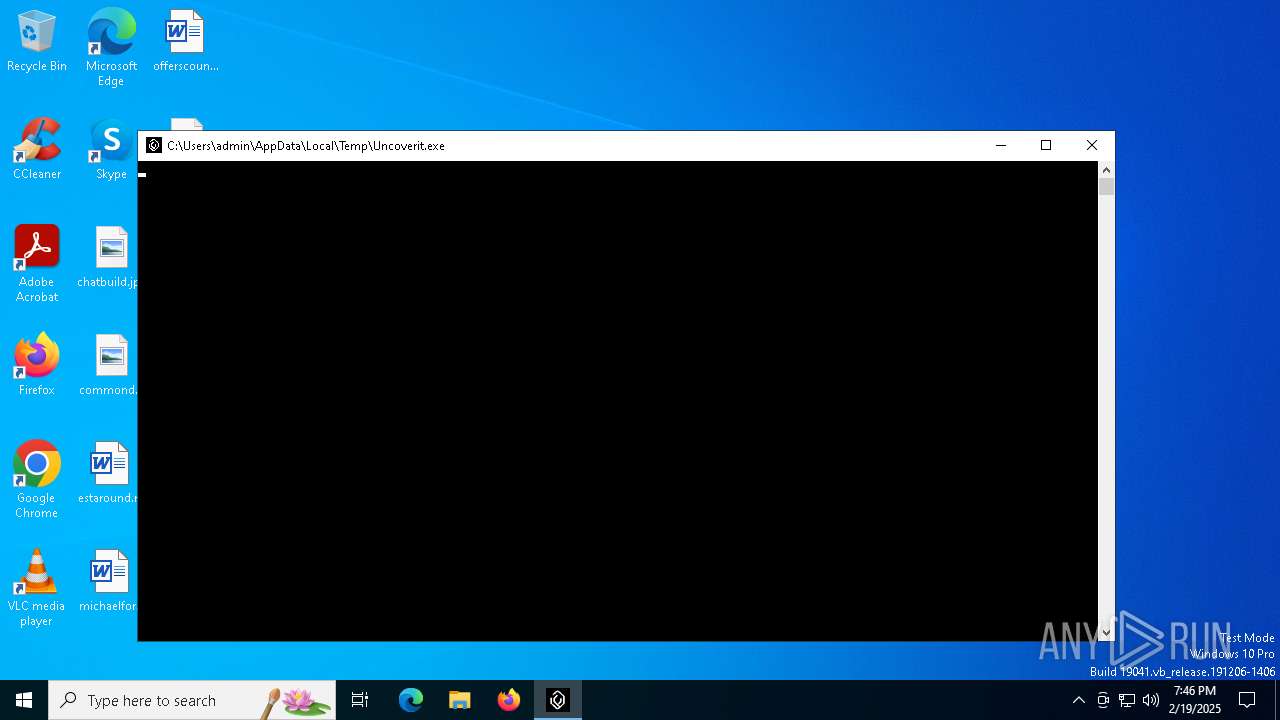
| File name: | Uncoverit.exe |
| Full analysis: | https://app.any.run/tasks/abb5a0ad-2828-4201-9108-b7073d0e32a1 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2025, 19:46:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | B935ED0823B3E9A1A95278CC1C0DDFB9 |
| SHA1: | 9B78FE7A8F402776982672837039B1BD993037BF |
| SHA256: | C7BCDAE60A83CC39B9A428E30C7BFA6F910723C3F74E2B35D86BE8B188AEB2D0 |
| SSDEEP: | 24576:kMmepZ8529twFYDhh7Q8ainNIBdhN/IOTx:J/elFYDhh7Q8ainNIBdhuO |
MALICIOUS
Adds extension to the Windows Defender exclusion list
- Uncoverit.exe (PID: 6236)
- cmd.exe (PID: 6440)
Changes the autorun value in the registry
- Uncoverit.exe (PID: 6236)
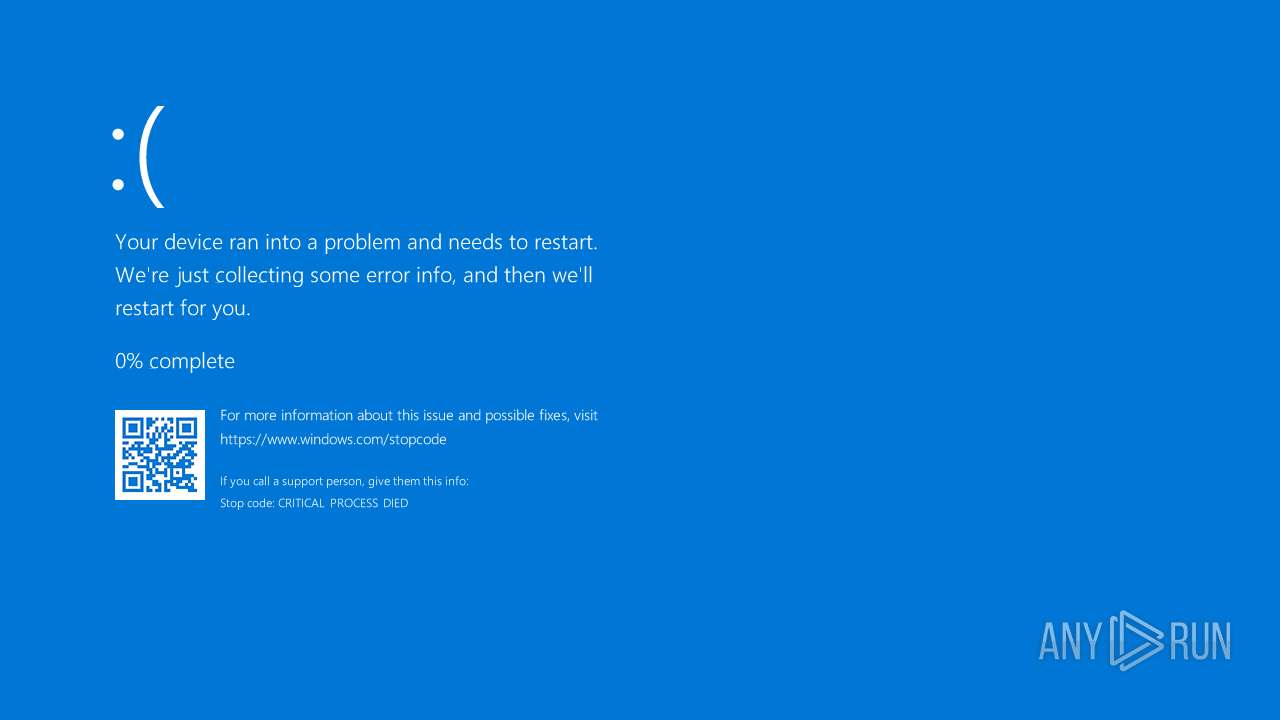
Deletes shadow copies
- cmd.exe (PID: 7092)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Uncoverit.exe (PID: 6236)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 6440)
Reads security settings of Internet Explorer
- Uncoverit.exe (PID: 6236)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6440)
Script adds exclusion extension to Windows Defender
- cmd.exe (PID: 6440)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6440)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6536)
Executing commands from a ".bat" file
- Uncoverit.exe (PID: 6236)
Found strings related to reading or modifying Windows Defender settings
- Uncoverit.exe (PID: 6236)
Executable content was dropped or overwritten
- Uncoverit.exe (PID: 6236)
INFO
Reads the computer name
- Uncoverit.exe (PID: 6236)
Reads the machine GUID from the registry
- Uncoverit.exe (PID: 6236)
Creates files or folders in the user directory
- Uncoverit.exe (PID: 6236)
Process checks computer location settings
- Uncoverit.exe (PID: 6236)
Checks supported languages
- Uncoverit.exe (PID: 6236)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5392)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:02:19 19:43:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 784896 |
| InitializedDataSize: | 13824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc186e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.3 |
| ProductVersionNumber: | 1.0.0.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Discord.gg/uncoverit |
| CompanyName: | Discord.gg/uncoverit |
| FileDescription: | Discord.gg/uncoverit |
| FileVersion: | 1.0.0.3 |
| InternalName: | ConsoleApp2.exe |
| LegalCopyright: | Discord.gg/uncoverit |
| LegalTrademarks: | Discord.gg/uncoverit |
| OriginalFileName: | ConsoleApp2.exe |
| ProductName: | Discord.gg/uncoverit |
| ProductVersion: | 1.0.0.3 |
| AssemblyVersion: | 1.0.0.2 |
Total processes
189
Monitored processes
63
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | taskkill /F /IM GxVss* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | taskkill /F /IM GxCIMgr* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | taskkill /F /IM AcronisAgent* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | taskkill /F /IM GxBlr* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | taskkill /F /IM sql* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1916 | taskkill /F /IM YooIT* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2452 | taskkill /F /IM VeeamTransportSvc* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2972 | taskkill /F /IM svc$* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3840 | taskkill /F /IM backup* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3848 | taskkill /F /IM veeam* | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 190
Read events
13 187
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6236) Uncoverit.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | discord |
Value: C:\Users\admin\AppData\Local\discord.exe | |||
| (PID) Process: | (5004) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\System |
| Operation: | write | Name: | DisableCMD |
Value: 2 | |||
| (PID) Process: | (5892) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
Executable files
1
Suspicious files
2
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6236 | Uncoverit.exe | C:\Users\admin\AppData\Roaming\ID | text | |
MD5:A25D6DD6A9ABC8A203FBCE91595CDC49 | SHA256:8F1200E1137D047D05DB0158098EABA6997FD1BA9EDF6A7847D08D4B3B332C21 | |||
| 5392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ahqxirzj.144.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vu4lqqn1.pix.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5392 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5C345FF398B1443B56D8F6679DAE7AB3 | SHA256:2945542B1FC027A5C78C3AEBFF56458A57E857B2306ACBE66489D4C4F7DD5237 | |||
| 6236 | Uncoverit.exe | C:\Users\admin\AppData\Roaming\1.bat | text | |
MD5:DEA4A40E88C7D15D294266064679DF54 | SHA256:38AEAAD559D68C870B07F5D5E170E4A3A5B7B616B78D43EA2D4D7246FD60EA88 | |||
| 6236 | Uncoverit.exe | C:\Users\admin\AppData\Local\discord.exe | executable | |
MD5:B935ED0823B3E9A1A95278CC1C0DDFB9 | SHA256:C7BCDAE60A83CC39B9A428E30C7BFA6F910723C3F74E2B35D86BE8B188AEB2D0 | |||
| 6236 | Uncoverit.exe | C:\Users\admin\Pictures\imageBXORxi.CnJteueiFJvUeeVvOYthGcW.jpg | binary | |
MD5:18E059BE2BF807DFF8E9AD0571AFD4A7 | SHA256:ADE6FF4ABD6FC2CBA754A63ACA3841F2E8C09929454A25426944171E7D977519 | |||
| 5392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_glsylfbo.4hq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5eoio2wg.fri.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6236 | Uncoverit.exe | C:\Users\admin\AppData\Roaming\fondo_antiguo.jpg | image | |
MD5:55EFEF5901C13B31AEB3C93B4D92B382 | SHA256:A63ED4CF89181233746C694BD4C0FFE697C7FC137BE8A0387671E49B725D3D7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
904 | svchost.exe | GET | 200 | 23.48.23.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
904 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5856 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
904 | svchost.exe | 23.48.23.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
904 | svchost.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
904 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |