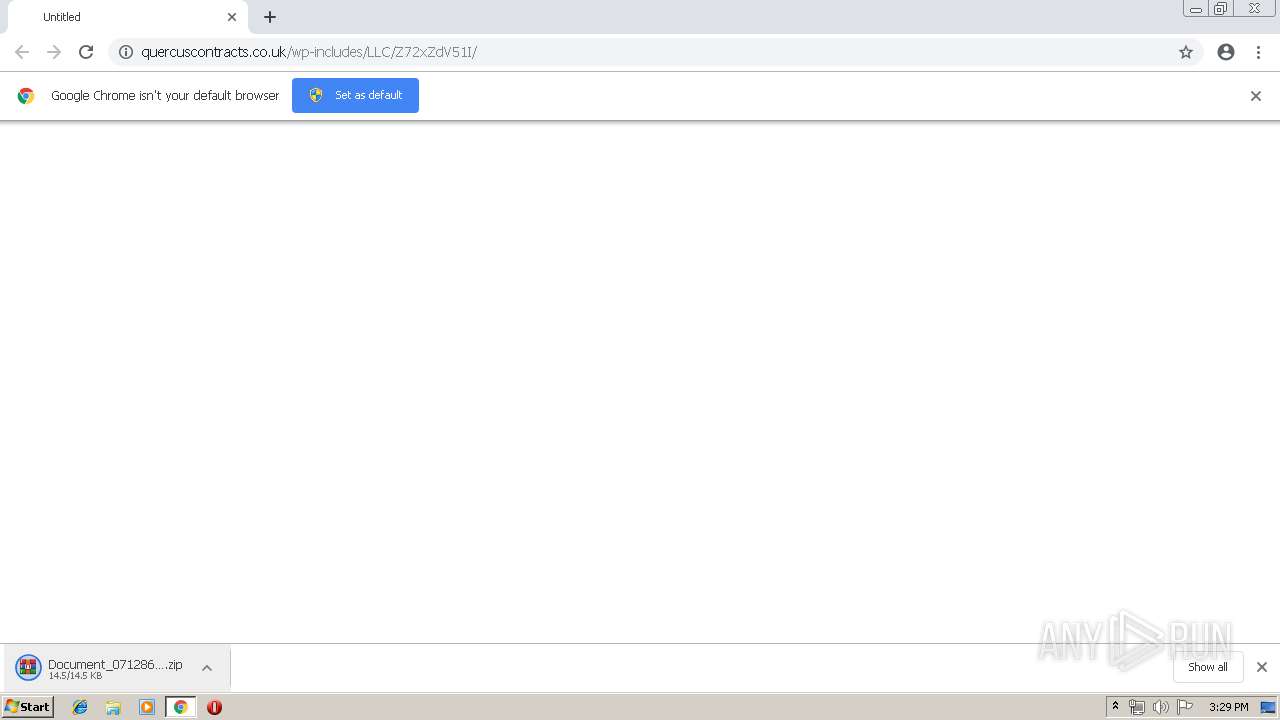
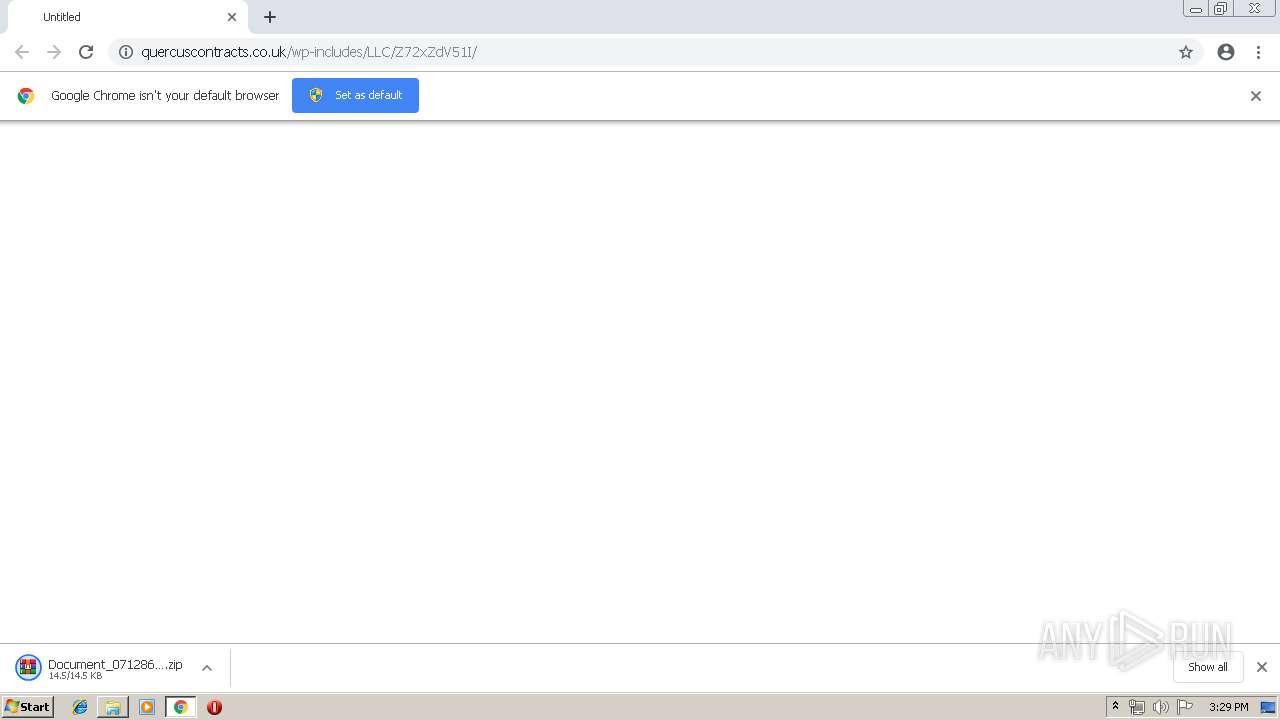
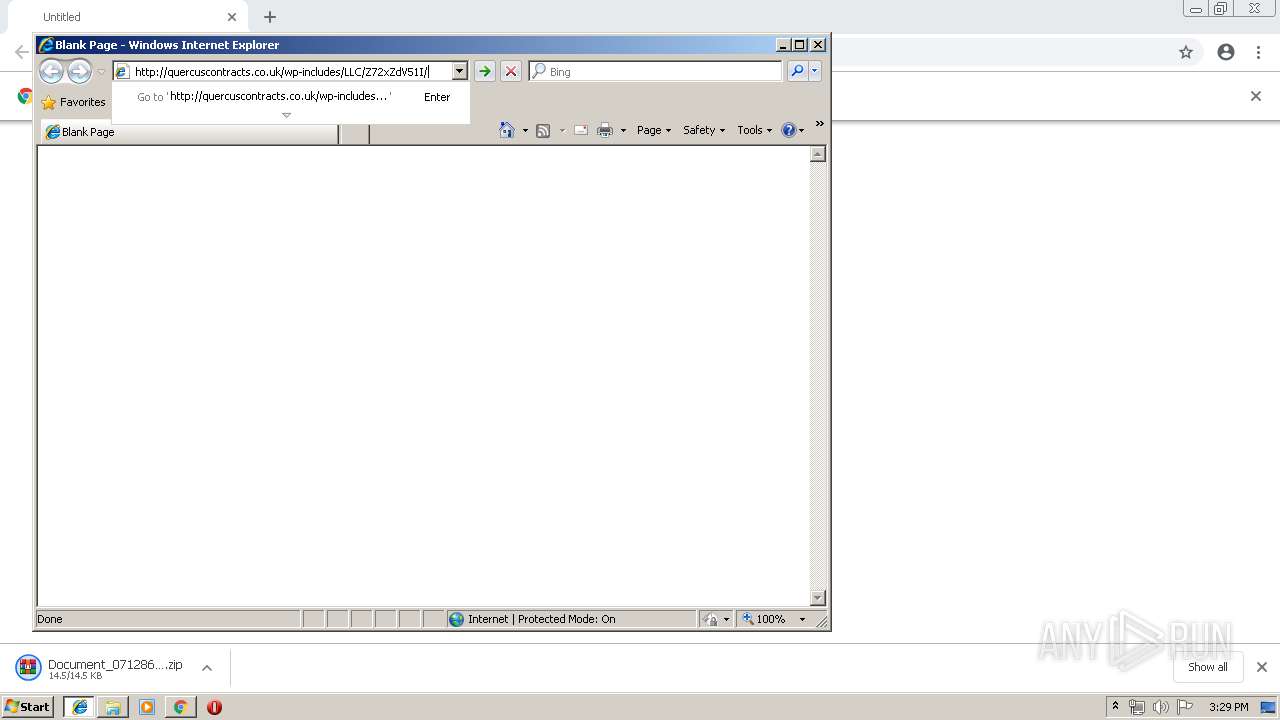
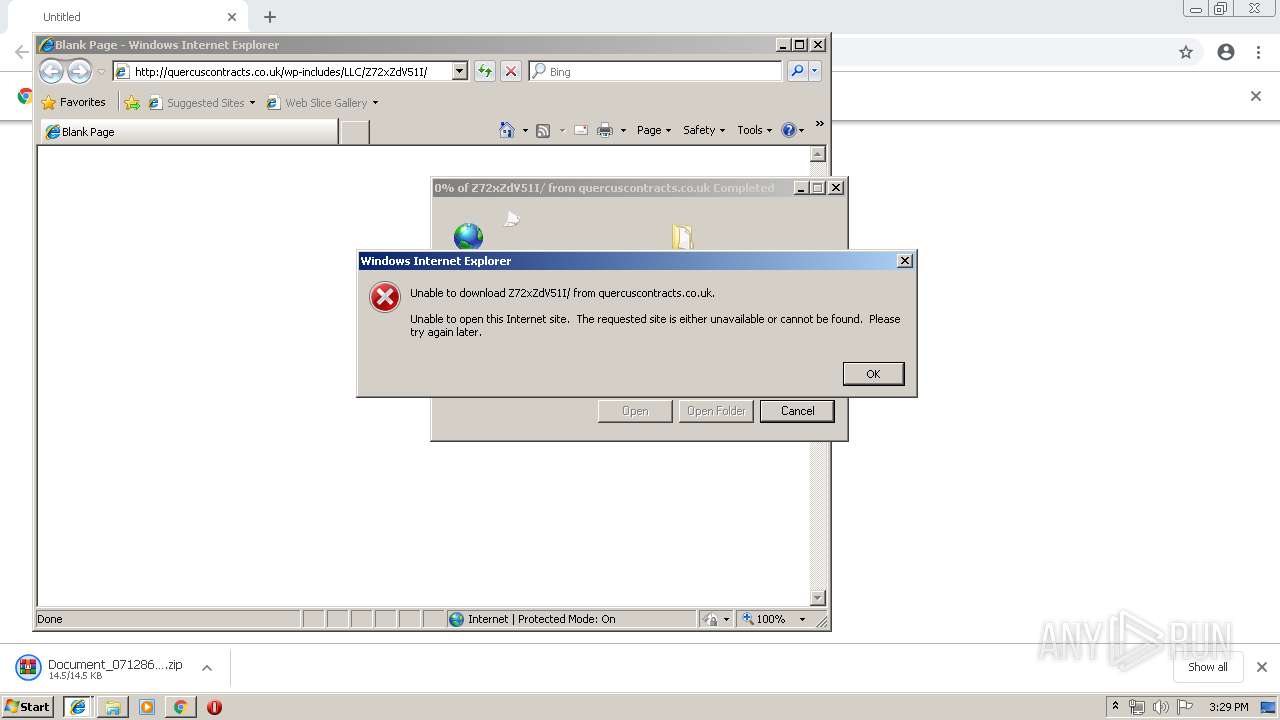
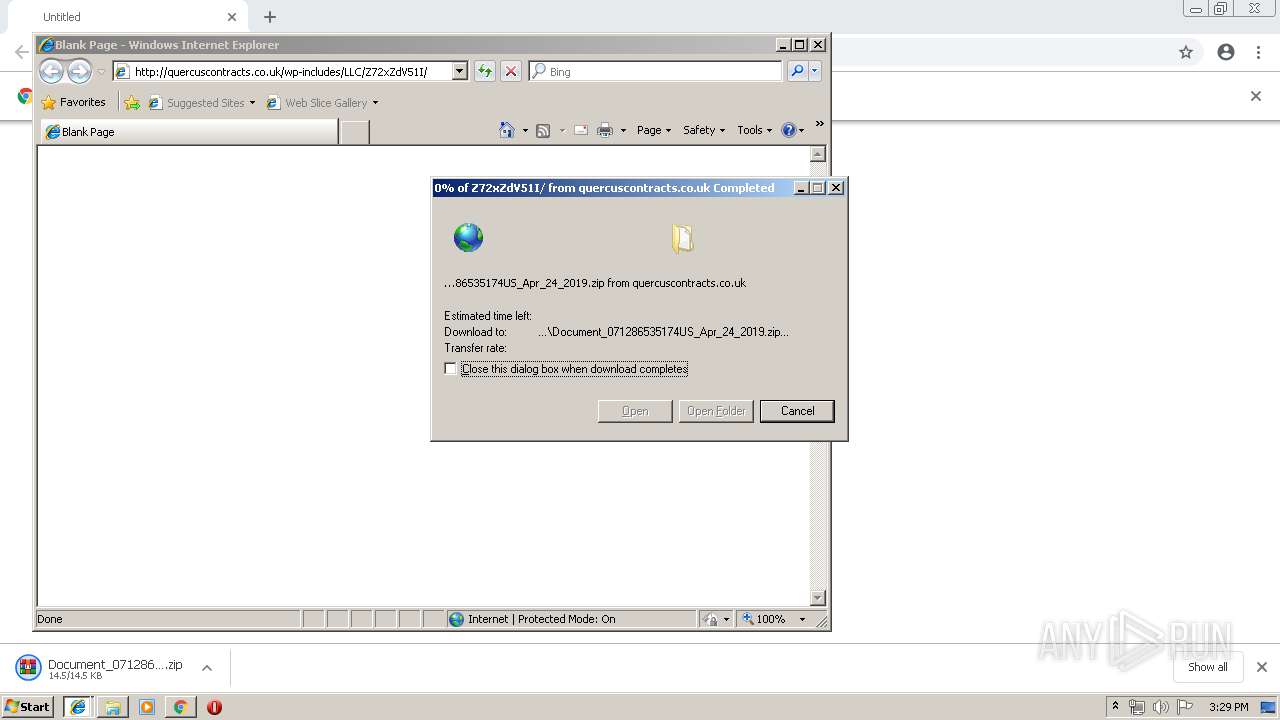
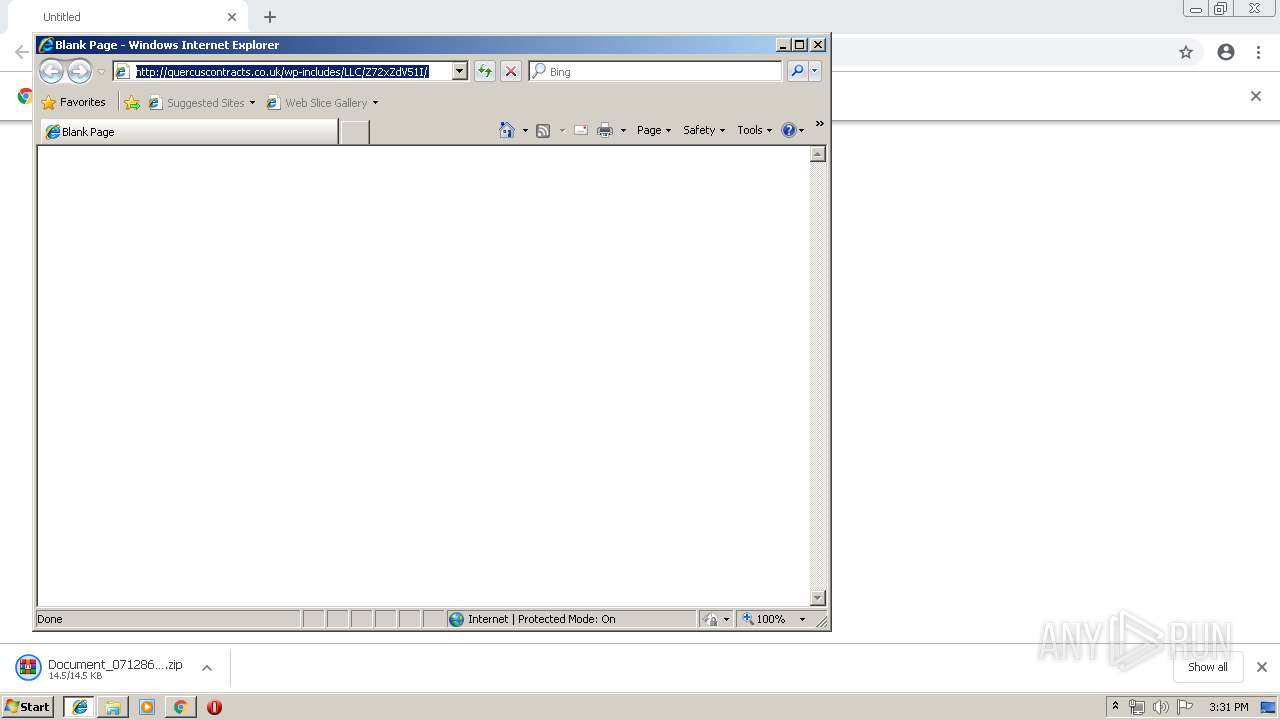
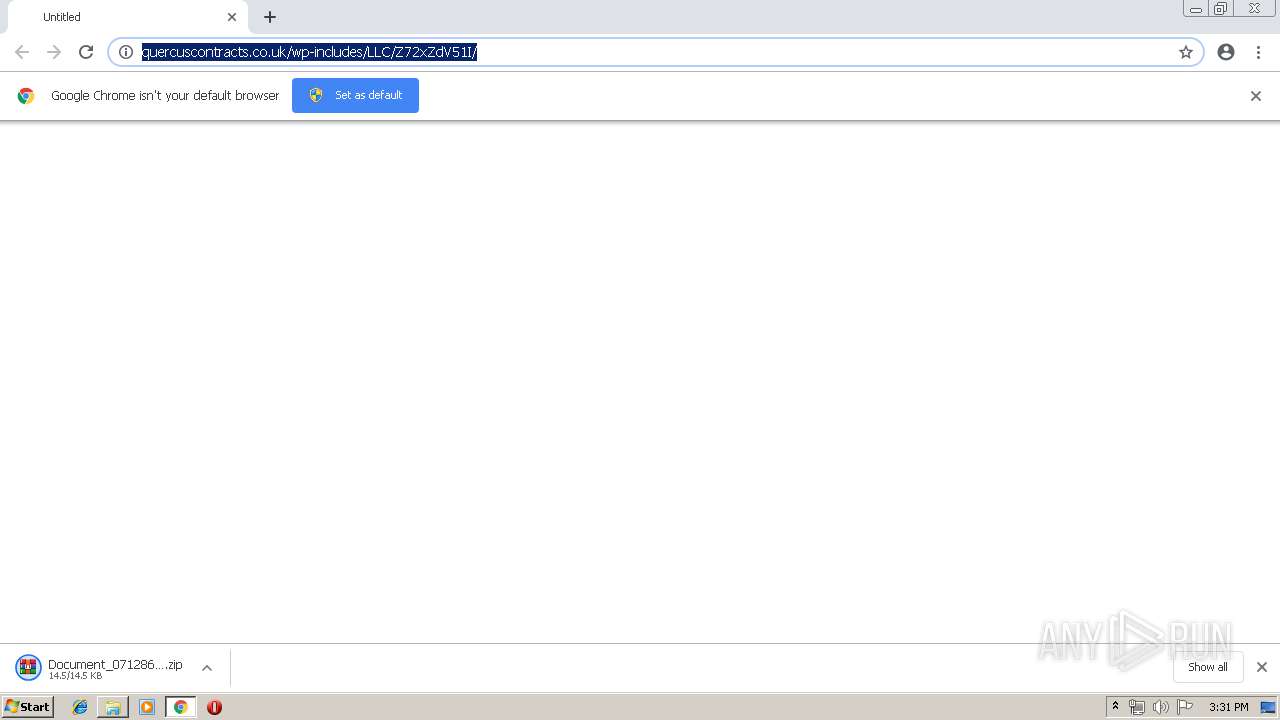
| URL: | http://quercuscontracts.co.uk/wp-includes/LLC/Z72xZdV51I/ |
| Full analysis: | https://app.any.run/tasks/e0b805f1-2fd2-471d-9bd6-d1500fe00401 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 25, 2019, 14:28:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 833887EADE3C86751F4E3EDDE6C8A0C1 |
| SHA1: | CB5525F26CE7C11154E5135F3CE8844F9929A054 |
| SHA256: | C7C9EB1A9A41F90A5B8845DA284523C7FC3FA39BA8BD0EBA080D9F388B80102F |
| SSDEEP: | 3:N1KPkQBEXEBZLQIVIMLGe273/SfaKn:Cs+QVdf73sBn |
MALICIOUS
Application was dropped or rewritten from another process
- p8au7elen.exe (PID: 2592)
- p8au7elen.exe (PID: 1260)
- soundser.exe (PID: 3876)
- GAHN.exe (PID: 116)
- soundser.exe (PID: 756)
- soundser.exe (PID: 2556)
- GAHN.exe (PID: 2760)
- soundser.exe (PID: 2580)
Emotet process was detected
- soundser.exe (PID: 3876)
- soundser.exe (PID: 2556)
Changes settings of System certificates
- WScript.exe (PID: 1020)
EMOTET was detected
- soundser.exe (PID: 756)
- soundser.exe (PID: 2580)
Connects to CnC server
- soundser.exe (PID: 756)
- soundser.exe (PID: 2580)
Changes the autorun value in the registry
- soundser.exe (PID: 756)
SUSPICIOUS
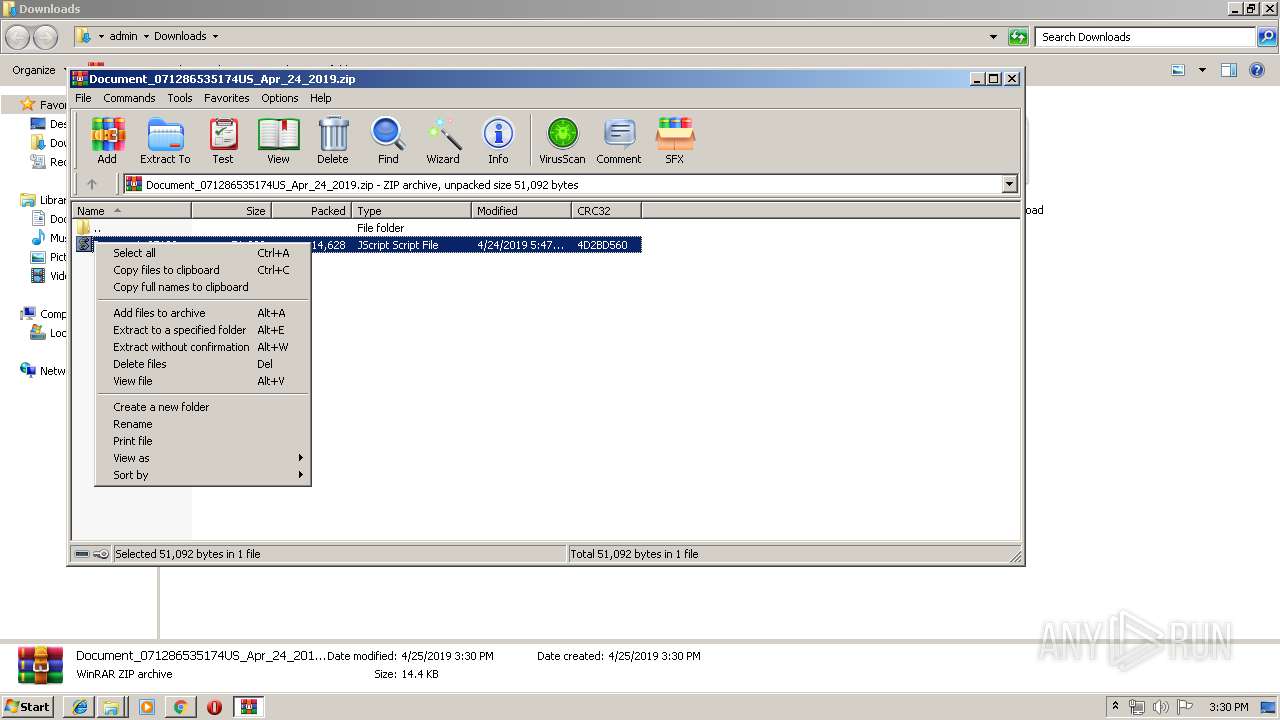
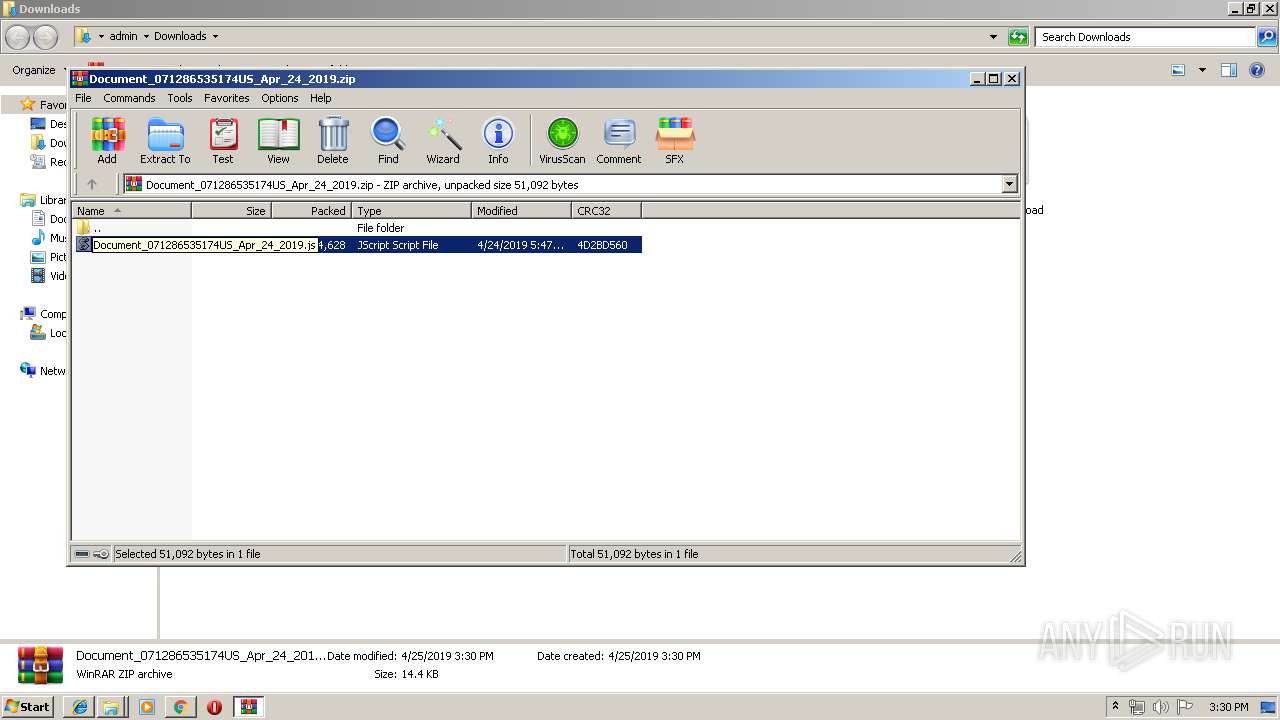
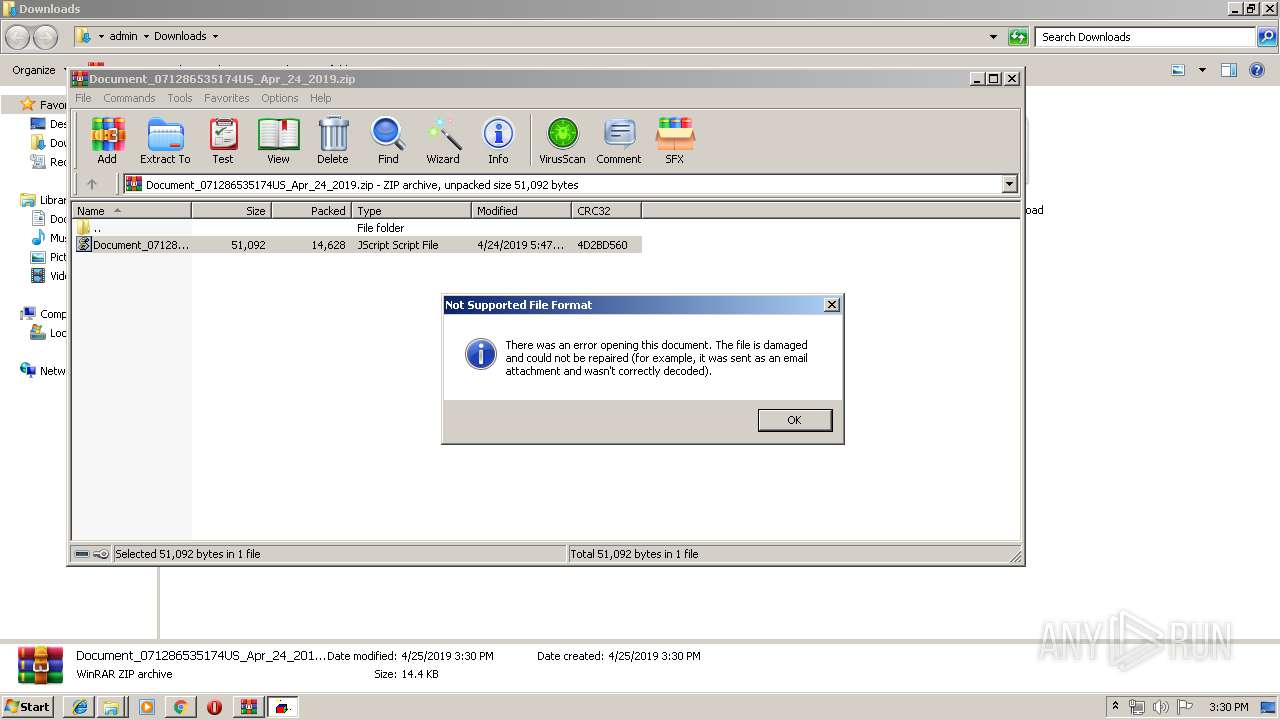
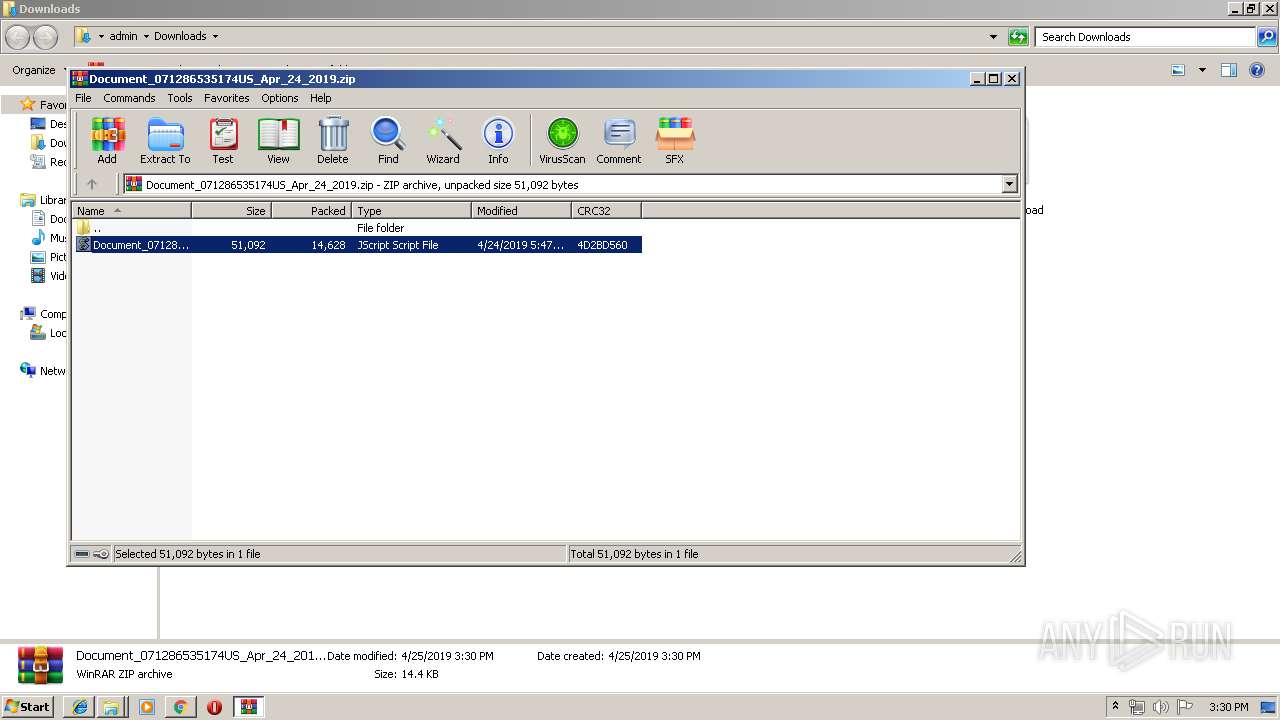
Executes scripts
- WinRAR.exe (PID: 2412)
Executable content was dropped or overwritten
- WScript.exe (PID: 1020)
- p8au7elen.exe (PID: 1260)
- soundser.exe (PID: 756)
- GAHN.exe (PID: 2760)
Creates files in the user directory
- WScript.exe (PID: 1020)
Application launched itself
- p8au7elen.exe (PID: 2592)
- soundser.exe (PID: 3876)
- GAHN.exe (PID: 116)
Starts itself from another location
- p8au7elen.exe (PID: 1260)
- GAHN.exe (PID: 2760)
Connects to server without host name
- soundser.exe (PID: 756)
- soundser.exe (PID: 2580)
Adds / modifies Windows certificates
- WScript.exe (PID: 1020)
INFO
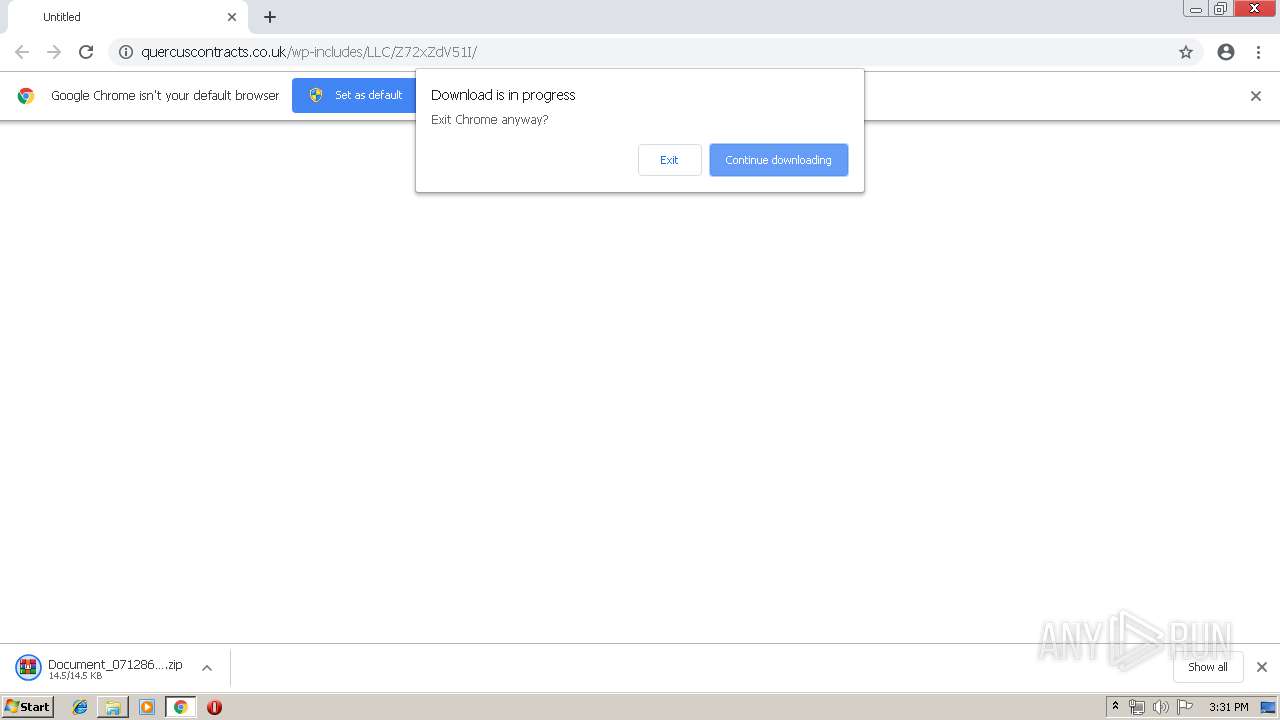
Application launched itself
- chrome.exe (PID: 3860)
Creates files in the user directory
- iexplore.exe (PID: 2228)
- iexplore.exe (PID: 2188)
Reads internet explorer settings
- iexplore.exe (PID: 2228)
Changes internet zones settings
- iexplore.exe (PID: 2188)
Reads Internet Cache Settings
- iexplore.exe (PID: 2228)
- iexplore.exe (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
23
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\soundser\GAHN.exe" | C:\Users\admin\AppData\Local\soundser\GAHN.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=936,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7121573323456087626 --mojo-platform-channel-handle=3616 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16815772926620672048 --mojo-platform-channel-handle=468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=936,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13573518157503743225 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --service-pipe-token=7470578327680934334 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7470578327680934334 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 756 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
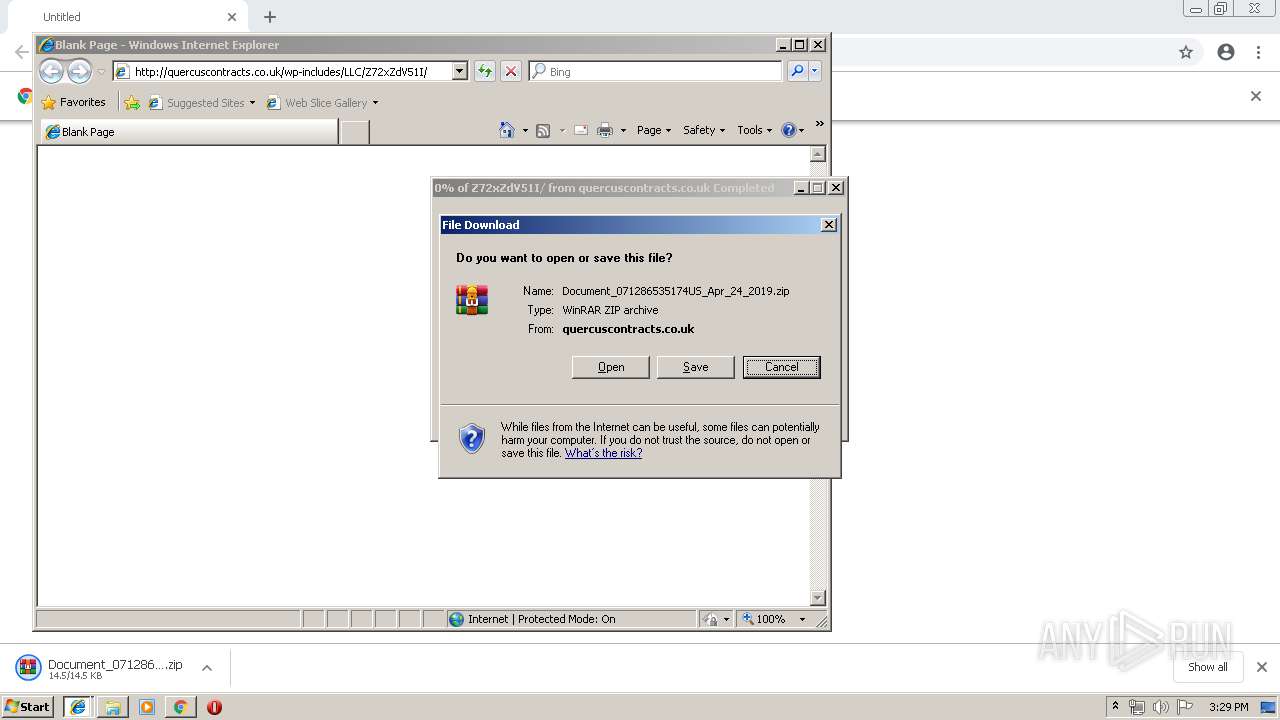
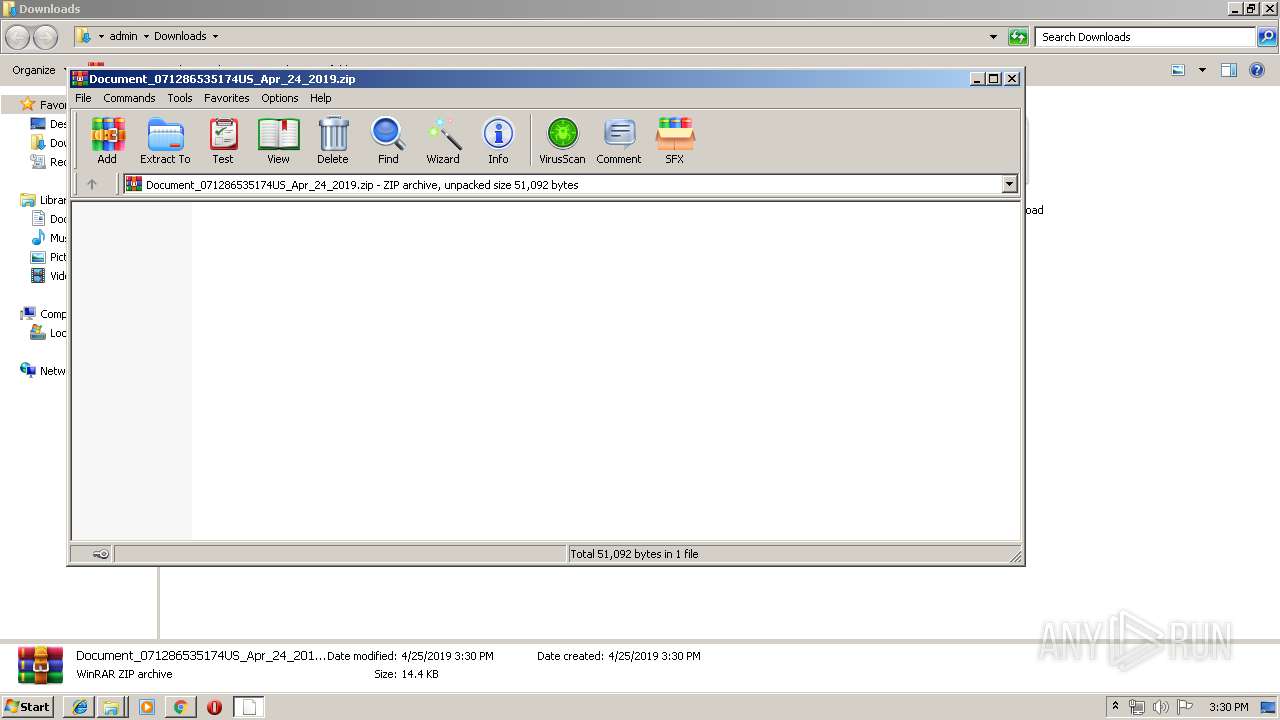
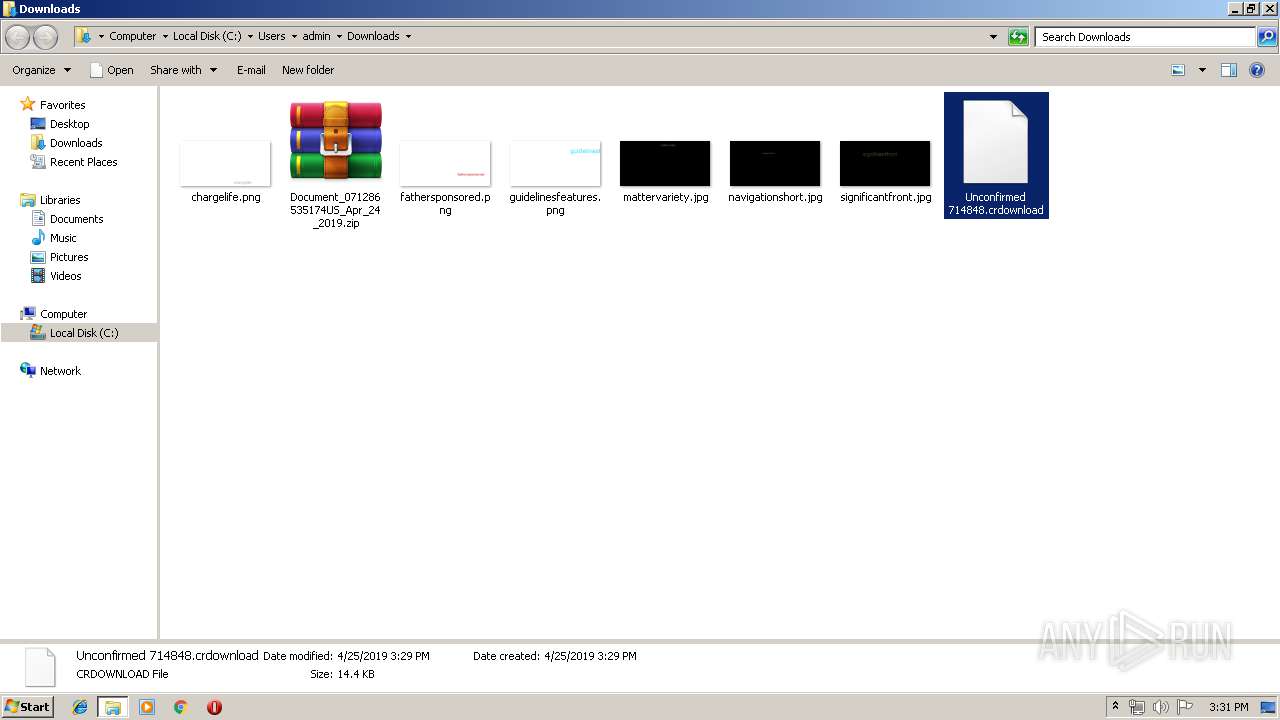
| 1020 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2412.11568\Document_071286535174US_Apr_24_2019.js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1260 | --cb8cab0f | C:\Users\admin\AppData\Local\Temp\p8au7elen.exe | p8au7elen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10767686924225834321 --mojo-platform-channel-handle=2084 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 494
Read events
2 237
Write events
248
Delete events
9
Modification events
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3860-13200676146653500 |
Value: 259 | |||
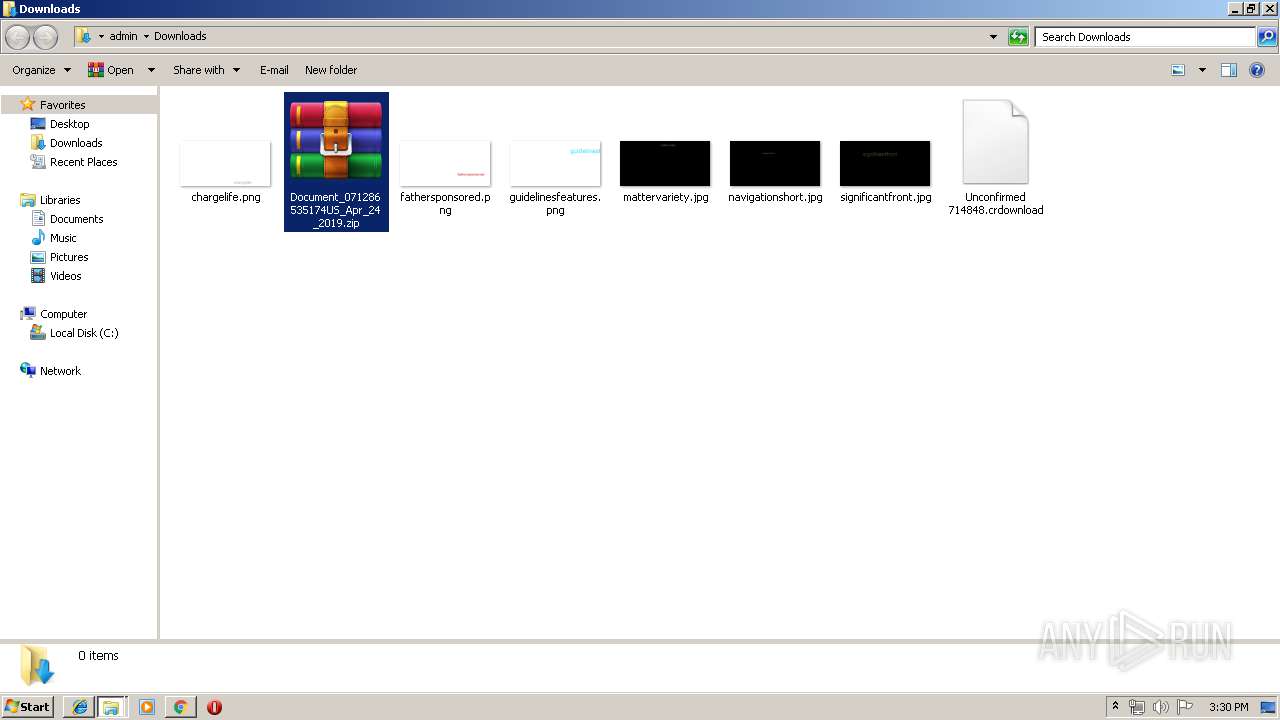
Executable files
4
Suspicious files
38
Text files
95
Unknown types
12
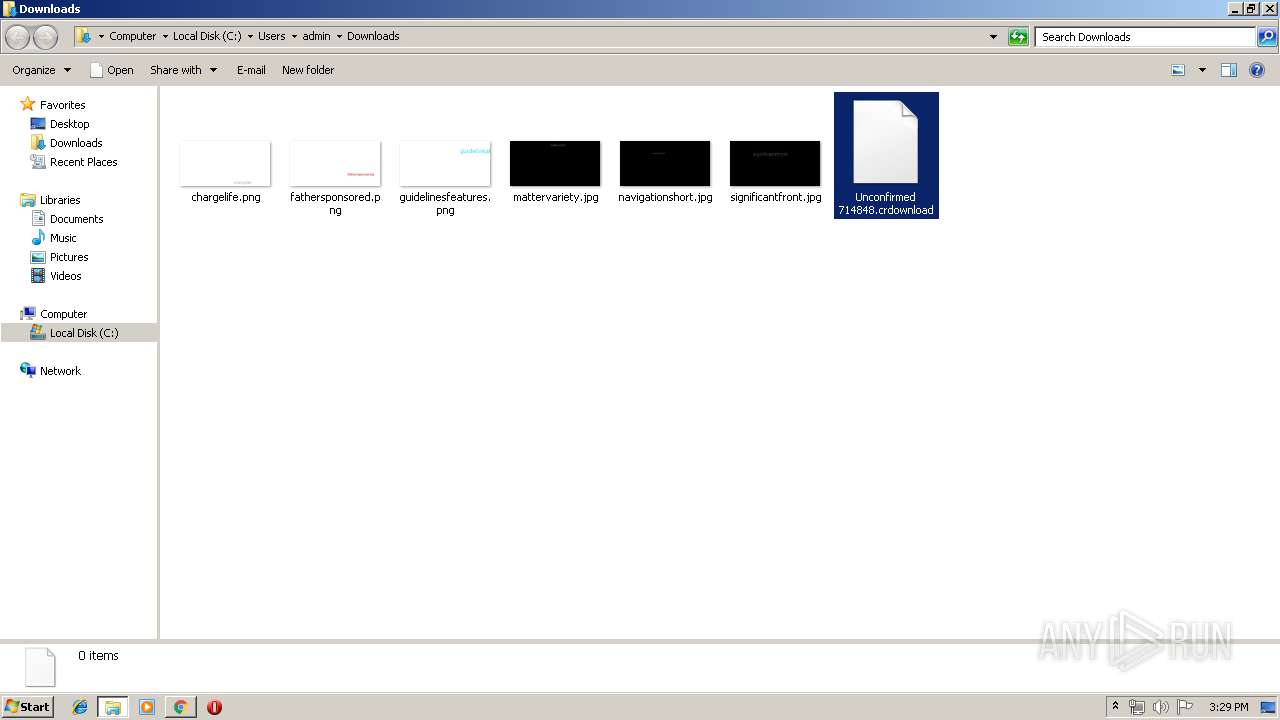
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\069b713f-9e5f-4d7f-a5ec-b42eb23f926e.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
23
DNS requests
13
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3860 | chrome.exe | GET | 200 | 50.87.151.200:80 | http://quercuscontracts.co.uk/wp-includes/LLC/Z72xZdV51I/ | US | compressed | 14.4 Kb | suspicious |
756 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/prov/badge/ | US | — | — | malicious |
2228 | iexplore.exe | GET | 200 | 50.87.151.200:80 | http://quercuscontracts.co.uk/wp-includes/LLC/Z72xZdV51I/ | US | compressed | 14.4 Kb | suspicious |
2228 | iexplore.exe | GET | 200 | 50.87.151.200:80 | http://quercuscontracts.co.uk/wp-includes/LLC/Z72xZdV51I/ | US | compressed | 14.4 Kb | suspicious |
2188 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
756 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/loadan/ | US | — | — | malicious |
756 | soundser.exe | POST | 200 | 190.112.228.47:443 | http://190.112.228.47:443/enable/ | CW | binary | 72.2 Kb | malicious |
2580 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/vermont/guids/ringin/merge/ | US | — | — | malicious |
2580 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/symbols/ringin/ | US | — | — | malicious |
2580 | soundser.exe | POST | — | 190.112.228.47:443 | http://190.112.228.47:443/teapot/ | CW | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | chrome.exe | 50.87.151.200:80 | quercuscontracts.co.uk | Unified Layer | US | suspicious |
3860 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3860 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3860 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3860 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3860 | chrome.exe | 216.58.206.3:443 | www.google.es | Google Inc. | US | whitelisted |
2188 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3860 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2228 | iexplore.exe | 50.87.151.200:80 | quercuscontracts.co.uk | Unified Layer | US | suspicious |
1020 | WScript.exe | 162.222.226.140:443 | continentalleap.com | PDR | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
quercuscontracts.co.uk |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.es |
| whitelisted |
www.bing.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
continentalleap.com |
| malicious |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2228 | iexplore.exe | Misc activity | ET INFO SUSPICIOUS Single JS file inside of ZIP Download (Observed as lure in malspam campaigns) |
3860 | chrome.exe | Misc activity | ET INFO SUSPICIOUS Single JS file inside of ZIP Download (Observed as lure in malspam campaigns) |
2228 | iexplore.exe | Misc activity | ET INFO SUSPICIOUS Single JS file inside of ZIP Download (Observed as lure in malspam campaigns) |
756 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
756 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
756 | soundser.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
756 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 11 |
756 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
756 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2580 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
17 ETPRO signatures available at the full report