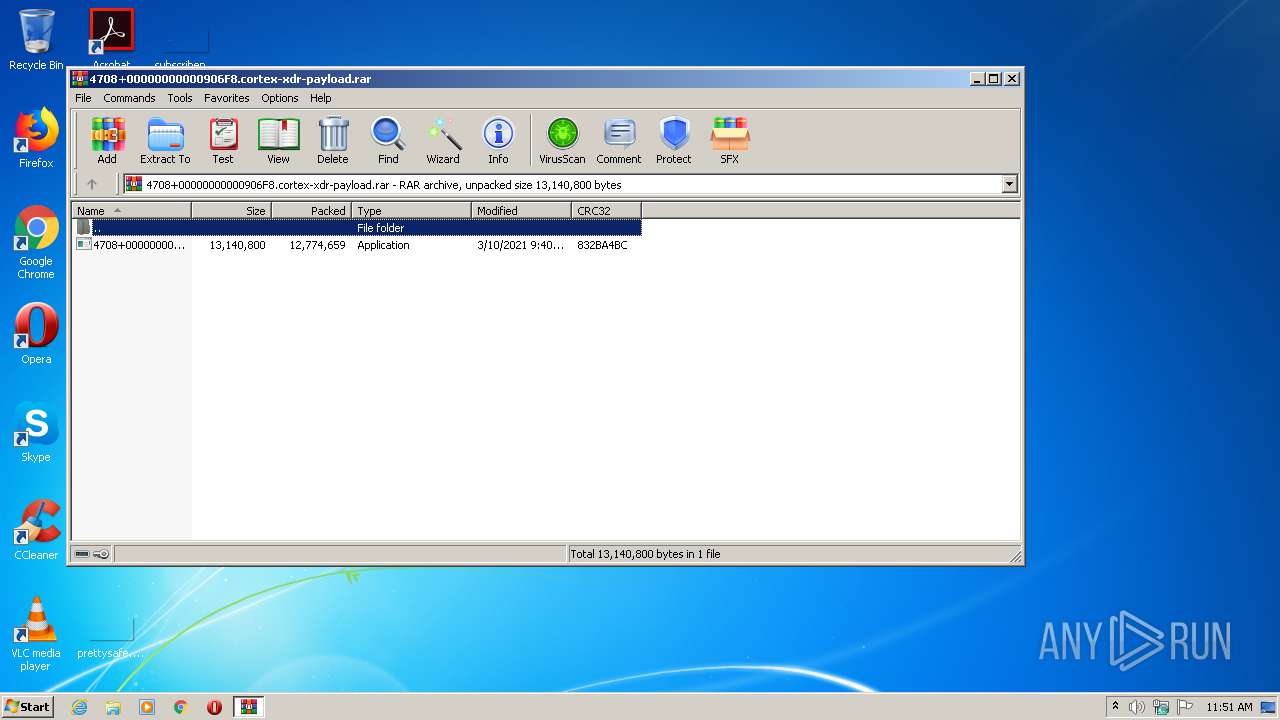
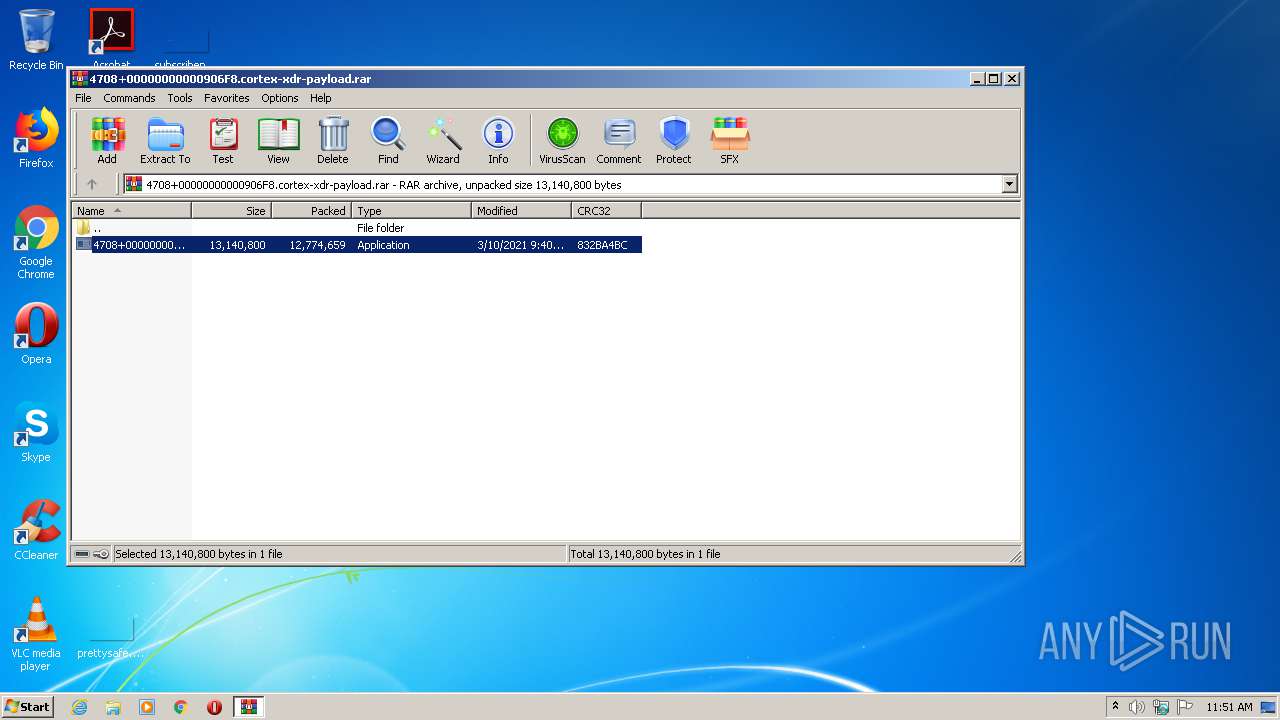
| File name: | 4708+00000000000906F8.cortex-xdr-payload.rar |
| Full analysis: | https://app.any.run/tasks/81543193-9917-4edf-bb08-55e7bd552a0d |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2021, 10:50:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A45C9B2EC20A41D56859C668F978C4C8 |
| SHA1: | 56F9A05F304D2E6398F318FAC91102CDDF0BAB55 |
| SHA256: | C7AC5E124DD773027168EEA4EBC307CE39D7D093347EAA8E19A638A0E6403EC2 |
| SSDEEP: | 393216:5a3/FjAP/M0DNf62Dkrx8Fvn4DLl1Z03s2h8aywoVn5:50/Fekf++89qR1C3flE |
MALICIOUS
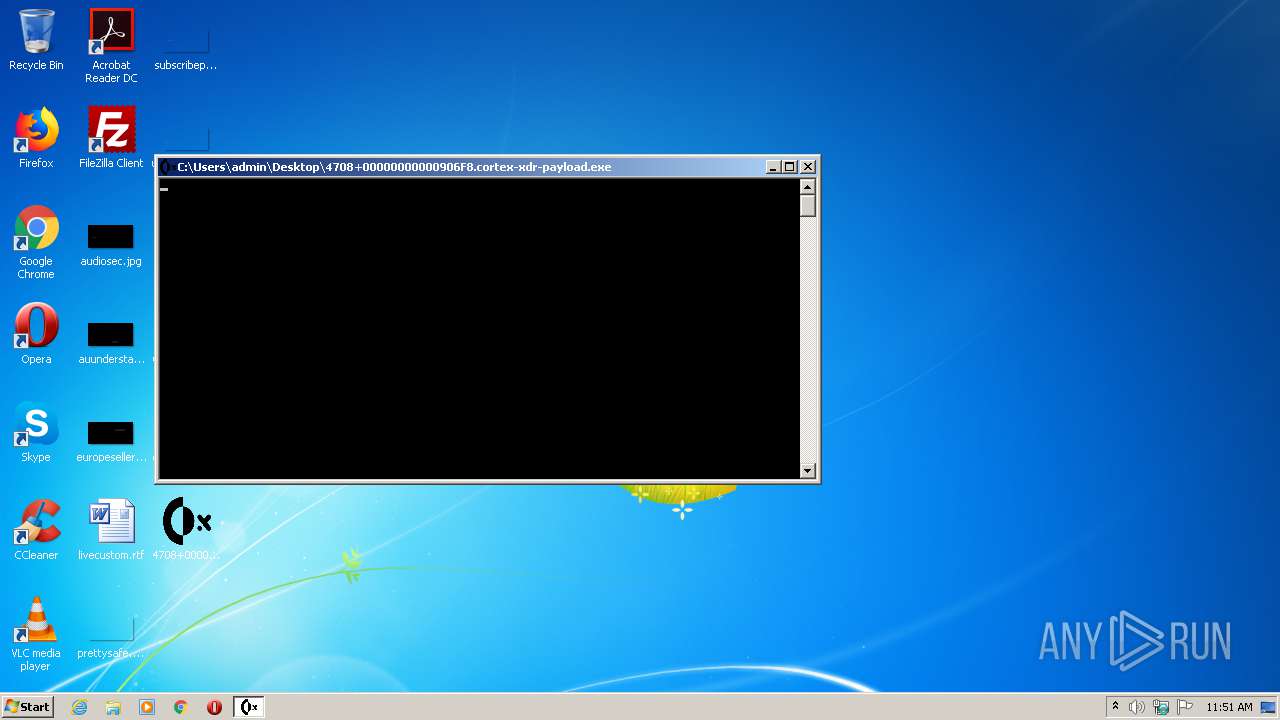
Application was dropped or rewritten from another process
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1424)
Drops executable file immediately after starts
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
Loads dropped or rewritten executable
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1424)
SUSPICIOUS
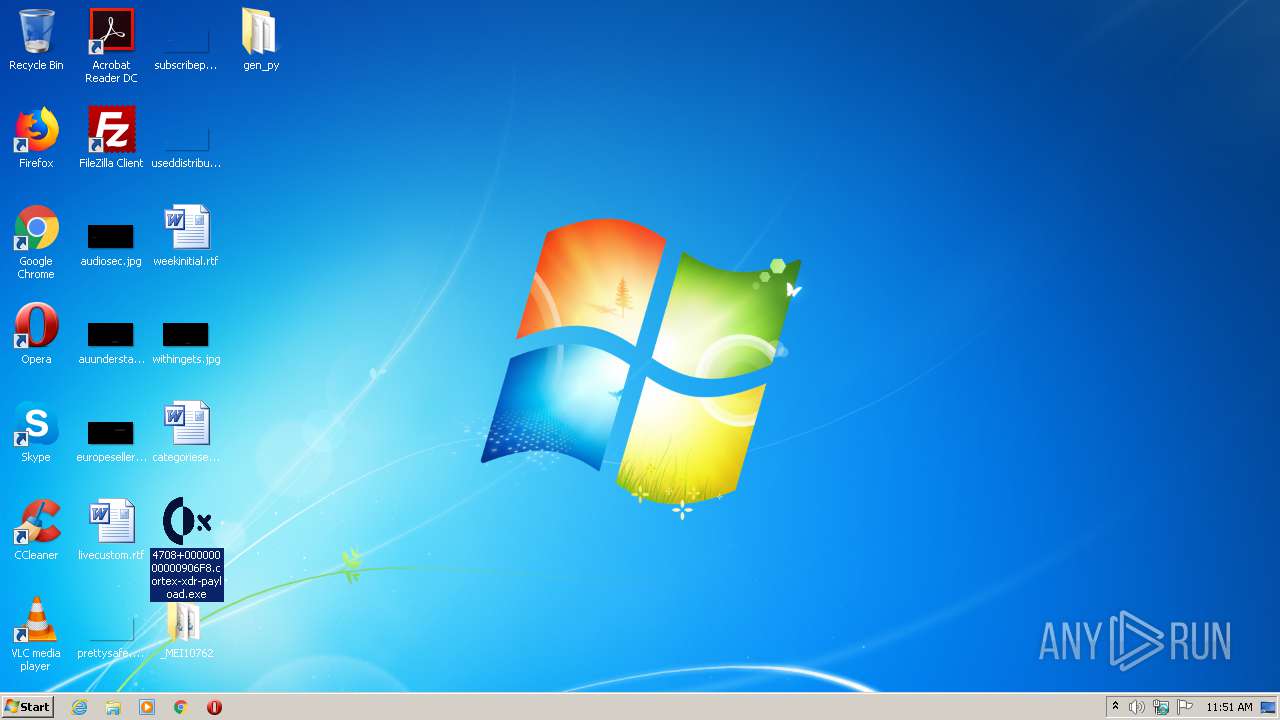
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2776)
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
Drops a file with too old compile date
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
Drops a file with a compile date too recent
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
Drops a file that was compiled in debug mode
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
Application launched itself
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
Loads Python modules
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1424)
INFO
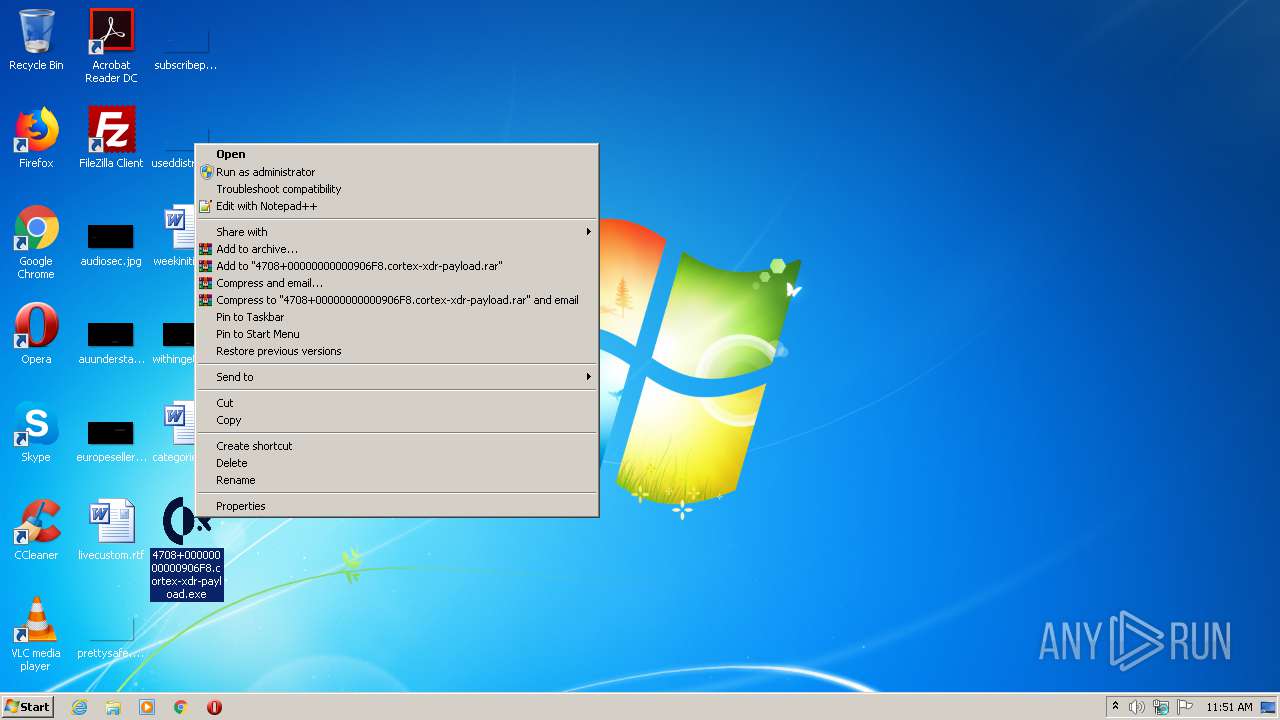
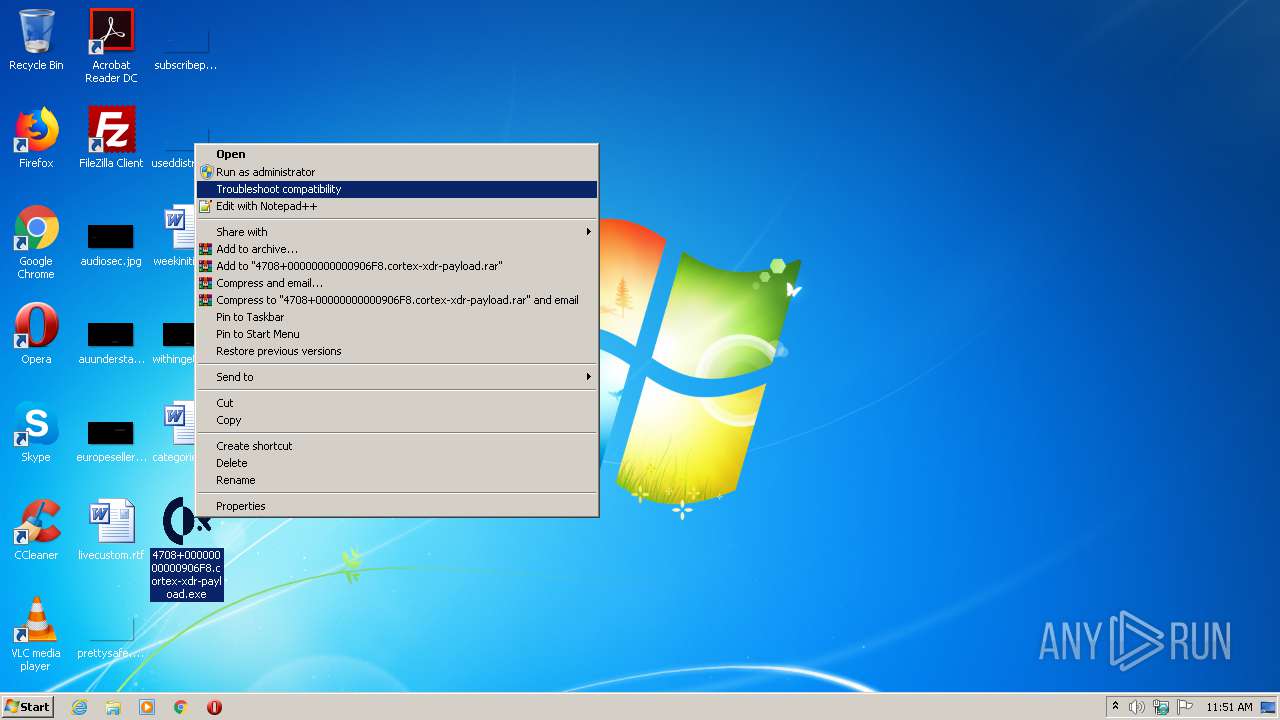
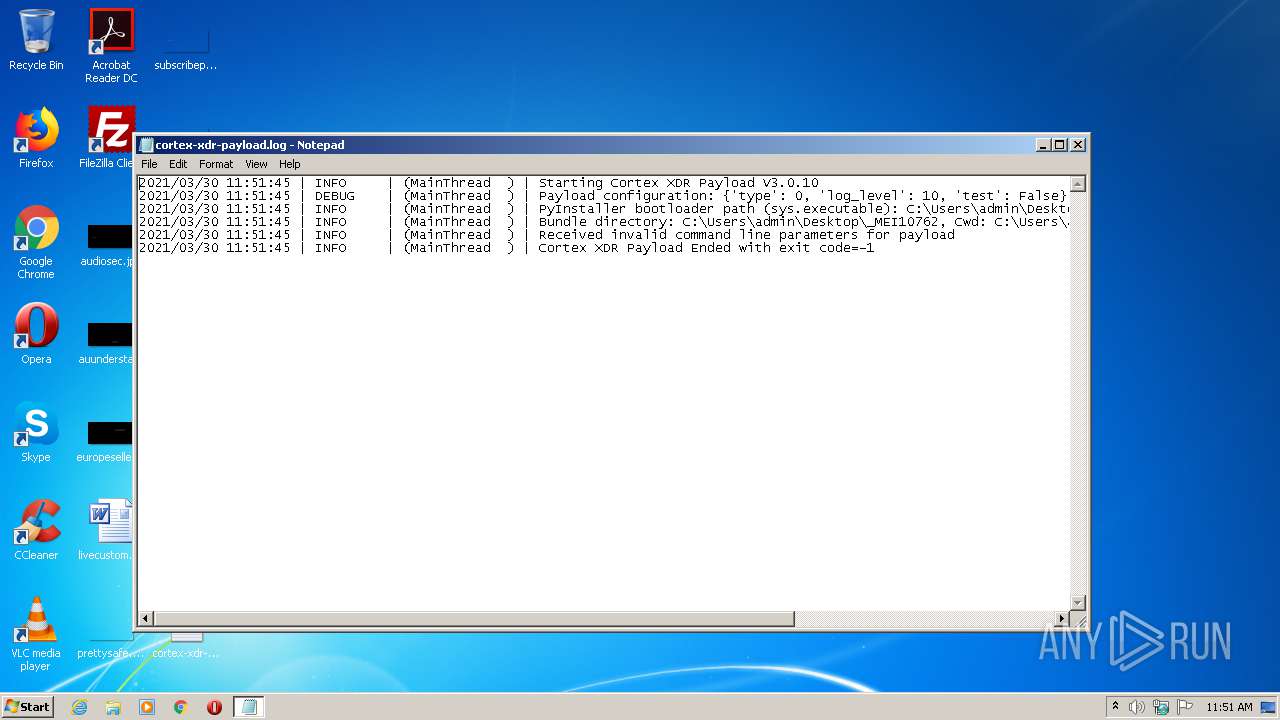
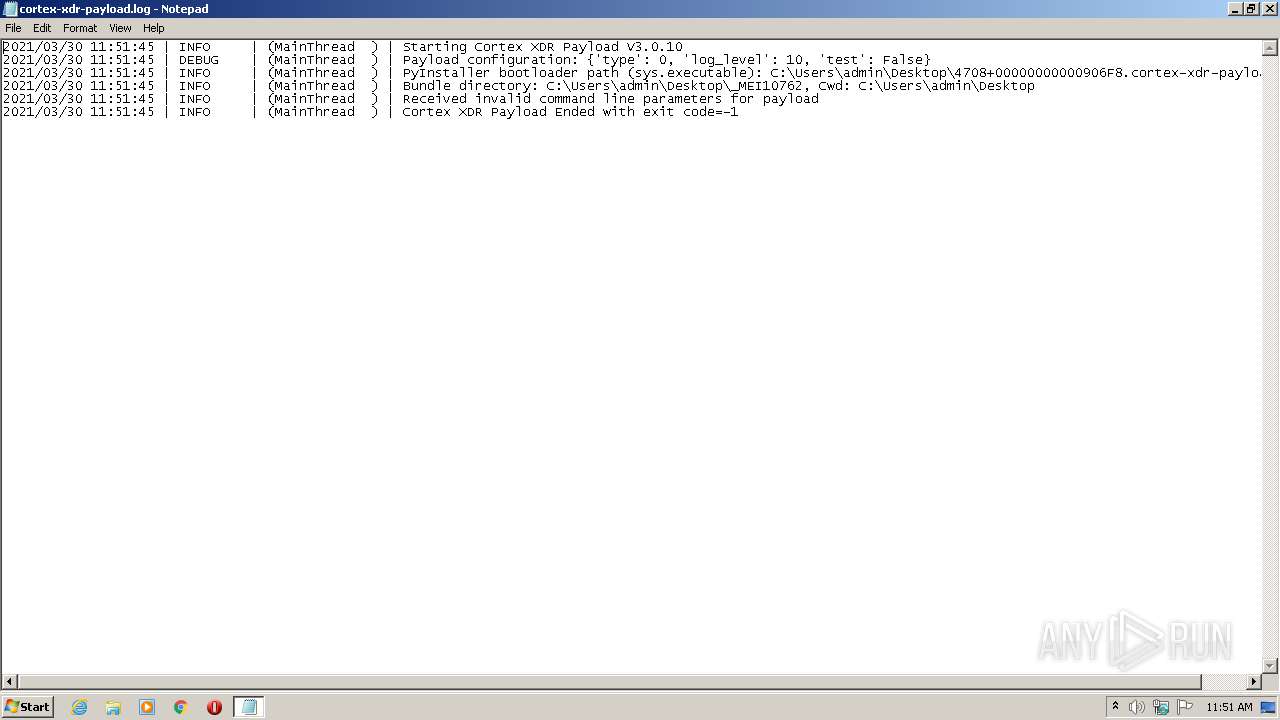
Manual execution by user
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
- NOTEPAD.EXE (PID: 1880)
Dropped object may contain Bitcoin addresses
- 4708+00000000000906F8.cortex-xdr-payload.exe (PID: 1076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
46
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | "C:\Users\admin\Desktop\4708+00000000000906F8.cortex-xdr-payload.exe" | C:\Users\admin\Desktop\4708+00000000000906F8.cortex-xdr-payload.exe | explorer.exe | ||||||||||||
User: admin Company: Palo Alto Networks Integrity Level: HIGH Description: Cortex XDR Payload Exit code: 0 Version: 3.0.10 Modules
| |||||||||||||||
| 1424 | "C:\Users\admin\Desktop\4708+00000000000906F8.cortex-xdr-payload.exe" | C:\Users\admin\Desktop\4708+00000000000906F8.cortex-xdr-payload.exe | — | 4708+00000000000906F8.cortex-xdr-payload.exe | |||||||||||
User: admin Company: Palo Alto Networks Integrity Level: HIGH Description: Cortex XDR Payload Exit code: 0 Version: 3.0.10 Modules
| |||||||||||||||
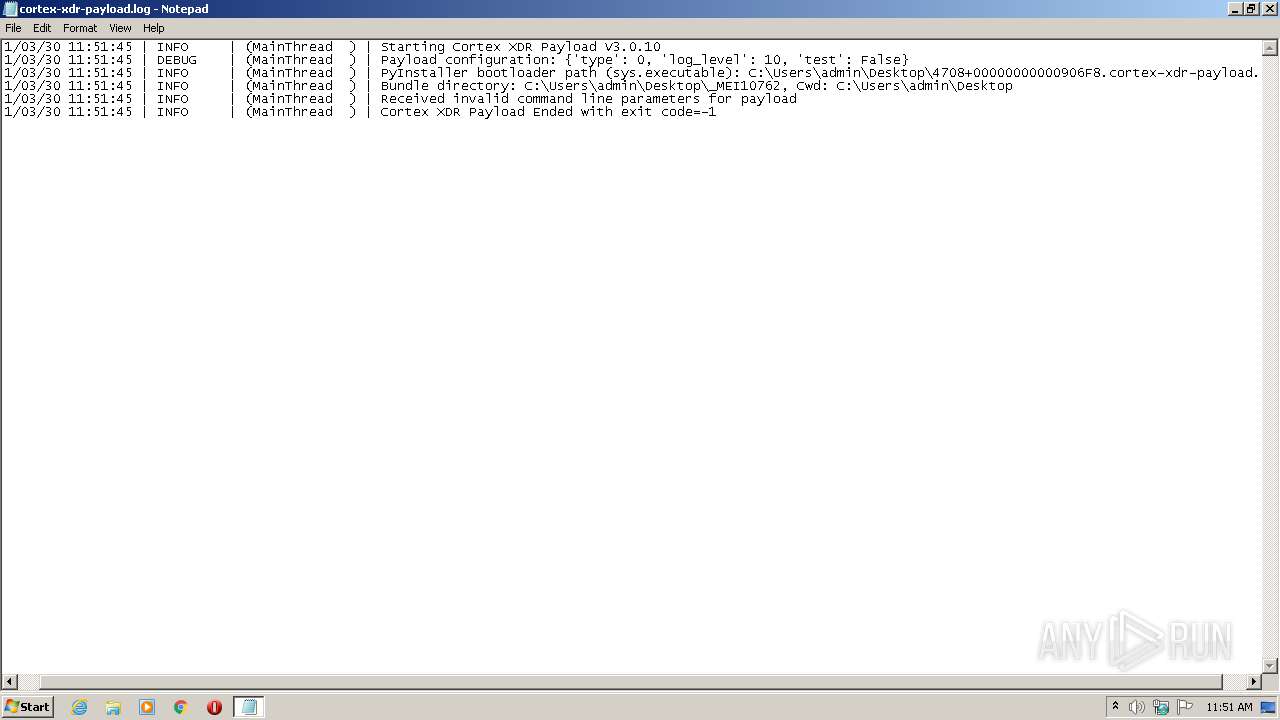
| 1880 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\cortex-xdr-payload.log | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
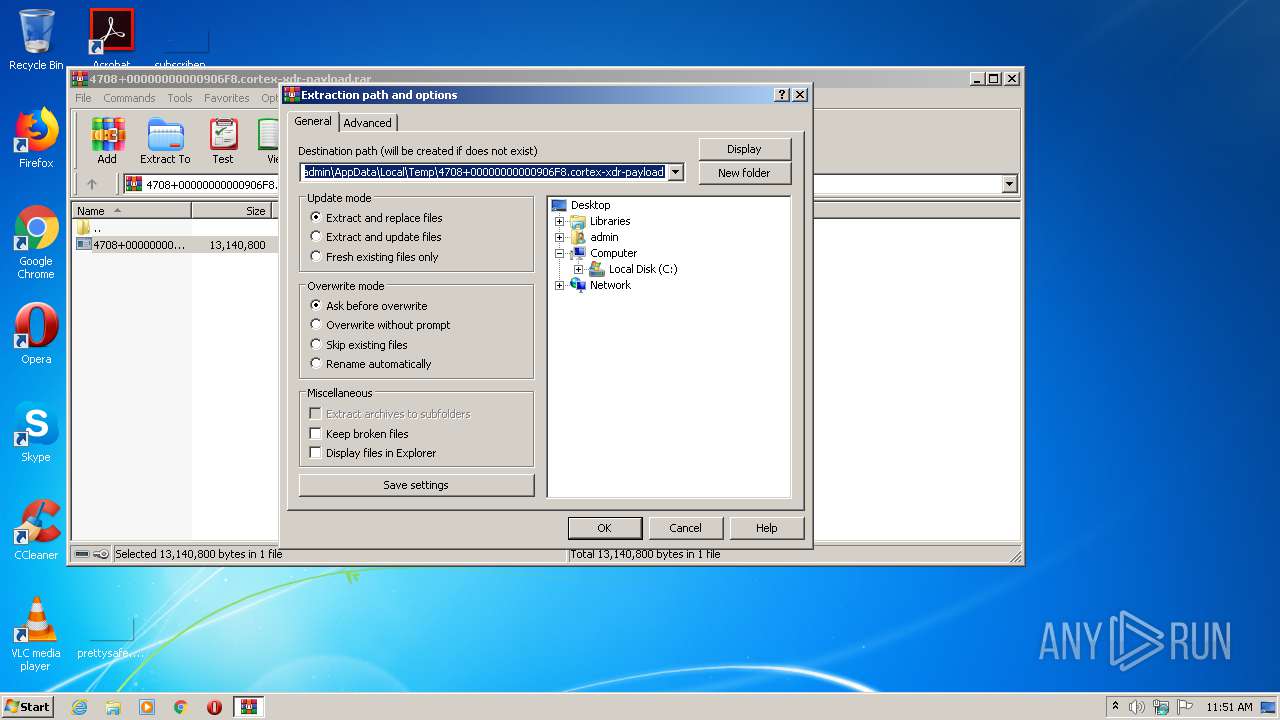
| 2776 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\4708+00000000000906F8.cortex-xdr-payload.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
482
Read events
460
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\4708+00000000000906F8.cortex-xdr-payload.rar | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
90
Suspicious files
2
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2776 | WinRAR.exe | C:\Users\admin\Desktop\4708+00000000000906F8.cortex-xdr-payload.exe | executable | |
MD5:— | SHA256:— | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\_bz2.pyd | executable | |
MD5:1C52BA084A3723940C0778AB5186893A | SHA256:CB008E0A6C65DDB5F20AB96E65285DEE874468DF203FAEAFCA5E9B4A9F2918DC | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\_hashlib.pyd | executable | |
MD5:4F51ED287BBAE386090A9BCC3531B2B8 | SHA256:5B6DA4B43C258B459159C4FBC7AD3521B387C377C058FE77AD74BA000606D72E | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\_ctypes.pyd | executable | |
MD5:10861D3FA19D7DC3B41EB6F837340782 | SHA256:6255BAB0B7F3E2209A9C8B89A3E1EC1BBC7A29849A18E70C0CF582A63C90BED1 | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\_multiprocessing.pyd | executable | |
MD5:05AB494CF791A50E4F8D2FFE1D3E1F3C | SHA256:4959342924E22B6A16EBC5C1ED39552E981515401EDA770E4AC87FD12ACF53F8 | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\_elementtree.pyd | executable | |
MD5:390552274C5F71C7EBD1F343BB74446C | SHA256:D6C7EA93CDEFE1973239A3DEC0F49A1027E943F1DE07E21FF378978CC6A438BC | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\_decimal.pyd | executable | |
MD5:5596249B64C074374EAA1D4084E336C3 | SHA256:673BD4CACF3B5F8DA67C9C84E03E238961CA98683483DE78D0A6410200F7ABA6 | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\_lzma.pyd | executable | |
MD5:F91A9F1F2EFEE2F5DBAE42EA5D5D7153 | SHA256:1F82BB06C79B6B392C92CAD87FFA736377FA25CD6D10DA8D61441D42C0D0101E | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\VCRUNTIME140.dll | executable | |
MD5:CFC08FCA16C3647A42E78EF7556E4090 | SHA256:0B08756920415C5F087E65C85DA1FBC7A1FAFC0D91038E0425CD339C0D903910 | |||
| 1076 | 4708+00000000000906F8.cortex-xdr-payload.exe | C:\Users\admin\Desktop\_MEI10762\_ssl.pyd | executable | |
MD5:2825BAE93CD459D835B74892C9BD80DB | SHA256:AF4379FDC8BD41F7A8A4B509DE949202CCDB5E4825797D7A5DDDD5E77671382C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report