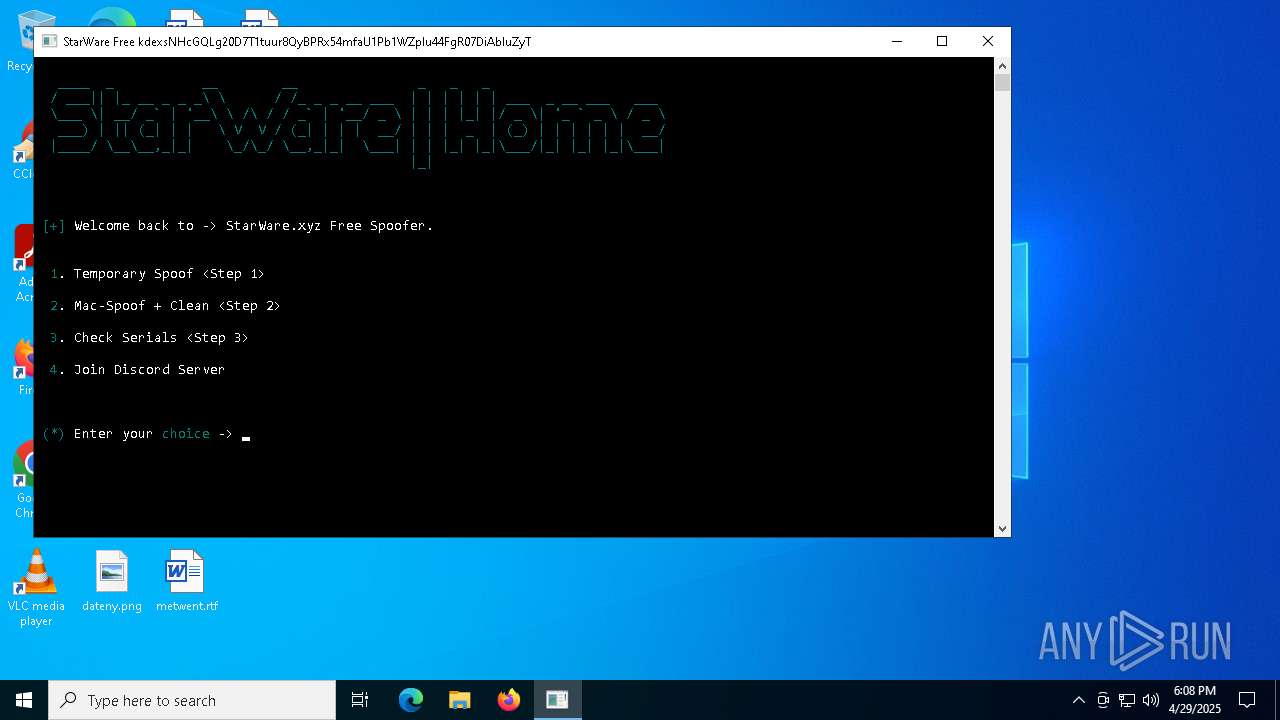
| File name: | SW-FREE.exe |
| Full analysis: | https://app.any.run/tasks/98f38763-6445-49f8-82cb-0e42d67856aa |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 18:07:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | FE38E7C8DB64D5D0A9DFF8369C9BD4F7 |
| SHA1: | D03FF84710BED11BEA3DA029714C8D47DAA204AF |
| SHA256: | C74954BCC4C4B65489A248B9E522C4C0ABCBE734530F57BB2A5B0AAB101A0638 |
| SSDEEP: | 98304:aLx0AI8+M9qZAqGAdW4oJxakBOuHVXVjXWoLU6Gp8Tn5bfgBhLsW/1Zvf+l8QDDo:BcQT |
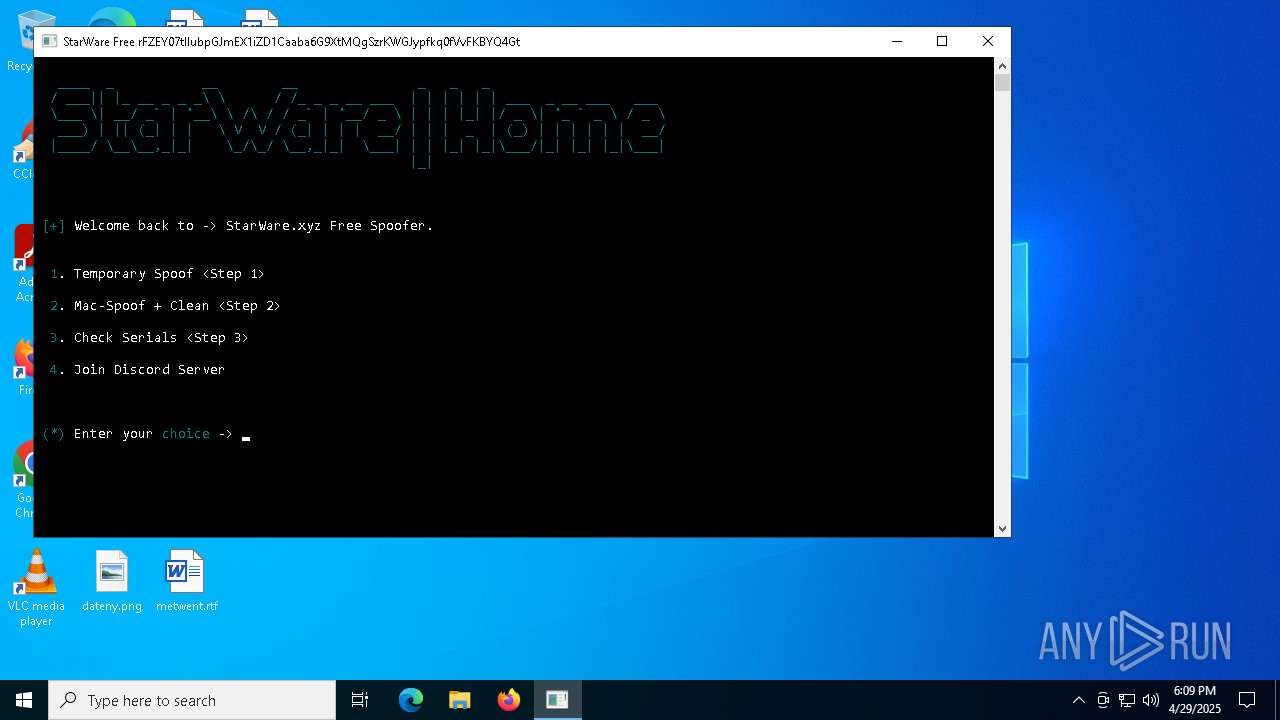
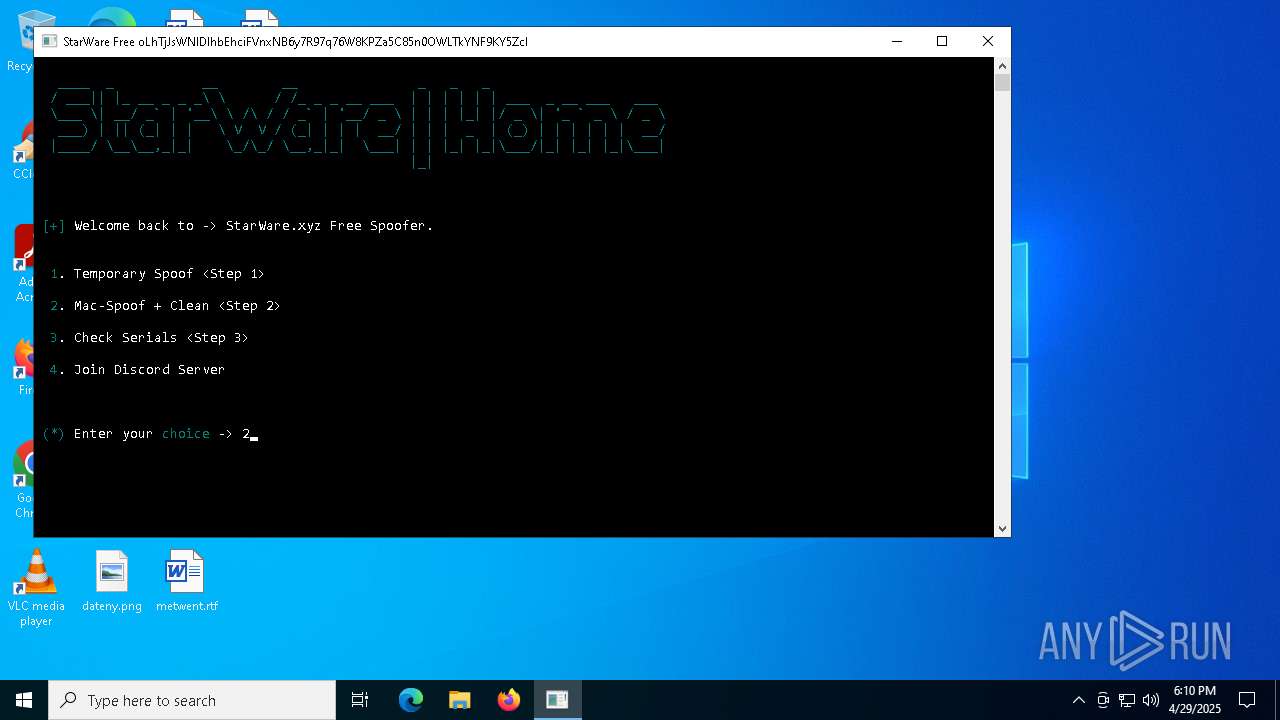
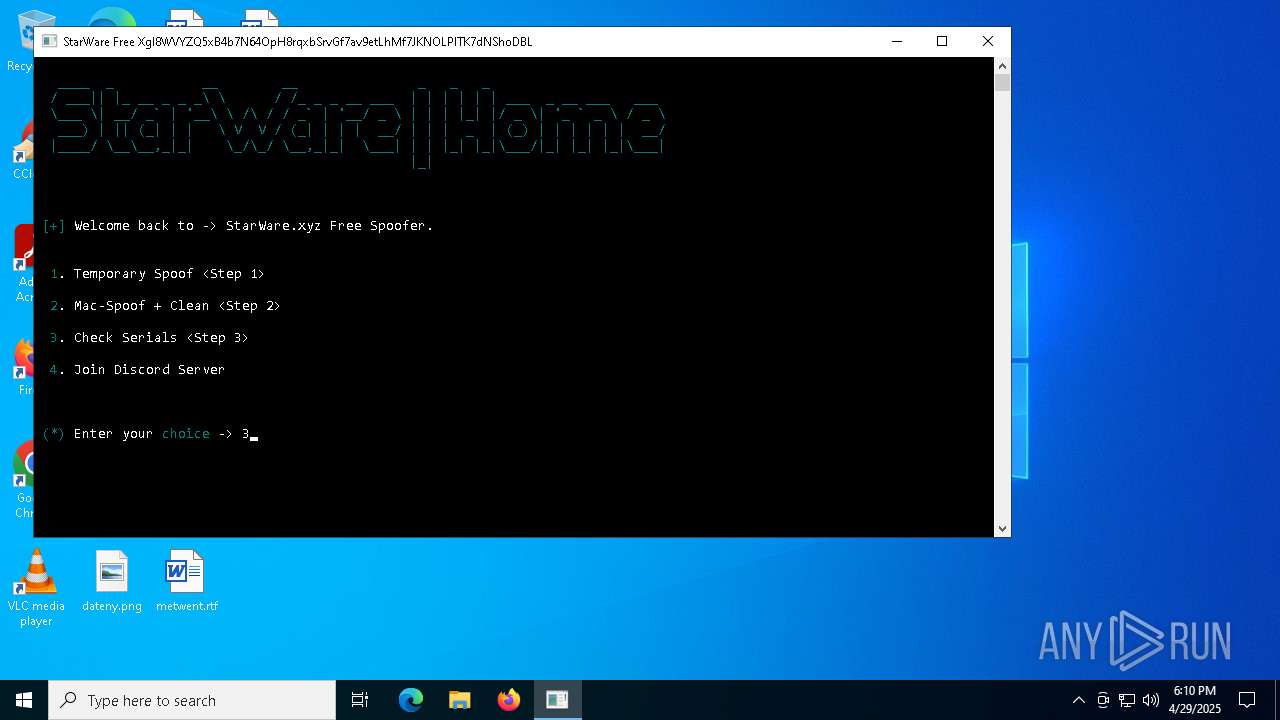
MALICIOUS
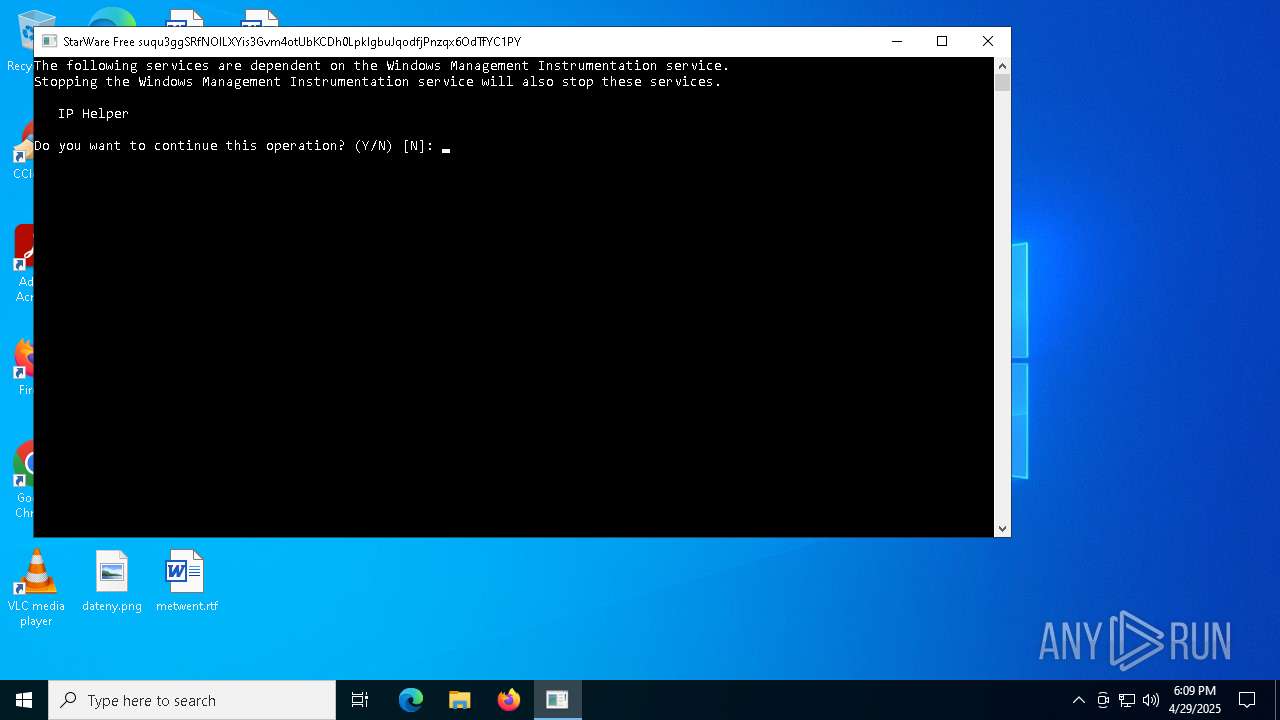
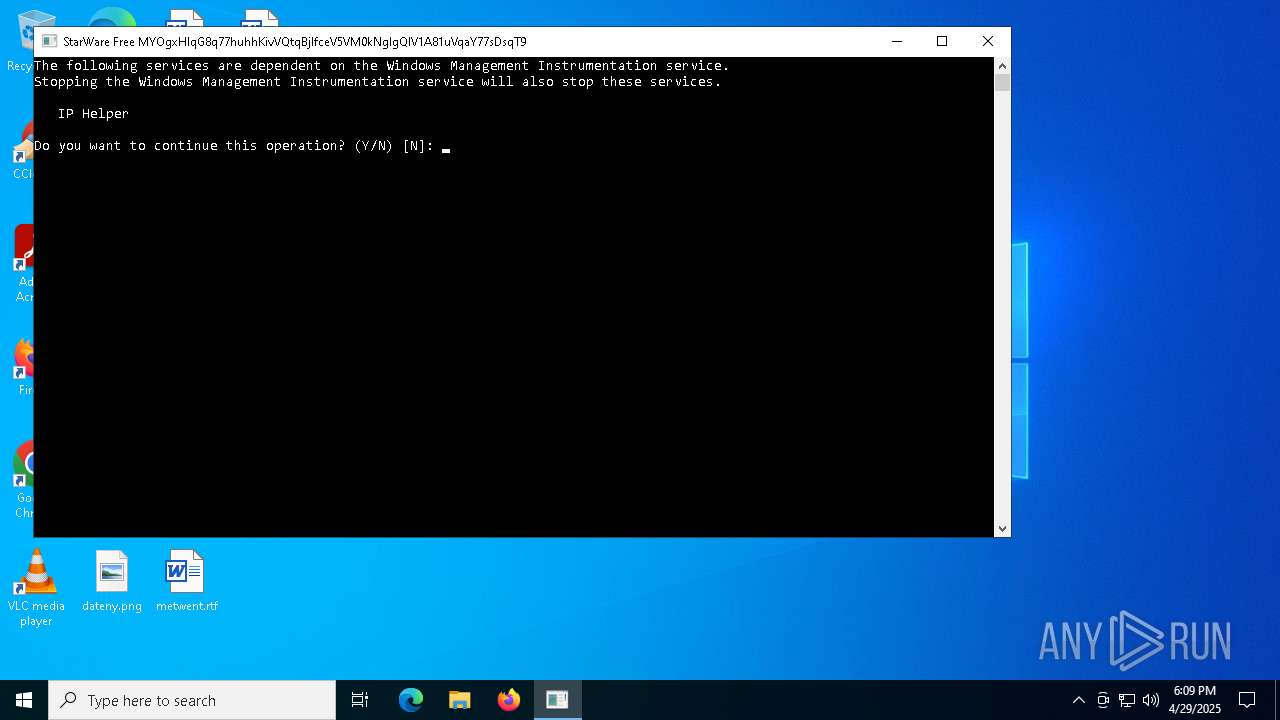
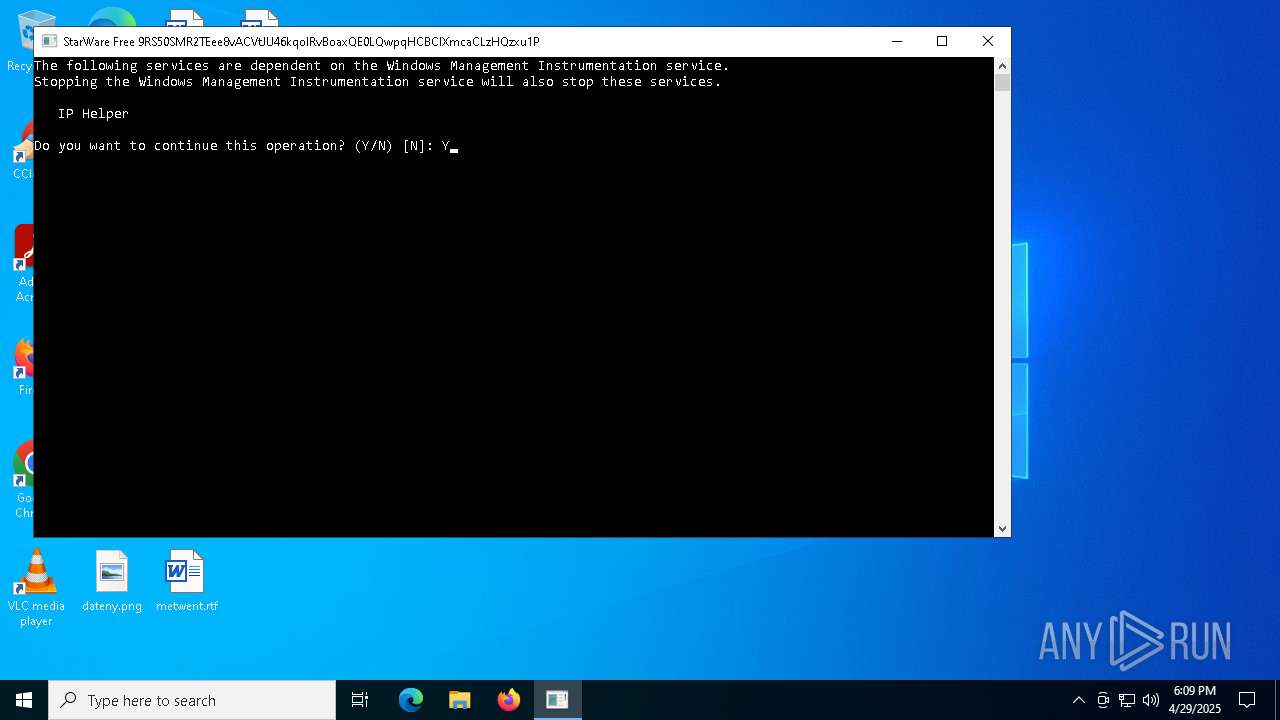
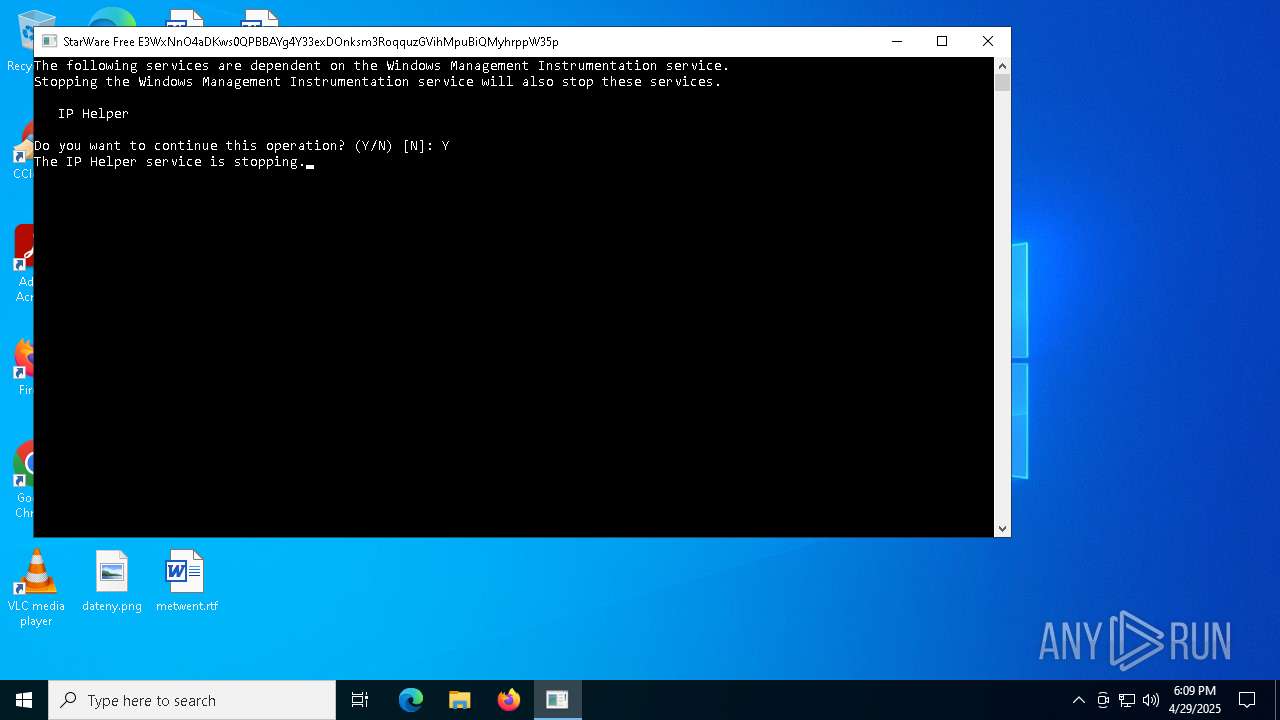
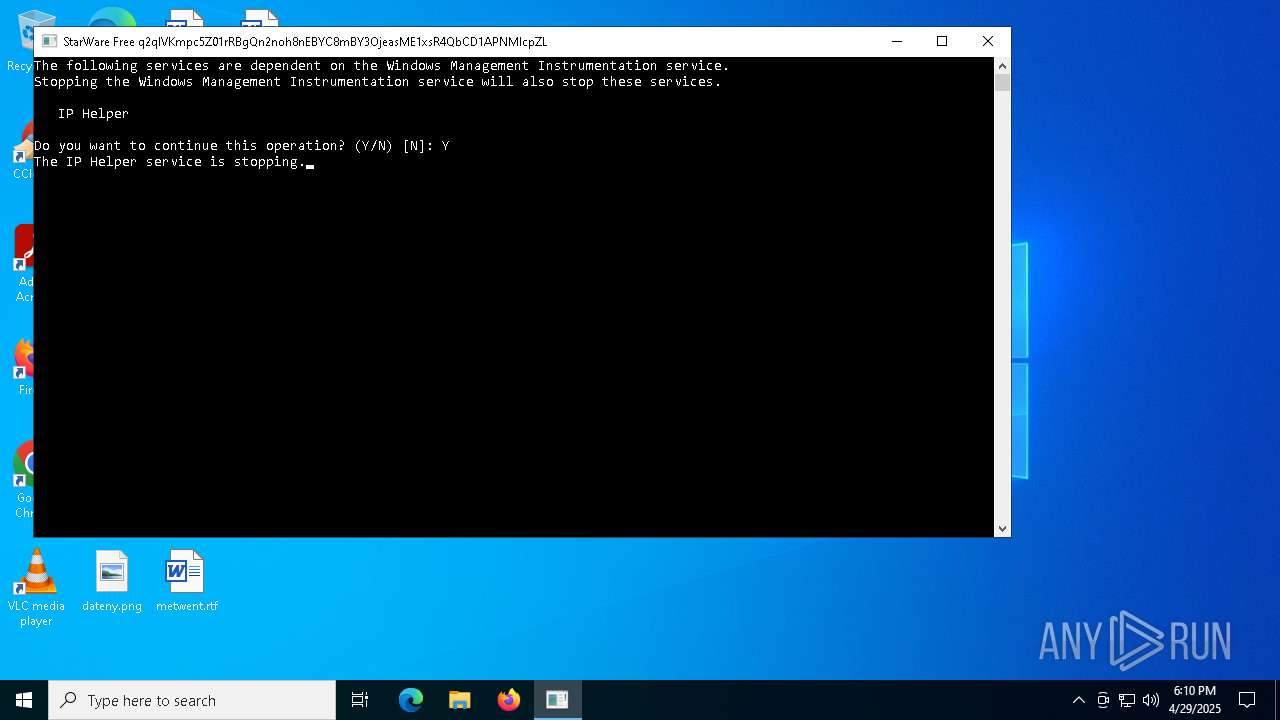
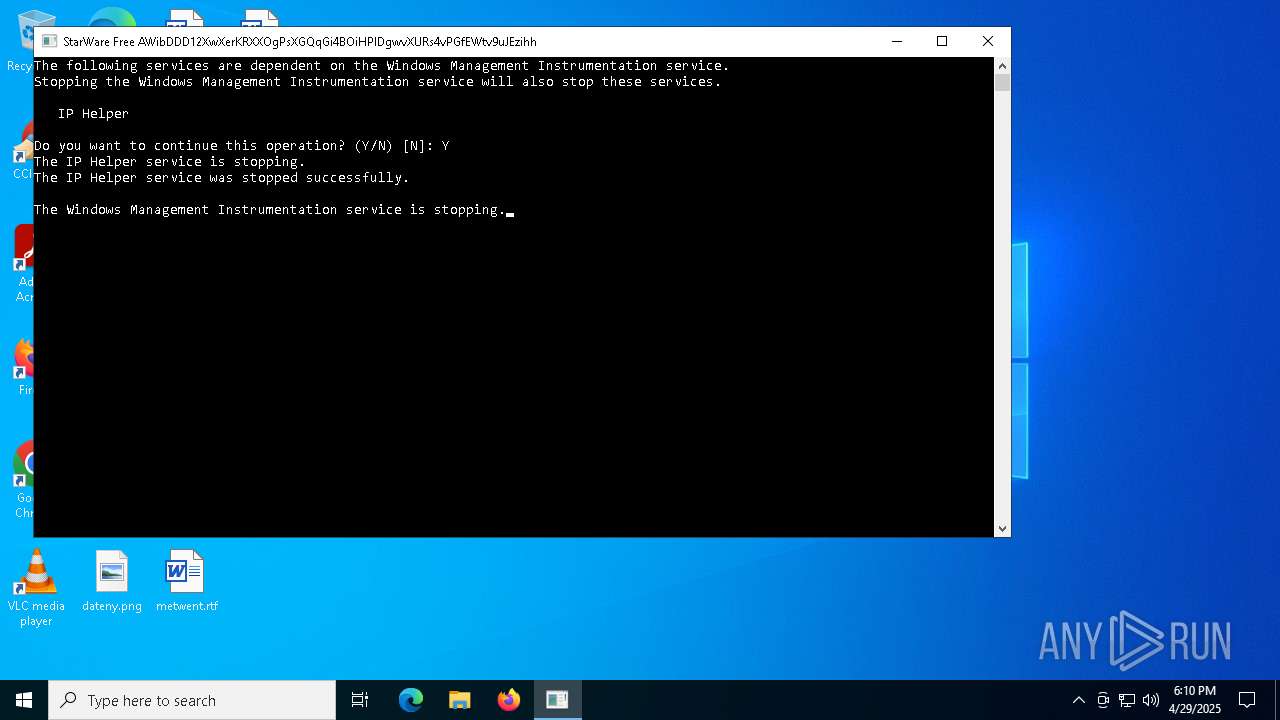
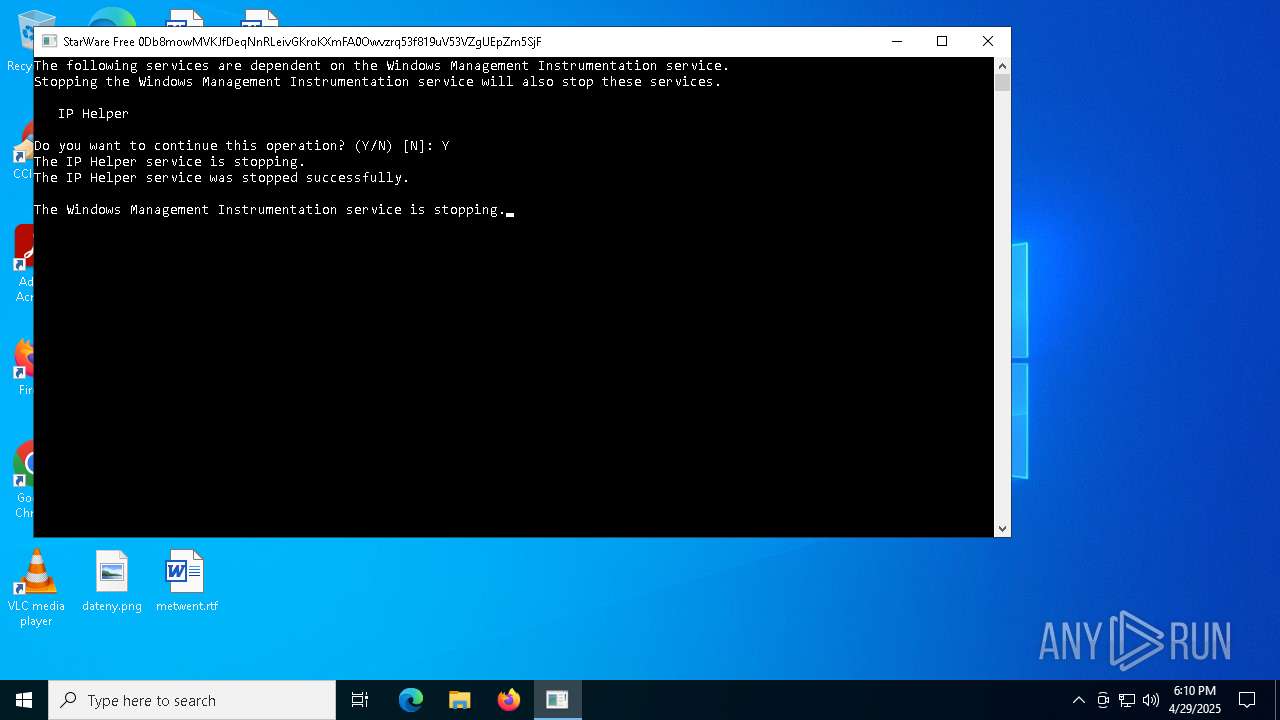
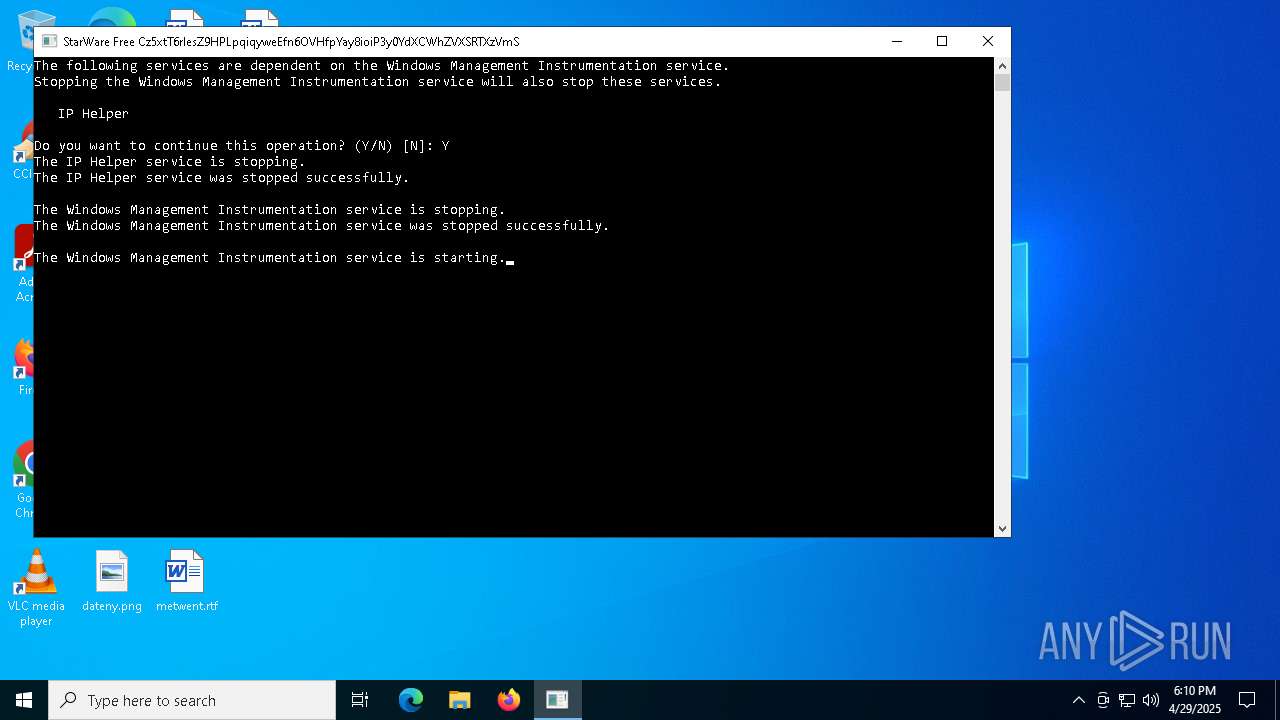
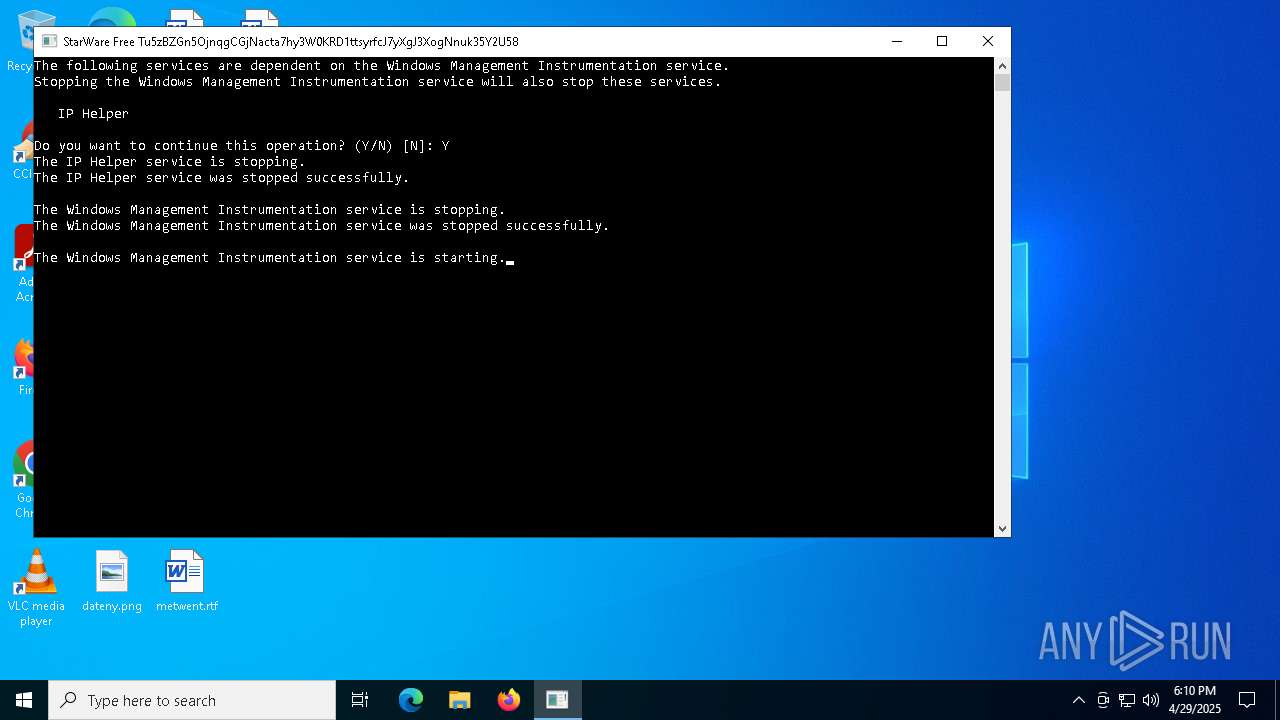
Starts NET.EXE for service management
- cmd.exe (PID: 6192)
- net.exe (PID: 7712)
- cmd.exe (PID: 1328)
- net.exe (PID: 2420)
SUSPICIOUS
Execution of CURL command
- SW-FREE.exe (PID: 4628)
Hides command output
- cmd.exe (PID: 8004)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 456)
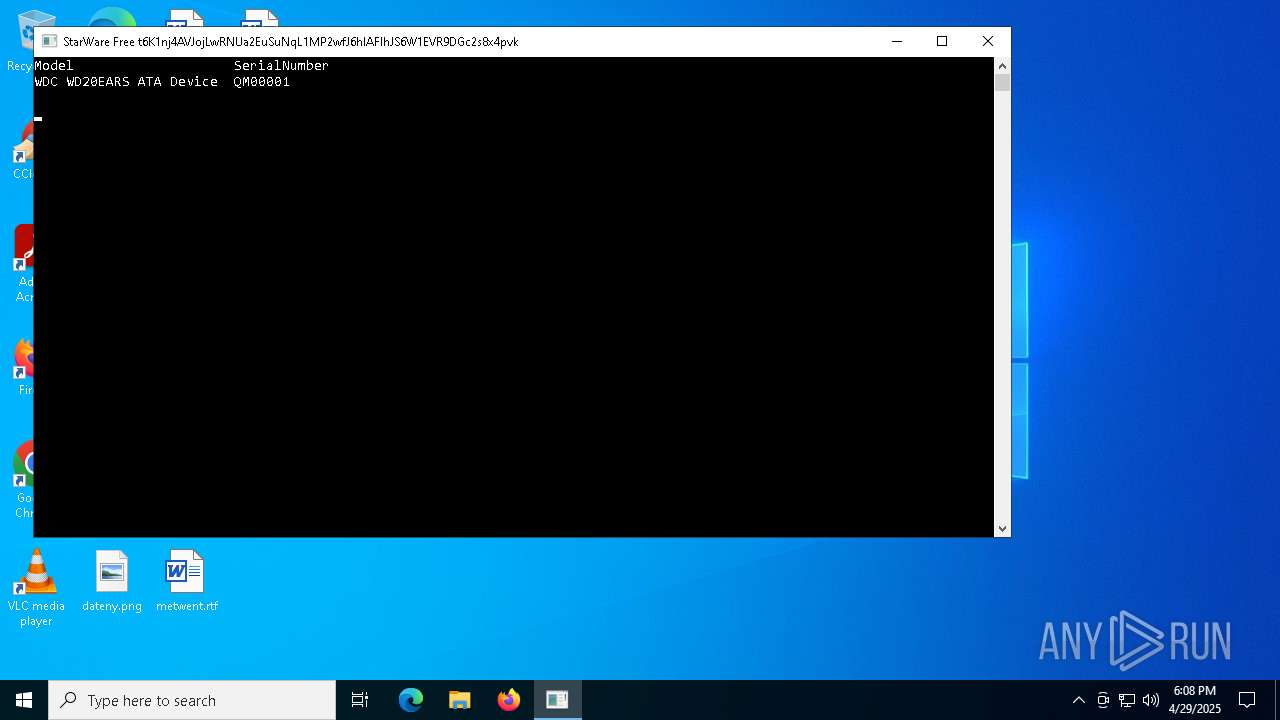
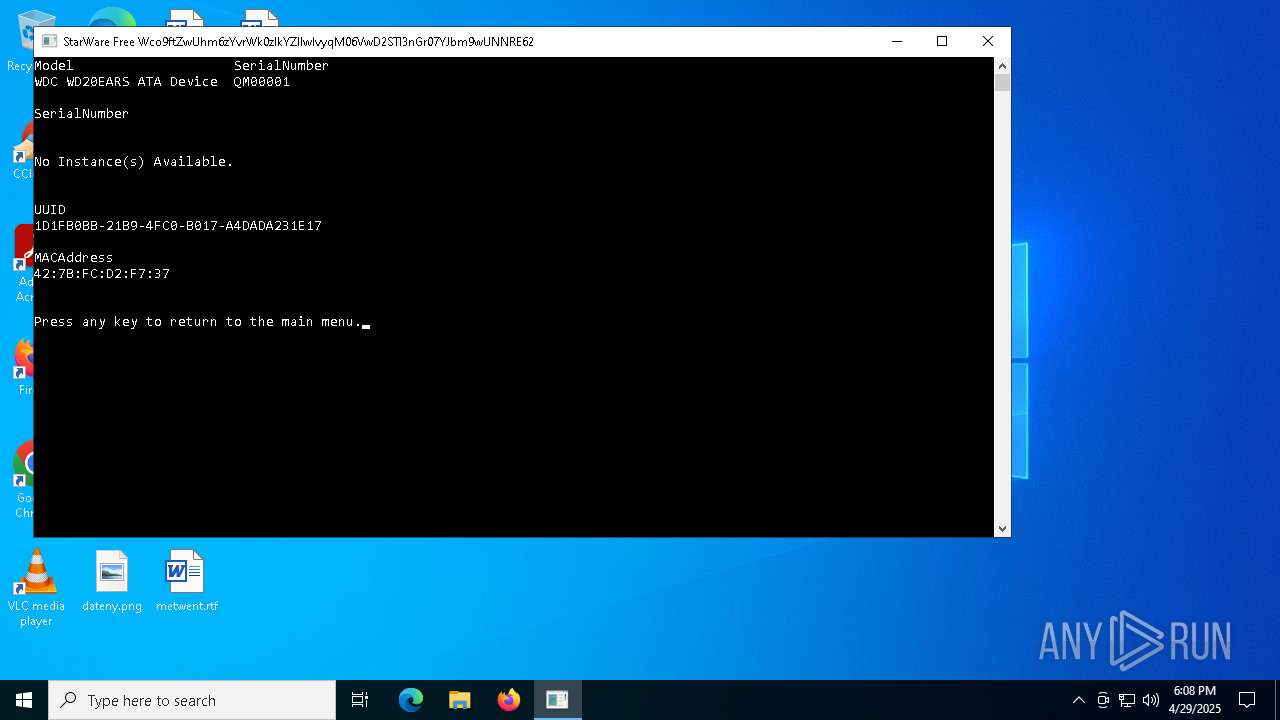
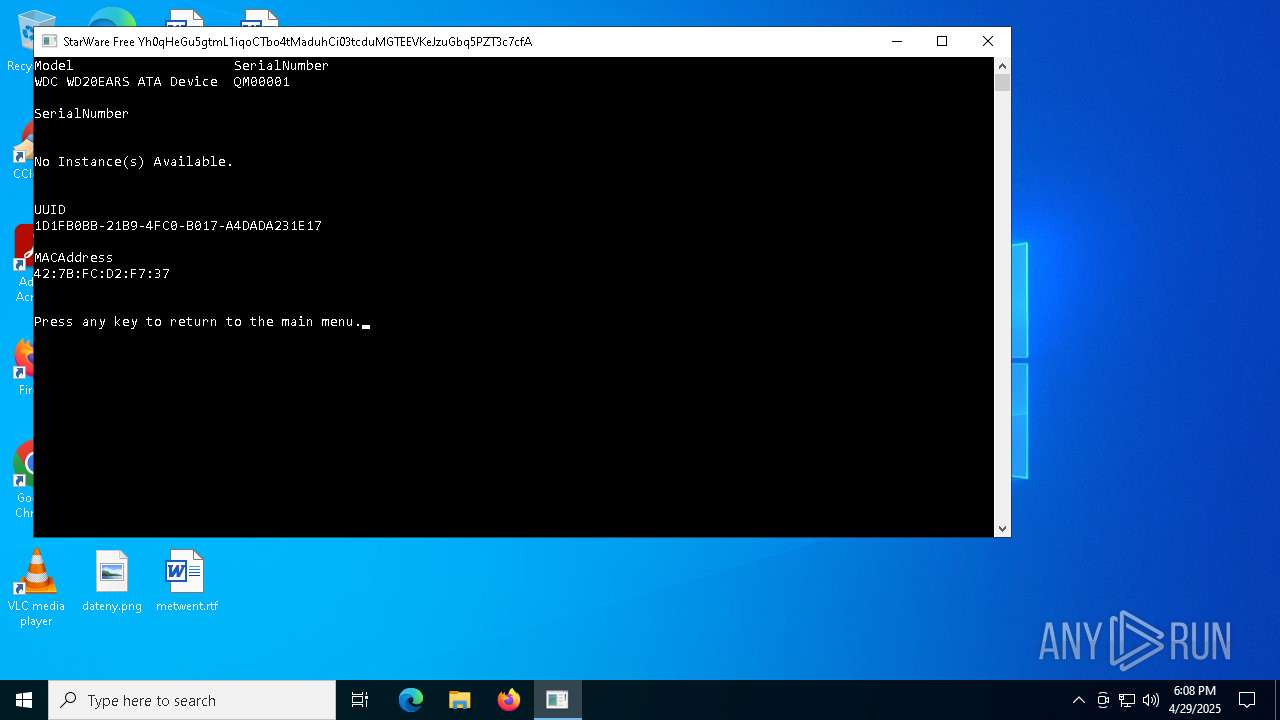
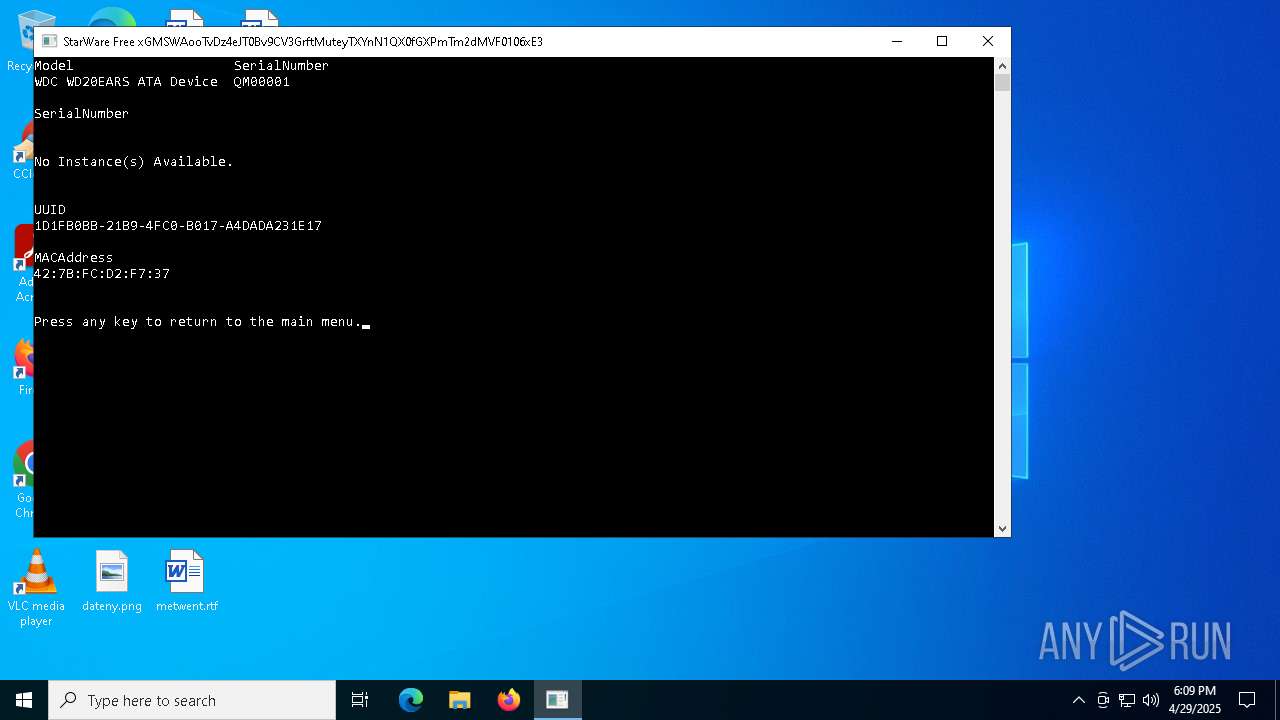
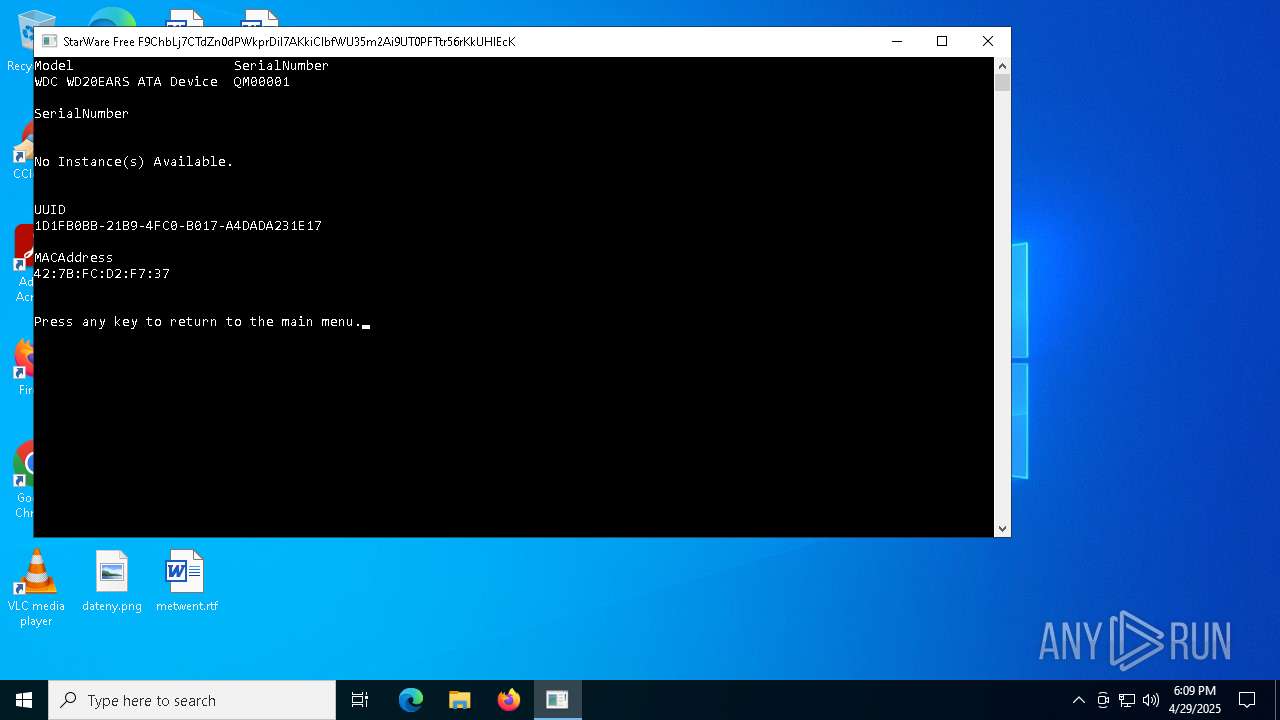
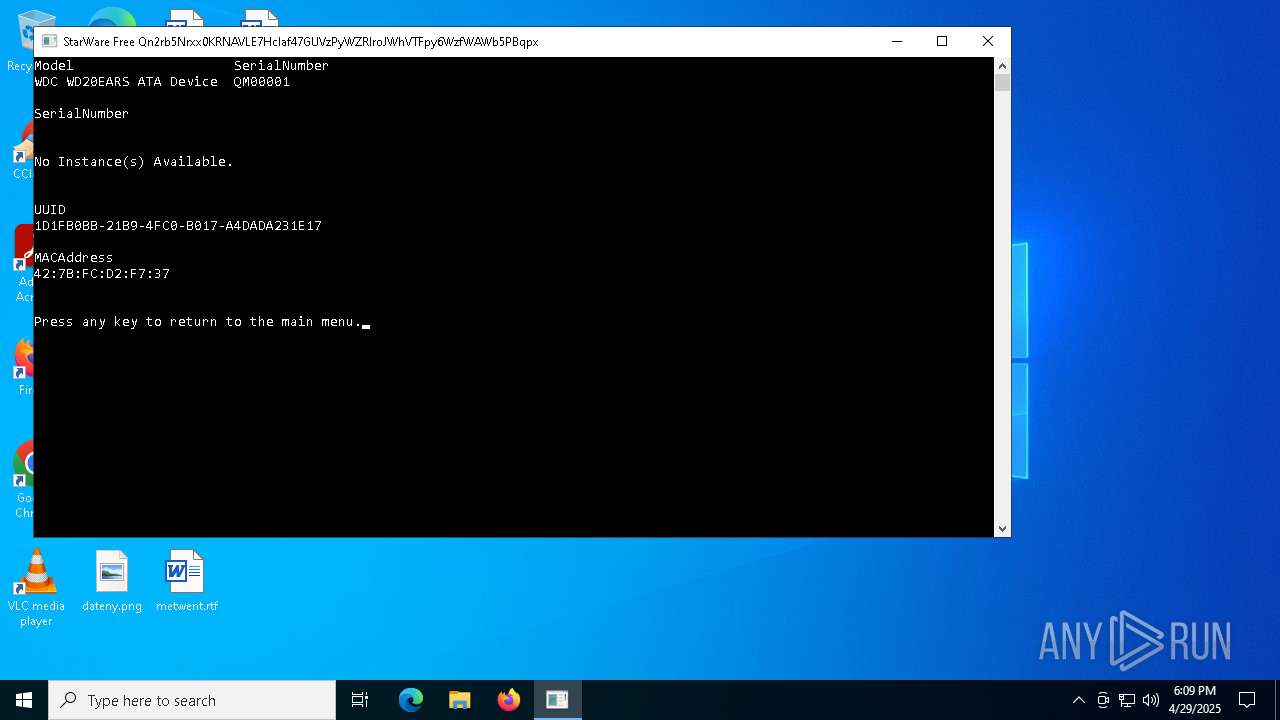
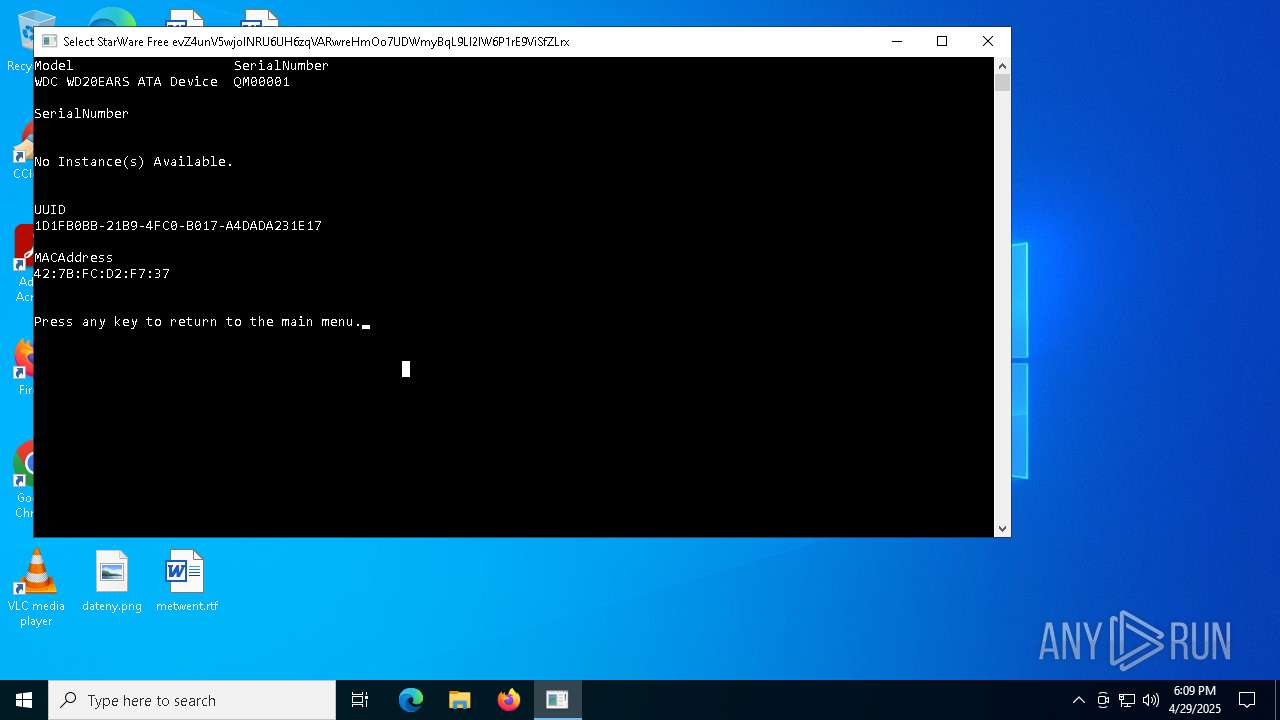
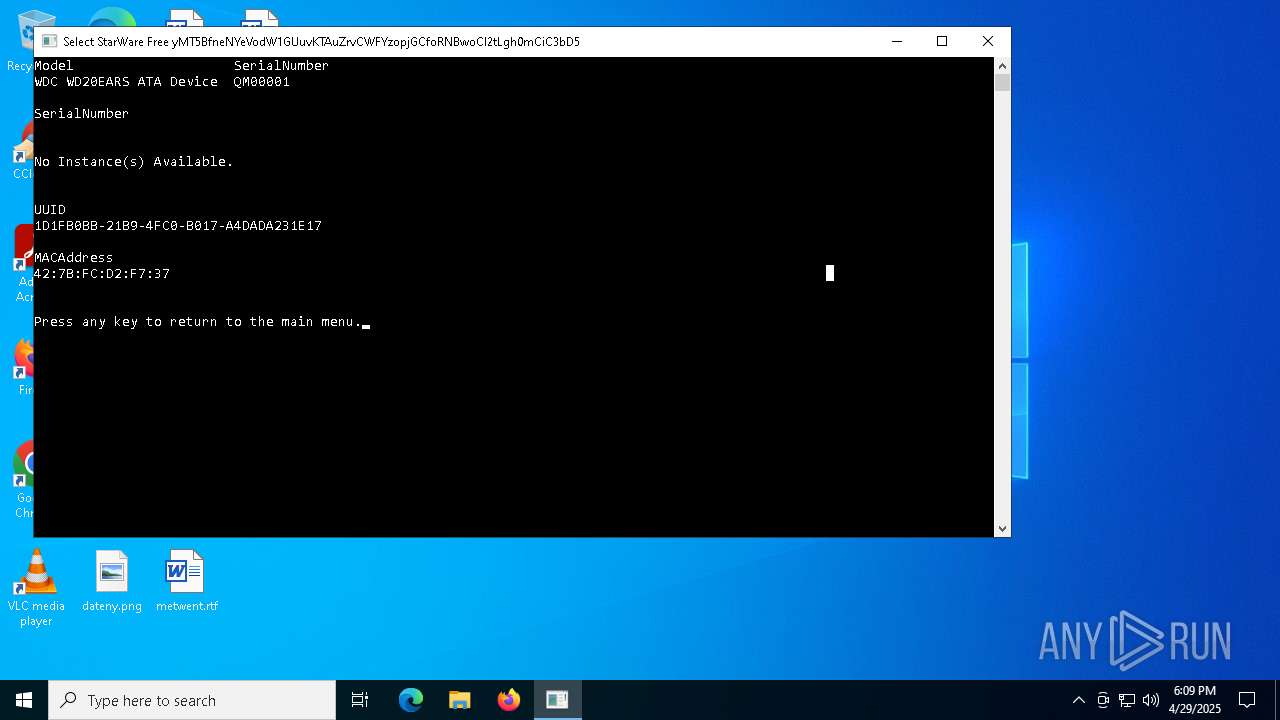
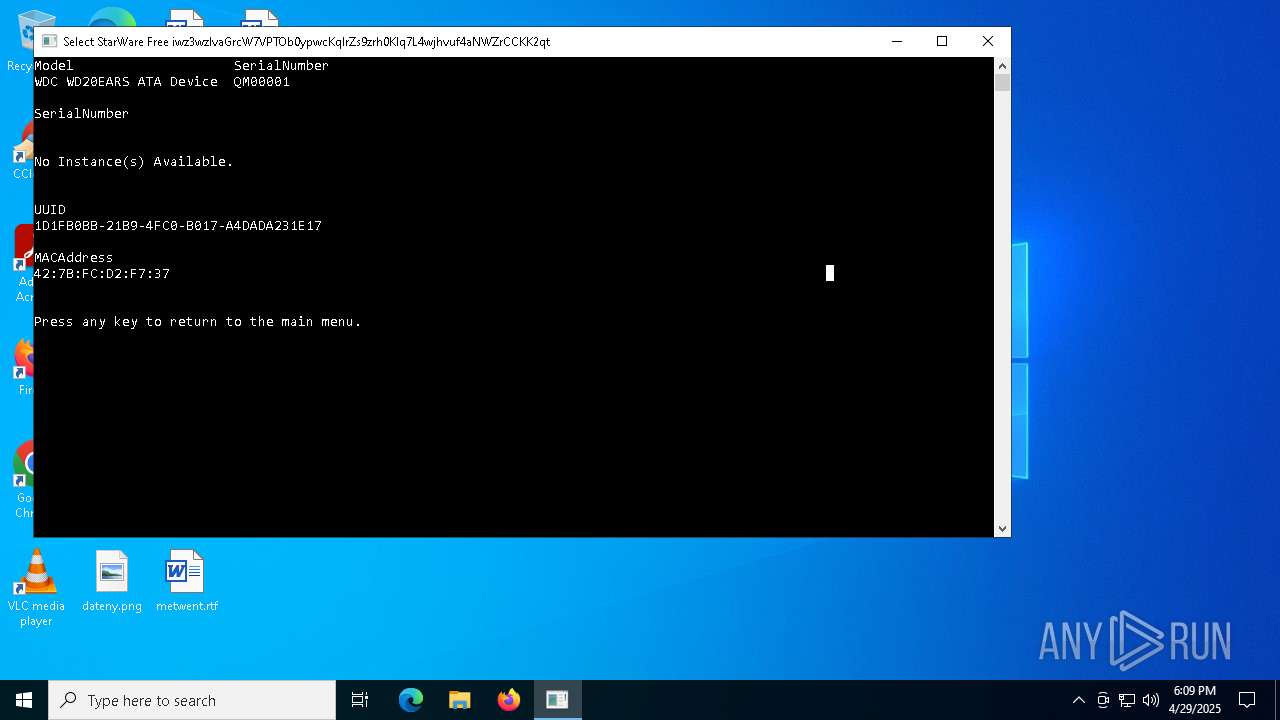
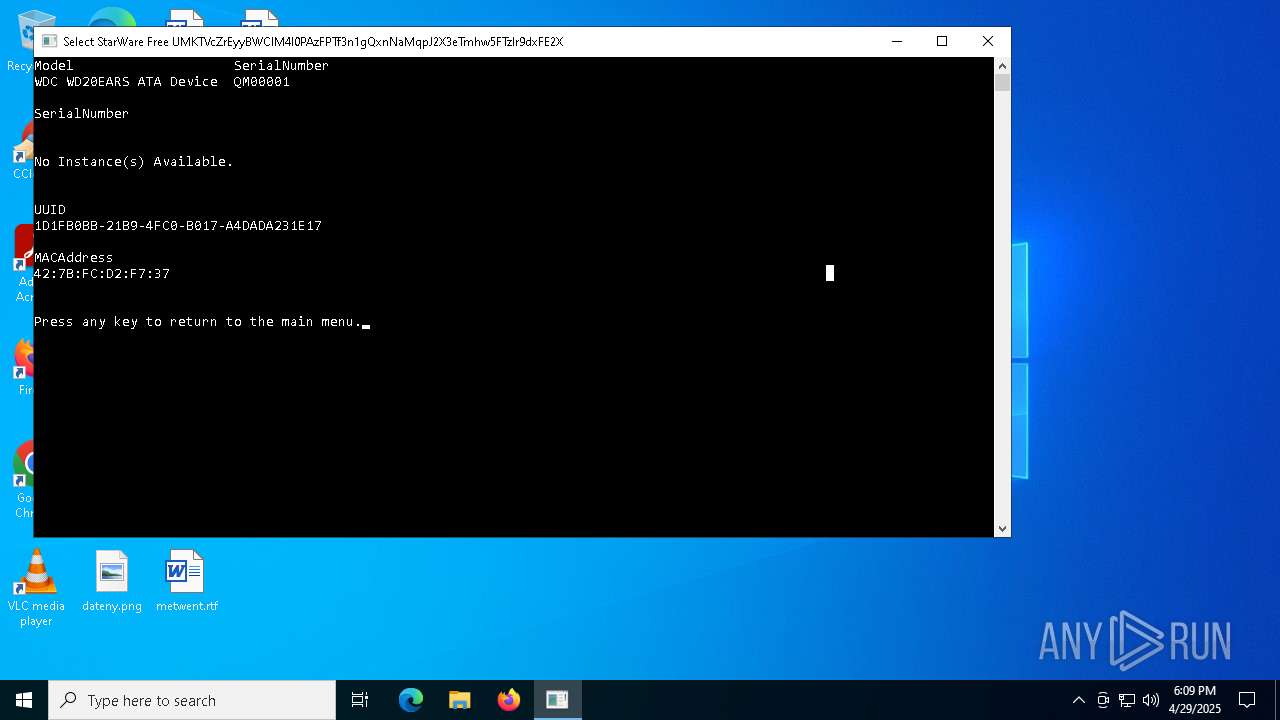
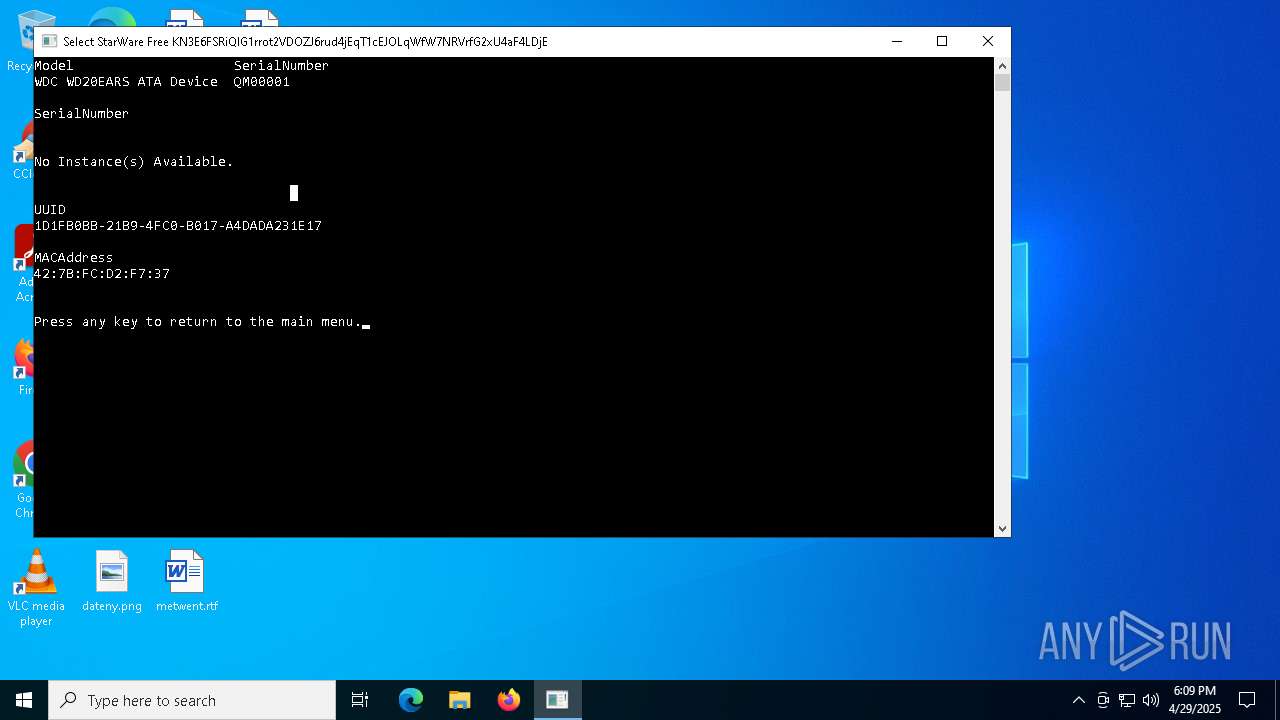
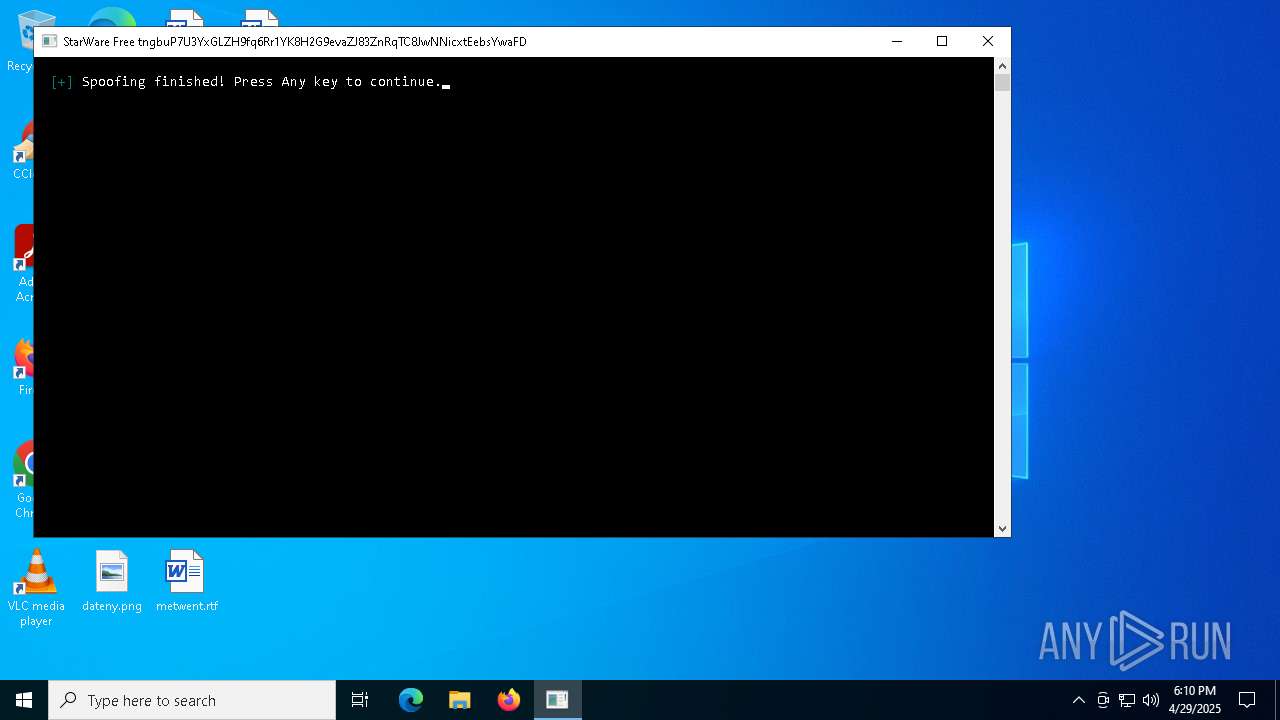
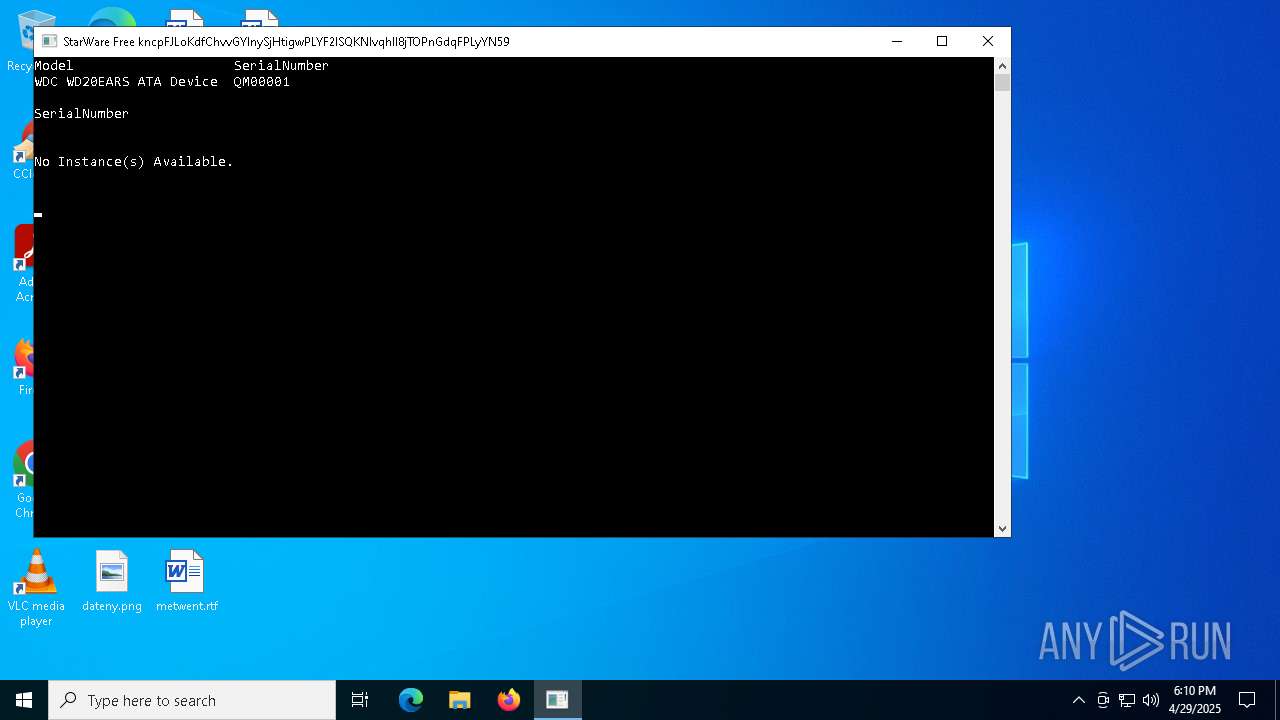
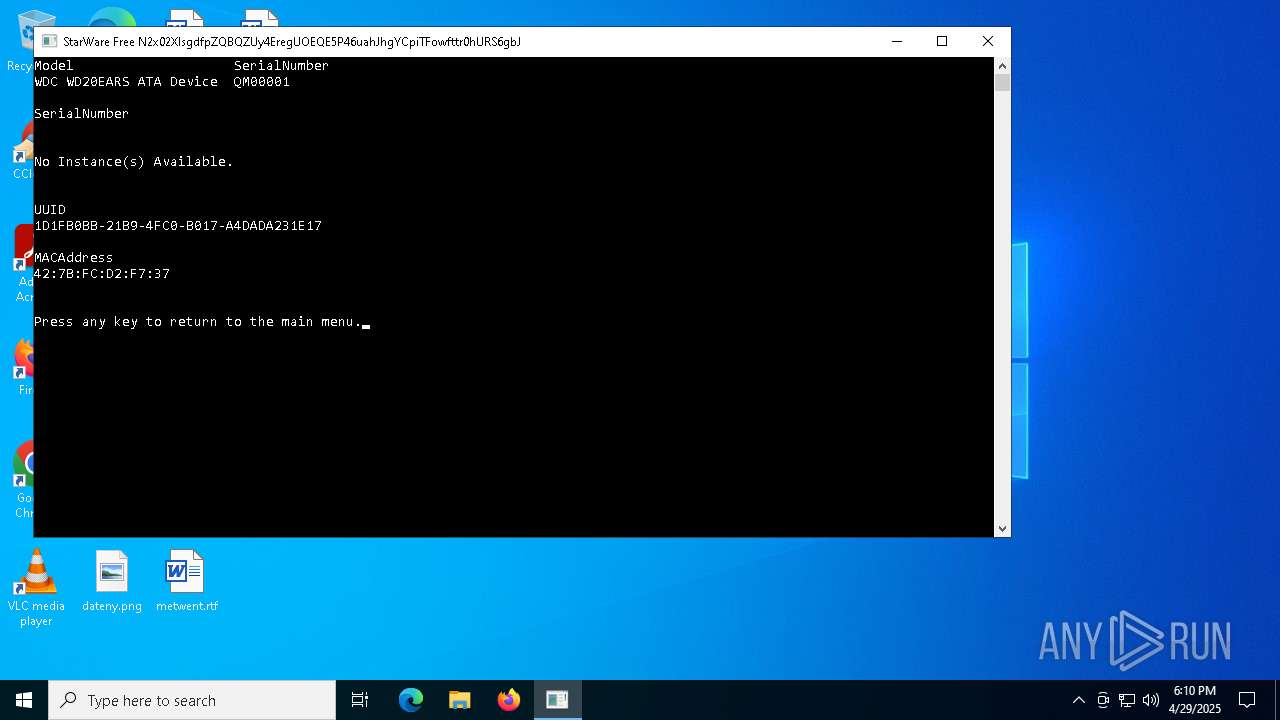
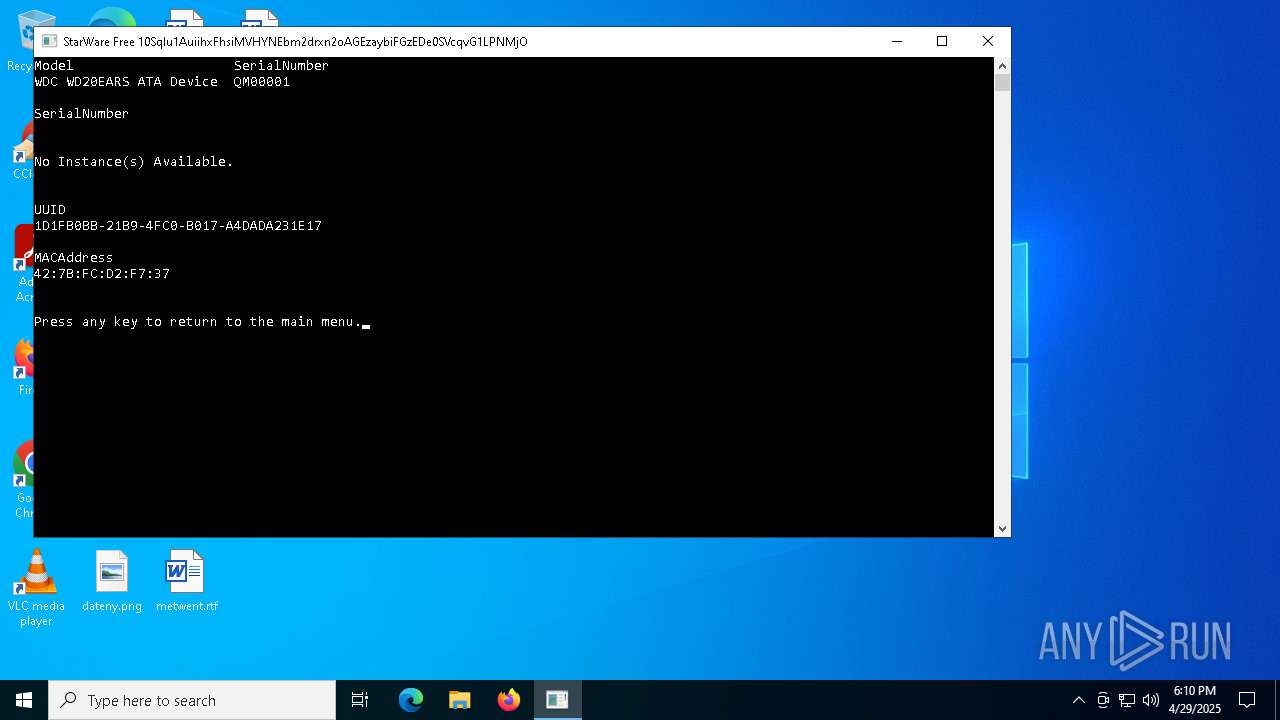
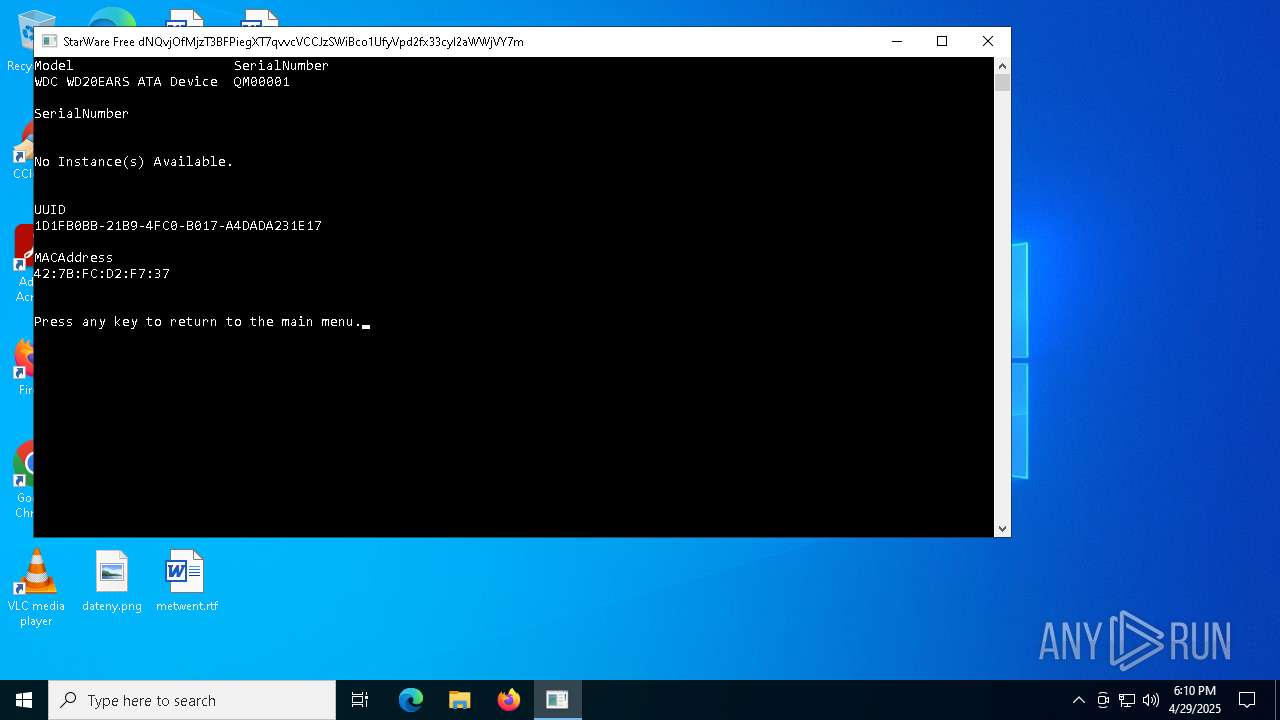
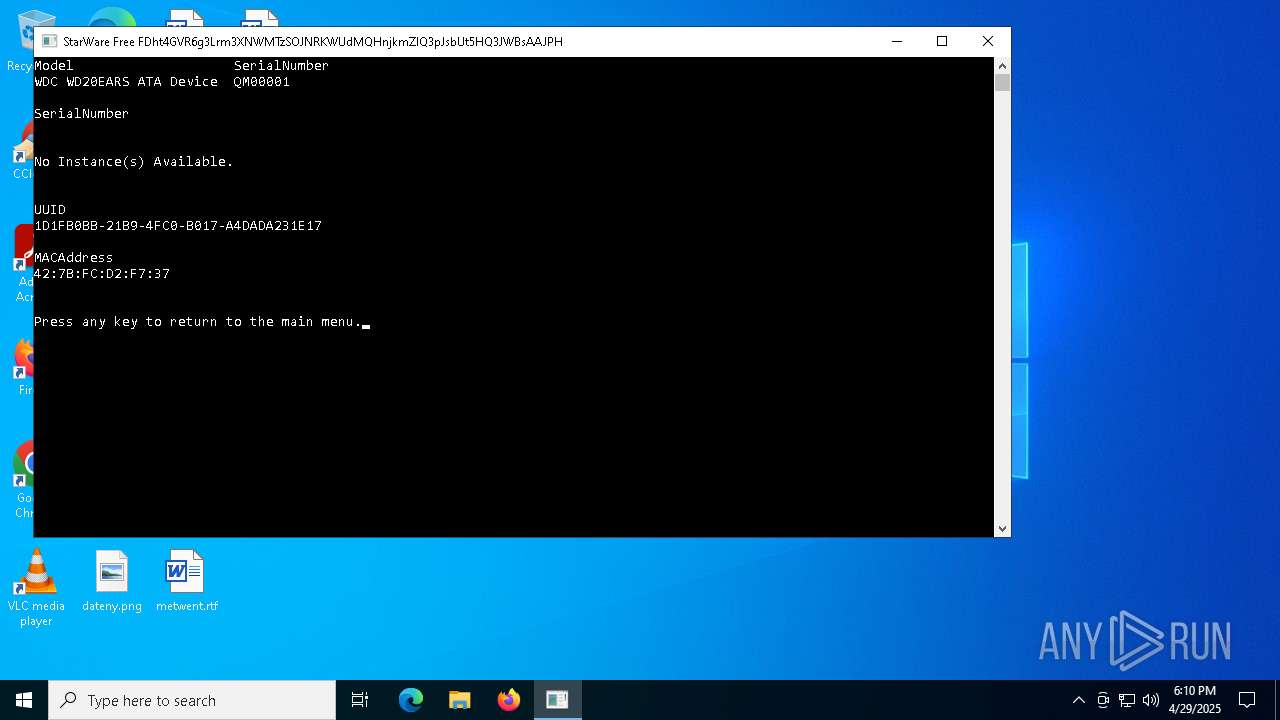
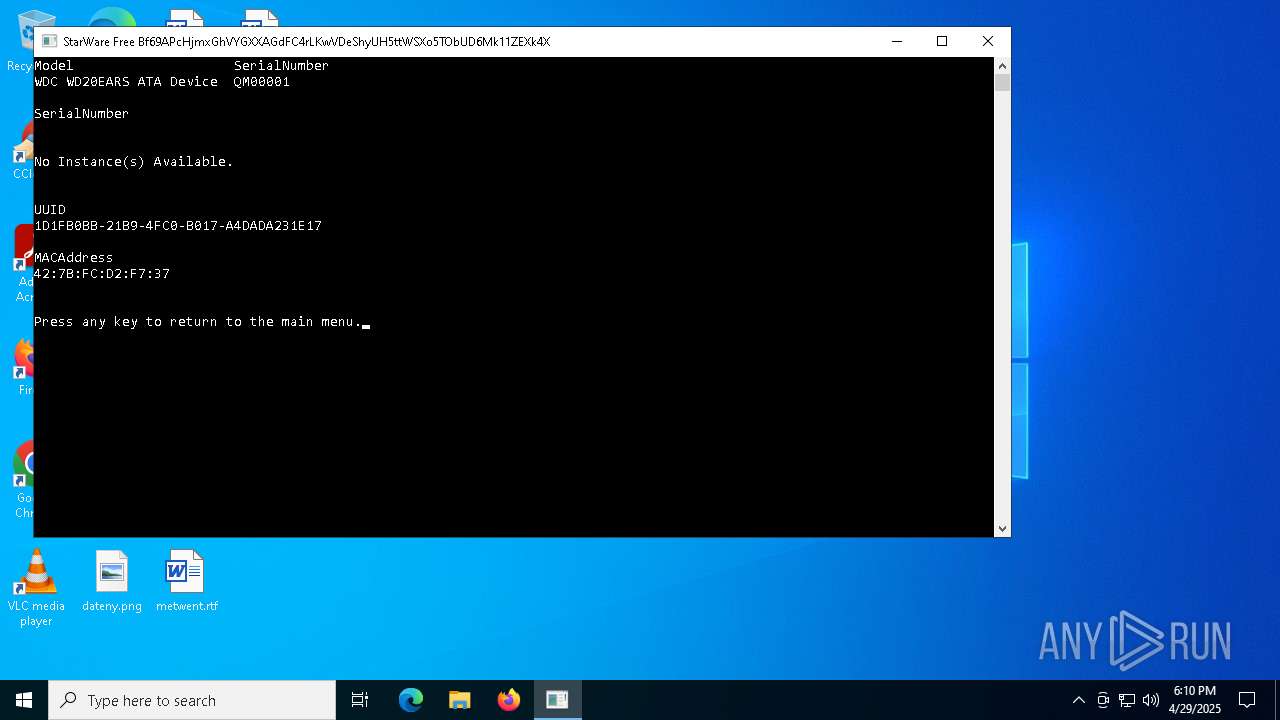
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 8188)
- cmd.exe (PID: 4996)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 1812)
- cmd.exe (PID: 8104)
Uses WMIC.EXE to obtain data on the base board management (motherboard or system board)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 5556)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4560)
- cmd.exe (PID: 6112)
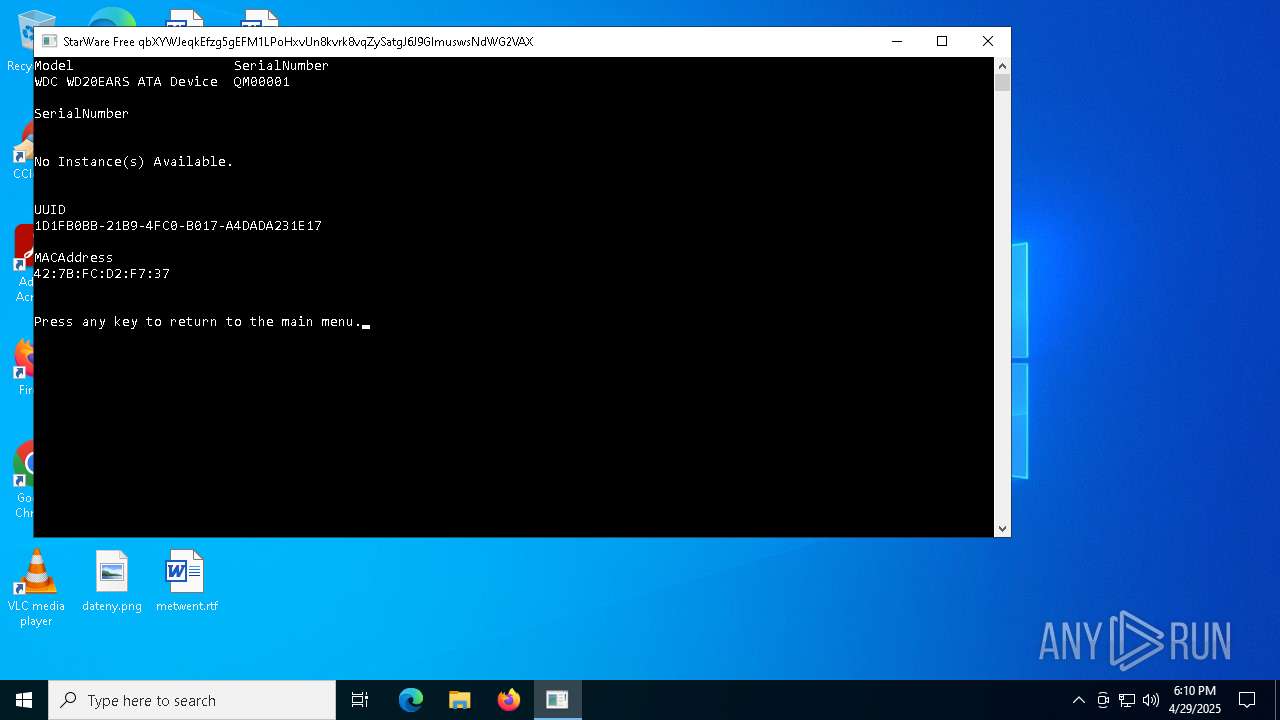
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 5528)
- WMIC.exe (PID: 8136)
Uses WMIC.EXE to obtain network information
- cmd.exe (PID: 1164)
- cmd.exe (PID: 8172)
Starts CMD.EXE for commands execution
- SW-FREE.exe (PID: 4628)
INFO
Checks supported languages
- SW-FREE.exe (PID: 4628)
- curl.exe (PID: 8020)
- curl.exe (PID: 7520)
- curl.exe (PID: 7800)
- curl.exe (PID: 7596)
VMProtect protector has been detected
- SW-FREE.exe (PID: 4628)
Execution of CURL command
- cmd.exe (PID: 8004)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7824)
Reads the computer name
- curl.exe (PID: 8020)
- curl.exe (PID: 7520)
- curl.exe (PID: 7800)
- curl.exe (PID: 7596)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6048)
- WMIC.exe (PID: 1452)
- WMIC.exe (PID: 4812)
- WMIC.exe (PID: 5528)
- WMIC.exe (PID: 2088)
- WMIC.exe (PID: 8116)
- WMIC.exe (PID: 2288)
- WMIC.exe (PID: 8136)
- WMIC.exe (PID: 2664)
- WMIC.exe (PID: 776)
Reads the software policy settings
- slui.exe (PID: 7248)
- slui.exe (PID: 3140)
Checks proxy server information
- slui.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:08 11:13:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 35328 |
| InitializedDataSize: | 18944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x691883 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
216
Monitored processes
84
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\WINDOWS\system32\cmd.exe /c pause > nul | C:\Windows\System32\cmd.exe | — | SW-FREE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | SW-FREE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | wmic baseboard get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | C:\WINDOWS\system32\cmd.exe /c wmic nic where (NetConnectionStatus=2) get MACAddress | C:\Windows\System32\cmd.exe | — | SW-FREE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\system32\cmd.exe /c pause > nul | C:\Windows\System32\cmd.exe | — | SW-FREE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\system32\cmd.exe /c net stop Winmgmt | C:\Windows\System32\cmd.exe | — | SW-FREE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | wmic bios get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | SW-FREE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | C:\WINDOWS\system32\cmd.exe /c wmic bios get serialnumber | C:\Windows\System32\cmd.exe | — | SW-FREE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | wmic nic where (NetConnectionStatus=2) get MACAddress | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 365
Read events
5 365
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7520 | curl.exe | C:\Windows\MemoryIntegrityx64.exe | html | |
MD5:A9F2163A24F9F4FCBD1AC0316494EFC6 | SHA256:2A9DC761FC33E70926CDBD914E0A347DA90396DF6C316C44899F396E923A855C | |||
| 7800 | curl.exe | C:\Windows\applecleaner.exe | html | |
MD5:A9F2163A24F9F4FCBD1AC0316494EFC6 | SHA256:2A9DC761FC33E70926CDBD914E0A347DA90396DF6C316C44899F396E923A855C | |||
| 8020 | curl.exe | C:\Windows\applecleaner.exe | html | |
MD5:A9F2163A24F9F4FCBD1AC0316494EFC6 | SHA256:2A9DC761FC33E70926CDBD914E0A347DA90396DF6C316C44899F396E923A855C | |||
| 7596 | curl.exe | C:\Windows\SteelSeriesGG.sys | html | |
MD5:A9F2163A24F9F4FCBD1AC0316494EFC6 | SHA256:2A9DC761FC33E70926CDBD914E0A347DA90396DF6C316C44899F396E923A855C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
32
DNS requests
21
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 142.250.185.195:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
7840 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7840 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
link.storjshare.io |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
8020 | curl.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Domain (link .storjshare .io in TLS SNI) |
8020 | curl.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (storjshare .io in TLS SNI) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Commonly Actor Abused Online Service Domain (storjshare .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
7520 | curl.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Domain (link .storjshare .io in TLS SNI) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Commonly Actor Abused Online Service Domain (storjshare .io) |
7520 | curl.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (storjshare .io in TLS SNI) |
7596 | curl.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Domain (link .storjshare .io in TLS SNI) |
7596 | curl.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (storjshare .io in TLS SNI) |