| File name: | c6f066035c64a1309d1d958b6536882847da51f2eb5cebe670b05bbdd97c12d1 |
| Full analysis: | https://app.any.run/tasks/fe17b636-3a35-4728-b6f7-3043b063760d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 01, 2020, 19:05:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
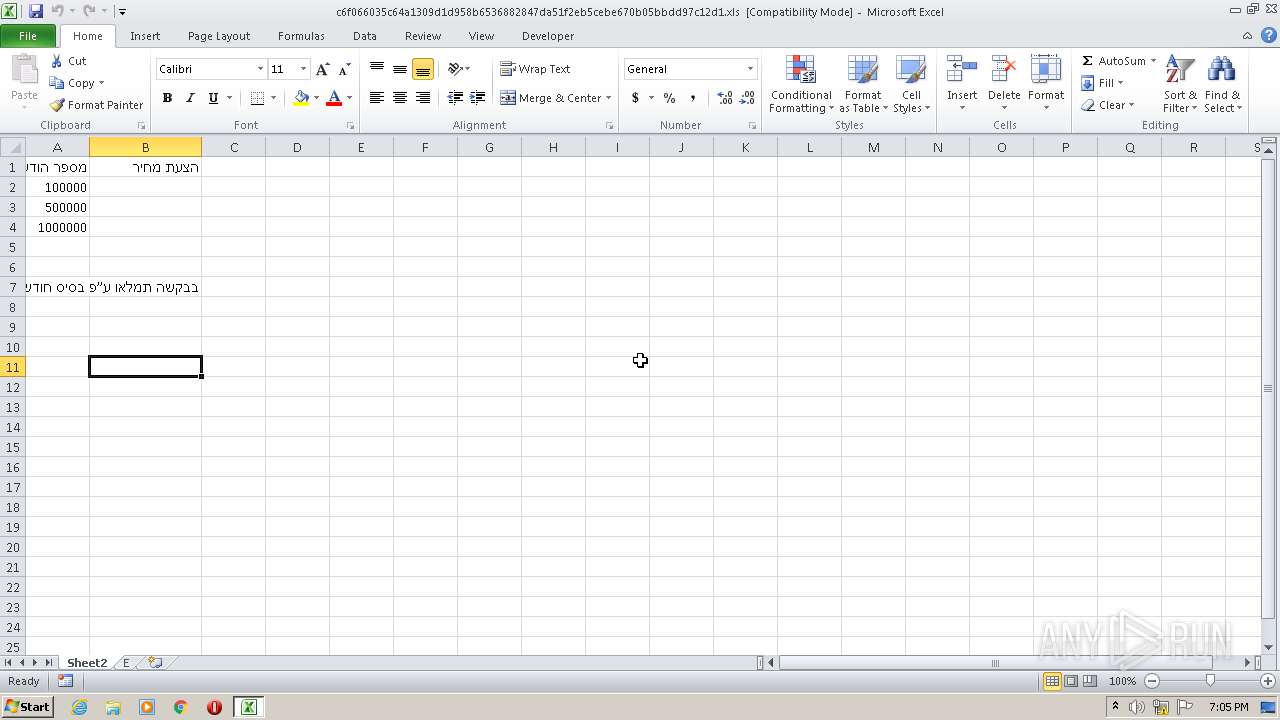
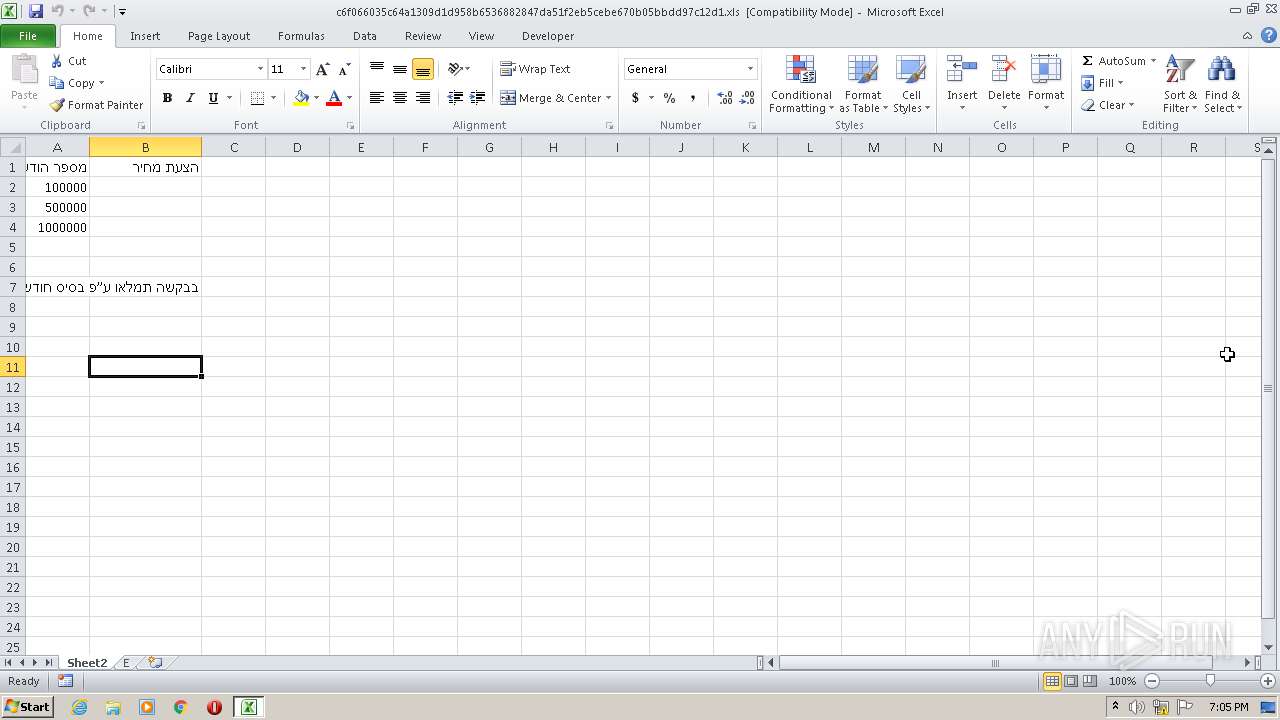
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: DrMDtHRzznZBX, Last Saved By: fckav, Name of Creating Application: Microsoft Excel, Create Time/Date: Mon Jun 22 19:07:27 2020, Last Saved Time/Date: Wed Oct 14 12:47:11 2020, Security: 0 |
| MD5: | 332F8351C92D72260846A9F8B5FDD7CB |
| SHA1: | 1B924898977E10900EAFCD655E282AE49BB476C1 |
| SHA256: | C6F066035C64A1309D1D958B6536882847DA51F2EB5CEBE670B05BBDD97C12D1 |
| SSDEEP: | 1536:7Yk3hbdlylKsgqopeJBWhZFGkE+cL2NdAomrUq/r4lDCUw5l64bycklZhVCeBq1V:7Yk3hbdlylKsgqopeJBWhZFGkE+cL2Nj |
MALICIOUS
Loads dropped or rewritten executable
- LJDVSoK.exe (PID: 2752)
Writes to a start menu file
- LJDVSoK.exe (PID: 2752)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 1788)
Application was dropped or rewritten from another process
- LJDVSoK.exe (PID: 2752)
NETWIRE was detected
- LJDVSoK.exe (PID: 2752)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1788)
SUSPICIOUS
Creates files in the user directory
- LJDVSoK.exe (PID: 2752)
Executable content was dropped or overwritten
- LJDVSoK.exe (PID: 2752)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1788)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 1788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | DrMDtHRzznZBX |
|---|---|
| LastModifiedBy: | fckav |
| Software: | Microsoft Excel |
| CreateDate: | 2020:06:22 18:07:27 |
| ModifyDate: | 2020:10:14 11:47:11 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
36
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1788 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2752 | "C:\jokwzPk\luFzdsM\LJDVSoK.exe" | C:\jokwzPk\luFzdsM\LJDVSoK.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Nevada Graph company Integrity Level: MEDIUM Description: Nevada Graph Application Exit code: 0 Version: 1.2.4 Modules
| |||||||||||||||
Total events
936
Read events
870
Write events
55
Delete events
11
Modification events
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | p#6 |
Value: 70233600FC060000010000000000000000000000 | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1788) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
3
Suspicious files
4
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1788 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR3FC0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1788 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Cab4B89.tmp | — | |
MD5:— | SHA256:— | |||
| 1788 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Tar4B8A.tmp | — | |
MD5:— | SHA256:— | |||
| 2752 | LJDVSoK.exe | C:\Users\admin\AppData\Local\Temp\fdsdf | — | |
MD5:— | SHA256:— | |||
| 2752 | LJDVSoK.exe | C:\Users\admin\AppData\Local\Temp\nnffdn.png | image | |
MD5:— | SHA256:— | |||
| 1788 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\2019[1].png | executable | |
MD5:— | SHA256:— | |||
| 1788 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 1788 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 2752 | LJDVSoK.exe | C:\Users\admin\AppData\Local\Temp\nsg4ED6.tmp\System.dll | executable | |
MD5:8CF2AC271D7679B1D68EEFC1AE0C5618 | SHA256:6950991102462D84FDC0E3B0AE30C95AF8C192F77CE3D78E8D54E6B22F7C09BA | |||
| 1788 | EXCEL.EXE | C:\jokwzPk\luFzdsM\LJDVSoK.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
959
DNS requests
5
Threats
1 910
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1788 | EXCEL.EXE | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
1788 | EXCEL.EXE | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgRwY0accMWhlW7PTdQZAscz%2Bg%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1788 | EXCEL.EXE | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
1788 | EXCEL.EXE | 2.16.186.27:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
— | — | 89.39.107.244:443 | — | WorldStream B.V. | NL | malicious |
2752 | LJDVSoK.exe | 89.39.107.244:443 | — | WorldStream B.V. | NL | malicious |
1788 | EXCEL.EXE | 87.98.154.146:443 | 17-14.com | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
17-14.com |
| malicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | LJDVSoK.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore/NetWire/Kovter |
2752 | LJDVSoK.exe | A Network Trojan was detected | MALWARE [PTsecurity] Netwire.RAT |
2752 | LJDVSoK.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore/NetWire/Kovter |
2752 | LJDVSoK.exe | A Network Trojan was detected | MALWARE [PTsecurity] Netwire.RAT |
2752 | LJDVSoK.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore/NetWire/Kovter |
2752 | LJDVSoK.exe | A Network Trojan was detected | MALWARE [PTsecurity] Netwire.RAT |
2752 | LJDVSoK.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore/NetWire/Kovter |
2752 | LJDVSoK.exe | A Network Trojan was detected | MALWARE [PTsecurity] Netwire.RAT |
2752 | LJDVSoK.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore/NetWire/Kovter |
2752 | LJDVSoK.exe | A Network Trojan was detected | MALWARE [PTsecurity] Netwire.RAT |