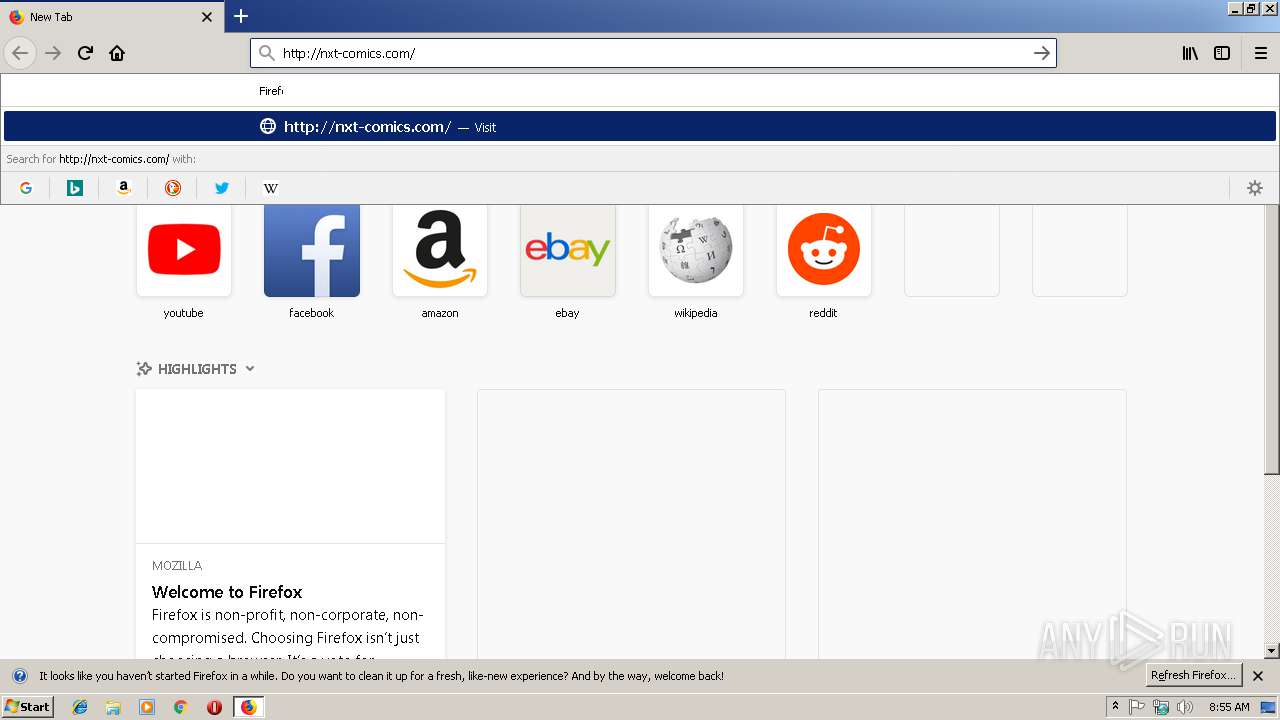
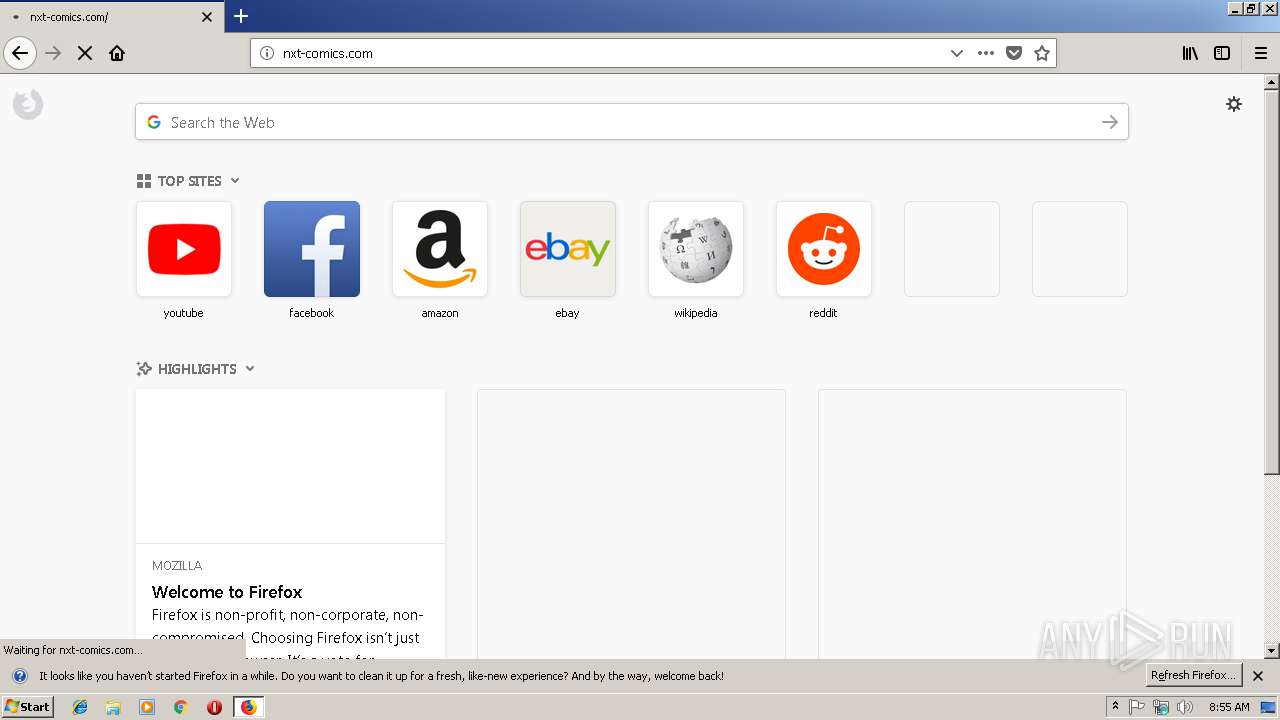
| URL: | http://nxt-comics.com |
| Full analysis: | https://app.any.run/tasks/0556b355-256c-4195-8dc8-ac1671ad3806 |
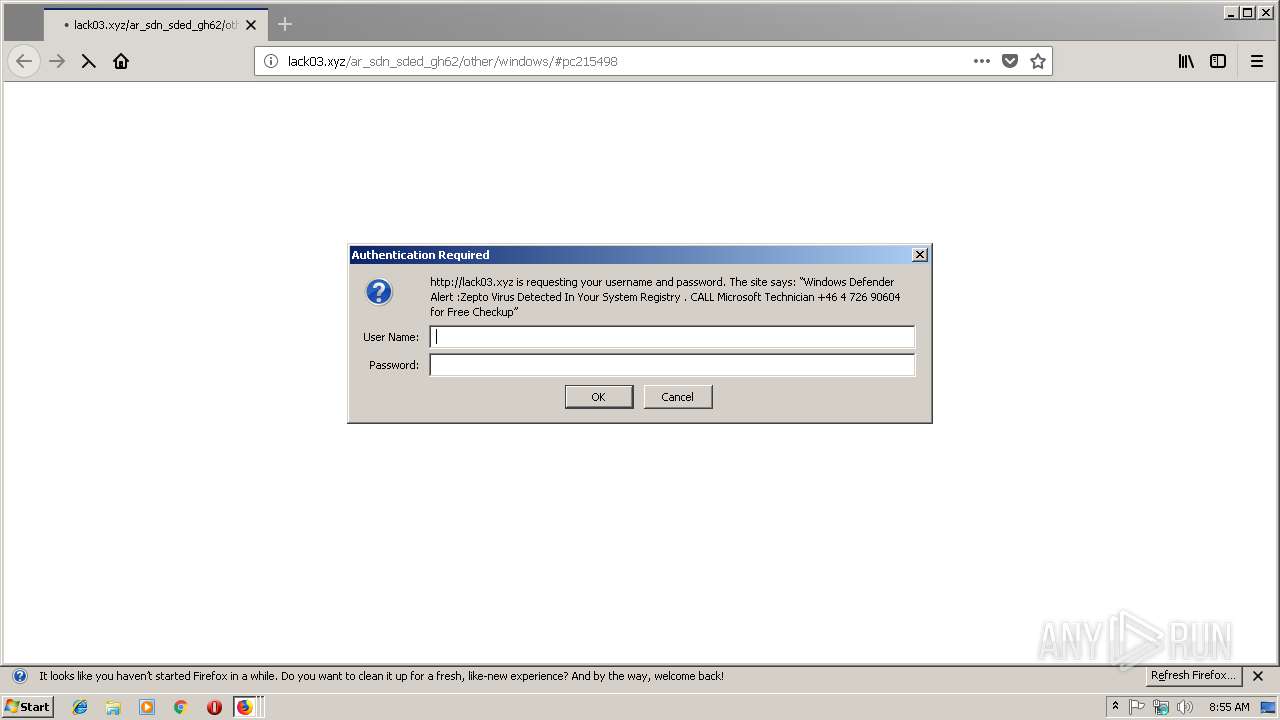
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2019, 08:54:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C769A1A6E9A3406BB1DE546A8EDB0B87 |
| SHA1: | 467464AFAB1FC8EFCEC6943FFBE42CF3B5BA5B9E |
| SHA256: | C781C15DD88A556FC877CF6A2D77B9A2ED8E273BDE5B815C6F8A2D0B79F6CB38 |
| SSDEEP: | 3:N1KQEKnT:CQ7nT |
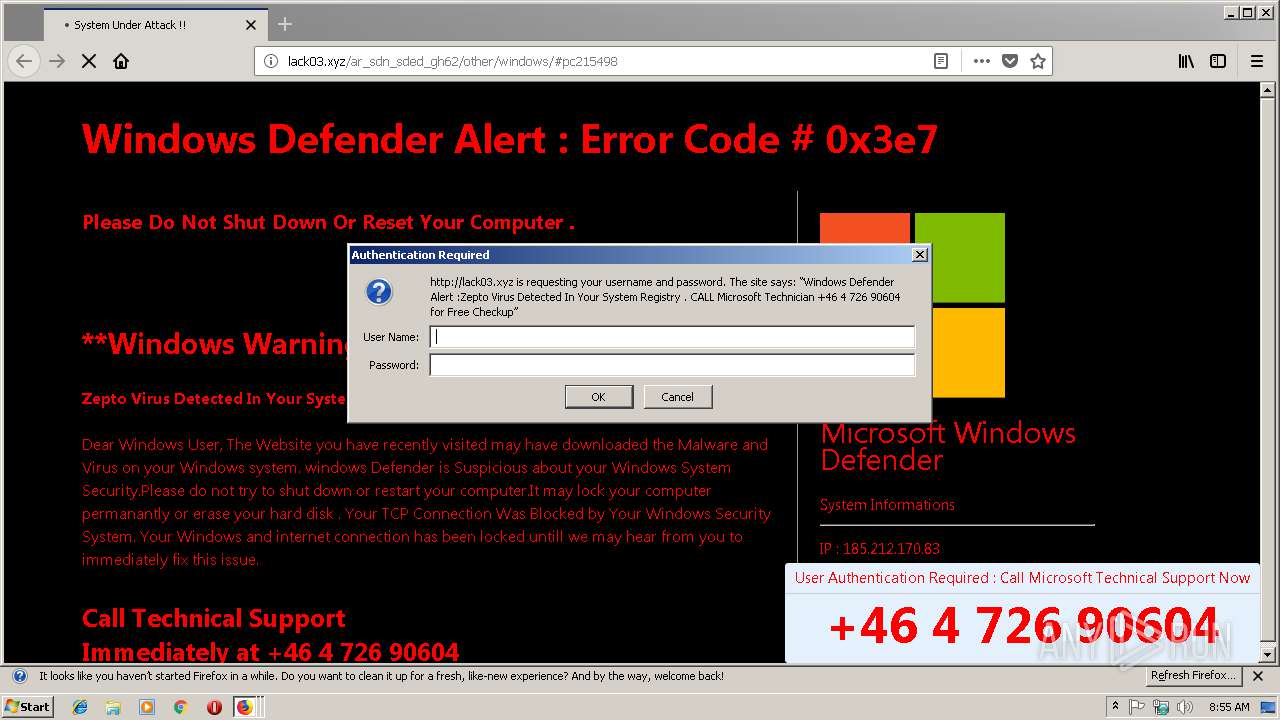
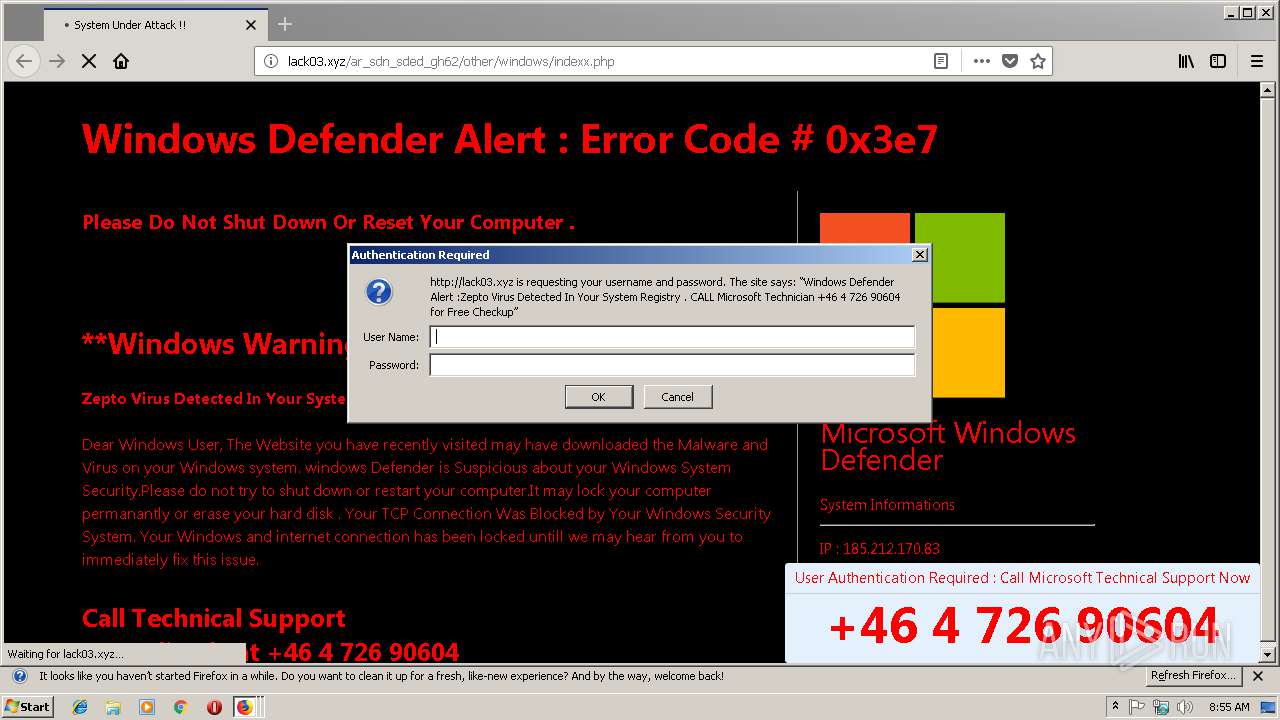
MALICIOUS
TECHSUPPORT was detected
- firefox.exe (PID: 1832)
SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3292)
- iexplore.exe (PID: 2836)
Changes internet zones settings
- iexplore.exe (PID: 2836)
Application launched itself
- iexplore.exe (PID: 2836)
- firefox.exe (PID: 1832)
Reads internet explorer settings
- iexplore.exe (PID: 3292)
Creates files in the user directory
- iexplore.exe (PID: 3292)
- iexplore.exe (PID: 2836)
- firefox.exe (PID: 1832)
Reads CPU info
- firefox.exe (PID: 1832)
- firefox.exe (PID: 3904)
- firefox.exe (PID: 3572)
- firefox.exe (PID: 2972)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 1832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1832 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1832.12.662832627\1294892053" -childID 3 -isForBrowser -prefsHandle 3104 -prefsLen 11808 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1832 "\\.\pipe\gecko-crash-server-pipe.1832" 3156 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2836 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3572 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1832.6.604162857\585963820" -childID 2 -isForBrowser -prefsHandle 2584 -prefsLen 11442 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1832 "\\.\pipe\gecko-crash-server-pipe.1832" 2600 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3904 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1832.0.1796822136\1750325932" -childID 1 -isForBrowser -prefsHandle 768 -prefsLen 8309 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1832 "\\.\pipe\gecko-crash-server-pipe.1832" 1480 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
Total events
625
Read events
564
Write events
57
Delete events
4
Modification events
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {84CDBF61-495B-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070300010012000800370004005E02 | |||
Executable files
0
Suspicious files
214
Text files
289
Unknown types
74
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\nxt-comics_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\themify-builder-style[1].css | text | |
MD5:60CA24AD7B716517FAB22FE7E3C52019 | SHA256:3D8CDD71C9ED72B44AA213F2853F11206E170CA535BD5153EB090A7CD7E2DE27 | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\nxt-comics_com[1].htm | html | |
MD5:405F2BB4DB8549874C8B5CD157A44F29 | SHA256:BD456118F0176544EC214F697D7A02F765CA97E1B67F7CA1F982A847FC3FD40D | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\style[1].css | text | |
MD5:01BEA18F29B034F80CEE1C3824FE3FC1 | SHA256:E8F453EAB76B3E8A0F9BF3184A6E96C561A41822D43EC9F3A2B41495D78EFE17 | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\media-queries[1].css | text | |
MD5:D25182AA20ED45EFC1A52BDBDC396F44 | SHA256:B6EF44089C0E70704C51F78B01EAE2D1C681720D82030E7F6473519B89FF4D68 | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\themify-customizer[1].css | text | |
MD5:A34A9503FF35E612C5FF771326AC5B01 | SHA256:660E7E0AC934D86DE1A973818105763AC73C9DD9B45EEBCB865B59491D94332A | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@nxt-comics[1].txt | text | |
MD5:42B4C325B66CED5CD7A3BFAC93FCA520 | SHA256:B8338DB60B9E58F65F450B57B86B0C0B69AC13AE52F68EF34A8DE70F6875F511 | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\themify.framework[1].css | text | |
MD5:3B5D2C0EC4D7E00924947171332ABE19 | SHA256:1E19AFF9D7BA045810C746E61AD2D71469758EB752061EC47B8590FA586429BE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
137
TCP/UDP connections
100
DNS requests
189
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2836 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
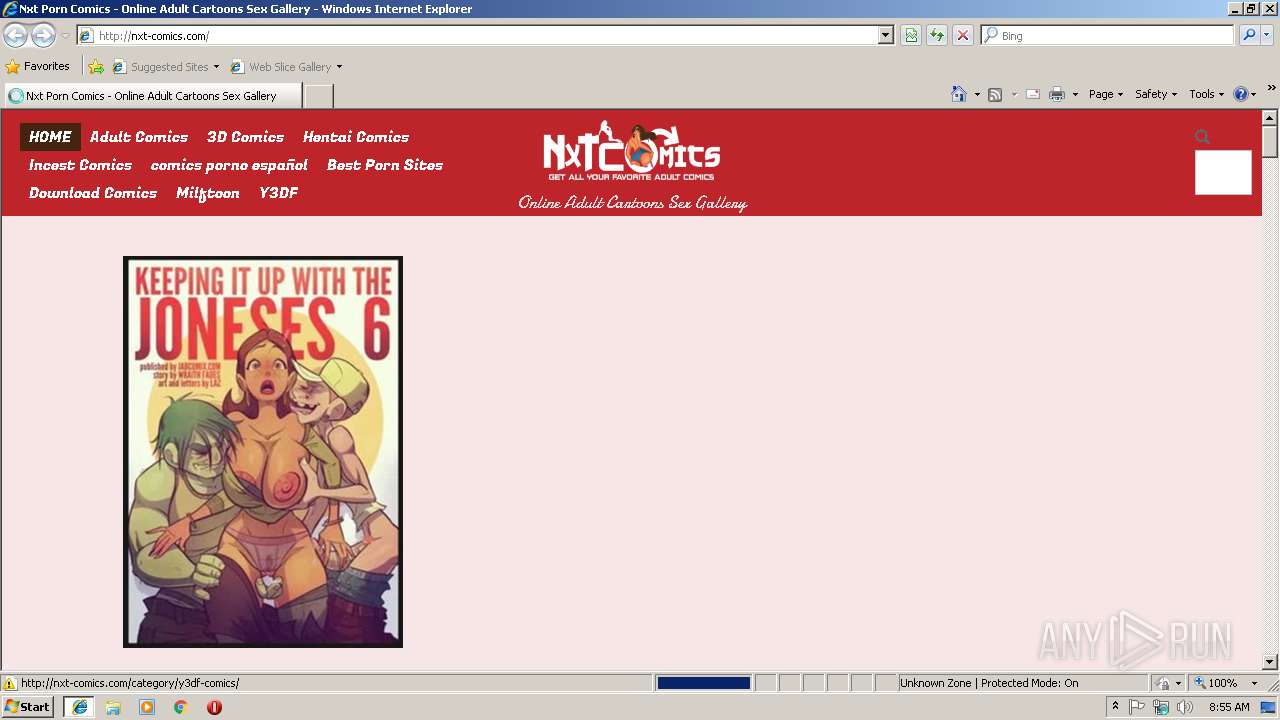
3292 | iexplore.exe | GET | 200 | 104.27.155.161:80 | http://nxt-comics.com/ | US | html | 10.1 Kb | whitelisted |
3292 | iexplore.exe | GET | 200 | 104.27.155.161:80 | http://nxt-comics.com/wp-content/themes/nxtcomics/themify/themify-builder/css/themify-builder-style.css | US | text | 11.3 Kb | whitelisted |
3292 | iexplore.exe | GET | 200 | 104.27.155.161:80 | http://nxt-comics.com/wp-content/plugins/contextual-related-posts/css/default-style.css | US | text | 434 b | whitelisted |
3292 | iexplore.exe | GET | 200 | 104.27.155.161:80 | http://nxt-comics.com/wp-content/themes/nxtcomics/themify/fontawesome/css/font-awesome.min.css | US | text | 5.99 Kb | whitelisted |
3292 | iexplore.exe | GET | 200 | 104.27.155.161:80 | http://nxt-comics.com/wp-content/themes/nxtcomics/style.css | US | text | 8.83 Kb | whitelisted |
3292 | iexplore.exe | GET | 200 | 104.27.155.161:80 | http://nxt-comics.com/wp-content/themes/nxtcomics/media-queries.css | US | text | 1.61 Kb | whitelisted |
3292 | iexplore.exe | GET | 200 | 172.217.22.10:80 | http://fonts.googleapis.com/css?family=Fugaz+One&subset=latin | US | text | 166 b | whitelisted |
3292 | iexplore.exe | GET | 200 | 104.27.155.161:80 | http://nxt-comics.com/wp-includes/js/jquery/jquery.js | US | text | 32.9 Kb | whitelisted |
3292 | iexplore.exe | GET | 200 | 104.27.155.161:80 | http://nxt-comics.com/wp-content/themes/nxtcomics/themify/themify-icons/themify-icons.css | US | text | 2.67 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2836 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3292 | iexplore.exe | 104.27.155.161:80 | nxt-comics.com | Cloudflare Inc | US | shared |
3292 | iexplore.exe | 172.217.22.10:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3292 | iexplore.exe | 151.139.236.208:443 | js.juicyads.com | netDNA | US | unknown |
3292 | iexplore.exe | 94.31.29.128:80 | cdn.popcash.net | netDNA | GB | malicious |
3292 | iexplore.exe | 172.217.21.227:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3292 | iexplore.exe | 99.192.193.4:80 | adserver.juicyads.com | MOJOHOST | US | unknown |
3292 | iexplore.exe | 104.20.2.47:443 | secure.statcounter.com | Cloudflare Inc | US | shared |
3292 | iexplore.exe | 104.20.3.47:80 | secure.statcounter.com | Cloudflare Inc | US | shared |
1832 | firefox.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
nxt-comics.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.popcash.net |
| whitelisted |
js.juicyads.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
adserver.juicyads.com |
| suspicious |
secure.statcounter.com |
| whitelisted |
c.statcounter.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1832 | firefox.exe | A Network Trojan was detected | ET CURRENT_EVENTS Tech Support Phone Scam Landing (err.mp3) Aug 12 2016 |