| File name: | Yihujbttaxryvvhwefnnvgbyoikrczk |
| Full analysis: | https://app.any.run/tasks/da82d0aa-a81a-40de-ba8e-1f9a8823233c |
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2024, 15:54:37 |
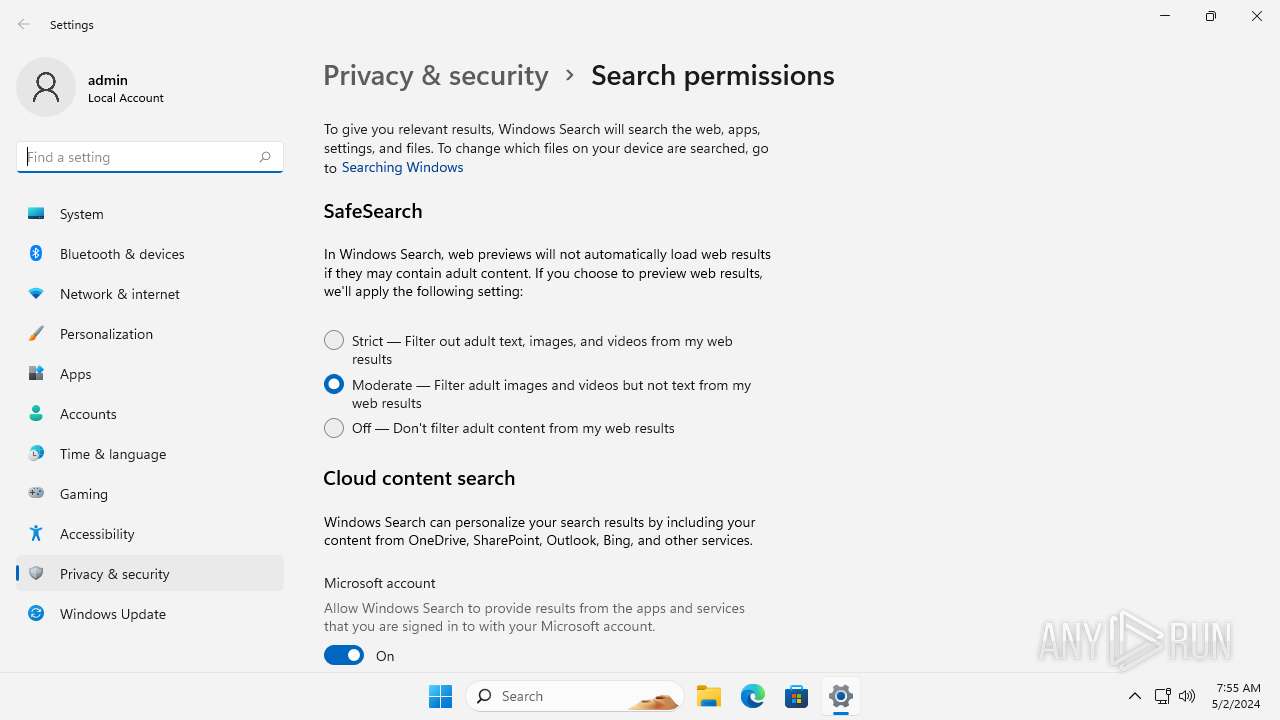
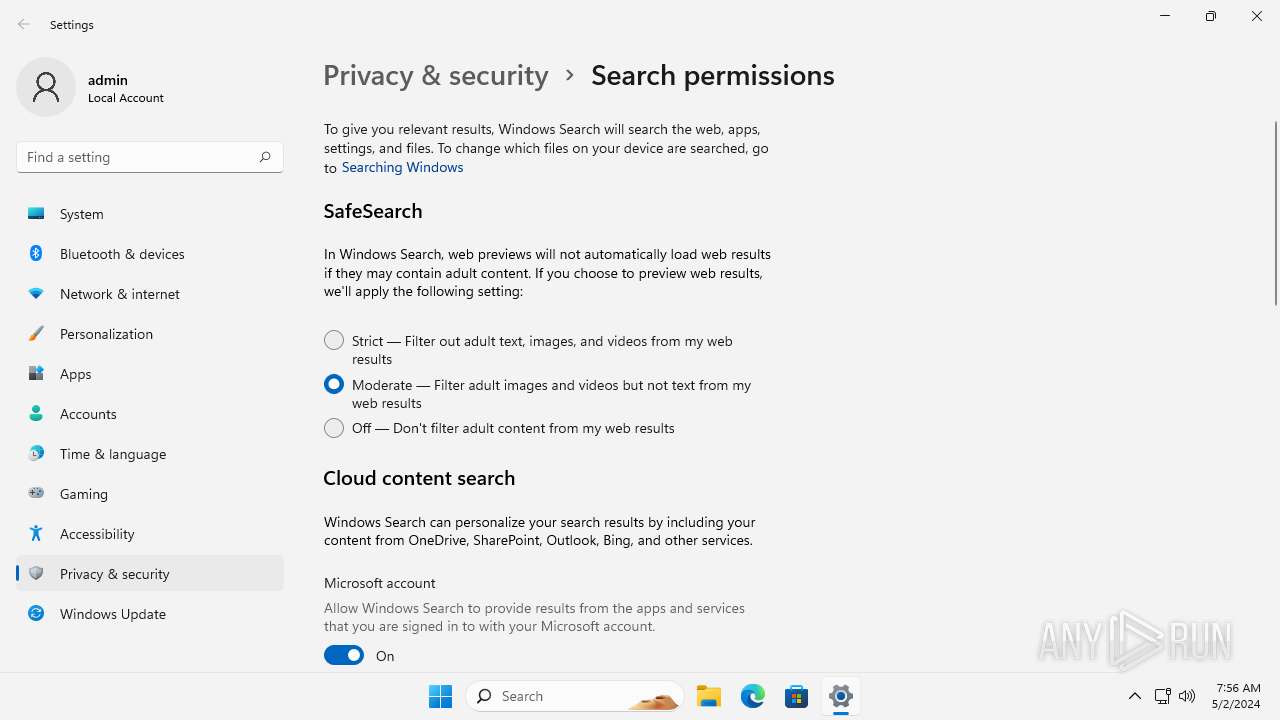
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 45EDE5054CC016B01ABF39C980DA71DE |
| SHA1: | BE7FA47E039EDF1F571516F5EBC80603701303E8 |
| SHA256: | C7673576998AEFBD890F9967E16C9AE084726F00EC9FC3BECC9FA33D5D52A794 |
| SSDEEP: | 12288:uE/gvz8mntHi9B/5lNbdUPGaiyATFv8iHw:uE/gvzhntHi9BRbdUPGaiTRv8iHw |
MALICIOUS
No malicious indicators.SUSPICIOUS
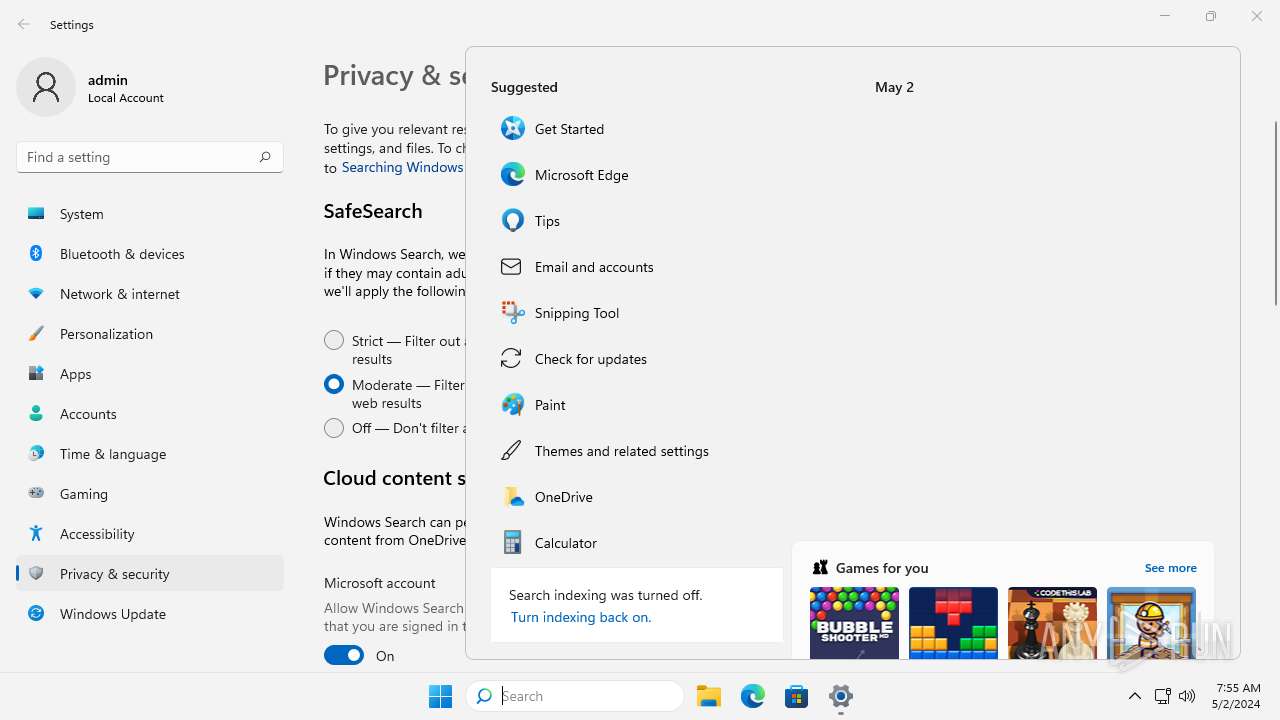
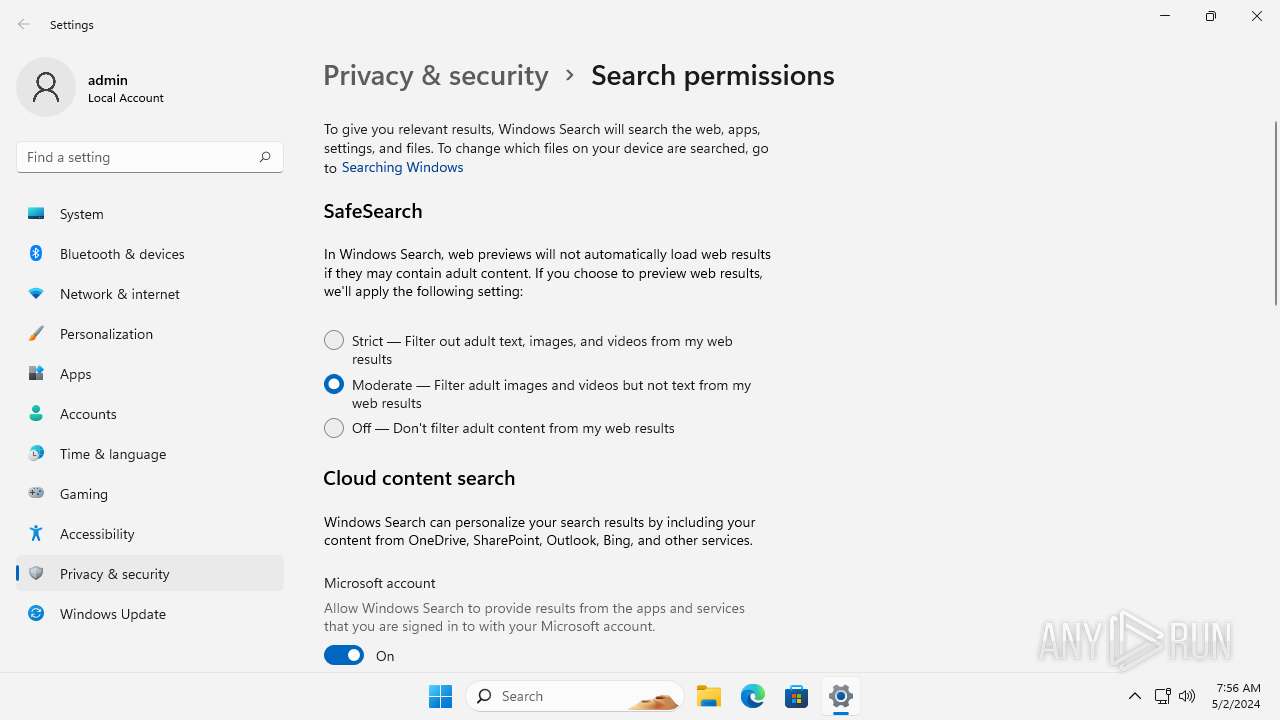
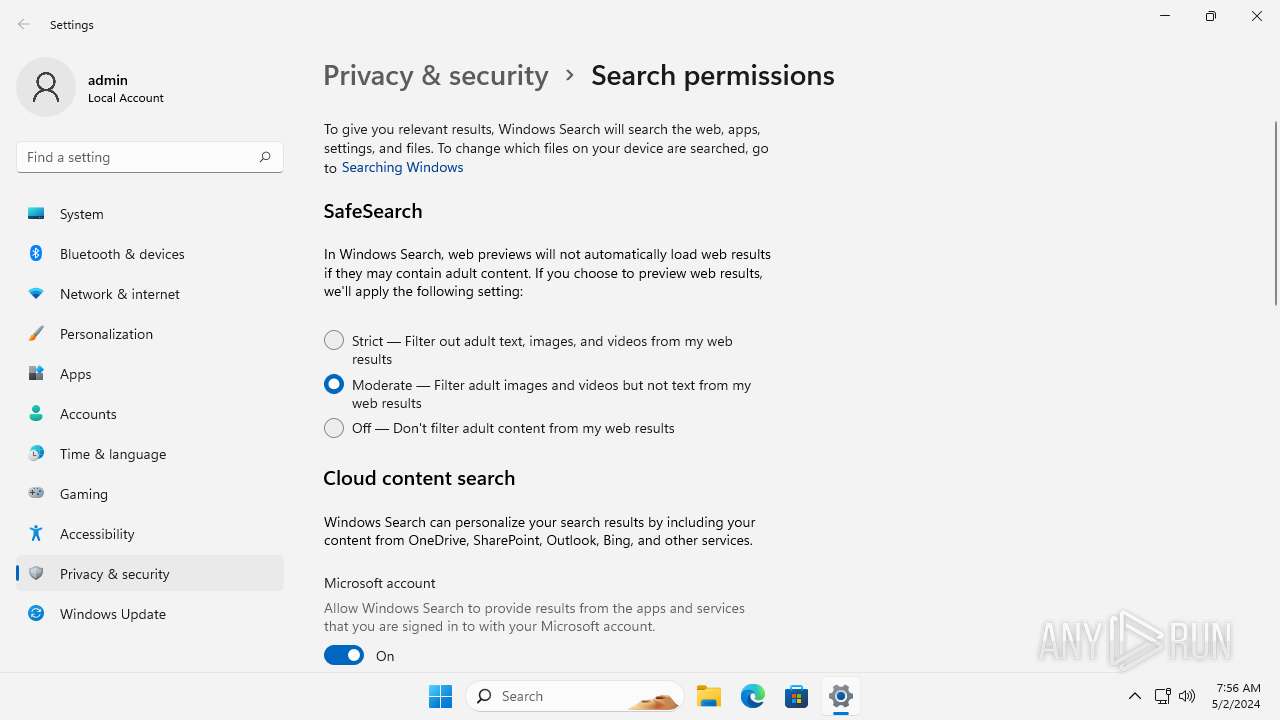
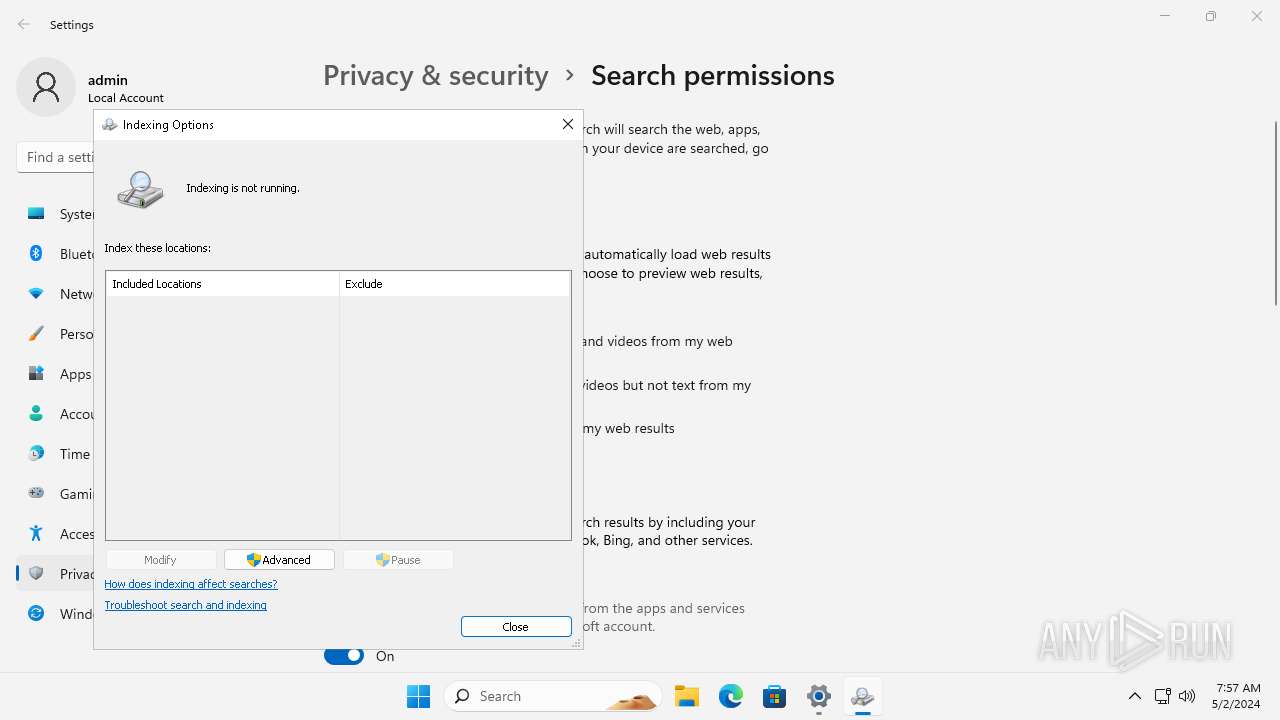
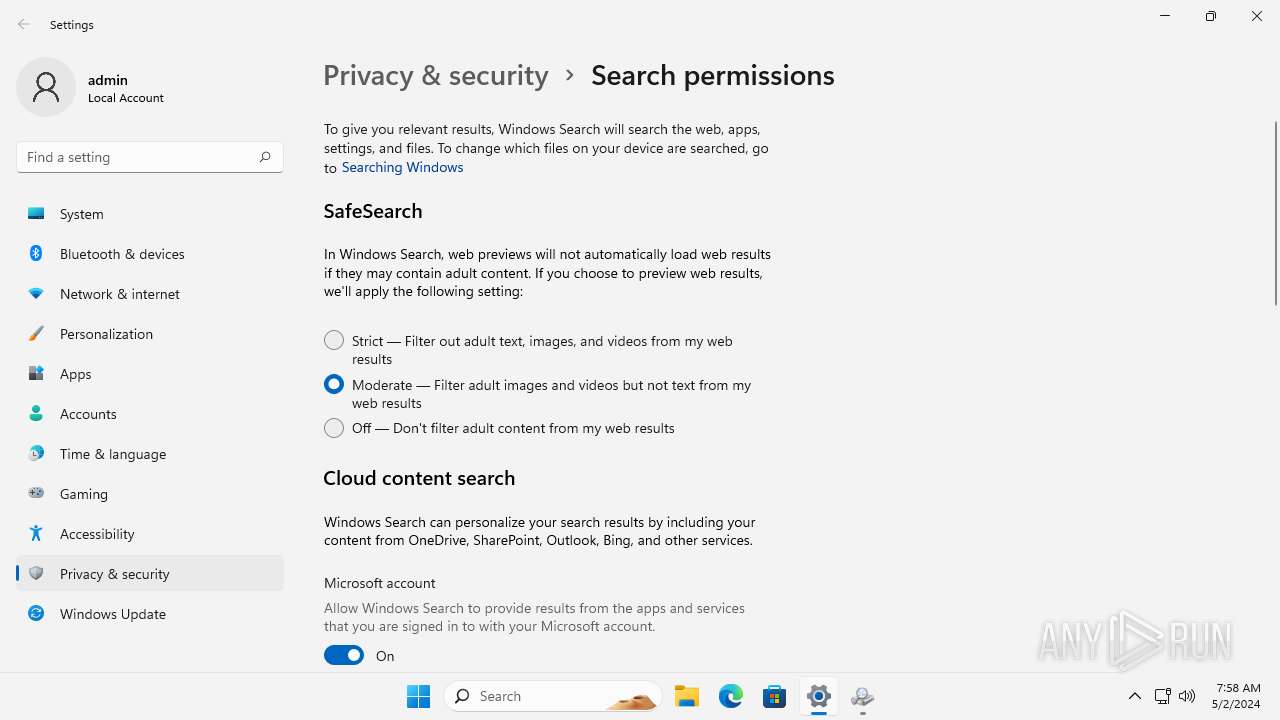
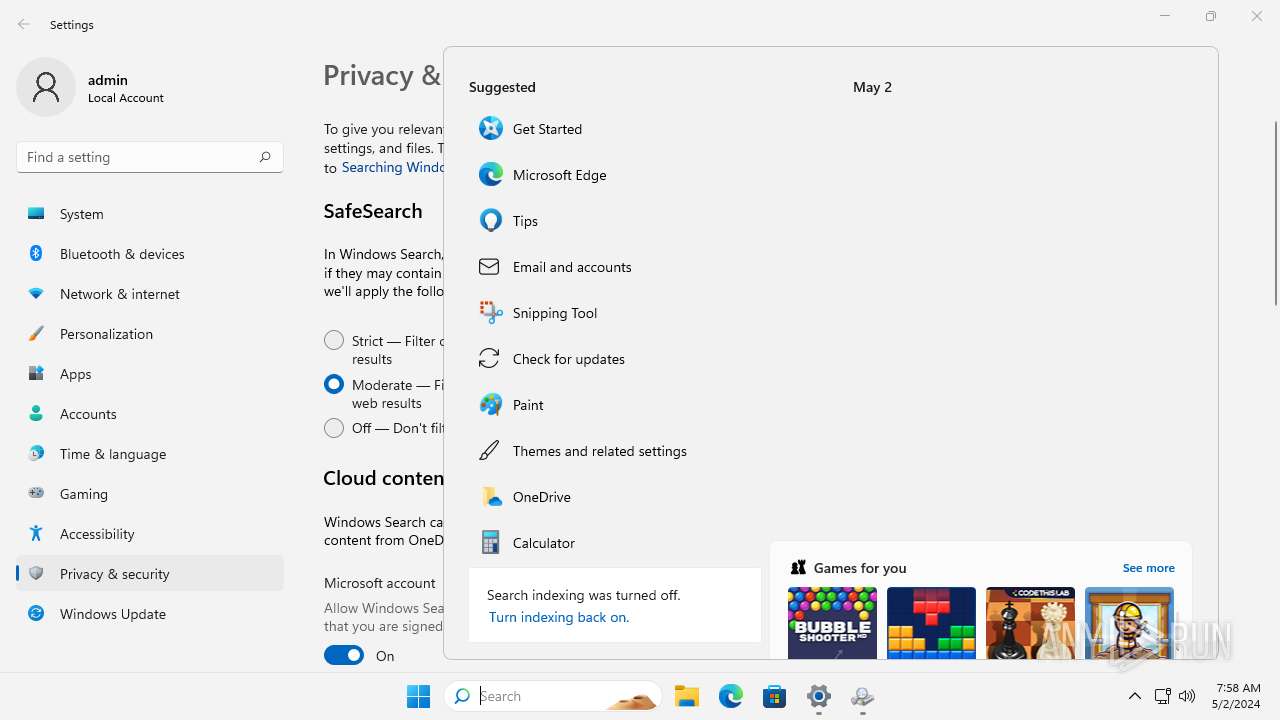
Reads the Internet Settings
- SystemSettings.exe (PID: 1308)
- OpenWith.exe (PID: 4984)
- WindowsPackageManagerServer.exe (PID: 6556)
- WindowsPackageManagerServer.exe (PID: 6676)
Reads settings of System Certificates
- WindowsPackageManagerServer.exe (PID: 6556)
- WindowsPackageManagerServer.exe (PID: 6676)
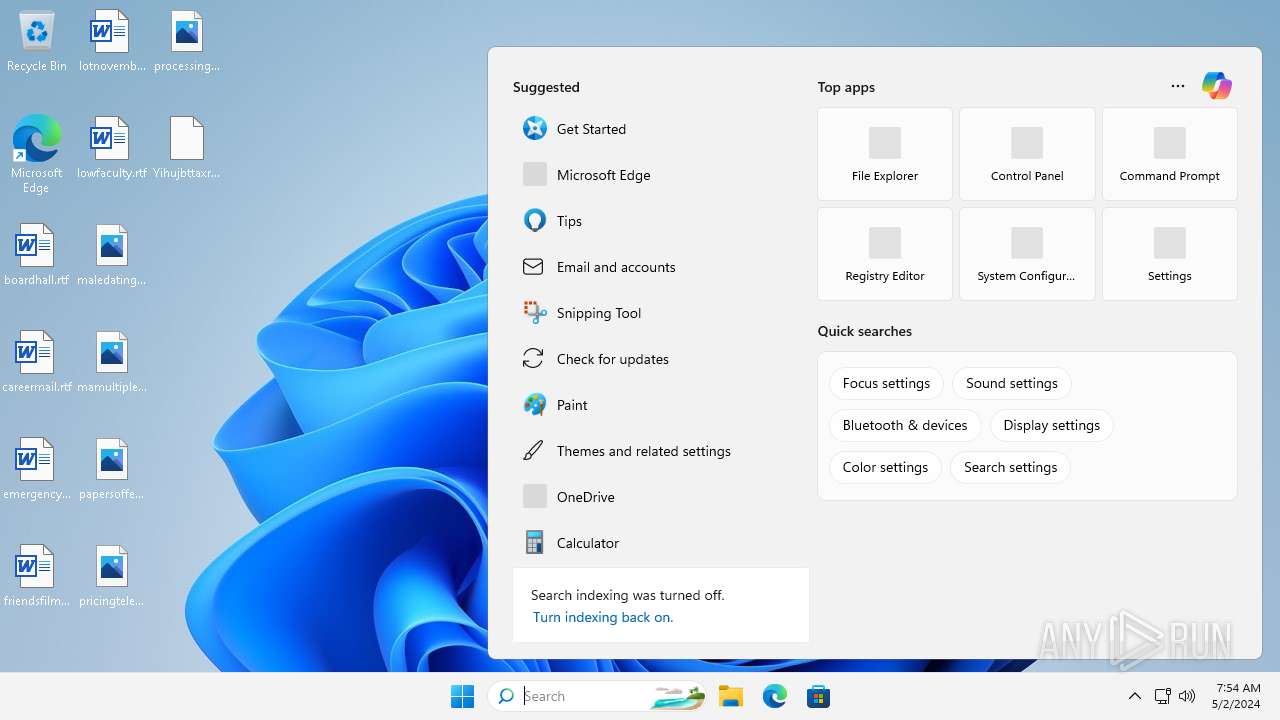
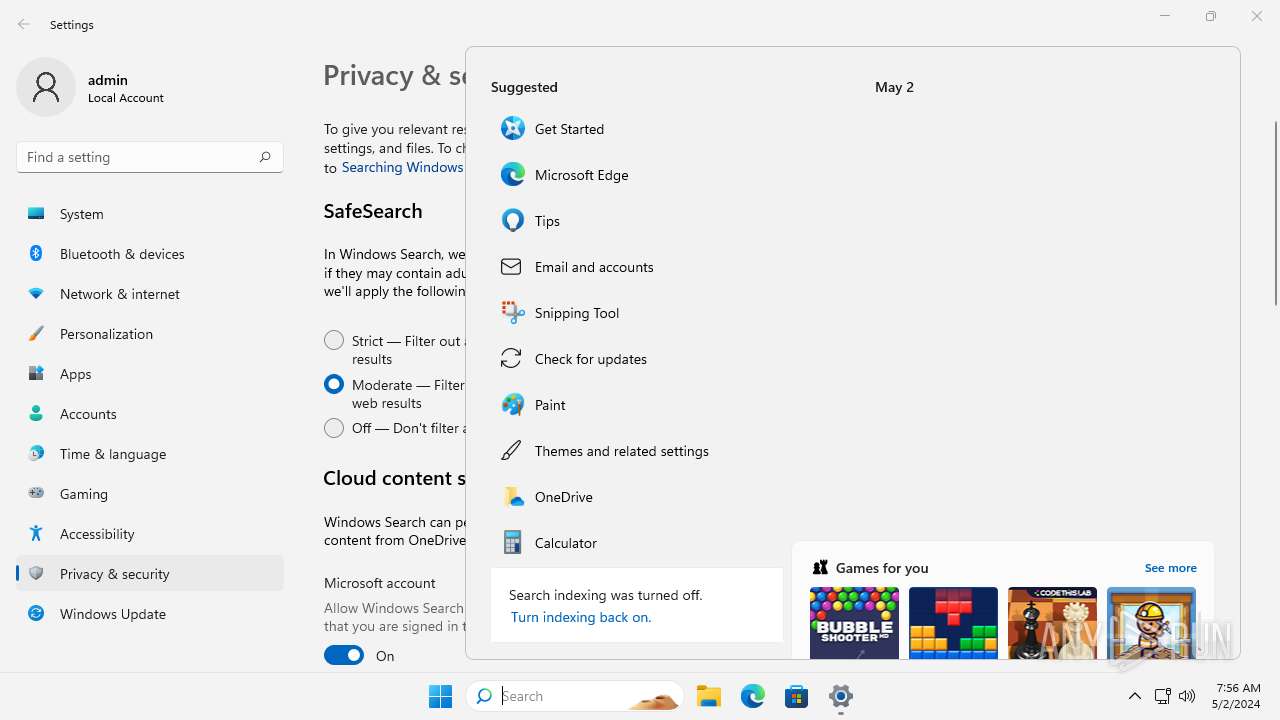
Searches for installed software
- WindowsPackageManagerServer.exe (PID: 6556)
- WindowsPackageManagerServer.exe (PID: 6676)
Reads security settings of Internet Explorer
- WindowsPackageManagerServer.exe (PID: 6556)
- WindowsPackageManagerServer.exe (PID: 6676)
INFO
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 4984)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4984)
Reads the computer name
- SystemSettings.exe (PID: 1308)
- WindowsPackageManagerServer.exe (PID: 6556)
- WindowsPackageManagerServer.exe (PID: 6676)
Creates files or folders in the user directory
- WindowsPackageManagerServer.exe (PID: 6556)
- WindowsPackageManagerServer.exe (PID: 6676)
Checks supported languages
- WindowsPackageManagerServer.exe (PID: 6556)
- SystemSettings.exe (PID: 1308)
- WindowsPackageManagerServer.exe (PID: 6676)
Reads the machine GUID from the registry
- SystemSettings.exe (PID: 1308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
123
Monitored processes
6
Malicious processes
2
Suspicious processes
0
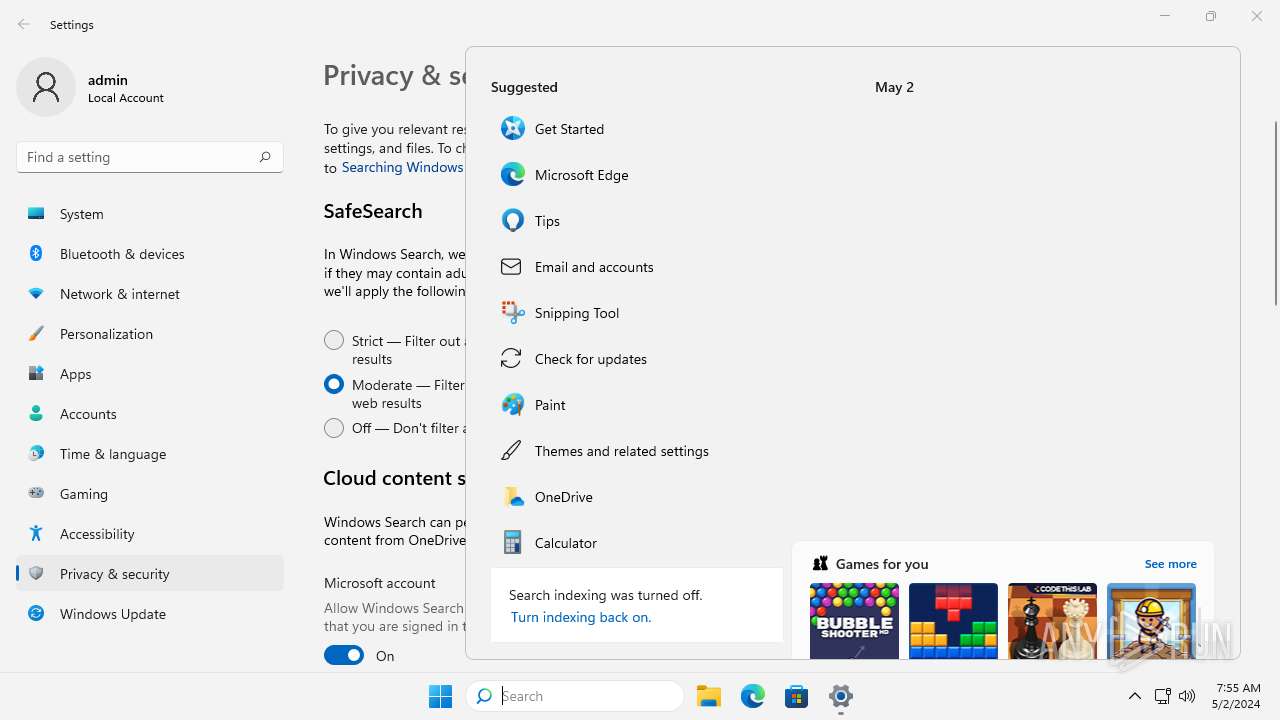
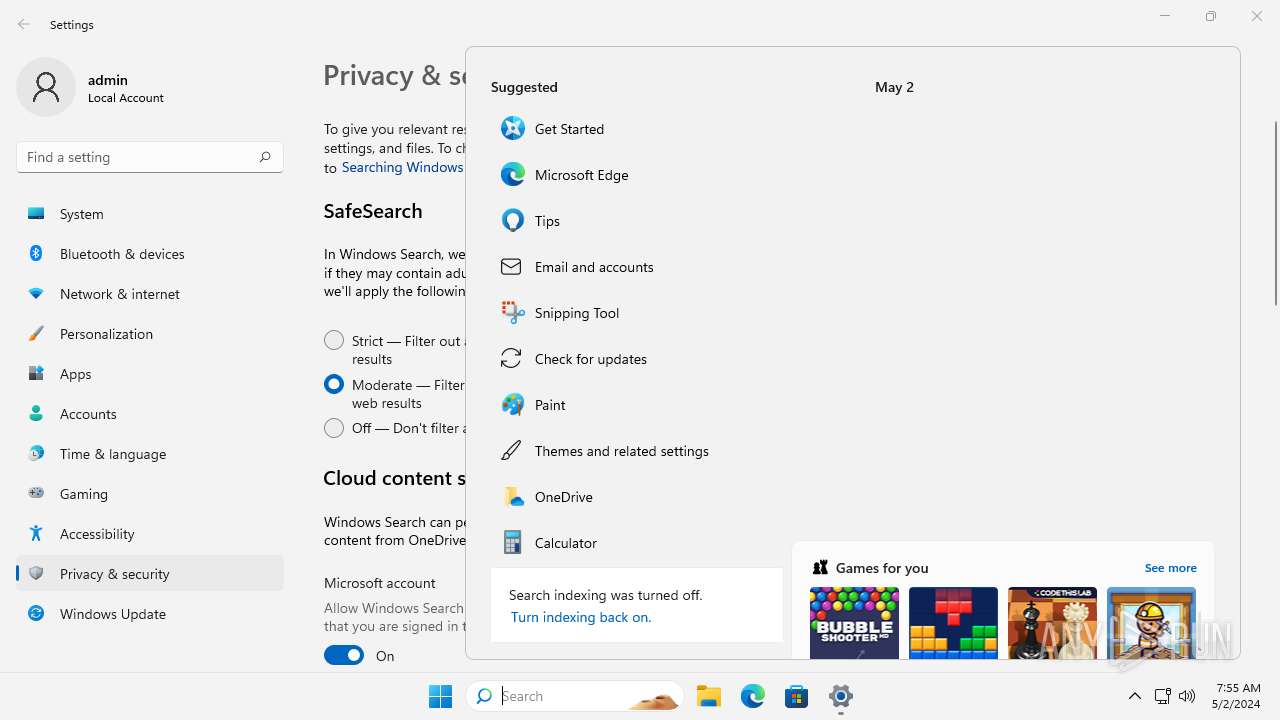
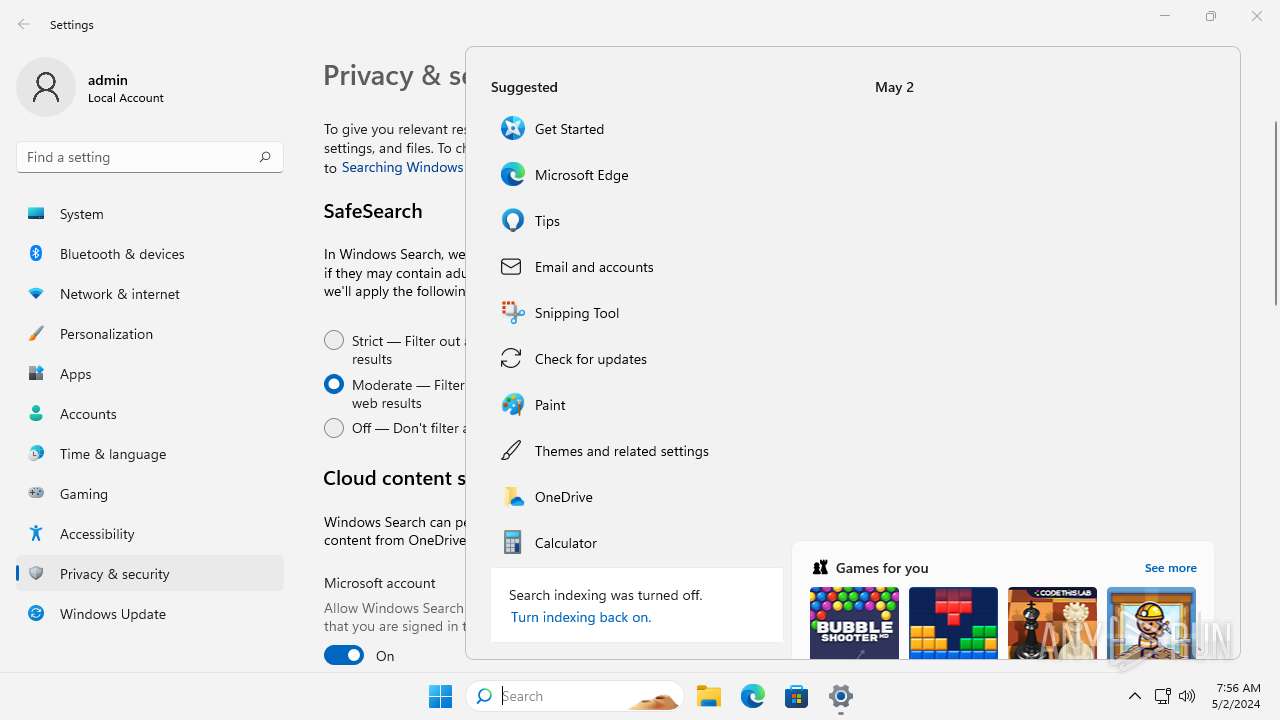
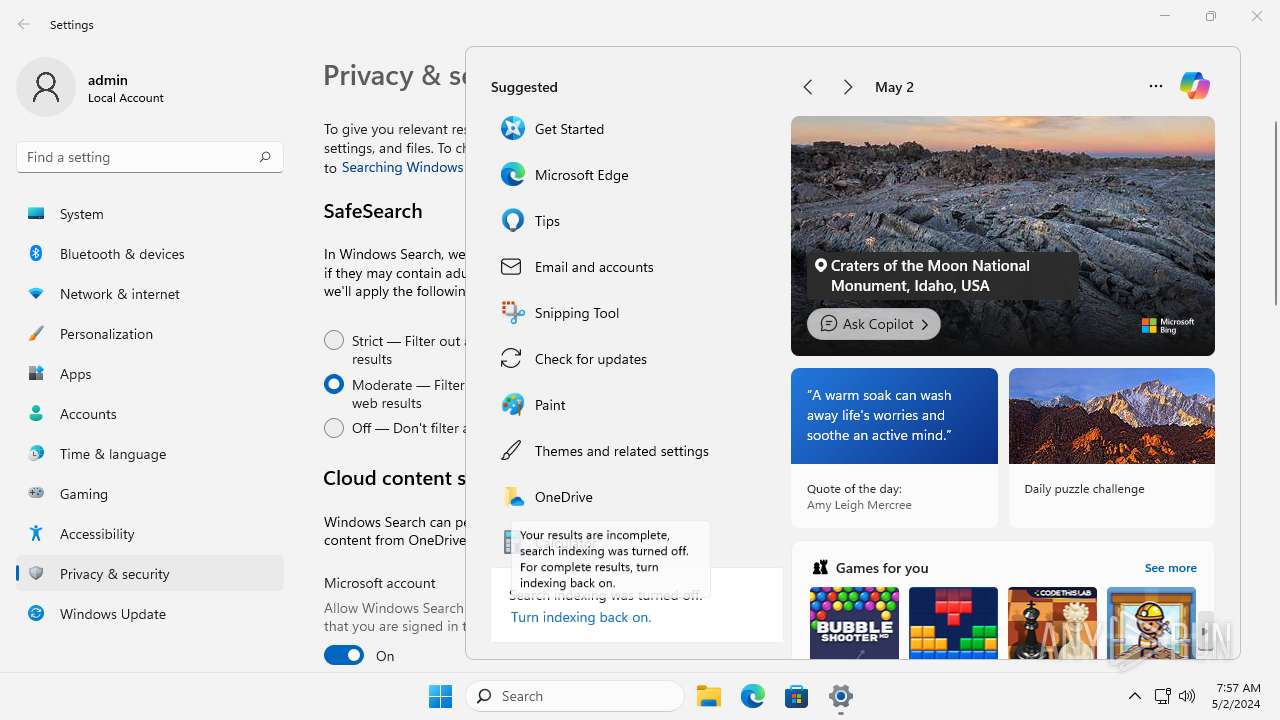
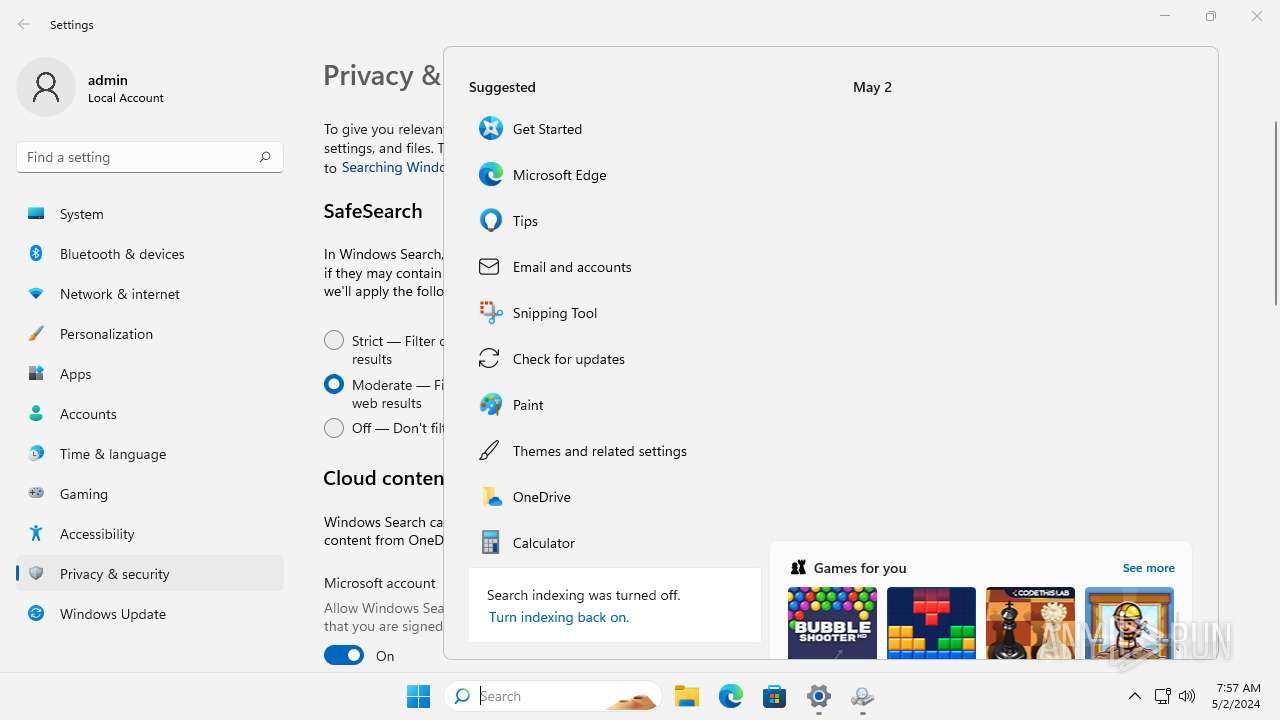
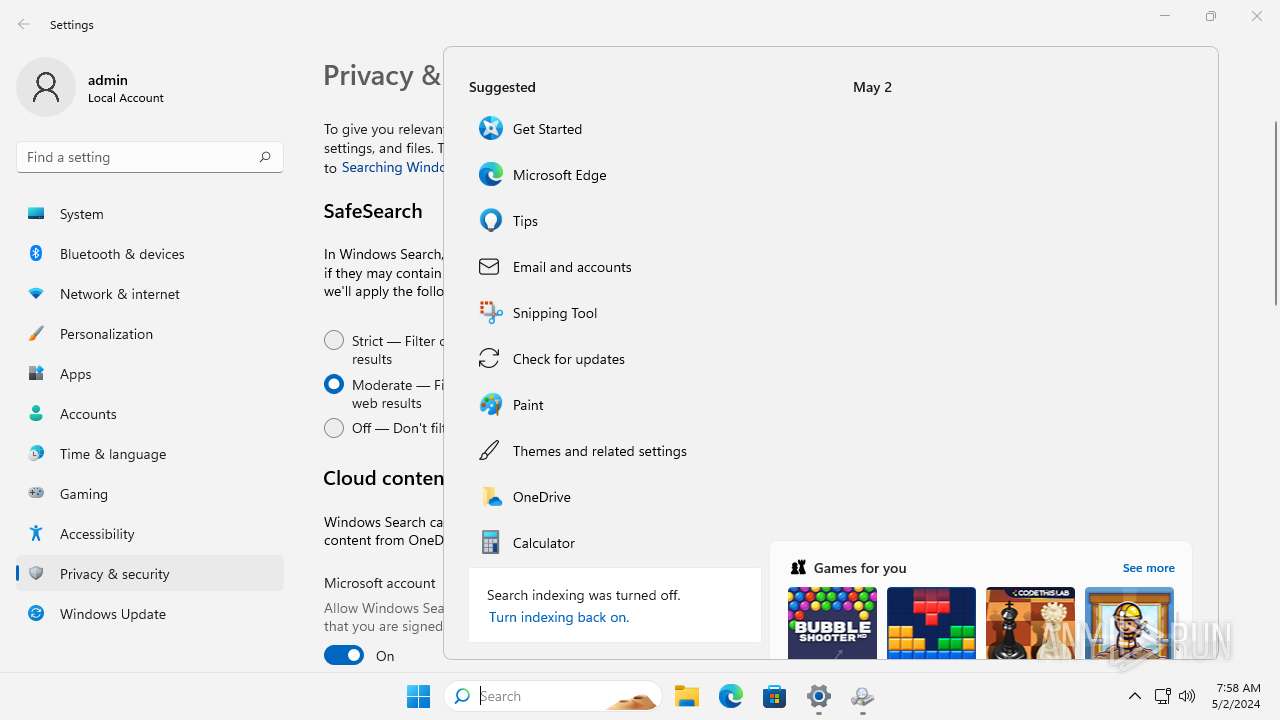
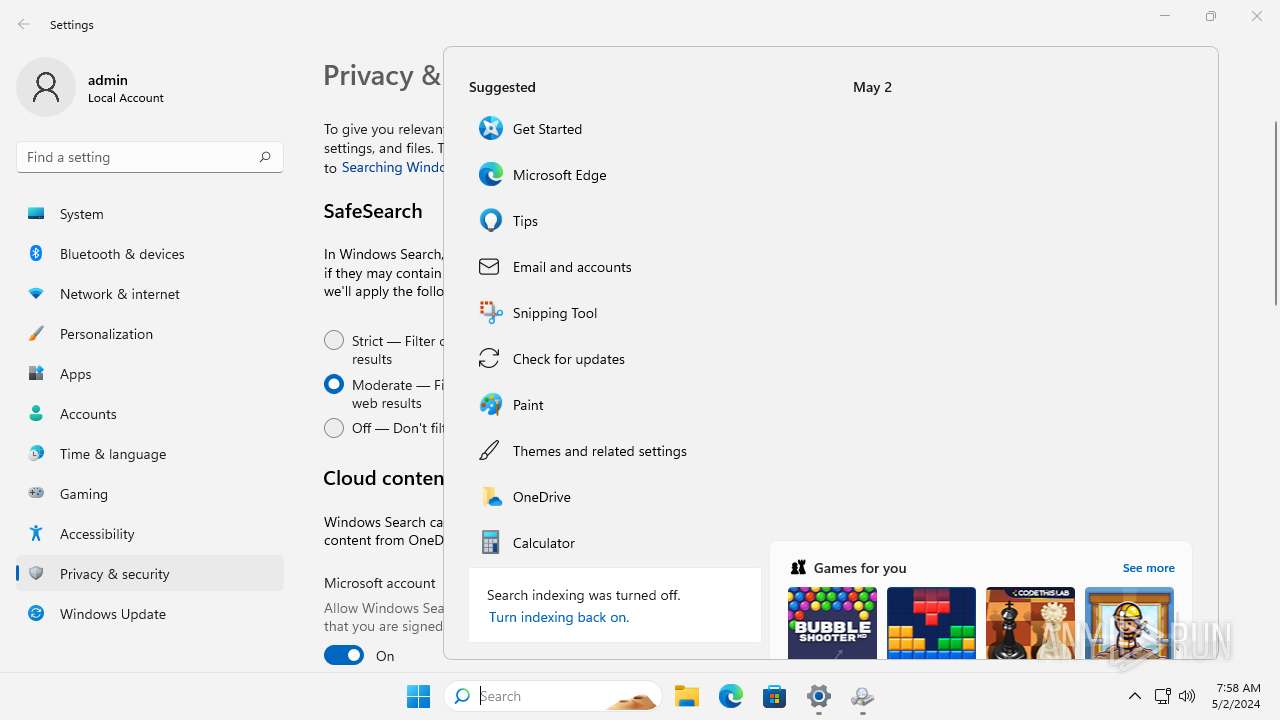
Behavior graph
Click at the process to see the details
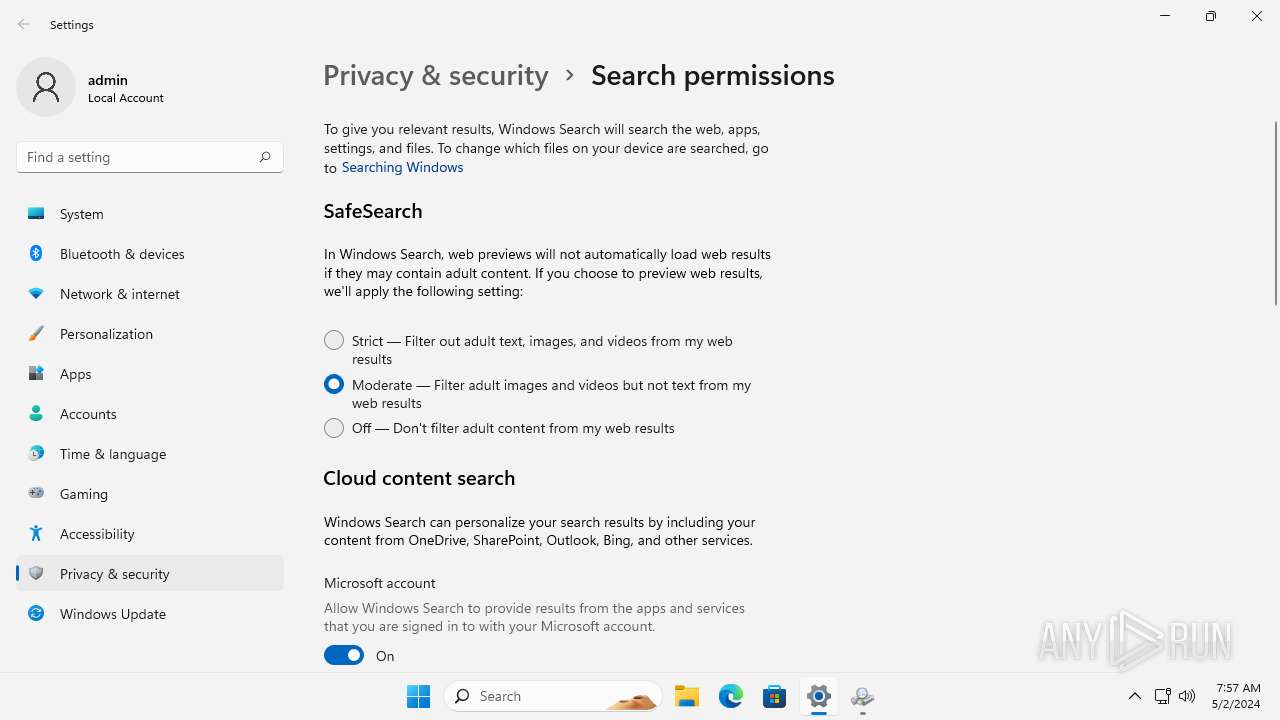
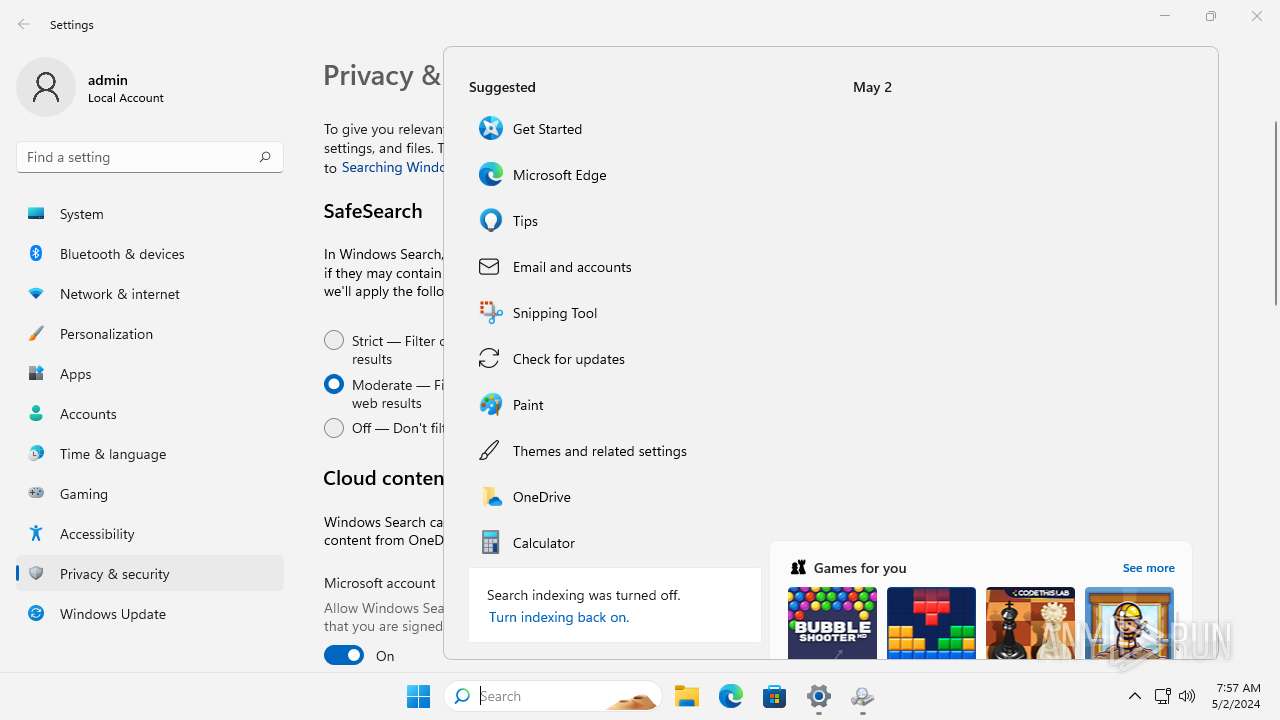
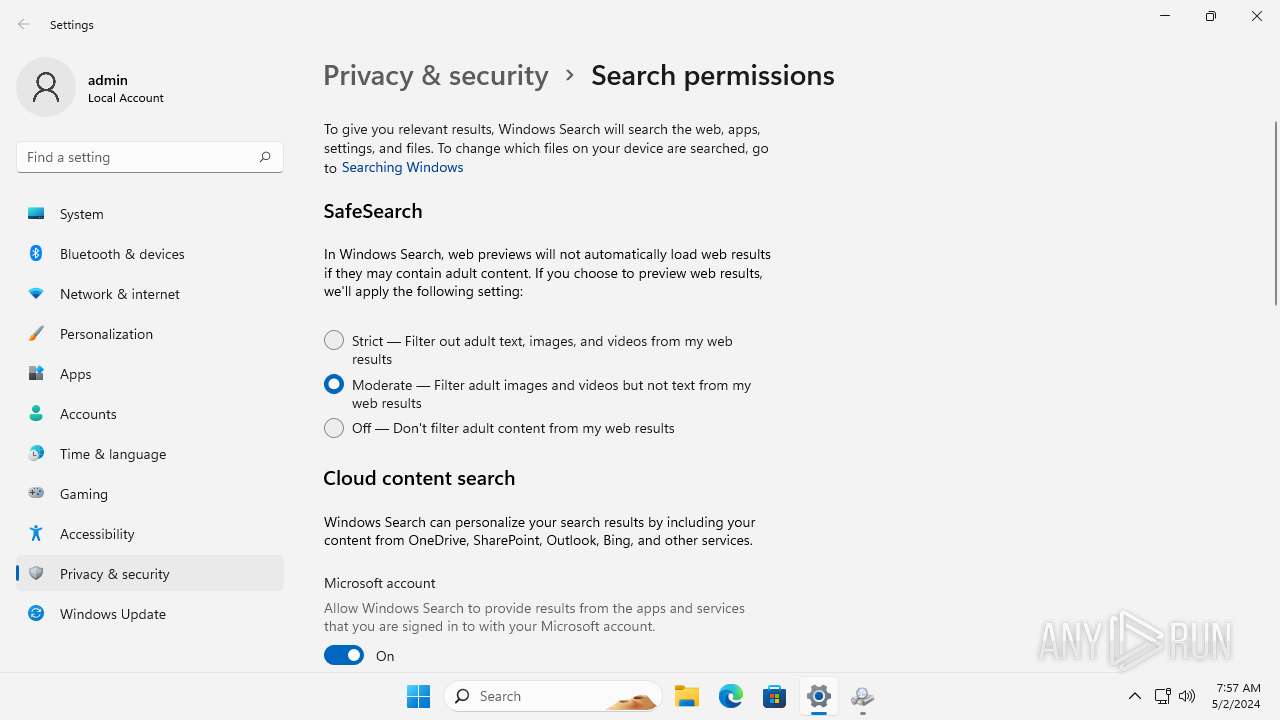
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1308 | "C:\Windows\ImmersiveControlPanel\SystemSettings.exe" -ServerName:microsoft.windows.immersivecontrolpanel | C:\Windows\ImmersiveControlPanel\SystemSettings.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Settings Version: 10.0.22000.2124 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3812 | C:\Windows\SysWOW64\DllHost.exe /Processid:{06622D85-6856-4460-8DE1-A81921B41C4B} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4984 | "C:\Windows\System32\OpenWith.exe" C:\Users\admin\Desktop\Yihujbttaxryvvhwefnnvgbyoikrczk | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6084 | C:\Windows\system32\ApplicationFrameHost.exe -Embedding | C:\Windows\System32\ApplicationFrameHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Frame Host Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6556 | "C:\Program Files\WindowsApps\Microsoft.DesktopAppInstaller_1.17.11601.0_x64__8wekyb3d8bbwe\WindowsPackageManagerServer.exe" -Embedding | C:\Program Files\WindowsApps\Microsoft.DesktopAppInstaller_1.17.11601.0_x64__8wekyb3d8bbwe\WindowsPackageManagerServer.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6676 | "C:\Program Files\WindowsApps\Microsoft.DesktopAppInstaller_1.17.11601.0_x64__8wekyb3d8bbwe\WindowsPackageManagerServer.exe" -Embedding | C:\Program Files\WindowsApps\Microsoft.DesktopAppInstaller_1.17.11601.0_x64__8wekyb3d8bbwe\WindowsPackageManagerServer.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
20 877
Read events
20 840
Write events
28
Delete events
9
Modification events
| (PID) Process: | (4984) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\29\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-205 |
Value: Word | |||
| (PID) Process: | (4984) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\root\Office16\Winword.exe.FriendlyAppName |
Value: Word | |||
| (PID) Process: | (4984) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\root\Office16\Winword.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (4984) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\29\52C64B7E |
| Operation: | write | Name: | @wmploc.dll,-102 |
Value: Windows Media Player | |||
| (PID) Process: | (4984) OpenWith.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Software\Microsoft\TIP\AggregateResults |
| Operation: | write | Name: | data |
Value: D9A7A80101000300EC03F46F000000004900000000000000D9A7A80102000800BAF9F550000000000A0000000000000049A8A801010003005C4614A6000000004300000000000000D1A8A8010100030064B6561100000000F801000000000000D1A8A80101000400FB3B54EB000000008B000000030000007545B801010002002972674D0000000003000000B10A00007545B8010300A5002CBBB4C700000000010000005E740000C8CCB9010100008092617636000000000D000000B6000000AFFBB9010100008055161AFB0000000004000000556816002B7ABA01017F0080192CC3DC0000000008000000000000004428C30101000080469996A200000000A70000006A0800004428C30104000100541F4AF4000000000B000000000000002C06D801010004008A1488B40000000007000000380100002C06D80101000C00424174840000000004000000DD0000004245D901010005007177B2F300000000010000006F0600004245D90101000700436CB73F0000000007000000B03500009F49DD010100008045734BE100000000D9000000200000004959DD0101000400F34A296B00000000050000000E0100006A44DF010100008054528C5D0000000004000000150100009178E10101020080DF19D73200000000010000000000000081F7E10104000100C177129C00000000850000002600000081F7E101040002002AF214C200000000210000004A010000D81BE20104000500FCAC50C7000000000300000000000000EC9BE501010000806E4C67B6000000000100000000000000AA26E701010000801490D0EE02000000090000003D000000DA49E80101000080C483AE790000000004000000CE0100007FE9E90101000080A5B9B0290000000006000000200100007FE9E9010200050089B029380000000024000000DF060000C527EB01010000804B8D54FB000000000D000000850000007C22ED01017F0080FE0EED5500000000010000004F0000007C22ED010300004071B6685200000000060000003B0000008C5FF2010100030025B04D21000000000700000015000000BA0BF30101000000248CDFD40000000008000000300100006EFCF3010100010079586E99000000002B000000150800006EFCF30101000200E2D270BF0000000046000000F50200006EFCF301017F03004B4D73E500000000A4130000211800006EFCF30101000080105E373600000000980E0000DC0000003F0EF40101000080E58C865C0000000059010000D5040000EE8FF801010000809096E6C200000000080000008E010000E5140102017F00806B2E500700000000060000005D0100003D4A060201000080C39240F0000000001100000071000000564A060201000080784A674B00000000040000005E000000BFDE08020100008065B49D6B000000002E0000003600000044240E020100008046DDF50500000000040000000000000044240E02040001005463A9570000000003000000000000005F37110201000080856D77FF00000000100000000B010000D2EF1402030001403B2AE65900000000040000006300000088531E0203000100A5067F520000000005000000D4000000A410270201000080260FB9F9000000003D00000055000000F2A23702010100805C882F6600000000040000006F0900003339420202000300FB8663320000000003000000DDAF00003339420204000100EBC5C65F00000000010000008F0600007738460201000400799840C90000000002000000030000007738460201000500101E3EA3000000000100000000000000FDBE49020100008003520DB60000000006000000A4160000FDBE49020101008003520DB6010000000500000035010000FDBE490203001740163625F30000000001000000DD12000056804F020100008078F05D3000000000020000000A00000056804F0203000140779193350000000002000000030000005ECC7E0203000400F2591D09000000000500000040000000E0CD7E02010000802A3AEA3F010000000500000008000000 | |||
| (PID) Process: | (6084) ApplicationFrameHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppModel\SystemAppData\windows.immersivecontrolpanel_cw5n1h2txyewy\PersistedTitleBarData\windows.immersivecontrolpanel_cw5n1h2txyewy!microsoft.windows.immersivecontrolpanel |
| Operation: | write | Name: | AppVersion |
Value: E803060000000A00 | |||
| (PID) Process: | (1308) SystemSettings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\WSX\WSXPacks\Windows.Settings.Account\1.1.651.580 |
| Operation: | write | Name: | packOpenedCount |
Value: 4 | |||
| (PID) Process: | (1308) SystemSettings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1308) SystemSettings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1308) SystemSettings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
5
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1308 | SystemSettings.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L62DDG6LW2Z4W1ZZJ370.temp | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
| 1308 | SystemSettings.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\f18460fded109990.customDestinations-ms~RFeedd6.TMP | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
| 1308 | SystemSettings.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:F4782C2D90F8D5BBAC6B9C915AEB3B7E | SHA256:D5839D9D33A6DEC9B10D7B31F2FC2B047AD2A8ECEE38FC20084F09D48CF1502C | |||
| 1308 | SystemSettings.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\f18460fded109990.customDestinations-ms | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
| 1308 | SystemSettings.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9D6B3FE9E6E4067193F477ABAD990106 | binary | |
MD5:19CAD37DA25011B97849D68C268E7BB9 | SHA256:1348B037813007C4FAC50FC172130E0BD8DFCDA83C1D47380EA6799074B6001B | |||
| 1308 | SystemSettings.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9D6B3FE9E6E4067193F477ABAD990106 | der | |
MD5:73D194E3436D0B2174E873ED1FF1EEEB | SHA256:C562DF444359DD6F01AEDEF856685DB1451915CA58EF4DB65F02CF51EE1039F6 | |||
| 1308 | SystemSettings.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | der | |
MD5:A5DF96E581C3D71E44253CAB84340EDA | SHA256:1120A001058D7E7C5E279760646E54AB15E6C57505152B82654D4038FE4BBF8A | |||
| 6676 | WindowsPackageManagerServer.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.DesktopAppInstaller_8wekyb3d8bbwe\LocalState\DiagOutputDir\WPM-2024-05-02-07-55-12.918.log | text | |
MD5:4DEF95B4A5394FC192A3BED2FF466229 | SHA256:61E2D06CCD88DC89AC52305F25CC1A5D044EC06A50498D548E3A4960389D2758 | |||
| 6556 | WindowsPackageManagerServer.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.DesktopAppInstaller_8wekyb3d8bbwe\LocalState\DiagOutputDir\WPM-2024-05-02-07-55-10.297.log | text | |
MD5:CCE1C86906C424DFDE0549B8E77E4D13 | SHA256:E177950437B664C7D735C2F22408D9AD71D61C46A2140267110FBF1991F76D25 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
430
TCP/UDP connections
165
DNS requests
88
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.35:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | unknown |
3808 | WindowsPackageManagerServer.exe | GET | 200 | 2.23.154.139:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33040546788fd130 | unknown | — | — | unknown |
3808 | WindowsPackageManagerServer.exe | GET | — | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
4768 | SearchHost.exe | GET | 200 | 2.23.154.139:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?867b38ab38064181 | unknown | — | — | unknown |
4768 | SearchHost.exe | GET | 200 | 2.23.154.139:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c93149cbdc56ca2b | unknown | — | — | unknown |
4768 | SearchHost.exe | GET | 200 | 2.23.154.139:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?07e37c49729e728c | unknown | — | — | unknown |
4768 | SearchHost.exe | GET | 200 | 2.23.154.139:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fcab01459285e9f3 | unknown | — | — | unknown |
4768 | SearchHost.exe | GET | 200 | 2.23.154.139:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c66e2e5d6154e34c | unknown | — | — | unknown |
4768 | SearchHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
3040 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2520 | svchost.exe | 23.34.232.119:443 | disc801.prod.do.dsp.mp.microsoft.com | Bezeq International | US | unknown |
3808 | WindowsPackageManagerServer.exe | 23.34.233.163:443 | storeedgefd.dsx.mp.microsoft.com | Bezeq International | US | unknown |
4792 | OfficeC2RClient.exe | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4780 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 2.16.164.35:80 | — | Akamai International B.V. | NL | unknown |
3808 | WindowsPackageManagerServer.exe | 2.23.154.139:80 | ctldl.windowsupdate.com | Akamai International B.V. | AT | unknown |
5040 | svchost.exe | 104.103.72.50:80 | — | Akamai International B.V. | AT | unknown |
3808 | WindowsPackageManagerServer.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
2844 | OfficeClickToRun.exe | 52.109.89.117:443 | mrodevicemgr.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3040 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
disc801.prod.do.dsp.mp.microsoft.com |
| whitelisted |
kv801.prod.do.dsp.mp.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
Process | Message |
|---|---|
dllhost.exe | Start |
dllhost.exe | CPL_INIT
|