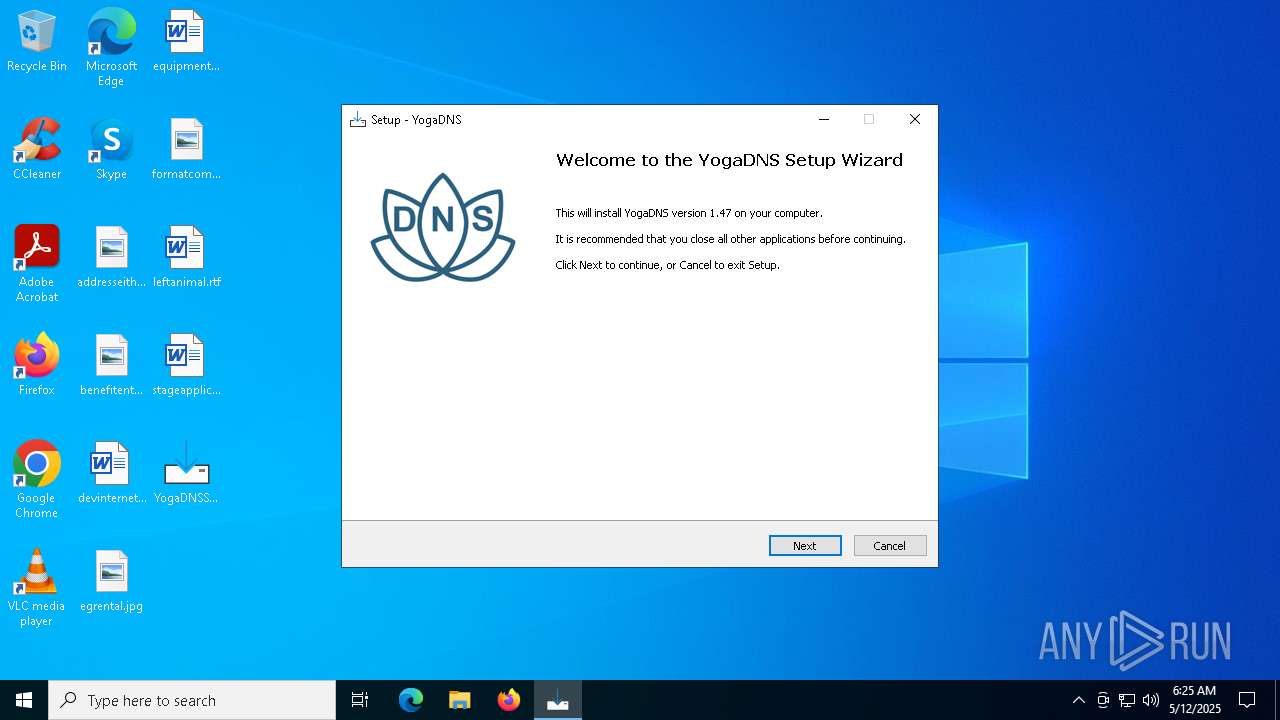
| File name: | YogaDNSSetupv1.47.exe |
| Full analysis: | https://app.any.run/tasks/326de46c-5b5a-42f1-8e82-d9b0cb00bcdb |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 06:25:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | 3AFDCE3C960B183AB7DF42ECF2B8A45D |
| SHA1: | E649850AAC6E1B7D5B18F985763758B8A7D68724 |
| SHA256: | C790B930B990D3906124CBFF26A634D6400460F1E24616E41A88A6DF0EAE0CE4 |
| SSDEEP: | 98304:/+QqZ8feKxrR4AnQ9BC1F3f25srt6QGrEY30ZYfMfw/jZVUbWL7aw5E0QEErWgP4:VtGLtLdlKOKXK1CqPN3 |
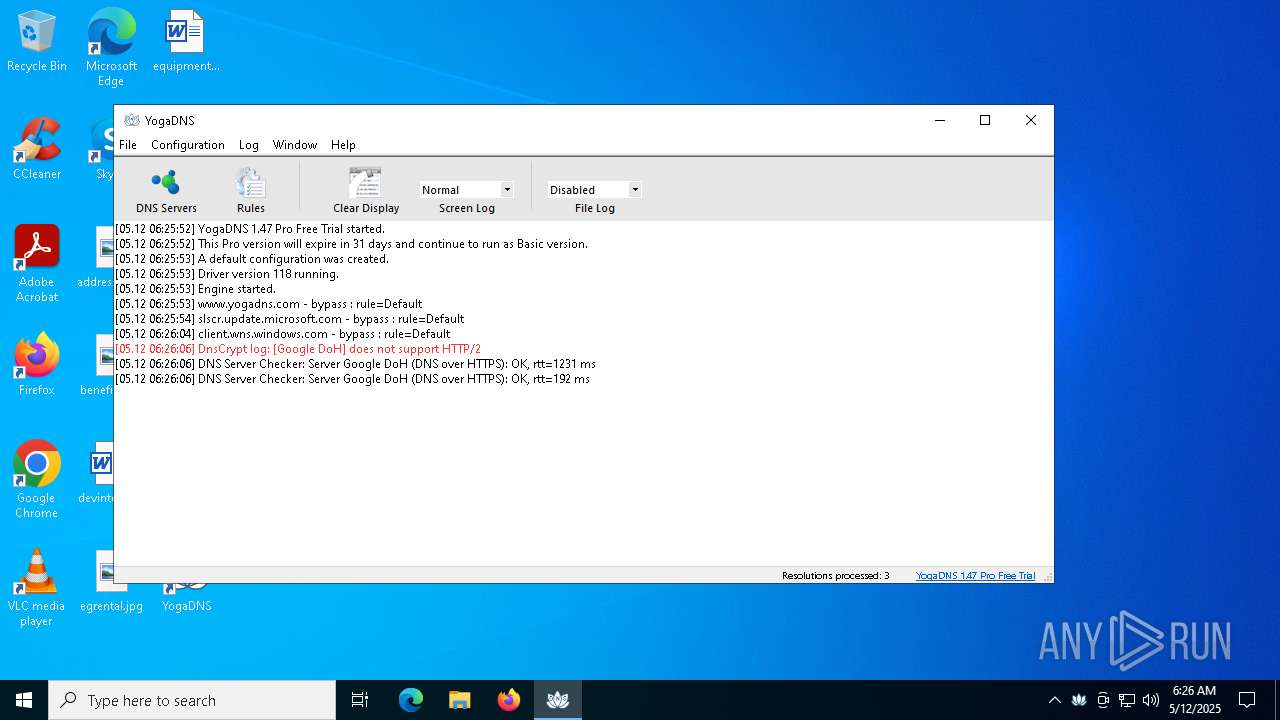
MALICIOUS
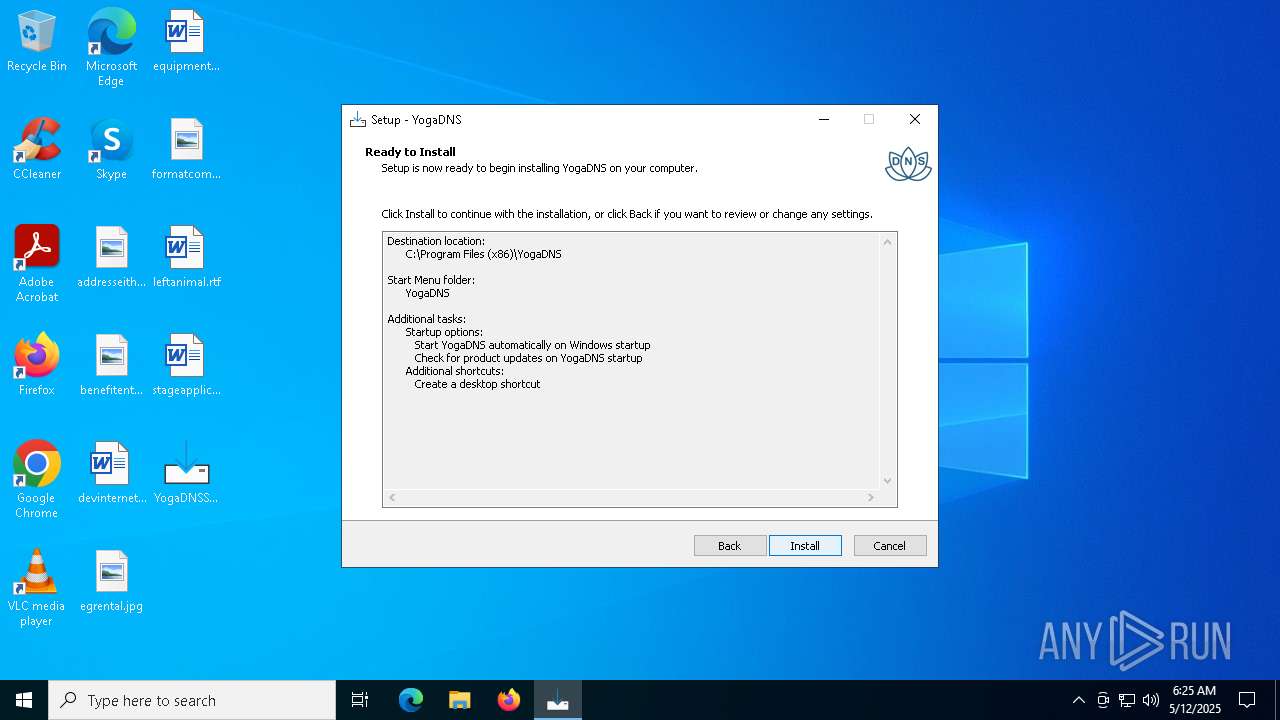
Changes the autorun value in the registry
- YogaDNSSetupv1.47.tmp (PID: 7564)
- rundll32.exe (PID: 8184)
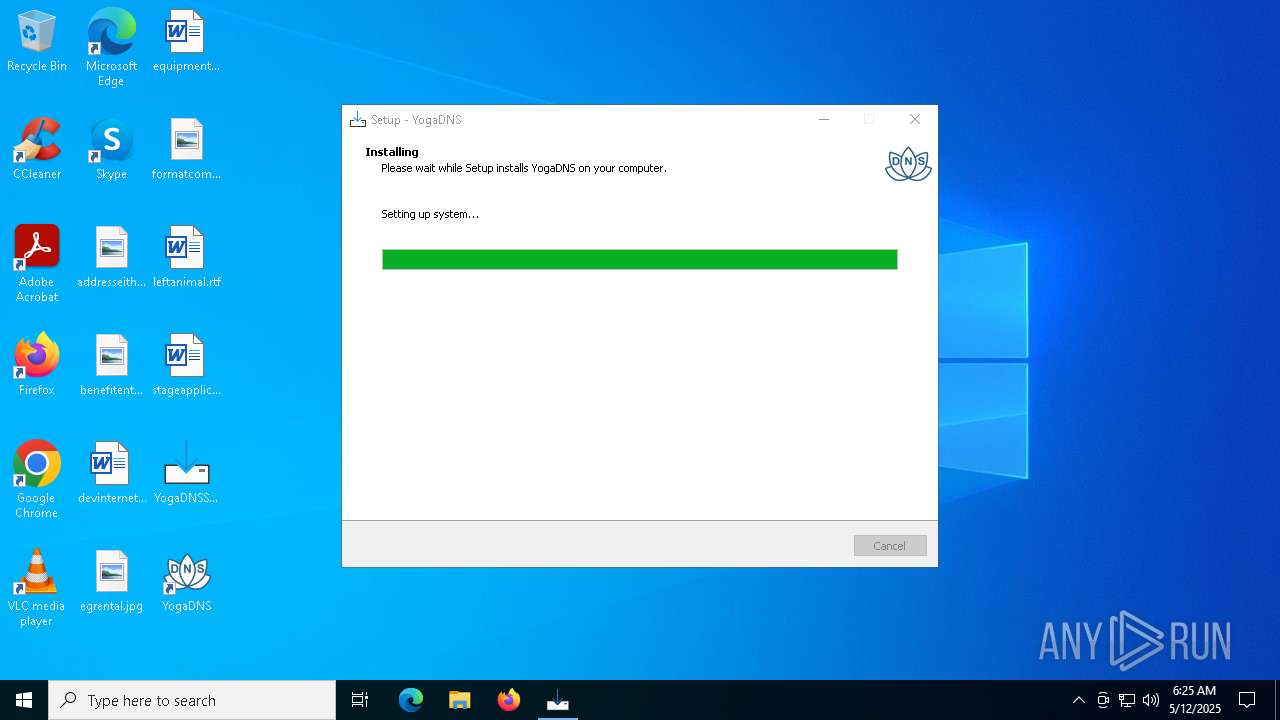
Starts NET.EXE for service management
- YogaDNSSetupv1.47.tmp (PID: 7564)
- net.exe (PID: 8088)
SUSPICIOUS
Reads security settings of Internet Explorer
- YogaDNSSetupv1.47.tmp (PID: 7408)
- YogaDNS.exe (PID: 1132)
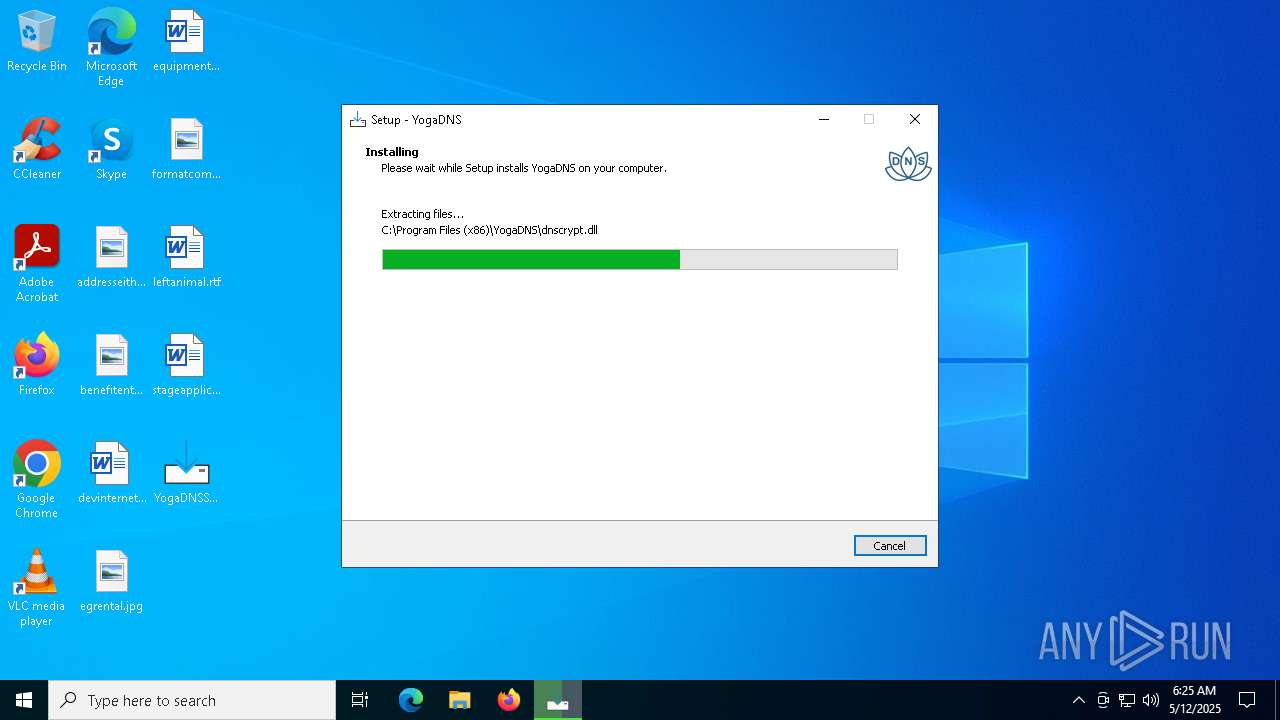
Executable content was dropped or overwritten
- YogaDNSSetupv1.47.exe (PID: 7540)
- YogaDNSSetupv1.47.exe (PID: 7388)
- YogaDNSSetupv1.47.tmp (PID: 7564)
- drvinst.exe (PID: 4740)
- rundll32.exe (PID: 8184)
- drvinst.exe (PID: 5064)
Reads the Windows owner or organization settings
- YogaDNSSetupv1.47.tmp (PID: 7564)
Drops a system driver (possible attempt to evade defenses)
- YogaDNSSetupv1.47.tmp (PID: 7564)
- rundll32.exe (PID: 8184)
- drvinst.exe (PID: 4740)
- drvinst.exe (PID: 5064)
Uses RUNDLL32.EXE to load library
- YogaDNSSetupv1.47.tmp (PID: 7564)
Creates files in the driver directory
- drvinst.exe (PID: 4740)
- drvinst.exe (PID: 5064)
Creates or modifies Windows services
- drvinst.exe (PID: 5064)
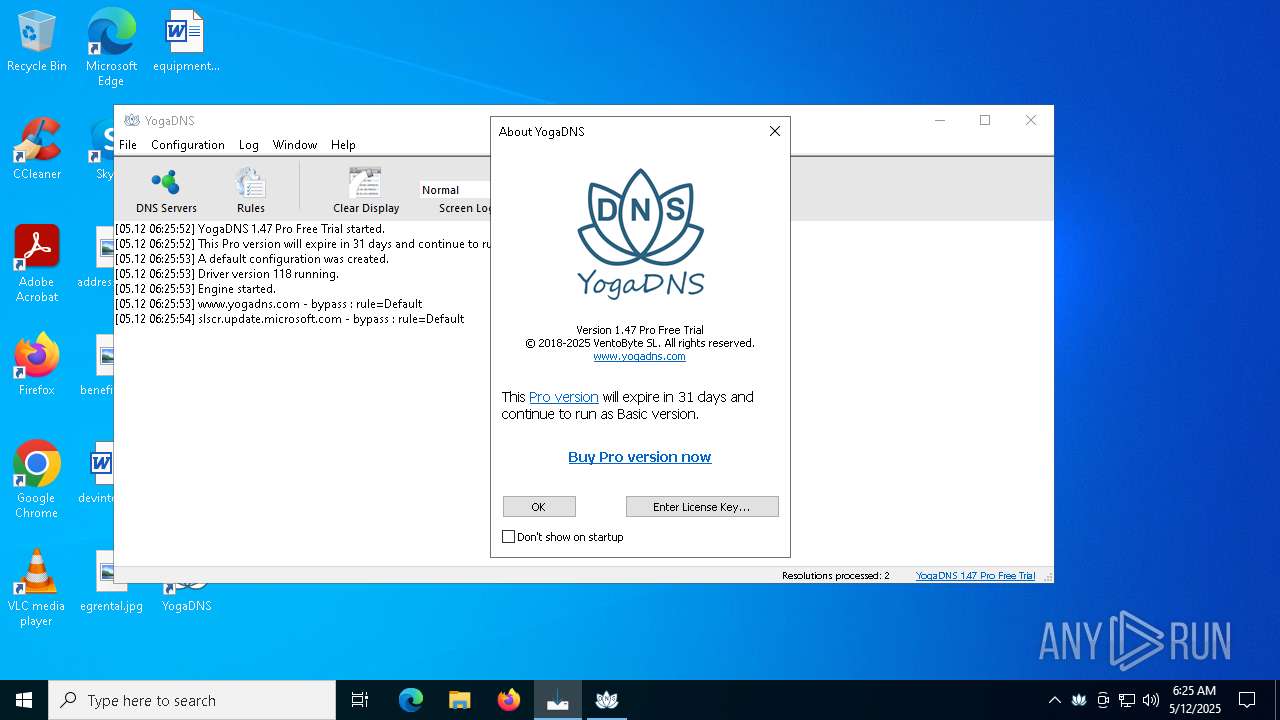
Process uses IPCONFIG to clear DNS cache
- YogaDNS.exe (PID: 1132)
INFO
Reads the computer name
- YogaDNSSetupv1.47.tmp (PID: 7408)
- YogaDNSSetupv1.47.tmp (PID: 7564)
- drvinst.exe (PID: 4740)
- drvinst.exe (PID: 5064)
- YogaDNS.exe (PID: 1132)
Checks supported languages
- YogaDNSSetupv1.47.tmp (PID: 7408)
- YogaDNSSetupv1.47.exe (PID: 7388)
- YogaDNSSetupv1.47.exe (PID: 7540)
- YogaDNSSetupv1.47.tmp (PID: 7564)
- YogaDNS.exe (PID: 8052)
- drvinst.exe (PID: 4740)
- drvinst.exe (PID: 5064)
- YogaDNS.exe (PID: 1132)
- YogaDNS.exe (PID: 3884)
Create files in a temporary directory
- YogaDNSSetupv1.47.exe (PID: 7388)
- YogaDNSSetupv1.47.exe (PID: 7540)
- YogaDNSSetupv1.47.tmp (PID: 7564)
- rundll32.exe (PID: 8184)
Process checks computer location settings
- YogaDNSSetupv1.47.tmp (PID: 7408)
Compiled with Borland Delphi (YARA)
- YogaDNSSetupv1.47.exe (PID: 7540)
- YogaDNSSetupv1.47.tmp (PID: 7564)
- YogaDNSSetupv1.47.exe (PID: 7388)
- YogaDNSSetupv1.47.tmp (PID: 7408)
Detects InnoSetup installer (YARA)
- YogaDNSSetupv1.47.tmp (PID: 7564)
- YogaDNSSetupv1.47.exe (PID: 7388)
- YogaDNSSetupv1.47.tmp (PID: 7408)
- YogaDNSSetupv1.47.exe (PID: 7540)
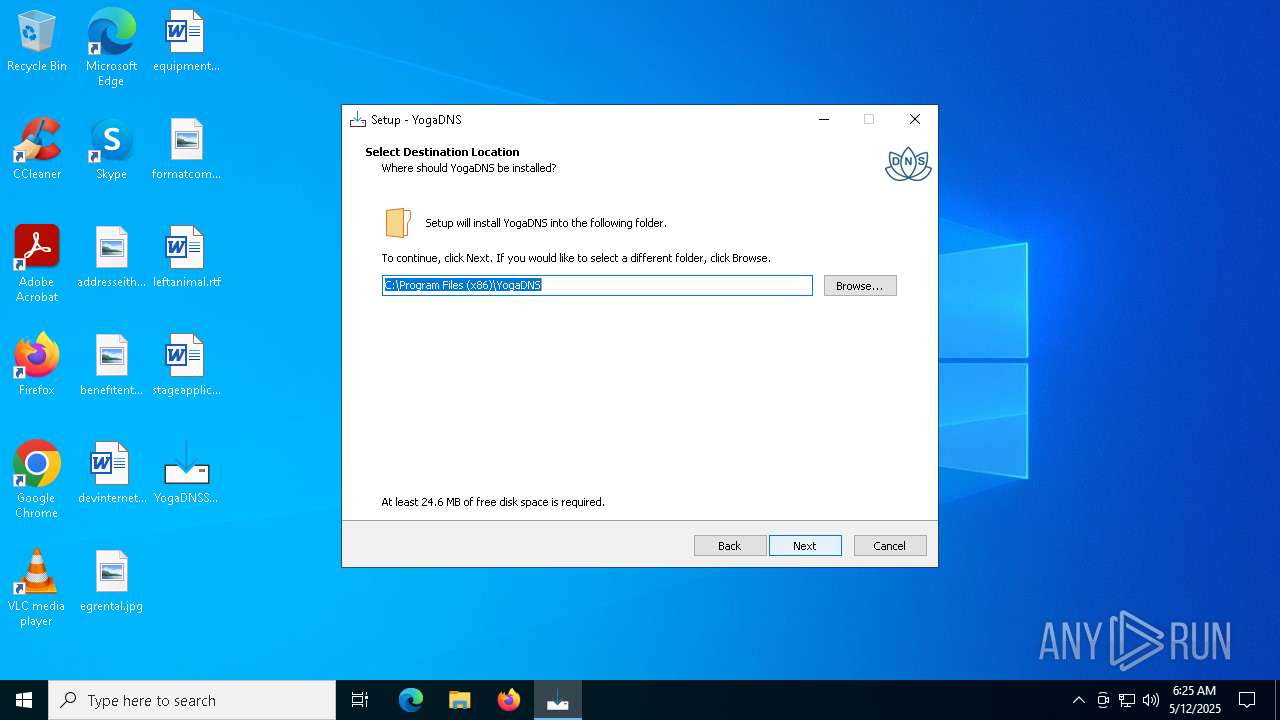
Creates files in the program directory
- YogaDNSSetupv1.47.tmp (PID: 7564)
The sample compiled with english language support
- YogaDNSSetupv1.47.tmp (PID: 7564)
- rundll32.exe (PID: 8184)
- drvinst.exe (PID: 4740)
- drvinst.exe (PID: 5064)
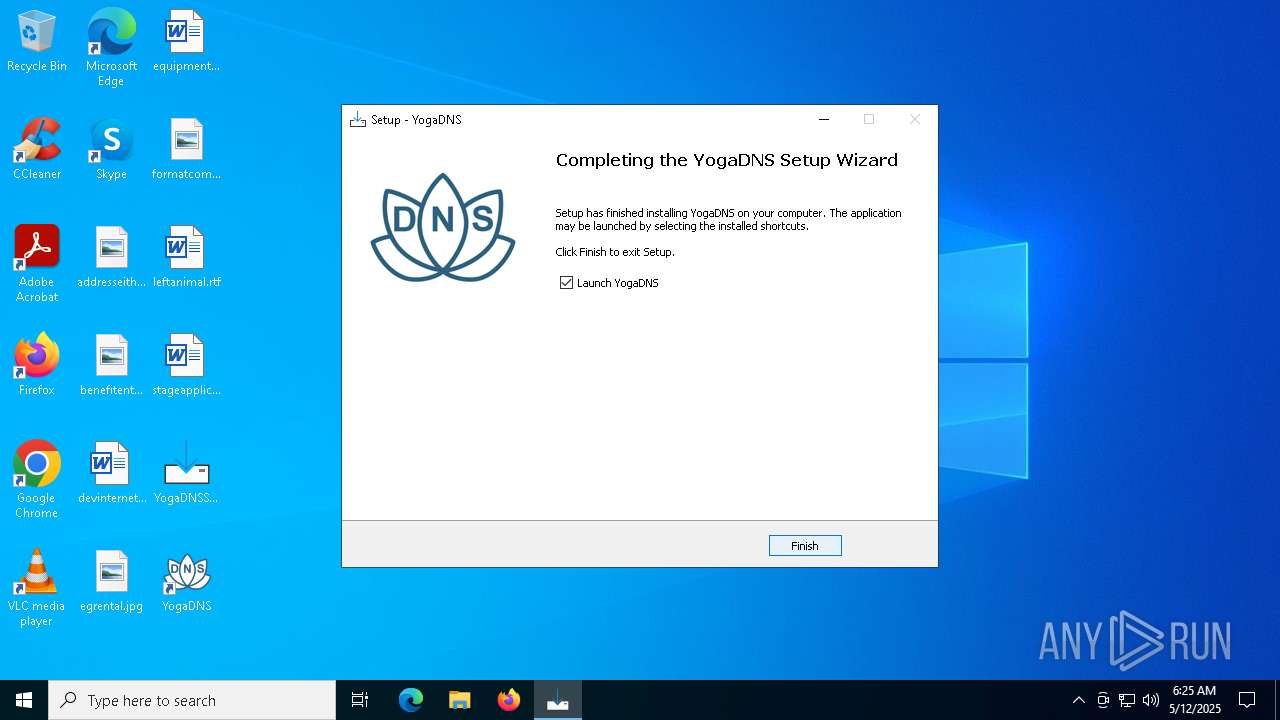
Auto-launch of the file from Registry key
- YogaDNSSetupv1.47.tmp (PID: 7564)
- rundll32.exe (PID: 8184)
Creates a software uninstall entry
- YogaDNSSetupv1.47.tmp (PID: 7564)
Reads the software policy settings
- drvinst.exe (PID: 4740)
- YogaDNS.exe (PID: 1132)
- slui.exe (PID: 5376)
Reads the machine GUID from the registry
- drvinst.exe (PID: 4740)
- YogaDNS.exe (PID: 1132)
Reads security settings of Internet Explorer
- runonce.exe (PID: 2152)
Manual execution by a user
- YogaDNS.exe (PID: 1132)
- grpconv.exe (PID: 4408)
Reads the time zone
- runonce.exe (PID: 2152)
Disables trace logs
- YogaDNS.exe (PID: 1132)
Checks proxy server information
- YogaDNS.exe (PID: 1132)
- slui.exe (PID: 5376)
Creates files or folders in the user directory
- YogaDNS.exe (PID: 1132)
Application based on Golang
- YogaDNS.exe (PID: 1132)
Detects GO elliptic curve encryption (YARA)
- YogaDNS.exe (PID: 1132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:03 08:09:11+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 89088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.47.0.1 |
| ProductVersionNumber: | 1.47.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
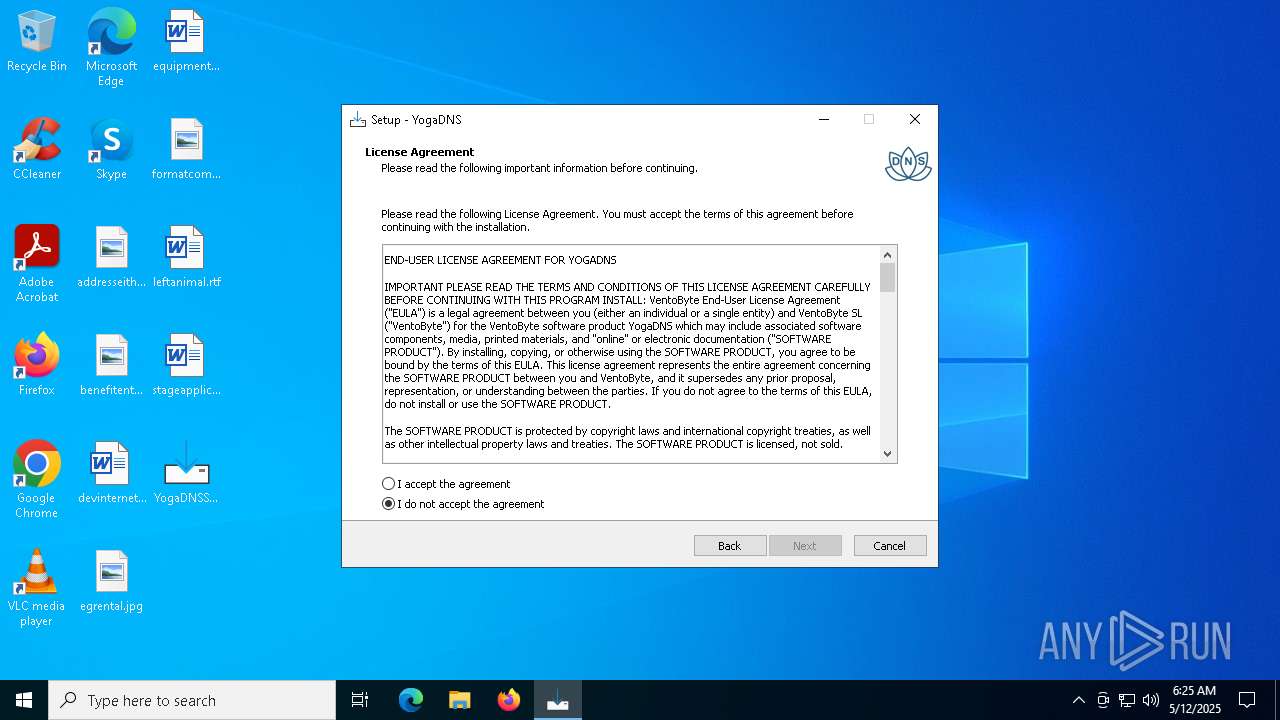
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | VentoByte SL |
| FileDescription: | YogaDNS Setup |
| FileVersion: | 1.47.0.1 |
| LegalCopyright: | Copyright © 2018-2025 VentoByte SL. All rights reserved. |
| OriginalFileName: | |
| ProductName: | YogaDNS |
| ProductVersion: | 1.47 |
Total processes
152
Monitored processes
21
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | ipconfig /flushdns | C:\Windows\SysWOW64\ipconfig.exe | — | YogaDNS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\YogaDNS\YogaDNS.exe" /AutoRun | C:\Program Files (x86)\YogaDNS\YogaDNS.exe | explorer.exe | ||||||||||||
User: admin Company: VentoByte SL Integrity Level: MEDIUM Description: YogaDNS Version: 1.47.0.1 Modules
| |||||||||||||||
| 1452 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ipconfig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2152 | "C:\WINDOWS\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3272 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ipconfig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | "C:\Program Files (x86)\YogaDNS\YogaDNS.exe" /ShowWnd | C:\Program Files (x86)\YogaDNS\YogaDNS.exe | — | YogaDNSSetupv1.47.tmp | |||||||||||
User: admin Company: VentoByte SL Integrity Level: MEDIUM Description: YogaDNS Exit code: 0 Version: 1.47.0.1 Modules
| |||||||||||||||
| 4408 | grpconv -o | C:\Windows\System32\grpconv.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4740 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{f1425c95-6e44-924b-99e4-f7f3b5dbbf9c}\DnsFltEngineDrv.inf" "9" "48ceef827" "00000000000001E4" "WinSta0\Default" "00000000000001CC" "208" "C:\Program Files (x86)\YogaDNS\Driver" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5064 | DrvInst.exe "8" "4" "C:\WINDOWS\System32\DriverStore\FileRepository\dnsfltenginedrv.inf_amd64_70fcb7f63230c89c\dnsfltenginedrv.inf" "0" "48ceef827" "00000000000001CC" "WinSta0\Default" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 141
Read events
12 093
Write events
46
Delete events
2
Modification events
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | YogaDNS |
Value: "C:\Program Files (x86)\YogaDNS\YogaDNS.exe" /AutoRun | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Initex\YogaDNS\Settings |
| Operation: | write | Name: | UpdateCheck |
Value: 1 | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{642D9E44-C22E-4F97-9C5C-FDD97BF60891}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.0 | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{642D9E44-C22E-4F97-9C5C-FDD97BF60891}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\YogaDNS | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{642D9E44-C22E-4F97-9C5C-FDD97BF60891}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\YogaDNS\ | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{642D9E44-C22E-4F97-9C5C-FDD97BF60891}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: YogaDNS | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{642D9E44-C22E-4F97-9C5C-FDD97BF60891}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{642D9E44-C22E-4F97-9C5C-FDD97BF60891}_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: autostart,updates,desktopicon | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{642D9E44-C22E-4F97-9C5C-FDD97BF60891}_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (7564) YogaDNSSetupv1.47.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{642D9E44-C22E-4F97-9C5C-FDD97BF60891}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
Executable files
20
Suspicious files
20
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7564 | YogaDNSSetupv1.47.tmp | C:\Users\admin\AppData\Local\Temp\is-BQUI3.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7564 | YogaDNSSetupv1.47.tmp | C:\Program Files (x86)\YogaDNS\is-S9QPO.tmp | executable | |
MD5:88C54E70857DB7938054CD6F5492BA50 | SHA256:F98F28977104C3DBE806FF7A9182A6668C5D346CE47ED5DACC9AB7460141F3B2 | |||
| 7564 | YogaDNSSetupv1.47.tmp | C:\Program Files (x86)\YogaDNS\root.key | text | |
MD5:240DF71B1A110C4DCEFFC1B77751B781 | SHA256:06C74EF5EF53344C78C9AF2B29DC458A2ABE93F1BFF429705955C033E7A0686F | |||
| 7564 | YogaDNSSetupv1.47.tmp | C:\Program Files (x86)\YogaDNS\is-2TOFR.tmp | executable | |
MD5:0FF3D040B249F0C87A44A9A3B124009B | SHA256:514332330249BA4EAC10F3EA53D6214C6CB917B9EEEBFB9A6922A6E2805A3691 | |||
| 7564 | YogaDNSSetupv1.47.tmp | C:\Program Files (x86)\YogaDNS\public-resolvers.md | text | |
MD5:87266FAFF9BEA0D9464D17AE6F99C742 | SHA256:692184F7D1272B8D1EC73A56C91D6C94C4E8F2C49FD1BE6DD3F6D75BFC48574F | |||
| 7540 | YogaDNSSetupv1.47.exe | C:\Users\admin\AppData\Local\Temp\is-3OC6E.tmp\YogaDNSSetupv1.47.tmp | executable | |
MD5:0FF3D040B249F0C87A44A9A3B124009B | SHA256:514332330249BA4EAC10F3EA53D6214C6CB917B9EEEBFB9A6922A6E2805A3691 | |||
| 7388 | YogaDNSSetupv1.47.exe | C:\Users\admin\AppData\Local\Temp\is-C720Q.tmp\YogaDNSSetupv1.47.tmp | executable | |
MD5:0FF3D040B249F0C87A44A9A3B124009B | SHA256:514332330249BA4EAC10F3EA53D6214C6CB917B9EEEBFB9A6922A6E2805A3691 | |||
| 7564 | YogaDNSSetupv1.47.tmp | C:\Program Files (x86)\YogaDNS\is-QU8VV.tmp | text | |
MD5:63425B993E903CA712124B3E4DF56B9F | SHA256:4849089C9D47D5240228C00FE5C8EE9C7FEF402780FBC442FE708F1C142E1C2D | |||
| 7564 | YogaDNSSetupv1.47.tmp | C:\Program Files (x86)\YogaDNS\Driver\DnsFltEngineDrv.sys | executable | |
MD5:E280E289AED282E8B611E91732B0C620 | SHA256:8A06B07E861304616EC3B8A49CDF82BB7F2817E4BA32EEC6CE784023B0D86F9E | |||
| 7564 | YogaDNSSetupv1.47.tmp | C:\Program Files (x86)\YogaDNS\YogaDNS.exe | executable | |
MD5:A9899BFA1B5DF045AC7FC668F9893DDF | SHA256:1D3668CF38150782FE3D31240117D4DDEFA13B856EA8C858148019830BFB4A06 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
56
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
7892 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 23.216.77.39:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 23.216.77.39:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
7892 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4812 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4812 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.yogadns.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1132 | YogaDNS.exe | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |