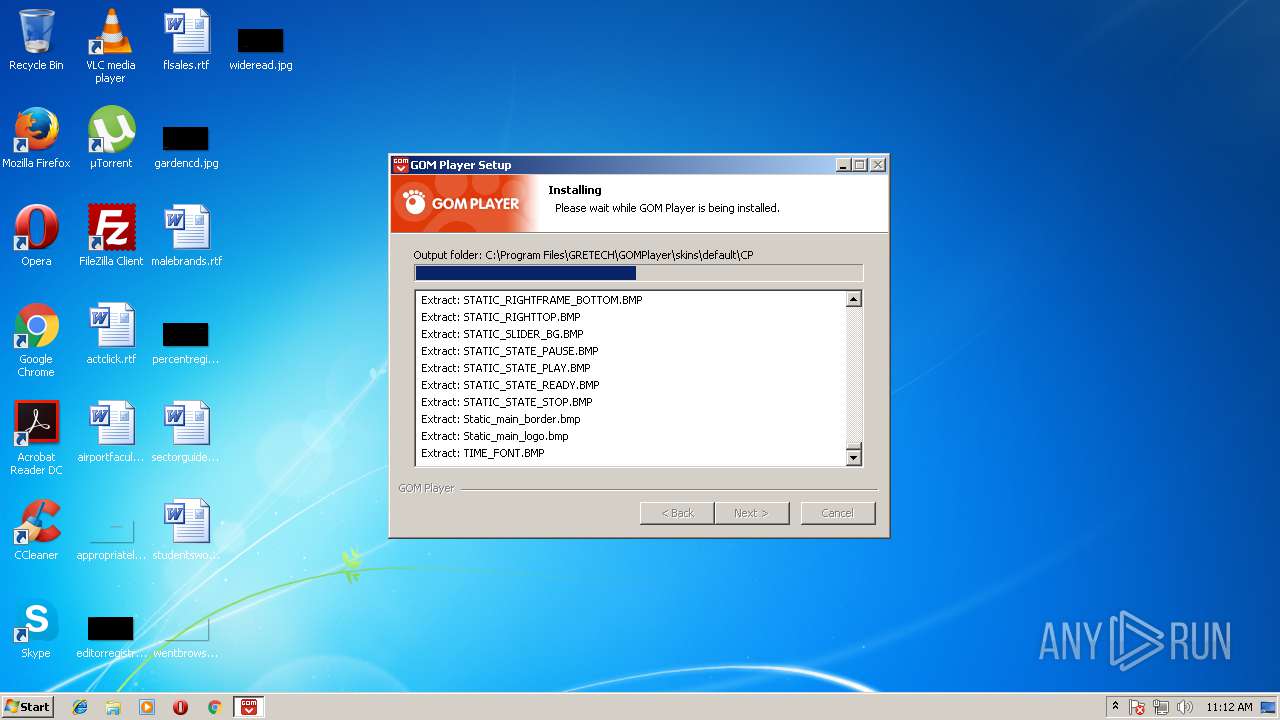
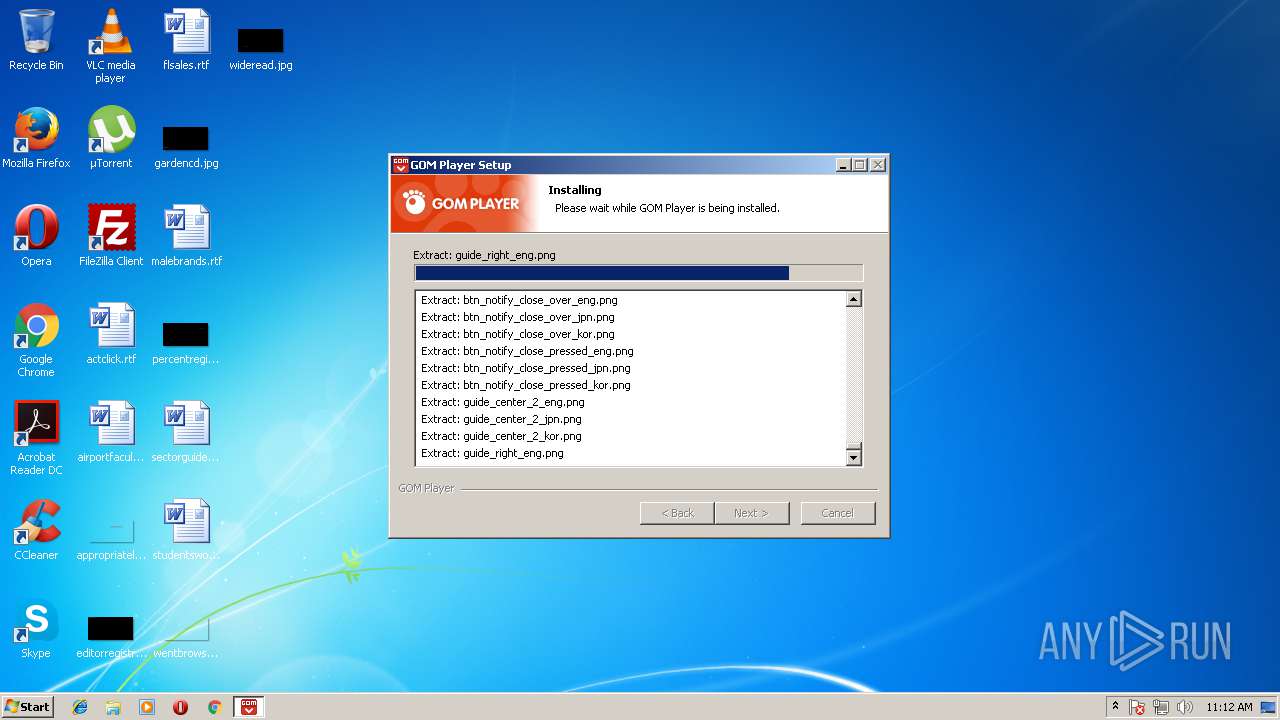
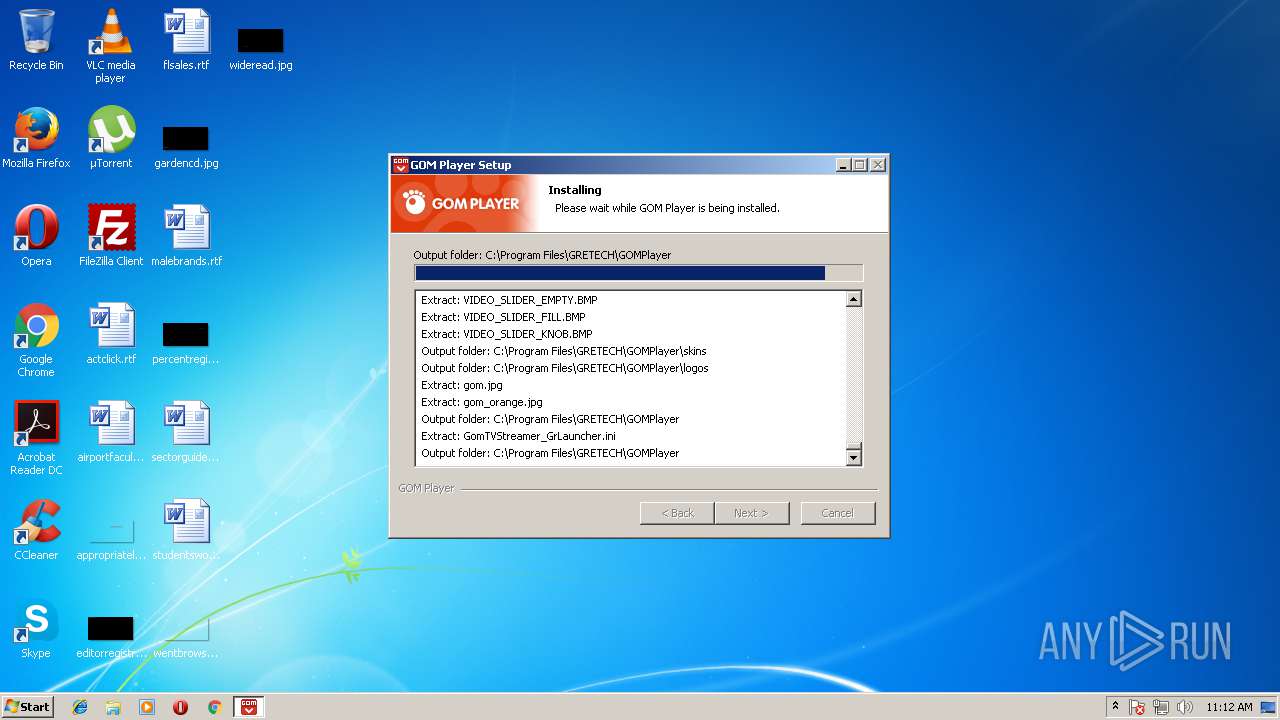
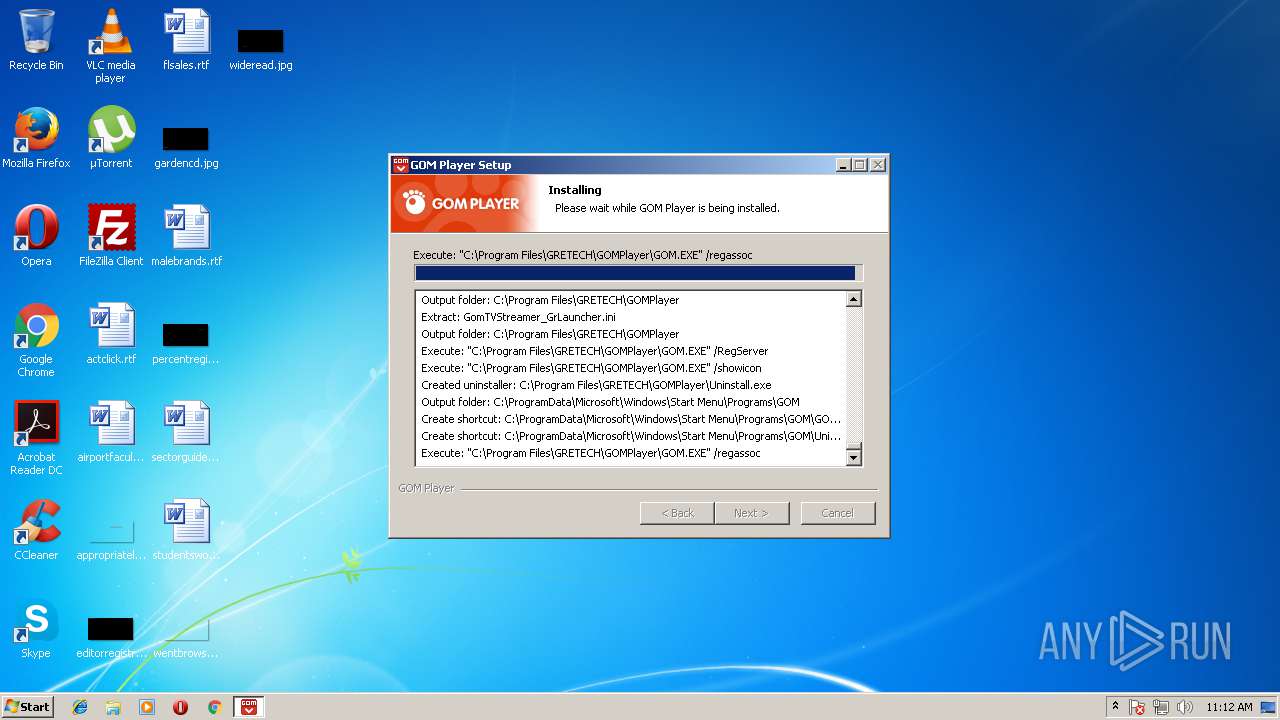
| download: | GOMPLAYERGLOBALSETUP.EXE |
| Full analysis: | https://app.any.run/tasks/e6223564-256c-4111-9c59-9afc685a03e4 |
| Verdict: | Malicious activity |
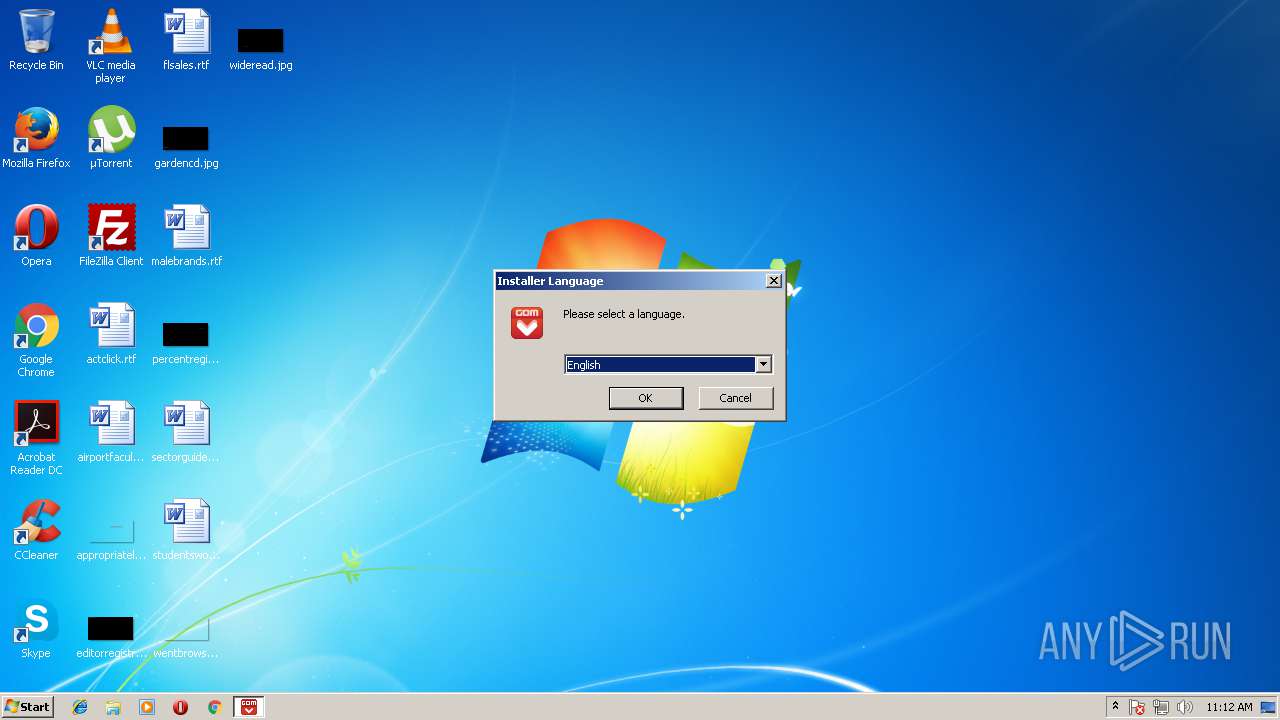
| Analysis date: | May 14, 2018, 10:11:30 |
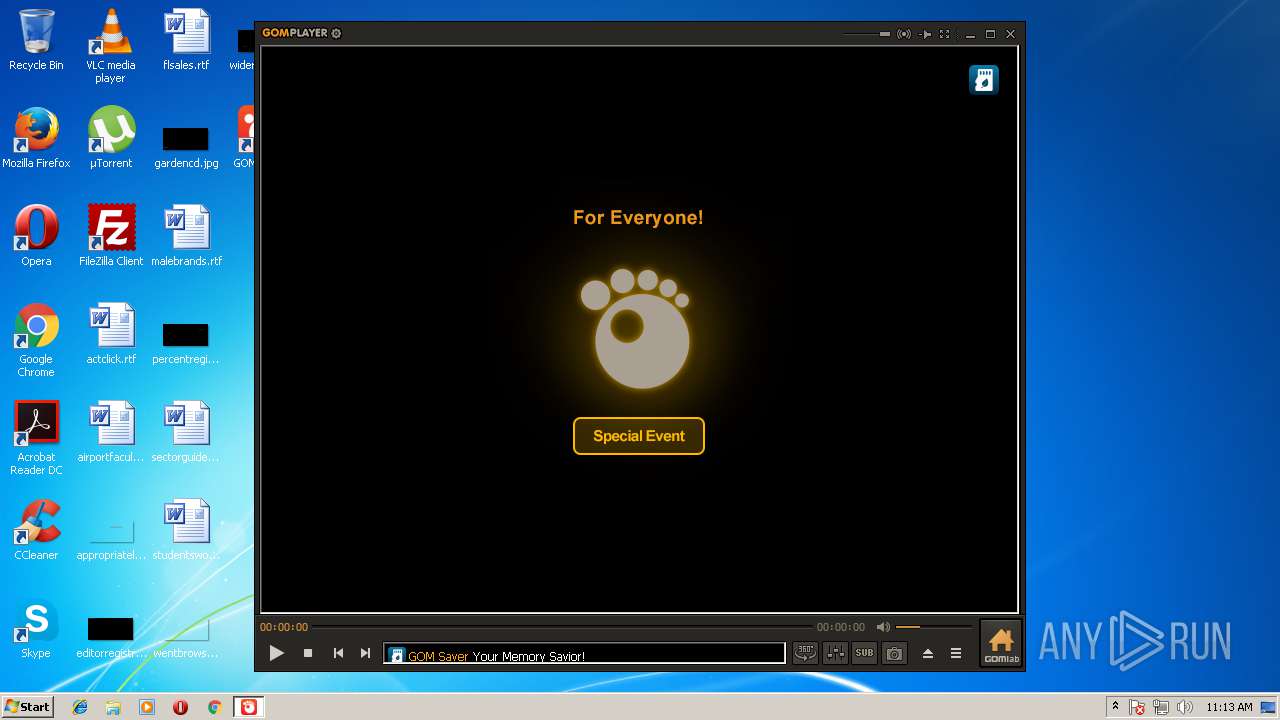
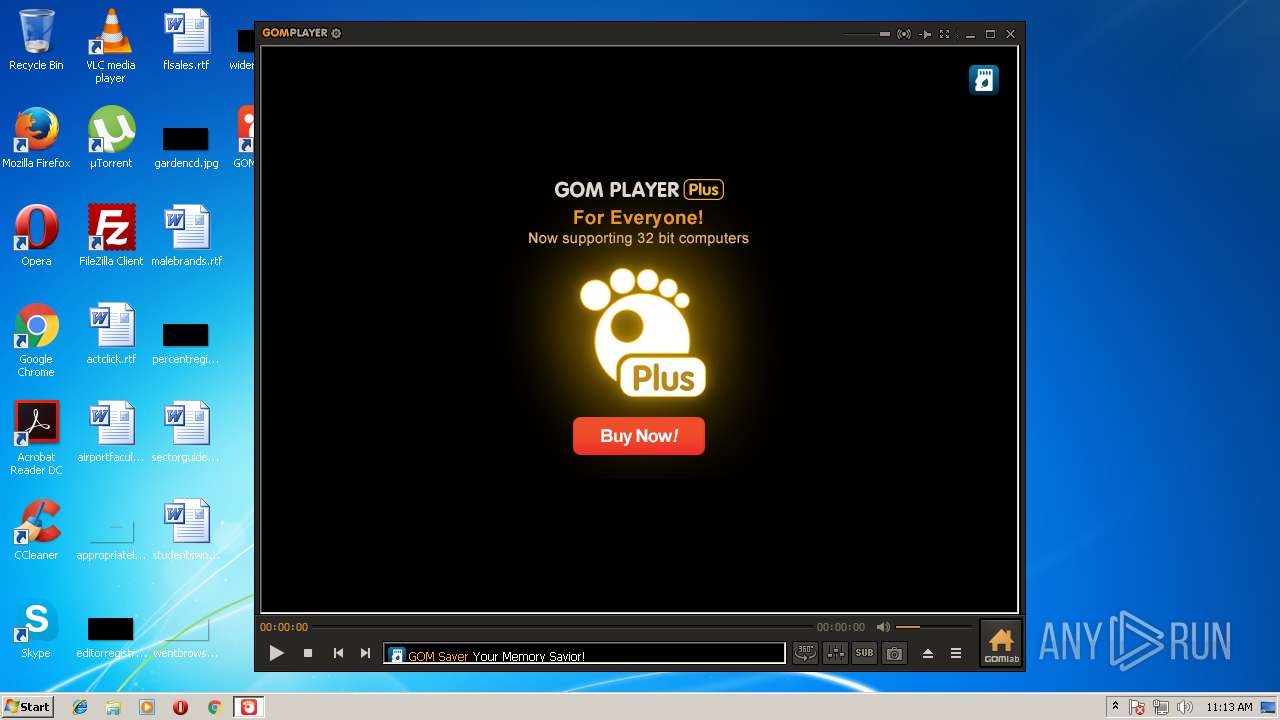
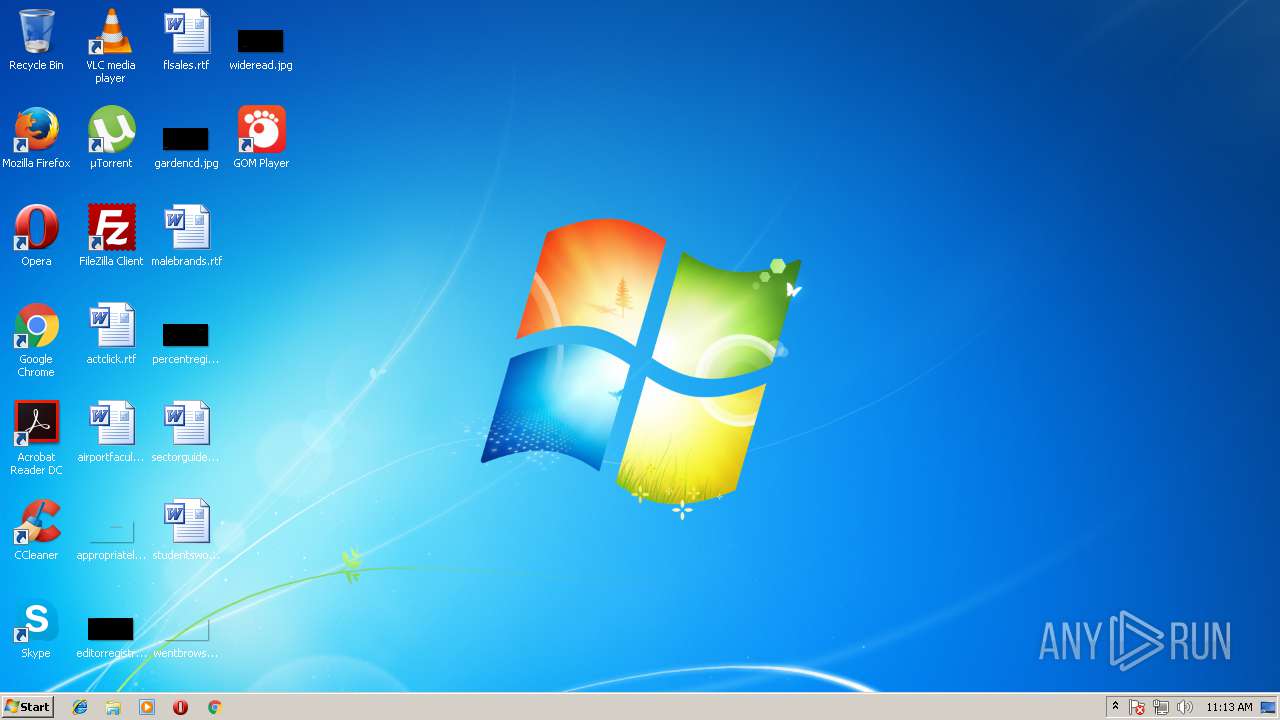
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D49B982B0BA6359FFFA30F06215A7FF9 |
| SHA1: | 94667AB780E77591498E21374F5F88A131530948 |
| SHA256: | C6E07A14F86281509583CB2C6127E0DD868D2514B9D0F84AF6B06417CDCFECA1 |
| SSDEEP: | 393216:dp3EF6VeKI8e93zpRzDdpVdIvhLe0ui7ibYTTIUZPyohhXmaq4Oim9T+qaHRbI6F:dZs6VePnBZ27i0/IGliKemRbxZNTm/Y3 |
MALICIOUS
Application loaded dropped or rewritten executable
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
- GOM.EXE (PID: 2772)
- GOM.EXE (PID: 1204)
- GOM.EXE (PID: 2148)
- DllHost.exe (PID: 2796)
- DllHost.exe (PID: 2764)
- GOM.EXE (PID: 2392)
- svchost.exe (PID: 692)
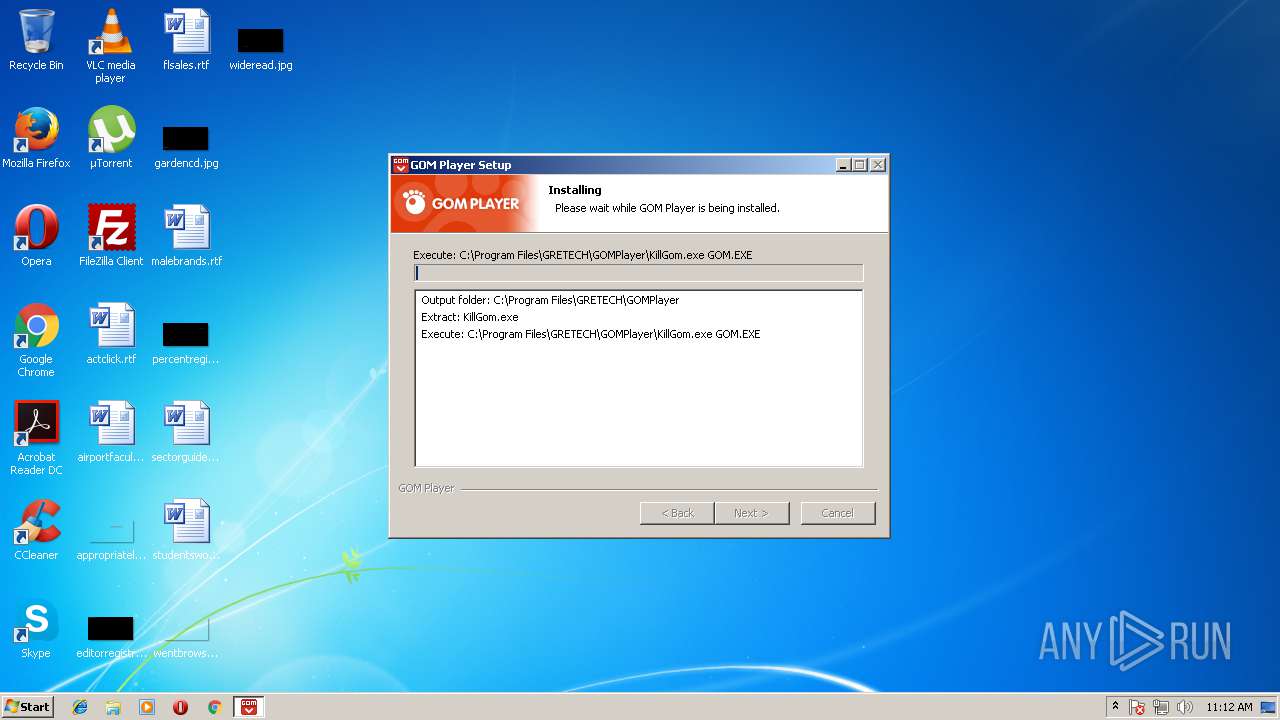
Application was dropped or rewritten from another process
- KillGom.exe (PID: 2004)
- KillGom.exe (PID: 348)
- GOM.EXE (PID: 2772)
- GOM.EXE (PID: 2148)
- GrLauncher.exe (PID: 2724)
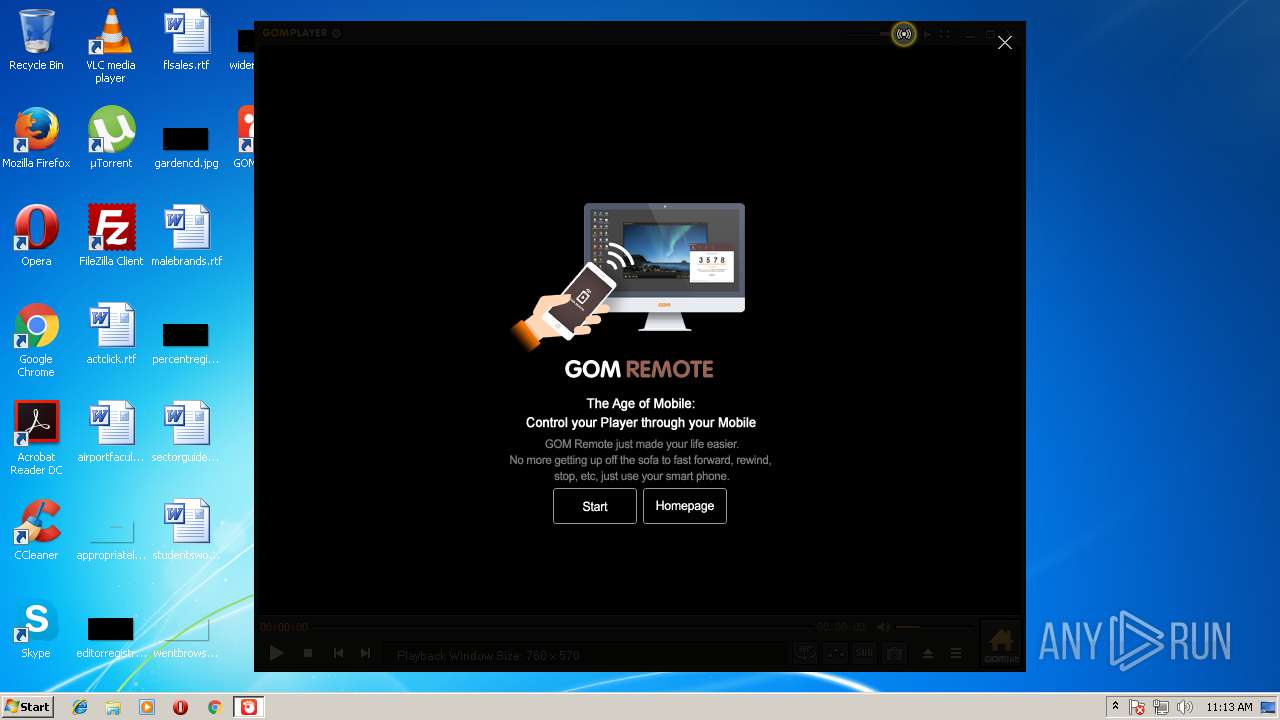
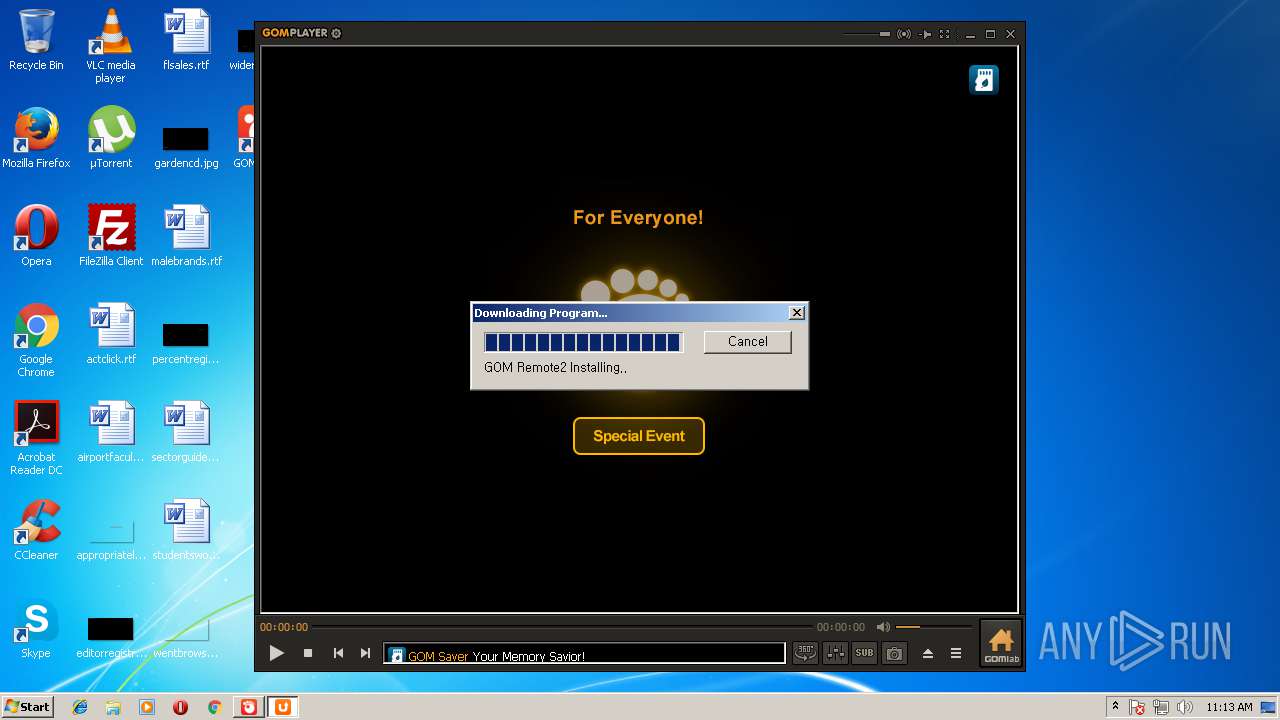
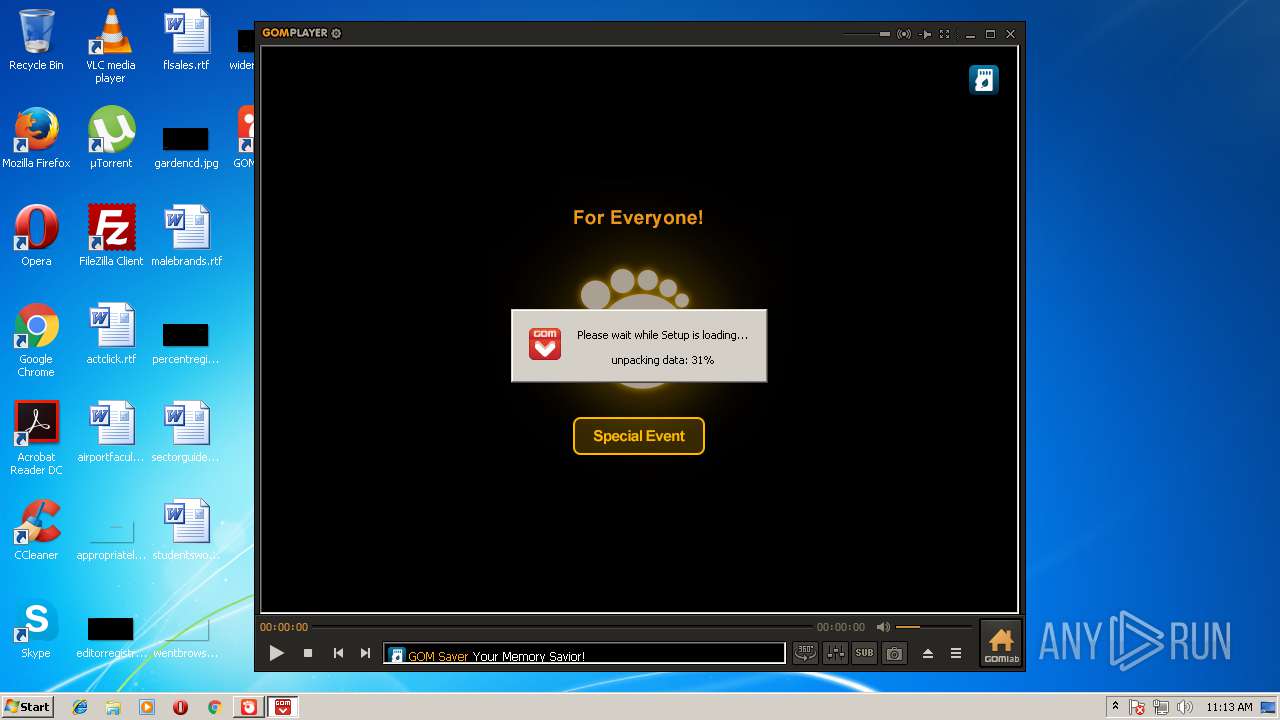
- GOMREMOTETRAYSETUP.EXE (PID: 2960)
- GrLauncher.exe (PID: 980)
- GOM.EXE (PID: 1204)
- GOMREMOTETRAYSETUP.EXE (PID: 3020)
- popup.exe (PID: 2132)
- GOM.EXE (PID: 2392)
SUSPICIOUS
Modifies the open verb of a shell class
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
- GOM.EXE (PID: 2772)
- GOM.EXE (PID: 1204)
- DllHost.exe (PID: 2764)
- GOM.EXE (PID: 2148)
Creates COM task schedule object
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
Creates a software uninstall entry
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
Changes IE settings (feature browser emulation)
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
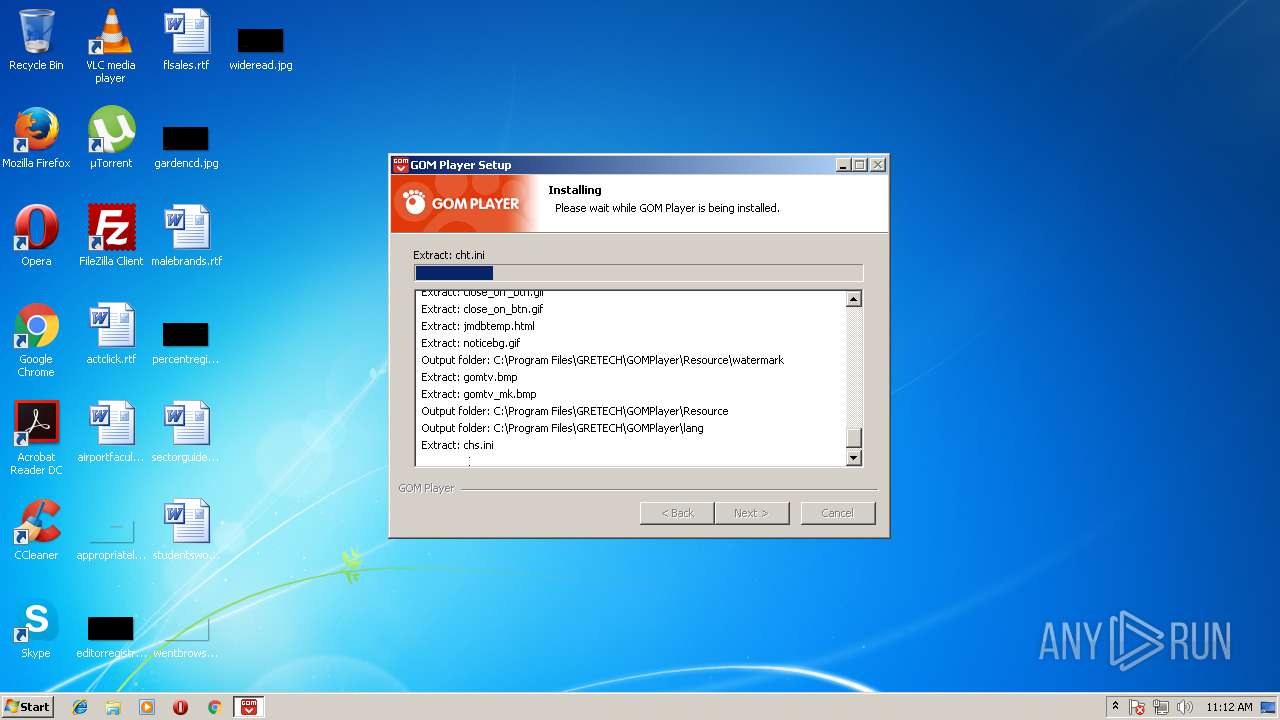
Executable content was dropped or overwritten
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
- GOMREMOTETRAYSETUP.EXE (PID: 3020)
- GrLauncher.exe (PID: 980)
Creates files in the user directory
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
- GOM.EXE (PID: 2392)
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 1024)
- popup.exe (PID: 2132)
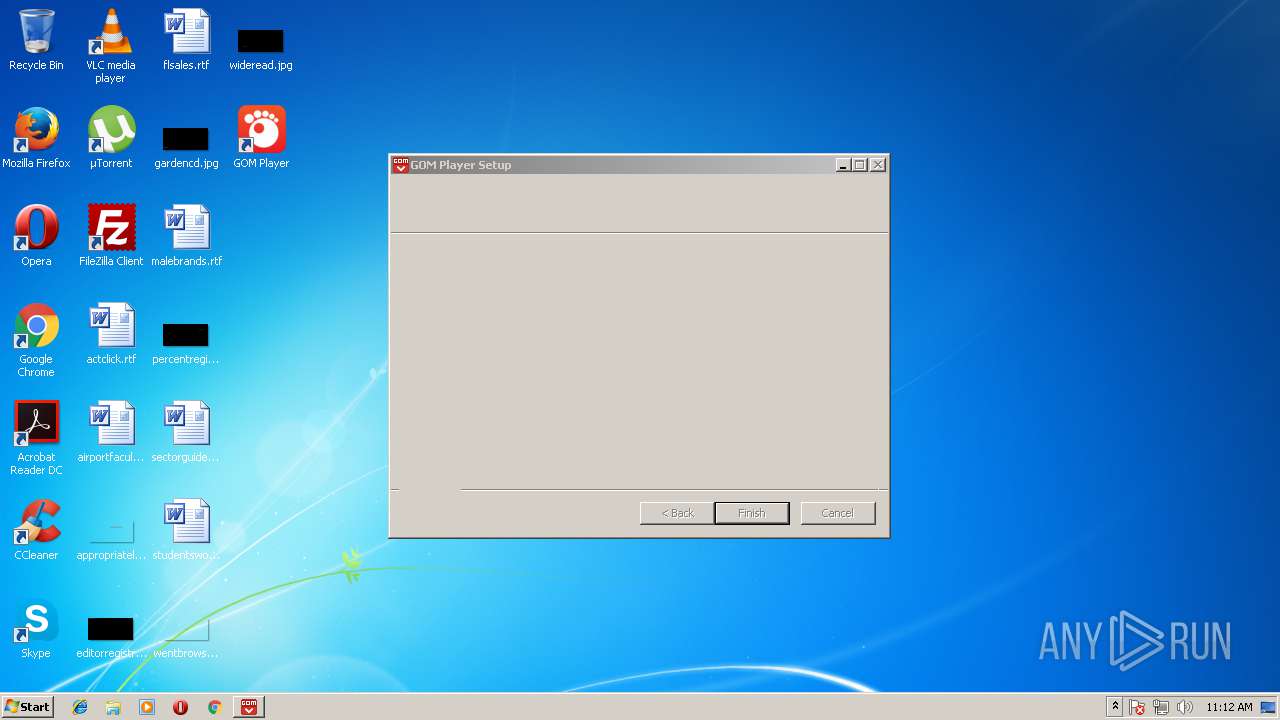
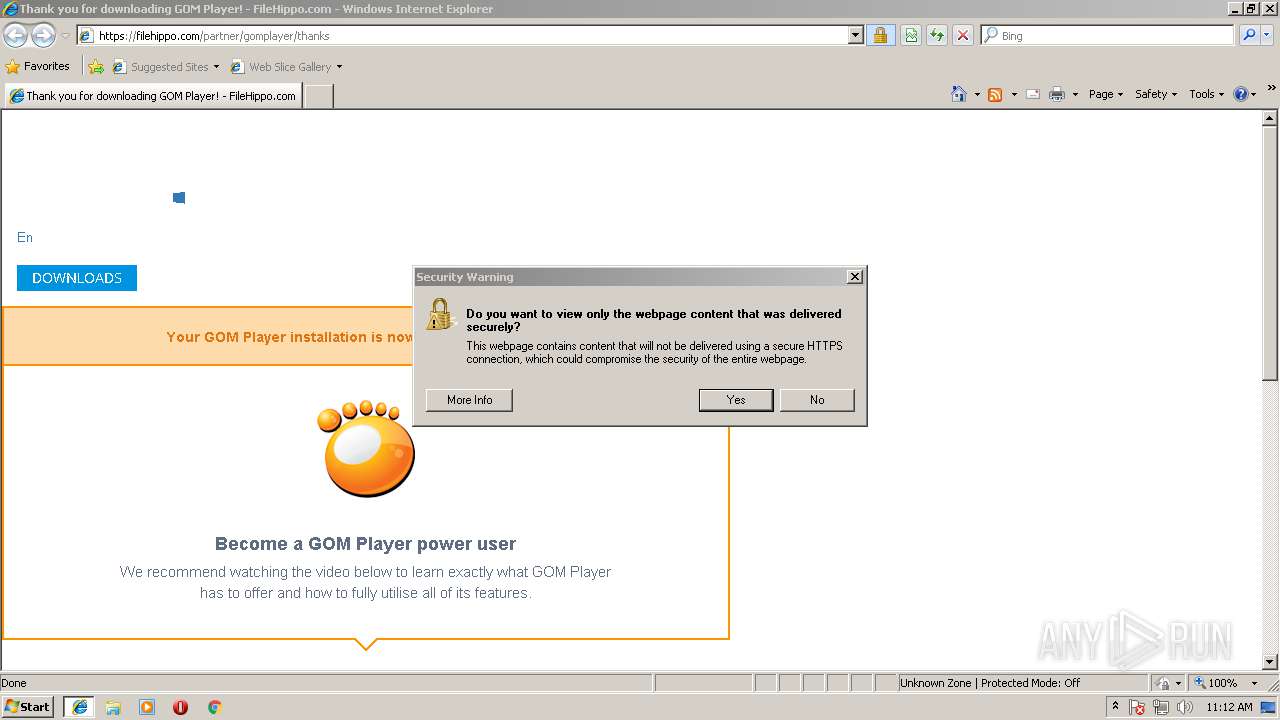
Starts Internet Explorer
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
- GOM.EXE (PID: 2392)
Creates files in the program directory
- GOM.EXE (PID: 2392)
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
- GrLauncher.exe (PID: 980)
- GrLauncher.exe (PID: 2724)
Reads internet explorer settings
- GOM.EXE (PID: 2392)
- popup.exe (PID: 2132)
Reads Internet Cache Settings
- popup.exe (PID: 2132)
INFO
Dropped object may contain Bitcoin addresses
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
- iexplore.exe (PID: 2460)
Changes internet zones settings
- iexplore.exe (PID: 2208)
- iexplore.exe (PID: 1452)
Creates files in the user directory
- iexplore.exe (PID: 3688)
- iexplore.exe (PID: 2460)
Reads internet explorer settings
- iexplore.exe (PID: 3688)
- iexplore.exe (PID: 2460)
Dropped object may contain URL's
- iexplore.exe (PID: 2208)
- GOM.EXE (PID: 2392)
- GrLauncher.exe (PID: 2724)
- GrLauncher.exe (PID: 980)
- GOMPLAYERGLOBALSETUP.EXE (PID: 2344)
- iexplore.exe (PID: 1452)
- popup.exe (PID: 2132)
- iexplore.exe (PID: 3688)
- iexplore.exe (PID: 2460)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3688)
Reads Internet Cache Settings
- iexplore.exe (PID: 2460)
Changes settings of System certificates
- iexplore.exe (PID: 3688)
Reads settings of System Certificates
- iexplore.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:25 02:55:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x33b6 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.29.5288 |
| ProductVersionNumber: | 2.3.29.5288 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Traditional) |
| CharacterSet: | Windows, Taiwan (Big5) |
| Comments: | GOM Player Setup File (2018-05-02 16:05:55) |
| CompanyName: | GOM & Company |
| FileDescription: | GOM Player Setup File |
| FileVersion: | 2.3 |
| LegalCopyright: | Copyright 2003 GOM & Company All Rights Reserved. |
| ProductName: | GOM Player |
| ProductVersion: | 2.3.29.5288 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jul-2016 00:55:51 |
| Detected languages: |
|
| Comments: | GOM Player Setup File (2018-05-02 16:05:55) |
| CompanyName: | GOM & Company |
| FileDescription: | GOM Player Setup File |
| FileVersion: | 2.3 |
| LegalCopyright: | Copyright 2003 GOM & Company All Rights Reserved. |
| ProductName: | GOM Player |
| ProductVersion: | 2.3.29.5288 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Jul-2016 00:55:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000615D | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45023 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9824 |
.ndata | 0x0002B000 | 0x00021000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0004C000 | 0x00014240 | 0x00014400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.51852 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28717 | 1069 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.20381 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.33645 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 6.26009 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.61626 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 6.51448 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 6.56152 | 1736 | UNKNOWN | English - United States | RT_ICON |
8 | 5.96078 | 1384 | UNKNOWN | English - United States | RT_ICON |
9 | 3.29788 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
63
Monitored processes
21
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\GRETECH\GOMPlayer\KillGom.exe" popup.EXE | C:\Program Files\GRETECH\GOMPlayer\KillGom.exe | — | GOMPLAYERGLOBALSETUP.EXE | |||||||||||
User: admin Company: GOM & Company Integrity Level: HIGH Description: Kill GOM Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 692 | C:\Windows\system32\svchost.exe -k RPCSS | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | "C:\Program Files\GRETECH\GOMPlayer\GrLauncher.exe" "<GRLAUNCHER_PARAM Command='forceinstall' Lang='eng' AgentName='GOMPlayer 2, 3, 29, 5288 (ENG)' ProgramID='GOMREMOTE2' SilentMessage='1' AutoInstall='0' ForceCheck='1' IniFileName='C:\Users\admin\AppData\Roaming\GRETECH\GOMPlayer\gomremote2.ini' />" | C:\Program Files\GRETECH\GOMPlayer\GrLauncher.exe | GOM.EXE | ||||||||||||
User: admin Company: GOM & Company Integrity Level: MEDIUM Description: GrLauncher Exit code: 16 Version: 2.1.1.0 Modules
| |||||||||||||||
| 1024 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,137 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\GRETECH\GOMPlayer\GOM.EXE" /showicon | C:\Program Files\GRETECH\GOMPlayer\GOM.EXE | — | GOMPLAYERGLOBALSETUP.EXE | |||||||||||
User: admin Company: GOM & Company Integrity Level: HIGH Description: GOM Player Exit code: 0 Version: 2, 3, 29, 5288 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome http://playerapi.gomlab.com/index.gom?type=home&lang=ENG | C:\Program Files\Internet Explorer\iexplore.exe | GOM.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1980 | "C:\Users\admin\AppData\Local\Temp\GOMPLAYERGLOBALSETUP.EXE" | C:\Users\admin\AppData\Local\Temp\GOMPLAYERGLOBALSETUP.EXE | — | explorer.exe | |||||||||||
User: admin Company: GOM & Company Integrity Level: MEDIUM Description: GOM Player Setup File Exit code: 3221226540 Version: 2.3 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\GRETECH\GOMPlayer\KillGom.exe" GOM.EXE | C:\Program Files\GRETECH\GOMPlayer\KillGom.exe | — | GOMPLAYERGLOBALSETUP.EXE | |||||||||||
User: admin Company: GOM & Company Integrity Level: HIGH Description: Kill GOM Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\GRETECH\GOMPlayer\popup.exe" /product=gomplayer /lang=eng /build=softpedia | C:\Program Files\GRETECH\GOMPlayer\popup.exe | GOM.EXE | ||||||||||||
User: admin Company: GOM & Company Integrity Level: MEDIUM Description: Popup Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\GRETECH\GOMPlayer\GOM.EXE" /regassoc | C:\Program Files\GRETECH\GOMPlayer\GOM.EXE | — | GOMPLAYERGLOBALSETUP.EXE | |||||||||||
User: admin Company: GOM & Company Integrity Level: HIGH Description: GOM Player Exit code: 0 Version: 2, 3, 29, 5288 Modules
| |||||||||||||||
Total events
7 363
Read events
2 090
Write events
5 264
Delete events
9
Modification events
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_CURRENT_USER\Software\GRETECH\GomPlayer\OPTION |
| Operation: | write | Name: | bFirstUpdateLaunching |
Value: 1 | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{2DB4F9B7-144E-4319-B14A-432AC74C0CEF} |
| Operation: | write | Name: | |
Value: VSUtil | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{2DB4F9B7-144E-4319-B14A-432AC74C0CEF} |
| Operation: | write | Name: | DllSurrogate |
Value: | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\VSUtil.DLL |
| Operation: | write | Name: | AppID |
Value: {2DB4F9B7-144E-4319-B14A-432AC74C0CEF} | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VSUtil.VSFile.1 |
| Operation: | write | Name: | |
Value: VSFile Class | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VSUtil.VSFile.1\CLSID |
| Operation: | write | Name: | |
Value: {BFF03BA9-F3B8-438C-9482-357E05CBA4E6} | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VSUtil.VSFile |
| Operation: | write | Name: | |
Value: VSFile Class | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VSUtil.VSFile\CLSID |
| Operation: | write | Name: | |
Value: {BFF03BA9-F3B8-438C-9482-357E05CBA4E6} | |||
| (PID) Process: | (2344) GOMPLAYERGLOBALSETUP.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VSUtil.VSFile\CurVer |
| Operation: | write | Name: | |
Value: VSUtil.VSFile.1 | |||
Executable files
50
Suspicious files
60
Text files
1 269
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\Local\Temp\Cab1574.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\Local\Temp\Tar1575.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C46E7B0F942663A1EDC8D9D6D7869173_6043FC604A395E1485AF7AC16D16B7CE | der | |
MD5:— | SHA256:— | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C46E7B0F942663A1EDC8D9D6D7869173_6043FC604A395E1485AF7AC16D16B7CE | binary | |
MD5:— | SHA256:— | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\Local\Temp\nsrDF6F.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\Local\Temp\nsrDF6F.tmp\advsplash.dll | executable | |
MD5:505C7C214C17AC801F5930ABC57D38C3 | SHA256:999EBF5EF6BF51828193DEAF7697E6D22419E437C65E603BFFA0BB2ACC7F40C8 | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\Local\Temp\nsrDF6F.tmp\LangDLL.dll | executable | |
MD5:0C44F21D4AFC81CC99FAC7CC35E4503A | SHA256:8DC2BE6679497994E3DDC97BC7BC1CE2B3C17EF3528B03DED6696EF198A11D10 | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\Local\Temp\nsrDF6F.tmp\nsisos.dll | executable | |
MD5:69806691D649EF1C8703FD9E29231D44 | SHA256:BA79AB7F63F02ED5D5D46B82B11D97DAC5B7EF7E9B9A4DF926B43CEAC18483B6 | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\Local\Temp\nsrDF6F.tmp\InstallOptions.dll | executable | |
MD5:5B3EDB39FE9C026322CAF37EA10F6733 | SHA256:A96B1C95F51B088ED5EC476485A6AA562CBE68A88D0261CE88BCB3DCA1F1C8B0 | |||
| 2344 | GOMPLAYERGLOBALSETUP.EXE | C:\Users\admin\AppData\Local\Temp\nsrDF6F.tmp\md5dll.dll | executable | |
MD5:7059F133EA2316B9E7E39094A52A8C34 | SHA256:32C3D36F38E7E8A8BAFD4A53663203EF24A10431BDA16AF9E353C7D5D108610F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
97
TCP/UDP connections
130
DNS requests
73
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
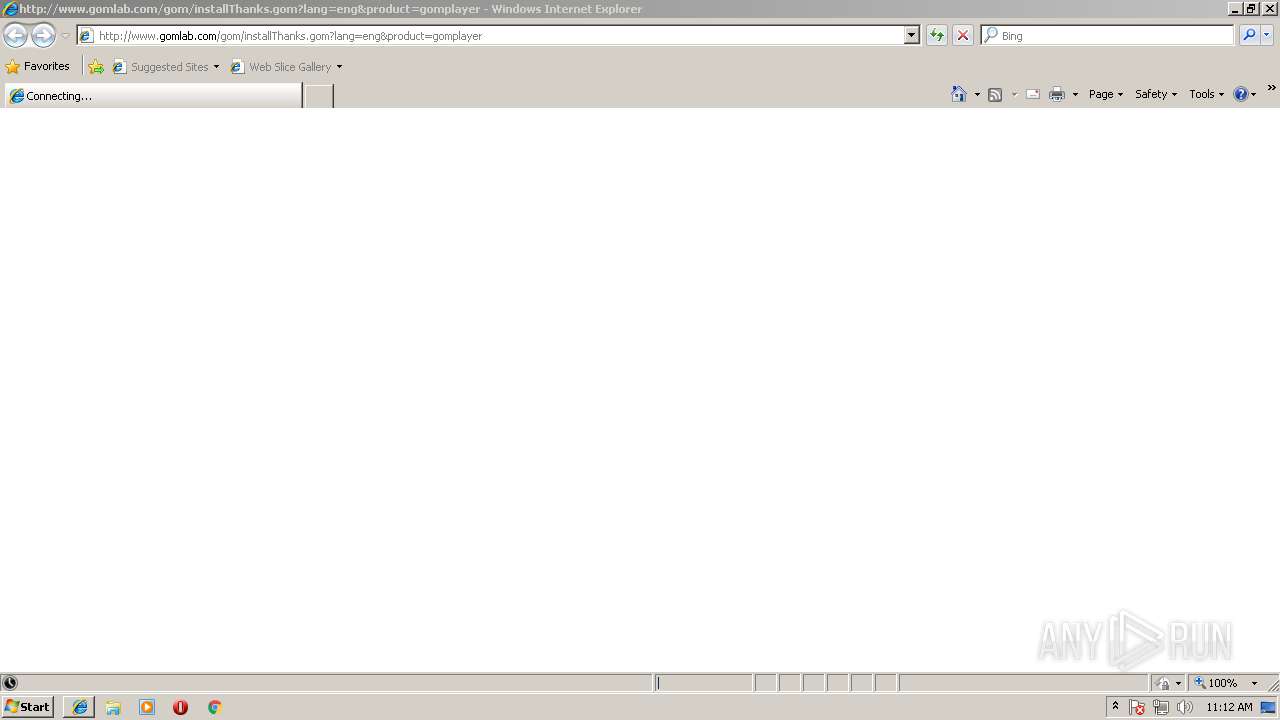
3688 | iexplore.exe | GET | 302 | 52.85.173.240:80 | http://www.gomlab.com/gom/installThanks.gom?lang=eng&product=gomplayer | US | — | — | malicious |
2344 | GOMPLAYERGLOBALSETUP.EXE | GET | 200 | 23.51.123.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
2344 | GOMPLAYERGLOBALSETUP.EXE | GET | 200 | 23.37.43.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEFYMP7wrCwvOpqIyaQe7ilk%3D | NL | der | 1.57 Kb | shared |
3688 | iexplore.exe | GET | 200 | 104.31.74.124:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.48 Kb | whitelisted |
3688 | iexplore.exe | GET | 200 | 216.58.207.46:80 | http://ocsp.pki.goog/GTSGIAG3/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCCBk%2BAiY78DaI | US | der | 463 b | whitelisted |
3688 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3688 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 52.4 Kb | whitelisted |
3688 | iexplore.exe | GET | 200 | 216.58.207.46:80 | http://ocsp.pki.goog/GTSGIAG3/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCCEja1uWAMGyR | US | der | 463 b | whitelisted |
2344 | GOMPLAYERGLOBALSETUP.EXE | GET | 404 | 52.20.146.86:80 | http://log.gomlab.com/player/install?build=softpedia&fpb=softpedia&version=2.3.29.5288&bit=32bit&os=windows732bit&lang=eng&guid=c967096763bba334d0a2cfe63d38b8bb&browser=ie | US | binary | 1 b | unknown |
3688 | iexplore.exe | GET | 200 | 216.58.207.46:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjqTAc%2FHIGOD%2BaUx0%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2344 | GOMPLAYERGLOBALSETUP.EXE | 23.51.123.27:80 | s2.symcb.com | Akamai Technologies, Inc. | NL | whitelisted |
2344 | GOMPLAYERGLOBALSETUP.EXE | 52.20.146.86:80 | log.gomlab.com | Amazon.com, Inc. | US | unknown |
2208 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3688 | iexplore.exe | 104.31.74.124:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3688 | iexplore.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
3688 | iexplore.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
3688 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3688 | iexplore.exe | 52.85.173.240:80 | www.gomlab.com | Amazon.com, Inc. | US | unknown |
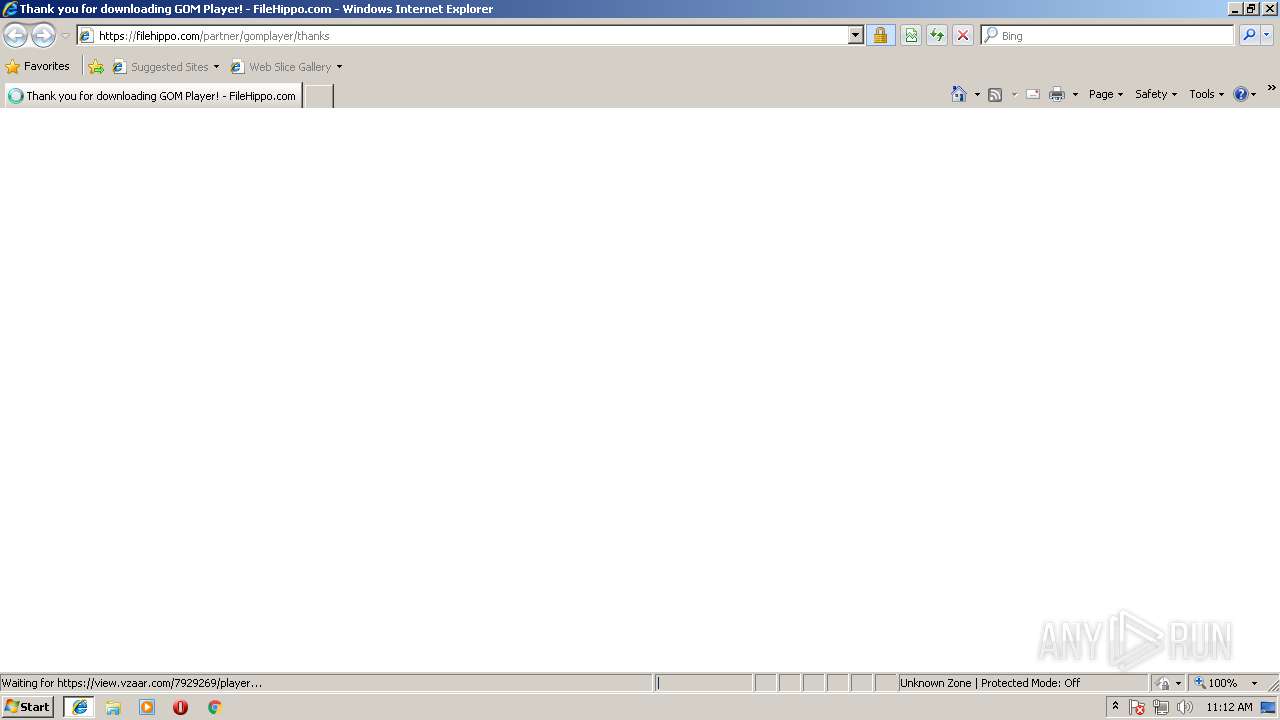
3688 | iexplore.exe | 151.101.66.217:80 | filehippo.com | Fastly | US | suspicious |
3688 | iexplore.exe | 151.101.66.217:443 | filehippo.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s2.symcb.com |
| whitelisted |
sv.symcd.com |
| shared |
log.gomlab.com |
| unknown |
www.gomlab.com |
| malicious |
www.bing.com |
| whitelisted |
filehippo.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
cache-01.filehippo.net |
| shared |
code.jquery.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GOM.EXE | Mouse Lbutton UP 346, 486
|