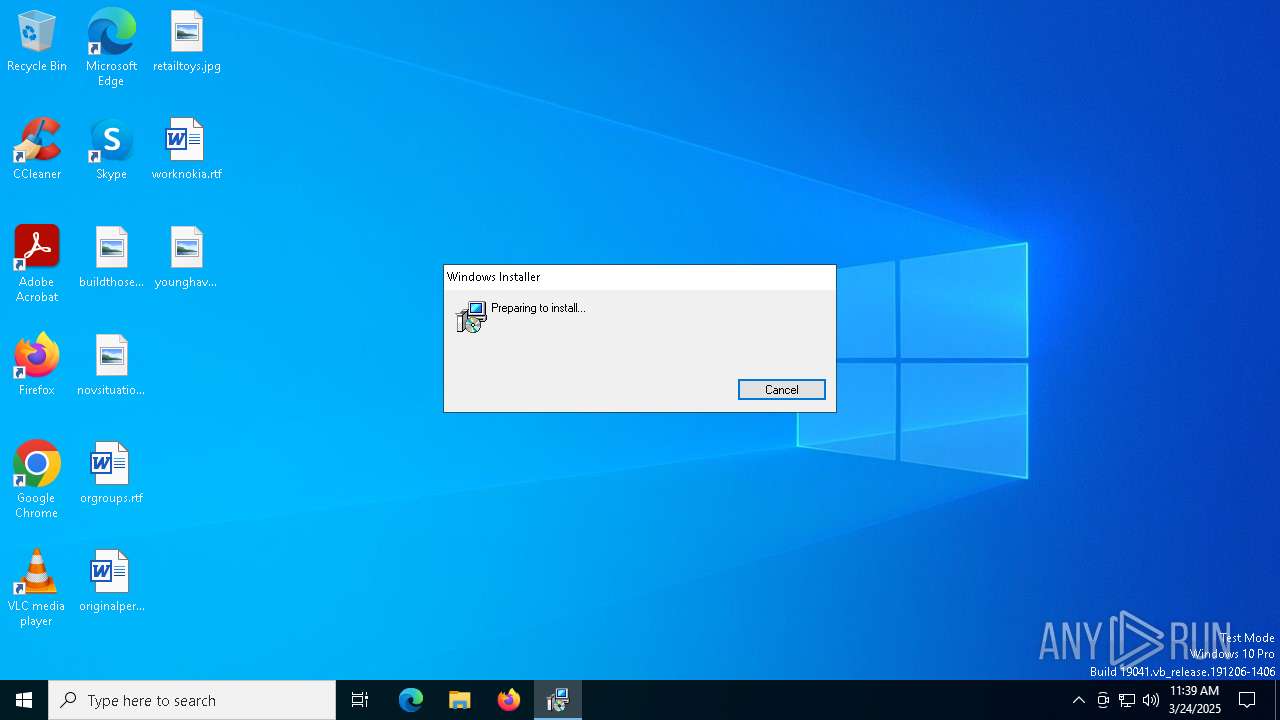
| File name: | Setup.msi |
| Full analysis: | https://app.any.run/tasks/c283d95f-c2aa-4307-b08b-d371a47f1706 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 11:39:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {67E25B2E-0588-4942-9D33-9996558C9A70}, Number of Words: 2, Subject: World Wide Web, Author: World Wide Solutions, Name of Creating Application: World Wide Web, Template: ;1033, Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Sun Mar 23 19:10:58 2025, Last Saved Time/Date: Sun Mar 23 19:10:58 2025, Last Printed: Sun Mar 23 19:10:58 2025, Number of Pages: 450 |
| MD5: | 5E6717D0F5545DA9E5D5AB1756F6A769 |
| SHA1: | 6F26D1EC4D17952689423EE62411CB64B251CAC8 |
| SHA256: | C6DF56593FFB976A0510BDA8C94E0AEF8C5AFBB013A4C3CB2905BB57B3CA34B3 |
| SSDEEP: | 98304:19ILoGgDggmCP1iiOA0tI1jHS9qPZ+/CB2QtynvrUuYKU95w0Enmm3gUngp/keoR: |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2340)
Creates a new scheduled task via Registry
- msiexec.exe (PID: 6192)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 7312)
SUSPICIOUS
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6112)
- msiexec.exe (PID: 7524)
- viewer.exe (PID: 7200)
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 5324)
Adds/modifies Windows certificates
- viewer.exe (PID: 7200)
Executes as Windows Service
- VSSVC.exe (PID: 7840)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 7312)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 7312)
The process executes Powershell scripts
- msiexec.exe (PID: 7312)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 7312)
INFO
An automatically generated document
- msiexec.exe (PID: 5324)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5324)
- msiexec.exe (PID: 6112)
- msiexec.exe (PID: 5352)
- msiexec.exe (PID: 7304)
Reads the computer name
- msiexec.exe (PID: 6112)
- msiexec.exe (PID: 5352)
- viewer.exe (PID: 7200)
Checks supported languages
- msiexec.exe (PID: 5352)
- msiexec.exe (PID: 6112)
- viewer.exe (PID: 7200)
- msiexec.exe (PID: 6192)
- identity_helper.exe (PID: 2240)
The sample compiled with english language support
- msiexec.exe (PID: 5324)
- msiexec.exe (PID: 7304)
- msiexec.exe (PID: 5352)
Reads Environment values
- msiexec.exe (PID: 6112)
- msiexec.exe (PID: 7524)
- msiexec.exe (PID: 7312)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6112)
- viewer.exe (PID: 7200)
- msiexec.exe (PID: 7524)
Create files in a temporary directory
- msiexec.exe (PID: 6112)
Reads the software policy settings
- msiexec.exe (PID: 6112)
- msiexec.exe (PID: 7524)
- viewer.exe (PID: 7200)
- msiexec.exe (PID: 7304)
Process checks computer location settings
- msiexec.exe (PID: 6112)
Manages system restore points
- SrTasks.exe (PID: 7228)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2340)
Reads security settings of Internet Explorer
- powershell.exe (PID: 2340)
Manual execution by a user
- msedge.exe (PID: 2316)
Application launched itself
- msedge.exe (PID: 7888)
- msedge.exe (PID: 2268)
- msedge.exe (PID: 2316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {67E25B2E-0588-4942-9D33-9996558C9A70} |
| Words: | 2 |
| Subject: | World Wide Web |
| Author: | World Wide Solutions |
| LastModifiedBy: | - |
| Software: | World Wide Web |
| Template: | ;1033 |
| Comments: | - |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2025:03:23 19:10:58 |
| ModifyDate: | 2025:03:23 19:10:58 |
| LastPrinted: | 2025:03:23 19:10:58 |
| Pages: | 450 |
Total processes
196
Monitored processes
60
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5228 --field-trial-handle=2228,i,18302420608328551116,7411535038182312148,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2f4,0x2f8,0x2fc,0x2ec,0x304,0x7ffc80635fd8,0x7ffc80635fe4,0x7ffc80635ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6444 --field-trial-handle=2228,i,18302420608328551116,7411535038182312148,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3424 --field-trial-handle=2228,i,18302420608328551116,7411535038182312148,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2240 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3312 --field-trial-handle=2376,i,14785102813158630798,1223766300510368153,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://download.isready.online/notification/?verify=110mrdd1742816416 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2316 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --flag-switches-end --do-not-de-elevate --single-argument https://download.isready.online/notification/?verify=110mrdd1742816416 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2340 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss1A6E.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi1A5B.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr1A5C.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr1A5D.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5324 --field-trial-handle=2228,i,18302420608328551116,7411535038182312148,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6284 --field-trial-handle=2228,i,18302420608328551116,7411535038182312148,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
34 070
Read events
33 816
Write events
234
Delete events
20
Modification events
| (PID) Process: | (7200) viewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
Value: | |||
| (PID) Process: | (7200) viewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000E94FB54871208C00DF70F708AC47085B0F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C0300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B809000000010000000C000000300A06082B060105050703031D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD91400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B53000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C06200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF860B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000001900000001000000100000005D1B8FF2C30F63F5B536EDD400F7F9B4200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (7200) viewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000001900000001000000100000005D1B8FF2C30F63F5B536EDD400F7F9B40B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000006200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF8653000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C01400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B1D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD909000000010000000C000000300A06082B060105050703030300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B80F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C040000000100000010000000E94FB54871208C00DF70F708AC47085B200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000012EB9676B19CDB01E8140000901E0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000050BB3276B19CDB01E8140000901E0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000050BB3276B19CDB01E8140000901E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000E4BB8F76B19CDB01E8140000901E0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000E4BB8F76B19CDB01E8140000901E0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000009A849476B19CDB01E8140000901E0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5352) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000018F2377B19CDB01E8140000901E0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
33
Suspicious files
127
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7304 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSICE80.tmp | executable | |
MD5:2330EBBE491C6026AF5E8853F3692798 | SHA256:3ADA2257732FAE73114BB6A5E082CEF4BD72C3D6842924BE6F22728C7D7CACC4 | |||
| 5352 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5352 | msiexec.exe | C:\Windows\Installer\111450.msi | — | |
MD5:— | SHA256:— | |||
| 5324 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB9ED.tmp | executable | |
MD5:2330EBBE491C6026AF5E8853F3692798 | SHA256:3ADA2257732FAE73114BB6A5E082CEF4BD72C3D6842924BE6F22728C7D7CACC4 | |||
| 5324 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A1D627669EFC8CD4F21BCF387D97F9B5_A9CA4191D05D34A8E11E01F09820AAAF | binary | |
MD5:DD84CAECD188E1E65014E6044D61AEC1 | SHA256:B18836FCB20D8853D0DC5939E9145133F1EFB78069988EEEE09C0FCE25A61444 | |||
| 5324 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB826.tmp | executable | |
MD5:2330EBBE491C6026AF5E8853F3692798 | SHA256:3ADA2257732FAE73114BB6A5E082CEF4BD72C3D6842924BE6F22728C7D7CACC4 | |||
| 5324 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A1D627669EFC8CD4F21BCF387D97F9B5_A9CA4191D05D34A8E11E01F09820AAAF | binary | |
MD5:21AB60755620586C1BC836285F382B10 | SHA256:8CC09F6111519D242083FF2A6F5FA0FDC23AE4AEDE409286D442E9AC32351462 | |||
| 5324 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_6C354C532D063DF5607A63BA827F5164 | binary | |
MD5:6B72342F98070BF0D0C5F43B44A4A6C3 | SHA256:A26734EF1285086FC9590A84847F753CC161F2151041EC5EE2D3207EC8ADB221 | |||
| 5324 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIB921.tmp | executable | |
MD5:2330EBBE491C6026AF5E8853F3692798 | SHA256:3ADA2257732FAE73114BB6A5E082CEF4BD72C3D6842924BE6F22728C7D7CACC4 | |||
| 5324 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_6C354C532D063DF5607A63BA827F5164 | binary | |
MD5:977FC114C85D547D9D4EA5E580C6EEB4 | SHA256:AC9A9AB3F3E336A4860E29C1DCA659CF8717F6428FB64EE918231A8CC34A6A77 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
58
DNS requests
51
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5324 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsgccr45codesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLuA3ygnKW%2F7xuSx%2F09F%2BhHVuEUQQU2rONwCSQo2t30wygWd0hZ2R2C3gCDHN1wNgKbULDD4ZKng%3D%3D | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
7604 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
7428 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
7604 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
5324 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgOhtwj4VKsGchDZBEc%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
5324 | msiexec.exe | 104.18.21.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | unknown |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | unknown |
7428 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
7428 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.globalsign.com |
| unknown |
settings-win.data.microsoft.com |
| unknown |
client.wns.windows.com |
| unknown |
login.live.com |
| unknown |
ocsp.digicert.com |
| unknown |
arc.msn.com |
| unknown |
go.microsoft.com |
| unknown |
slscr.update.microsoft.com |
| unknown |
www.microsoft.com |
| unknown |
fe3cr.delivery.mp.microsoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |