| File name: | What.exe |
| Full analysis: | https://app.any.run/tasks/90ebc543-3046-42c8-9cdf-8f9cfe722caf |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2025, 00:59:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 26D924D1876C67B0895FEB3A0E9FF765 |
| SHA1: | 7BF9FBF37CDA6311229EE6ACCACE02ABCB87B1AD |
| SHA256: | C7A02528151348F2CA29ADB828451165EA2FAAA41708BFAD50894D45960D2BF4 |
| SSDEEP: | 384:+EYA/53nvizM1kQ1h0bIN6dV5gO00J/R6boPXobQ9:3YAVviAHh0YKnj/RJgbc |
MALICIOUS
Disables task manager
- What.exe (PID: 5020)
SUSPICIOUS
Reads security settings of Internet Explorer
- What.exe (PID: 2780)
- StartMenuExperienceHost.exe (PID: 4236)
- What.exe (PID: 5020)
Reads the date of Windows installation
- What.exe (PID: 2780)
- StartMenuExperienceHost.exe (PID: 4236)
- SearchApp.exe (PID: 3100)
Application launched itself
- What.exe (PID: 2780)
Write to the desktop.ini file (may be used to cloak folders)
- What.exe (PID: 5020)
There is functionality for taking screenshot (YARA)
- What.exe (PID: 5020)
INFO
Checks supported languages
- What.exe (PID: 2780)
- What.exe (PID: 5020)
- TextInputHost.exe (PID: 1132)
- StartMenuExperienceHost.exe (PID: 4236)
- SearchApp.exe (PID: 3100)
Reads the computer name
- What.exe (PID: 2780)
- What.exe (PID: 5020)
- TextInputHost.exe (PID: 1132)
- SearchApp.exe (PID: 3100)
- StartMenuExperienceHost.exe (PID: 4236)
Process checks computer location settings
- What.exe (PID: 2780)
- StartMenuExperienceHost.exe (PID: 4236)
- SearchApp.exe (PID: 3100)
Checks proxy server information
- What.exe (PID: 5020)
- SearchApp.exe (PID: 3100)
Reads the software policy settings
- What.exe (PID: 5020)
- SearchApp.exe (PID: 3100)
Reads the machine GUID from the registry
- What.exe (PID: 5020)
- SearchApp.exe (PID: 3100)
Creates files or folders in the user directory
- What.exe (PID: 5020)
Create files in a temporary directory
- What.exe (PID: 5020)
Reads Environment values
- SearchApp.exe (PID: 3100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:07:13 00:57:25+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.37 |
| CodeSize: | 12288 |
| InitializedDataSize: | 14848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3258 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
140
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\Desktop\What.exe" | C:\Users\admin\Desktop\What.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3100 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4236 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5020 | "C:\Users\admin\Desktop\What.exe" | C:\Users\admin\Desktop\What.exe | What.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 6828 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 832
Read events
16 729
Write events
100
Delete events
3
Modification events
| (PID) Process: | (4236) StartMenuExperienceHost.exe | Key: | \REGISTRY\A\{a086686a-ed07-6932-63fd-45a5ddbd168e}\LocalState\DataCorruptionRecovery |
| Operation: | write | Name: | InitializationAttemptCount |
Value: 010000003B54EA6E91F3DB01 | |||
| (PID) Process: | (4236) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (4236) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_AppUsageData |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (4236) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_TargetedContentTiles |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (3100) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (3100) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Recognizers |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Recognizers\Tokens\MS-1033-110-WINMO-DNN | |||
| (PID) Process: | (3100) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | IsMSACloudSearchEnabled |
Value: 0 | |||
| (PID) Process: | (3100) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | IsAADCloudSearchEnabled |
Value: 0 | |||
| (PID) Process: | (3100) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | CortanaStateLastRun |
Value: 0605736800000000 | |||
| (PID) Process: | (4236) StartMenuExperienceHost.exe | Key: | \REGISTRY\A\{a086686a-ed07-6932-63fd-45a5ddbd168e}\LocalState\DataCorruptionRecovery |
| Operation: | write | Name: | InitializationAttemptCount |
Value: 00000000226D1C6F91F3DB01 | |||
Executable files
2
Suspicious files
33
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
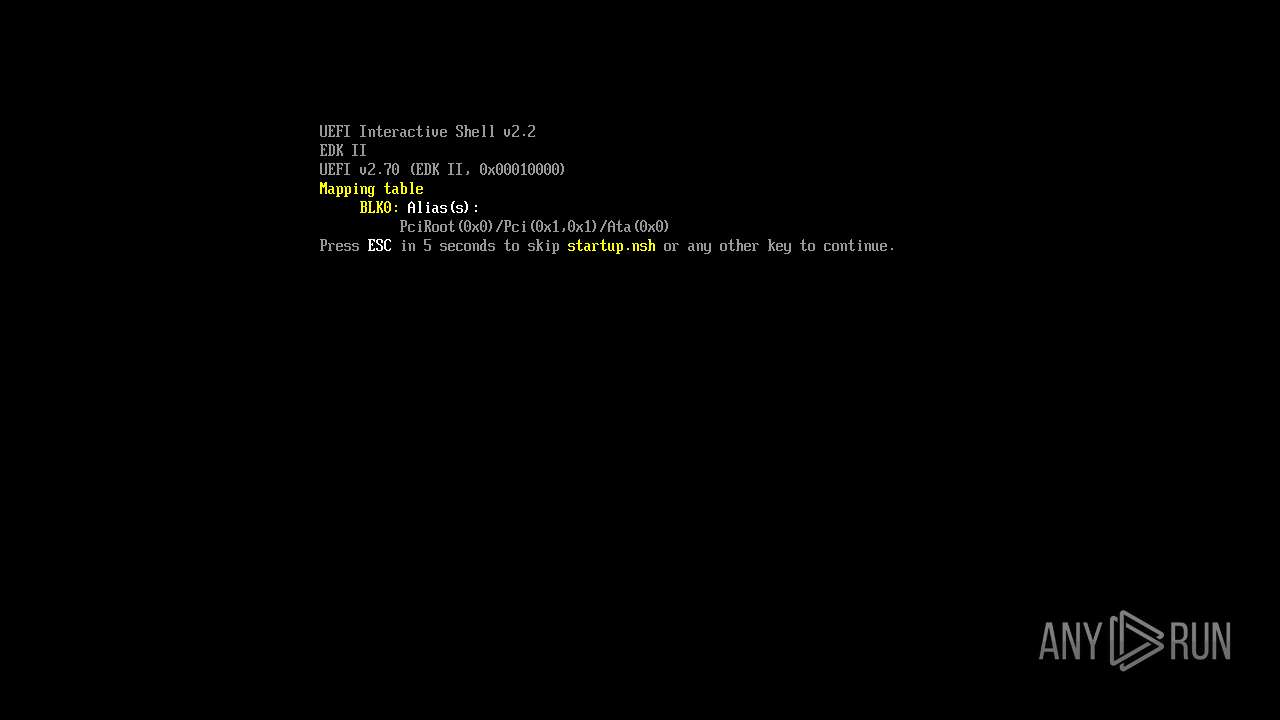
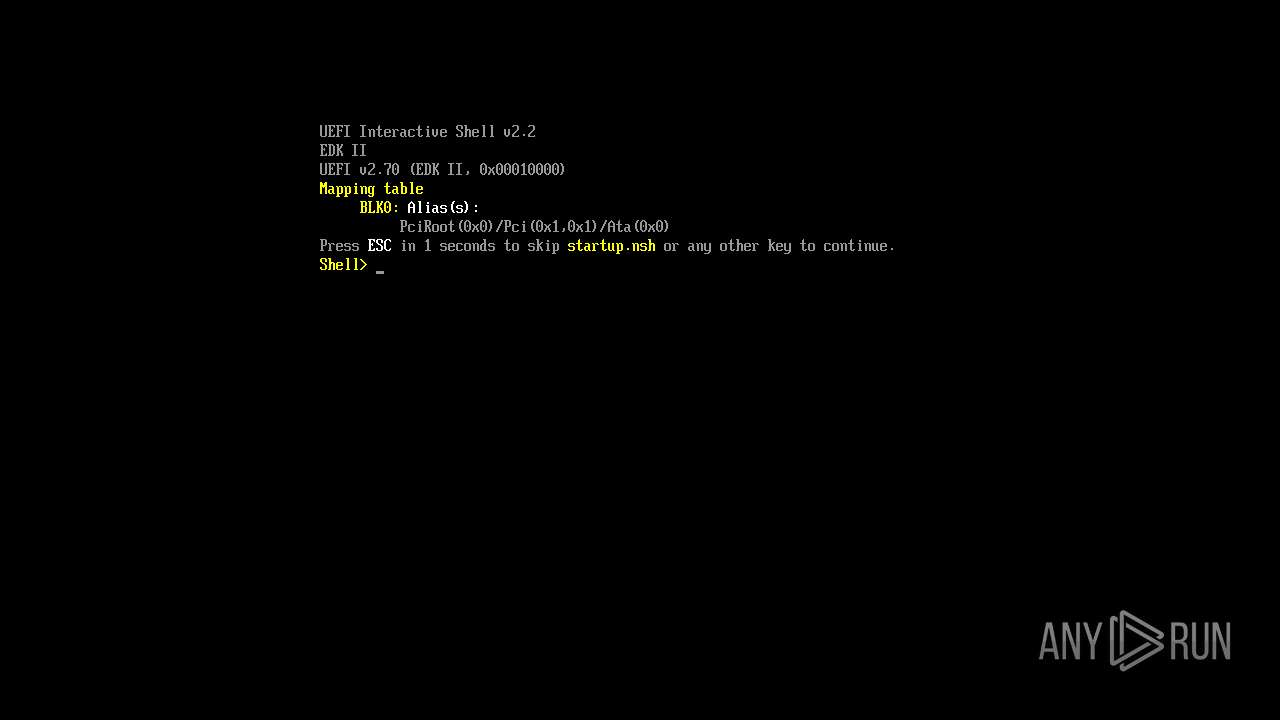
| 5020 | What.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 3100 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\INetCache\Q84V0JUH\6hU_LneafI_NFLeDvM367ebFaKQ[1].js | binary | |
MD5:C6C21B7634D82C53FB86080014D86E66 | SHA256:D39E9BA92B07F4D50B11A49965E9B162452D7B9C9F26D9DCB07825727E31057E | |||
| 5020 | What.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\GOVERNMENT_GLOWIE[1].mp3 | binary | |
MD5:6E2494399234DF4DB385129D80E53018 | SHA256:97546DB5FD6875582ECADFB6020BF94B0E342C05A89DD2207626A26CD89EBD54 | |||
| 5020 | What.exe | C:\Users\admin\AppData\Local\Temp\boot_image.img | html | |
MD5:9071B9DA6E1E20FF593682BC4D3012B8 | SHA256:6B4899F7ED5360D312F3EBFD81E9E492E93B21E73E8AC980A2C381EC51294859 | |||
| 3100 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\tUCiVcVWZ-go7BLlq95YW6bKHZE[1].css | text | |
MD5:445D78544E0CFC11EFC1E172DA3ECBBC | SHA256:76EFEBABB82AE8342985C99A498137C04B3E46BC59D78191F0DA44C660B980F5 | |||
| 5020 | What.exe | C:\Users\admin\Documents\comesmajor.rtf | binary | |
MD5:7BF6DF669EB8A8888C8656E9E61EC50F | SHA256:6850D5FA10244922EECEB3B391E415D8BAA6819A7031F602A22DB09AF0294AF8 | |||
| 5020 | What.exe | C:\Users\admin\Documents\holidayround.rtf | binary | |
MD5:496E348C4A895F7441DB6CB44F9721DE | SHA256:C9B34F6933CF5A18F1DCF22DBABF907F2FED380D1AADB544A808CC76D167CDB0 | |||
| 3100 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\FgBbpIj0thGWZOh_xFnM9i4O7ek[1].css | text | |
MD5:908111EB0FFB1360D5DD61279C21703E | SHA256:1ED87CF425DED994B05A842271AB4D28A76F399E571688CF2E7B186F70DC3059 | |||
| 5020 | What.exe | C:\Users\admin\Documents\servicescustomers.rtf | binary | |
MD5:D26059E68587D6C57B73EDA8AB2ED257 | SHA256:181E5A910C3C144044704ACF88E8851E4CCAB8F37594801144BE9B7A0F6D13BE | |||
| 3100 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\-M-8YWX0KlEtdAHVrkTvKQHOghs[1].js | binary | |
MD5:32EE4742328DFB725F3A96641B93B344 | SHA256:061E63AF37D22CCEF7FB5BB9BEABA0DF2F36B64F985BB8A408638846C895D0A7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
21
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 303 | 142.250.185.110:443 | https://drive.google.com/uc?export=download&id=1hLGm2T2asgZVnXI4w-NLjJ_sSLHYP7pz | US | — | — | unknown |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
— | — | GET | 302 | 142.250.184.193:443 | https://drive.usercontent.google.com/download?id=1nTBQeZ2hXCH2B_e3Kk4QKRRtoA6hFtlG&export=download&authuser=0 | US | — | — | unknown |
2512 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 302 | 74.125.133.84:443 | https://accounts.google.com/ServiceLogin?service=wise&passive=1209600&continue=https://drive.usercontent.google.com/download?id%3D1nTBQeZ2hXCH2B_e3Kk4QKRRtoA6hFtlG%26export%3Ddownload%26authuser%3D0&followup=https://drive.usercontent.google.com/download?id%3D1nTBQeZ2hXCH2B_e3Kk4QKRRtoA6hFtlG%26export%3Ddownload%26authuser%3D0 | US | — | — | unknown |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 200 | 92.123.104.32:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | binary | 21.3 Kb | whitelisted |
— | — | GET | 200 | 142.250.184.193:443 | https://drive.usercontent.google.com/download?id=1hLGm2T2asgZVnXI4w-NLjJ_sSLHYP7pz&export=download | US | binary | 582 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2512 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5020 | What.exe | 172.217.18.14:443 | drive.google.com | GOOGLE | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2512 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
drive.google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
accounts.google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |