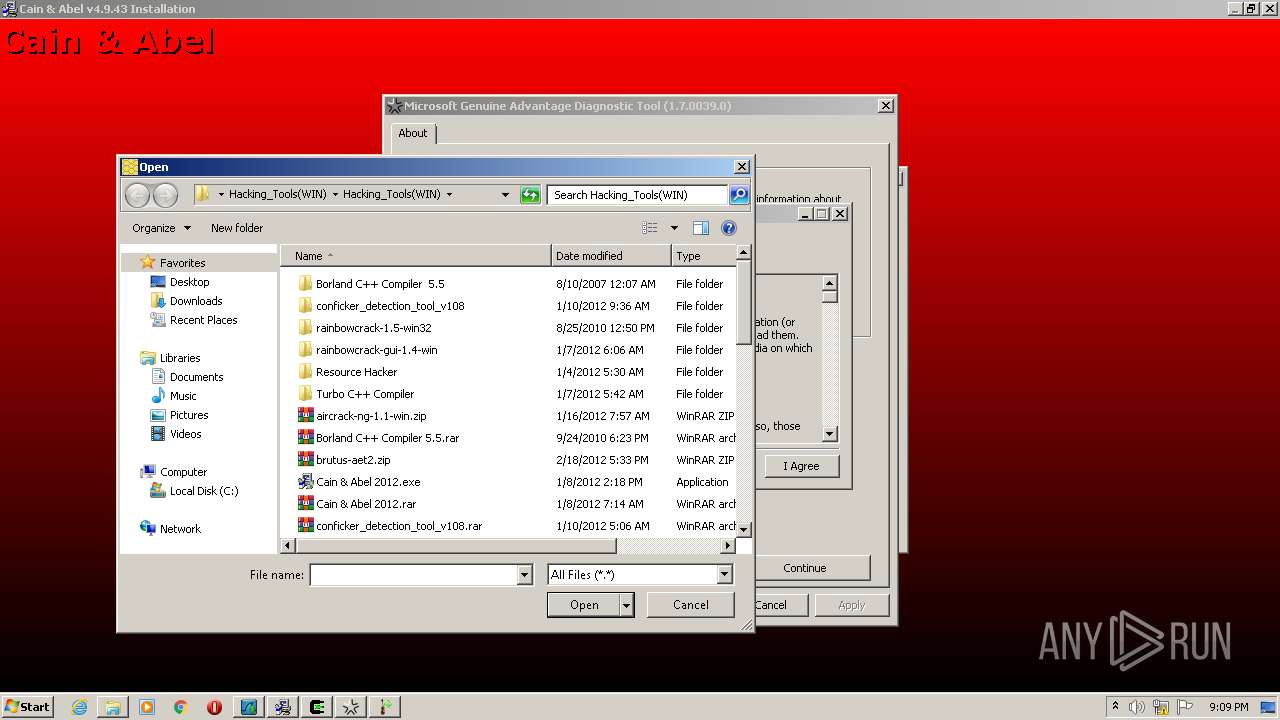
Manual execution by user
- WinRAR.exe (PID: 2420)
- wireshark-win32-1.6.5.exe (PID: 3064)
- wireshark-win32-1.6.5.exe (PID: 3892)
- WinRAR.exe (PID: 4020)
- Fiddler2.exe (PID: 3304)
- Cain & Abel 2012.exe (PID: 2844)
- Cain & Abel 2012.exe (PID: 3704)
- cygwin.exe (PID: 1908)
- Fiddler2.exe (PID: 3436)
- hexedit.exe (PID: 2780)
- Genuine Check.exe (PID: 2204)
- GPU-Z.0.4.2.exe (PID: 2280)
- GPU-Z.0.4.2.exe (PID: 3140)
Reads the hosts file
- chrome.exe (PID: 3832)
- chrome.exe (PID: 1856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
43
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13676580578238256159,14956559975687984350,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10506071709651059313 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1928 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,13676580578238256159,14956559975687984350,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12220872328957454503 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13676580578238256159,14956559975687984350,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9956708289215292490 --mojo-platform-channel-handle=4320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13676580578238256159,14956559975687984350,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11341561662635921148 --mojo-platform-channel-handle=4396 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://mega.nz/folder/RvJTnSaZ#aXAmZLoF6M8iXtICKSJenw/folder/xzBXTYiY" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6eb9a9d0,0x6eb9a9e0,0x6eb9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
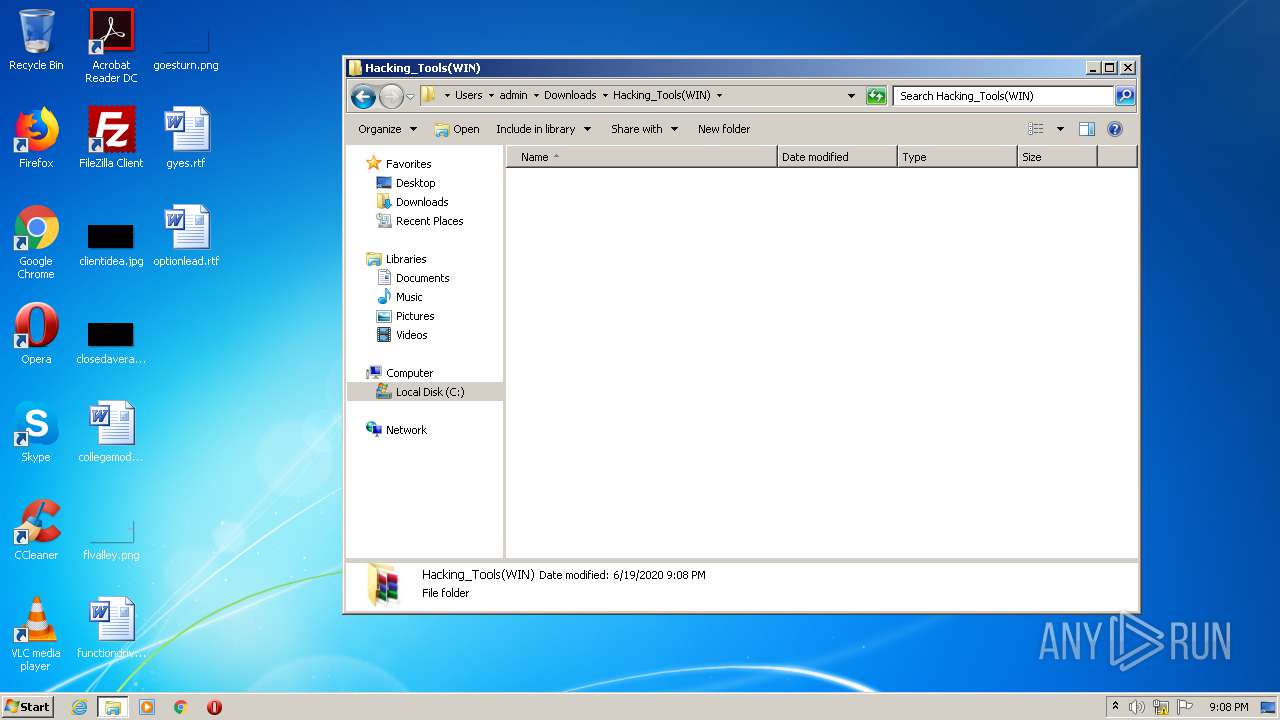
| 1908 | "C:\Users\admin\Downloads\Hacking_Tools(WIN)\Hacking_Tools(WIN)\cygwin.exe" | C:\Users\admin\Downloads\Hacking_Tools(WIN)\Hacking_Tools(WIN)\cygwin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,13676580578238256159,14956559975687984350,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1437985890555868977 --mojo-platform-channel-handle=4704 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,13676580578238256159,14956559975687984350,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2912654841746955036 --mojo-platform-channel-handle=4508 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 643
Read events
2 503
Write events
135
Delete events
5
Modification events
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1856-13237070843992250 |
Value: 259 | |||
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1856) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
27
Suspicious files
219
Text files
225
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EED1AFC-740.pma | — | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF1074b5.TMP | — | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF107467.TMP | text | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF10766a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
91
DNS requests
46
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3832 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3832 | chrome.exe | GET | 200 | 173.194.5.218:80 | http://r4---sn-aigl6n7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.92.25.193&mm=28&mn=sn-aigl6n7d&ms=nvh&mt=1592597174&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3832 | chrome.exe | GET | 200 | 173.194.183.71:80 | http://r2---sn-aigl6ned.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.92.25.193&mm=28&mn=sn-aigl6ned&ms=nvh&mt=1592597174&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
3832 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3832 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3832 | chrome.exe | 31.216.148.10:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
3832 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
3832 | chrome.exe | 172.217.21.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3832 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3832 | chrome.exe | 173.194.5.218:80 | r4---sn-aigl6n7d.gvt1.com | Google Inc. | US | whitelisted |
3832 | chrome.exe | 31.216.148.13:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
3832 | chrome.exe | 185.206.27.25:443 | gfs214n115.userstorage.mega.co.nz | — | — | suspicious |
3832 | chrome.exe | 154.53.224.174:443 | gfs262n144.userstorage.mega.co.nz | Cogent Communications | US | unknown |
3832 | chrome.exe | 89.44.168.96:443 | gfs270n380.userstorage.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
cygwin.exe | LOG: 2 io_stream_cygfile: fopen(/etc/setup/last-mirror) failed 2 No such file or directory |
cygwin.exe | LOG: 2 Starting cygwin install, version 2.697 |
cygwin.exe | LOG: 2 io_stream_cygfile: fopen(/etc/setup/net-proxy-host) failed 2 No such file or directory |
cygwin.exe | LOG: 2 io_stream_cygfile: fopen(/etc/setup/last-cache) failed 2 No such file or directory |
cygwin.exe | LOG: 2 io_stream_cygfile: fopen(/etc/setup/net-method) failed 2 No such file or directory |
cygwin.exe | LOG: 2 io_stream_cygfile: fopen(/etc/setup/setup.rc) failed 2 No such file or directory |
cygwin.exe | LOG: 2 io_stream_cygfile: fopen(/etc/setup/last-action) failed 2 No such file or directory |
cygwin.exe | LOG: 2 io_stream_cygfile: fopen(/etc/setup/net-proxy-port) failed 2 No such file or directory |
cygwin.exe | LOG: 2 io_stream_cygfile: fopen(/etc/setup/chooser_window_settings) failed 2 No such file or directory |
cygwin.exe | LOG: 2 Changing gid to Administrators |