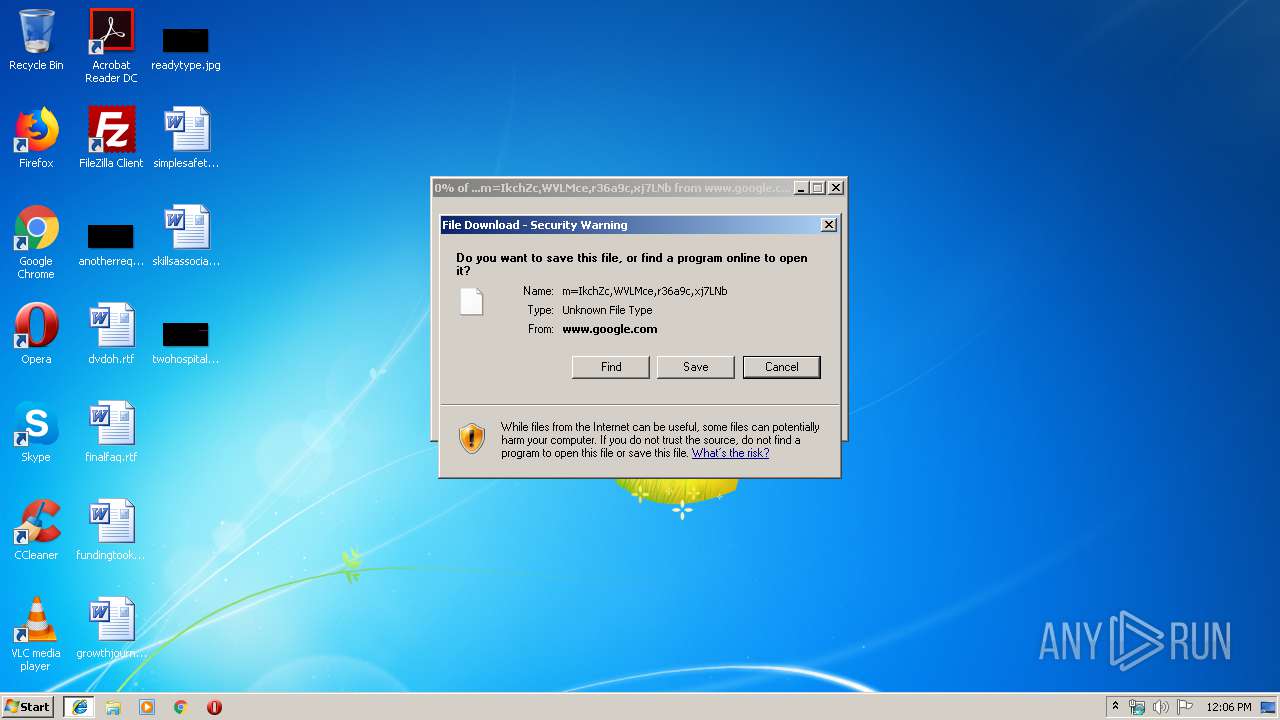
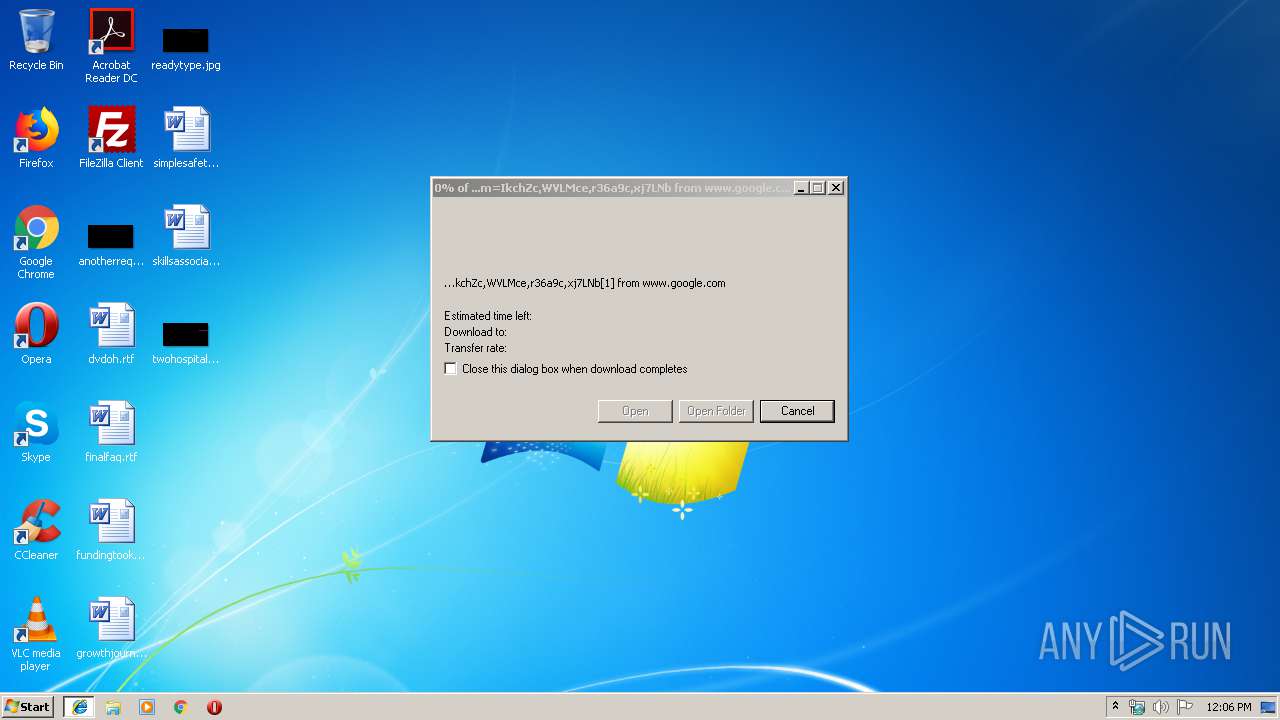
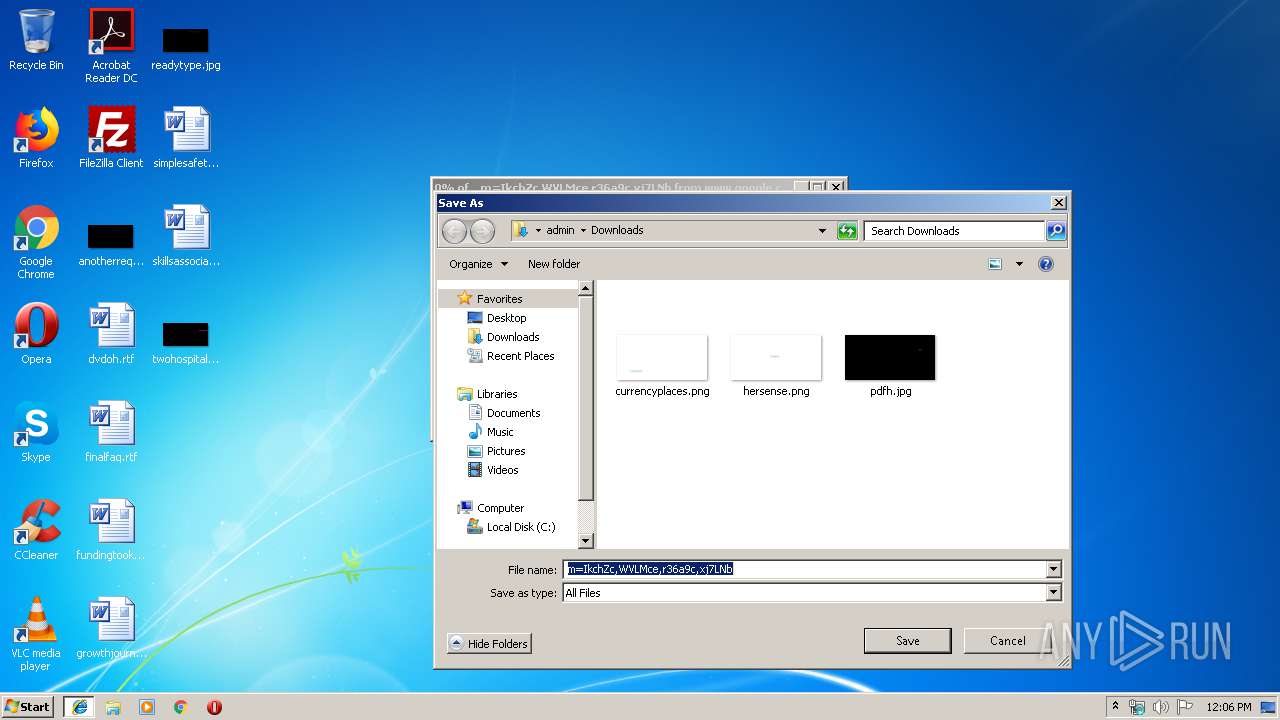
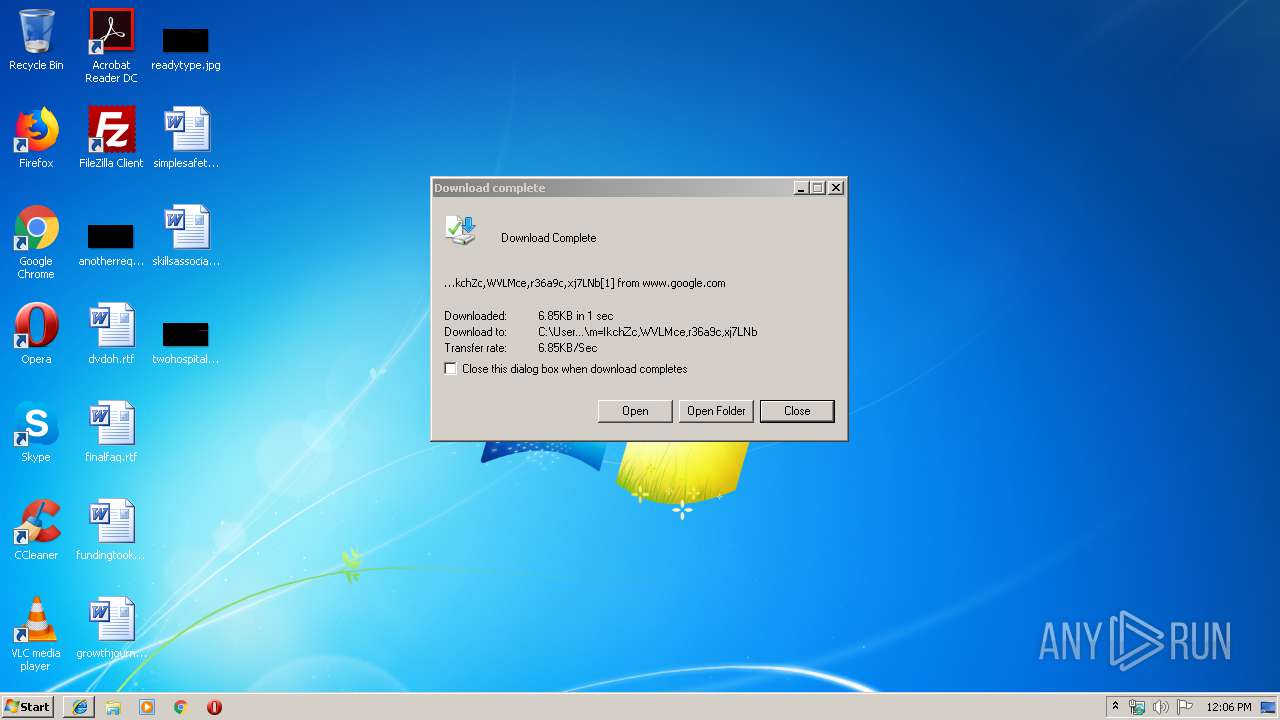
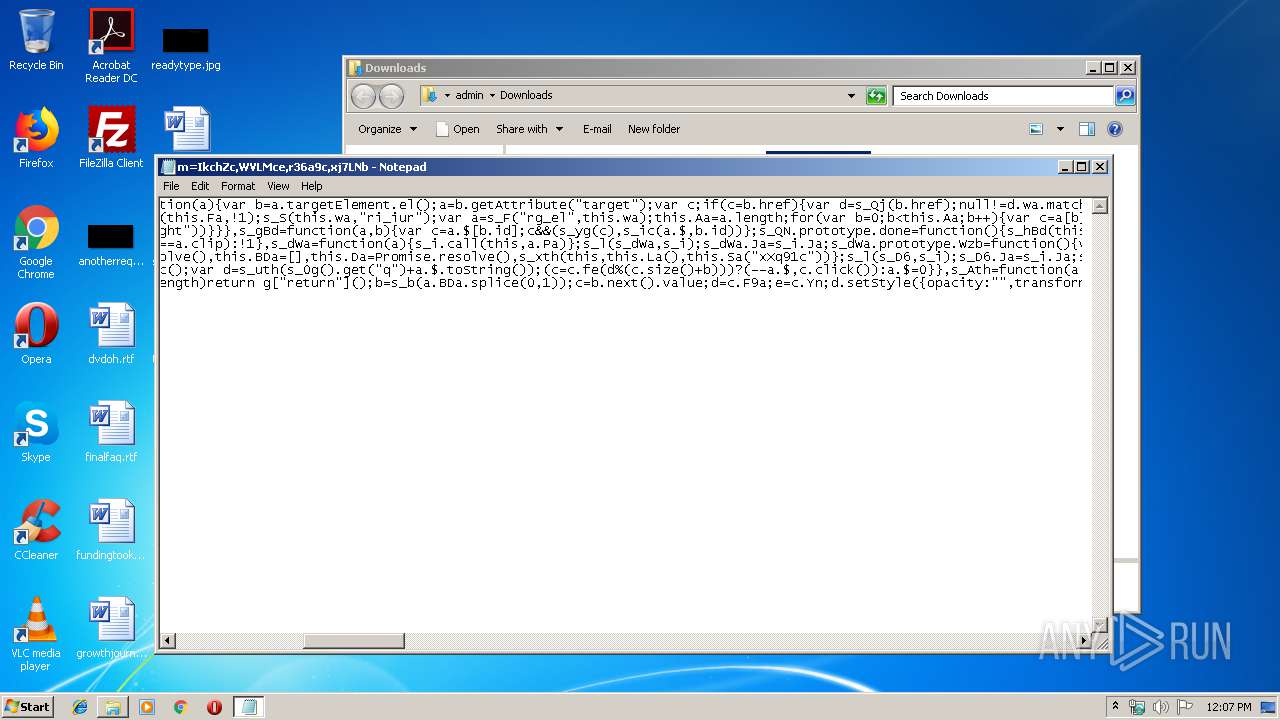
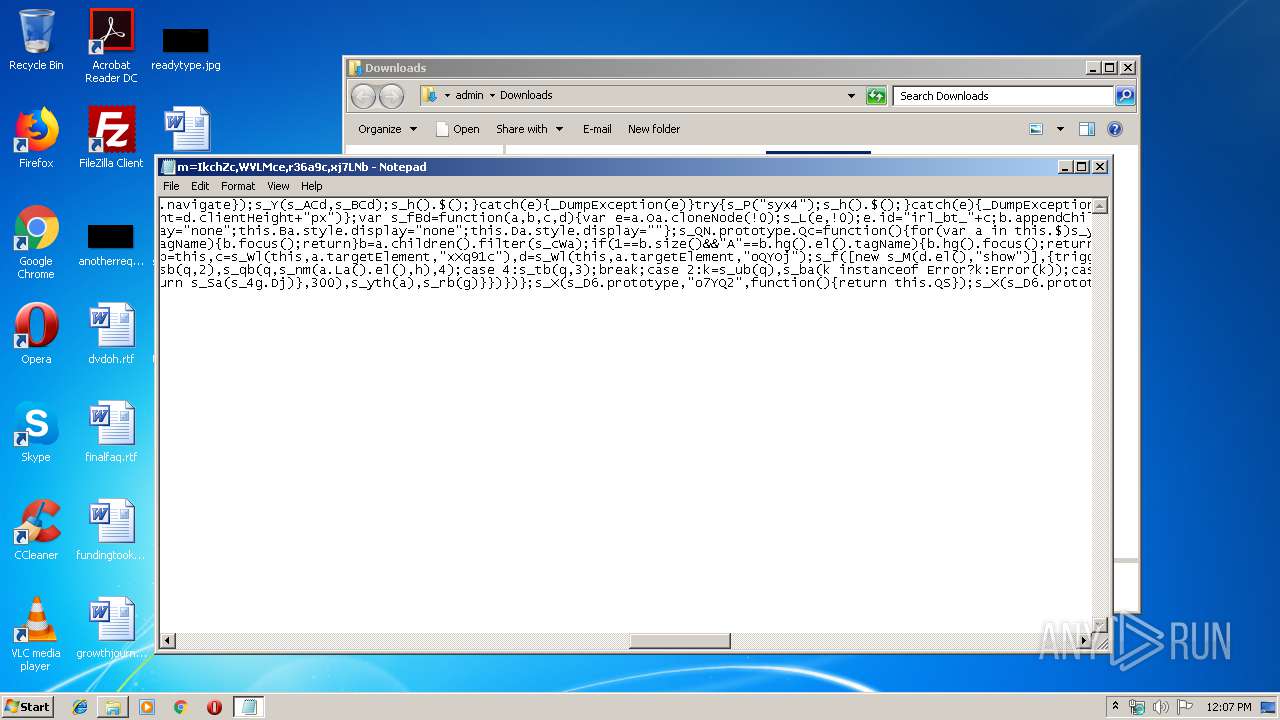
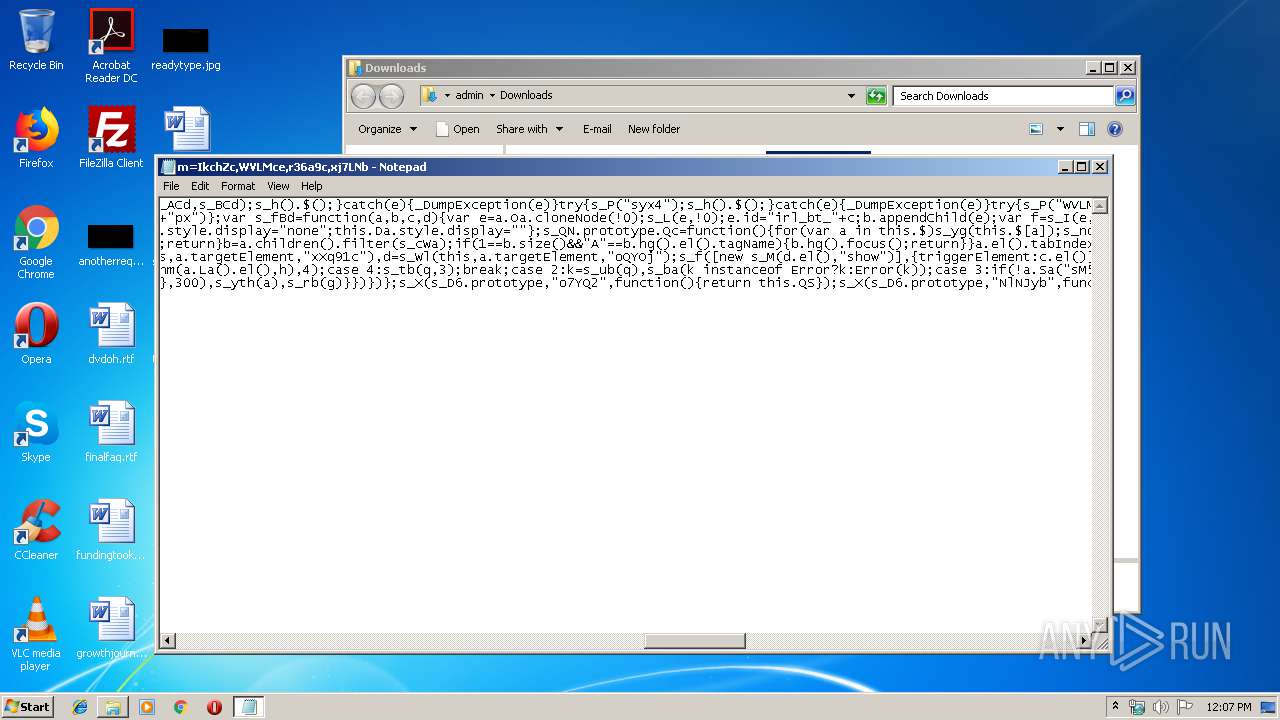
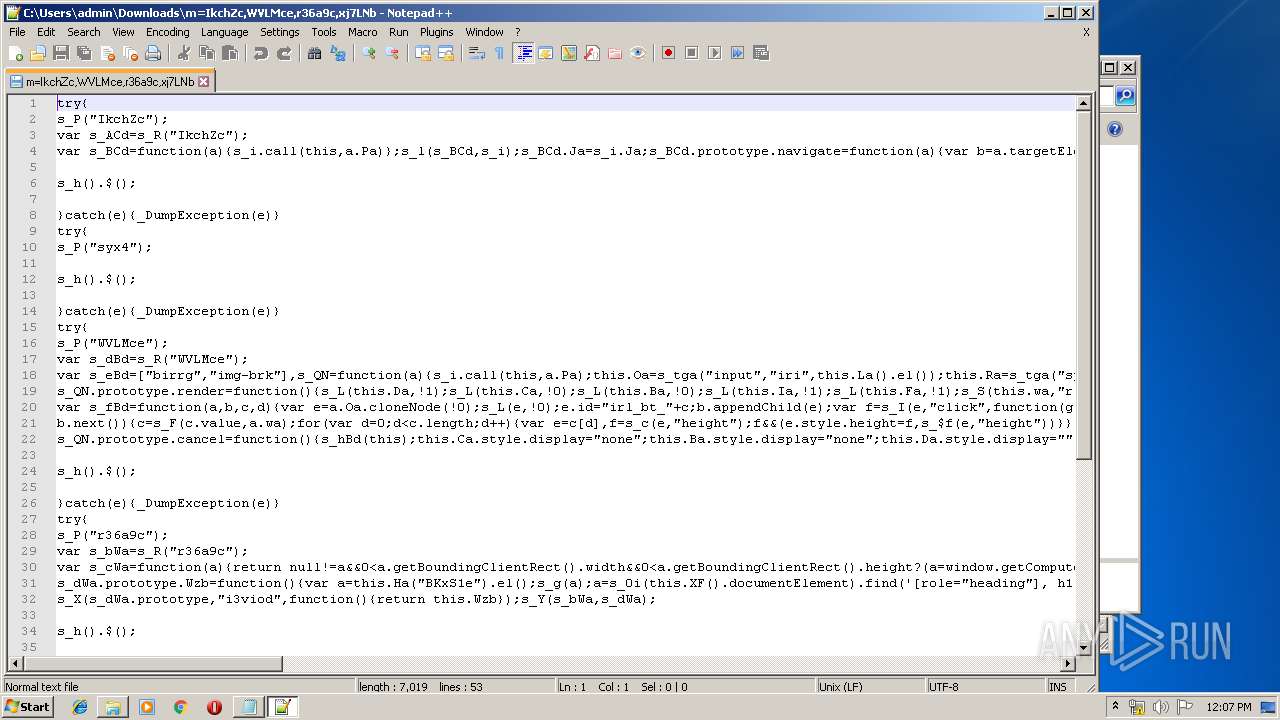
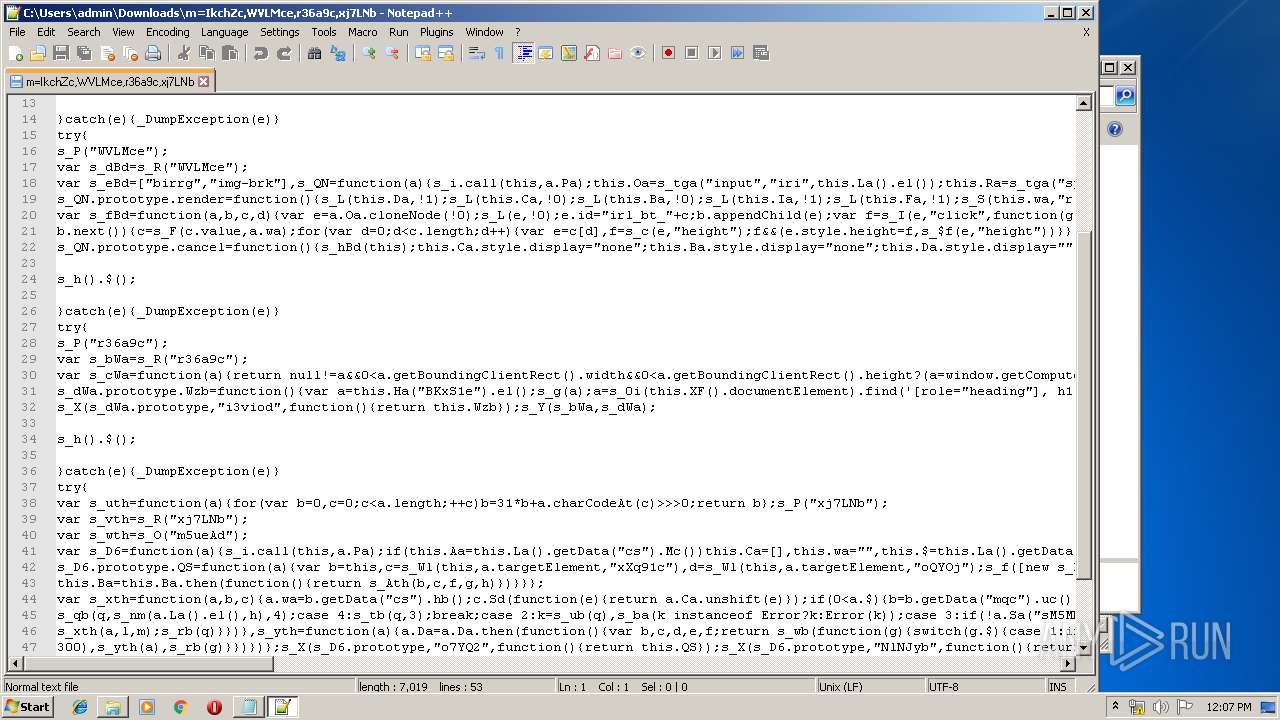
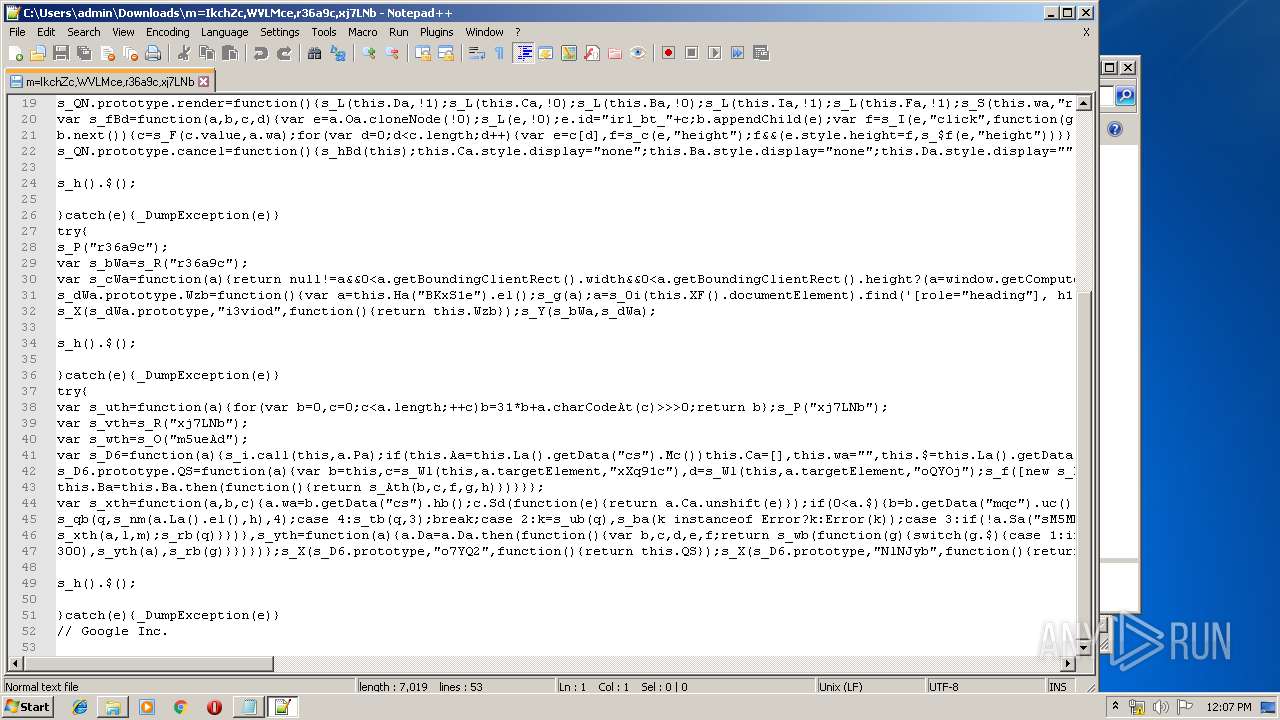
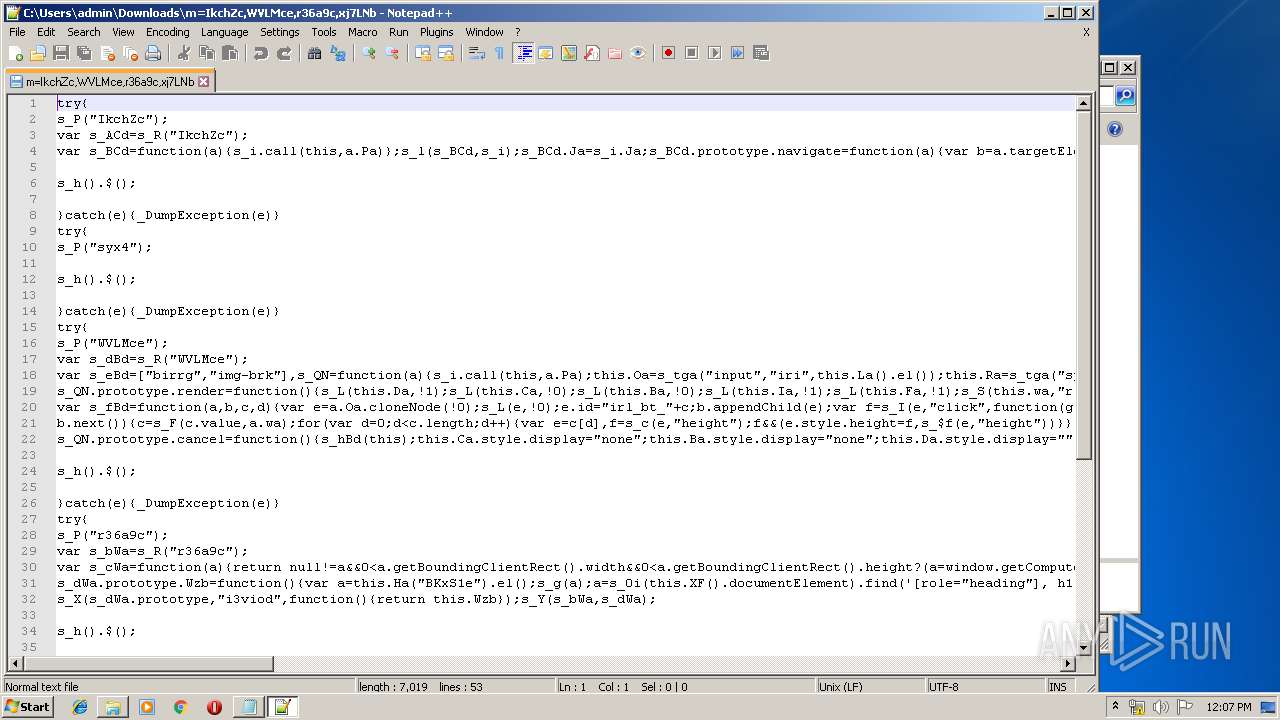
| URL: | https://www.google.com/xjs/_/js/k=xjs.s.en_GB.IfrOTSWH_to.O/ck=xjs.s.pDuUZZDMmVw.L.I11.O/am=AAAAgEUAMwAAIP8PBQAAQB0DAAABYcEGC4QhIcNYmIAAEA/d=1/exm=Fkg7bd,HcFEGb,IvlUe,MC8mtf,MkHyGd,OF7gzc,OG6ZHd,RMhBfe,SvnKM,T4BAC,T6sTsf,T7XTS,TJw5qb,TbaHGc,TxZWcc,URQPYc,WgDvvc,Wq6lxf,XMgU6d,XjCeUc,Y33vzc,ZyRBae,aCZVp,aa,aam1T,abd,aspn,async,bgd,cdos,cr,csi,d,dvl,eN4qad,ebqyud,foot,hsm,iDPoPb,jsa,kyn,lazG7b,lli,lu,m,mI3LFb,mUpTid,mpck,mu,mvYTse,o02Jie,pB6Zqd,qik19b,rHjpXd,sb_wiz,sf,tg8oTe,tl,uiNkee,uz938c,vWNDde,vs,wkrYee,ws9Tlc,xc1DSd,xz7cCd,yQ43ff,zbML3c/ed=1/dg=2/ct=zgms/rs=ACT90oHB8hpqHUGl7ek8w57bpeIMVTSo9g/m=IkchZc,WVLMce,r36a9c,xj7LNb?xjs=s2 |
| Full analysis: | https://app.any.run/tasks/53fed234-cd65-4a8c-8c84-3b83dd74aa28 |
| Verdict: | No threats detected |
| Analysis date: | December 20, 2019, 12:06:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A4544C02467ED655529ED37498D78516 |
| SHA1: | 05FF6A1F57D9224B9BC840726949C642EF7F2317 |
| SHA256: | C73C081B8DD2FDC4B67CFB0BCCFCF2DF1A4880530E4731E70CF417838D5A29CF |
| SSDEEP: | 12:2VTuV2DDQrS282isSKdMVVThWEk3zLQeUKJnVh8zjZUAYUthiFJ4bzpBVJJKAU:25uVPrSRe5uTUE4z0SVh8zjRqWbzpBXu |
MALICIOUS
No malicious indicators.SUSPICIOUS
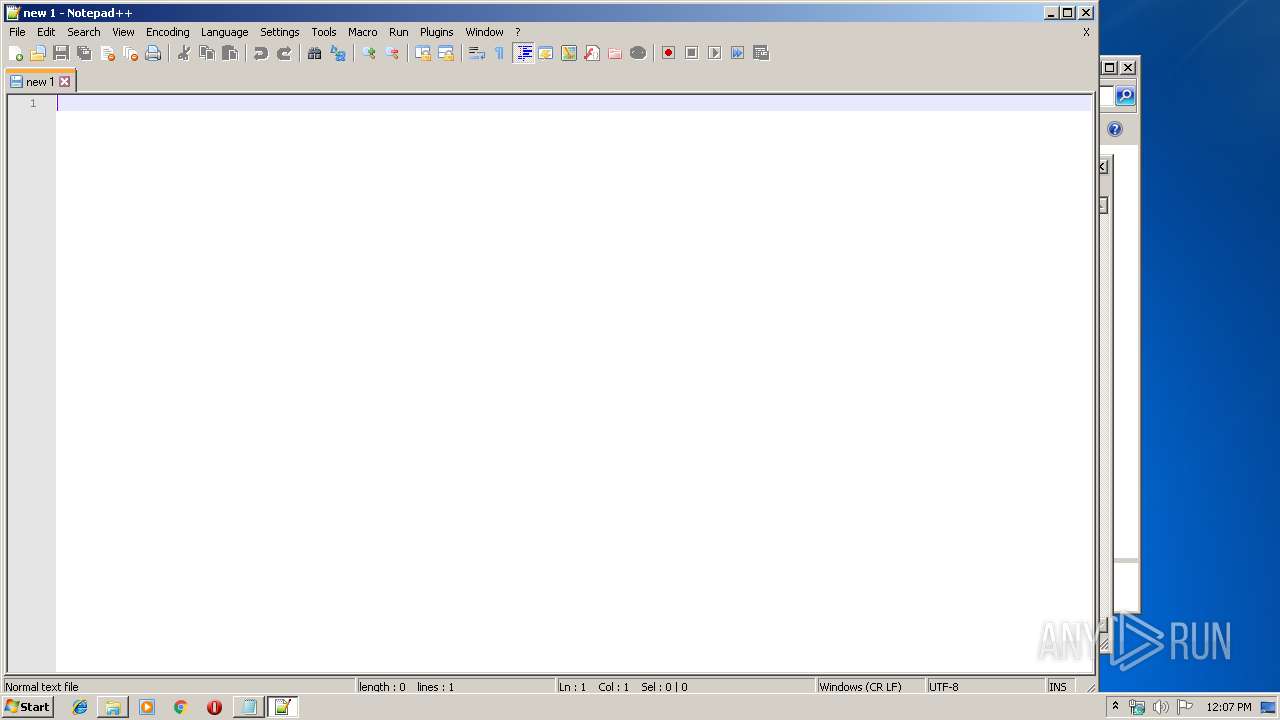
Creates files in the user directory
- notepad++.exe (PID: 4088)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 748)
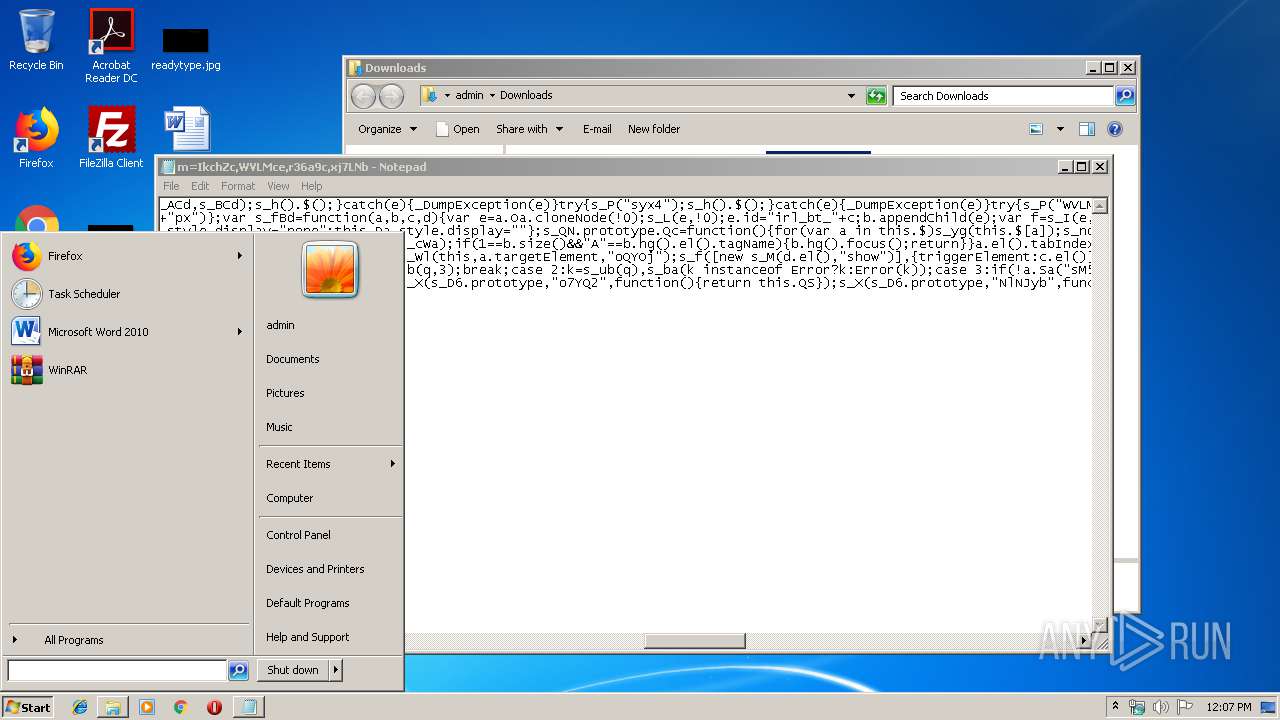
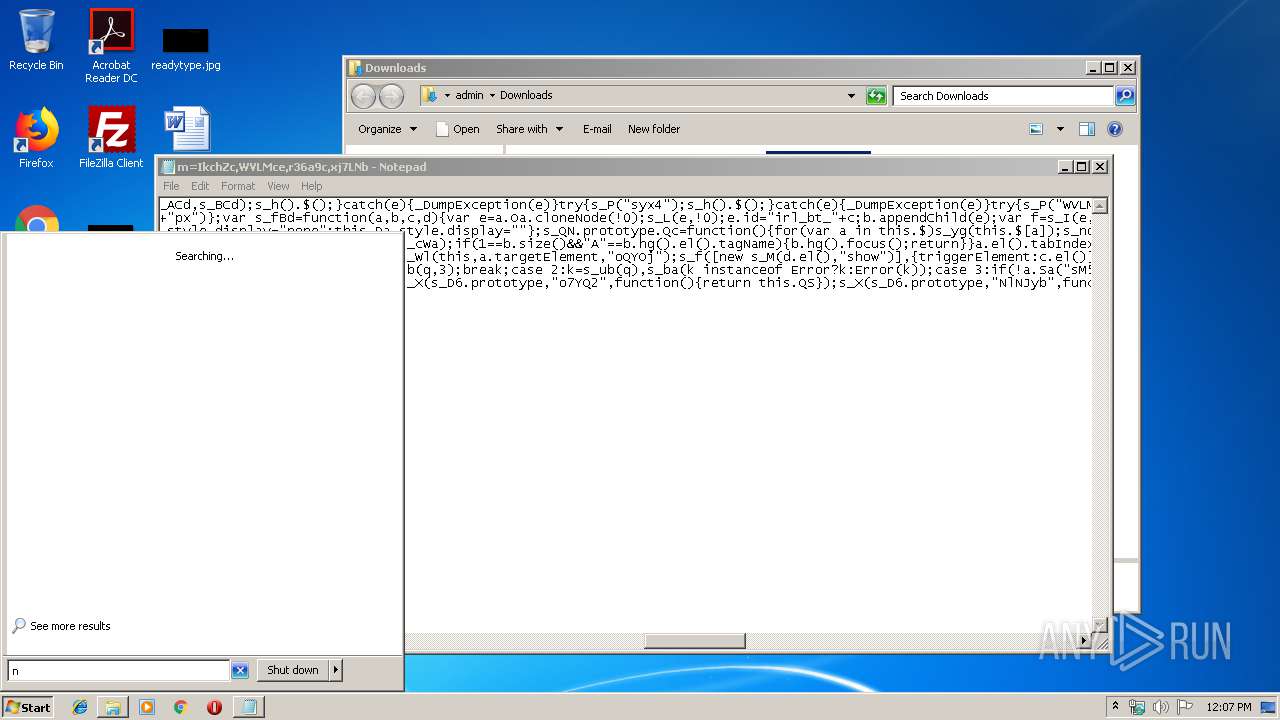
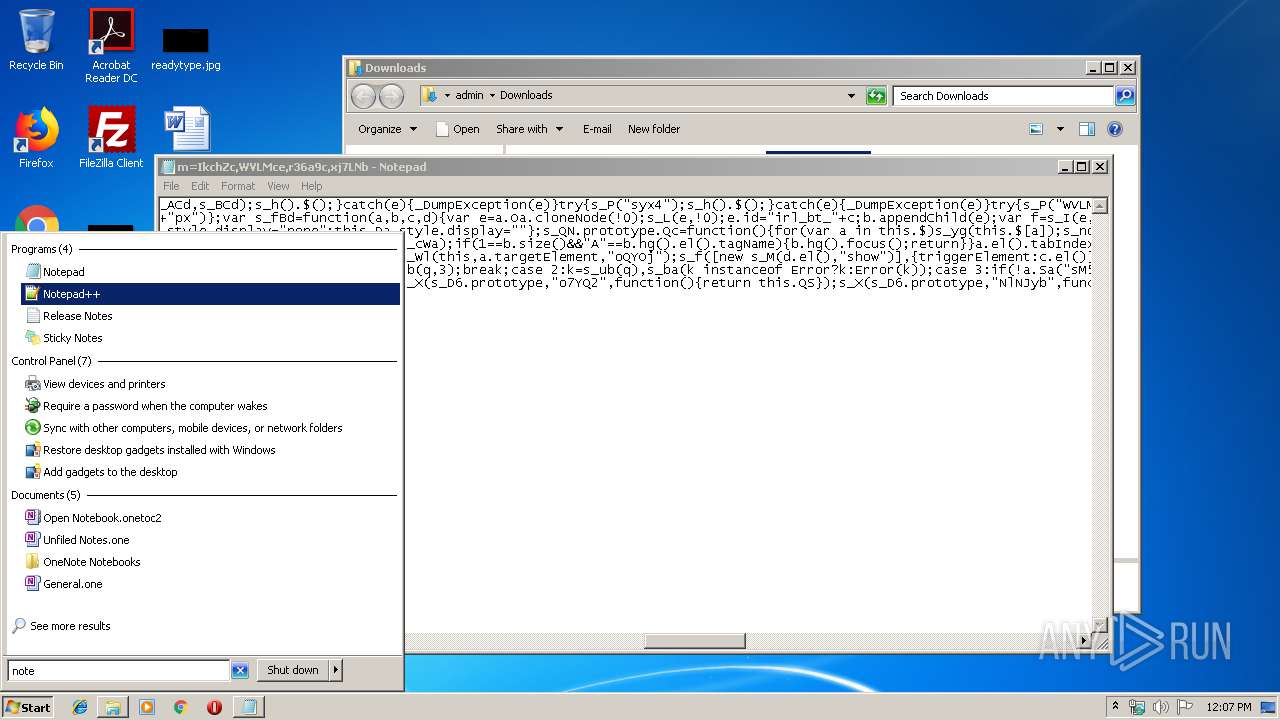
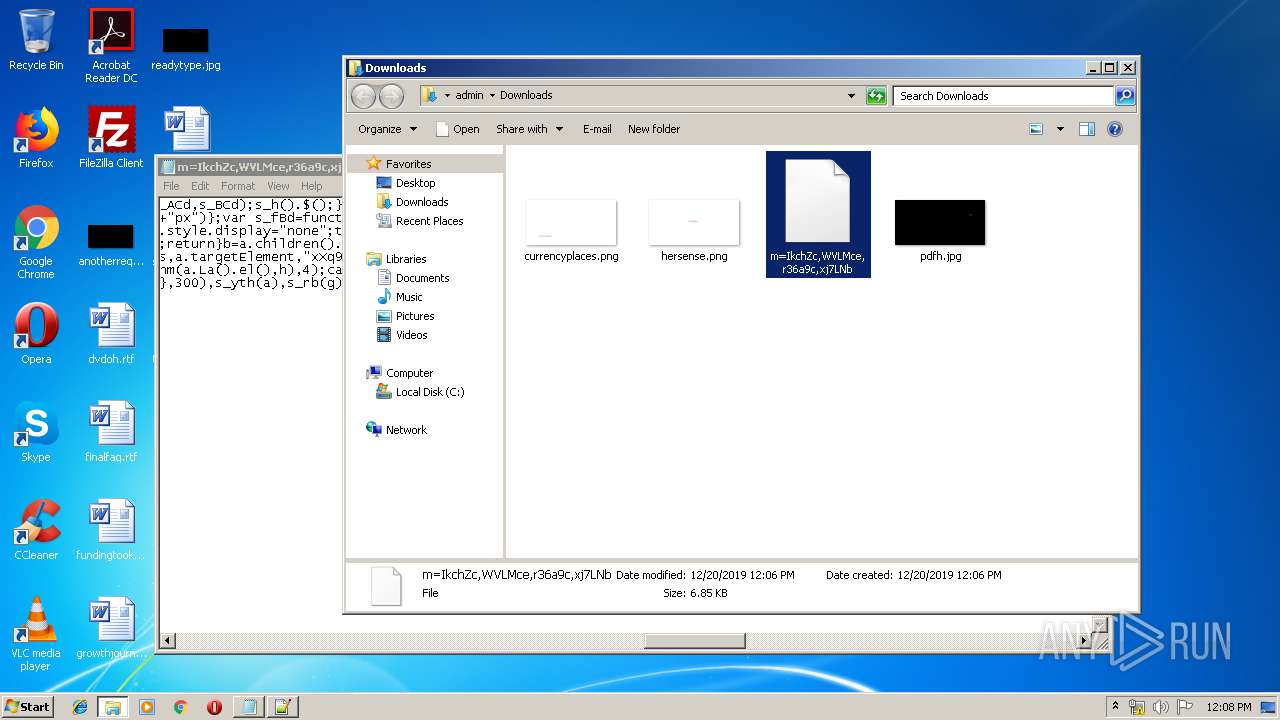
Manual execution by user
- notepad++.exe (PID: 4088)
- rundll32.exe (PID: 856)
- iexplore.exe (PID: 748)
Creates files in the user directory
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 748)
Application launched itself
- iexplore.exe (PID: 748)
Reads Internet Cache Settings
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 2396)
- iexplore.exe (PID: 2516)
Reads settings of System Certificates
- iexplore.exe (PID: 748)
Changes settings of System certificates
- iexplore.exe (PID: 748)
Adds / modifies Windows certificates
- iexplore.exe (PID: 748)
Reads internet explorer settings
- iexplore.exe (PID: 1764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
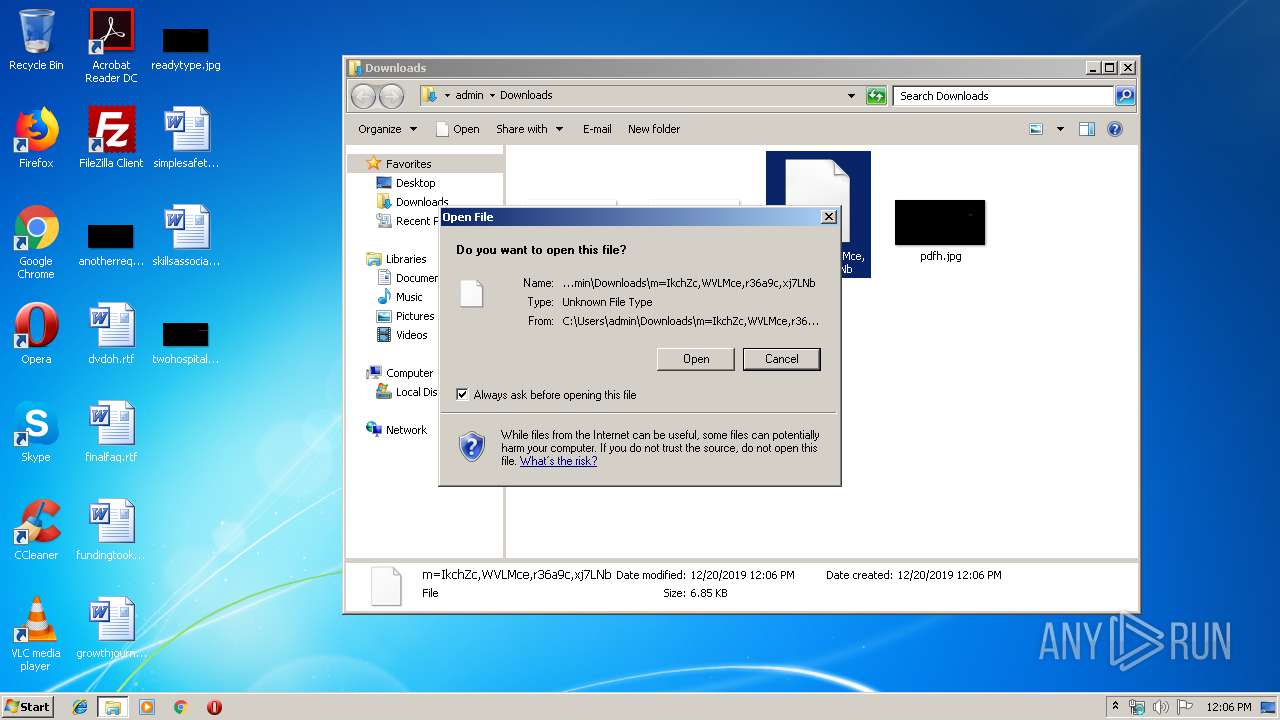
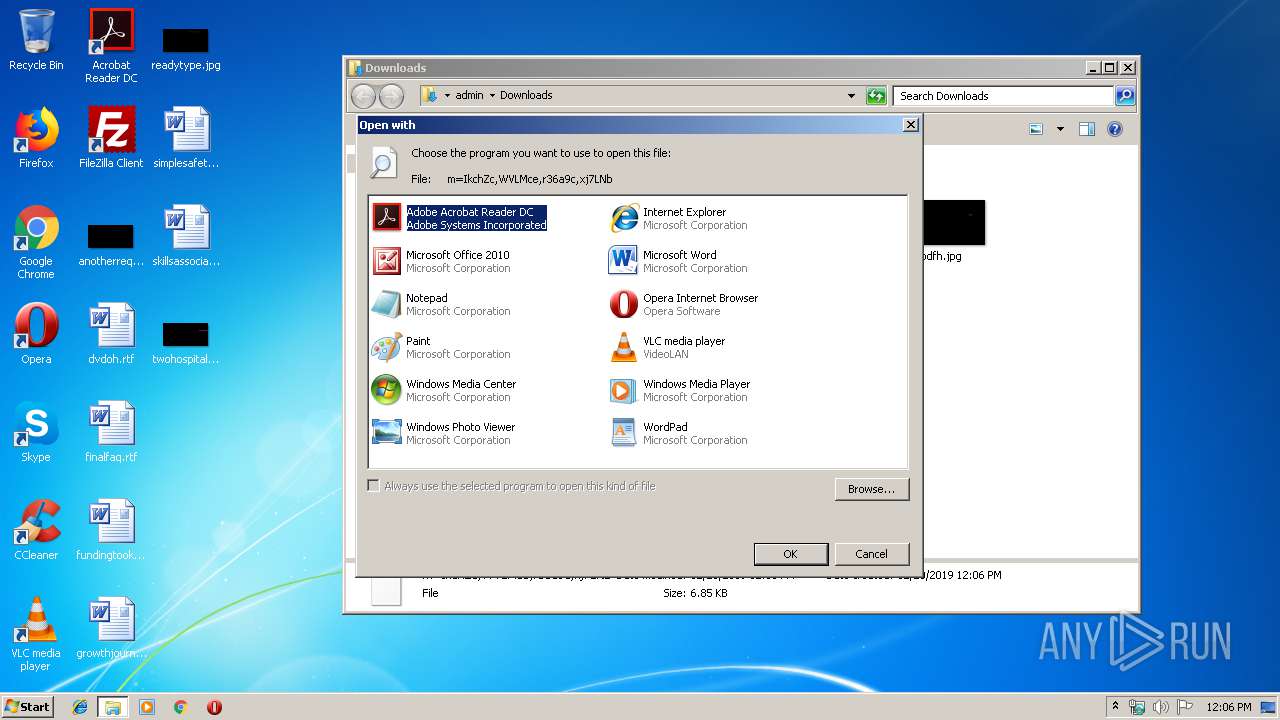
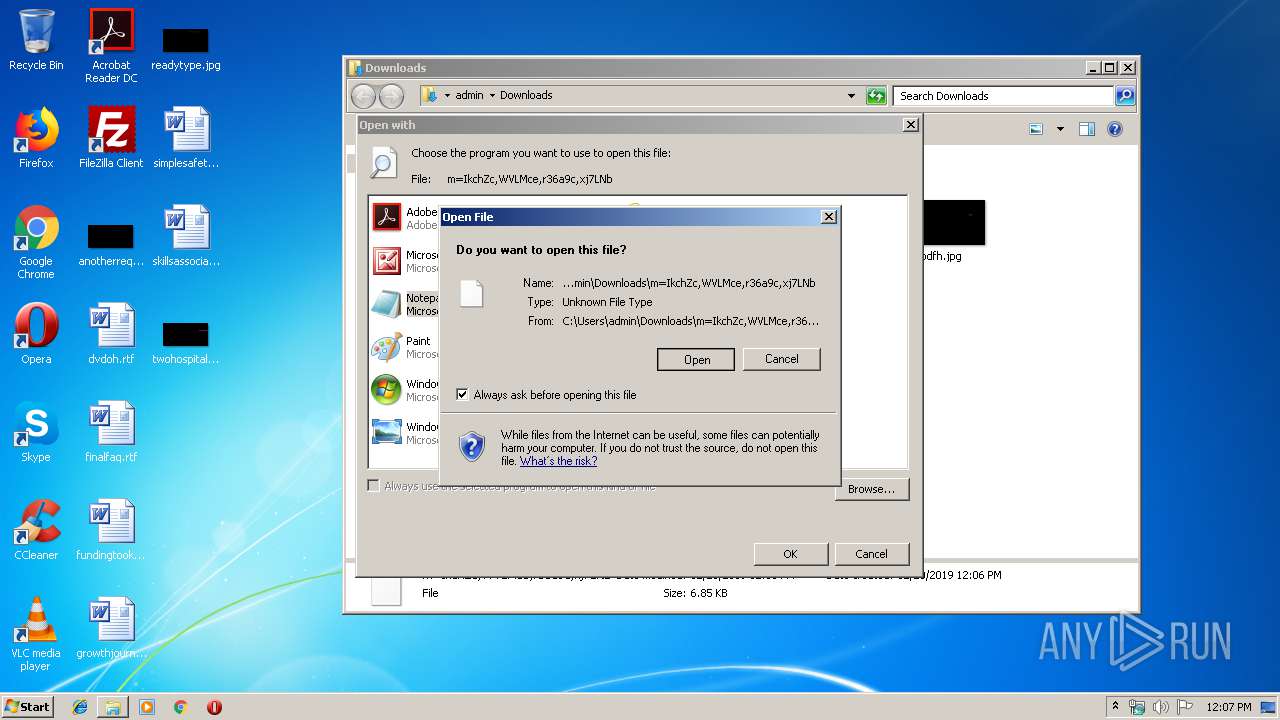
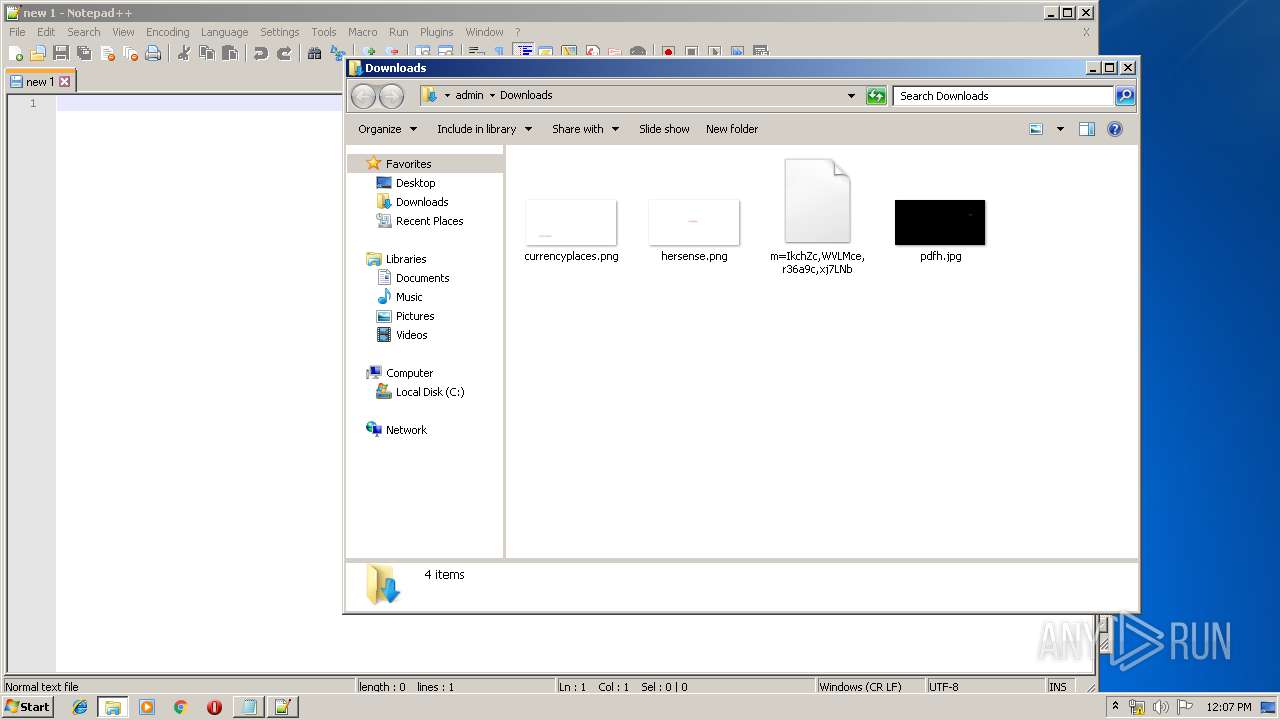
| 856 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\m=IkchZc,WVLMce,r36a9c,xj7LNb | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:748 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.google.com/xjs/_/js/k=xjs.s.en_GB.IfrOTSWH_to.O/ck=xjs.s.pDuUZZDMmVw.L.I11.O/am=AAAAgEUAMwAAIP8PBQAAQB0DAAABYcEGC4QhIcNYmIAAEA/d=1/exm=Fkg7bd,HcFEGb,IvlUe,MC8mtf,MkHyGd,OF7gzc,OG6ZHd,RMhBfe,SvnKM,T4BAC,T6sTsf,T7XTS,TJw5qb,TbaHGc,TxZWcc,URQPYc,WgDvvc,Wq6lxf,XMgU6d,XjCeUc,Y33vzc,ZyRBae,aCZVp,aa,aam1T,abd,aspn,async,bgd,cdos,cr,csi,d,dvl,eN4qad,ebqyud,foot,hsm,iDPoPb,jsa,kyn,lazG7b,lli,lu,m,mI3LFb,mUpTid,mpck,mu,mvYTse,o02Jie,pB6Zqd,qik19b,rHjpXd,sb_wiz,sf,tg8oTe,tl,uiNkee,uz938c,vWNDde,vs,wkrYee,ws9Tlc,xc1DSd,xz7cCd,yQ43ff,zbML3c/ed=1/dg=2/ct=zgms/rs=ACT90oHB8hpqHUGl7ek8w57bpeIMVTSo9g/m=IkchZc,WVLMce,r36a9c,xj7LNb?xjs=s2" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
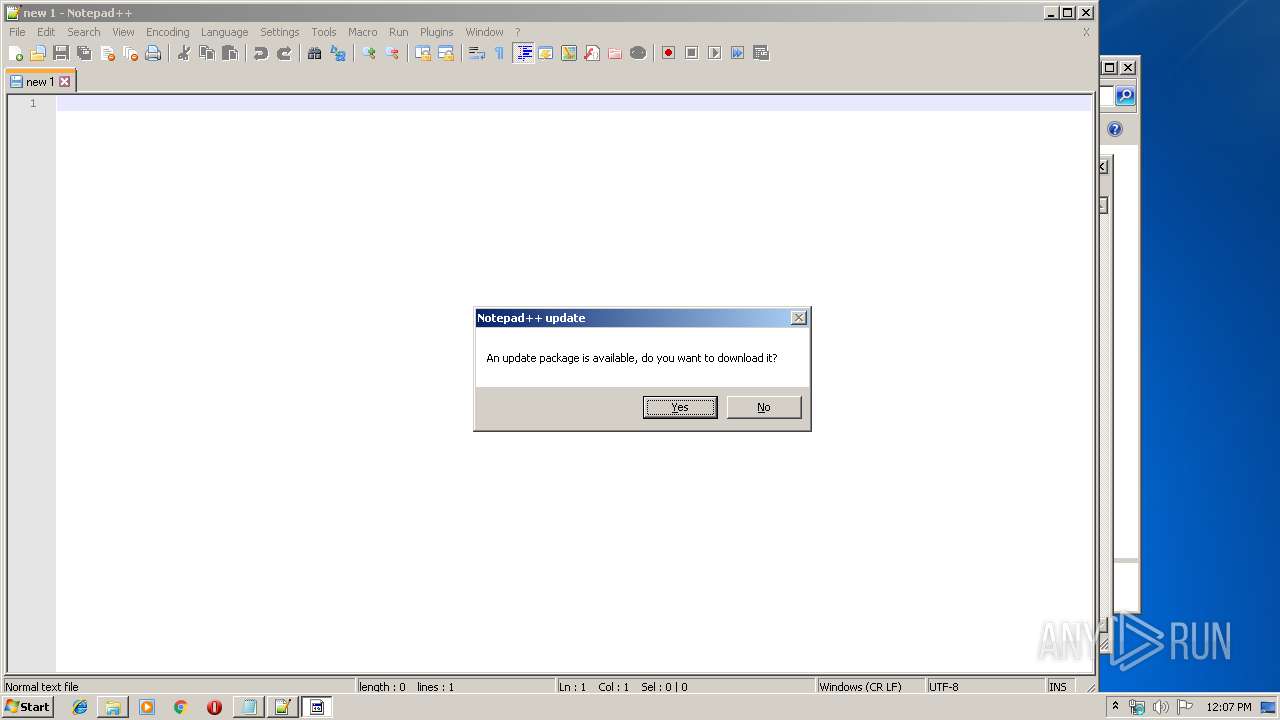
| 3084 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
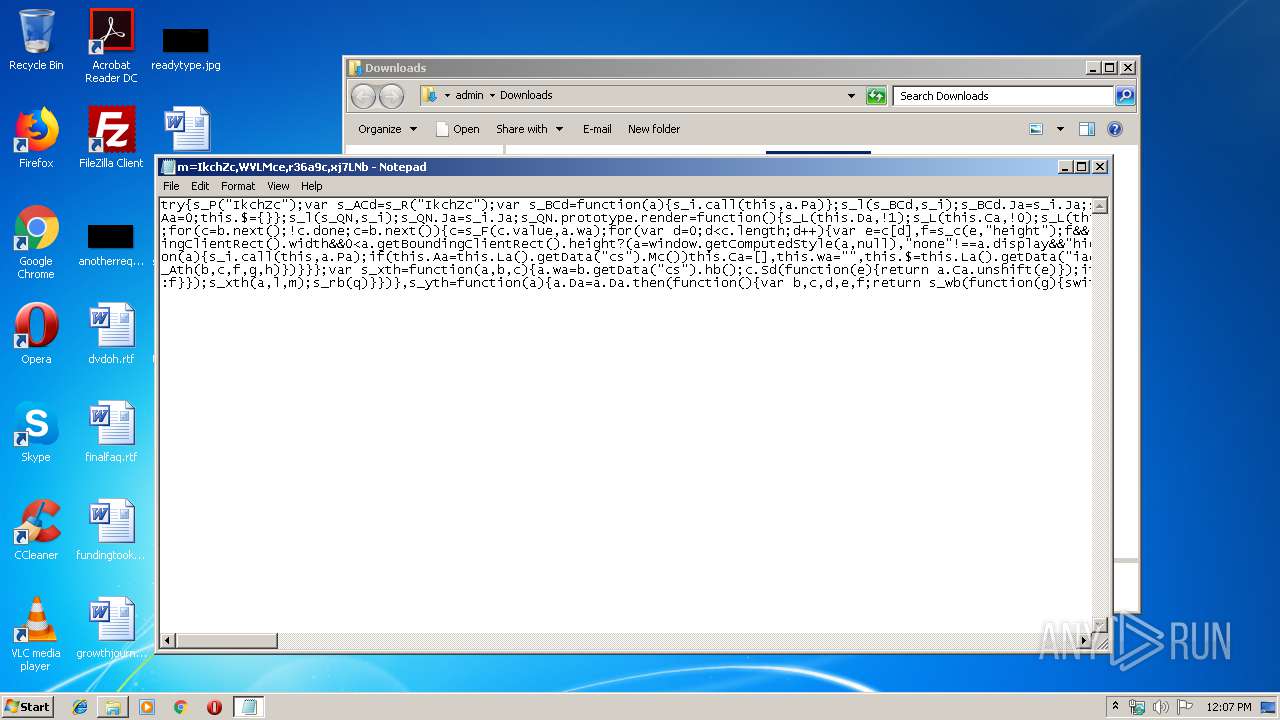
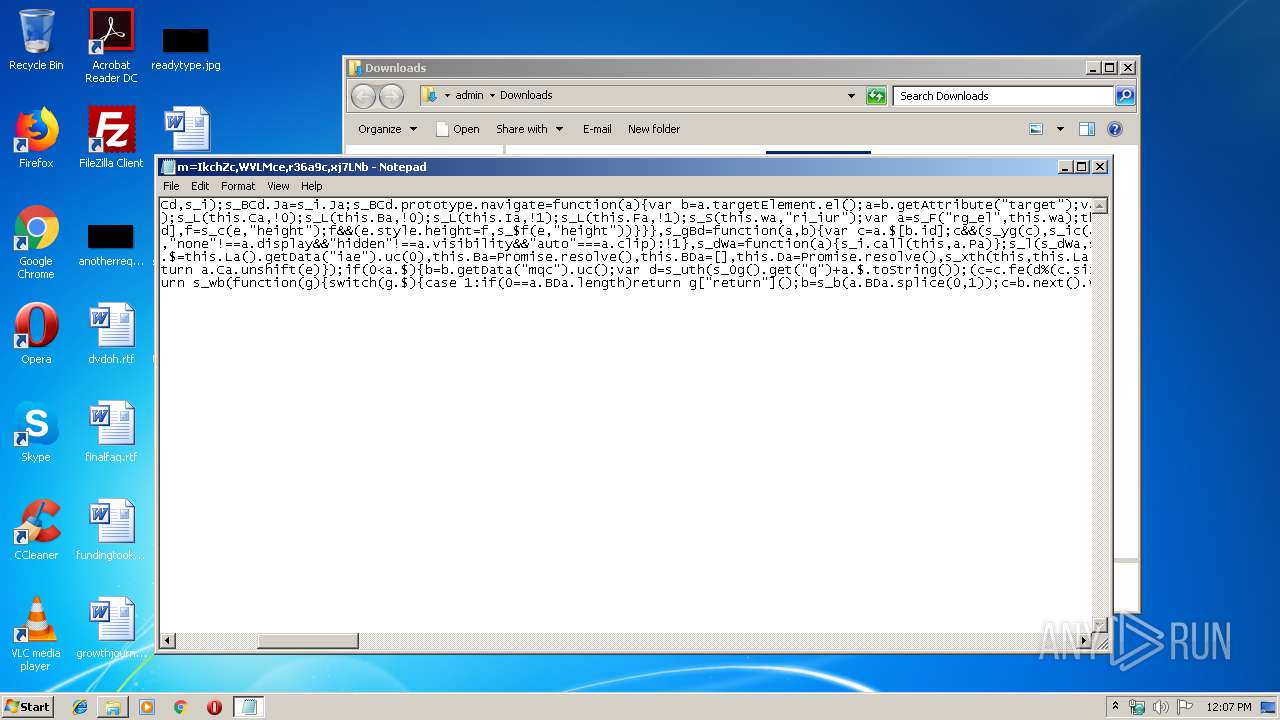
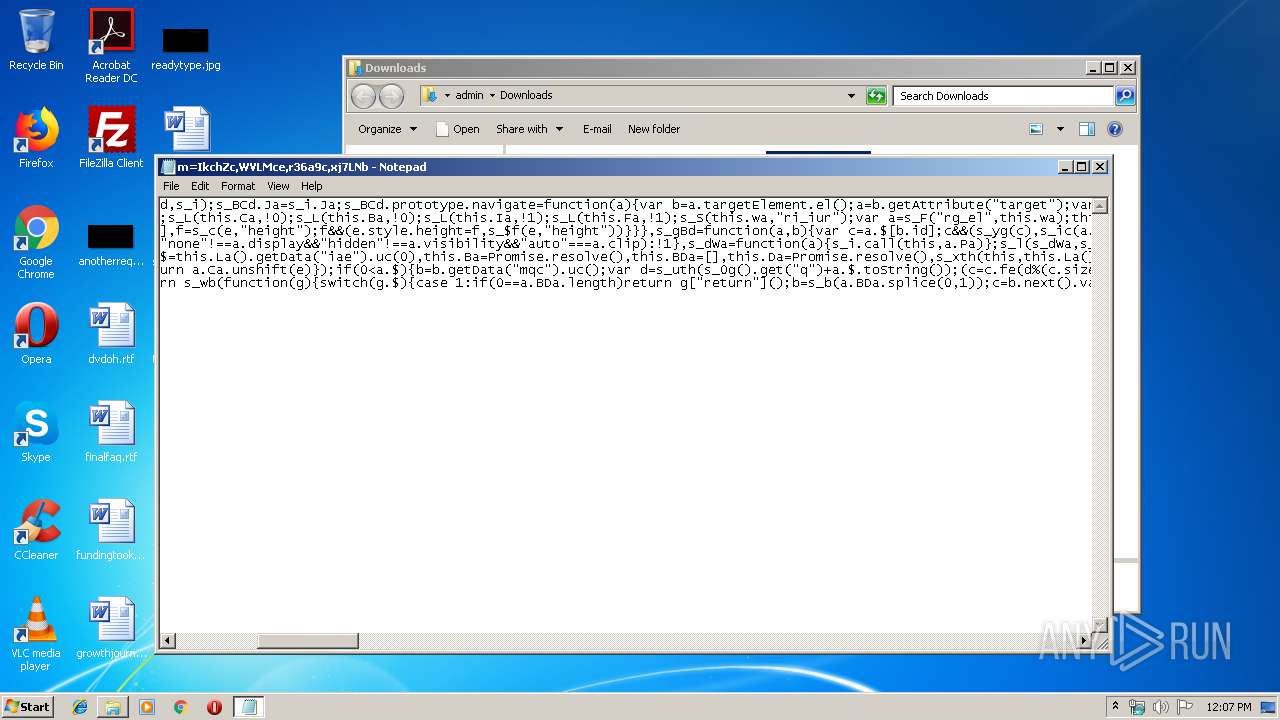
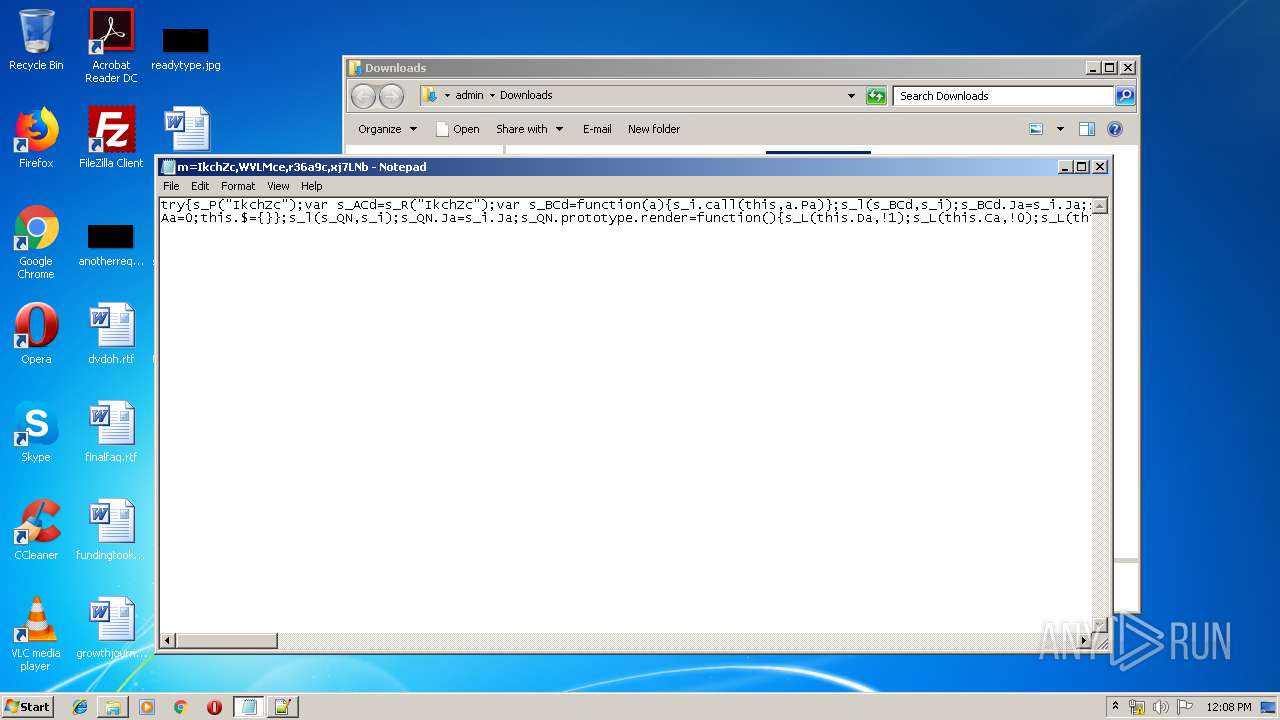
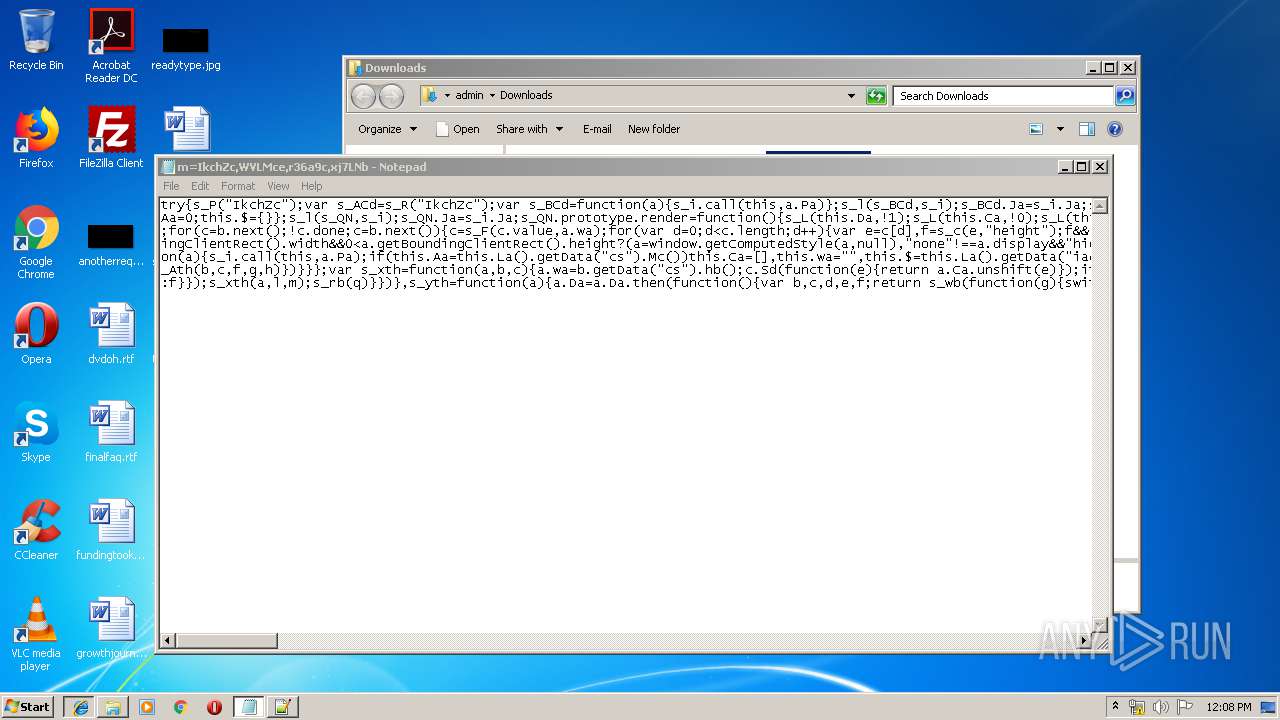
| 3928 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\m=IkchZc,WVLMce,r36a9c,xj7LNb | C:\Windows\system32\NOTEPAD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4088 | "C:\Program Files\Notepad++\notepad++.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
Total events
1 963
Read events
1 673
Write events
284
Delete events
6
Modification events
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {280D2C0D-2321-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C00050014000C0006001F003501 | |||
Executable files
0
Suspicious files
1
Text files
47
Unknown types
6
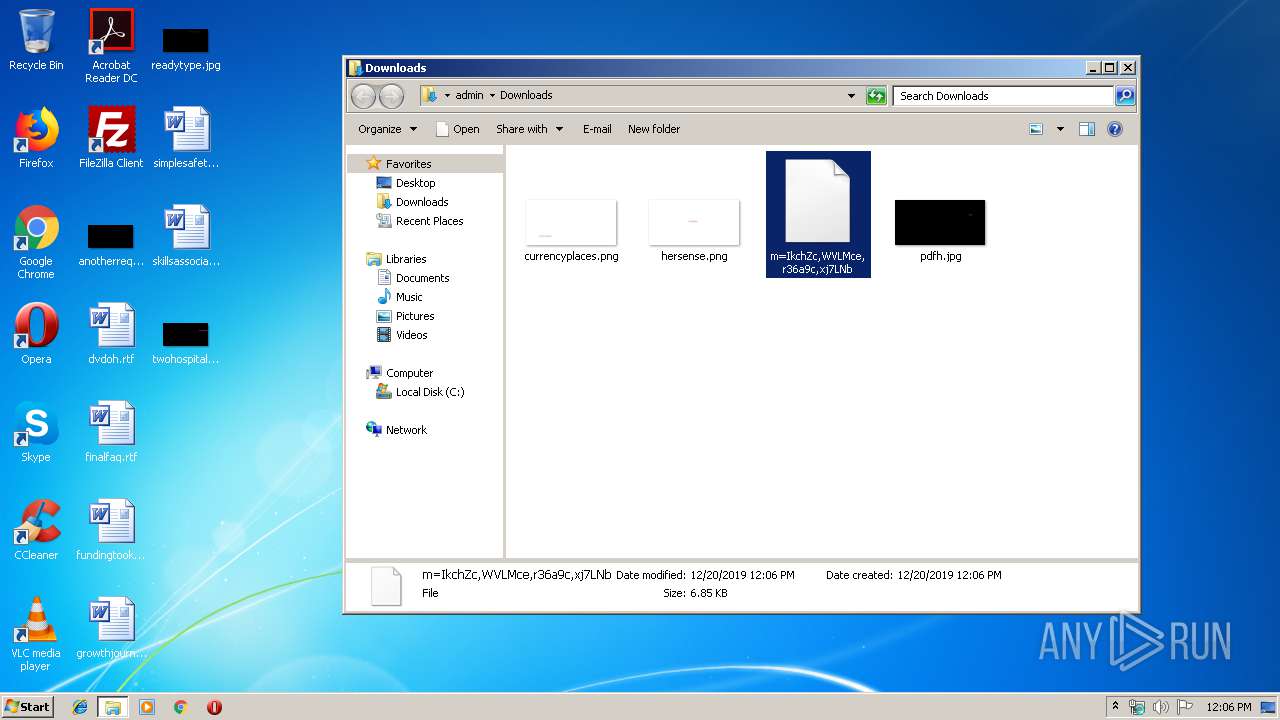
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3C2B4C6C0B355842.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF208903C04DBBB404.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{280D2C0D-2321-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{280D2C0E-2321-11EA-AB41-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AHDK4DRO\url[1].txt | — | |
MD5:— | SHA256:— | |||
| 2396 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019122020191221\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
15
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
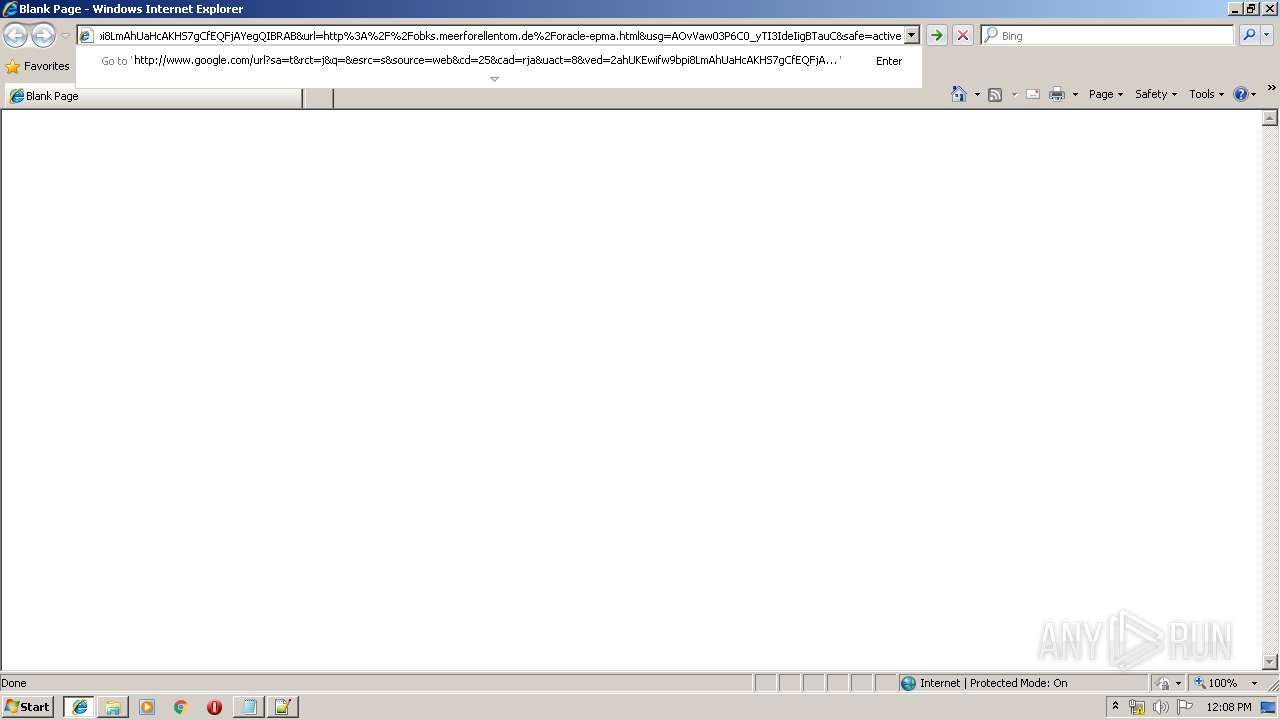
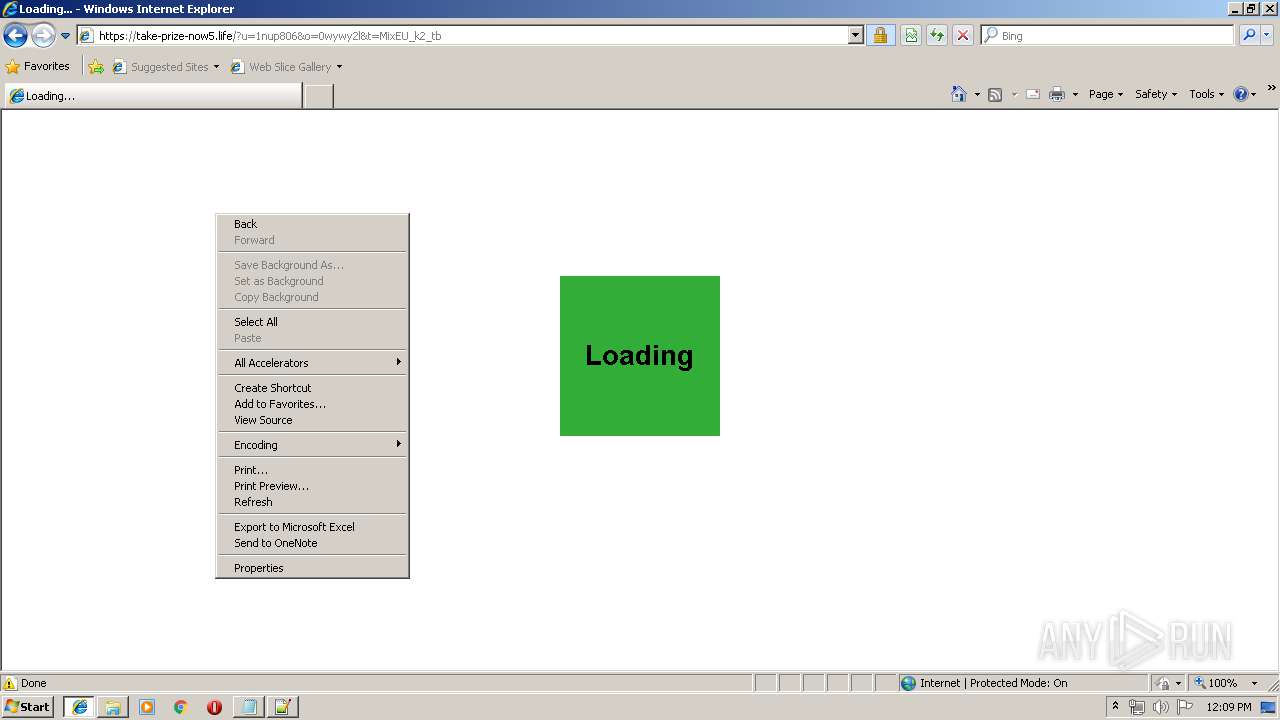
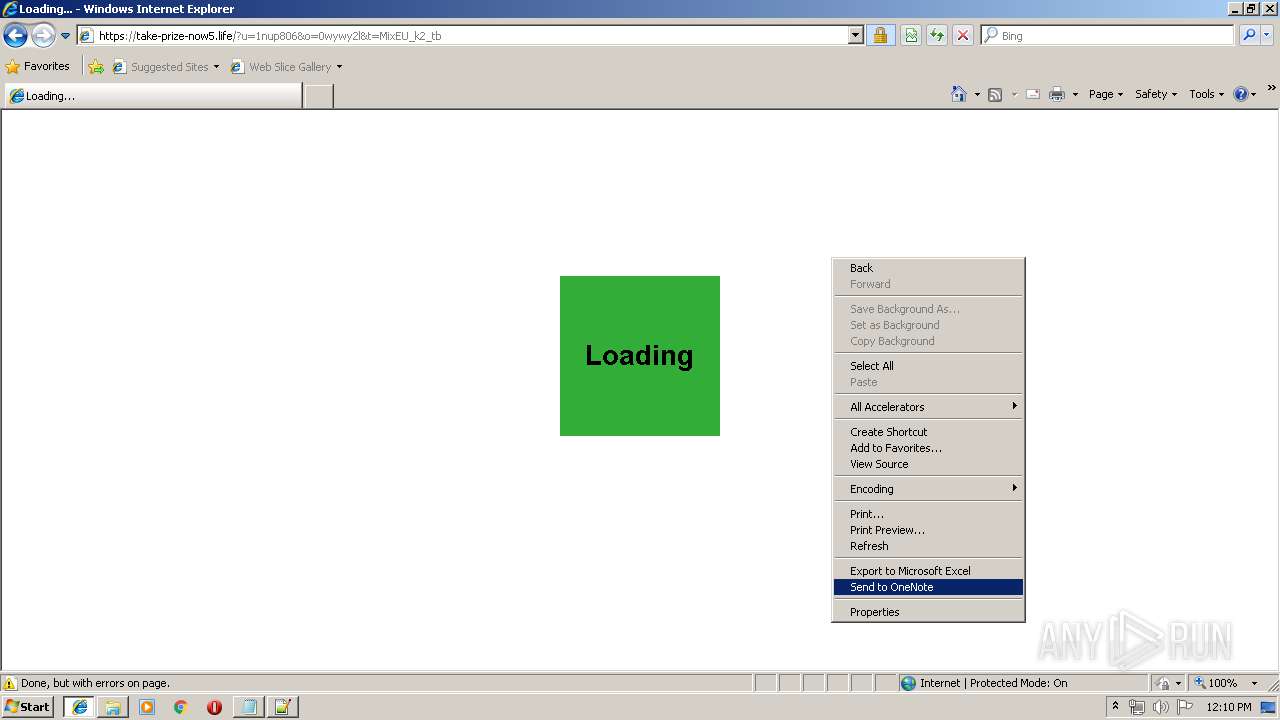
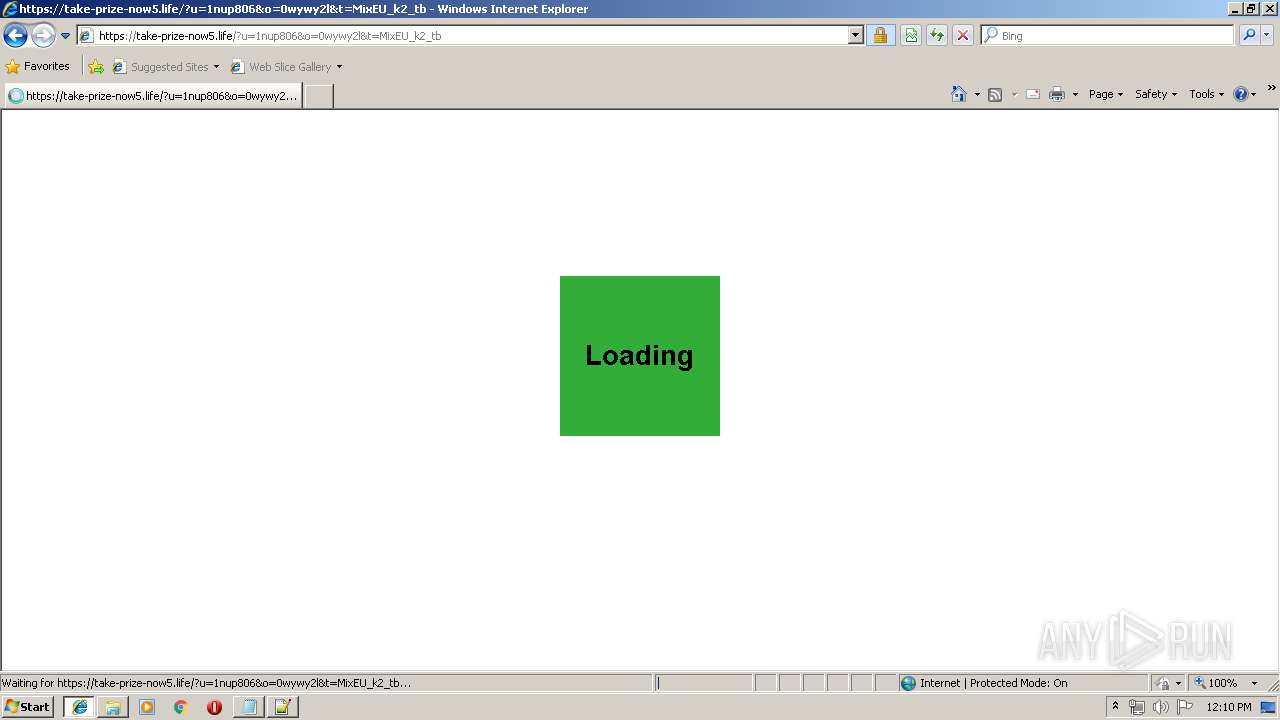
1764 | iexplore.exe | GET | 302 | 104.28.24.80:80 | http://obks.meerforellentom.de/oracle-epma.html | US | — | — | whitelisted |
1764 | iexplore.exe | GET | 302 | 176.114.9.149:8081 | http://176.114.9.149:8081/offer?sid=MixEU_k2&keys=oracle+epma&lan=en&redir=http%3A%2F%2F149.202.65.142%2FmxJV5f%3Fsub_id_1%3DMixEU_k2_tb | UA | — | — | suspicious |
1764 | iexplore.exe | GET | 302 | 149.202.65.142:80 | http://149.202.65.142/mxJV5f?sub_id_1=MixEU_k2_tb | FR | — | — | unknown |
1764 | iexplore.exe | GET | 301 | 136.244.101.20:80 | http://take-prize-now5.life/?u=1nup806&o=0wywy2l&t=MixEU_k2_tb | US | html | 178 b | suspicious |
2516 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1764 | iexplore.exe | GET | 200 | 172.217.21.228:80 | http://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=25&cad=rja&uact=8&ved=2ahUKEwifw9bpi8LmAhUaHcAKHS7gCfEQFjAYegQIBRAB&url=http%3A%2F%2Fobks.meerforellentom.de%2Foracle-epma.html&usg=AOvVaw03P6C0_yTI3IdeIigBTauC&safe=active | US | html | 586 b | malicious |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAxHWpoyfQpCuYL7zNoKQA4%3D | US | der | 280 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2396 | iexplore.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
2516 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3084 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1764 | iexplore.exe | 172.217.21.228:80 | www.google.com | Google Inc. | US | whitelisted |
1764 | iexplore.exe | 104.28.24.80:80 | obks.meerforellentom.de | Cloudflare Inc | US | unknown |
1764 | iexplore.exe | 176.114.9.149:8081 | — | FOP Sedinkin Olexandr Valeriyovuch | UA | suspicious |
1764 | iexplore.exe | 149.202.65.142:80 | — | OVH SAS | FR | unknown |
1764 | iexplore.exe | 136.244.101.20:80 | take-prize-now5.life | Connecticut College | US | suspicious |
1764 | iexplore.exe | 136.244.101.20:443 | take-prize-now5.life | Connecticut College | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
www.bing.com |
| whitelisted |
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
obks.meerforellentom.de |
| unknown |
take-prize-now5.life |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1764 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|