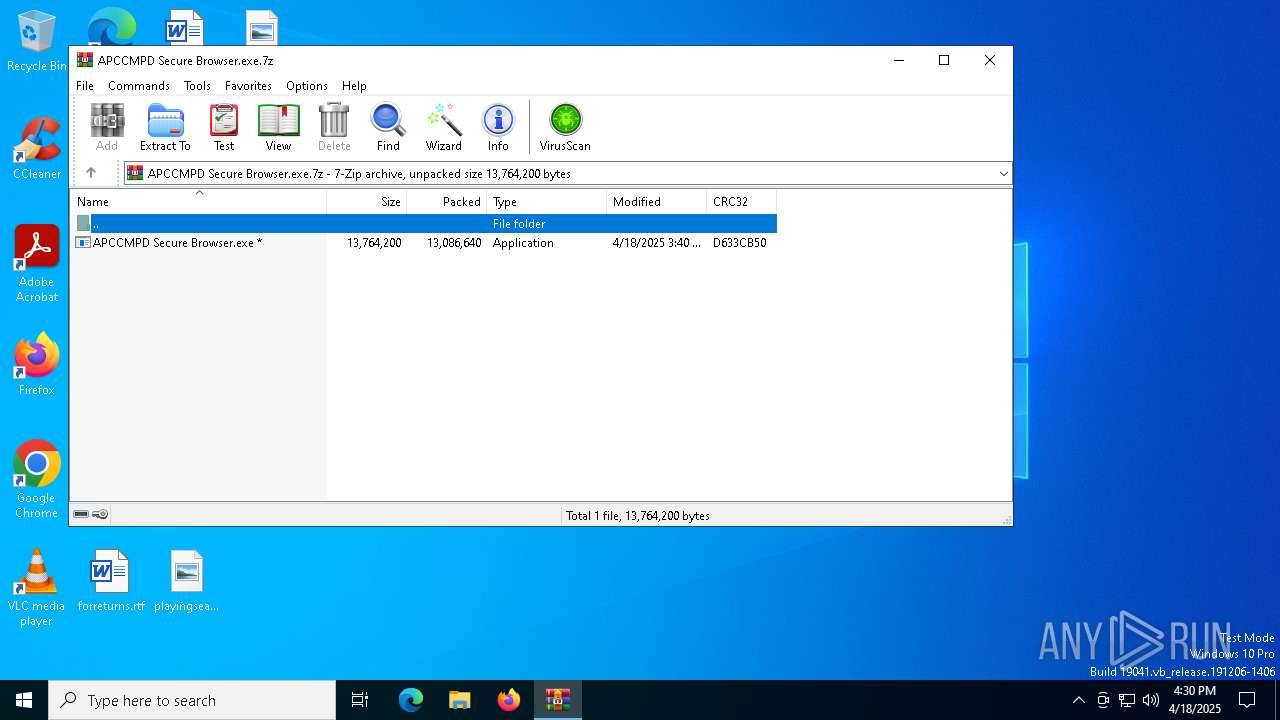
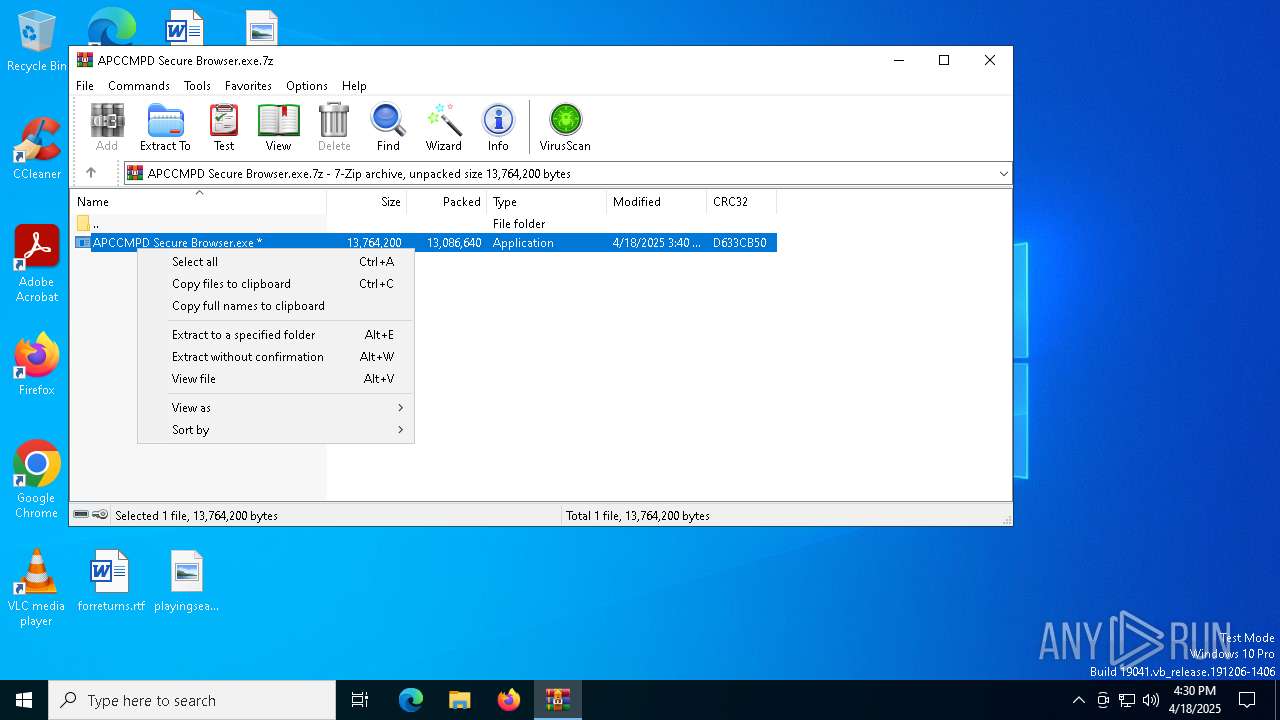
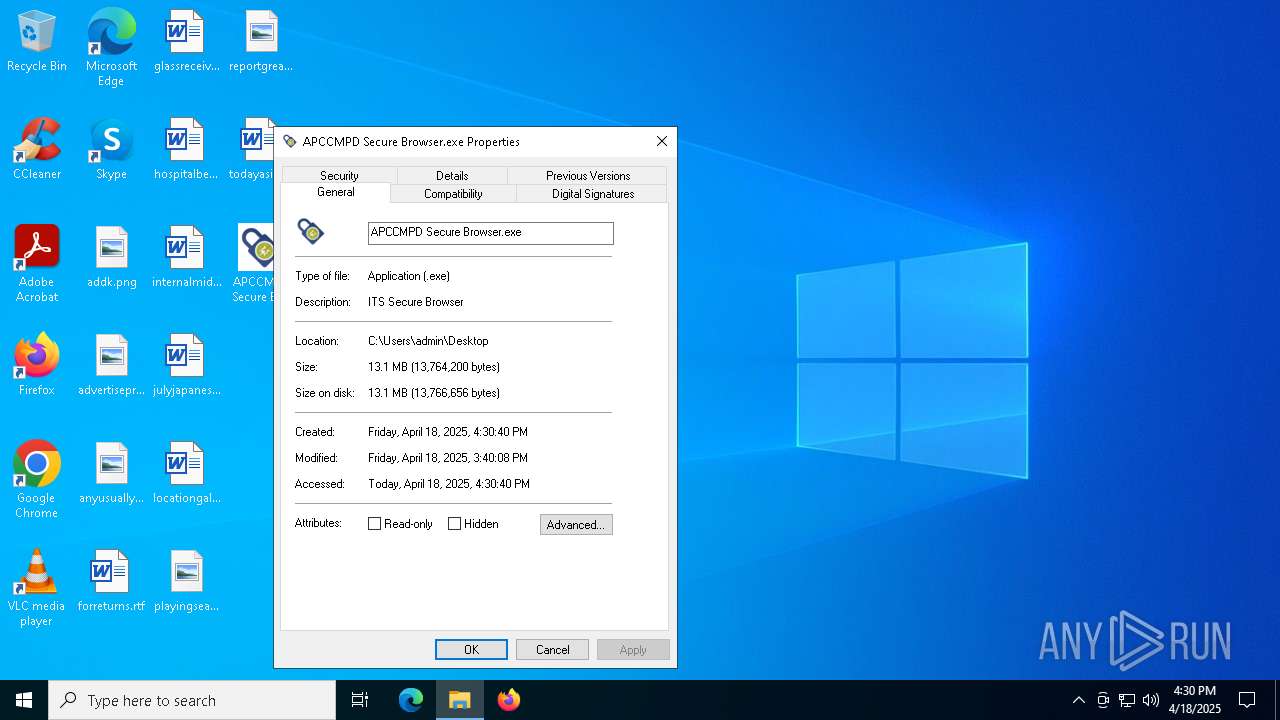
| File name: | APCCMPD Secure Browser.exe.7z |
| Full analysis: | https://app.any.run/tasks/6daaa5a8-50fd-4b6d-b42a-0f99f2e3aa2a |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2025, 16:29:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 4B56C7CA313D6A994285C0E7739F3BCA |
| SHA1: | 57C4452683E72BFA589E0DFBFDFE873274856852 |
| SHA256: | C719245CA8DF3B04BA212A4CD3133F7CB817358A11F975CC3A797A2C02A7A6D8 |
| SSDEEP: | 98304:fwvAtYiqdy3J36TkPeD76TPpR60vpNJdtT3Rsc2ZjOt0MMm9KJR5Ce03j6VSNmd9:hN0Z93+jmd/aBkUNyVWsY42 |
MALICIOUS
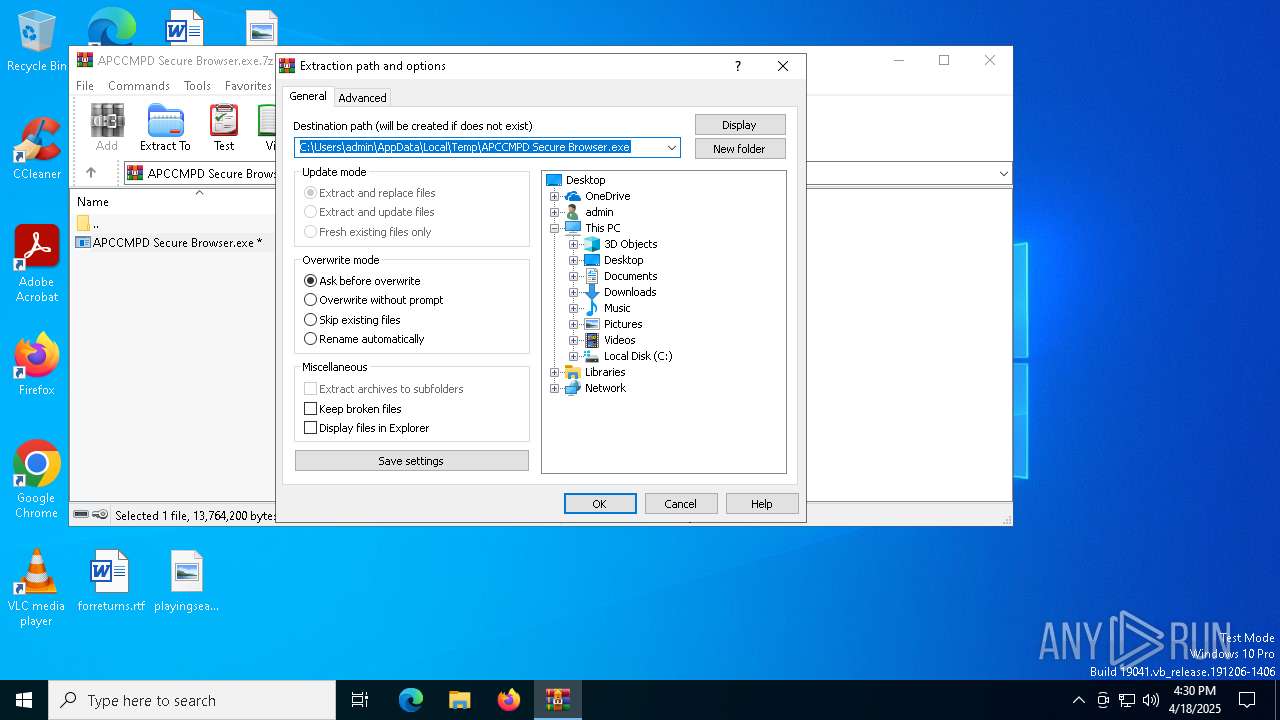
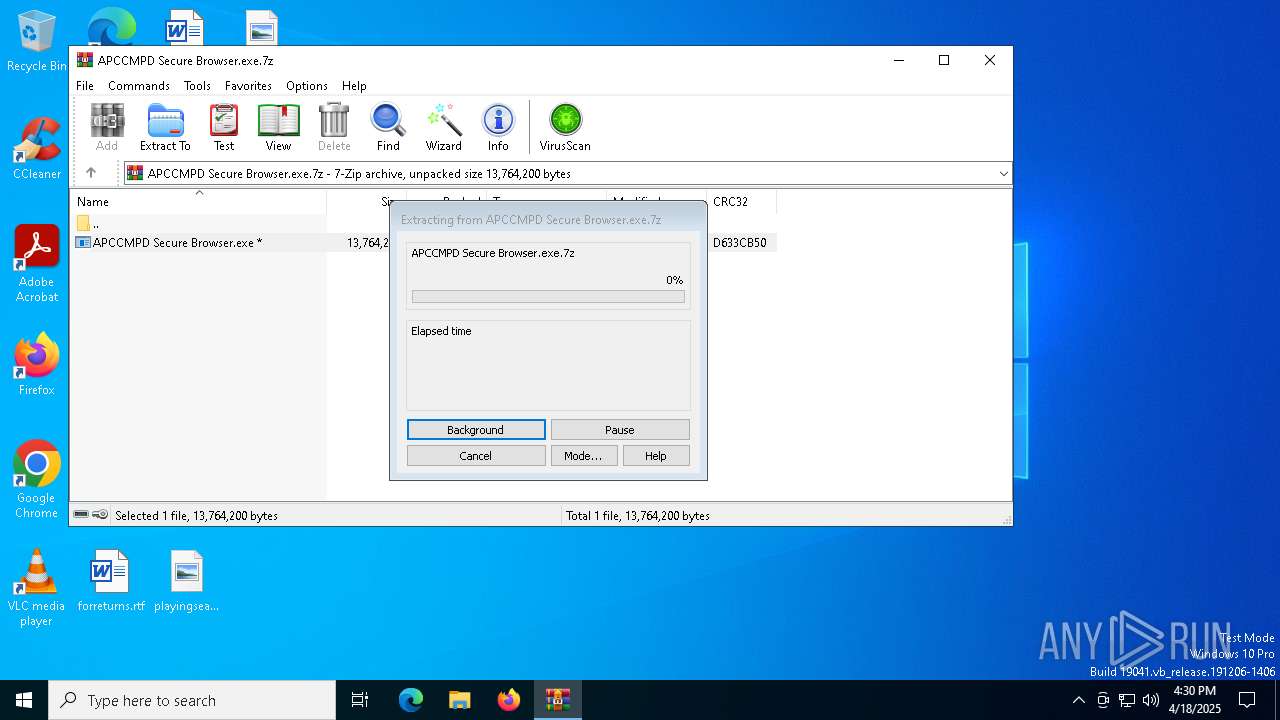
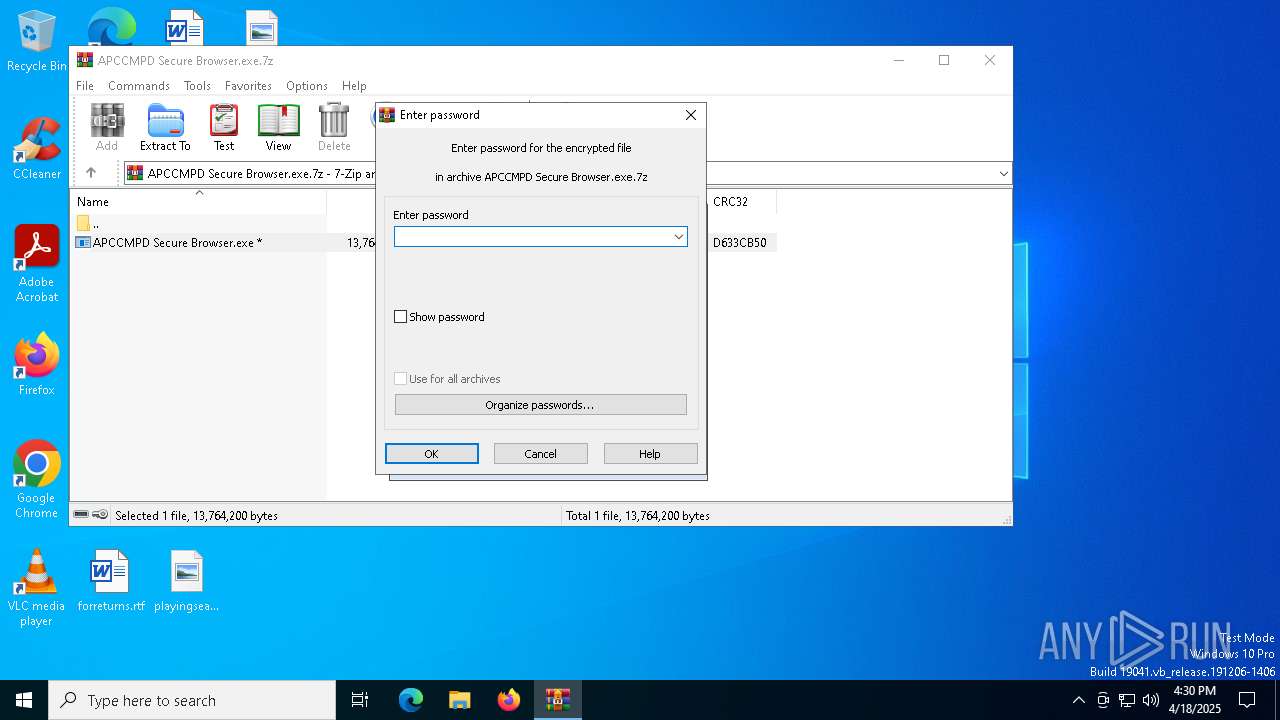
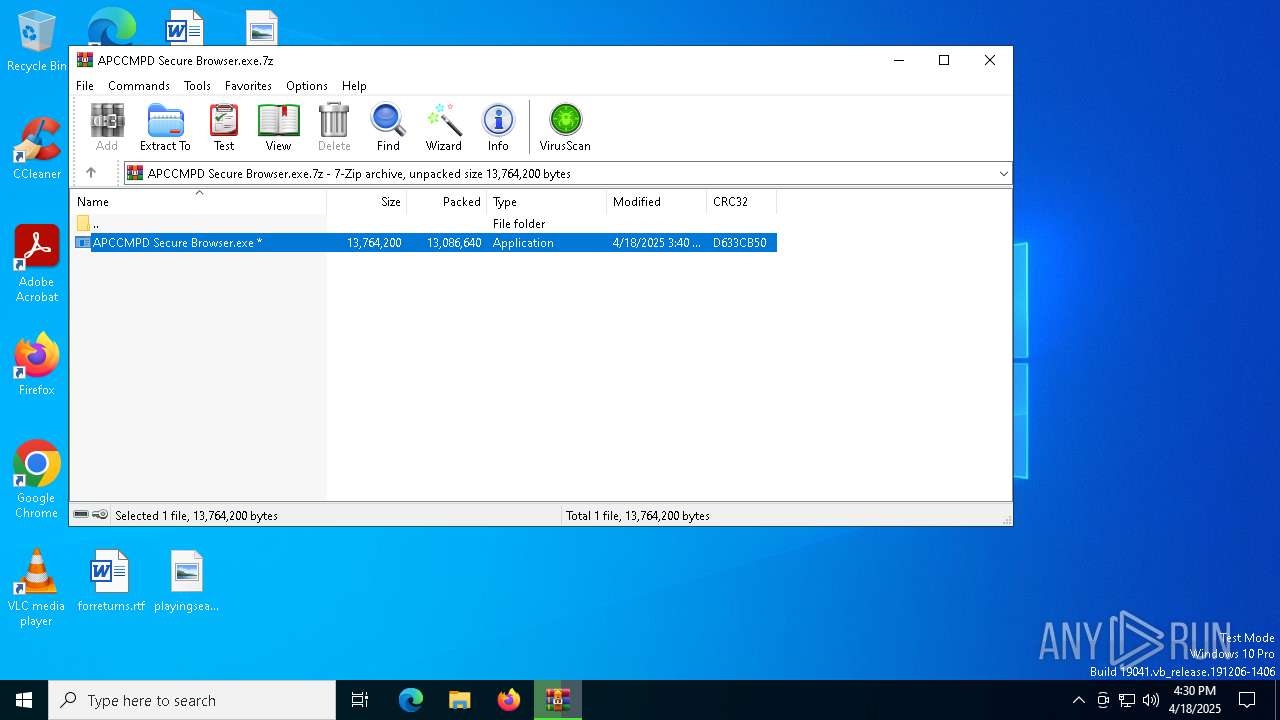
Generic archive extractor
- WinRAR.exe (PID: 4220)
Scans artifacts that could help determine the target
- msedgewebview2.exe (PID: 1188)
SUSPICIOUS
Reads the BIOS version
- APCCMPD Secure Browser.exe (PID: 8064)
Executable content was dropped or overwritten
- APCCMPD Secure Browser.exe (PID: 8064)
Reads security settings of Internet Explorer
- APCCMPD Secure Browser.exe (PID: 8064)
- msedgewebview2.exe (PID: 1188)
Application launched itself
- msedgewebview2.exe (PID: 1188)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4220)
Checks supported languages
- APCCMPD Secure Browser.exe (PID: 8064)
- SignInfoConsole.exe (PID: 8116)
- SignInfoConsole.exe (PID: 6040)
- SignInfoConsole.exe (PID: 4976)
- msedgewebview2.exe (PID: 4120)
- msedgewebview2.exe (PID: 5064)
- msedgewebview2.exe (PID: 1188)
- msedgewebview2.exe (PID: 7224)
- msedgewebview2.exe (PID: 2140)
- msedgewebview2.exe (PID: 7448)
- msedgewebview2.exe (PID: 6824)
- msedgewebview2.exe (PID: 5344)
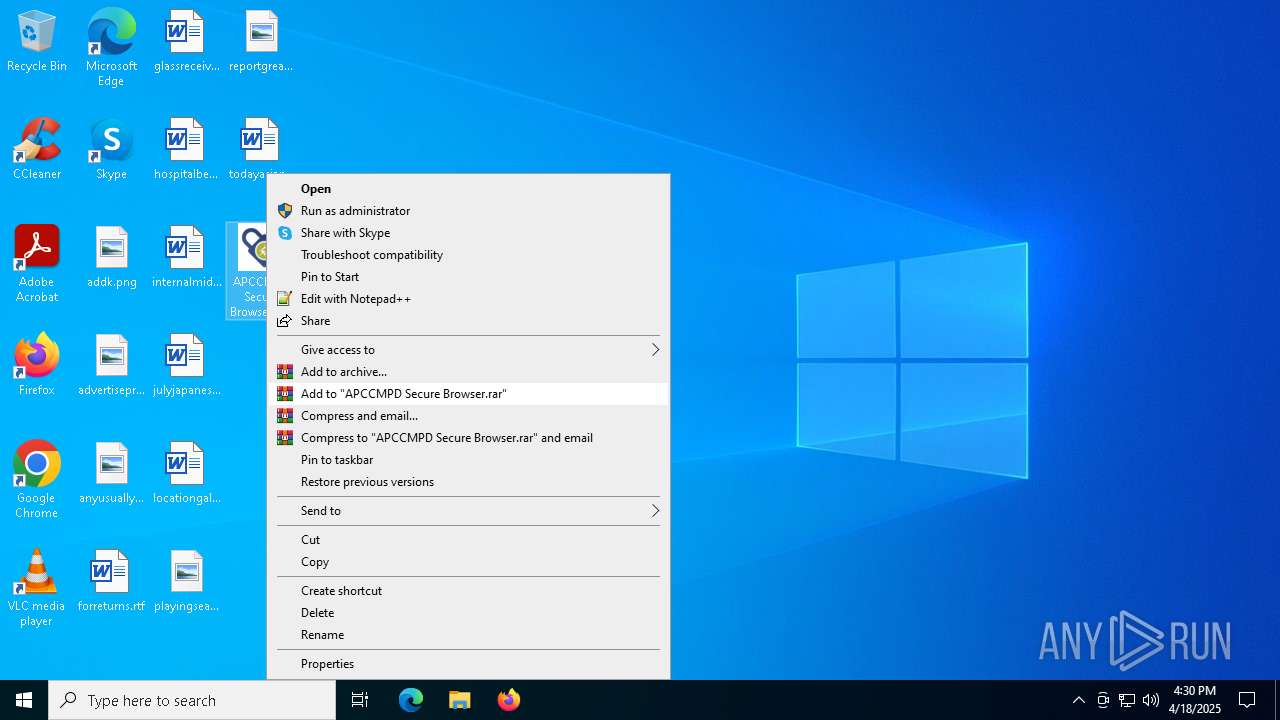
Manual execution by a user
- APCCMPD Secure Browser.exe (PID: 8064)
Reads the machine GUID from the registry
- APCCMPD Secure Browser.exe (PID: 8064)
- SignInfoConsole.exe (PID: 8116)
- SignInfoConsole.exe (PID: 6040)
- SignInfoConsole.exe (PID: 4976)
- msedgewebview2.exe (PID: 1188)
Reads the computer name
- APCCMPD Secure Browser.exe (PID: 8064)
- SignInfoConsole.exe (PID: 8116)
- SignInfoConsole.exe (PID: 6040)
- SignInfoConsole.exe (PID: 4976)
- msedgewebview2.exe (PID: 1188)
- msedgewebview2.exe (PID: 5064)
- msedgewebview2.exe (PID: 7448)
- msedgewebview2.exe (PID: 6824)
- msedgewebview2.exe (PID: 7224)
- msedgewebview2.exe (PID: 5344)
Create files in a temporary directory
- APCCMPD Secure Browser.exe (PID: 8064)
- msedgewebview2.exe (PID: 1188)
- msedgewebview2.exe (PID: 4120)
- msedgewebview2.exe (PID: 7224)
Disables trace logs
- APCCMPD Secure Browser.exe (PID: 8064)
Checks proxy server information
- APCCMPD Secure Browser.exe (PID: 8064)
- msedgewebview2.exe (PID: 1188)
Reads the software policy settings
- APCCMPD Secure Browser.exe (PID: 8064)
- slui.exe (PID: 7268)
Reads Environment values
- APCCMPD Secure Browser.exe (PID: 8064)
- msedgewebview2.exe (PID: 1188)
- msedgewebview2.exe (PID: 7224)
- msedgewebview2.exe (PID: 2140)
- msedgewebview2.exe (PID: 7448)
- msedgewebview2.exe (PID: 6824)
- msedgewebview2.exe (PID: 5064)
- msedgewebview2.exe (PID: 5344)
Creates files or folders in the user directory
- APCCMPD Secure Browser.exe (PID: 8064)
- msedgewebview2.exe (PID: 1188)
Reads product name
- APCCMPD Secure Browser.exe (PID: 8064)
Process checks computer location settings
- msedgewebview2.exe (PID: 1188)
- APCCMPD Secure Browser.exe (PID: 8064)
- msedgewebview2.exe (PID: 7448)
- msedgewebview2.exe (PID: 5344)
- msedgewebview2.exe (PID: 6824)
Reads CPU info
- APCCMPD Secure Browser.exe (PID: 8064)
Themida protector has been detected
- APCCMPD Secure Browser.exe (PID: 8064)
Creates files in the program directory
- APCCMPD Secure Browser.exe (PID: 8064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2025:04:18 15:40:08+00:00 |
| ArchivedFileName: | APCCMPD Secure Browser.exe |
Total processes
151
Monitored processes
19
Malicious processes
1
Suspicious processes
1
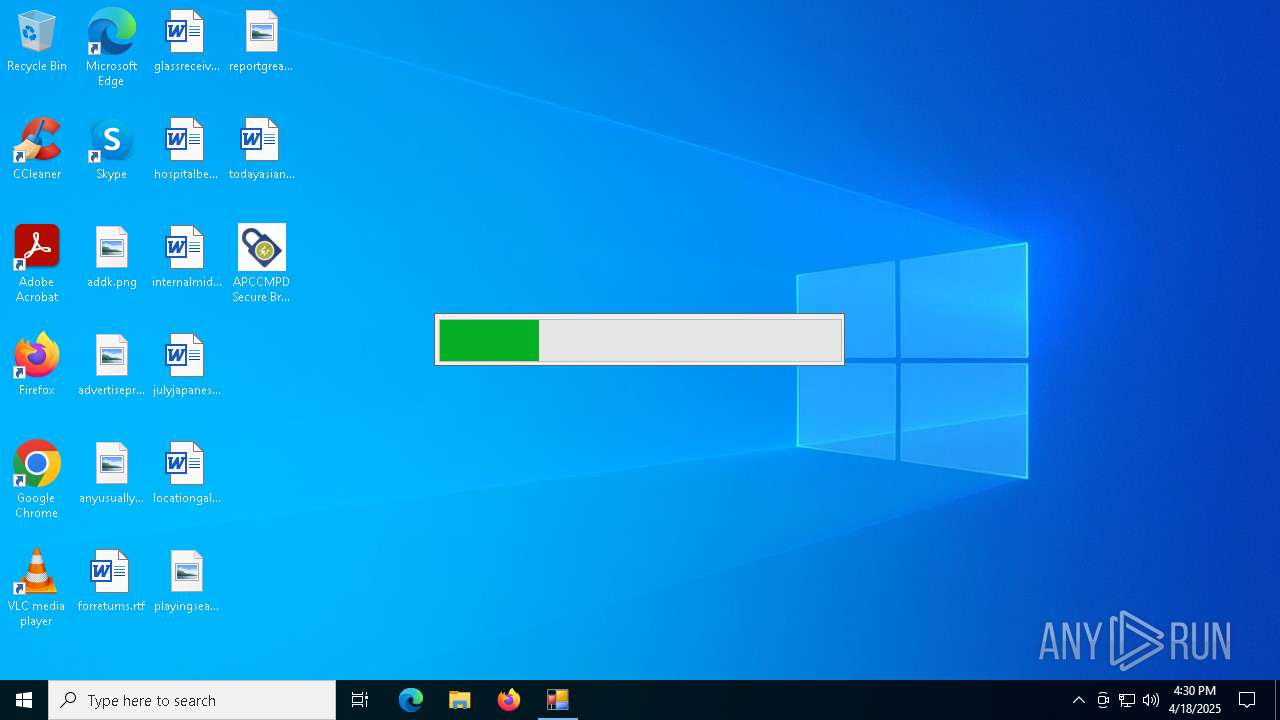
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe" --embedded-browser-webview=1 --webview-exe-name="APCCMPD Secure Browser.exe" --webview-exe-version=15.0.11.0 --user-data-dir="C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView" --noerrdialogs --embedded-browser-webview-dpi-awareness=0 --edge-webview-custom-scheme --autoplay-policy=no-user-gesture-required --disable-features=OverscrollHistoryNavigation,msExperimentalScrolling --enable-features=MojoIpcz --mojo-named-platform-channel-pipe=8064.6192.14900842674323237658 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe | — | APCCMPD Secure Browser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Exit code: 4294967295 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2140 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView" --webview-exe-name="APCCMPD Secure Browser.exe" --webview-exe-version=15.0.11.0 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=0 --edge-webview-custom-scheme --no-appcompat-clear --mojo-platform-channel-handle=2544 --field-trial-handle=2188,i,18084245309069112119,16089431924076752659,262144 --enable-features=MojoIpcz --disable-features=OverscrollHistoryNavigation,msExperimentalScrolling --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4120 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe" --annotation=plat=Win64 "--annotation=prod=Edge WebView2" --annotation=ver=122.0.2365.59 --initial-client-data=0x1ac,0x1b0,0x1b4,0x180,0x184,0x7ffc898e5fd8,0x7ffc898e5fe4,0x7ffc898e5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4220 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\APCCMPD Secure Browser.exe.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SignInfoConsole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4976 | "C:\Users\admin\AppData\Local\Temp\OSB\SignInfoConsole.exe" "C:\Users\admin\Desktop\APCCMPD Secure Browser.exe" | C:\Users\admin\AppData\Local\Temp\OSB\SignInfoConsole.exe | — | APCCMPD Secure Browser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SignInfoConsole Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5064 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe" --type=gpu-process --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView" --webview-exe-name="APCCMPD Secure Browser.exe" --webview-exe-version=15.0.11.0 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=0 --edge-webview-custom-scheme --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2184 --field-trial-handle=2188,i,18084245309069112119,16089431924076752659,262144 --enable-features=MojoIpcz --disable-features=OverscrollHistoryNavigation,msExperimentalScrolling --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5344 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView" --webview-exe-name="APCCMPD Secure Browser.exe" --webview-exe-version=15.0.11.0 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=0 --edge-webview-custom-scheme --no-appcompat-clear --autoplay-policy=no-user-gesture-required --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --js-flags="--harmony-weak-refs-with-cleanup-some --expose-gc --ms-user-locale=" --mojo-platform-channel-handle=4872 --field-trial-handle=2188,i,18084245309069112119,16089431924076752659,262144 --enable-features=MojoIpcz --disable-features=OverscrollHistoryNavigation,msExperimentalScrolling --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6040 | "C:\Users\admin\AppData\Local\Temp\OSB\SignInfoConsole.exe" "C:\Users\admin\Desktop\APCCMPD Secure Browser.exe" | C:\Users\admin\AppData\Local\Temp\OSB\SignInfoConsole.exe | — | APCCMPD Secure Browser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SignInfoConsole Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6344 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 060
Read events
7 992
Write events
55
Delete events
13
Modification events
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\APCCMPD Secure Browser.exe.7z | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
13
Suspicious files
130
Text files
33
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8064 | APCCMPD Secure Browser.exe | C:\Users\admin\AppData\Local\Temp\OSB\SignInfoConsole.exe | executable | |
MD5:9C11A9BD1765AA8B89E9DE29D252A524 | SHA256:E7832BCF1BDDD4A296C52AF635AD831DF01ED596ADAADDEFD4A9B1B1343F2387 | |||
| 1188 | msedgewebview2.exe | C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 8064 | APCCMPD Secure Browser.exe | C:\Users\admin\AppData\Local\Temp\7e70eca.dll | executable | |
MD5:7AFBF68246B7D5E54B7BBE4659DA4925 | SHA256:2692CC47E8A4E6E4CB46C19739A337BB7443CFFE6DB4A84AF0B80277697C3288 | |||
| 8064 | APCCMPD Secure Browser.exe | C:\Users\admin\AppData\Local\Temp\7e70ec9.dll | executable | |
MD5:D161D1106439AC4FF6A7A18B09EFF2E2 | SHA256:DBF8957B44B525B564DDA7485BBC9B4668C97ABCCDCA19478458CAF112003CFD | |||
| 1188 | msedgewebview2.exe | C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView\d15aa179-4048-41a2-9156-5cabe6ac40ea.tmp | binary | |
MD5:57F7EA39442338EAA1CDFFA4D33A238A | SHA256:CED90DECEC32D5AD29124EF96A805EC133D00E6E40A3437B7C09CBC577473C97 | |||
| 1188 | msedgewebview2.exe | C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView\ShaderCache\data_0 | binary | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 1188 | msedgewebview2.exe | C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView\ShaderCache\index | binary | |
MD5:D1673CEEF2210EB25BB509B534C80EBF | SHA256:7F5B8C29B9A3B6A000D49A3427D57796022694C50AB0E068881AE0A7DC455548 | |||
| 1188 | msedgewebview2.exe | C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView\Crashpad\throttle_store.dat | text | |
MD5:9E4E94633B73F4A7680240A0FFD6CD2C | SHA256:41C91A9C93D76295746A149DCE7EBB3B9EE2CB551D84365FFF108E59A61CC304 | |||
| 8064 | APCCMPD Secure Browser.exe | C:\Users\admin\AppData\Local\IsolatedStorage\pcl5vf1d.eb5\den3dnjh.r33\Url.ebdb4ytxmvmgp54yrcuettt1opcvulwt\info.dat | binary | |
MD5:0A53C1D28669E7E0E50FCDF88C8127C5 | SHA256:D5755A80F47671E9C3E10C007865D7868432D9942CA2CE7D60510039A281CC5C | |||
| 1188 | msedgewebview2.exe | C:\Users\admin\AppData\Local\Temp\.WebView2\EBWebView\ShaderCache\data_3 | vxd | |
MD5:41876349CB12D6DB992F1309F22DF3F0 | SHA256:E09F42C398D688DCE168570291F1F92D079987DEDA3099A34ADB9E8C0522B30C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
37
DNS requests
24
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
7836 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
8064 | APCCMPD Secure Browser.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEEkNsD53GoJVFMAtazZydYk%3D | unknown | binary | 471 b | whitelisted |
8064 | APCCMPD Secure Browser.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | binary | 1.42 Kb | whitelisted |
7836 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
8064 | APCCMPD Secure Browser.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | whitelisted |
7224 | msedgewebview2.exe | GET | 200 | 161.47.163.213:80 | http://apccmpd.starttest.com/ | US | html | 302 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6656 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.starttest.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8064 | APCCMPD Secure Browser.exe | Misc activity | INFO [ANY.RUN] Pearson VUE Client SSL Cert |
8064 | APCCMPD Secure Browser.exe | Misc activity | INFO [ANY.RUN] Pearson VUE Client SSL Cert |
7224 | msedgewebview2.exe | Misc activity | INFO [ANY.RUN] Pearson VUE Client SSL Cert |
7224 | msedgewebview2.exe | Misc activity | INFO [ANY.RUN] Pearson VUE Client SSL Cert |