| File name: | 424c0f0d22d04bd2fcd087eac034706f.exe |
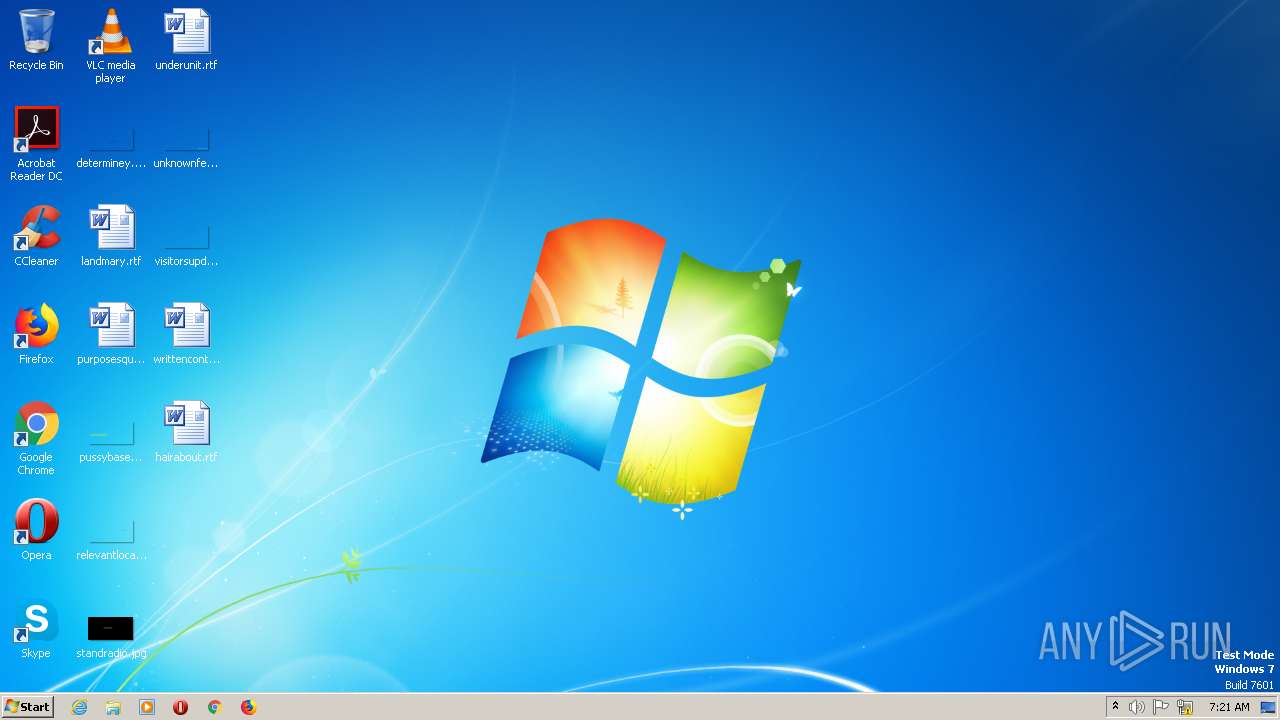
| Full analysis: | https://app.any.run/tasks/f7fe67cc-0362-4af0-8fc7-4199ff43a4e5 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 07:21:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 424C0F0D22D04BD2FCD087EAC034706F |
| SHA1: | B1161AF7038B2C27E44A5C0D5450F40292C78686 |
| SHA256: | C7123AE9EFB2106D9B875328DAFE1C5E943DAB9EA10EA504D6C88E65BF033E10 |
| SSDEEP: | 6144:ZE51S7leXHwUo9QB+QHEcHftOEm9M8rY/c57uG:8o7vHg+uf4J9frq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Checks Windows Trust Settings
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Process requests binary or script from the Internet
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Executable content was dropped or overwritten
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Reads settings of System Certificates
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Reads the Internet Settings
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
INFO
Checks supported languages
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Reads the machine GUID from the registry
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Create files in a temporary directory
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Reads the computer name
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
The process checks LSA protection
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Creates files or folders in the user directory
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Checks proxy server information
- 424c0f0d22d04bd2fcd087eac034706f.exe (PID: 1376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductName: | Imba |
|---|---|
| LegalCopyright: | Copyright (C) 2023, shmaer |
| InternalName: | GodGuest |
| FilesVersion: | 19.62.99 |
| CharacterSet: | Unknown (01F2) |
| LanguageCode: | Manipuri |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Unknown (0x20461) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x121a |
| ProductVersionNumber: | 26.0.0.0 |
| FileVersionNumber: | 2.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x6160 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 495104 |
| CodeSize: | 243200 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:02:04 16:19:03+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Feb-2022 16:19:03 |
| Detected languages: |
|
| Debug artifacts: |
|
| FilesVersion: | 19.62.99 |
| InternalName: | GodGuest |
| LegalCopyright: | Copyright (C) 2023, shmaer |
| ProductName: | Imba |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 04-Feb-2022 16:19:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003B442 | 0x0003B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.72971 |
.data | 0x0003D000 | 0x0006F69C | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.2227 |
.rsrc | 0x000AD000 | 0x000070C8 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.86611 |
.reloc | 0x000B5000 | 0x0000220C | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.73279 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34304 | 460 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 5.75646 | 2216 | UNKNOWN | Spanish - Mexico | RT_ICON |
3 | 5.33303 | 1736 | UNKNOWN | Spanish - Mexico | RT_ICON |
4 | 5.56649 | 1384 | UNKNOWN | Spanish - Mexico | RT_ICON |
5 | 5.24057 | 9640 | UNKNOWN | Spanish - Mexico | RT_ICON |
6 | 5.4725 | 4264 | UNKNOWN | Spanish - Mexico | RT_ICON |
7 | 5.60085 | 2440 | UNKNOWN | Spanish - Mexico | RT_ICON |
8 | 5.64988 | 1128 | UNKNOWN | Spanish - Mexico | RT_ICON |
22 | 3.13936 | 412 | UNKNOWN | UNKNOWN | RT_STRING |
23 | 3.22078 | 620 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
ole32.dll |
Total processes
29
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1376 | "C:\Users\admin\AppData\Local\Temp\424c0f0d22d04bd2fcd087eac034706f.exe" | C:\Users\admin\AppData\Local\Temp\424c0f0d22d04bd2fcd087eac034706f.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 692
Read events
1 658
Write events
34
Delete events
0
Modification events
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000008B000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1376) 424c0f0d22d04bd2fcd087eac034706f.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\14C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
4
Suspicious files
8
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3C428B1A3E5F57D887EC4B864FAC5DCC | der | |
MD5:E4A68AC854AC5242460AFD72481B2A44 | SHA256:CB3CCBB76031E5E0138F8DD39A23F9DE47FFC35E43C1144CEA27D46A5AB1CB5F | |||
| 1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | C:\Users\admin\AppData\Local\Temp\TarB4EF.tmp | cat | |
MD5:BE2BEC6E8C5653136D3E72FE53C98AA3 | SHA256:1919AAB2A820642490169BDC4E88BD1189E22F83E7498BF8EBDFB62EC7D843FD | |||
| 1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3C428B1A3E5F57D887EC4B864FAC5DCC | binary | |
MD5:— | SHA256:— | |||
| 1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | C:\Users\admin\AppData\Local\Temp\rAQBc8\dxwebsetup.exe | executable | |
MD5:2CBD6AD183914A0C554F0739069E77D7 | SHA256:2CF71D098C608C56E07F4655855A886C3102553F648DF88458DF616B26FD612F | |||
| 1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | C:\Users\admin\AppData\Local\Temp\CabB4EE.tmp | compressed | |
MD5:E71C8443AE0BC2E282C73FAEAD0A6DD3 | SHA256:95B0A5ACC5BF70D3ABDFD091D0C9F9063AA4FDE65BD34DBF16786082E1992E72 | |||
| 1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:E71C8443AE0BC2E282C73FAEAD0A6DD3 | SHA256:95B0A5ACC5BF70D3ABDFD091D0C9F9063AA4FDE65BD34DBF16786082E1992E72 | |||
| 1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\dxwebsetup[1].exe | executable | |
MD5:2CBD6AD183914A0C554F0739069E77D7 | SHA256:2CF71D098C608C56E07F4655855A886C3102553F648DF88458DF616B26FD612F | |||
| 1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
3
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | GET | 302 | 23.35.228.223:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/dxwebsetup.exe | US | — | — | whitelisted |
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | GET | 200 | 192.229.221.95:80 | http://cacerts.digicert.com/DigiCertGlobalRootG2.crt | US | der | 914 b | whitelisted |
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?023e1cae56c5a759 | US | compressed | 61.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | 23.35.228.223:80 | download.microsoft.com | AKAMAI-AS | DE | malicious |
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | 192.229.221.95:80 | cacerts.digicert.com | EDGECAST | US | whitelisted |
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | 23.35.228.223:443 | download.microsoft.com | AKAMAI-AS | DE | malicious |
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
cacerts.digicert.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
1376 | 424c0f0d22d04bd2fcd087eac034706f.exe | Unknown Traffic | ET JA3 Hash - [Abuse.ch] Possible Tofsee |