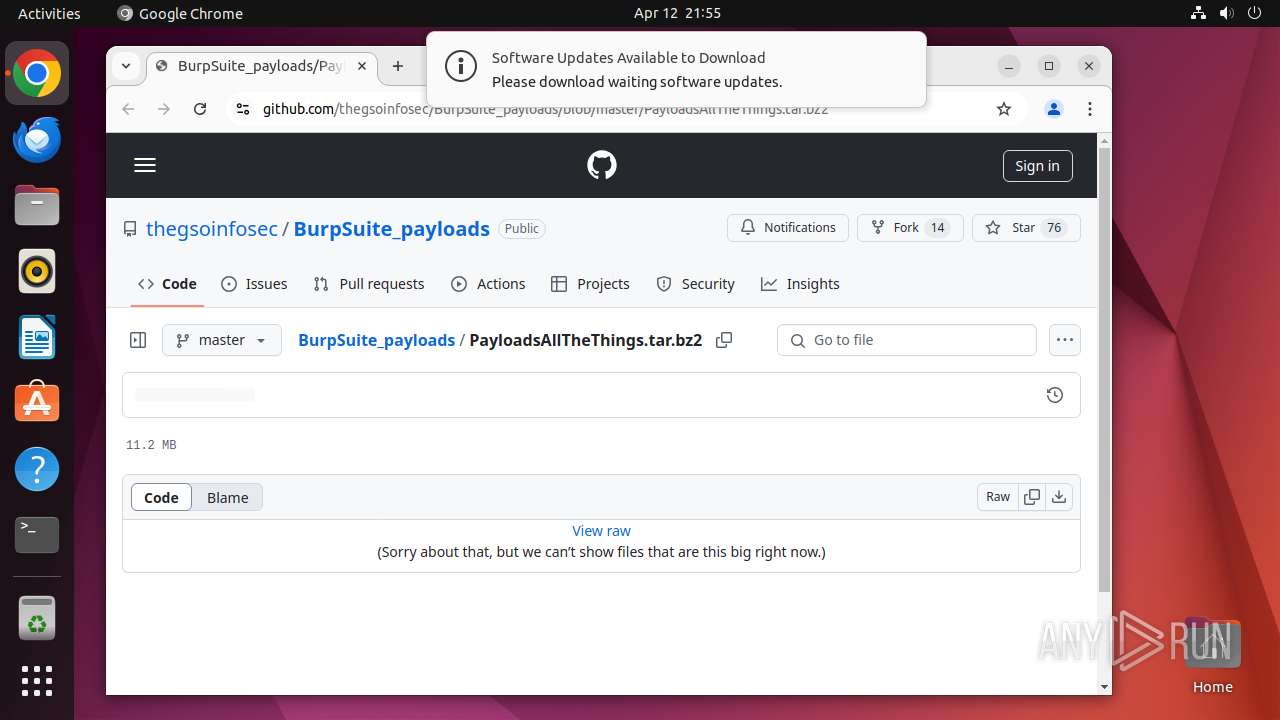
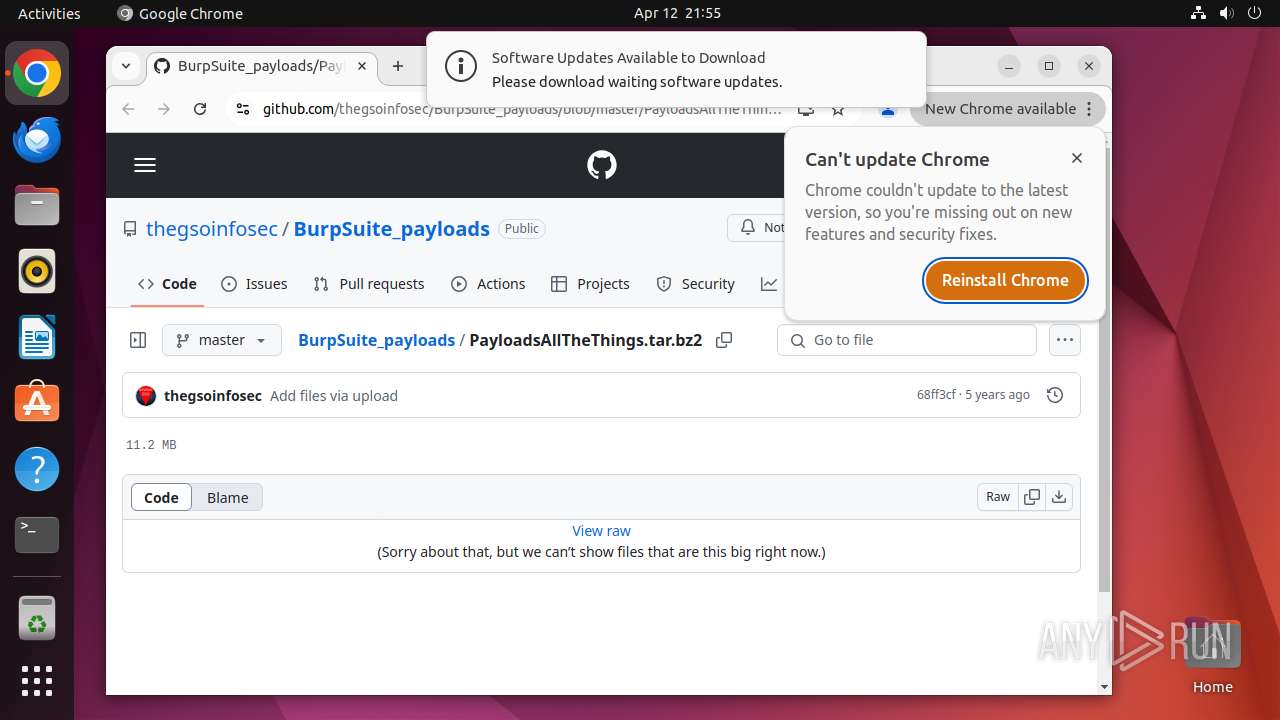
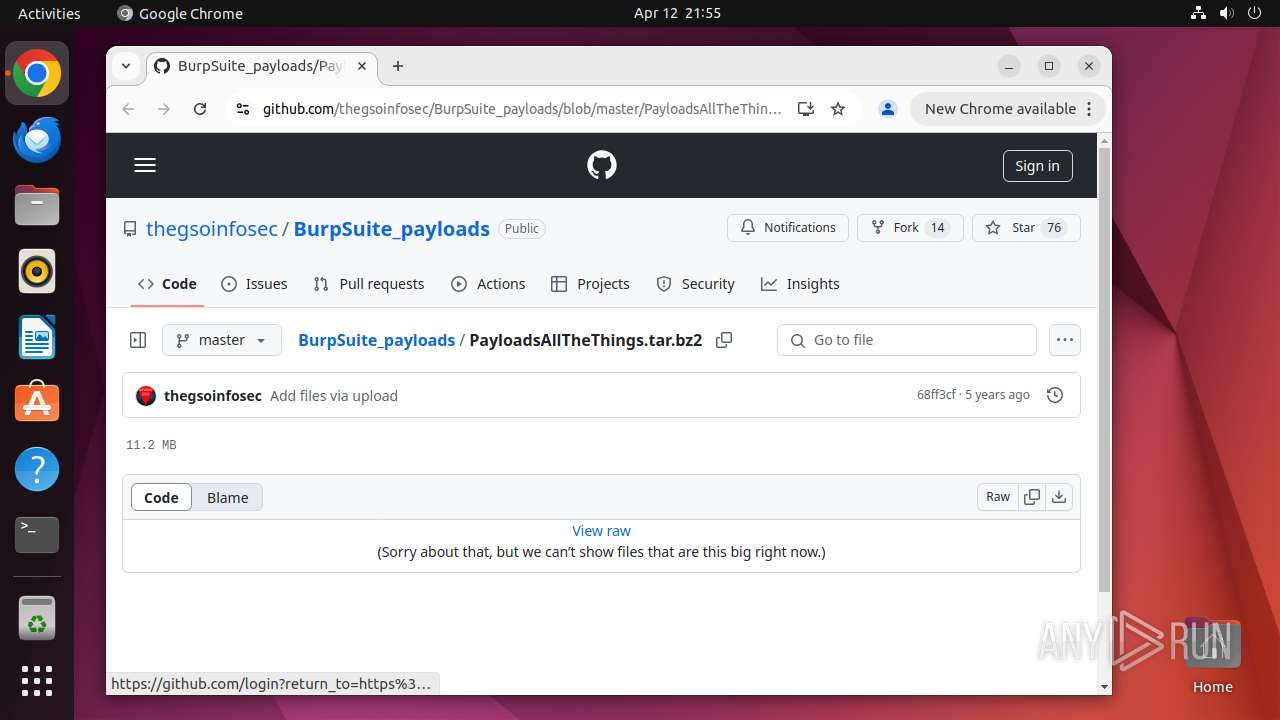
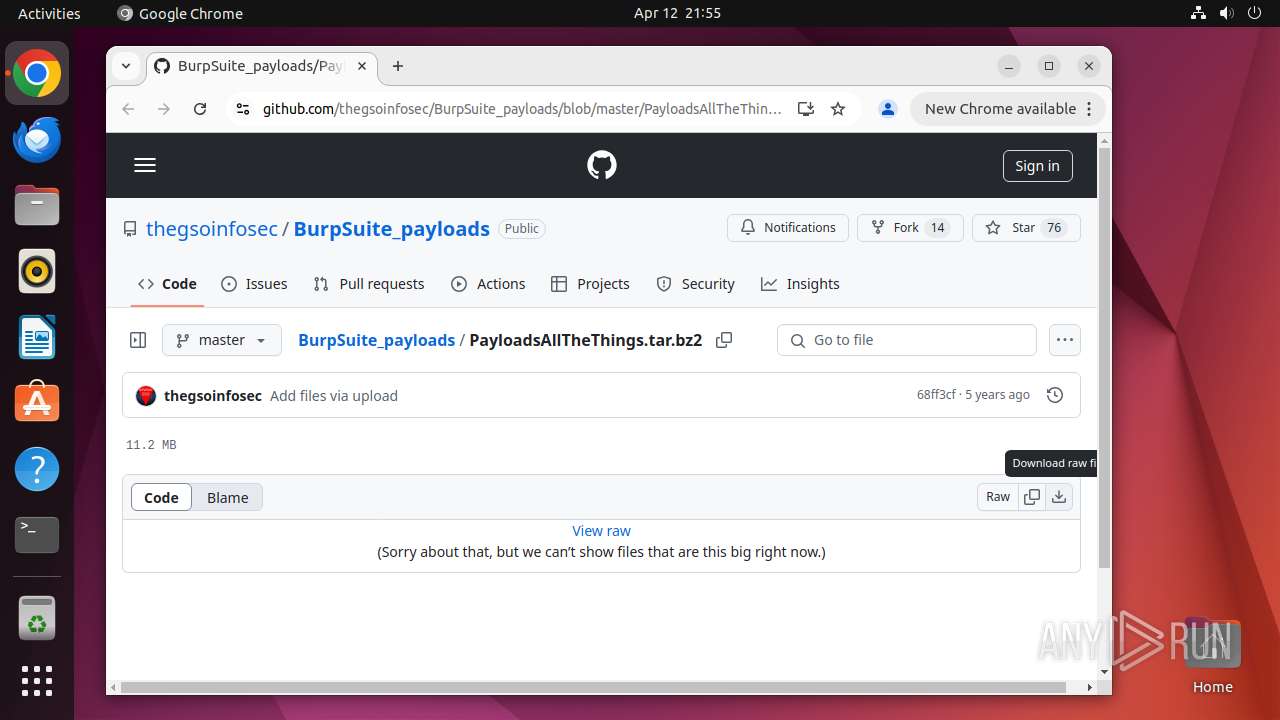
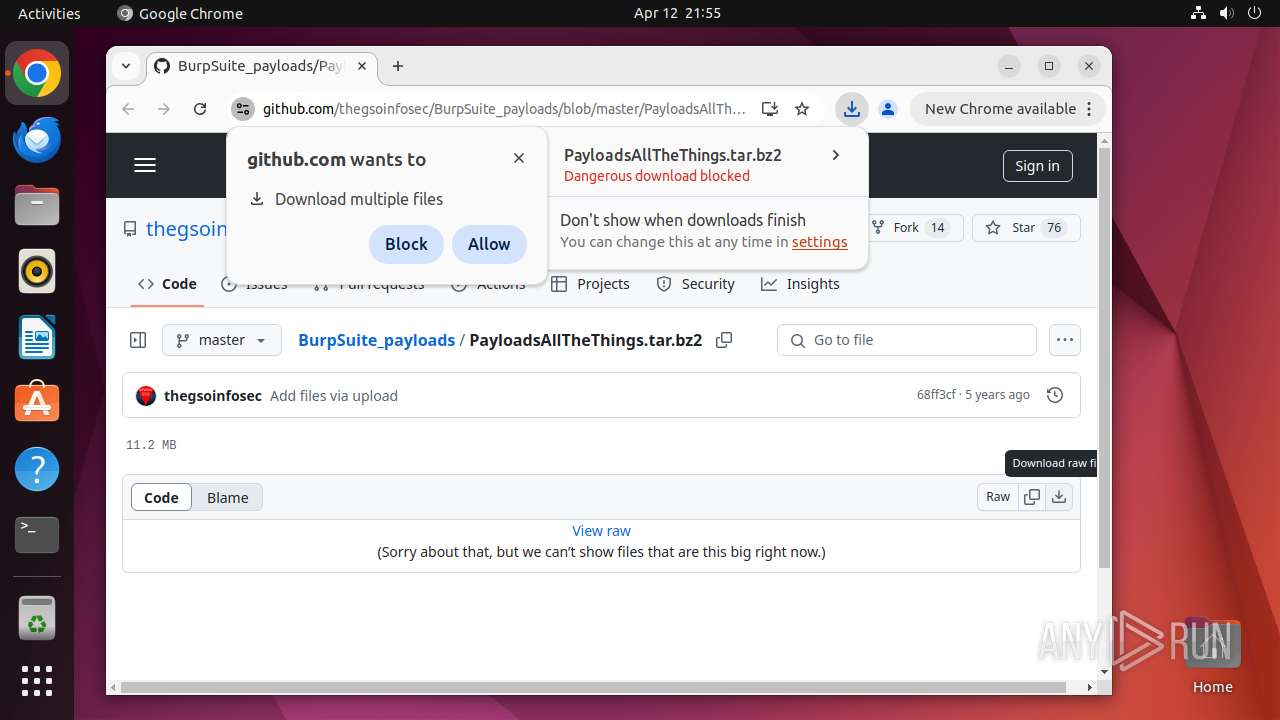
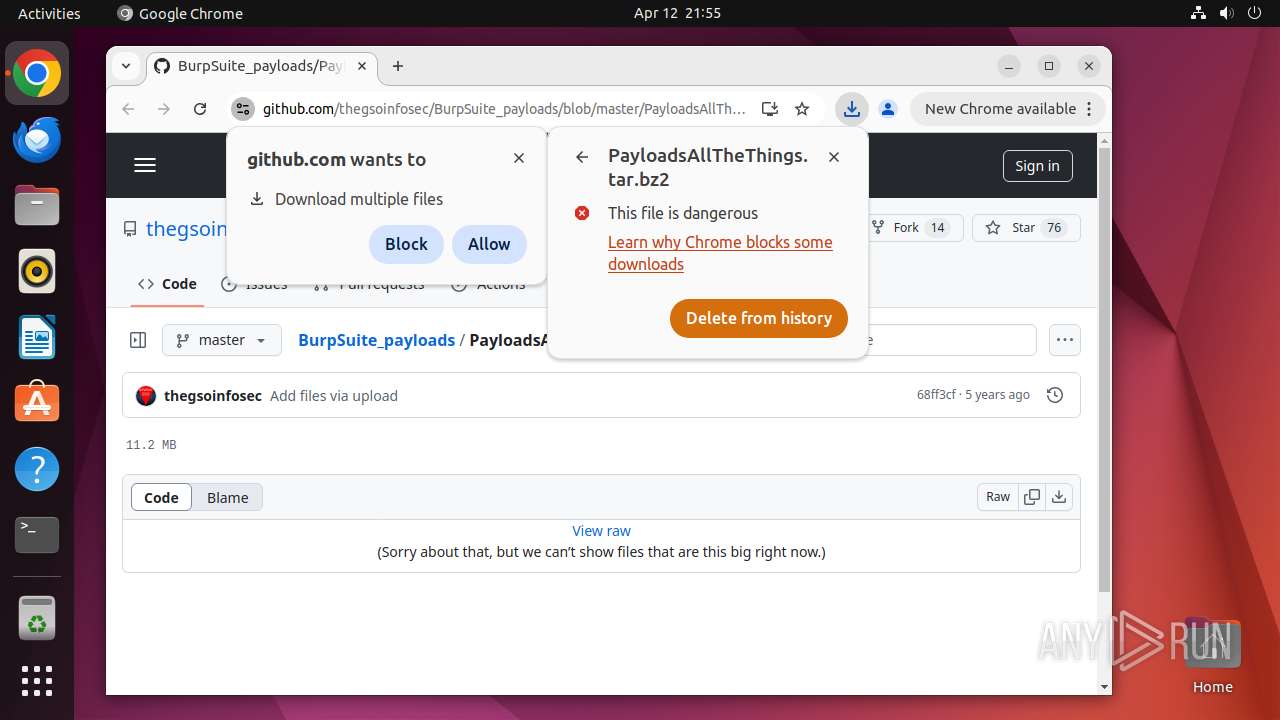
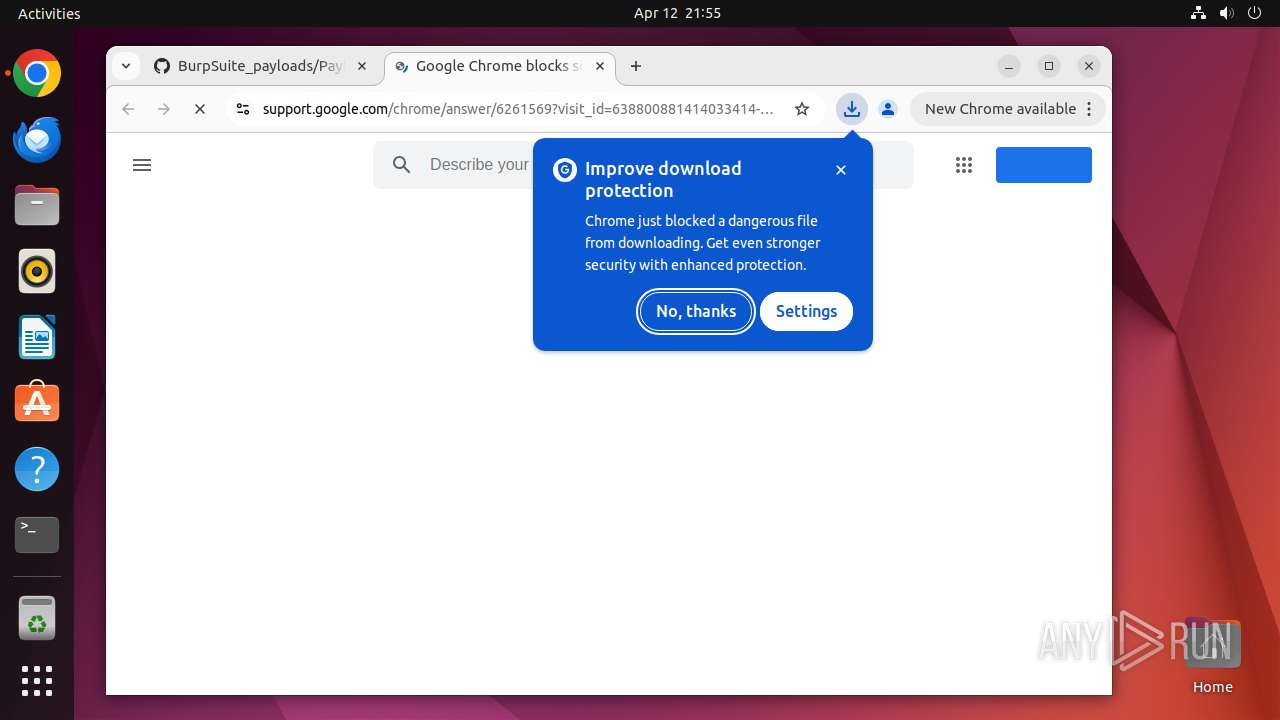
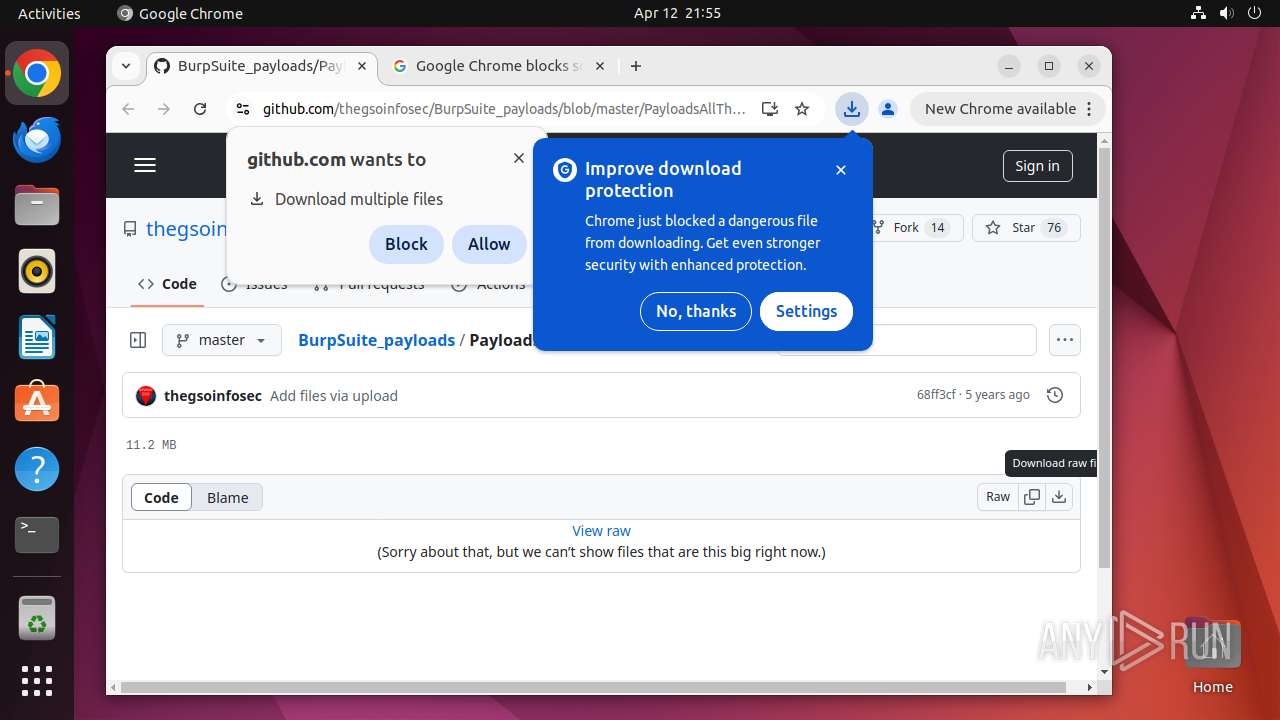
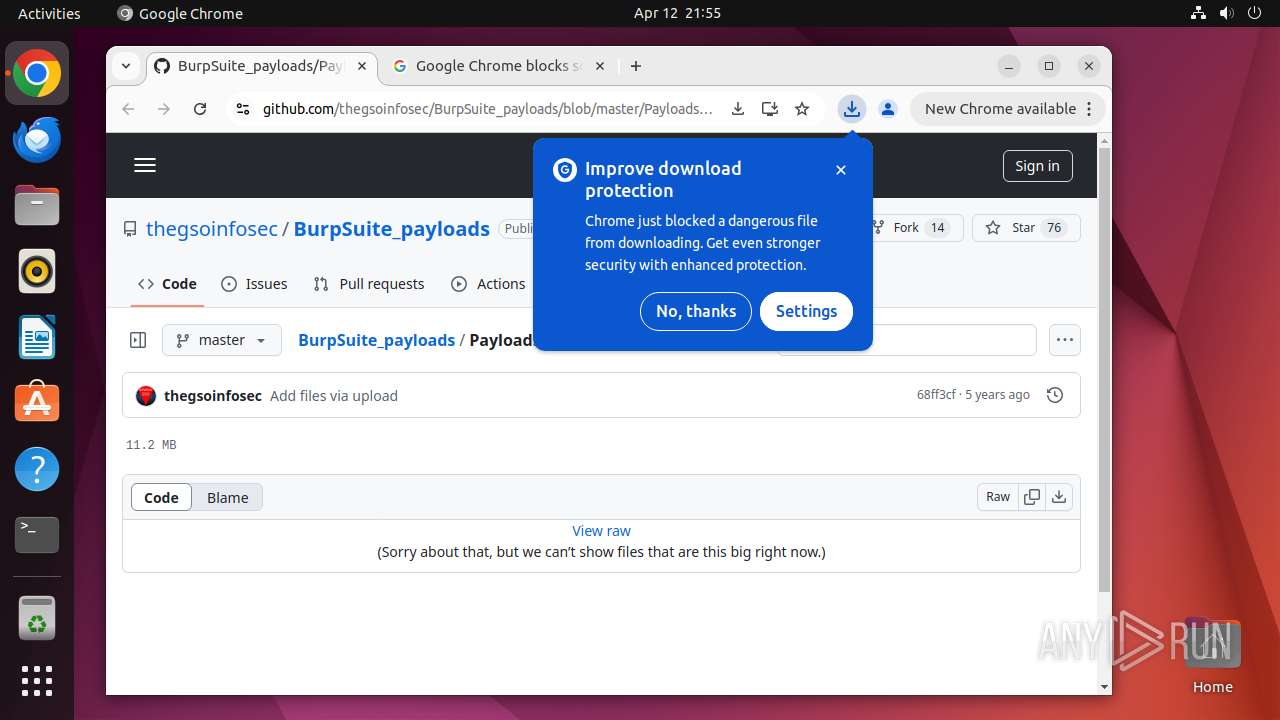
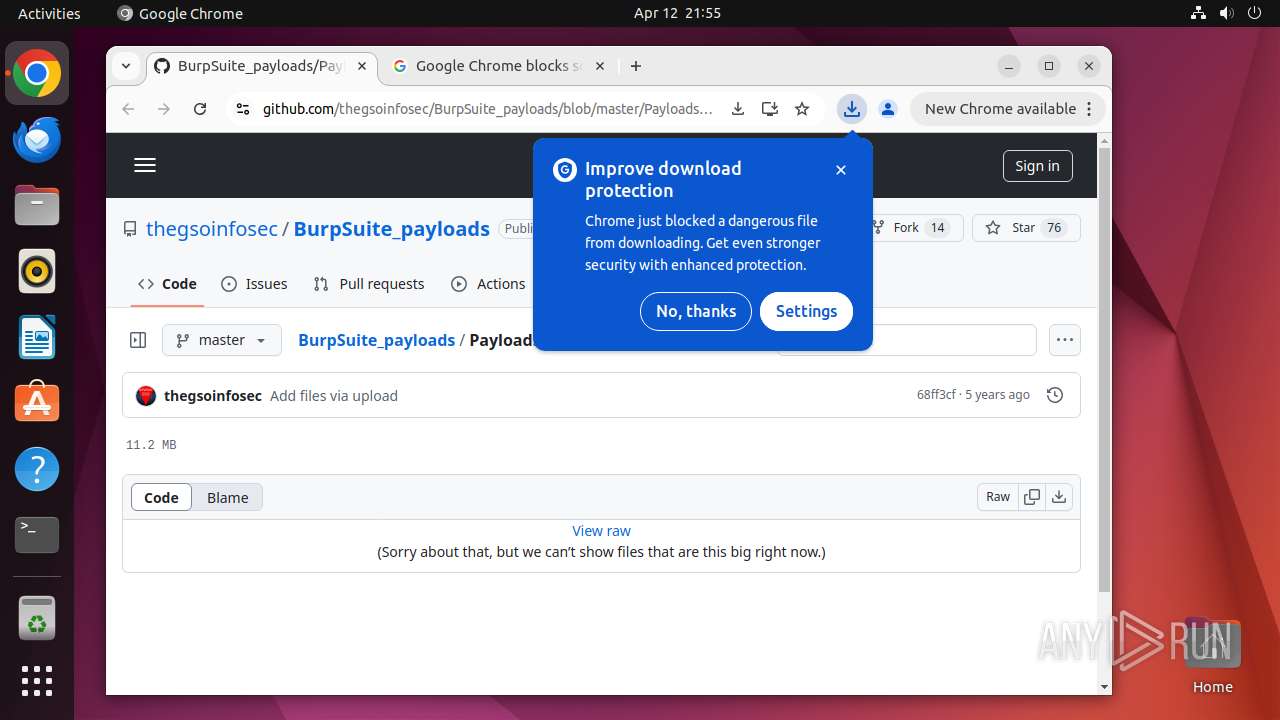
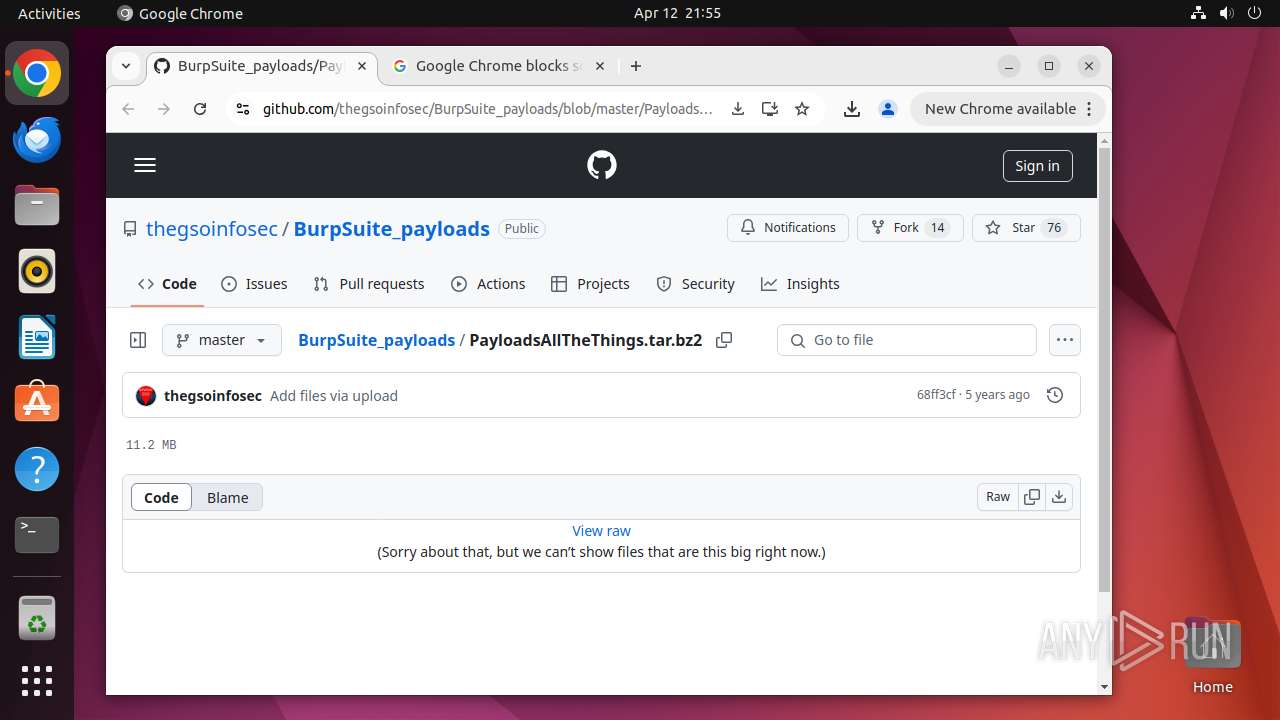
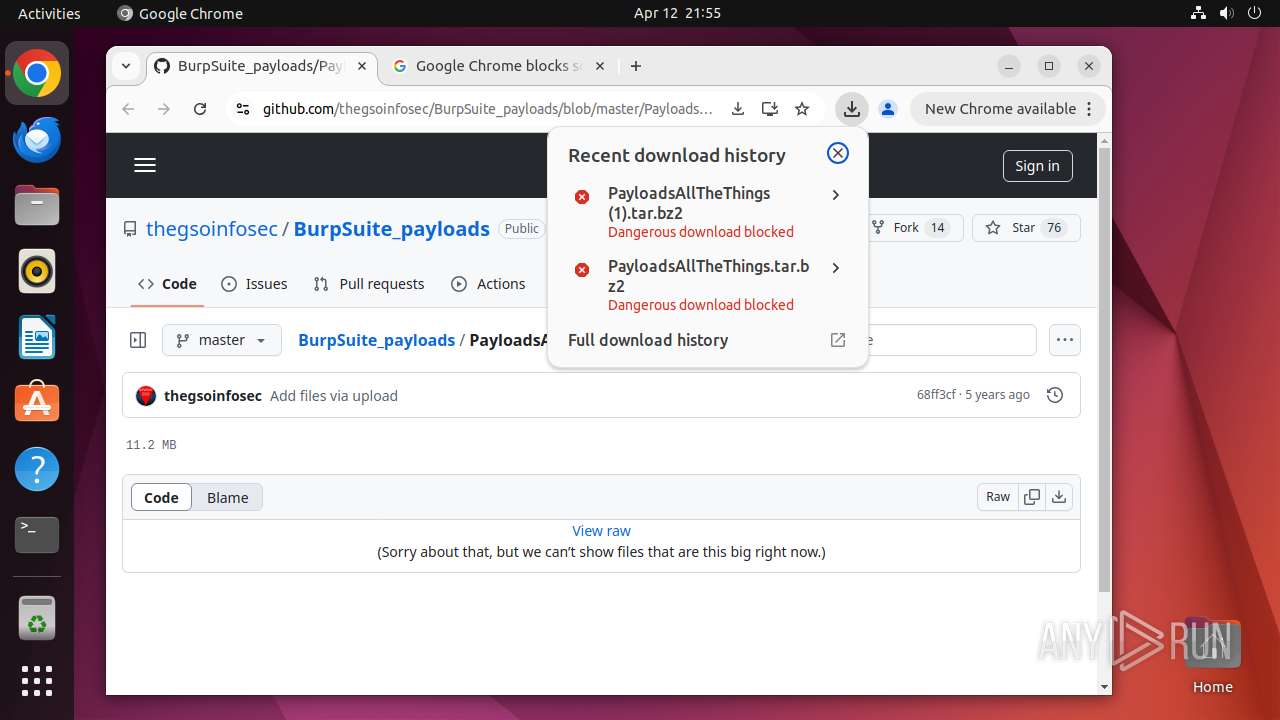
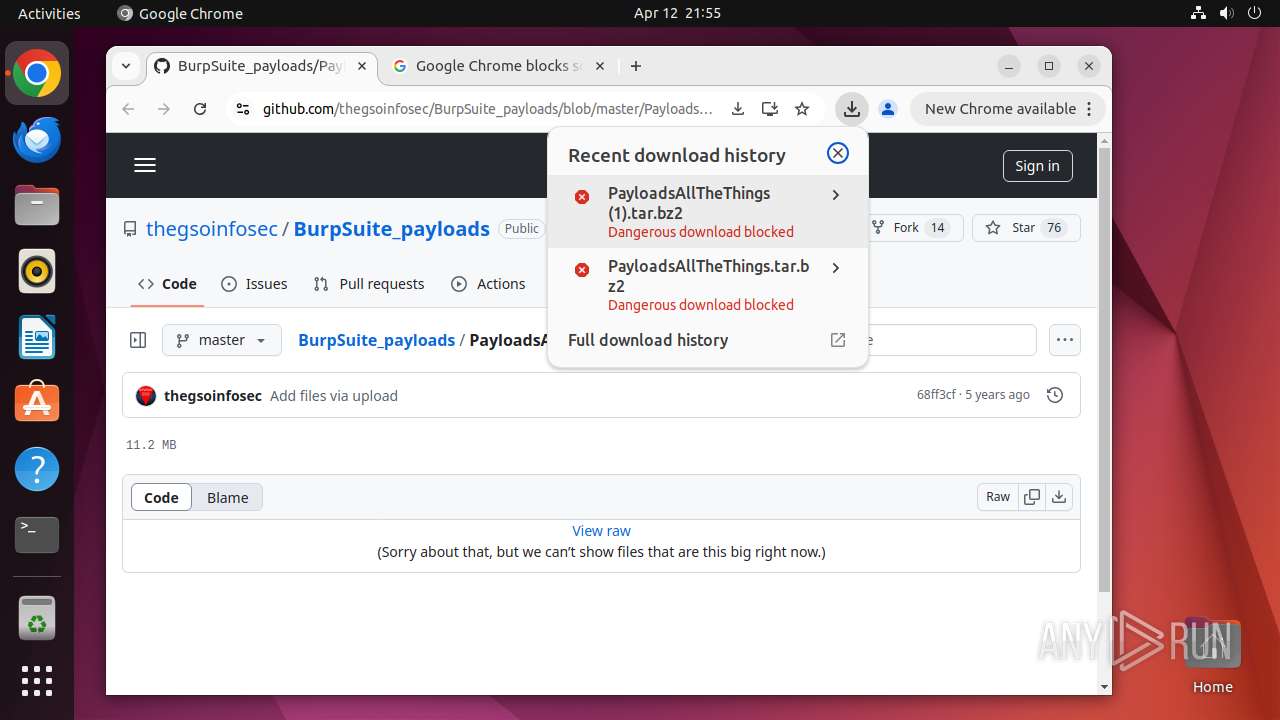
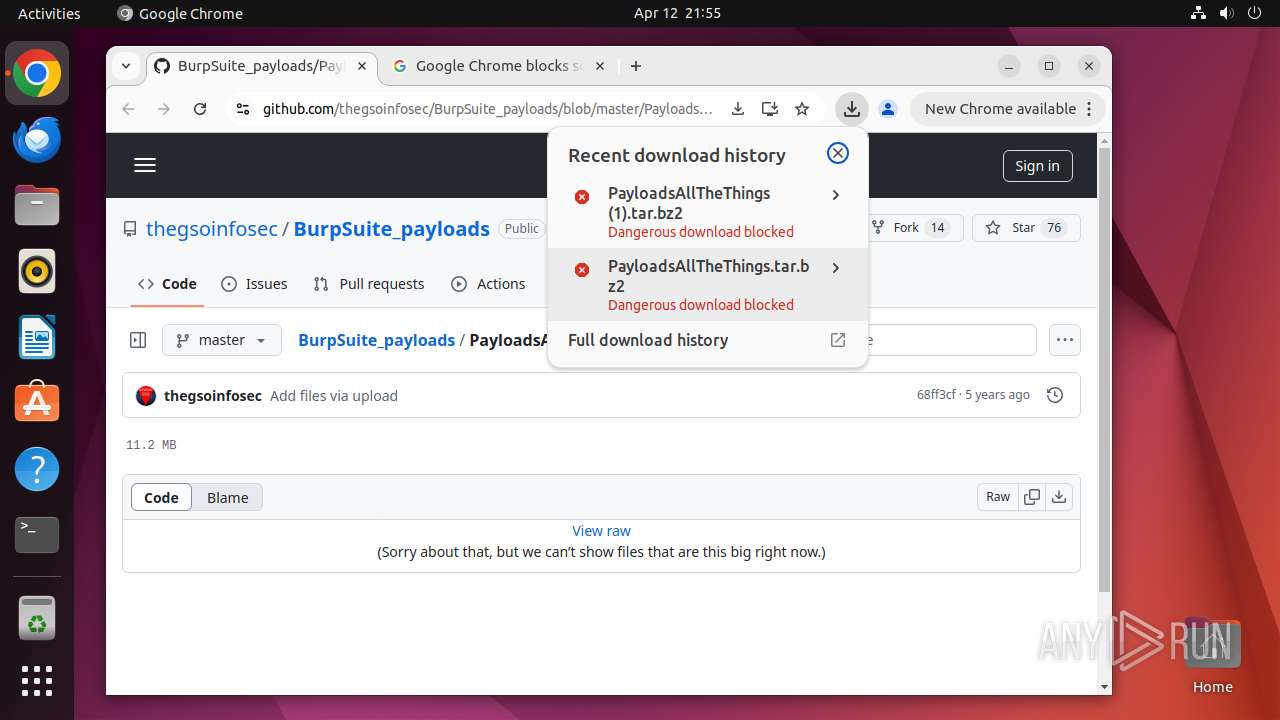
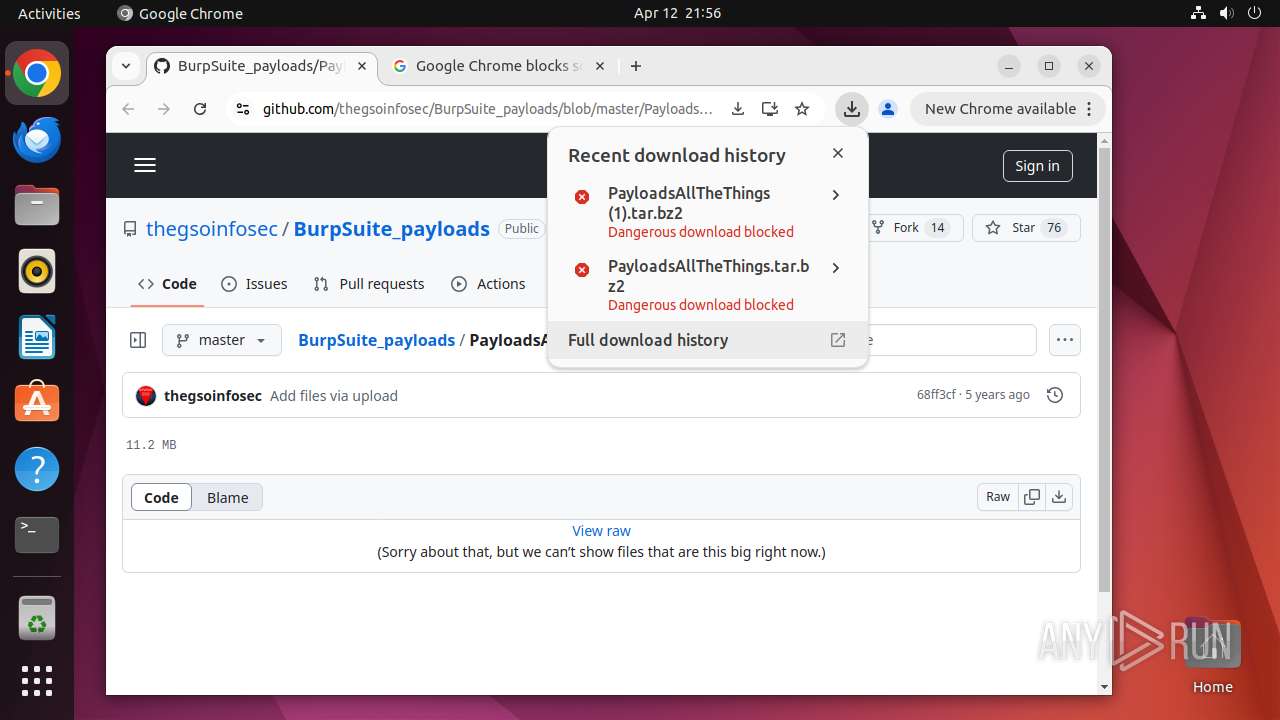
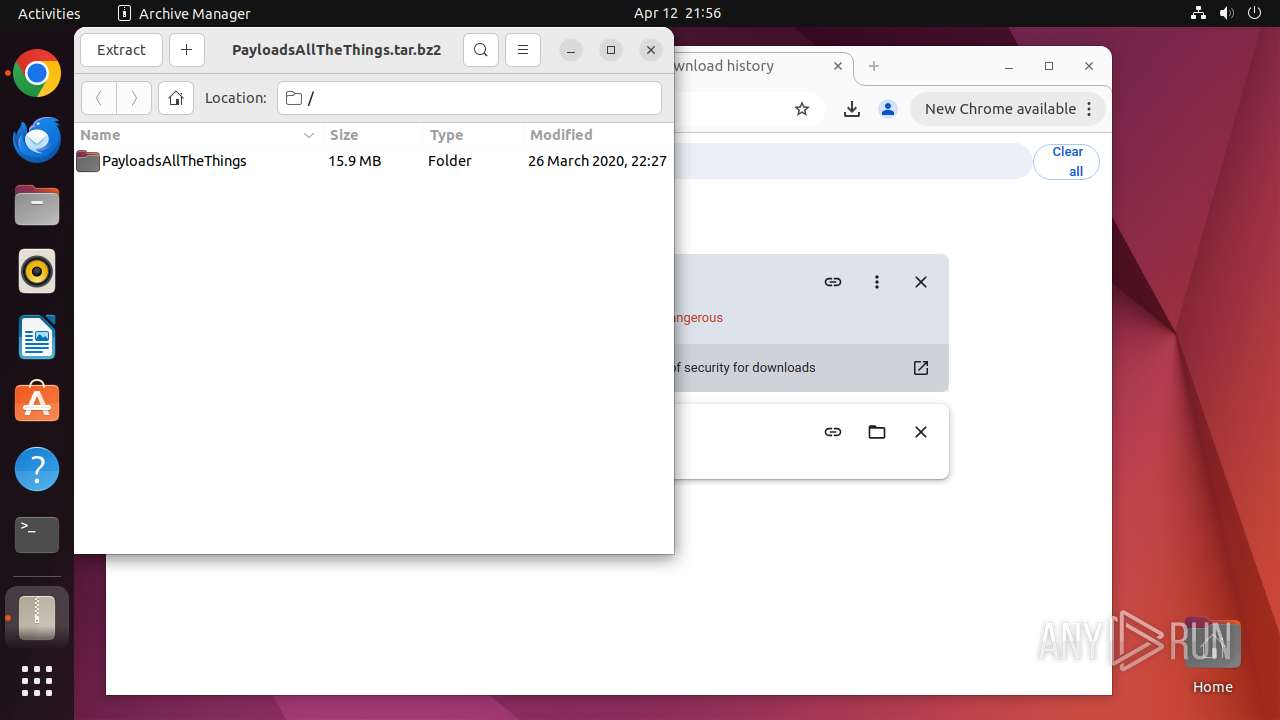
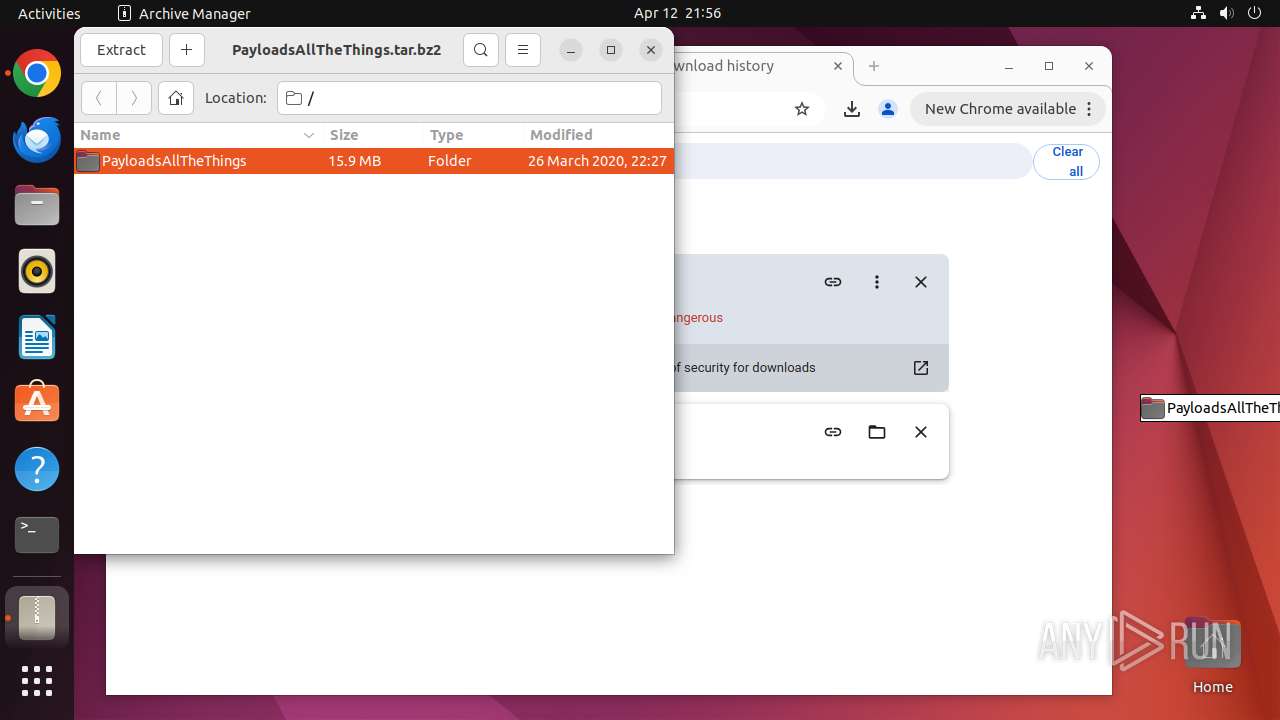
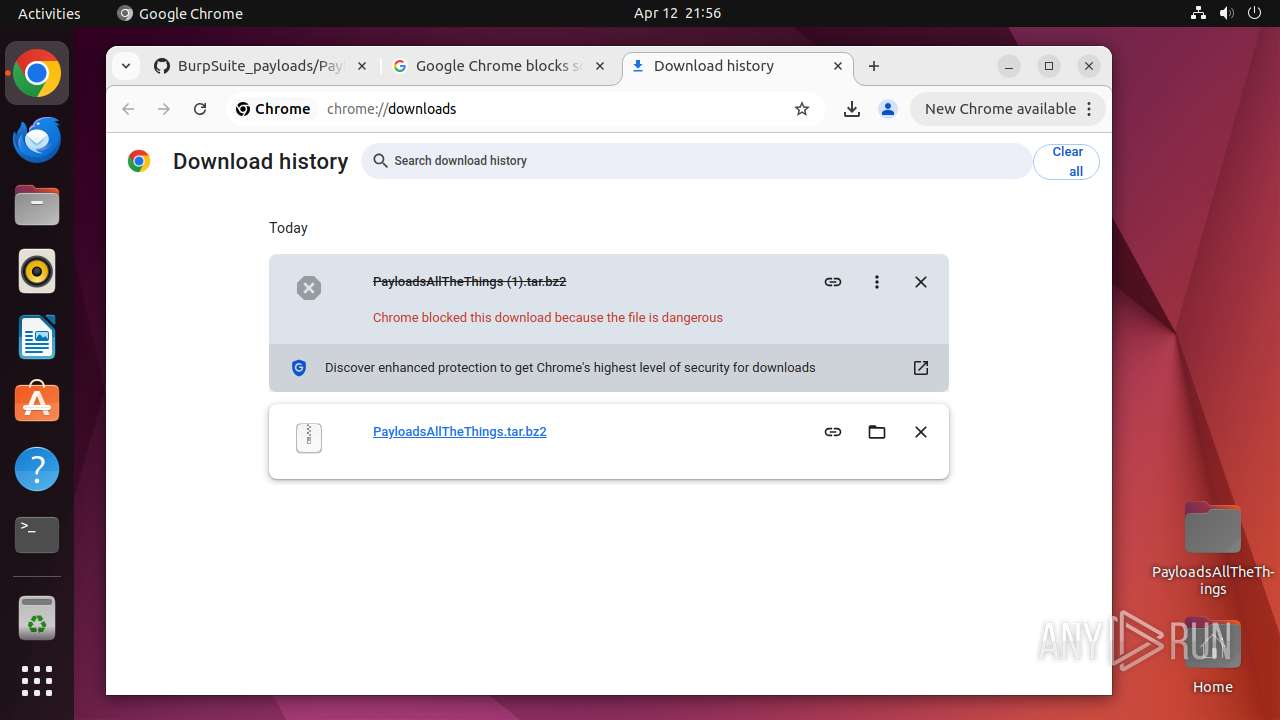
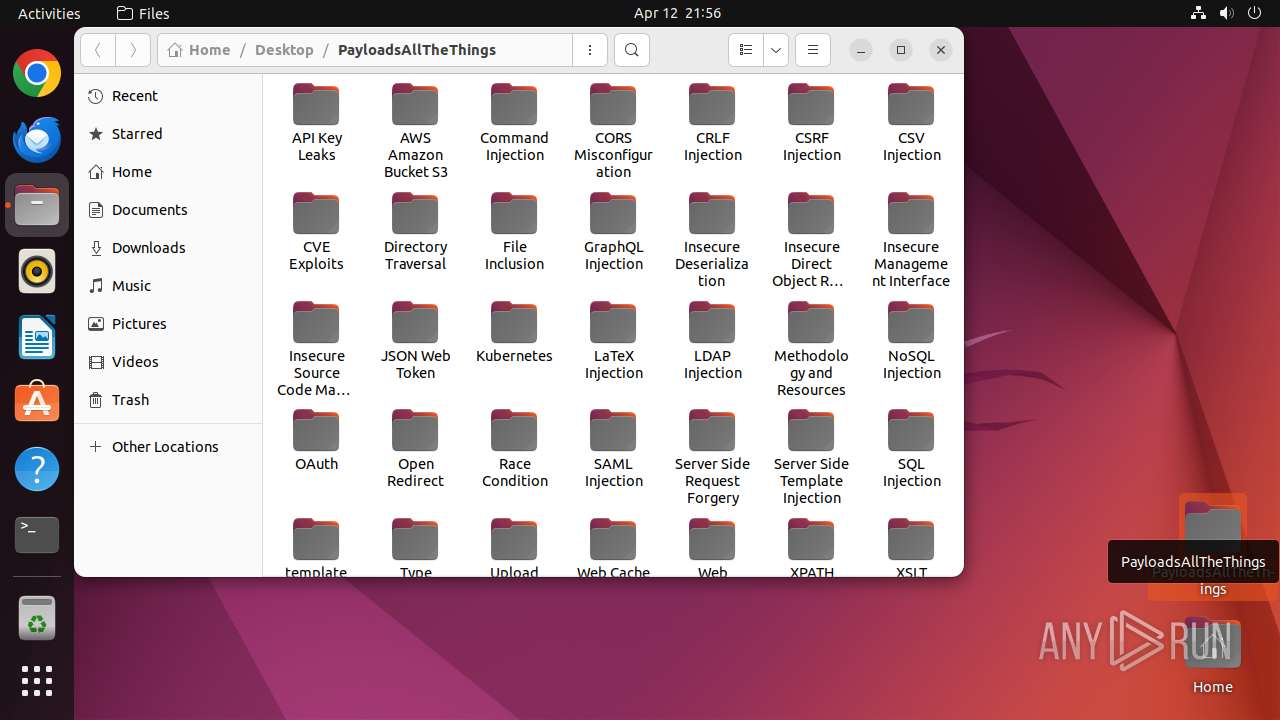
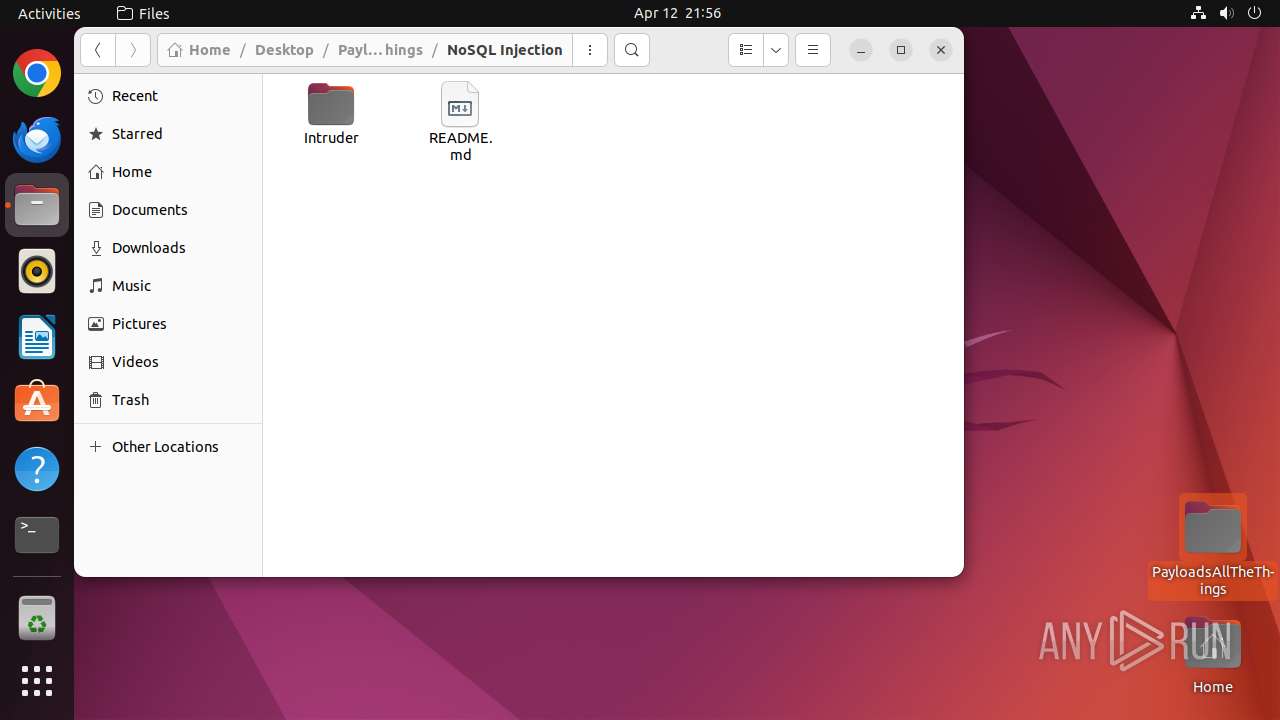
| URL: | https://github.com/thegsoinfosec/BurpSuite_payloads/blob/master/PayloadsAllTheThings.tar.bz2 |
| Full analysis: | https://app.any.run/tasks/140753c6-3b02-4058-80e1-b81f35ac0120 |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 20:55:13 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | F9AE7D1C92978A80907F100C4BCC10B6 |
| SHA1: | 6C6301ED6BEE7CB7B63392A8492AC4D8AEEE38FB |
| SHA256: | C6F8B20006520C3F18A06C65A0CB39888EA091F4FF1CC81E22AA92707E05451F |
| SSDEEP: | 3:N8tEdhNnWKnW1FgVDpwEHYPxCYyHfXn:2uhWKnW1Fh+ACYyH/n |
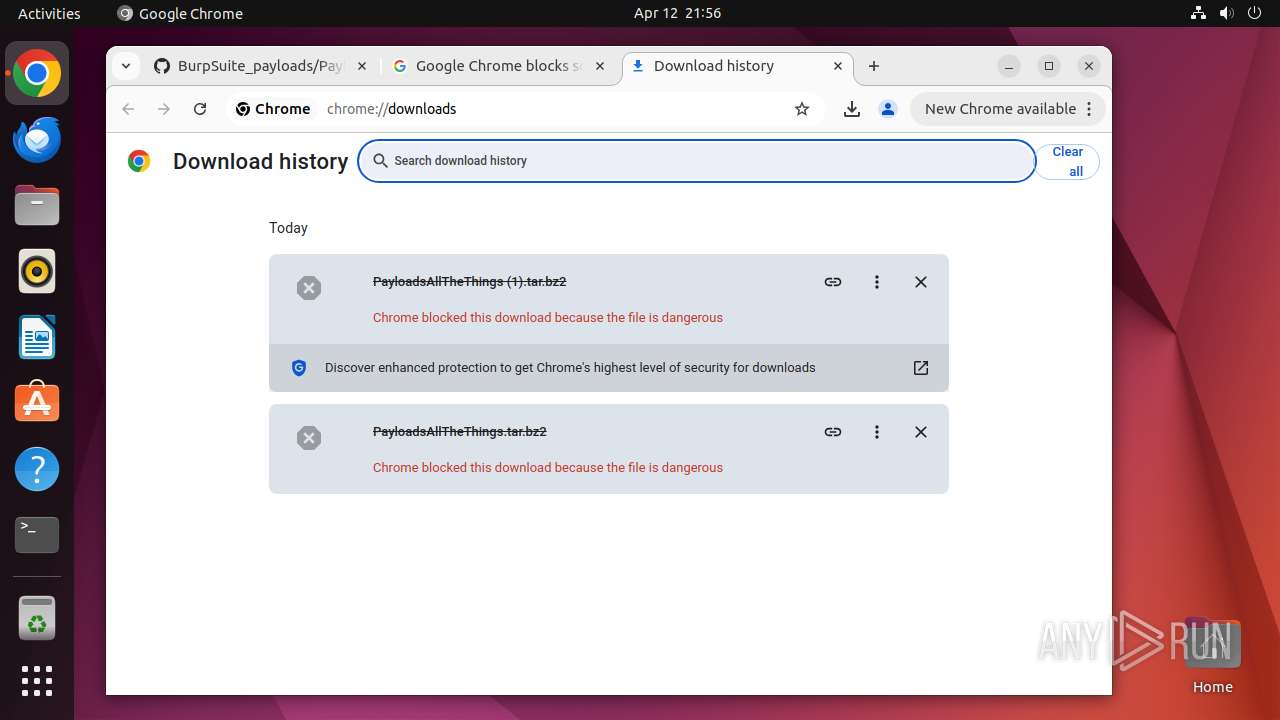
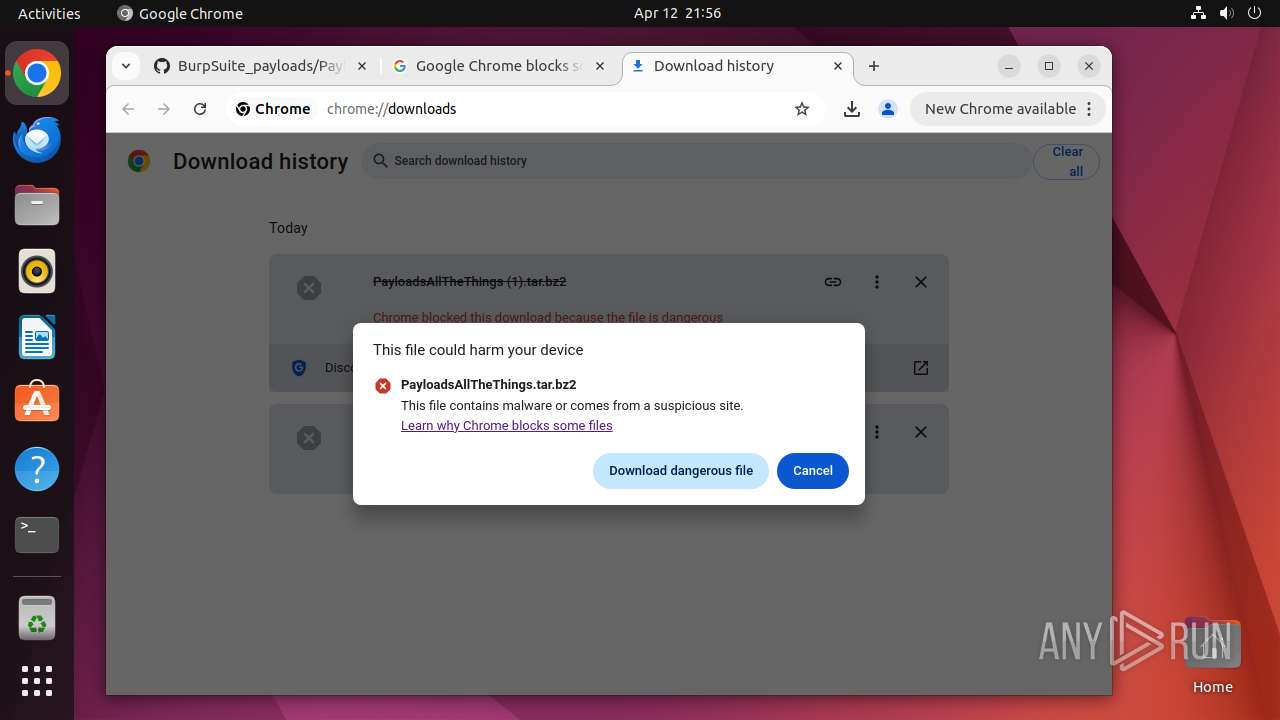
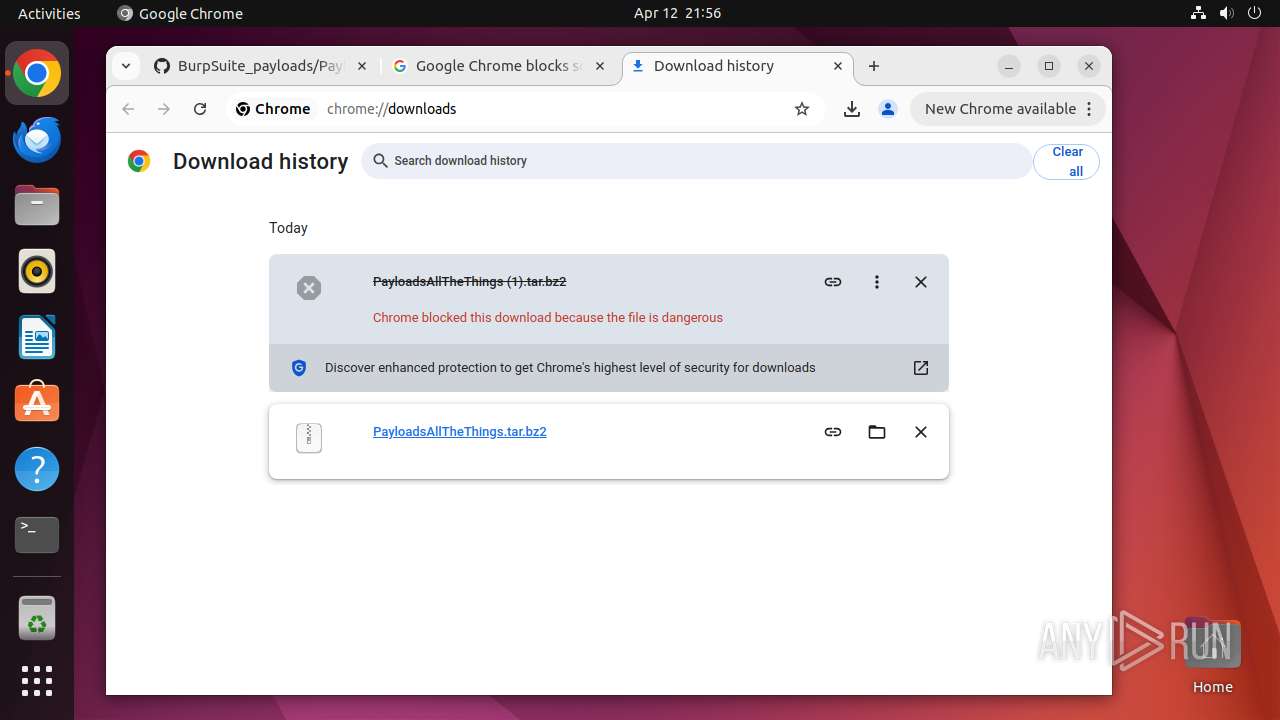
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 39500)
- chrome (PID: 39503)
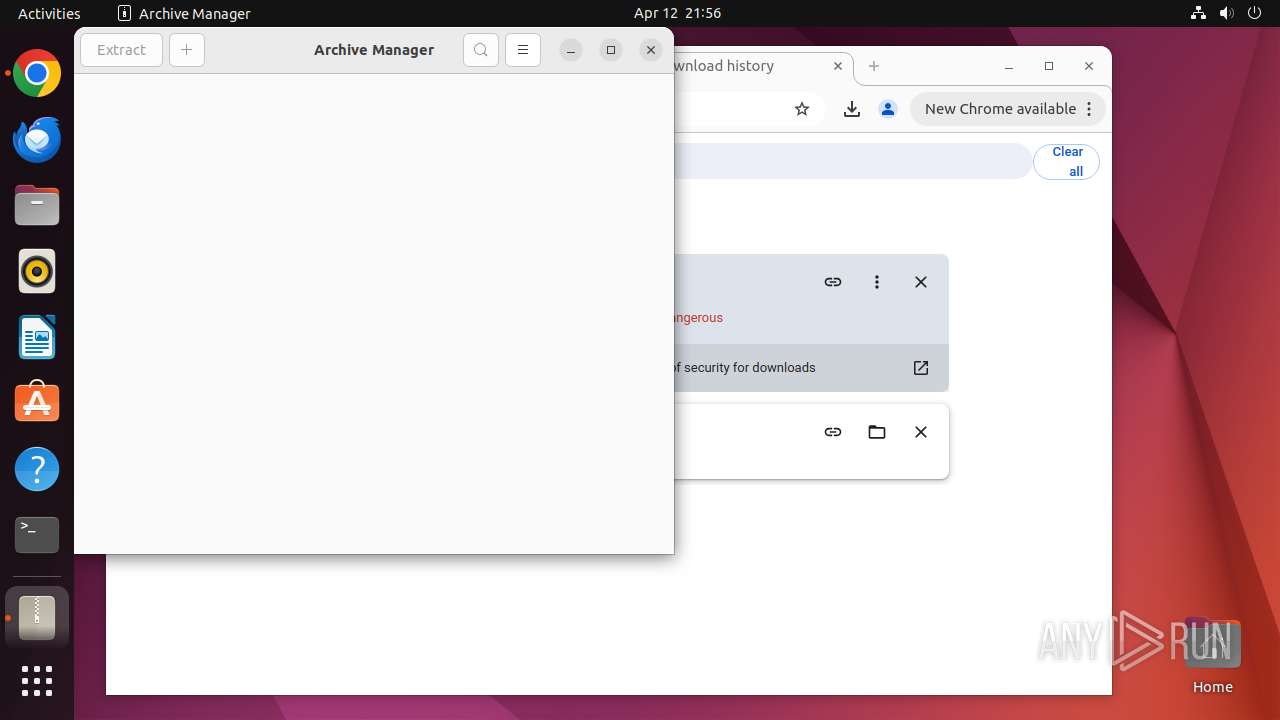
Creates shell script file
- file-roller (PID: 39811)
Reads passwd file
- file-roller (PID: 39811)
INFO
Checks timezone
- chrome (PID: 39503)
- file-roller (PID: 39811)
- tracker-extract-3 (PID: 39876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
336
Monitored processes
115
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 39498 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39499 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://github\.com/thegsoinfosec/BurpSuite_payloads/blob/master/PayloadsAllTheThings\.tar\.bz2 " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39500 | sudo -iu user google-chrome https://github.com/thegsoinfosec/BurpSuite_payloads/blob/master/PayloadsAllTheThings.tar.bz2 | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39501 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39502 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39503 | /usr/bin/google-chrome https://github.com/thegsoinfosec/BurpSuite_payloads/blob/master/PayloadsAllTheThings.tar.bz2 | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39504 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39505 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39506 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39507 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
2
Suspicious files
351
Text files
176
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39503 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39503 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39503 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39503 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39503 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39503 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39547 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39650 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39503 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 39503 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
82
DNS requests
82
Threats
114
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrovrpquemobbwthbstjwffhima_2025.1.17.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2025.01.17.01_all_dd5w5blqtgwb4xkyhfpmehllye.crx3 | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gikiajhx6vvdbwhrvbolvcybfm_499/lmelglejhemejginpboagddgdfbepgmp_499_all_ZZ_adtilvtzo6vcw6n4nqfq3oxd6zdq.crx3 | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aclxnidwwkj5di3vduduj2gqpgpq_4.10.2891.0/oimompecagnajdejgnnjijobebaeigek_4.10.2891.0_linux_b4hin3q5s66ws2322cyyfp35lu.crx3 | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpfsmx3jx54vc56xzsioflc3uiq_1283/efniojlnjndmcbiieegkicadnoecjjef_1283_all_oox2w4oahqh2damefcaxtqzrzu.crx3 | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/awrgx6b34mzyeczihbadhgnmjm_2025.4.11.1/jflhchccmppkfebkiaminageehmchikm_2025.04.11.01_all_pbamyfj5m6ue5vxb4eu7x5b64i.crx3 | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aczukimakiu3m7wr2zuaf2hwtara_9699/hfnkpimlhhgieaddgfemjhofmfblmnib_9699_all_ac4vcbjpkm626bopimdhiy3btzia.crx3 | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acozb2yc65v67toa3og2plxnuygq_20250315.743742949.14/obedbbhbpmojnkanicioggnmelmoomoc_20250315.743742949.14_all_ENGB500000_acy3hxc7mgf7hs45wwrp7osblgla.crx3 | unknown | — | — | whitelisted |
39549 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad75b3l6ifzhds2shjkt4plki3la_2025.4.9.0/niikhdgajlphfehepabhhblakbdgeefj_2025.04.09.00_all_npvw54ukij2olp3ypwysvazhva.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 37.19.194.81:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
39549 | chrome | 216.58.206.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
39549 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39549 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39549 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39549 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39549 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
39549 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39549 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39549 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |