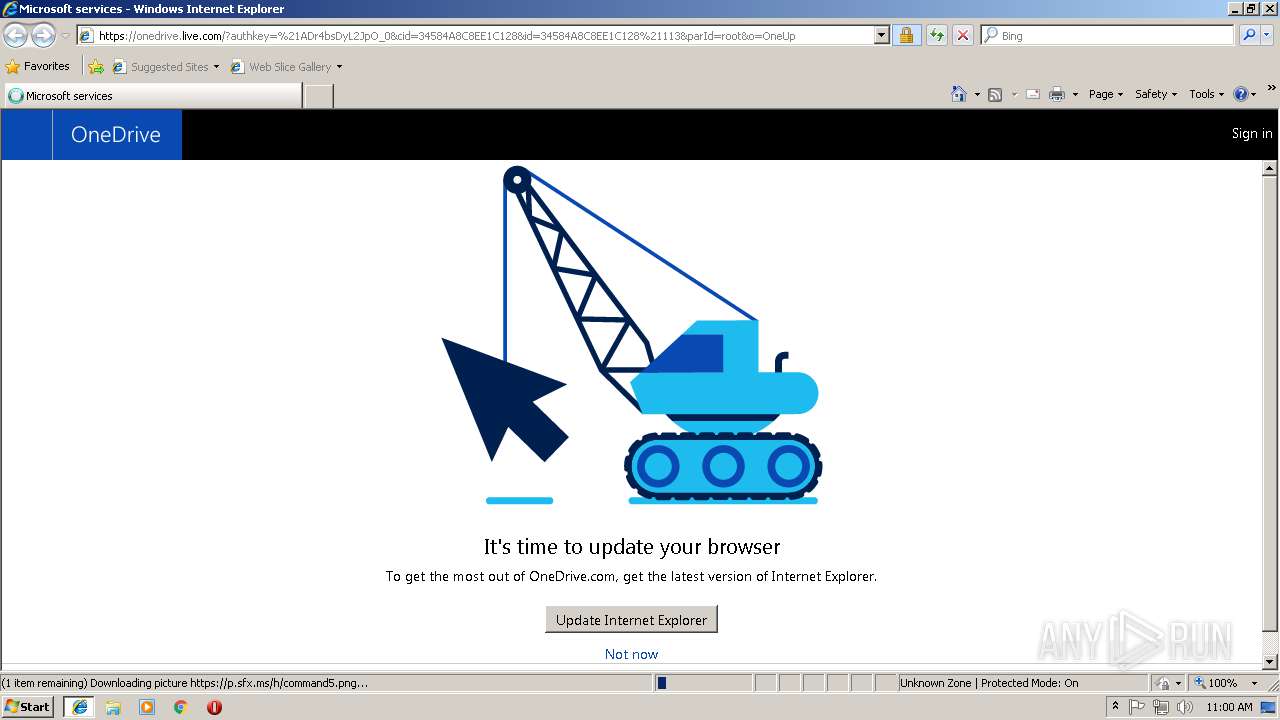
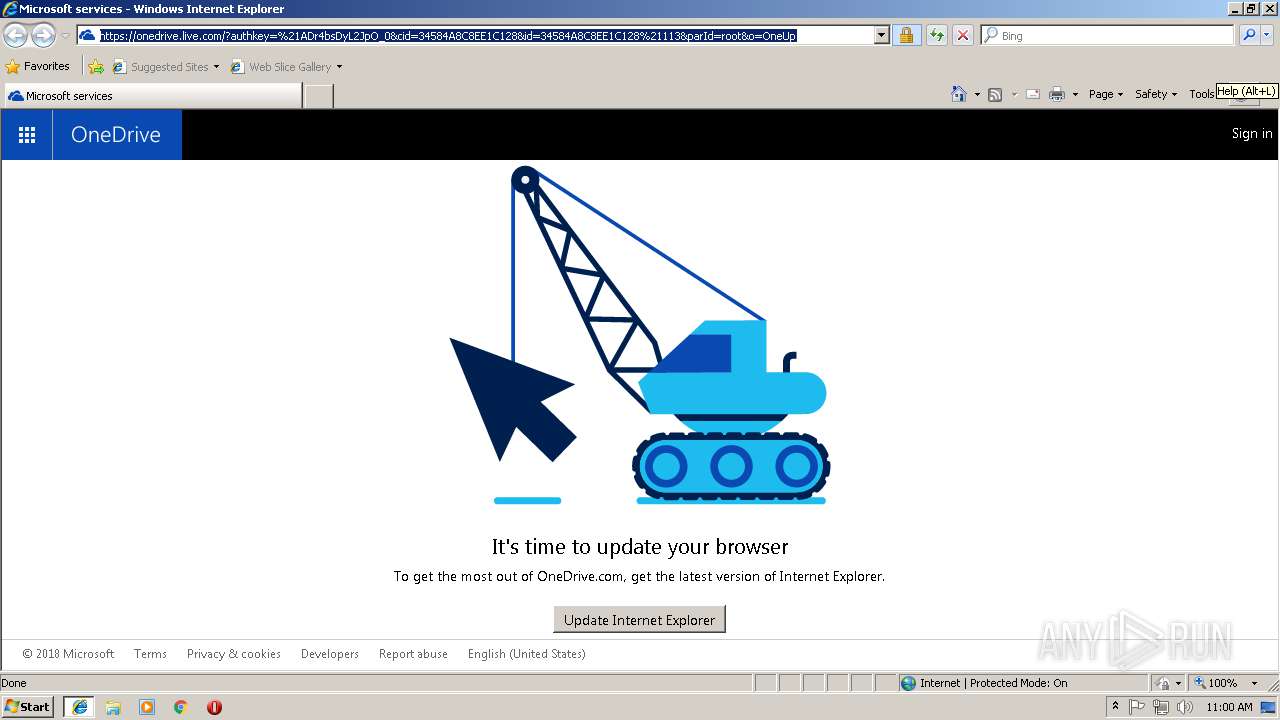
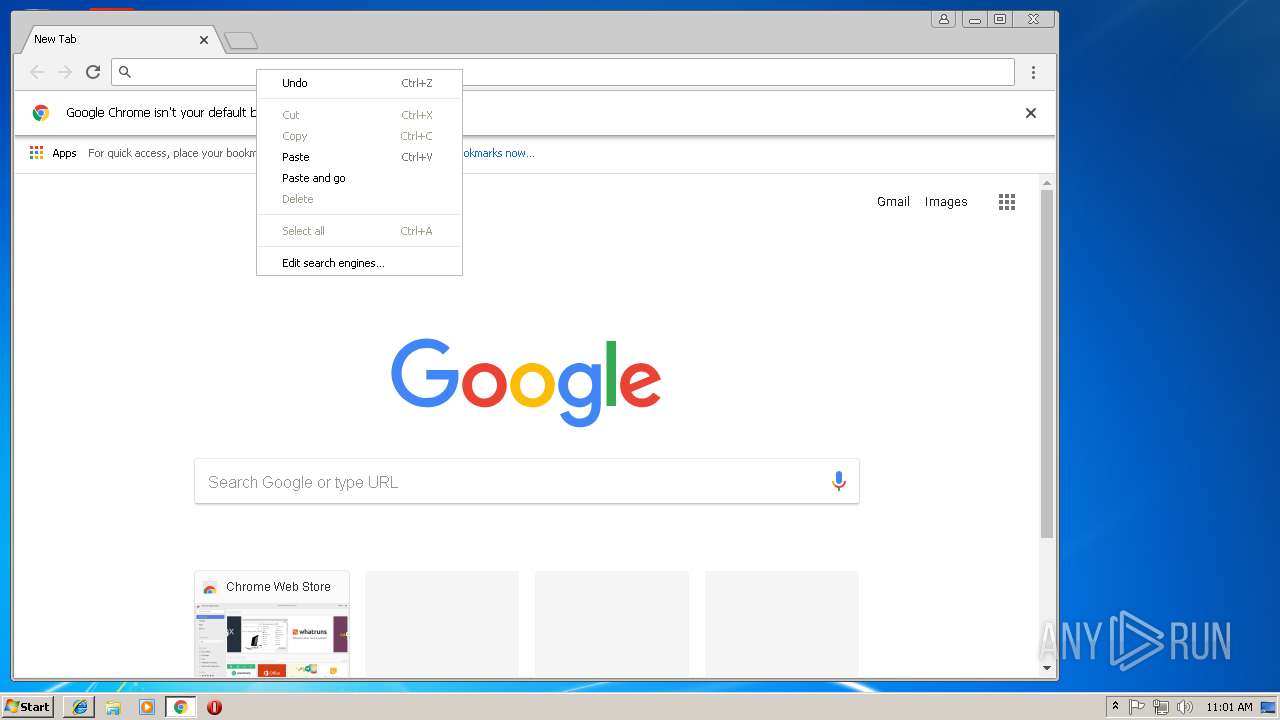
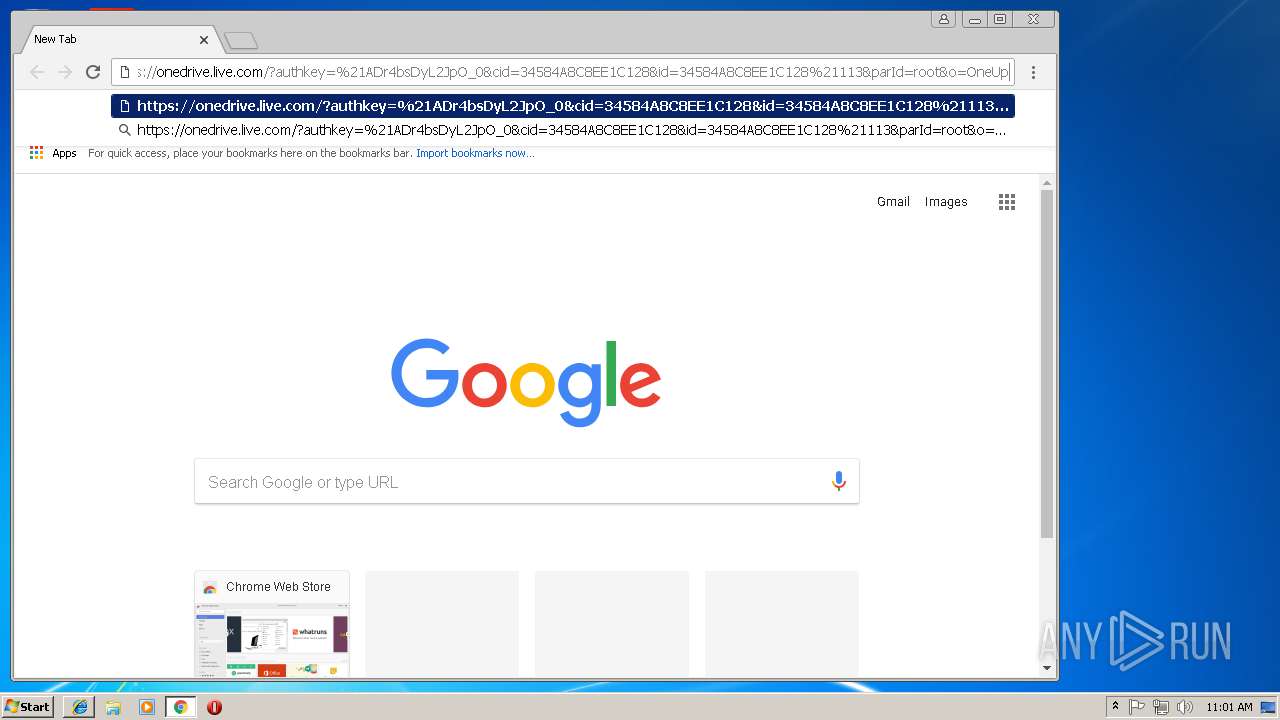
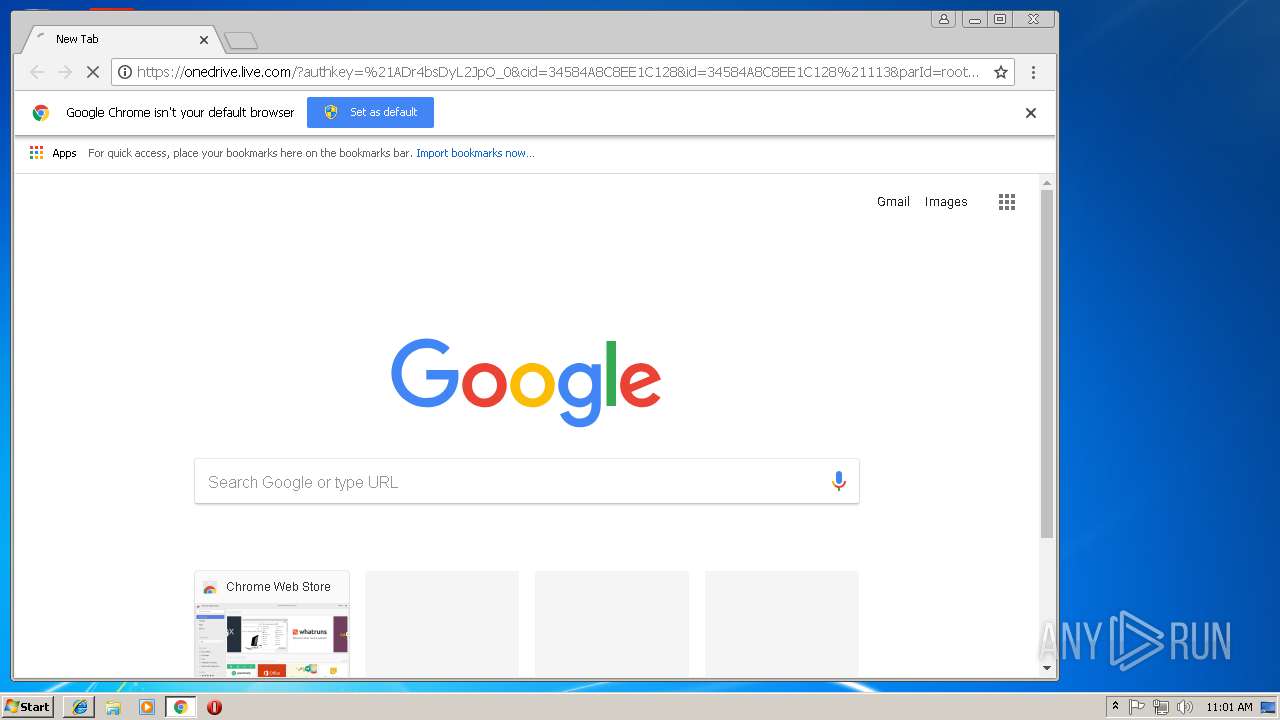
| URL: | https://onedrive.live.com/?authkey=%21ADr4bsDyL2JpO_0&cid=34584A8C8EE1C128&id=34584A8C8EE1C128%21113&parId=root&o=OneUp |
| Full analysis: | https://app.any.run/tasks/fcd9bb90-5d68-4dec-9560-1242c3b9b987 |
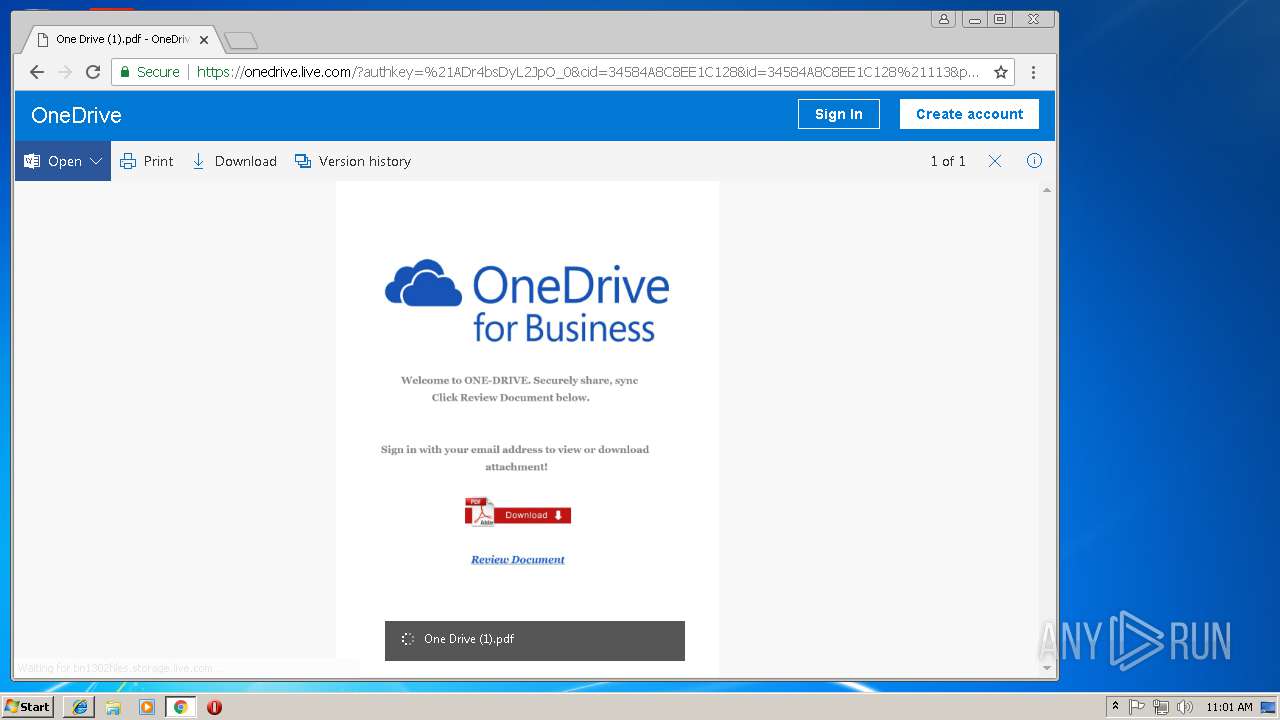
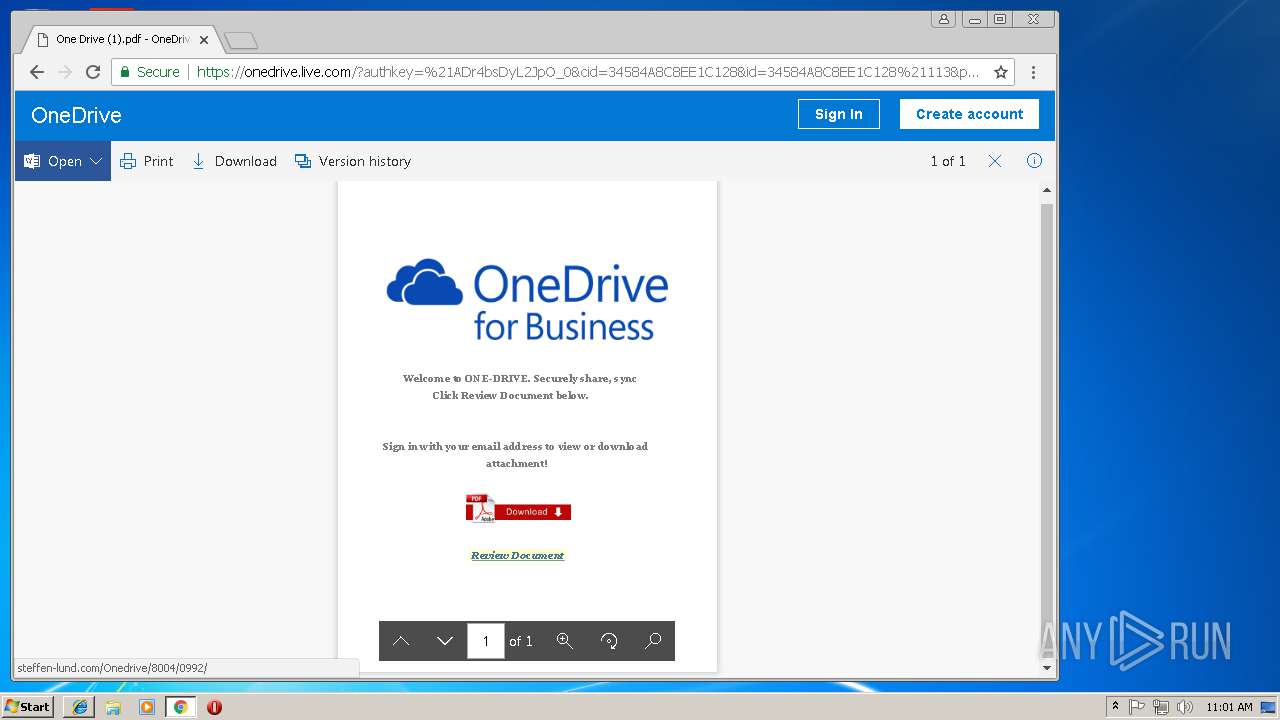
| Verdict: | Malicious activity |
| Analysis date: | November 06, 2018, 10:59:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E04EABE67BBCAF0A8AC217DAB13E1C2E |
| SHA1: | 1D27C59CD78145D8D0D4D84ACCF47ABE68A5587B |
| SHA256: | C7E623ED18A4F6A9FF774E46E1752252A0279D738DC6946EC92E5DBAC4D8FFC2 |
| SSDEEP: | 3:N8Ck3CTZxAXDBH9XZbvQTkUlUjkUlU9FzKHJV:2CkSTfAXlHnbITkPk5Fyb |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads internet explorer settings
- iexplore.exe (PID: 844)
Changes internet zones settings
- iexplore.exe (PID: 3088)
Creates files in the user directory
- iexplore.exe (PID: 3088)
- iexplore.exe (PID: 844)
Changes settings of System certificates
- iexplore.exe (PID: 3088)
Reads Internet Cache Settings
- iexplore.exe (PID: 844)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3088)
Reads settings of System Certificates
- iexplore.exe (PID: 3088)
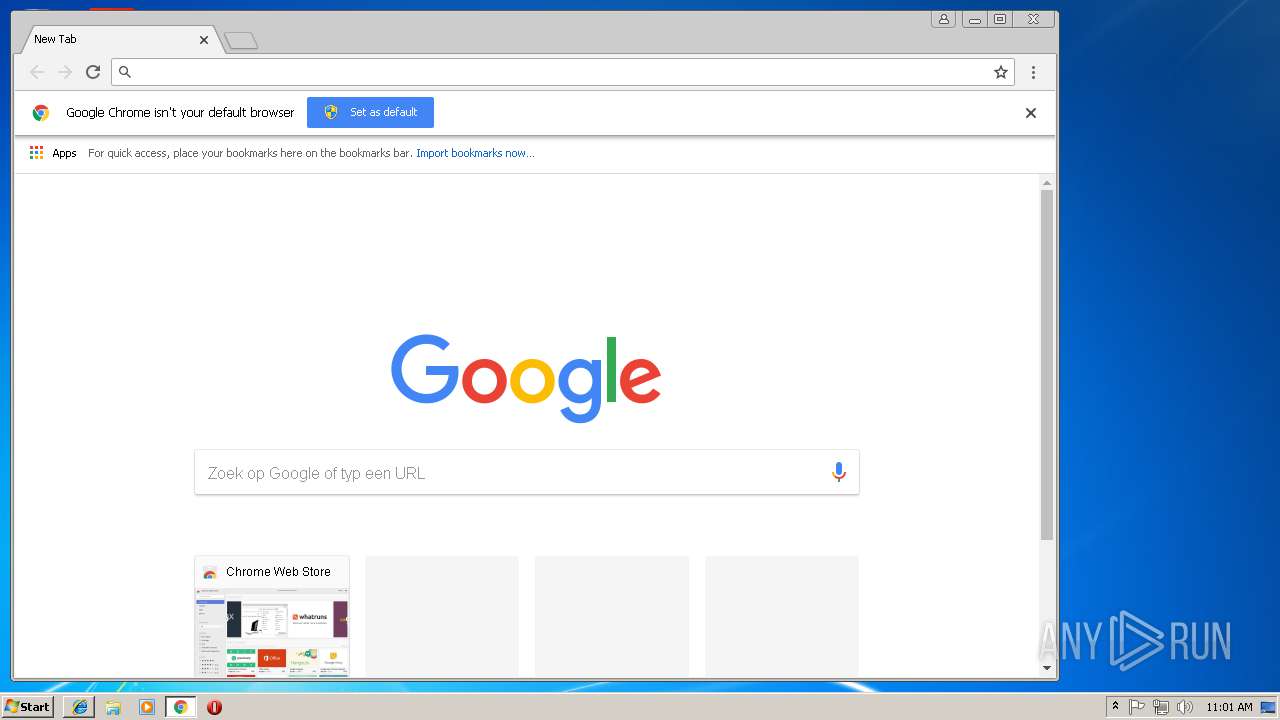
Application launched itself
- iexplore.exe (PID: 3088)
- chrome.exe (PID: 1388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3088 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,9149086516746910200,3180074079838609091,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=DD2CBD78C90EA7B971DB16F0892AC695 --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,9149086516746910200,3180074079838609091,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B2DC81A3142704CDFE16349B907B2EBE --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B2DC81A3142704CDFE16349B907B2EBE --renderer-client-id=9 --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,9149086516746910200,3180074079838609091,131072 --enable-features=PasswordImport --service-pipe-token=D4AC9AE50470276183ACEE29BBDD9BAA --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D4AC9AE50470276183ACEE29BBDD9BAA --renderer-client-id=5 --mojo-platform-channel-handle=1880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,9149086516746910200,3180074079838609091,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3E5B5505D961B9438421198635968351 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3E5B5505D961B9438421198635968351 --renderer-client-id=11 --mojo-platform-channel-handle=3696 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,9149086516746910200,3180074079838609091,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D268F1CAA24D04919F16BA040557E59D --mojo-platform-channel-handle=876 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,9149086516746910200,3180074079838609091,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=547B1AE7B95DEEDCBAB87199A128FD54 --mojo-platform-channel-handle=3712 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,9149086516746910200,3180074079838609091,131072 --enable-features=PasswordImport --service-pipe-token=7AE4F6B1AF6A1494F36239178207DD6C --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7AE4F6B1AF6A1494F36239178207DD6C --renderer-client-id=3 --mojo-platform-channel-handle=2064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,9149086516746910200,3180074079838609091,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A7EDDFE0A40F198A578E3DAE9DDCA52D --mojo-platform-channel-handle=3784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
971
Read events
860
Write events
107
Delete events
4
Modification events
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {23C8D503-E1B3-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B00020006000B00000010006001 | |||
Executable files
0
Suspicious files
91
Text files
91
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\onedrive_live_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\legacy_s_legacy-0f159289[1].js | text | |
MD5:— | SHA256:— | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\legacy0-e2cc9701[1].js | text | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 | binary | |
MD5:— | SHA256:— | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\legacy1-1a09fb82[1].js | text | |
MD5:— | SHA256:— | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\c7[1].png | image | |
MD5:D982209AA90DEBDEDBB71AC66AA5499E | SHA256:639B06D02E6139D78E0EAEB0F8A31D96AF88A0882D8036C5A6B45D10C3E321A3 | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\jquery-1.7.2-39eeb07e[1].js | text | |
MD5:39EEB07E6802E2B57F5E10A9AD9BCA24 | SHA256:D6C15974B6181A68E9B74E4F38FBAC81D640569EF0FBBAA3381CC59683A9763F | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\maincss-aec76c77[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
77
DNS requests
44
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1388 | chrome.exe | GET | 200 | 173.223.106.136:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | NL | der | 471 b | whitelisted |
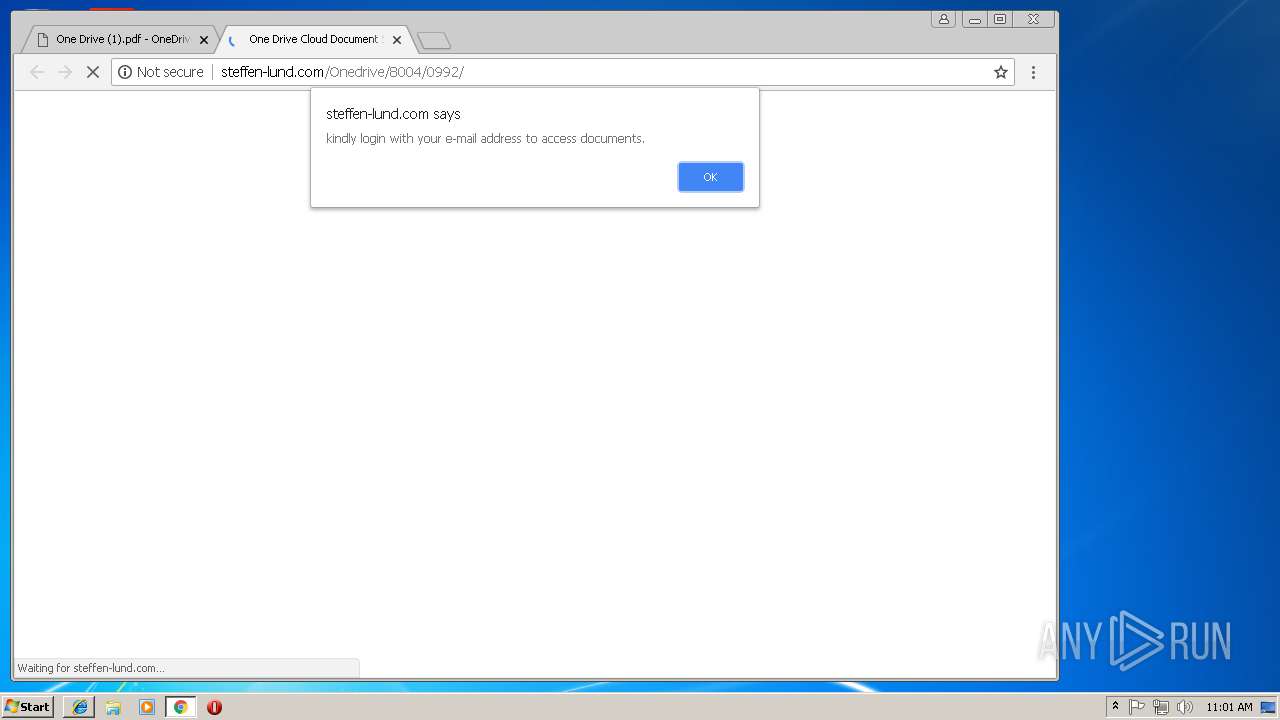
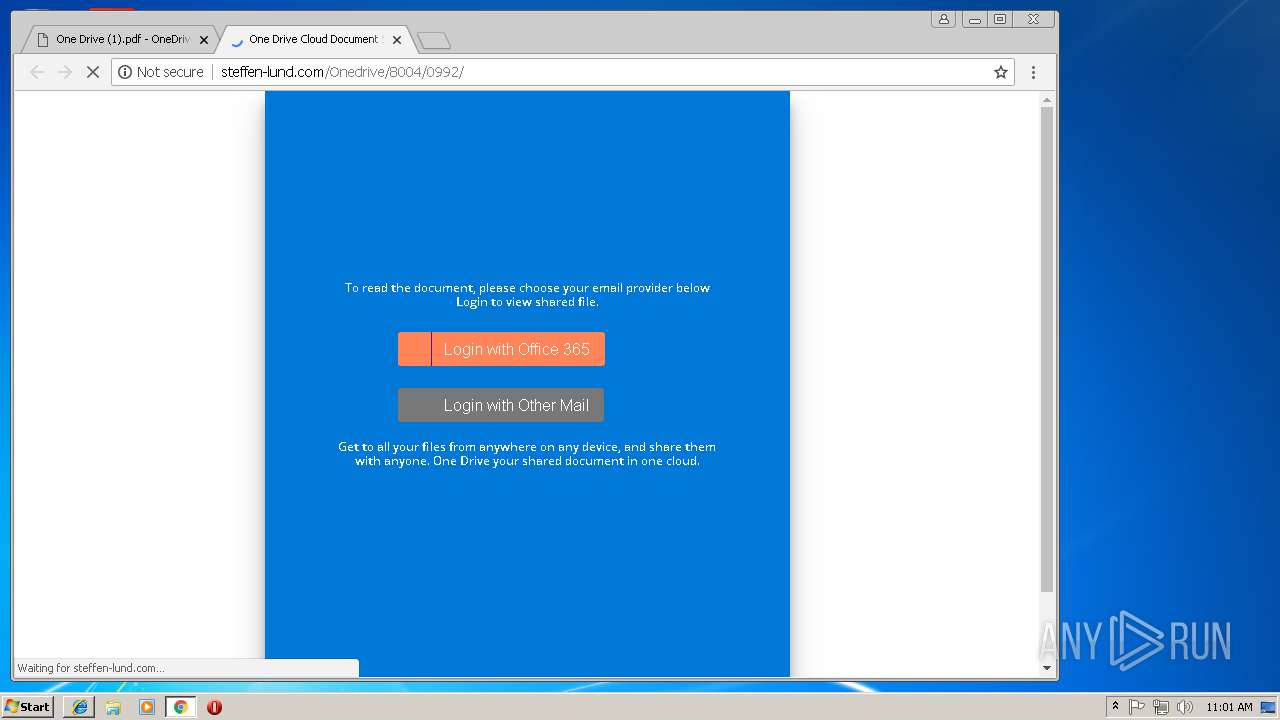
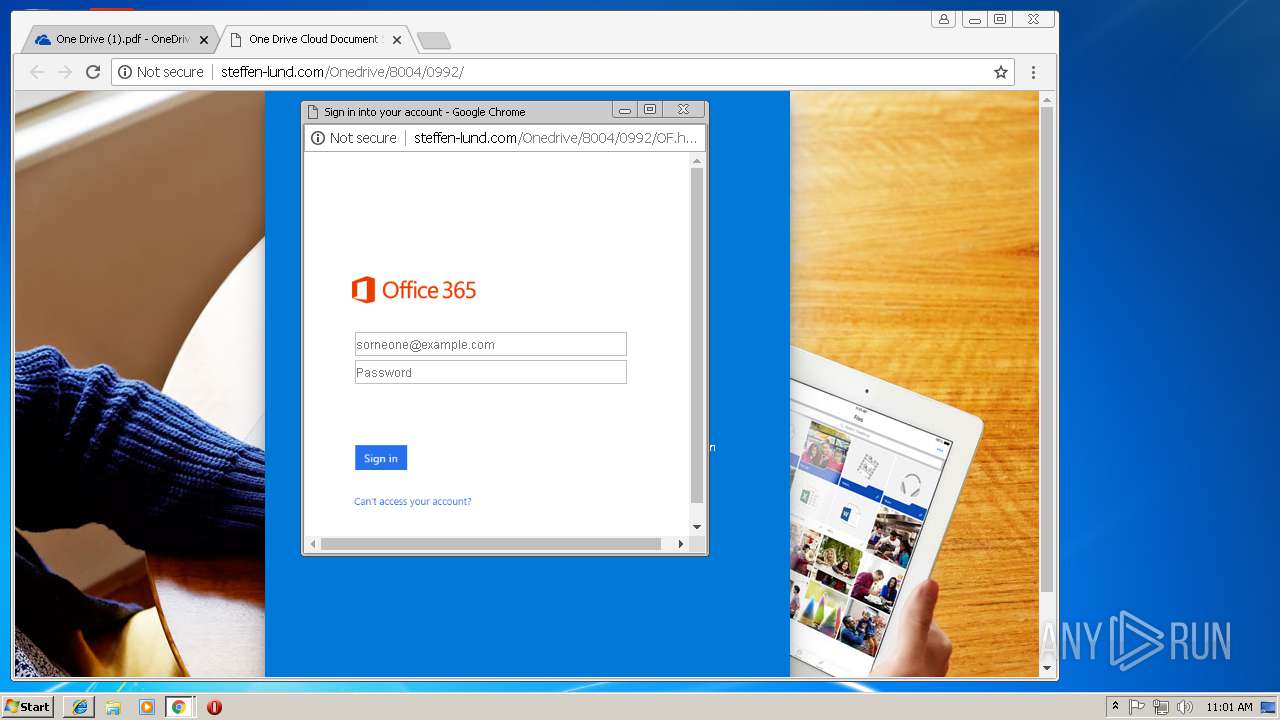
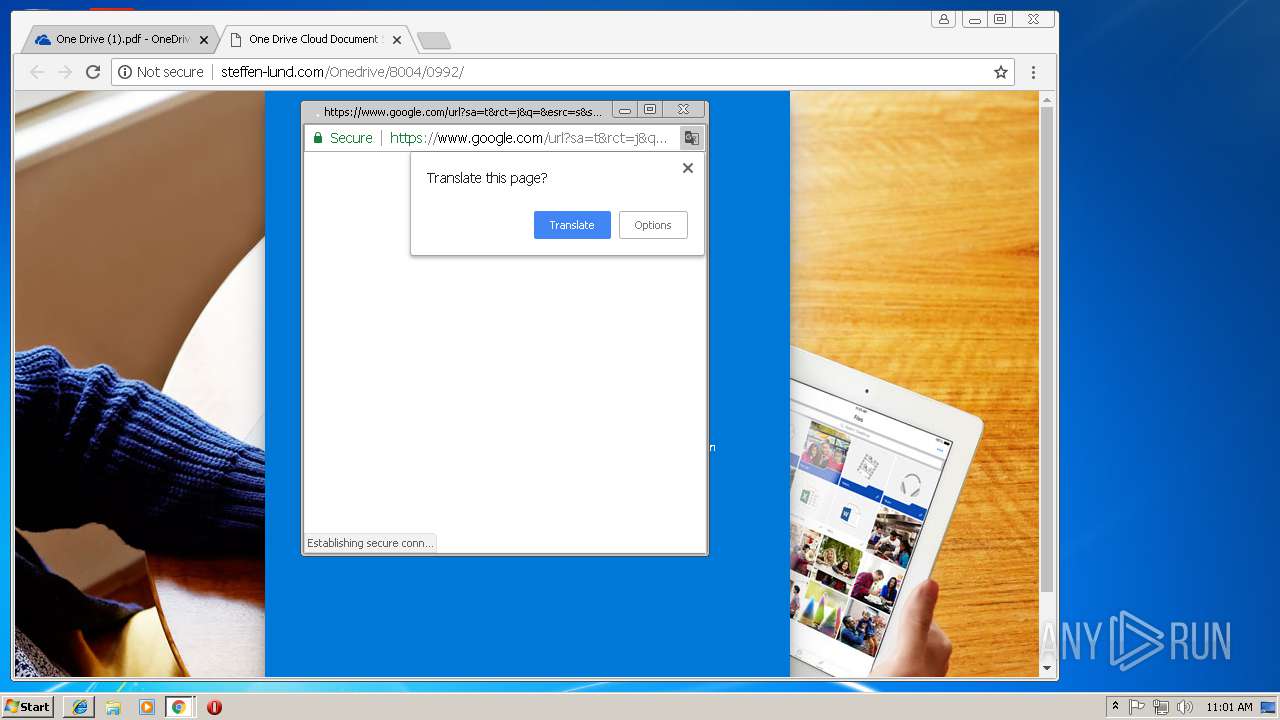
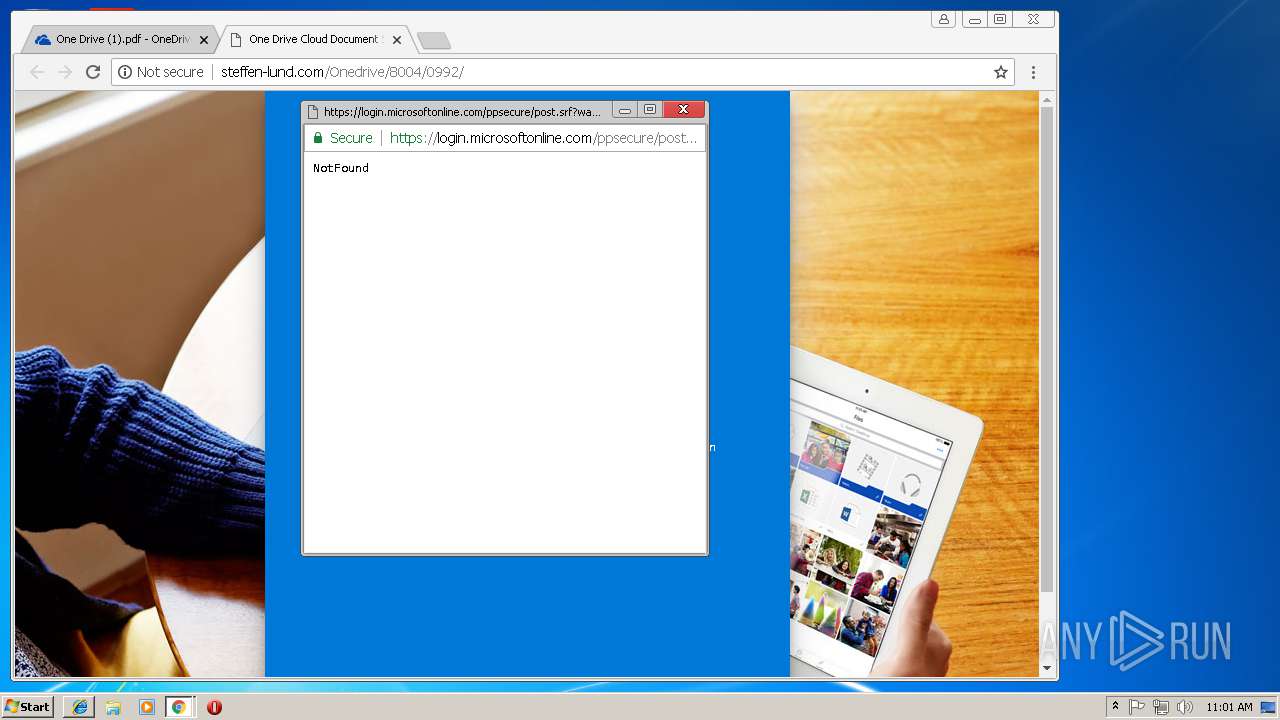
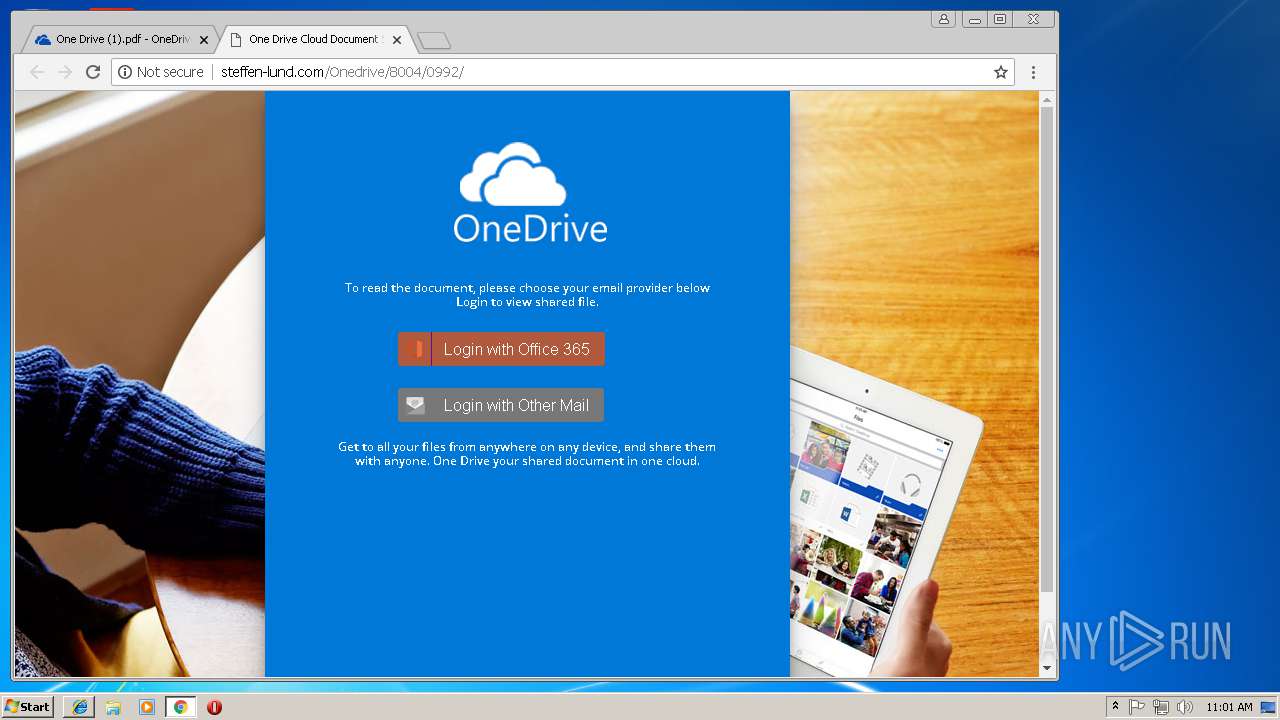
1388 | chrome.exe | GET | 200 | 50.87.150.234:80 | http://steffen-lund.com/Onedrive/8004/0992/ | US | html | 970 b | suspicious |
1388 | chrome.exe | GET | 200 | 50.87.150.234:80 | http://steffen-lund.com/Onedrive/8004/0992/ojomu/OF1.jpg | US | image | 11.0 Kb | suspicious |
1388 | chrome.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCED1AM6ZQ1WeP16w8r%2FAKqvU%3D | GB | der | 727 b | whitelisted |
1388 | chrome.exe | GET | 200 | 2.16.186.41:80 | http://ocsp.ssl.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBS09e2eDZ4%2BD4WY3yIXRy703I7%2FjQQUfVUE0fc1fCJxP0vmVxLDi5qldGsCEQCpCNDyPW%2FvFOcnxn%2FVjDWF | unknown | der | 472 b | whitelisted |
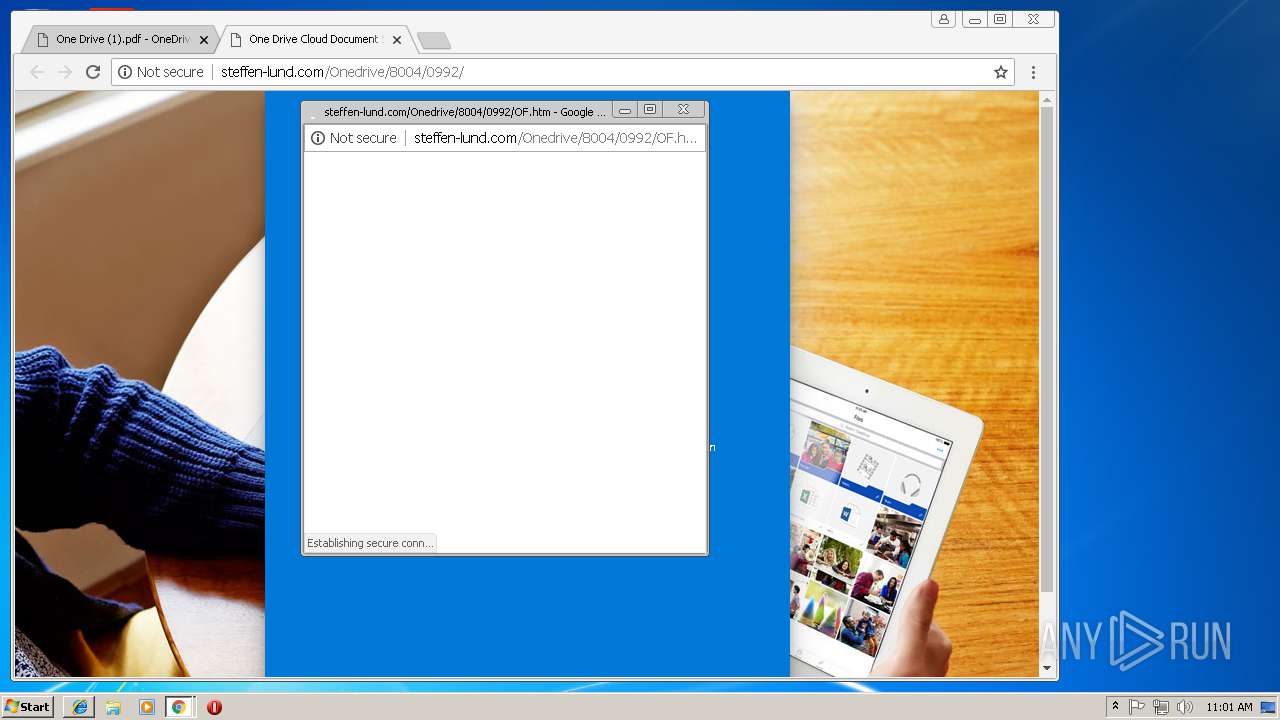
1388 | chrome.exe | GET | 200 | 50.87.150.234:80 | http://steffen-lund.com/Onedrive/8004/0992/OF.htm | US | html | 1.13 Kb | suspicious |
1388 | chrome.exe | GET | 200 | 50.87.150.234:80 | http://steffen-lund.com/Onedrive/8004/0992/images/landing-devices-bg.jpg | US | image | 195 Kb | suspicious |
1388 | chrome.exe | GET | 200 | 50.87.150.234:80 | http://steffen-lund.com/favicon.ico | US | image | 195 Kb | suspicious |
1388 | chrome.exe | GET | 200 | 50.87.150.234:80 | http://steffen-lund.com/Onedrive/8004/0992/css/style.css | US | text | 1.96 Kb | suspicious |
1388 | chrome.exe | GET | 200 | 50.87.150.234:80 | http://steffen-lund.com/Onedrive/8004/0992/images/office.png | US | image | 1.39 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
844 | iexplore.exe | 2.16.186.40:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
844 | iexplore.exe | 2.16.186.25:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
844 | iexplore.exe | 2.19.37.83:443 | p.sfx.ms | Akamai International B.V. | — | whitelisted |
3088 | iexplore.exe | 2.19.37.83:443 | p.sfx.ms | Akamai International B.V. | — | whitelisted |
1388 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
1388 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 216.58.215.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 2.16.186.40:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
onedrive.live.com |
| shared |
spoprod-a.akamaihd.net |
| whitelisted |
p.sfx.ms |
| whitelisted |
dns.msftncsi.com |
| shared |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1388 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Multi-Email Popupwnd Phishing Landing 2018-01-25 |
1388 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS OneDrive Phishing Landing 2018-02-12 |
1388 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS OneDrive Phishing Landing 2018-03-08 |
1388 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS OneDrive Phishing Landing 2018-05-01 |
2 ETPRO signatures available at the full report