| File name: | 02319807_1 |
| Full analysis: | https://app.any.run/tasks/0f52521b-3f35-46ce-8519-dfd6bce1d536 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2020, 23:16:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
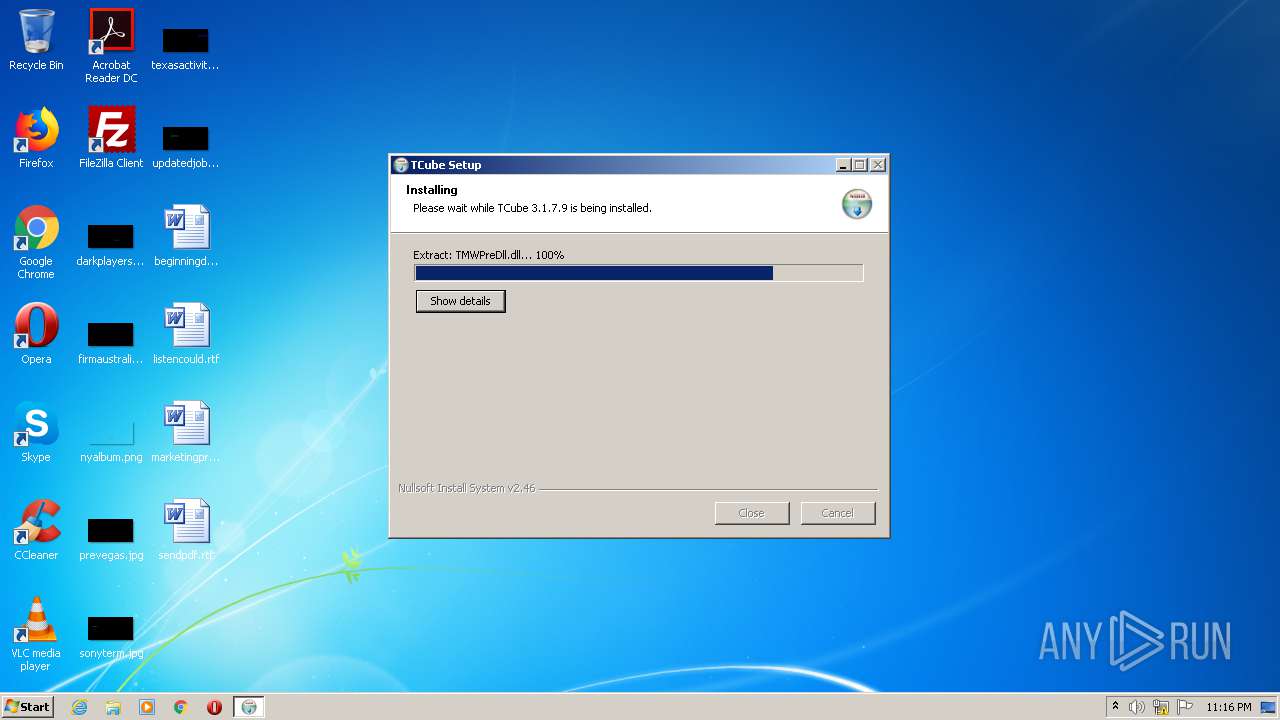
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | AC264C2D9B98298964F960AB7ED94801 |
| SHA1: | 67F1A3239AF8A43EA1FBE34F684A8ABC761974A4 |
| SHA256: | C78D186549F147D499F88F7F8D65CDB3515AACD84FFE6CB13C5ED1E4958E721F |
| SSDEEP: | 196608:rPMey+ii/GB92WVa8xpgMFcZjJ9YM/v6VE9l:rPMetioQ9lBDO96MH6WP |
MALICIOUS
Drops executable file immediately after starts
- 02319807_1.exe (PID: 4080)
- TCubeServiceMgr.exe (PID: 2504)
Loads dropped or rewritten executable
- 02319807_1.exe (PID: 4080)
- TCubeUpdater.exe (PID: 3236)
- TCubeServiceMgr.exe (PID: 2504)
- regsvr32.exe (PID: 2280)
- TCubeObserver.exe (PID: 3984)
Application was dropped or rewritten from another process
- TCubeUpdater.exe (PID: 3236)
- TCubeServiceMgr.exe (PID: 2504)
- importpfx.exe (PID: 3996)
- importpfx.exe (PID: 3472)
- TCubeDummy.exe (PID: 2116)
- TCubeObserver.exe (PID: 3984)
Actions looks like stealing of personal data
- TCubeUpdater.exe (PID: 3236)
Changes settings of System certificates
- importpfx.exe (PID: 3472)
- importpfx.exe (PID: 3996)
Registers / Runs the DLL via REGSVR32.EXE
- 02319807_1.exe (PID: 4080)
Changes internet zones settings
- 02319807_1.exe (PID: 4080)
- TCubeObserver.exe (PID: 3984)
SUSPICIOUS
Drops a file that was compiled in debug mode
- 02319807_1.exe (PID: 4080)
- TCubeUpdater.exe (PID: 3236)
- TCubeServiceMgr.exe (PID: 2504)
Creates a software uninstall entry
- 02319807_1.exe (PID: 4080)
Drops a file with too old compile date
- 02319807_1.exe (PID: 4080)
Creates files in the Windows directory
- TCubeUpdater.exe (PID: 3236)
- 02319807_1.exe (PID: 4080)
- TCubeServiceMgr.exe (PID: 2504)
Executable content was dropped or overwritten
- 02319807_1.exe (PID: 4080)
- TCubeUpdater.exe (PID: 3236)
- TCubeServiceMgr.exe (PID: 2504)
Creates files in the user directory
- TCubeUpdater.exe (PID: 3236)
Executed as Windows Service
- TCubeServiceMgr.exe (PID: 2504)
Removes files from Windows directory
- TCubeServiceMgr.exe (PID: 2504)
Creates files in the program directory
- importpfx.exe (PID: 3996)
- importpfx.exe (PID: 3472)
Modifies the open verb of a shell class
- 02319807_1.exe (PID: 4080)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.7.9 |
| ProductVersionNumber: | 3.1.7.9 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
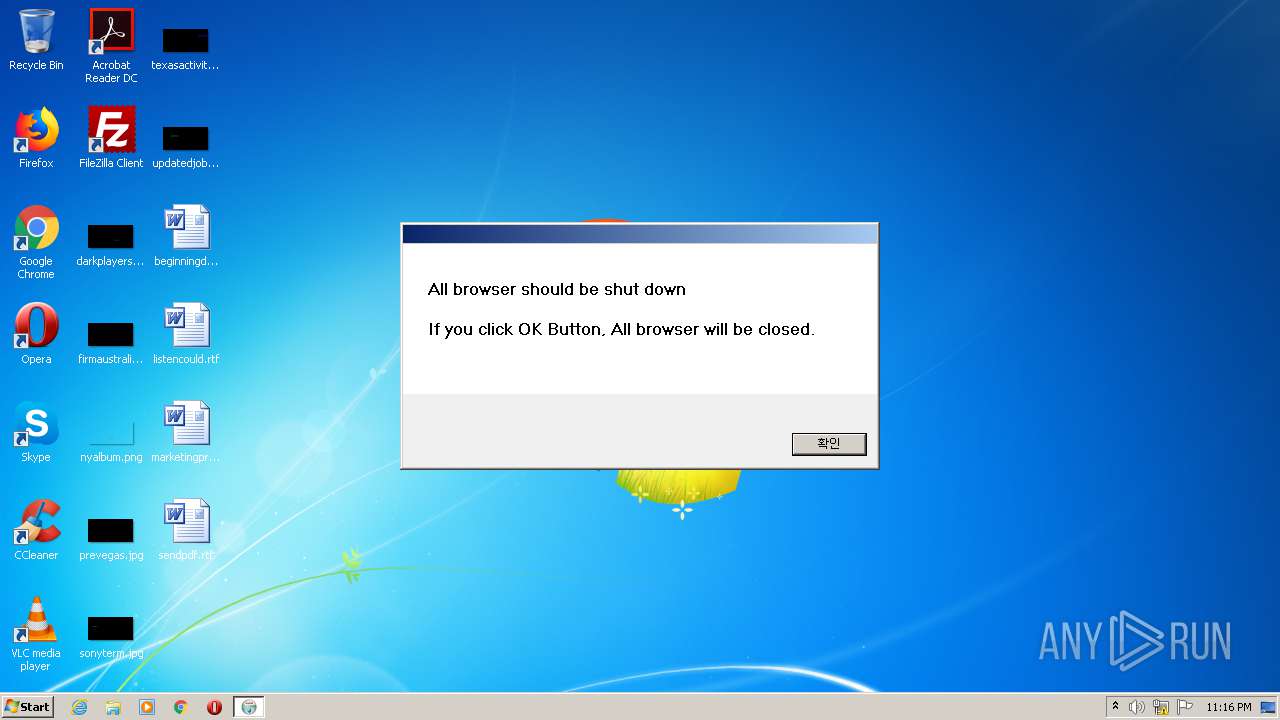
| CharacterSet: | Windows, Korea (Shift - KSC 5601) |
| CompanyName: | Teruten |
| FileDescription: | TCube |
| FileVersion: | 3.1.7.9 |
| LegalCopyright: | Teruten.inc |
| ProductName: | TCube |
| ProductVersion: | 3.1.7.9 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
| CompanyName: | Teruten |
| FileDescription: | TCube |
| FileVersion: | 3.1.7.9 |
| LegalCopyright: | Teruten.inc |
| ProductName: | TCube |
| ProductVersion: | 3.1.7.9 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003D000 | 0x00004728 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.70595 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
48
Monitored processes
10
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2112 | "C:\Users\admin\AppData\Local\Temp\02319807_1.exe" | C:\Users\admin\AppData\Local\Temp\02319807_1.exe | — | explorer.exe | |||||||||||
User: admin Company: Teruten Integrity Level: MEDIUM Description: TCube Exit code: 3221226540 Version: 3.1.7.9 Modules
| |||||||||||||||
| 2116 | C:\Windows\Teruten\TCube\TCubeDummy.exe 0 | C:\Windows\Teruten\TCube\TCubeDummy.exe | — | TCubeServiceMgr.exe | |||||||||||
User: SYSTEM Company: Teruten Integrity Level: SYSTEM Description: TCubeDummy Exit code: 0 Version: 3.1.7.9 Modules
| |||||||||||||||
| 2280 | regsvr32.exe /s "C:\Windows\Teruten\TCube\TCube.ocx" | C:\Windows\system32\regsvr32.exe | — | 02319807_1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | C:\Windows\Teruten\TCube\TCubeServiceMgr.exe | C:\Windows\Teruten\TCube\TCubeServiceMgr.exe | services.exe | ||||||||||||
User: SYSTEM Company: Teruten Integrity Level: SYSTEM Description: TCubeServiceMgr Exit code: 0 Version: 3.1.7.9 Modules
| |||||||||||||||
| 3236 | C:\Windows\Teruten\TCube\TCubeUpdater.exe | C:\Windows\Teruten\TCube\TCubeUpdater.exe | 02319807_1.exe | ||||||||||||
User: admin Company: Teruten Integrity Level: HIGH Description: TCubeUpdater Exit code: 0 Version: 3.1.7.9 Modules
| |||||||||||||||
| 3472 | -f "C:\Windows\Teruten\TCube\localhost_xp.p12" -p teruten123 -t MACHINE -s root | C:\Windows\Teruten\TCube\importpfx.exe | — | TCubeServiceMgr.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3888 | regsvr32.exe /s "C:\Windows\Teruten\TCube\TCube64.ocx" | C:\Windows\system32\regsvr32.exe | — | 02319807_1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | C:\Windows\Teruten\TCube\TCubeObserver.exe | C:\Windows\Teruten\TCube\TCubeObserver.exe | — | TCubeDummy.exe | |||||||||||
User: SYSTEM Company: Teruten Integrity Level: SYSTEM Description: TCubeObserver Exit code: 0 Version: 3.1.7.9 Modules
| |||||||||||||||
| 3996 | -f "C:\Windows\Teruten\TCube\localhost.p12" -p teruten123 -t MACHINE -s root | C:\Windows\Teruten\TCube\importpfx.exe | — | TCubeServiceMgr.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\02319807_1.exe" | C:\Users\admin\AppData\Local\Temp\02319807_1.exe | explorer.exe | ||||||||||||
User: admin Company: Teruten Integrity Level: HIGH Description: TCube Exit code: 0 Version: 3.1.7.9 Modules
| |||||||||||||||
Total events
421
Read events
342
Write events
77
Delete events
2
Modification events
| (PID) Process: | (4080) 02319807_1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TCube |
| Operation: | write | Name: | DisplayName |
Value: TCube 3.1.7.9 | |||
| (PID) Process: | (4080) 02319807_1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TCube |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\Teruten\TCube\Uninstall.exe | |||
| (PID) Process: | (3996) importpfx.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3996) importpfx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\C11B29E8C46BB97A724256BE419FAB7E1E9F5C08 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000C11B29E8C46BB97A724256BE419FAB7E1E9F5C080200000001000000CC0000001C0000006C00000001000000000000000000000000000000010000007B00410043004300310035003400340031002D0035003100330032002D0034003000440037002D0039004500430042002D004500360046003800420045003100350043003700350036007D00000000004D006900630072006F0073006F0066007400200045006E00680061006E006300650064002000430072007900700074006F0067007200610070006800690063002000500072006F00760069006400650072002000760031002E0030000000000020000000010000008D0300003082038930820271A003020102020900A634A1CF3DA5B19A300D06092A864886F70D01010B05003074310B3009060355040613024B52310E300C06035504080C0553656F756C310E300C06035504070C0553656F756C3110300E060355040A0C075465727574656E3112301006035504030C093132372E302E302E31311F301D06092A864886F70D010901161063756265407465727574656E2E636F6D301E170D3137303432353032313733305A170D3437303431383032313733305A3074310B3009060355040613024B52310E300C06035504080C0553656F756C310E300C06035504070C0553656F756C3110300E060355040A0C075465727574656E3112301006035504030C093132372E302E302E31311F301D06092A864886F70D010901161063756265407465727574656E2E636F6D30820122300D06092A864886F70D01010105000382010F003082010A0282010100DE840CAE45CCA157573DF64F9AEDAEFC67B8038C06637DB983DD69492591A4B046F20D16CDC28124544976F1E022BCFBB02F93A1F276C1E1E3FA50C125E0B1A7D3602110E38A5FDDD3377D0F1CB5BC3F3E8FCA37828302195F851EC59F130AD056C52349D4C7F3612C1890488F239B48497175492CD1DBE5509CCBB69F26A5A8CBFD7AFE016053B677E3C7EC2C9871D526CDD6D9477B3361EBCF7B9946B979CF261456CB921FEFA818EFA13A897A9199D14DDD30A7B38DD7CCEAF069A8513422BECC2CE1D449BDDC2DA5C777F1C9CF0BFBA0D55F712F8D15486FF5E2DF716ECD64DD14218F50FF084F24DBC5BC0C0E6C08027FF89D21E525D6F792FB9FC9A5CB0203010001A31E301C301A0603551D110413301182093132372E302E302E3187047F000001300D06092A864886F70D01010B05000382010100CFC5ADBDE897B9663FBFC94FE218505121DD8F281260740B25589ABE95C68E93906B689FF706C0212E445B7364BD2ECC7A84FF61E633887364469C51E25E4AAA2D9E921DE136227E39FA78EB72B3FC3A03D8CCF817F73DD4763E6A516D0F142D888E7CF6031ABE5B251132E9709B8FF137BFB2C1F16665E6A3CE255276702BF6DFE11D037097331952515D8FACCA469F405CC2EEB4BB805EAC5CD1169E0804E9ECAA1583AC283C73123E0DBB39547E65FFC80068EE2FE8ED751B7D2CF6A6DAC48F1A92A052388CCE9E559A1878D8BD95CD9816EF1EE42F6143B9C6E1FE1FB670CDB649ACC4C3AFDC97875080E9EBFB9FC80C12F1C5E84290C603CE047D536D80 | |||
| (PID) Process: | (3996) importpfx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\C11B29E8C46BB97A724256BE419FAB7E1E9F5C08 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3472) importpfx.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3472) importpfx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\57FD3FEE8F473F7EBE0DB8A81A380E4456A5919F |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000057FD3FEE8F473F7EBE0DB8A81A380E4456A5919F0200000001000000CC0000001C0000006C00000001000000000000000000000000000000010000007B00460038004400390030003300310044002D0035004100420042002D0034004600340038002D0038003700460037002D004400450042003400350037003200450038003100420033007D00000000004D006900630072006F0073006F0066007400200045006E00680061006E006300650064002000430072007900700074006F0067007200610070006800690063002000500072006F00760069006400650072002000760031002E0030000000000020000000010000008C03000030820388308202700209008C28F4CD21A27886300D06092A864886F70D01010B0500308185310B3009060355040613024B52310E300C06035504080C054B6F726561310E300C06035504070C0553656F756C3110300E060355040A0C075465727574656E310C300A060355040B0C034465763112301006035504030C093132372E302E302E313122302006092A864886F70D010901161368697331343135407465727574656E2E636F6D301E170D3135303930393031333030355A170D3435303930313031333030355A308185310B3009060355040613024B52310E300C06035504080C054B6F726561310E300C06035504070C0553656F756C3110300E060355040A0C075465727574656E310C300A060355040B0C034465763112301006035504030C093132372E302E302E313122302006092A864886F70D010901161368697331343135407465727574656E2E636F6D30820122300D06092A864886F70D01010105000382010F003082010A0282010100EDB953B5A98859378E5A866ABB02E7D4C8C398E64CBCF37E8A60B5978EEE18BD6B492FBC23884DB57E156F14A5156FE351E4FABEA3B1D8E337D27EA271388C815E698D963EC753CE07313138B71AC910C0A578583509CA22F250A7871C0BFE3C863E288A72D9AE18F4CFEE5BEF5104FF860ACF48CCAB1FE53755824EBC36D5819AE4092E10A41F87501D697D8660B5A4480F39ABEEF5D99145F095062C1B5440D2887845A2998E4A9337712CDE81C1FF78CD859C840D39BD6DD833BA6C3A724943D2EC9C4A4E8191BAFF3C84D7F3B90BF3A51D50B6E384998C874AC35FAA7CA6A0EC05E6C89DA4C22DF9613E6B7769974656836C2EDCCE1AA864998D74475A8D0203010001300D06092A864886F70D01010B050003820101001227A6ECE4BDDABAD06B878680D6F4204484390F0951FE81DD176BB264FBD8373E5E526093141ADB5DF9D2CA616C738F05EA034BD8E07CDA07A230CAFD2ACA957681F4F10F4E1793E91AFBC54504A59B86A33BF4B7ADE5E63A7399C06EBFA7B0A49DAF1820B5A3A09281028C03E7E4B7A72413D2F13AC67125B854E7721D06F13CE265F76540D505584551FDE6C0384514FB5EFB3B38904E6D1DD0FFE92AEB52168AB1AE22ECF02659A098888E85F0BAE2D923139C3C8D939A2AE9F60C78C9B9AA2610901EF7486E94626BD2BE5097F90DF102313E50676F51EBC4A1ACB686EB05170A23E144A41E521A441A86CD71CB014B3B4F9C0A229FBE7A516F059DACB7 | |||
| (PID) Process: | (3472) importpfx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\57FD3FEE8F473F7EBE0DB8A81A380E4456A5919F |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2280) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{3092419C-E838-4FE0-9790-698E3788ED09}\1.0 |
| Operation: | write | Name: | (default) |
Value: TCube ActiveX ÄÁÆ®·Ñ ¸ðµâ | |||
| (PID) Process: | (2280) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{3092419C-E838-4FE0-9790-698E3788ED09}\1.0\FLAGS |
| Operation: | write | Name: | (default) |
Value: 2 | |||
Executable files
46
Suspicious files
4
Text files
12
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | 02319807_1.exe | C:\Windows\Teruten\TCube\TCubeDummy.exe | executable | |
MD5:— | SHA256:— | |||
| 4080 | 02319807_1.exe | C:\Windows\Teruten\TCube\TCube.ocx | executable | |
MD5:— | SHA256:— | |||
| 4080 | 02319807_1.exe | C:\Windows\Teruten\TCube\TCubeUpdater.exe | executable | |
MD5:— | SHA256:— | |||
| 4080 | 02319807_1.exe | C:\Users\admin\AppData\Local\Temp\nsk4805.tmp\CheckProcess.dll | executable | |
MD5:— | SHA256:— | |||
| 4080 | 02319807_1.exe | C:\Users\admin\AppData\Local\Temp\nsk4805.tmp\System.dll | executable | |
MD5:0FF5120F1AFD0F295C2BAA0F7192D3F8 | SHA256:4CA5BF1BEB4B802914C4D3E2F37861F6BA5ECF969CFEADF5855EDF58F647A721 | |||
| 4080 | 02319807_1.exe | C:\Users\admin\AppData\Local\Temp\nsk4805.tmp\KillProc.dll | executable | |
MD5:6C2B245E89428FB917A5805815A4054E | SHA256:0558BBDFE61EEFB680E8560A7D4B174447A9516098F9CD8B4C84BF1552CEE5C5 | |||
| 4080 | 02319807_1.exe | C:\Windows\Teruten\TCube\TCubeServiceMgrB.exe | executable | |
MD5:— | SHA256:— | |||
| 4080 | 02319807_1.exe | C:\Windows\Teruten\TCube\TModule.dll | executable | |
MD5:— | SHA256:— | |||
| 4080 | 02319807_1.exe | C:\Windows\Teruten\TCube\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 4080 | 02319807_1.exe | C:\Windows\Teruten\TCube\TCubeObserverB.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report