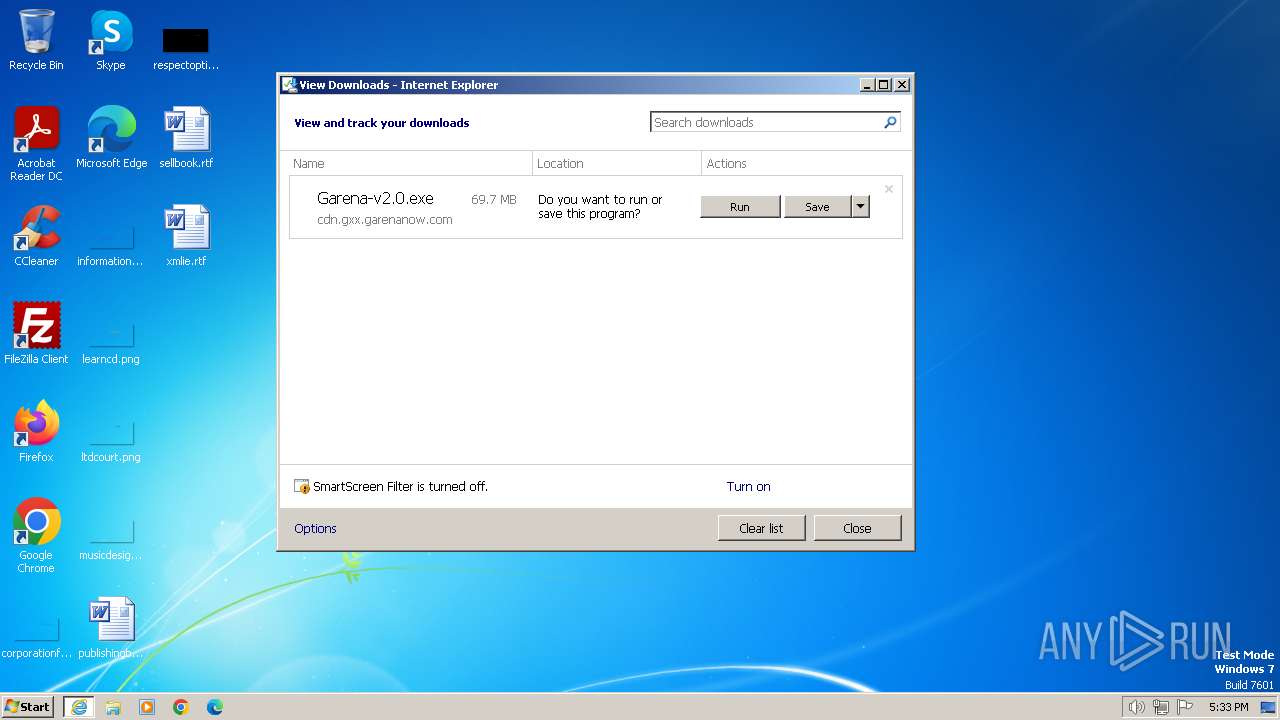
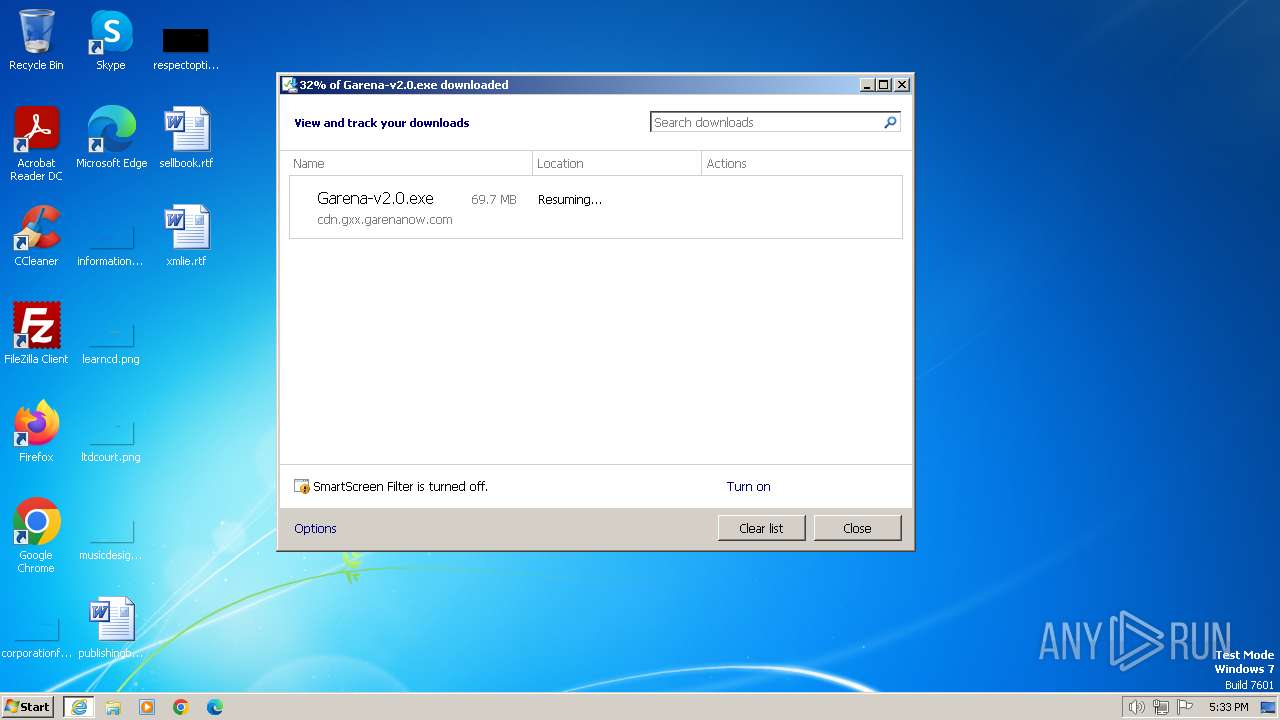
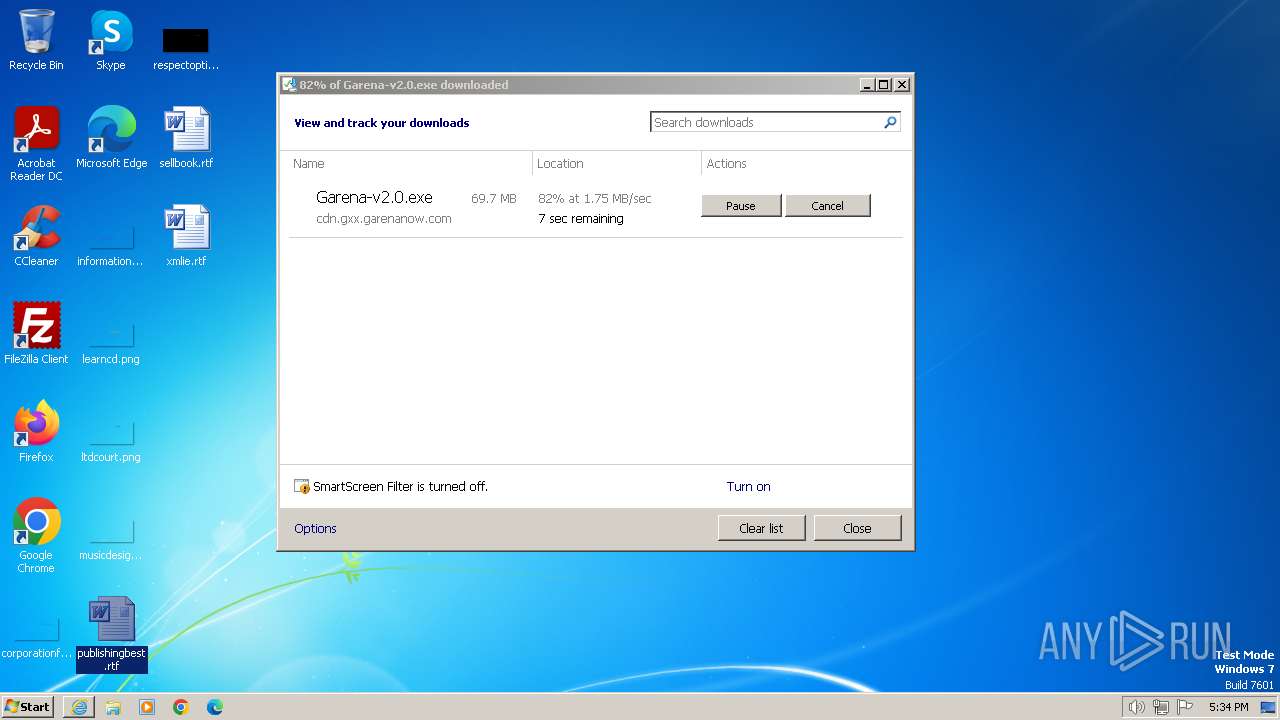
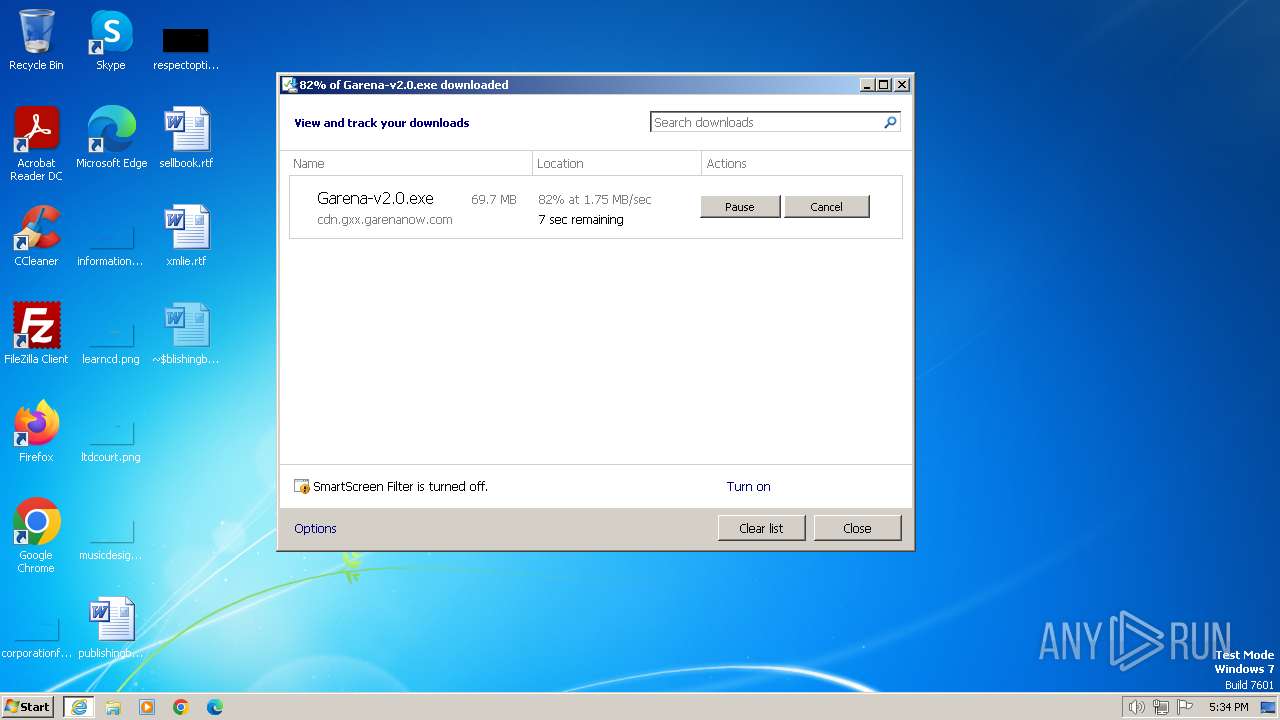
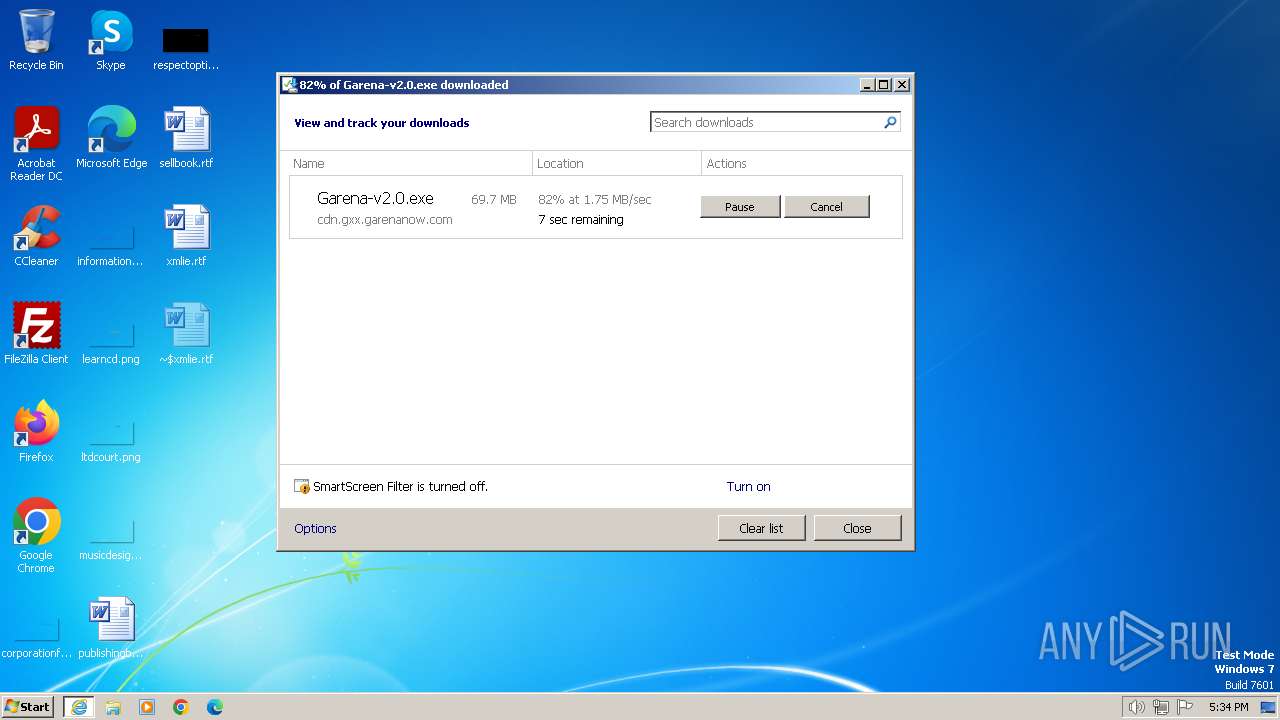
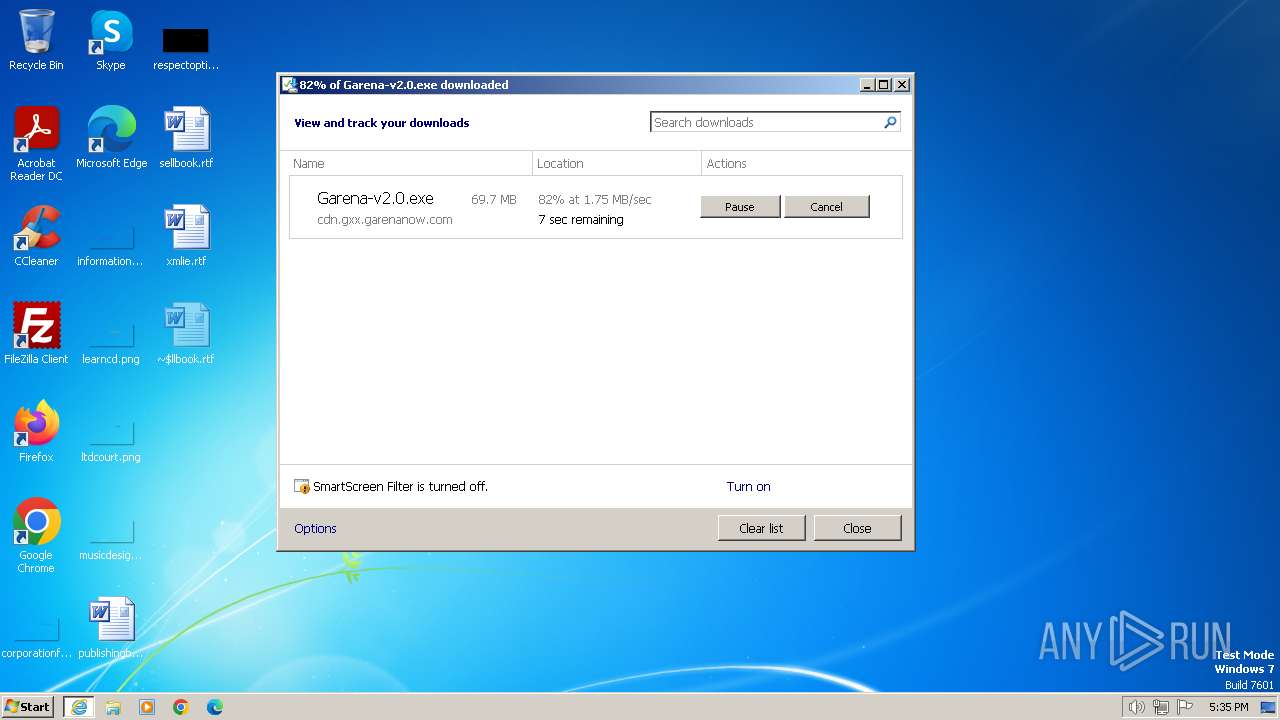
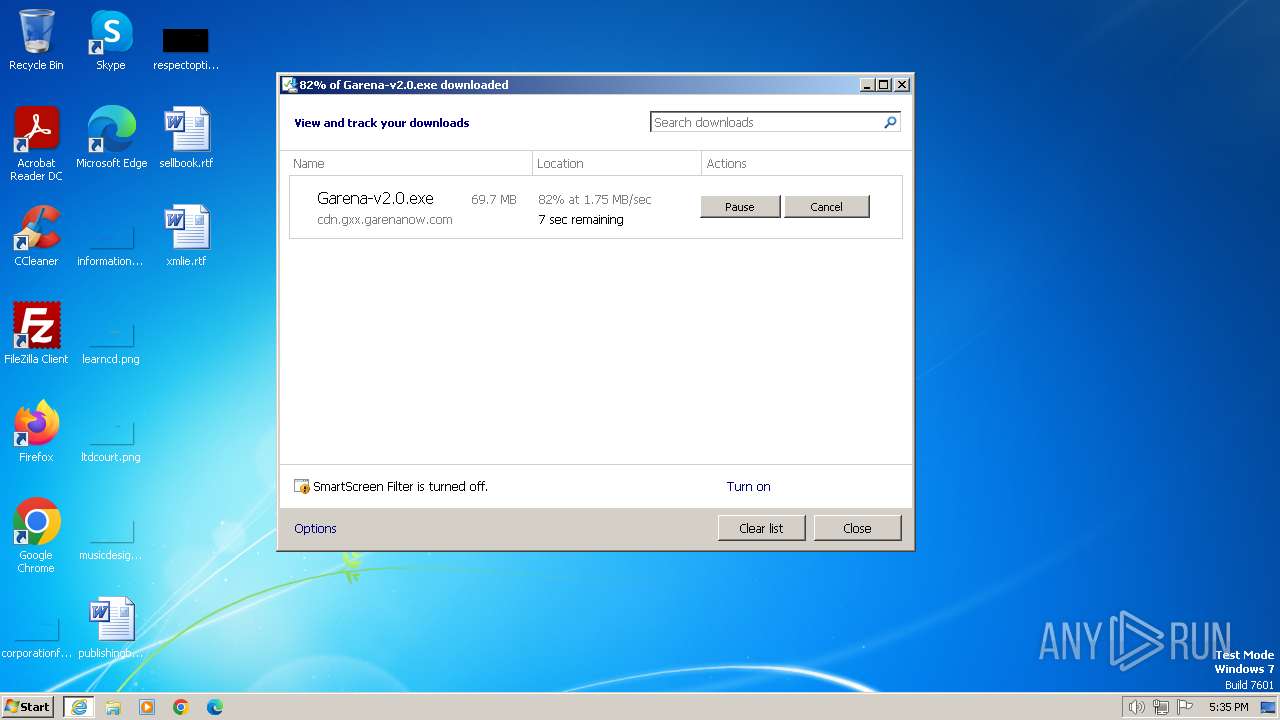
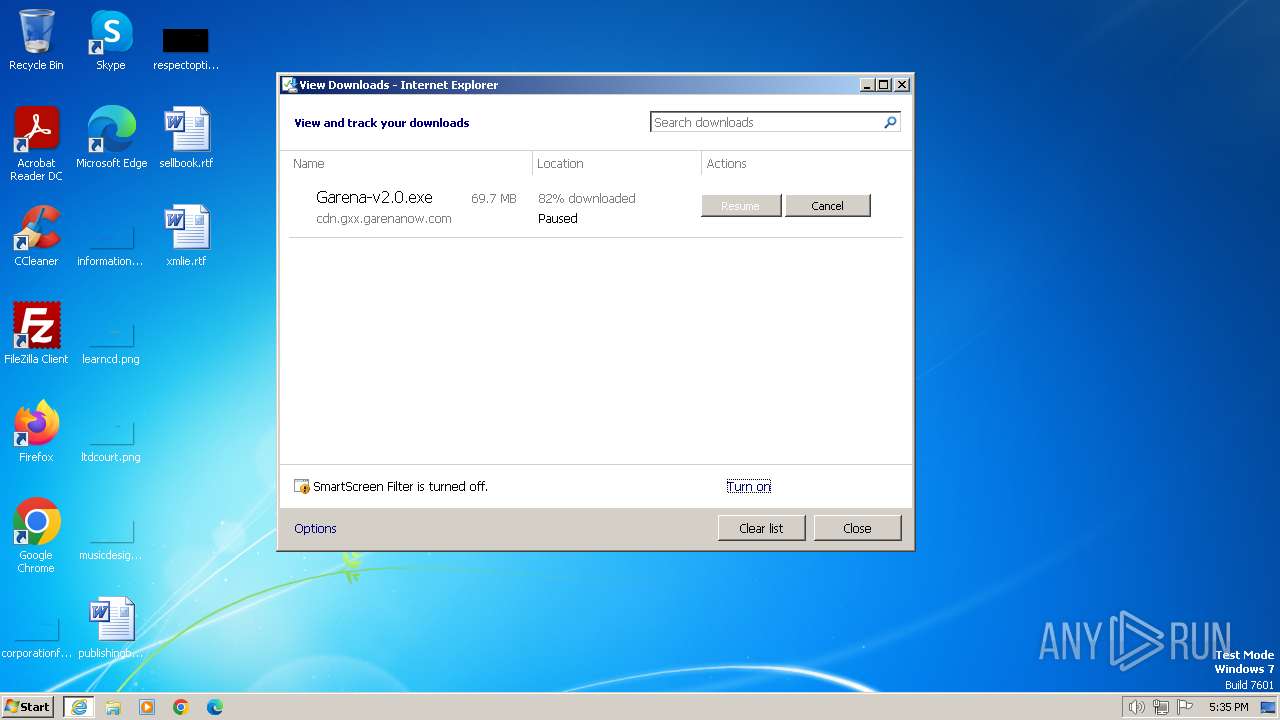
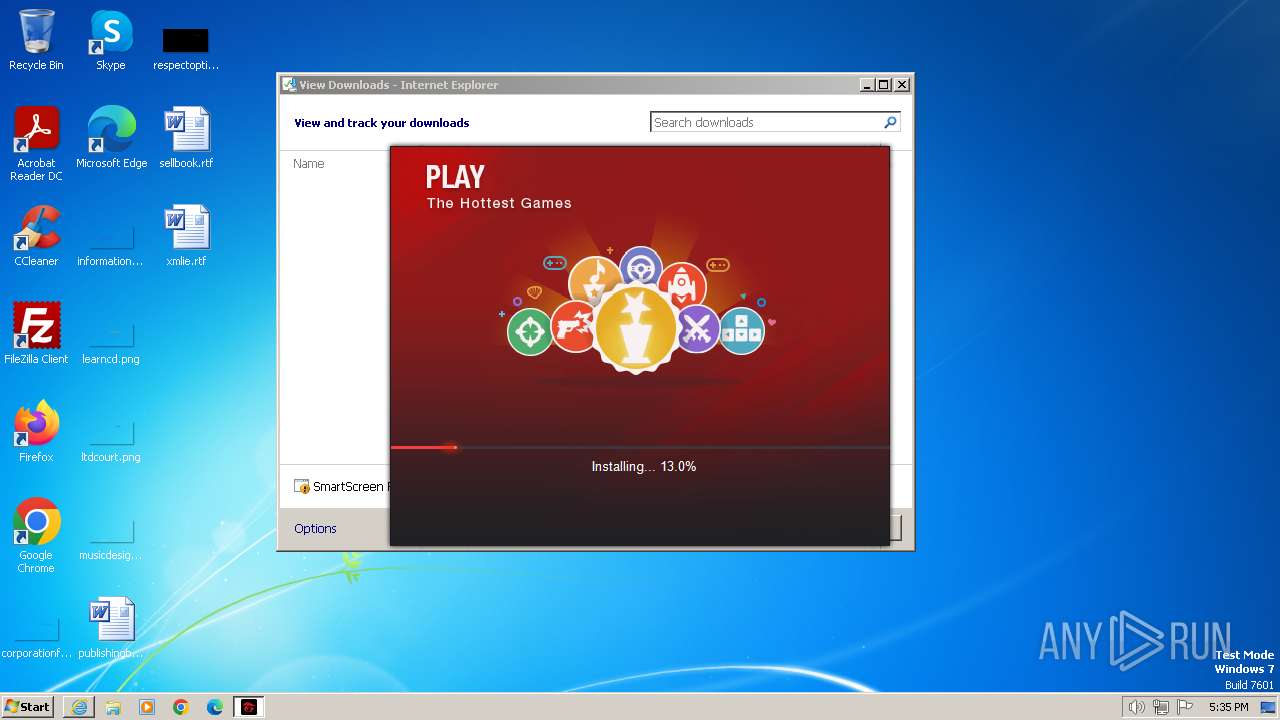
| URL: | https://cdn.gxx.garenanow.com/gxx/pc/installer/Garena-v2.0.exe |
| Full analysis: | https://app.any.run/tasks/5efd5df1-bfb2-41ad-80f0-4458f00b9b57 |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2024, 17:32:57 |
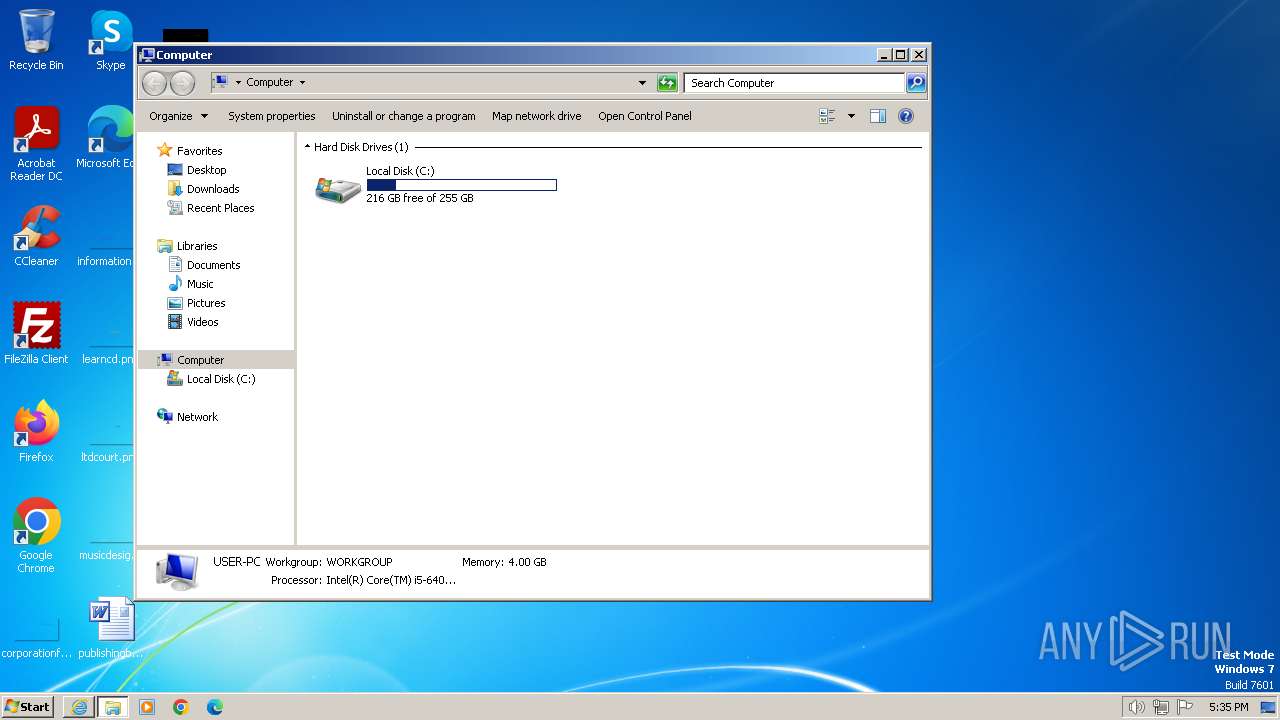
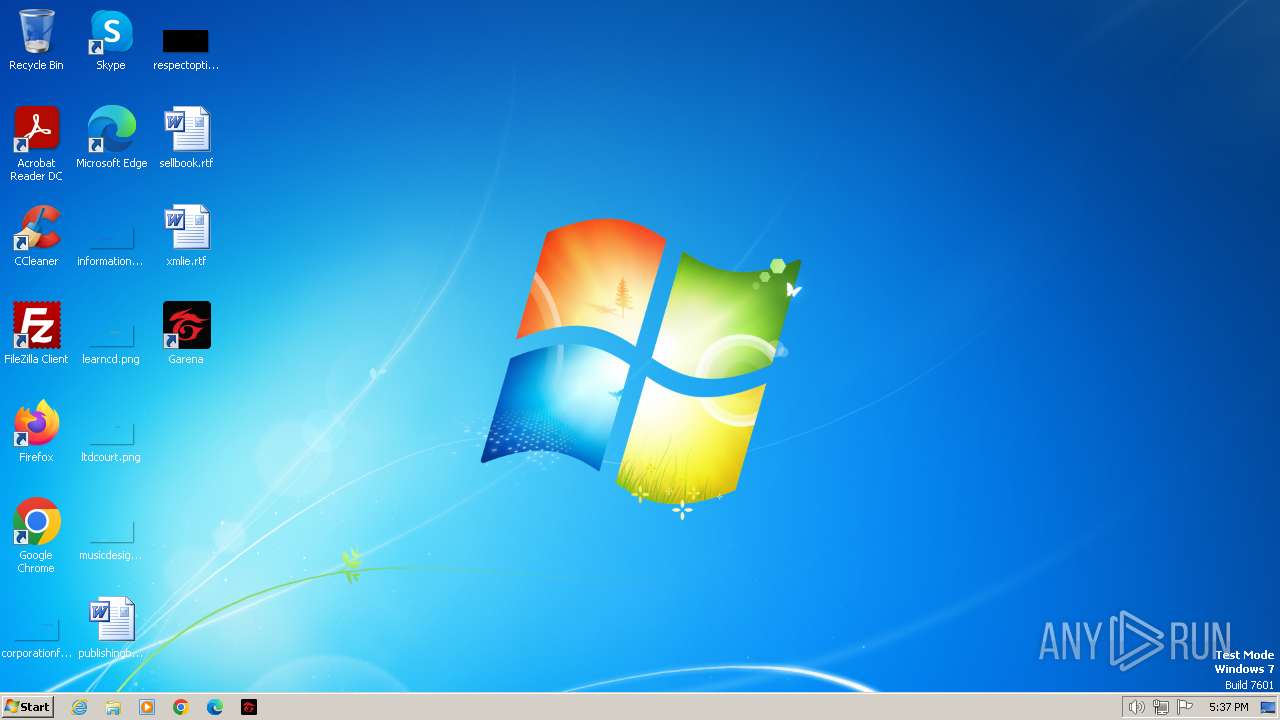
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BB99ACD2A33C4635E65F3CCAD6057855 |
| SHA1: | 9AA7C7FDA74AEF51178542D970E0854CA4FB1AB2 |
| SHA256: | C7AF7E2D5B054EBB047C35C630368A8FFBD7727958E9B69FEF53FABE7BE62D06 |
| SSDEEP: | 3:N8cGJHQYobyRgOXKQ9TXLhN:2cQHSGgOXrbhN |
MALICIOUS
Drops the executable file immediately after the start
- Garena-v2.0.exe (PID: 552)
SUSPICIOUS
The process creates files with name similar to system file names
- Garena-v2.0.exe (PID: 552)
Executable content was dropped or overwritten
- Garena-v2.0.exe (PID: 552)
Malware-specific behavior (creating "System.dll" in Temp)
- Garena-v2.0.exe (PID: 552)
Process drops legitimate windows executable
- Garena-v2.0.exe (PID: 552)
Executes as Windows Service
- gxxsvc.exe (PID: 392)
Creates a software uninstall entry
- Garena-v2.0.exe (PID: 552)
The process drops C-runtime libraries
- Garena-v2.0.exe (PID: 552)
INFO
Application launched itself
- iexplore.exe (PID: 3668)
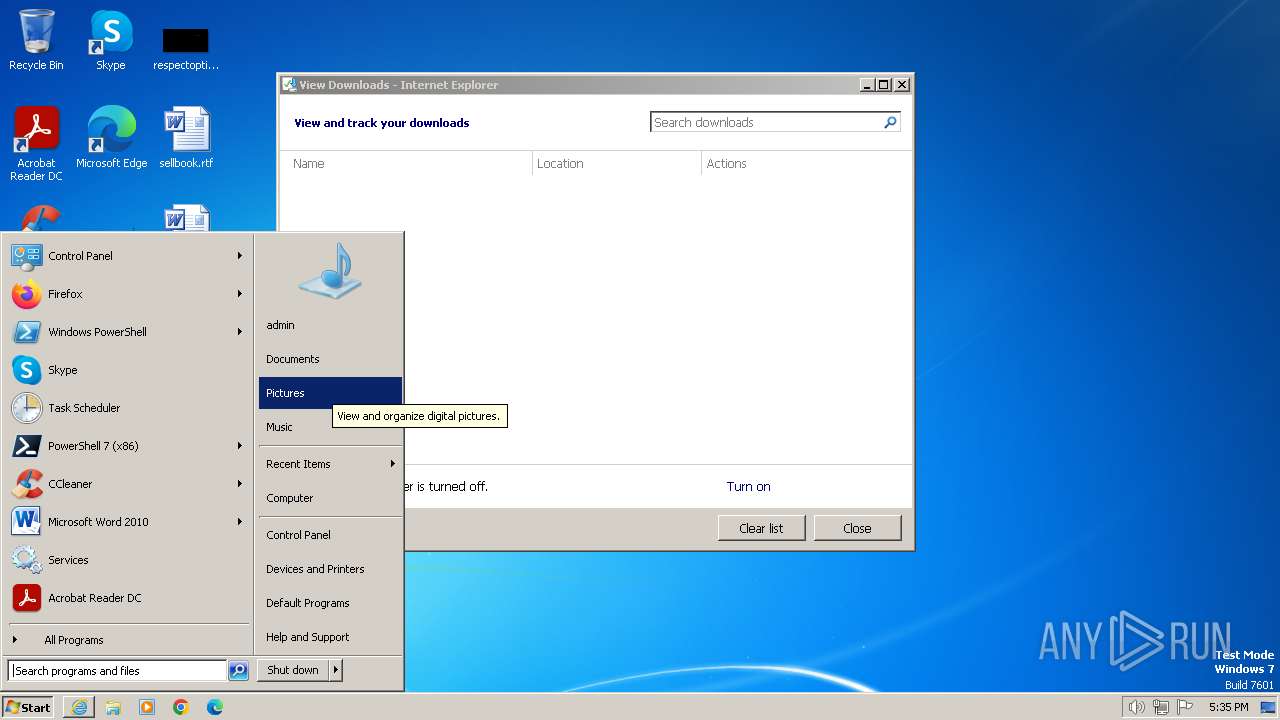
Modifies the phishing filter of IE
- iexplore.exe (PID: 3668)
Drops the executable file immediately after the start
- iexplore.exe (PID: 3348)
Checks supported languages
- Garena-v2.0.exe (PID: 552)
- gxxsvc.exe (PID: 2740)
- gxxsvc.exe (PID: 3768)
- gxxsvc.exe (PID: 392)
- Garena.exe (PID: 120)
Reads the computer name
- Garena-v2.0.exe (PID: 552)
- gxxsvc.exe (PID: 2740)
- gxxsvc.exe (PID: 392)
- gxxsvc.exe (PID: 3768)
- Garena.exe (PID: 120)
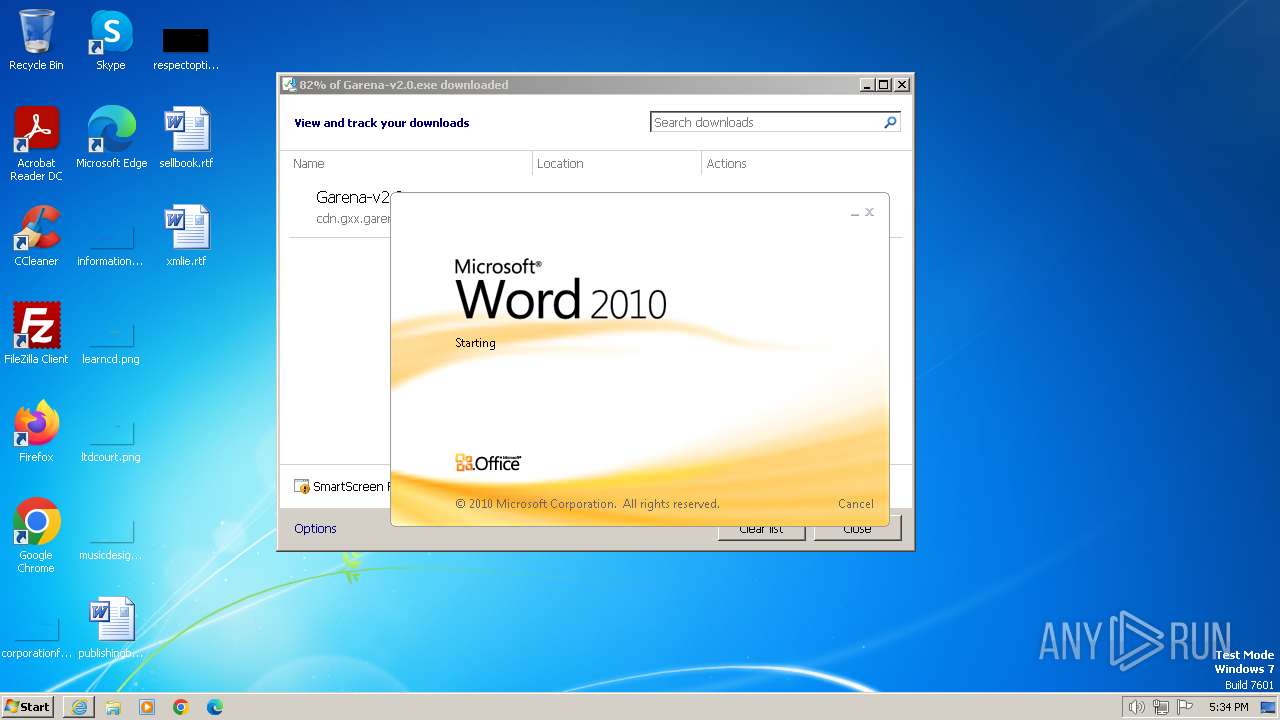
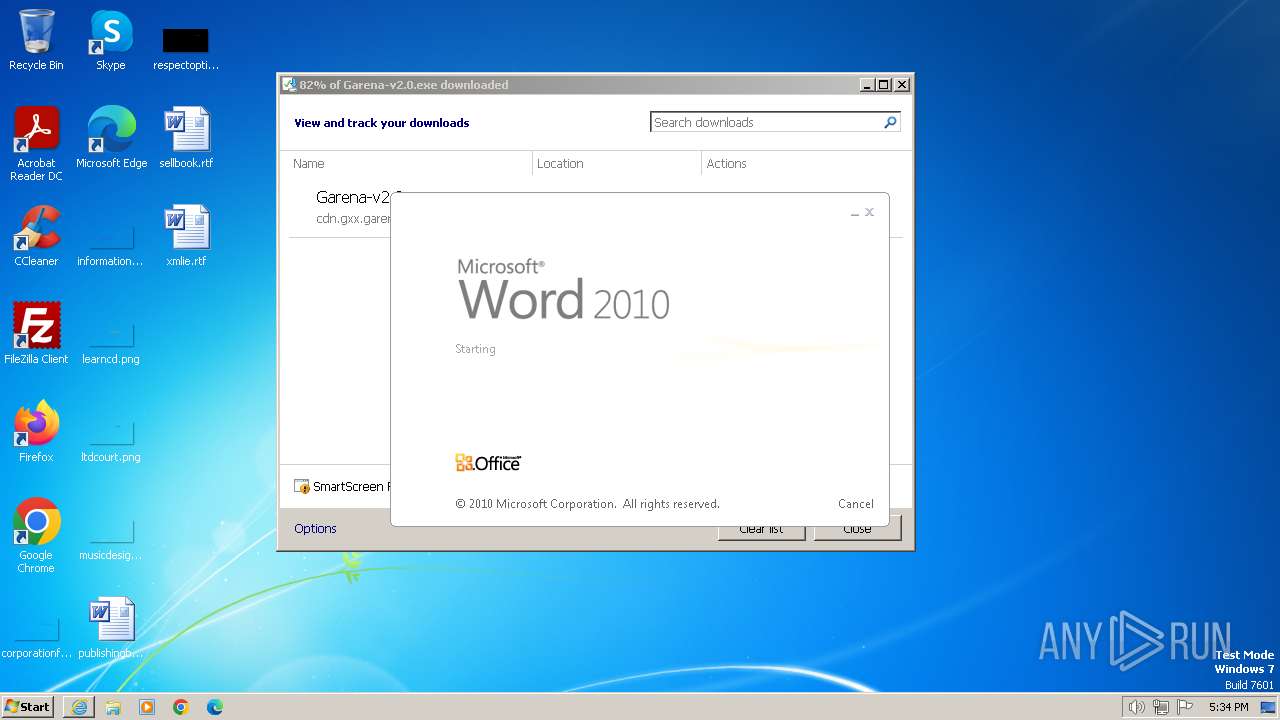
Manual execution by a user
- WINWORD.EXE (PID: 3072)
- WINWORD.EXE (PID: 2756)
- WINWORD.EXE (PID: 2240)
- Garena.exe (PID: 120)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3348)
The process uses the downloaded file
- iexplore.exe (PID: 3668)
Create files in a temporary directory
- Garena-v2.0.exe (PID: 552)
Creates files in the program directory
- Garena-v2.0.exe (PID: 552)
- gxxsvc.exe (PID: 2740)
- Garena.exe (PID: 120)
Reads the machine GUID from the registry
- Garena.exe (PID: 120)
- Garena-v2.0.exe (PID: 552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Garena\Garena\Garena.exe" -lang en -firstlaunch | C:\Program Files\Garena\Garena\Garena.exe | explorer.exe | ||||||||||||
User: admin Company: Garena Online Integrity Level: MEDIUM Description: Garena Platform Exit code: 0 Version: 2019.09.26.1823 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Garena\Garena\2.0.1909.2618\gxxsvc.exe" run | C:\Program Files\Garena\Garena\2.0.1909.2618\gxxsvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Garena Online Integrity Level: SYSTEM Description: Garena platform service Exit code: 0 Version: 2019.09.26.1824 Modules
| |||||||||||||||
| 480 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Garena-v2.0.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Garena-v2.0.exe | — | iexplore.exe | |||||||||||
User: admin Company: Garena Integrity Level: MEDIUM Description: Garena Installer Exit code: 3221226540 Version: 2.0.1909.2618 Modules
| |||||||||||||||
| 552 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Garena-v2.0.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Garena-v2.0.exe | iexplore.exe | ||||||||||||
User: admin Company: Garena Integrity Level: HIGH Description: Garena Installer Exit code: 1 Version: 2.0.1909.2618 Modules
| |||||||||||||||
| 2176 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\sellbook.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Garena\Garena\2.0.1909.2618\gxxsvc.exe" uninstall | C:\Program Files\Garena\Garena\2.0.1909.2618\gxxsvc.exe | — | Garena-v2.0.exe | |||||||||||
User: admin Company: Garena Online Integrity Level: HIGH Description: Garena platform service Exit code: 0 Version: 2019.09.26.1824 Modules
| |||||||||||||||
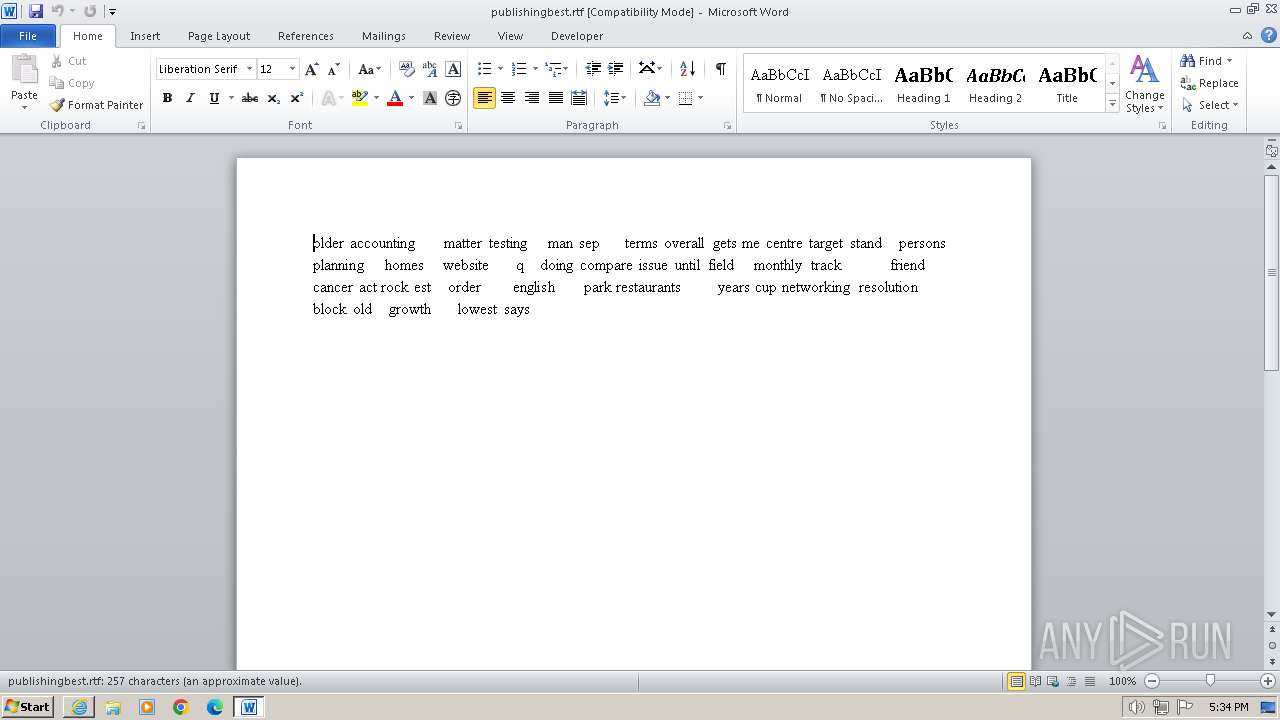
| 2756 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\publishingbest.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3072 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\xmlie.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3668 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
43 244
Read events
41 663
Write events
604
Delete events
977
Modification events
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 856759376 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31088894 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31088894 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
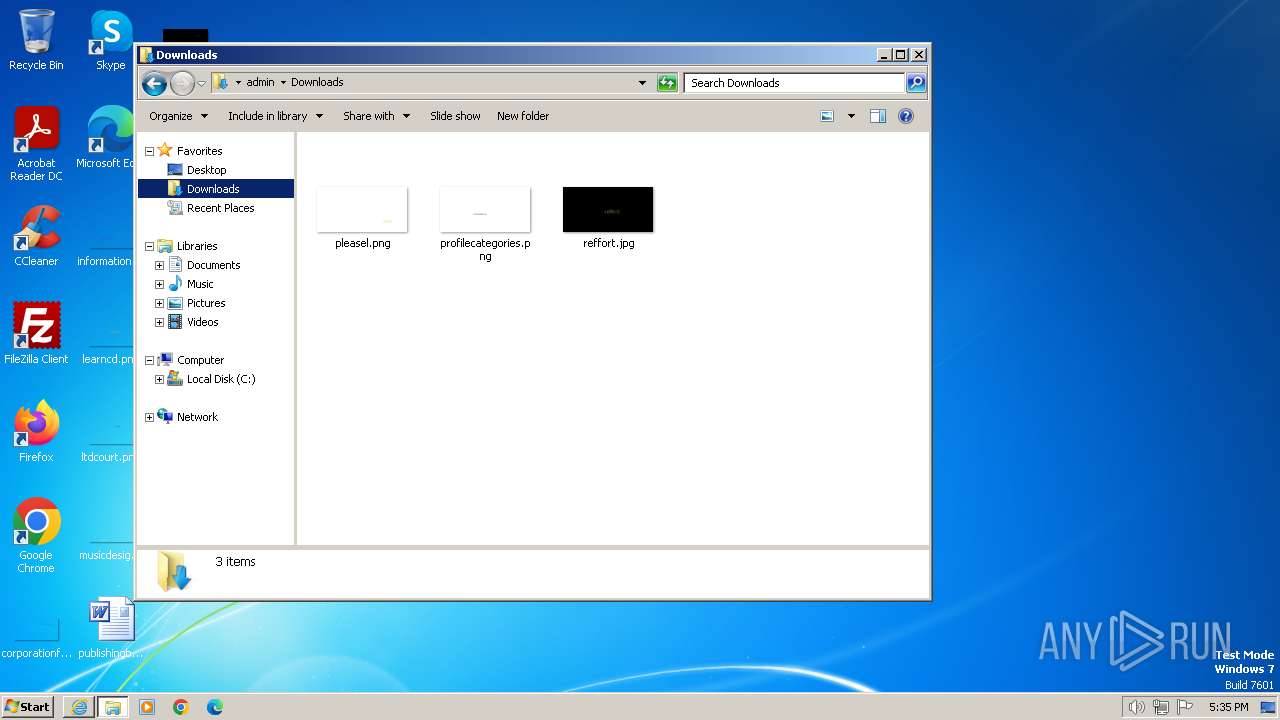
Executable files
98
Suspicious files
95
Text files
147
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:DBC2B99EE8F91ED3892126D3DA54AAB4 | SHA256:23BF92ADCBB38E38071BA3388C52C279A7288228C5C35314AD594791972AF0EF | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:6C234D7D9A7CB5CC6D7F3F8132581814 | SHA256:56B6E2399CD702830C9869D26156CF6F436187A8C1826AD0AC91A47E0DE3639A | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:89775095205084716FA74327A76FA884 | SHA256:04BC275D60C2D4EB83BE961AA8BCE1E08E7743986FBA309E0BF1C2E77B0C79D9 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:0D63EA152076F1330611F78545C56CDB | SHA256:97E3D231D2E59243BA5FE7D80AF472C1C44F14E31433DA0D2D42E9A6146E0DCD | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver6BB5.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E573CDF4C6D731D56A665145182FD759_D813440494A195256BD8324FC506AE99 | binary | |
MD5:8EF3B01728094B2D2E9BDA3EEE7EB952 | SHA256:797D959CAC9A6A2C6AE37879604B494042399D12BE7F5B3A3209286208878D60 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:CAB6225B861674F37BA35D7241B4D9D6 | SHA256:07AA9F1727174FFF61ED1F695EB071AD1113190CF02A7FEBC878E38B8C38941A | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Garena-v2.0[1].exe | executable | |
MD5:B4AB4F5EE78642383C0902D723189DBB | SHA256:B17BA97EE403D50F0548E266485EFCE4027B844DD79A2711E87060AC46A1EE2E | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9FACF5D589B1EFD3.TMP | binary | |
MD5:CCAFC64ECD96FE46EA5224EBAA32DC5D | SHA256:3F0FA365F00FFF256DBC51152E7C5549EE753F01D0CF05BF6504637AD9427EC7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
34
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | iexplore.exe | GET | 304 | 184.24.77.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f78d505714a595e3 | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 304 | 184.24.77.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
3348 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAkrZJnbtHSw4BDBj7VHN8Q%3D | unknown | binary | 471 b | unknown |
3668 | iexplore.exe | GET | 304 | 173.222.108.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b0be6f4ad90be2e5 | unknown | — | — | unknown |
3668 | iexplore.exe | GET | 304 | 173.222.108.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?70d85e3b0e586cab | unknown | — | — | unknown |
3668 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 173.222.108.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e90c163b6659448e | unknown | compressed | 65.2 Kb | unknown |
3668 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | unknown | binary | 471 b | unknown |
3668 | iexplore.exe | GET | 304 | 173.222.108.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e55f0cb727843010 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3348 | iexplore.exe | 2.21.20.146:443 | cdn.gxx.garenanow.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3348 | iexplore.exe | 184.24.77.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3348 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3668 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
3668 | iexplore.exe | 173.222.108.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
3668 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 173.222.108.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.gxx.garenanow.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
statscollection.garenanow.com |
| unknown |
udp.gxx.garenanow.com |
| unknown |
Threats
Process | Message |
|---|---|
Garena-v2.0.exe | {"id":"gxx","action":"0","data":{"ver":"2.0.1909.2618", "patch":"0", "stage":"init"}} |
Garena-v2.0.exe | SVCHOST.EXE |
Garena-v2.0.exe | SVCHOST.EXE |
Garena-v2.0.exe | IMEDICTUPDATE.EXE |
Garena-v2.0.exe | SVCHOST.EXE |
Garena-v2.0.exe | TASKHOST.EXE |
Garena-v2.0.exe | TASKENG.EXE |
Garena-v2.0.exe | DWM.EXE |
Garena-v2.0.exe | EXPLORER.EXE |
Garena-v2.0.exe | CTFMON.EXE |