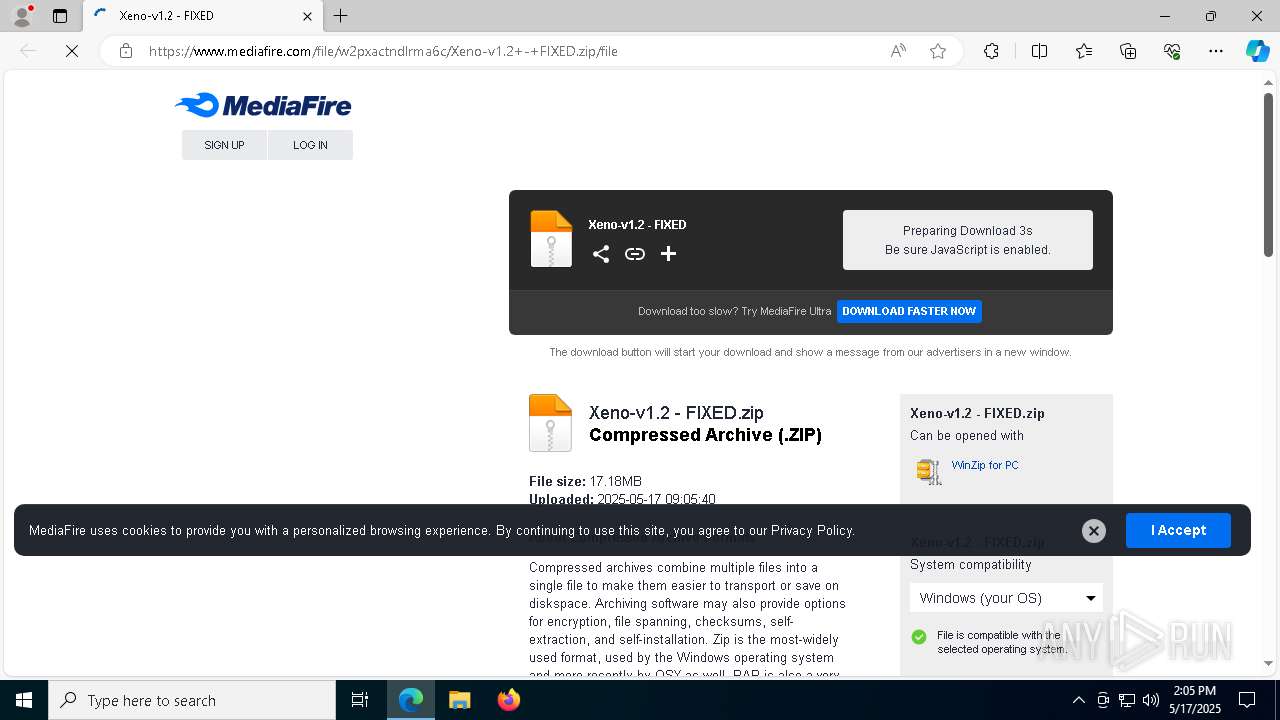
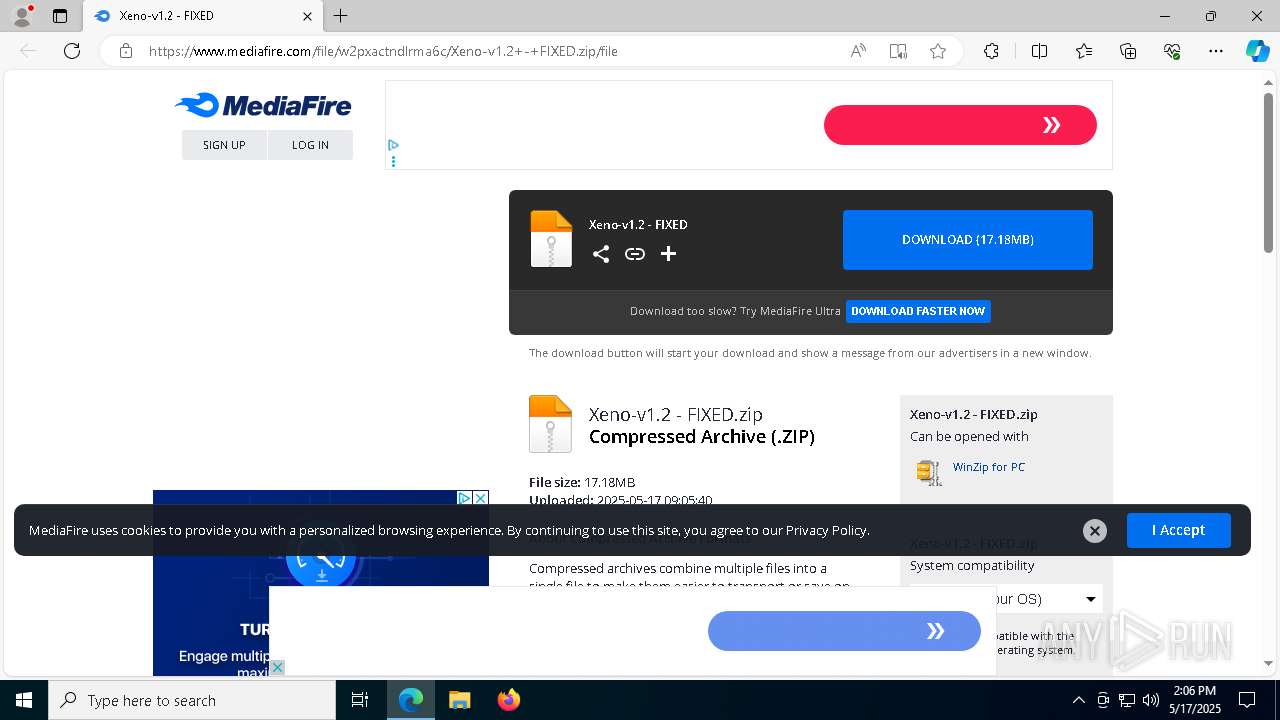
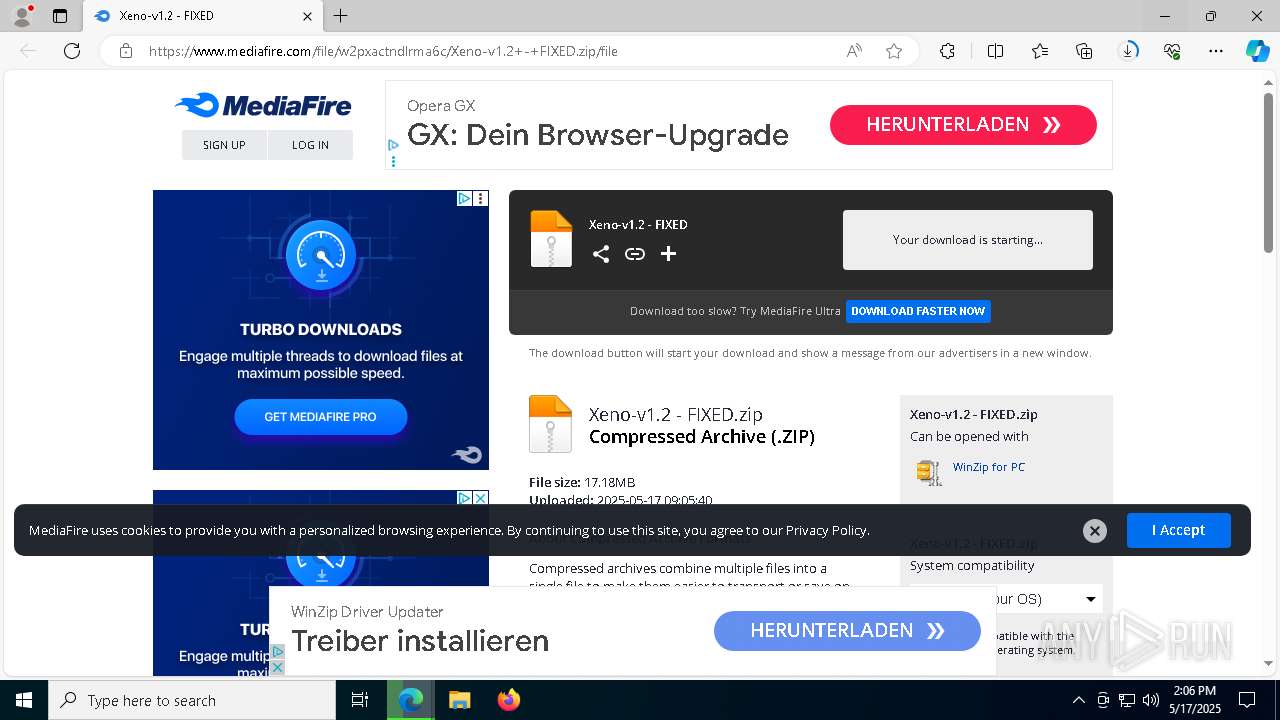
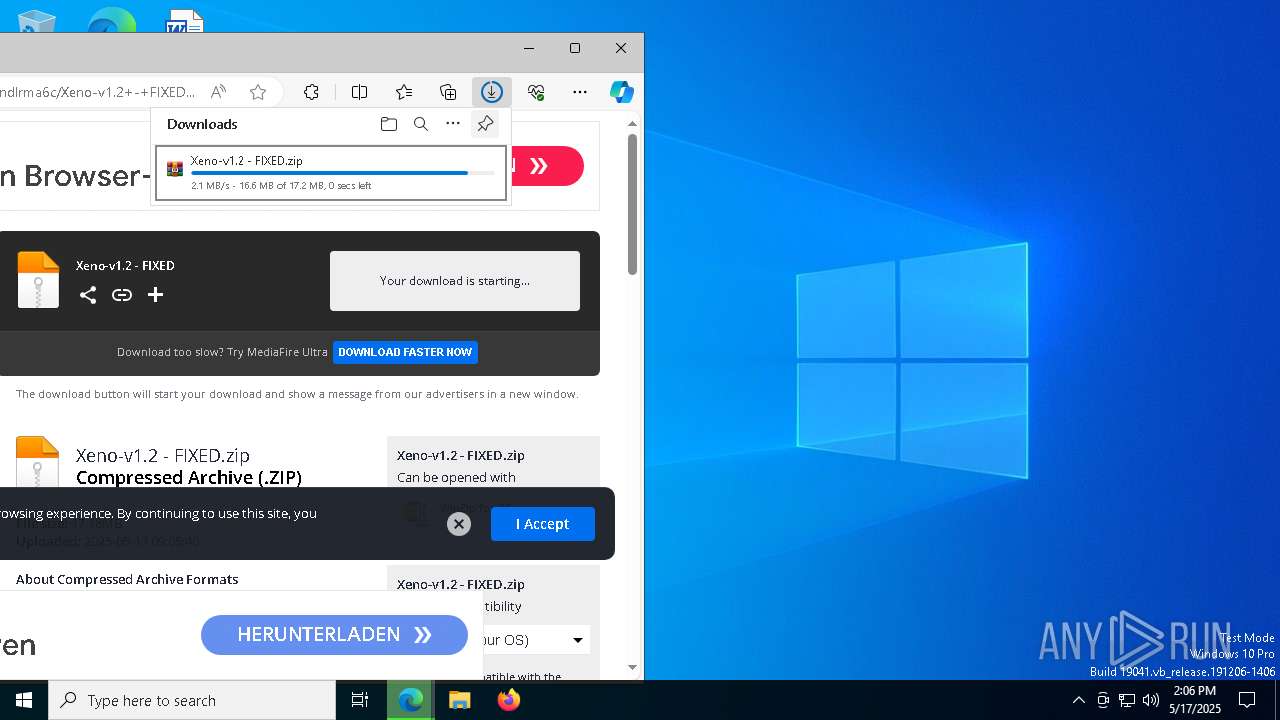
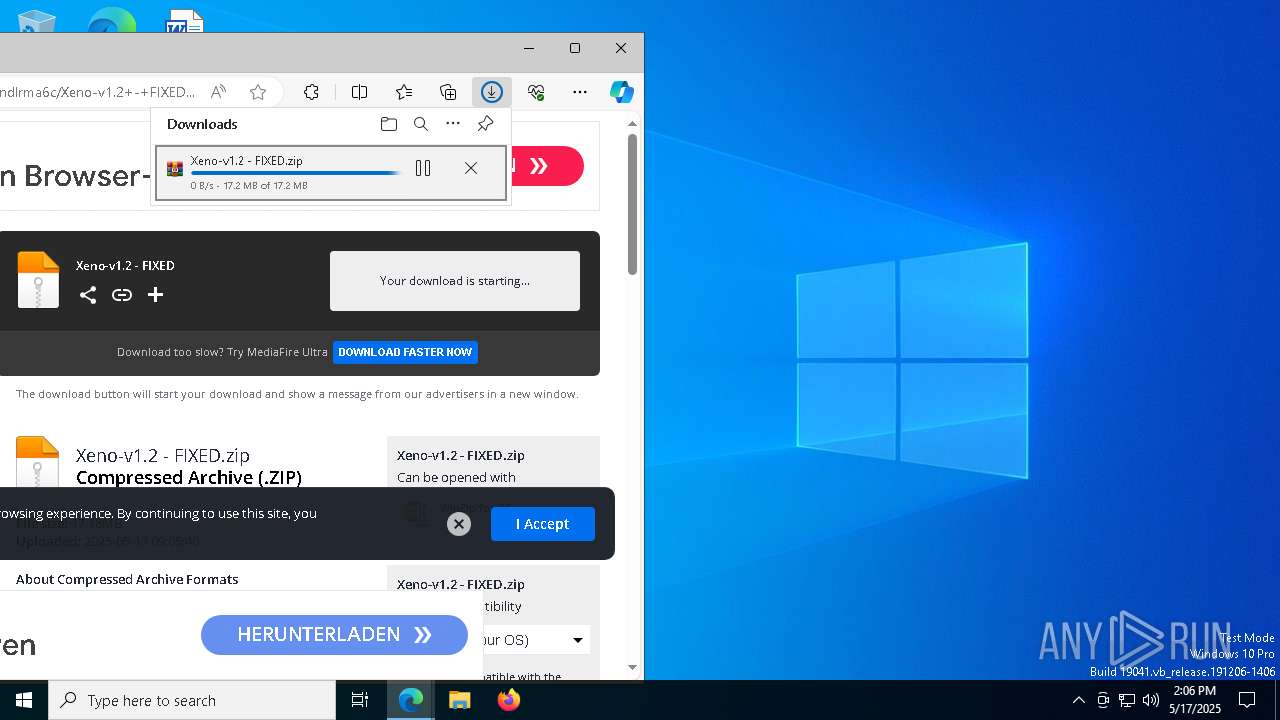
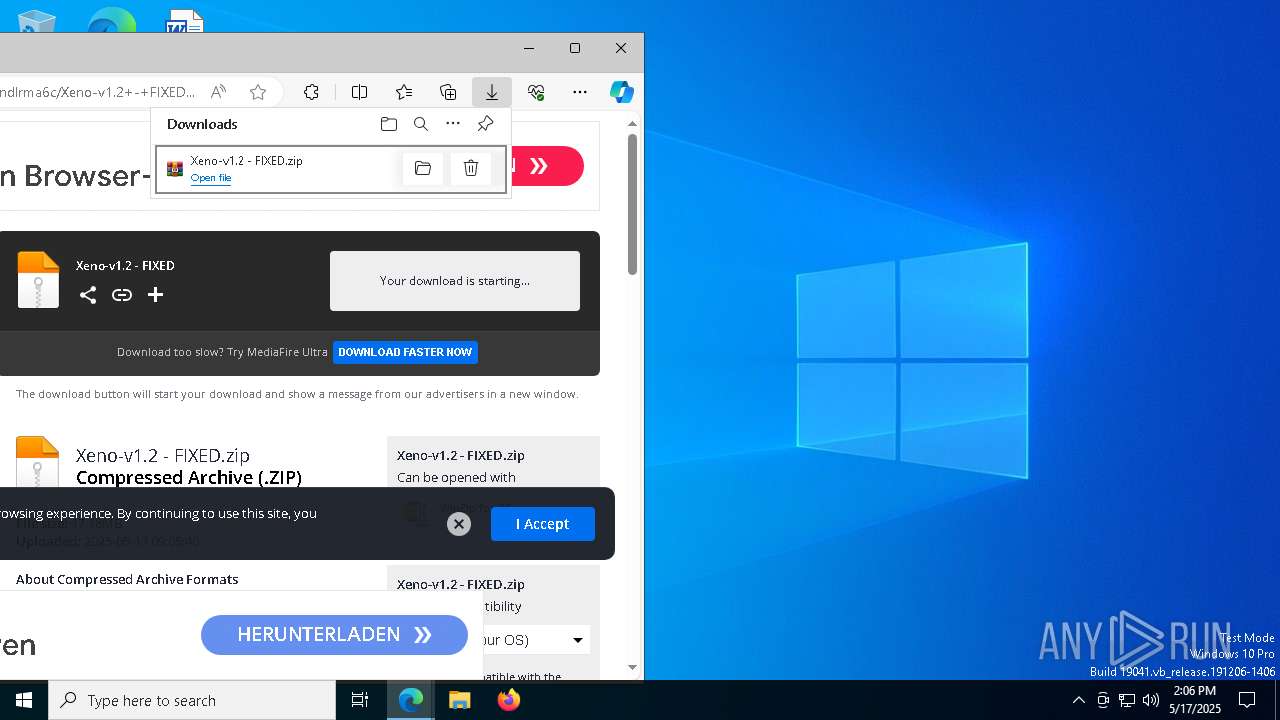
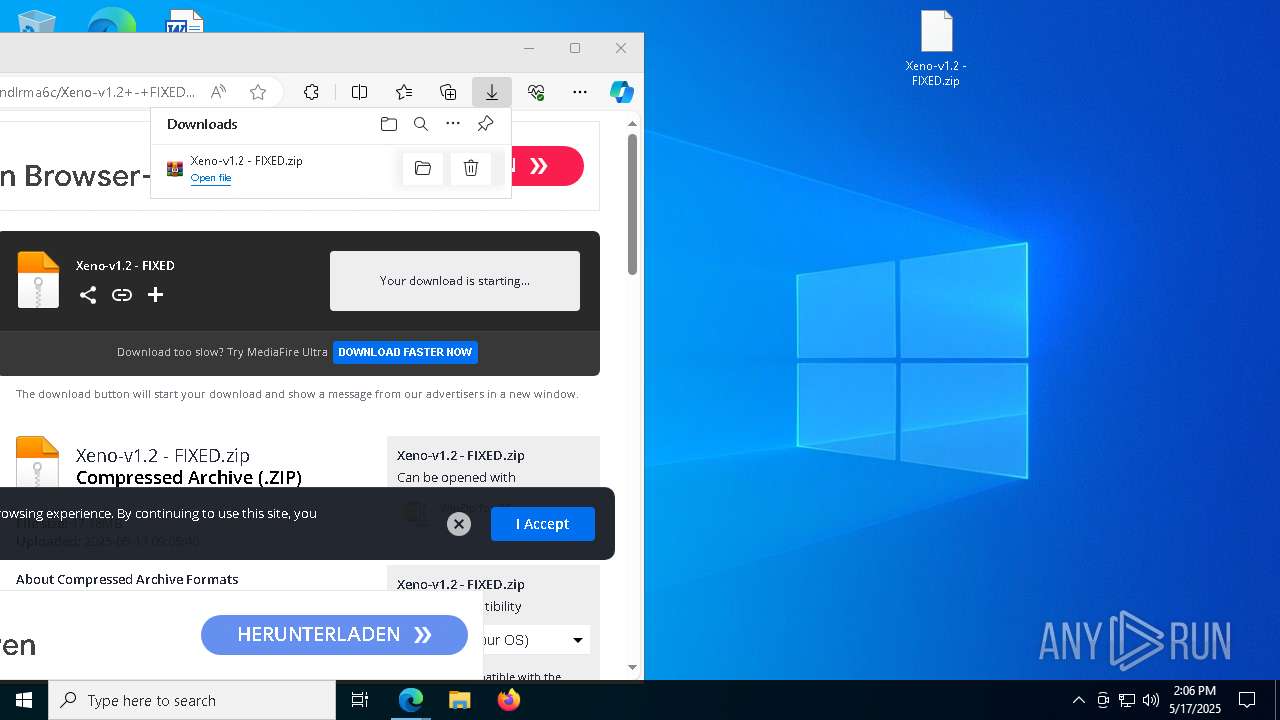
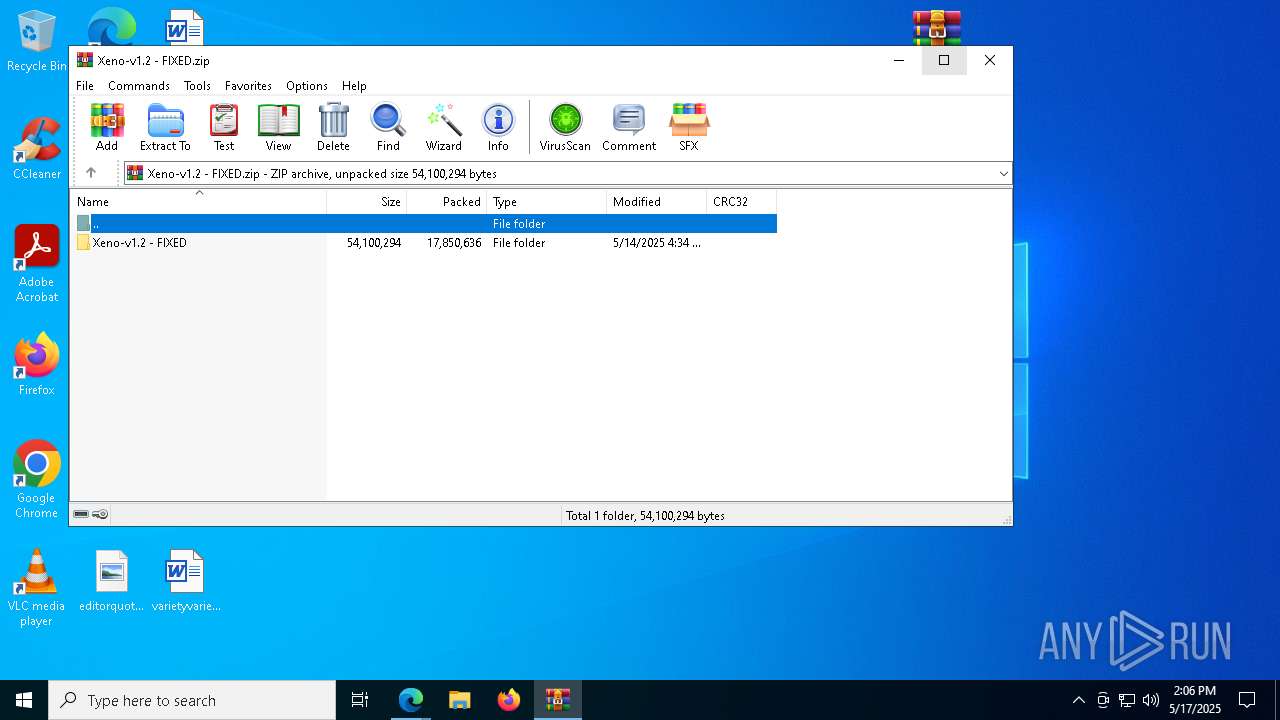
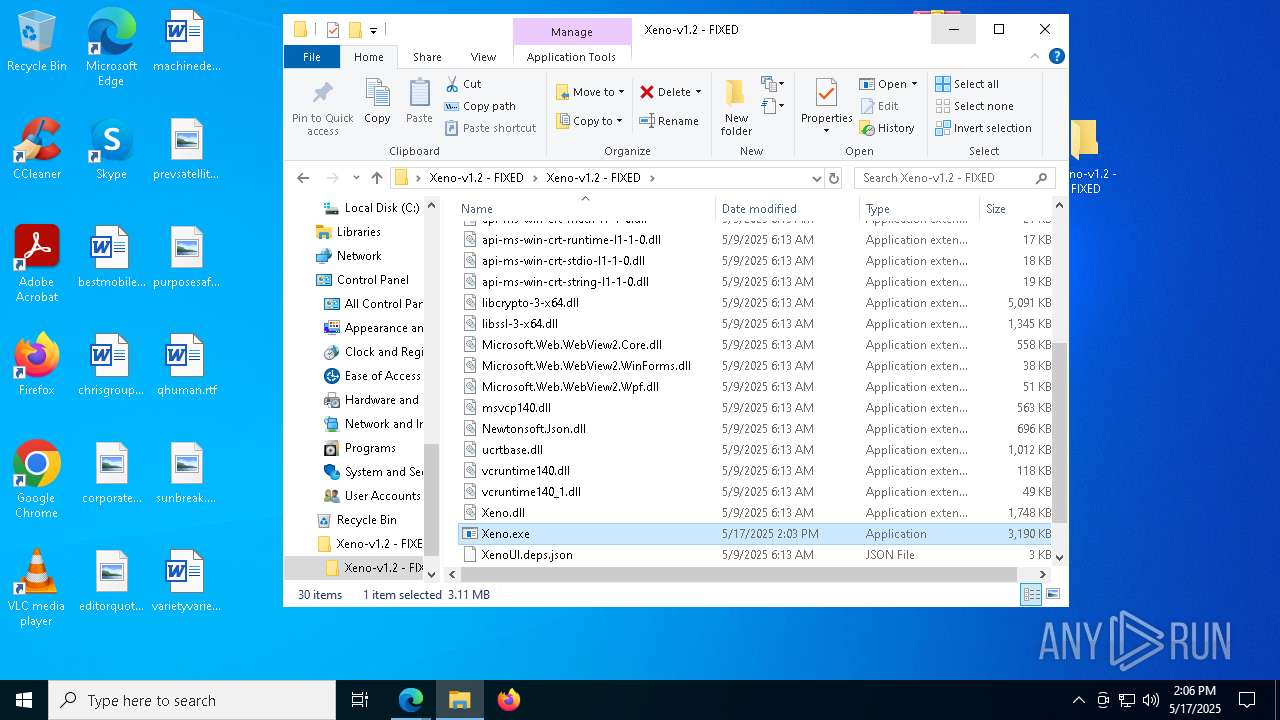
| URL: | https://www.mediafire.com/file/w2pxactndlrma6c/Xeno-v1.2+-+FIXED.zip/file |
| Full analysis: | https://app.any.run/tasks/8f6bcda2-b832-4b72-a44b-6ae7d56fad41 |
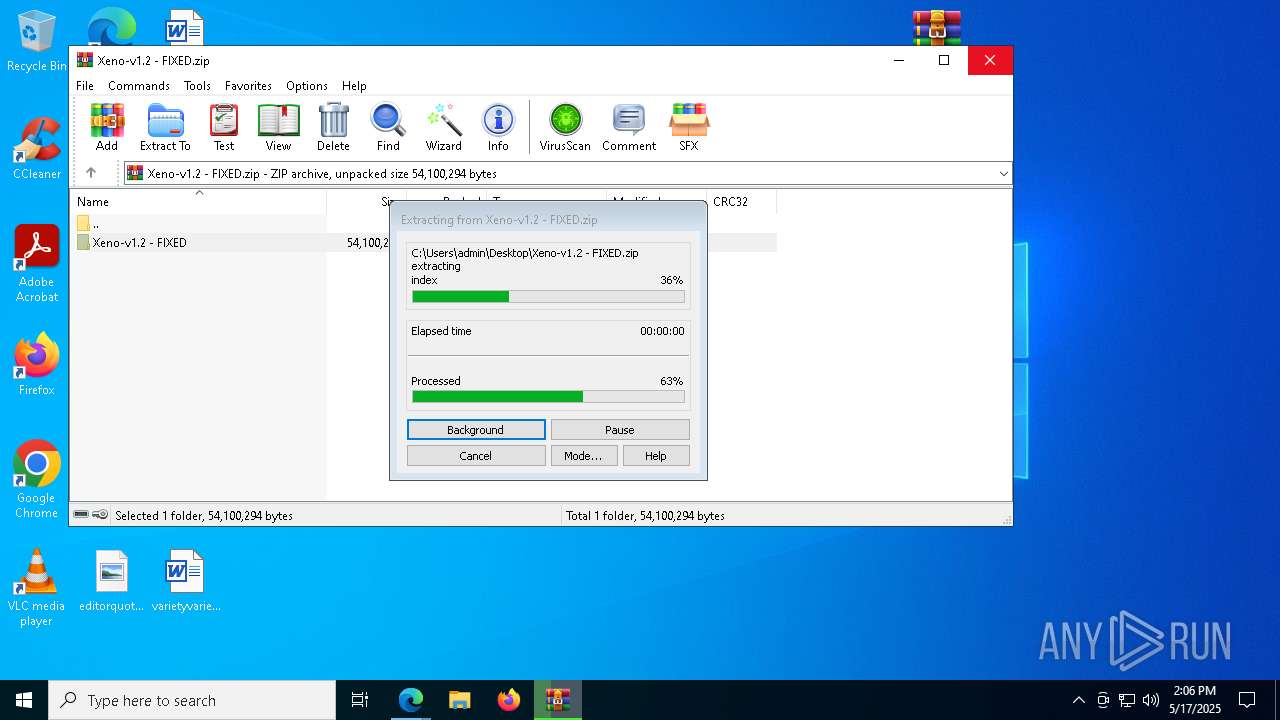
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 14:05:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6C3534C7B791FF27927E2551A7B872A4 |
| SHA1: | 4EB62AAF99C86AE84ACD76C26B7BF1C0B076BBED |
| SHA256: | C723ED0A5F89091DD1D0D07A36BDC290D77BE06880964DAB7DF0D08EA9D9EABC |
| SSDEEP: | 3:N8DSLw3eGUokZ1V9FbLXtiYVo:2OLw3eGwZ1VrjMYy |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 8912)
Starts application with an unusual extension
- cmd.exe (PID: 8744)
- cmd.exe (PID: 8776)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 9180)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 4488)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8484)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 924)
- cmd.exe (PID: 7636)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 6892)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8840)
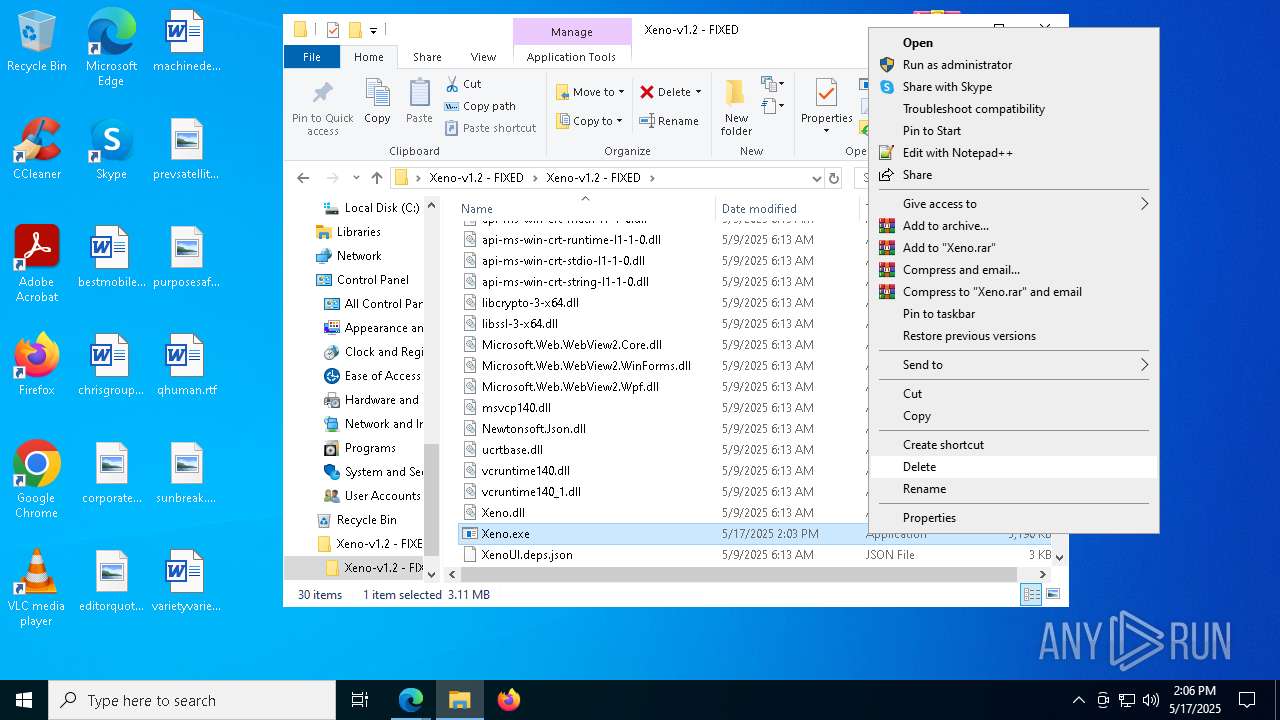
Starts itself from another location
- Xeno.exe (PID: 9208)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 8744)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 9180)
- cmd.exe (PID: 8776)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 4488)
- cmd.exe (PID: 8484)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 924)
- cmd.exe (PID: 7636)
- cmd.exe (PID: 6892)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 7956)
Executable content was dropped or overwritten
- Xeno.exe (PID: 9208)
Starts CMD.EXE for commands execution
- XenoUI.exe (PID: 8948)
- XenoUI.exe (PID: 8936)
- XenoUI.exe (PID: 8232)
- XenoUI.exe (PID: 4424)
- XenoUI.exe (PID: 3032)
- XenoUI.exe (PID: 8812)
- XenoUI.exe (PID: 7992)
- XenoUI.exe (PID: 1804)
- XenoUI.exe (PID: 7972)
- XenoUI.exe (PID: 8408)
- XenoUI.exe (PID: 5740)
- XenoUI.exe (PID: 8492)
- XenoUI.exe (PID: 9100)
- XenoUI.exe (PID: 3124)
- XenoUI.exe (PID: 2564)
- XenoUI.exe (PID: 4424)
- XenoUI.exe (PID: 7844)
- XenoUI.exe (PID: 8180)
- XenoUI.exe (PID: 8956)
- XenoUI.exe (PID: 8764)
- XenoUI.exe (PID: 4736)
Executing commands from a ".bat" file
- XenoUI.exe (PID: 8936)
- XenoUI.exe (PID: 8948)
- XenoUI.exe (PID: 4424)
- XenoUI.exe (PID: 3032)
- XenoUI.exe (PID: 5740)
- XenoUI.exe (PID: 8812)
- XenoUI.exe (PID: 8232)
- XenoUI.exe (PID: 7992)
- XenoUI.exe (PID: 1804)
- XenoUI.exe (PID: 7972)
- XenoUI.exe (PID: 8492)
- XenoUI.exe (PID: 9100)
- XenoUI.exe (PID: 3124)
- XenoUI.exe (PID: 2564)
- XenoUI.exe (PID: 4424)
- XenoUI.exe (PID: 7844)
- XenoUI.exe (PID: 8180)
- XenoUI.exe (PID: 8764)
- XenoUI.exe (PID: 8956)
- XenoUI.exe (PID: 4736)
- XenoUI.exe (PID: 8408)
The executable file from the user directory is run by the CMD process
- XenoUI.exe (PID: 8948)
- XenoUI.exe (PID: 8232)
- XenoUI.exe (PID: 4424)
- XenoUI.exe (PID: 3032)
- XenoUI.exe (PID: 5740)
- XenoUI.exe (PID: 7992)
- XenoUI.exe (PID: 1804)
- XenoUI.exe (PID: 7972)
- XenoUI.exe (PID: 8408)
- XenoUI.exe (PID: 8812)
- XenoUI.exe (PID: 8492)
- XenoUI.exe (PID: 9100)
- XenoUI.exe (PID: 2564)
- XenoUI.exe (PID: 3124)
- XenoUI.exe (PID: 7844)
- XenoUI.exe (PID: 4424)
- XenoUI.exe (PID: 8180)
- XenoUI.exe (PID: 8956)
- XenoUI.exe (PID: 8764)
- XenoUI.exe (PID: 4736)
INFO
Reads Environment values
- identity_helper.exe (PID: 8772)
Checks supported languages
- identity_helper.exe (PID: 8772)
Changes the display of characters in the console
- cmd.exe (PID: 8744)
- cmd.exe (PID: 8776)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 9180)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 4488)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8484)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 924)
- cmd.exe (PID: 7636)
- cmd.exe (PID: 6892)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8840)
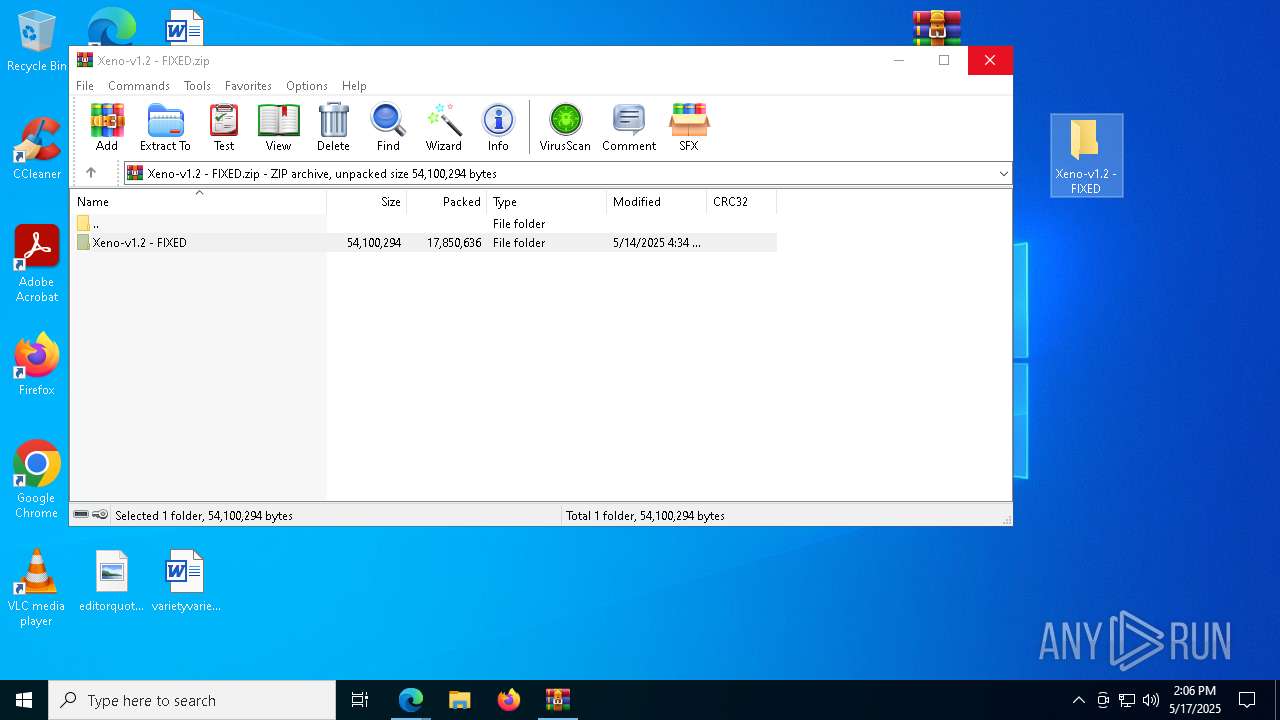
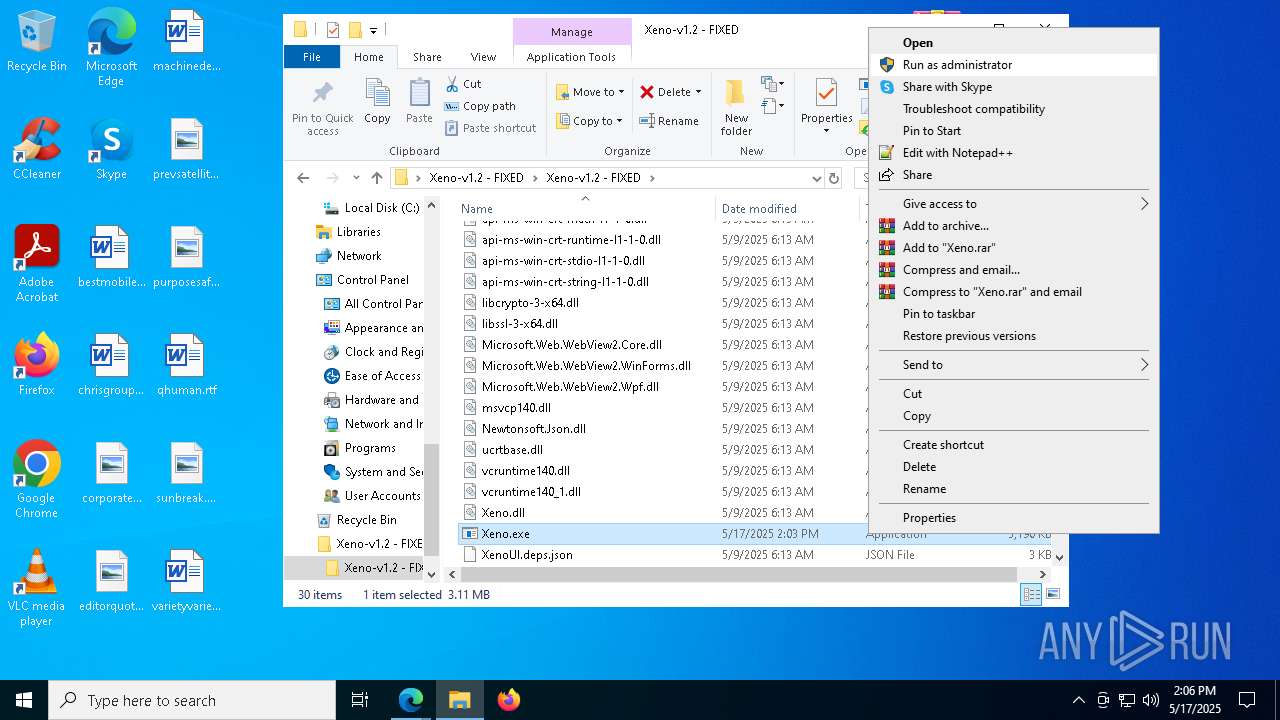
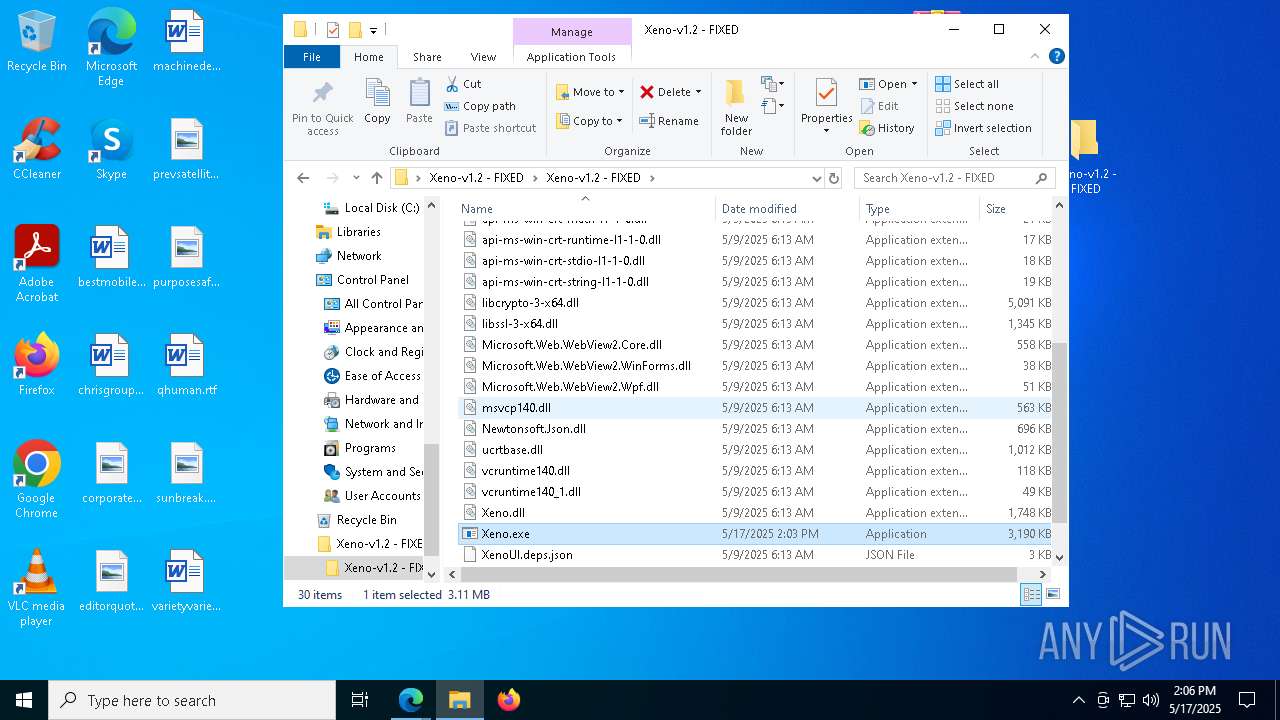
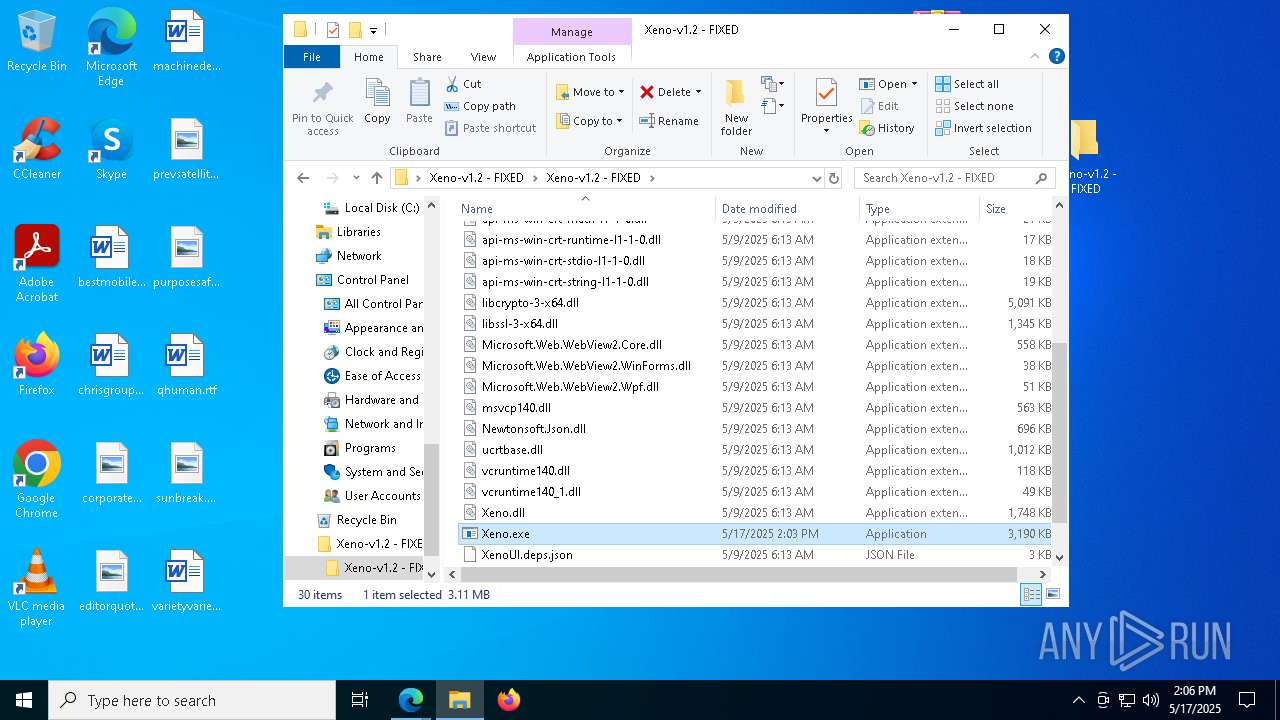
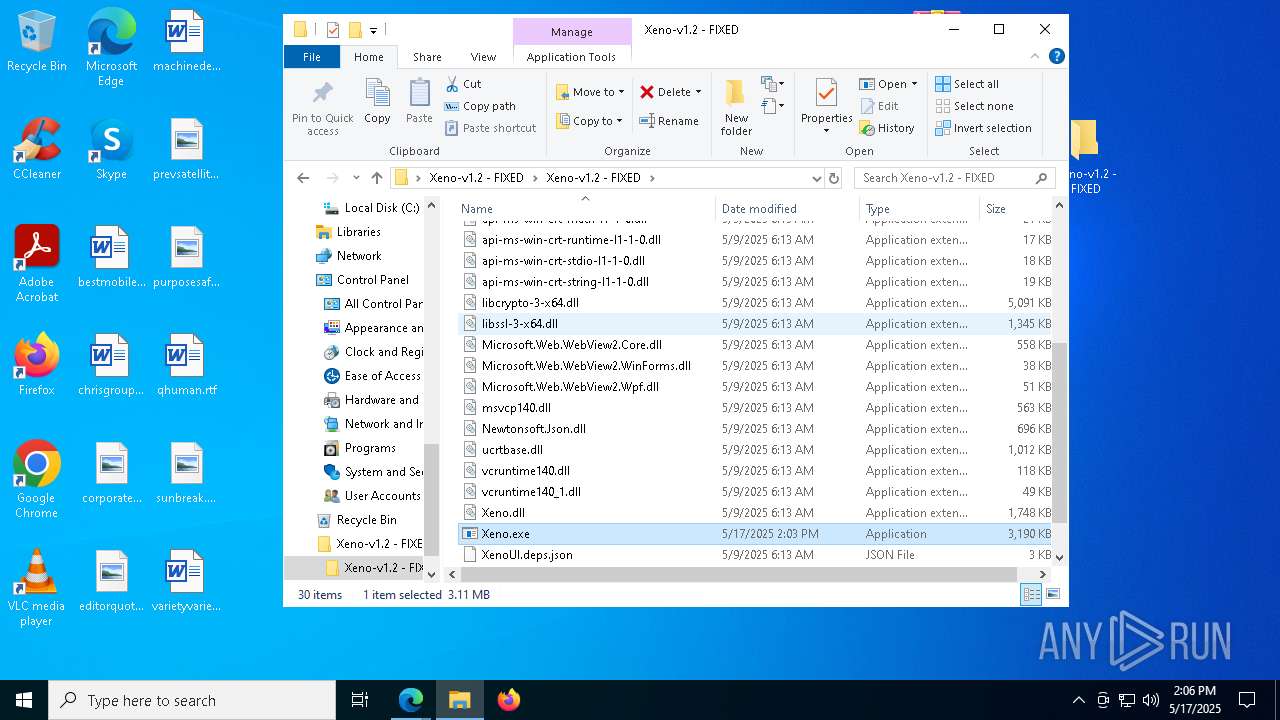
Manual execution by a user
- Xeno.exe (PID: 9208)
- Xeno.exe (PID: 3332)
- WinRAR.exe (PID: 8912)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8912)
- msedge.exe (PID: 632)
The sample compiled with english language support
- WinRAR.exe (PID: 8912)
- msedge.exe (PID: 632)
Reads the computer name
- identity_helper.exe (PID: 8772)
Application launched itself
- msedge.exe (PID: 7012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
316
Monitored processes
178
Malicious processes
1
Suspicious processes
33
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4192 --field-trial-handle=2624,i,9072863936877930558,10717981874086910347,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6088 --field-trial-handle=2624,i,9072863936877930558,10717981874086910347,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\7EucIE6AQkkJ.bat" " | C:\Windows\System32\cmd.exe | — | XenoUI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 446
Read events
31 380
Write events
66
Delete events
0
Modification events
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 29324AAEEB932F00 | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 807454AEEB932F00 | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {73D5C73B-2FCA-4ABD-8DE6-F88460148AF0} | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AAE2CED4-FE3B-47D5-98E5-46ACE8FEF5B2} | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {41A8E4AE-672B-494D-A3AF-4F7CE731527B} | |||
| (PID) Process: | (7012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CD460FEE-2C7A-4F50-969C-C9BFC24215E8} | |||
Executable files
54
Suspicious files
563
Text files
167
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b4fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b538.TMP | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b558.TMP | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b558.TMP | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b567.TMP | — | |
MD5:— | SHA256:— | |||
| 7012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
289
DNS requests
318
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.15:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
920 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8652 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747704462&P2=404&P3=2&P4=jn6fQk9%2fBghXh2zZckf591cN%2fRi%2f4sC%2bPBRgAwBlGRcZ2Dsz8lraT2H%2fUMfPZd53%2fTQPmFUzeMng01ZJEukm0A%3d%3d | unknown | — | — | whitelisted |
8652 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747704462&P2=404&P3=2&P4=jn6fQk9%2fBghXh2zZckf591cN%2fRi%2f4sC%2bPBRgAwBlGRcZ2Dsz8lraT2H%2fUMfPZd53%2fTQPmFUzeMng01ZJEukm0A%3d%3d | unknown | — | — | whitelisted |
8652 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747704462&P2=404&P3=2&P4=jn6fQk9%2fBghXh2zZckf591cN%2fRi%2f4sC%2bPBRgAwBlGRcZ2Dsz8lraT2H%2fUMfPZd53%2fTQPmFUzeMng01ZJEukm0A%3d%3d | unknown | — | — | whitelisted |
8652 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747704462&P2=404&P3=2&P4=jn6fQk9%2fBghXh2zZckf591cN%2fRi%2f4sC%2bPBRgAwBlGRcZ2Dsz8lraT2H%2fUMfPZd53%2fTQPmFUzeMng01ZJEukm0A%3d%3d | unknown | — | — | whitelisted |
8652 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747704462&P2=404&P3=2&P4=jn6fQk9%2fBghXh2zZckf591cN%2fRi%2f4sC%2bPBRgAwBlGRcZ2Dsz8lraT2H%2fUMfPZd53%2fTQPmFUzeMng01ZJEukm0A%3d%3d | unknown | — | — | whitelisted |
8652 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747704462&P2=404&P3=2&P4=jn6fQk9%2fBghXh2zZckf591cN%2fRi%2f4sC%2bPBRgAwBlGRcZ2Dsz8lraT2H%2fUMfPZd53%2fTQPmFUzeMng01ZJEukm0A%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.15:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7420 | msedge.exe | 172.67.199.186:443 | the.gatekeeperconsent.com | — | — | unknown |
7420 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7420 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7420 | msedge.exe | 104.17.150.117:443 | www.mediafire.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7420 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7420 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7420 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7420 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |