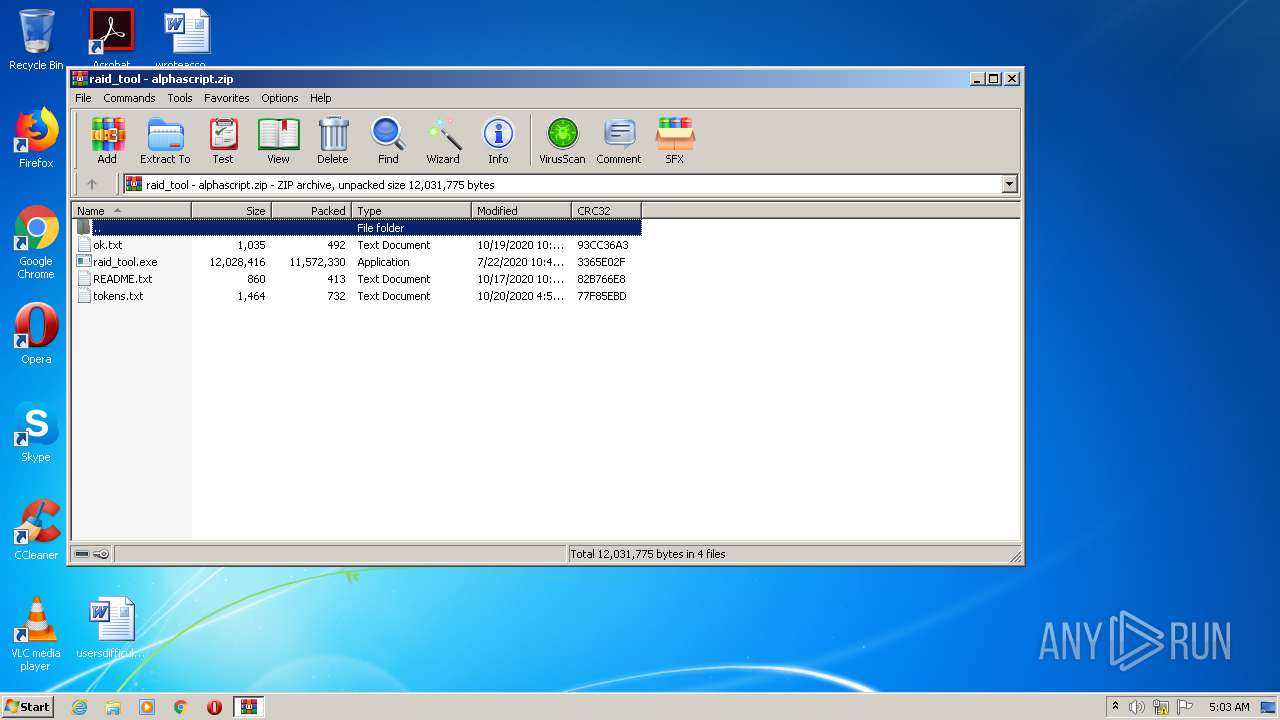
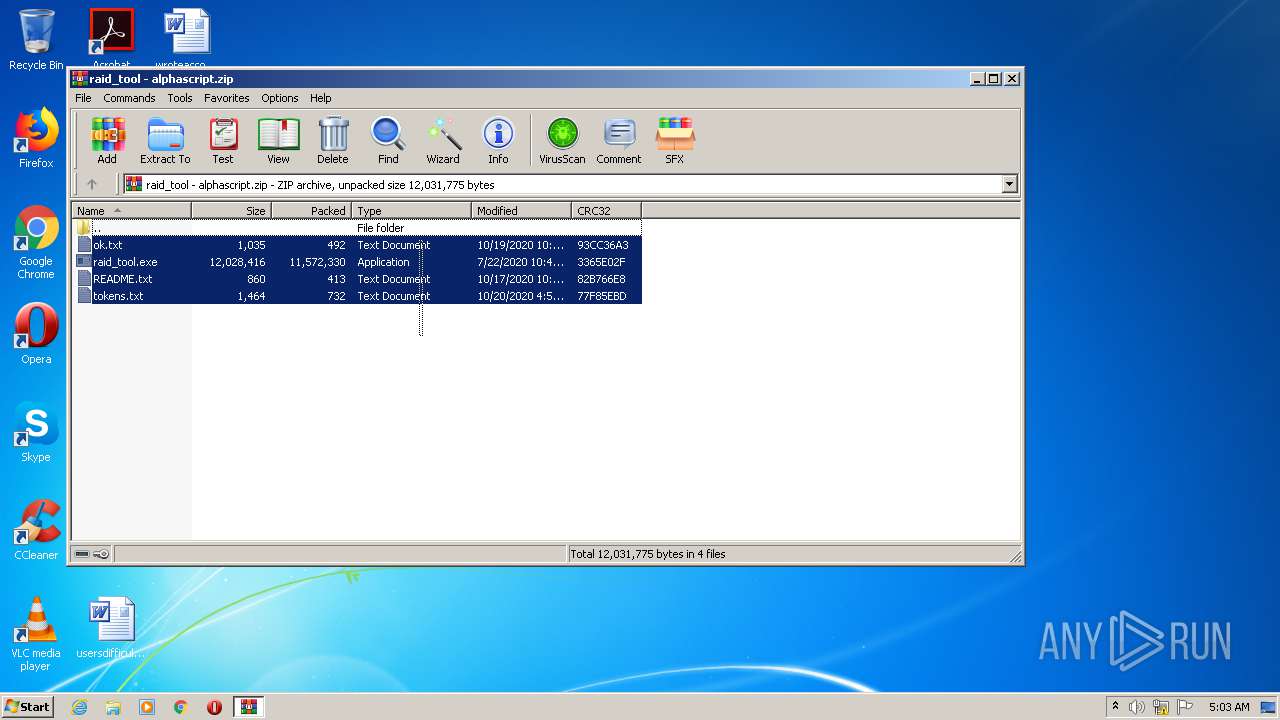
| File name: | raid_tool - alphascript.zip |
| Full analysis: | https://app.any.run/tasks/e4ef888d-e2d8-41c2-ab89-c6957167a9d3 |
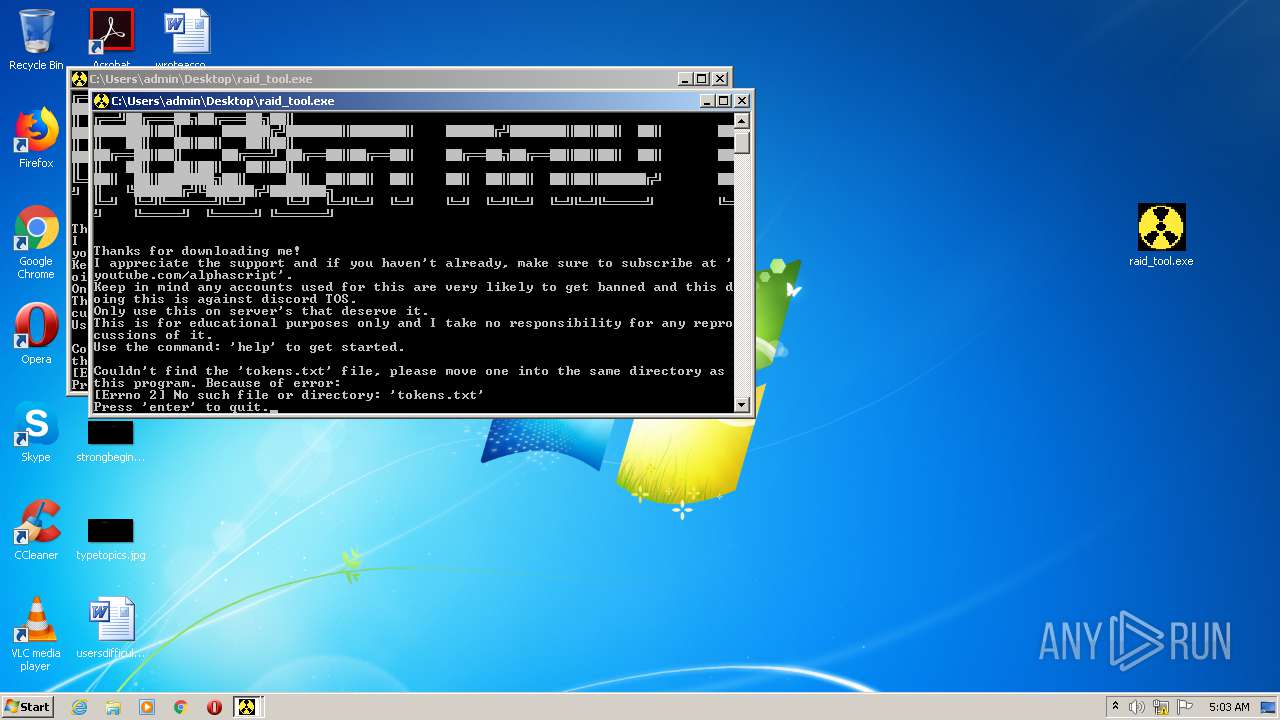
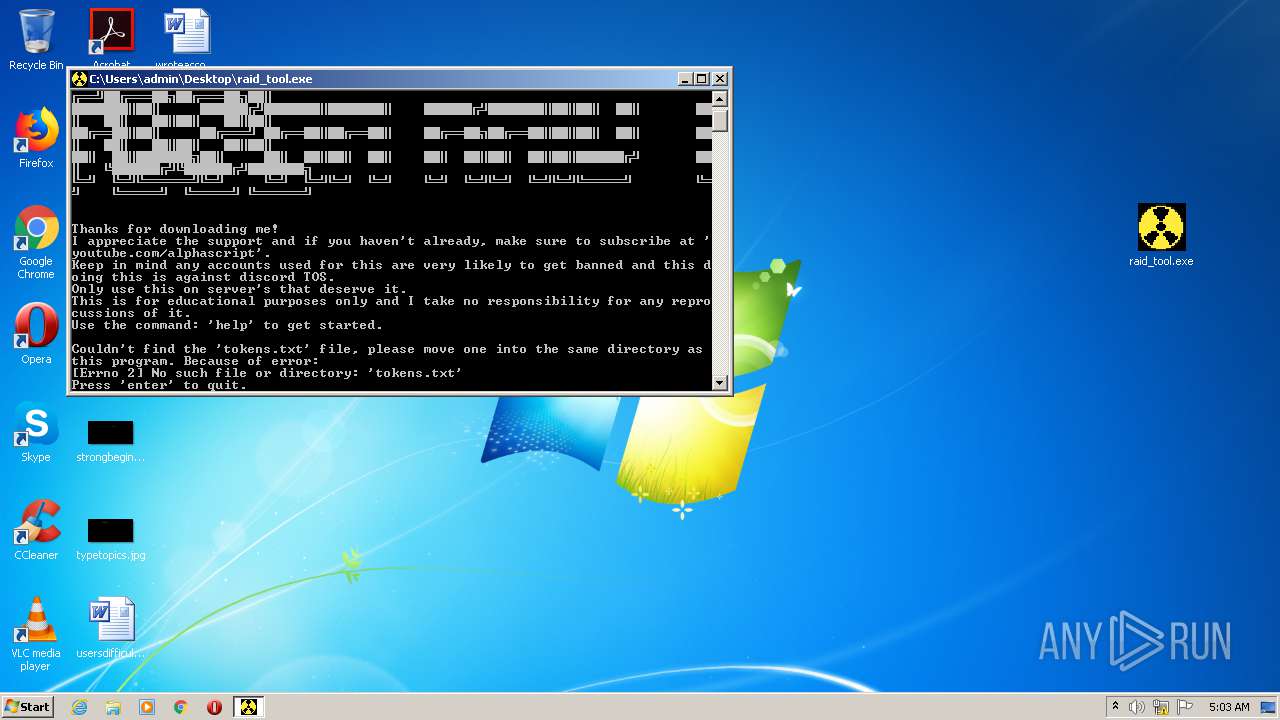
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 04:03:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 28440286BCCC4CDA9AFF930C0DF80373 |
| SHA1: | 21C724681ADB18974894433B494CF0D3D212854B |
| SHA256: | C7DA9A493534C075BB8C3D805F9D5FFA439D58EB6F8D11D575C9501E1DBC34D2 |
| SSDEEP: | 196608:egzE5VUziCh92ESzIYsbO1m8v26jrkNDRHcthJZ409aXKNdSF88C0YwAfcjrZIVK:dz/0nzIfi1m8u6QHcthbtE2V0Y9kxjGM |
MALICIOUS
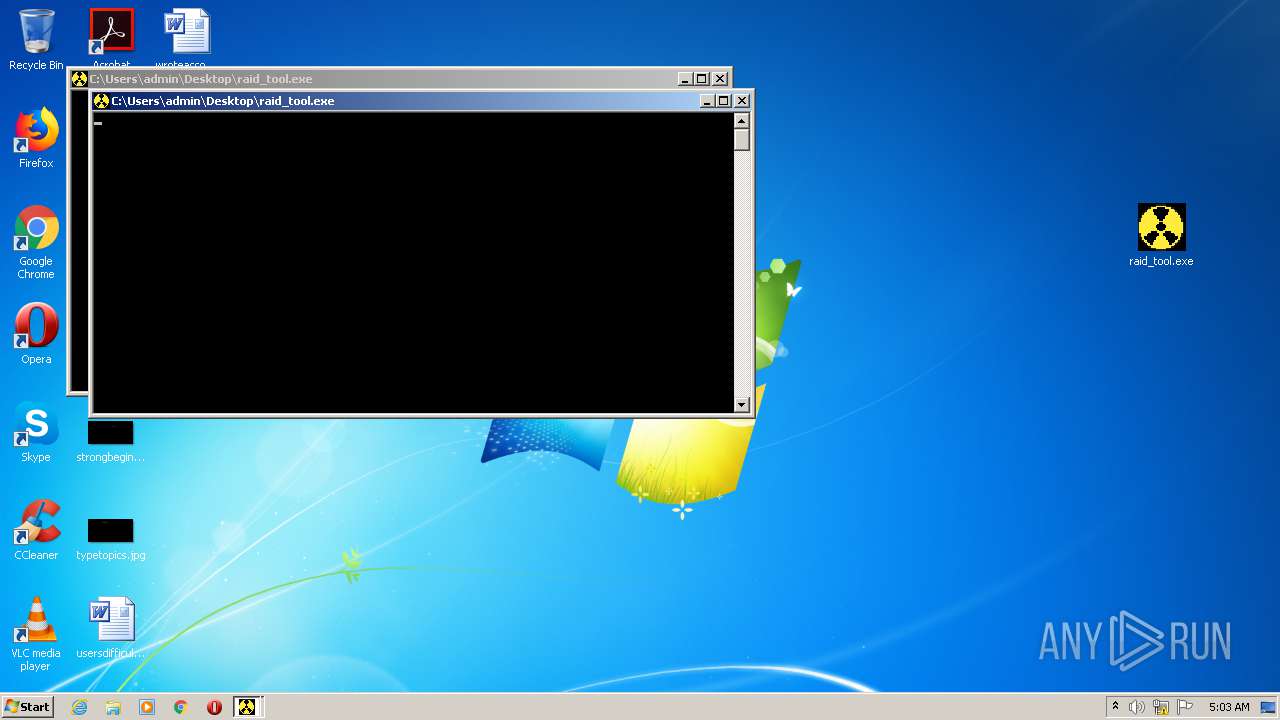
Application was dropped or rewritten from another process
- raid_tool.exe (PID: 2900)
- raid_tool.exe (PID: 3592)
- raid_tool.exe (PID: 3432)
- raid_tool.exe (PID: 4004)
Loads dropped or rewritten executable
- raid_tool.exe (PID: 4004)
- raid_tool.exe (PID: 3432)
SUSPICIOUS
Executable content was dropped or overwritten
- raid_tool.exe (PID: 2900)
- raid_tool.exe (PID: 3592)
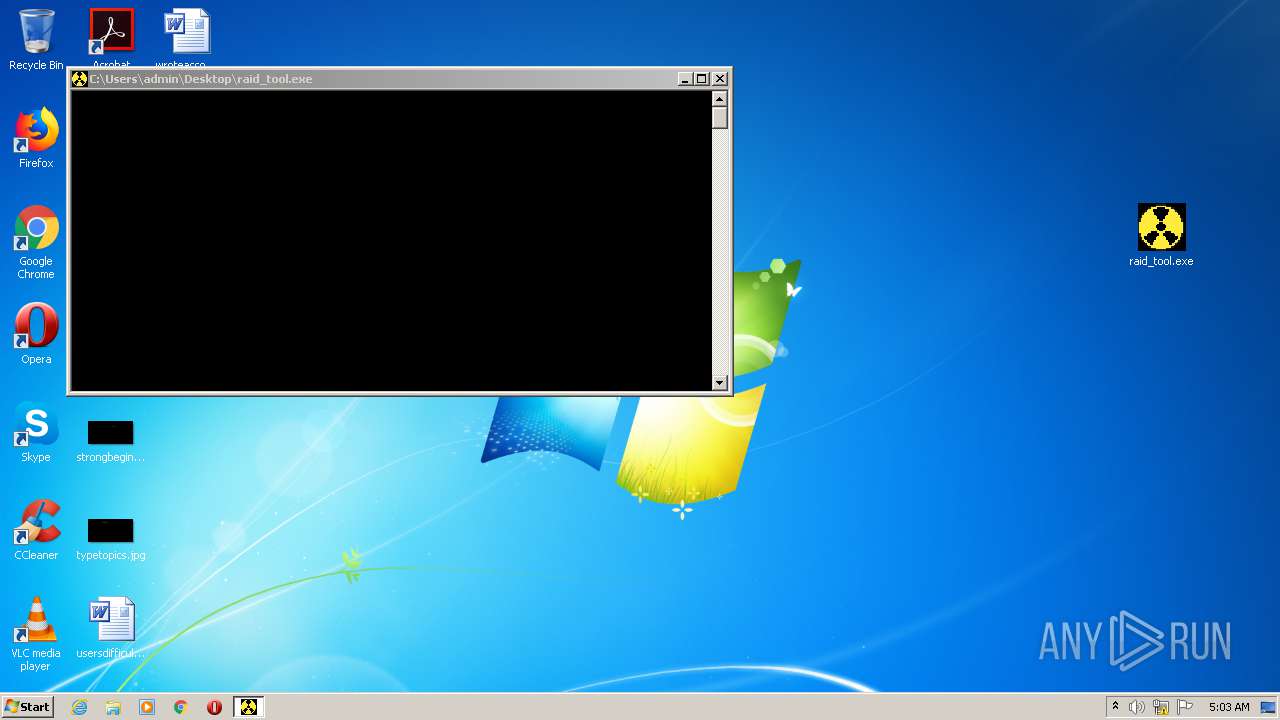
Application launched itself
- raid_tool.exe (PID: 2900)
- raid_tool.exe (PID: 3592)
Loads Python modules
- raid_tool.exe (PID: 3432)
- raid_tool.exe (PID: 4004)
INFO
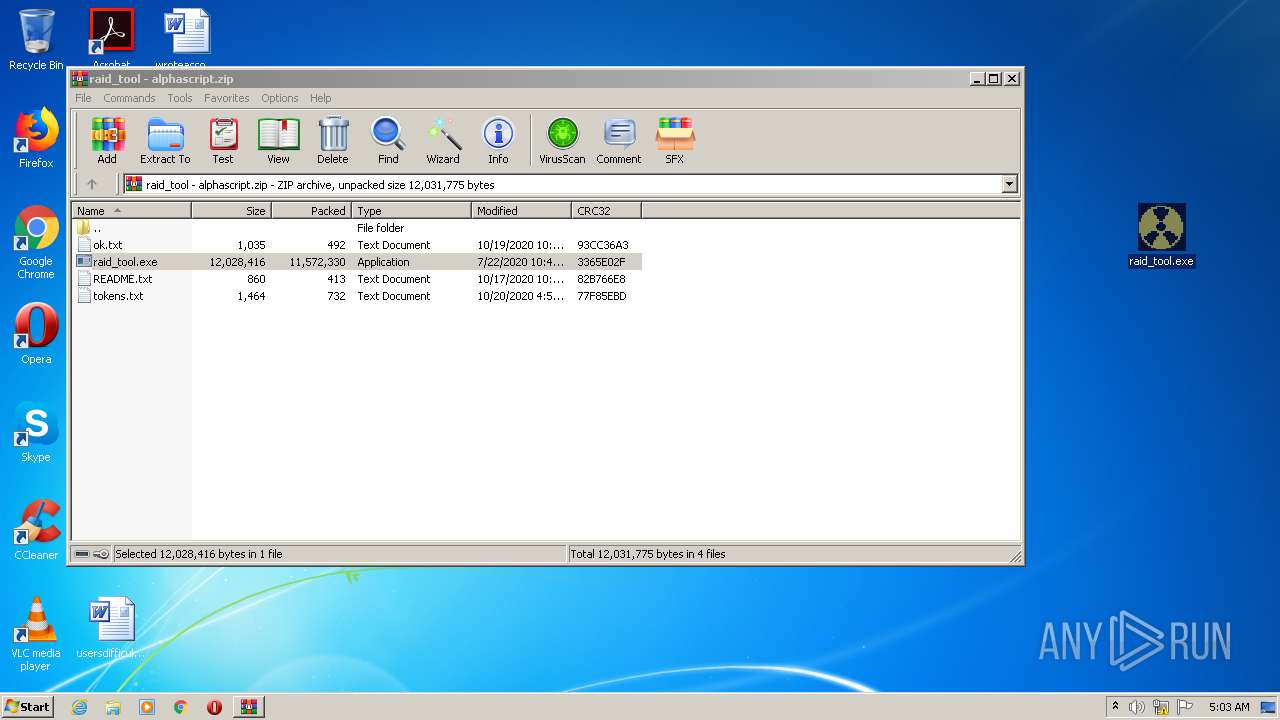
Manual execution by user
- raid_tool.exe (PID: 3592)
- raid_tool.exe (PID: 2900)
Dropped object may contain Bitcoin addresses
- raid_tool.exe (PID: 2900)
- raid_tool.exe (PID: 3592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:07:22 17:41:08 |
| ZipCRC: | 0x3365e02f |
| ZipCompressedSize: | 11572330 |
| ZipUncompressedSize: | 12028416 |
| ZipFileName: | raid_tool.exe |
Total processes
43
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2224 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\raid_tool - alphascript.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\Desktop\raid_tool.exe" | C:\Users\admin\Desktop\raid_tool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3432 | "C:\Users\admin\Desktop\raid_tool.exe" | C:\Users\admin\Desktop\raid_tool.exe | — | raid_tool.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 3592 | "C:\Users\admin\Desktop\raid_tool.exe" | C:\Users\admin\Desktop\raid_tool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 4004 | "C:\Users\admin\Desktop\raid_tool.exe" | C:\Users\admin\Desktop\raid_tool.exe | — | raid_tool.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
914
Read events
894
Write events
20
Delete events
0
Modification events
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\raid_tool - alphascript.zip | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
68
Suspicious files
6
Text files
1 718
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2224 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2224.44903\raid_tool.exe | — | |
MD5:— | SHA256:— | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\VCRUNTIME140.dll | executable | |
MD5:4C360F78DE1F5BAAA5F110E65FAC94B4 | SHA256:AD1B0992B890BFE88EF52D0A830873ACC0AECC9BD6E4FC22397DBCCF4D2B4E37 | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\_cffi_backend.cp38-win32.pyd | executable | |
MD5:012DB6C90D38DB71D0647659217CA286 | SHA256:4207E3276411F75A6680EAE28D7D5ED7F6CAD946B1DE7B724440F44593267414 | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\_ctypes.pyd | executable | |
MD5:3A2E78784B929003A6BACEEBDB0EFA4D | SHA256:F205948B01B29CB244AE09C5B57FD4B6C8F356DFCD2F8CB49E7CFD177A748CF9 | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\_lzma.pyd | executable | |
MD5:54F12E2385A77D825AE4D41A4AC515FE | SHA256:08DE18FBA635822F3BB89C9429F175E3680B7261546430BA9E2ED09BB31F5218 | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\_overlapped.pyd | executable | |
MD5:AA428E44A78A280EC8152C43D8284F6F | SHA256:F8FDA2A6E3FF0069E634FEEC4854EE7A8C24134C747DE3211AC2BA26E0188C79 | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\_decimal.pyd | executable | |
MD5:8601C853146A4BE85238A57C9FD56865 | SHA256:2A57023D4F355E3857187C02577FA4641A4D1DFF195196B3C33B90322EDF9FD4 | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\_multiprocessing.pyd | executable | |
MD5:8901E96BB7A8EEAD994AF2BDF54A2447 | SHA256:823A96F080A3424F4C5327CF61FF517723E19A69679EBE93EA97061063D8D593 | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\_queue.pyd | executable | |
MD5:BC5FCE7B8DE6CA765CBF79F9D0587164 | SHA256:A5DB4D041F40FB01761B5BAA907099DB89CF891B0DF0251D92DA2FBF9DC3897B | |||
| 2900 | raid_tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI29002\_asyncio.pyd | executable | |
MD5:5435CE08F40FBE43230CAE8D3DFF232C | SHA256:79FDA30CBFC95DB2BA60646FF53DFF45B5ADD57C12241C4A82FA798CB3B543DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report