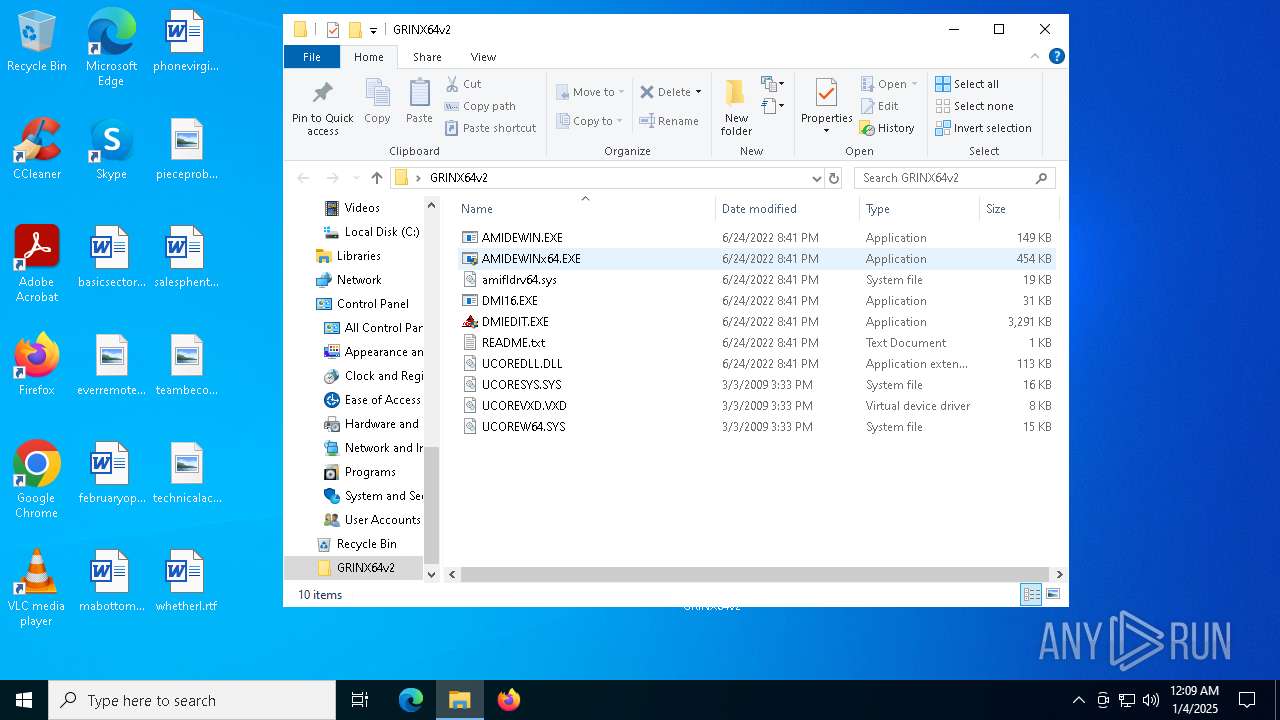
| File name: | GRINX64v2.rar |
| Full analysis: | https://app.any.run/tasks/c401406a-794c-49f3-a865-54f0c1d00616 |
| Verdict: | Malicious activity |
| Analysis date: | January 04, 2025, 00:09:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
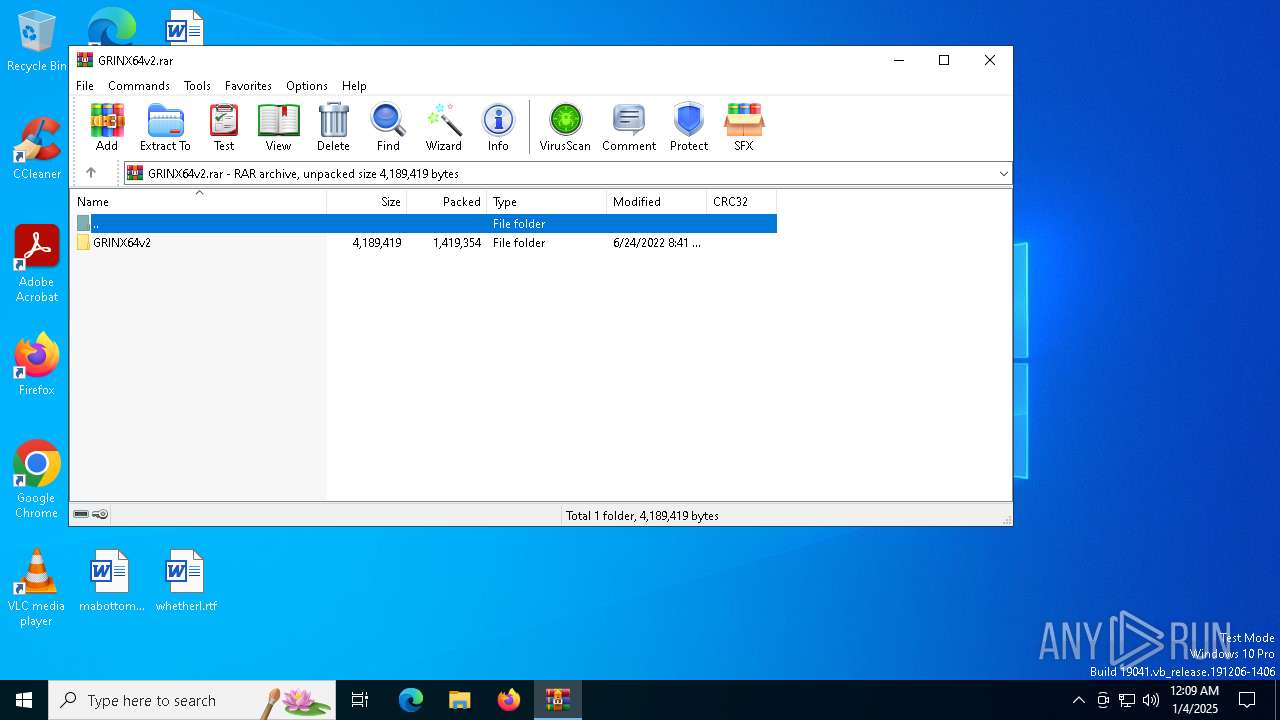
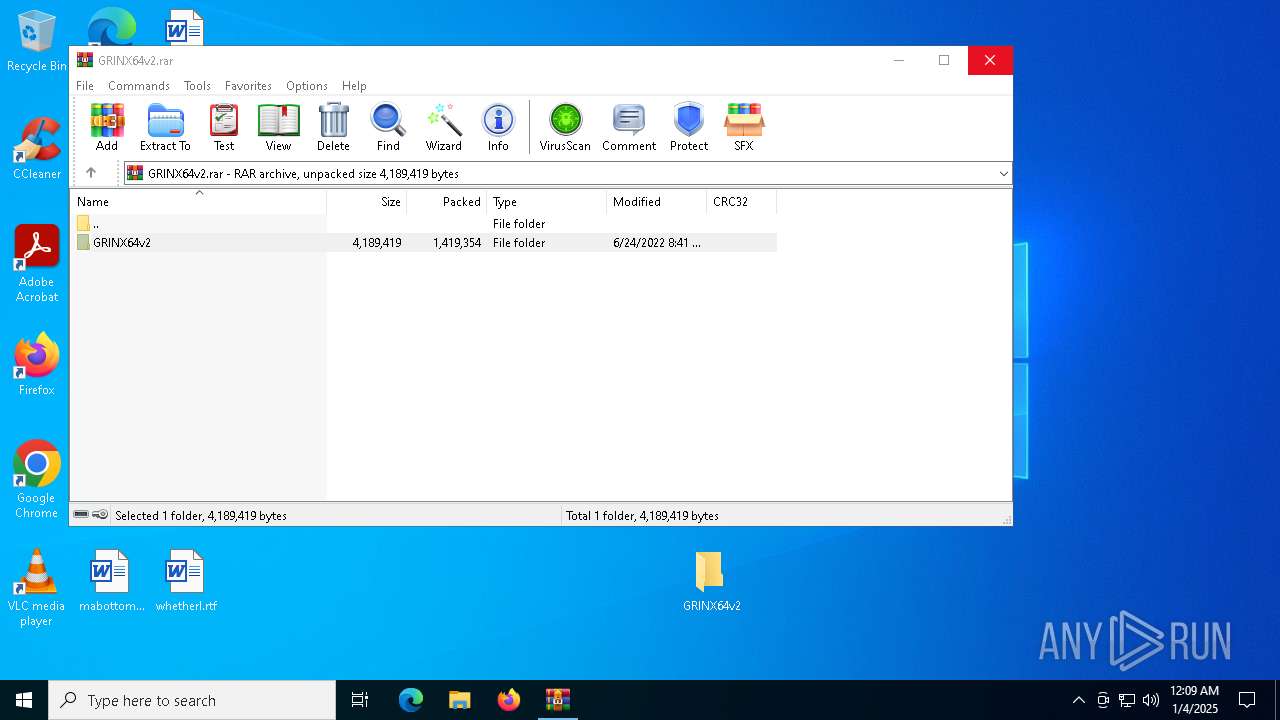
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A2407682730195CE9D6CD9B01E358FB6 |
| SHA1: | 6E29E43E32AFEA154D303303B141DC335CE15BA6 |
| SHA256: | C6DC38D4EB28E4F07A96CC63AF8EEFC557F3ACFF5439468FE6E1C9A7E2348C31 |
| SSDEEP: | 49152:cjo2TDH1r7quuWP8VQjN0m6h0jb9IWjIHe7XppBvHUL+9IOouGja3uAnxDa7Fgye:cjo1sumNuh+Izs5XUL+9IOYe7xClCdCi |
MALICIOUS
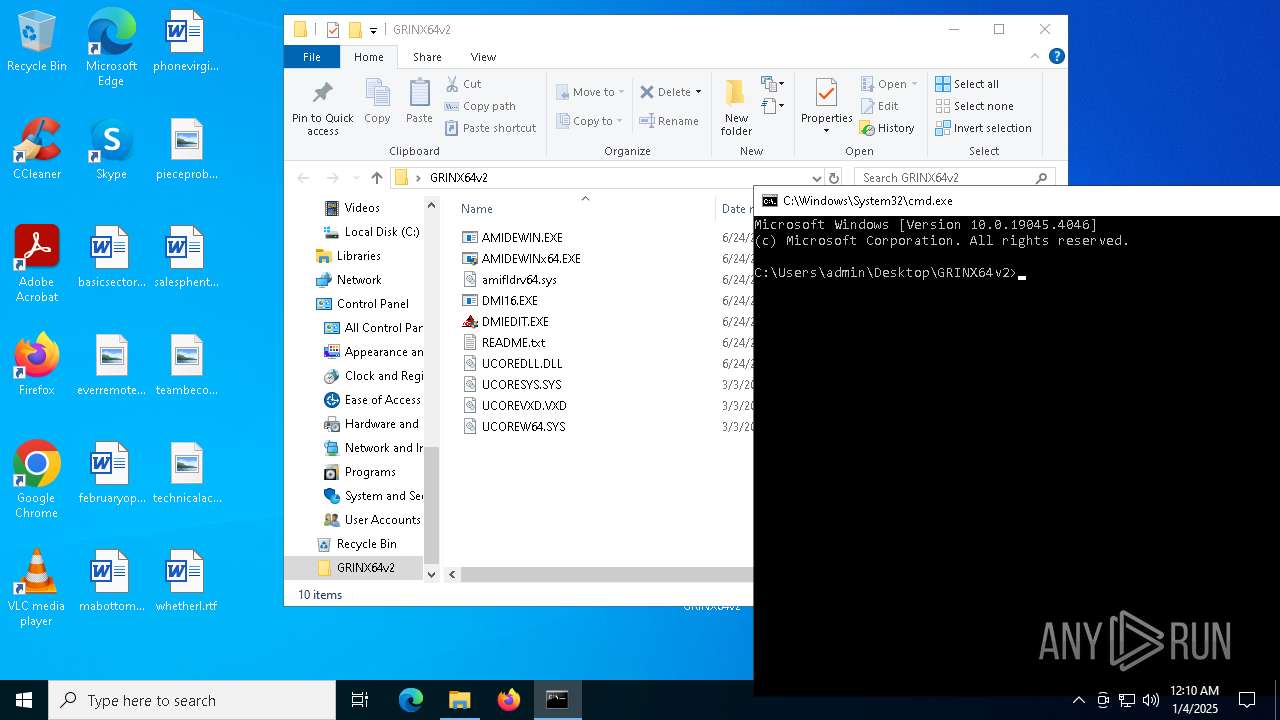
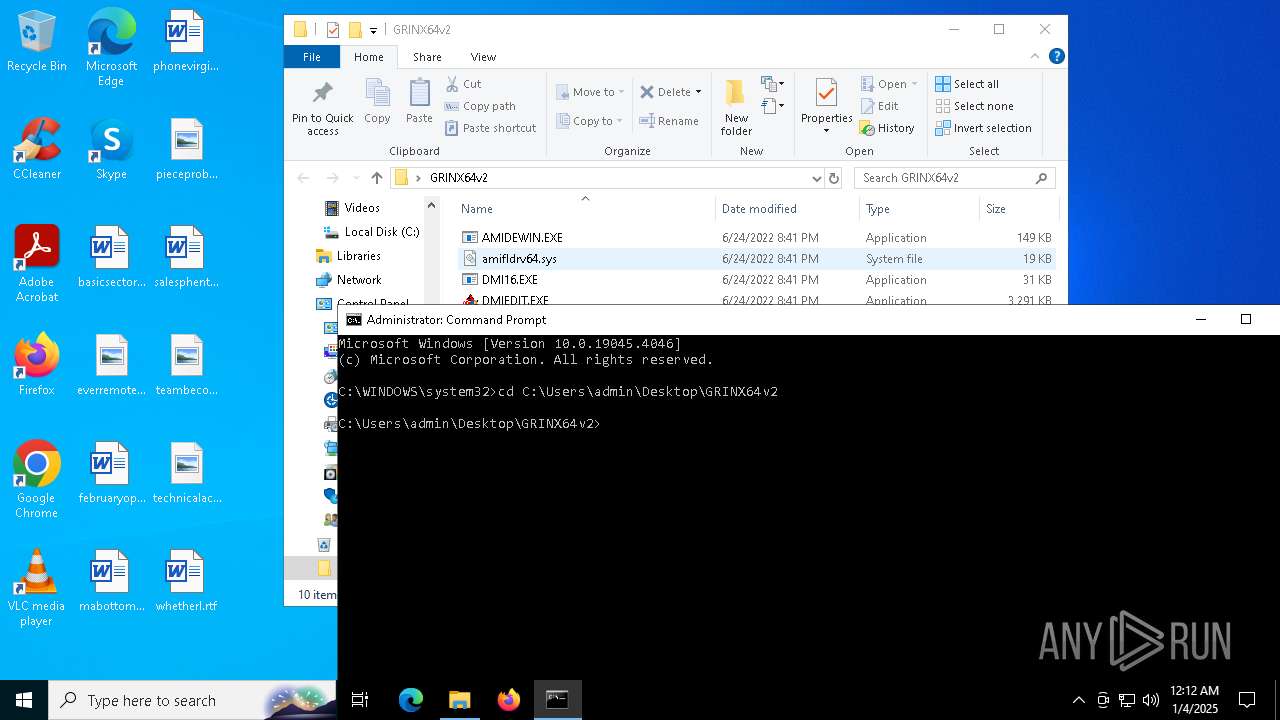
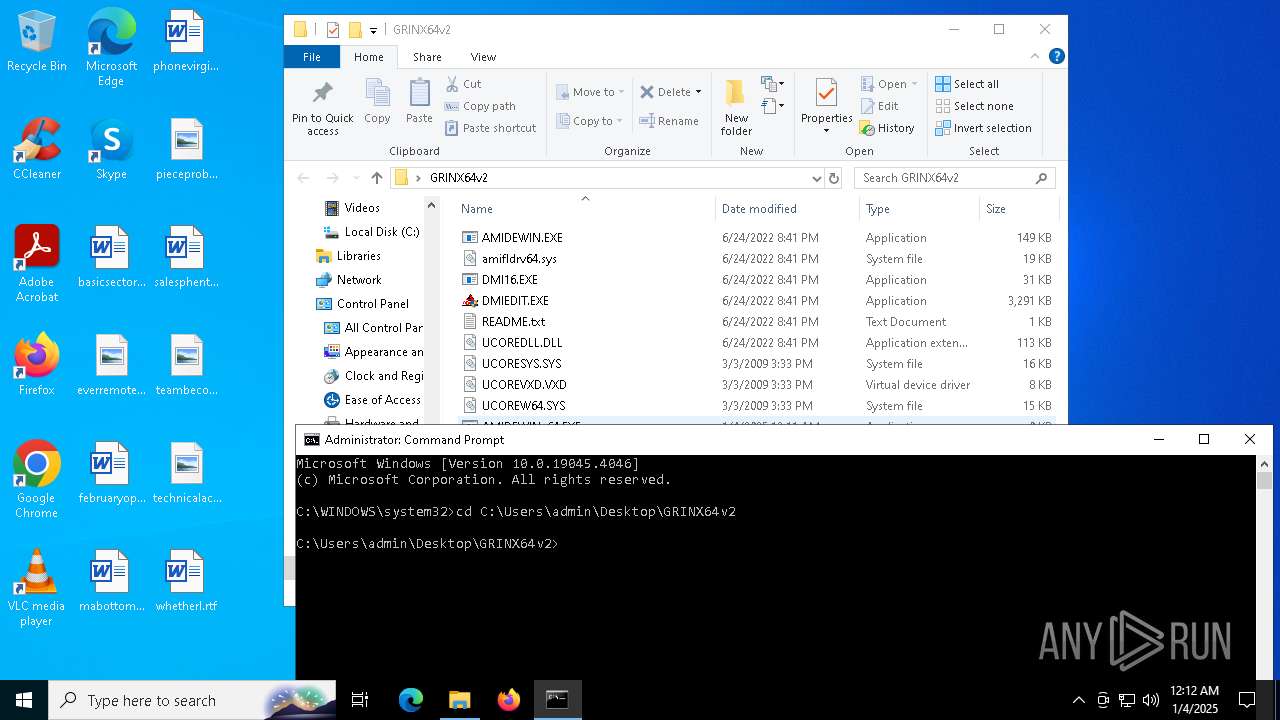
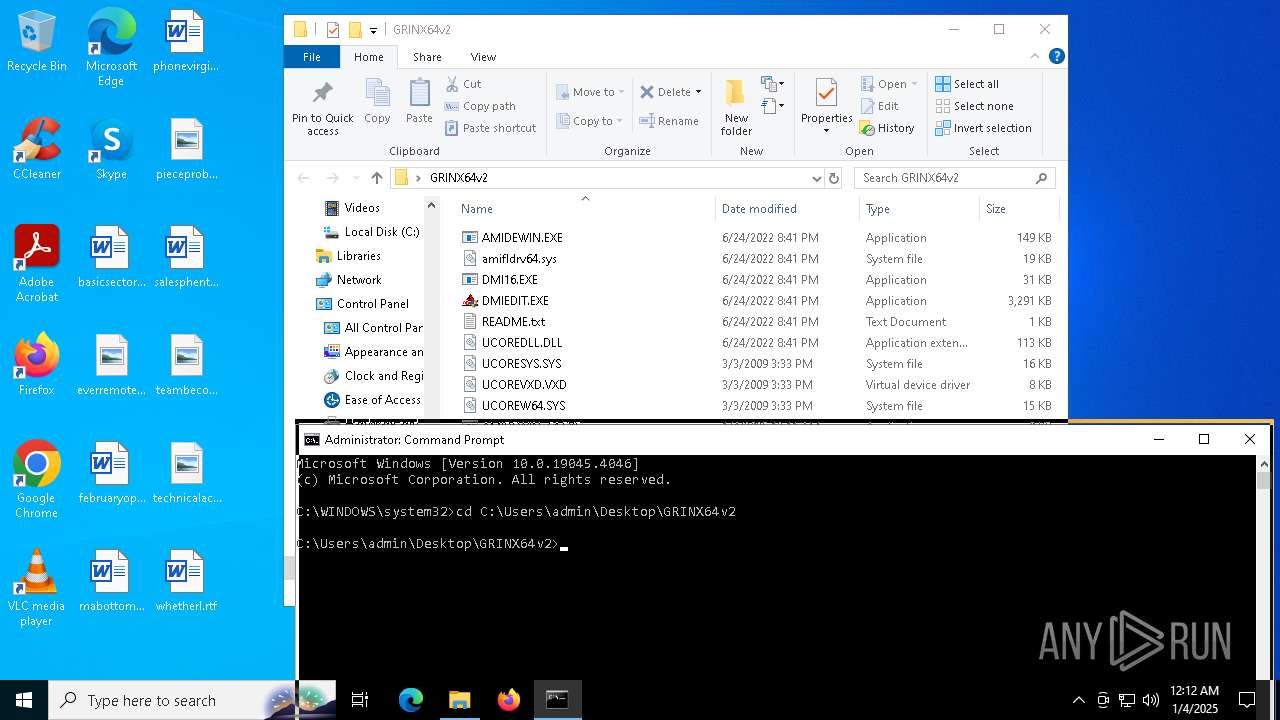
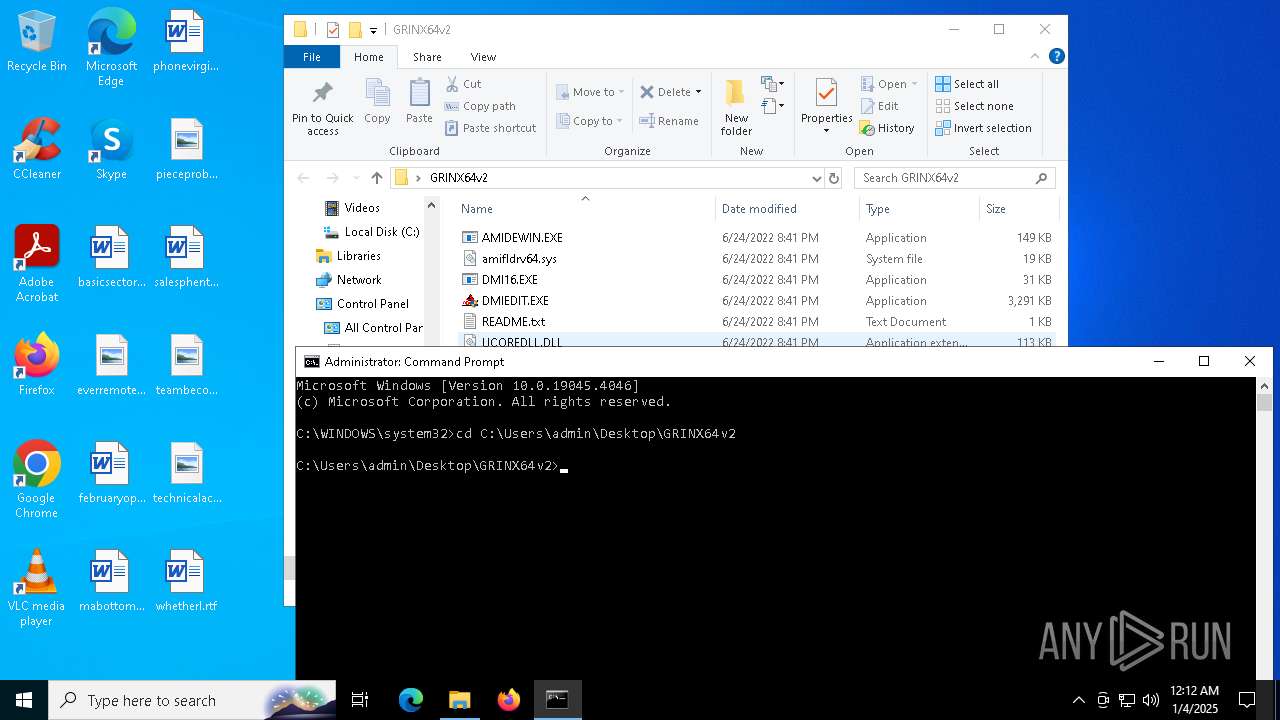
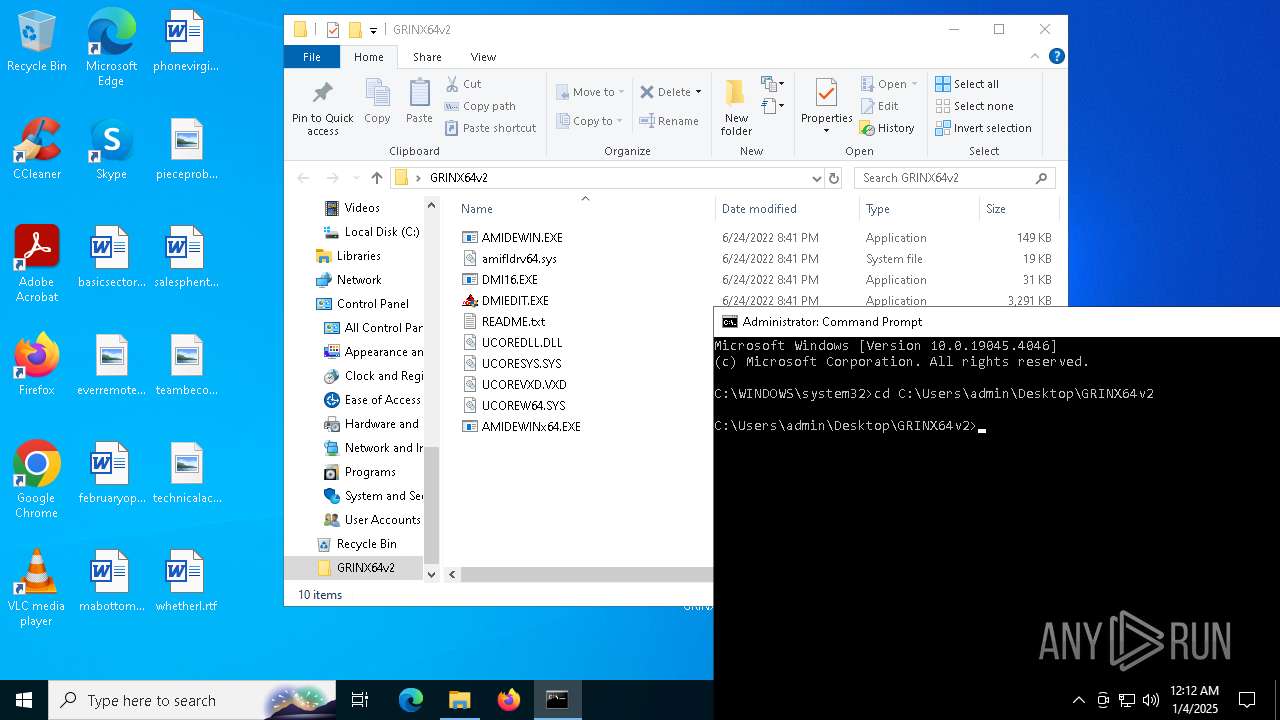
Generic archive extractor
- WinRAR.exe (PID: 6380)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6380)
INFO
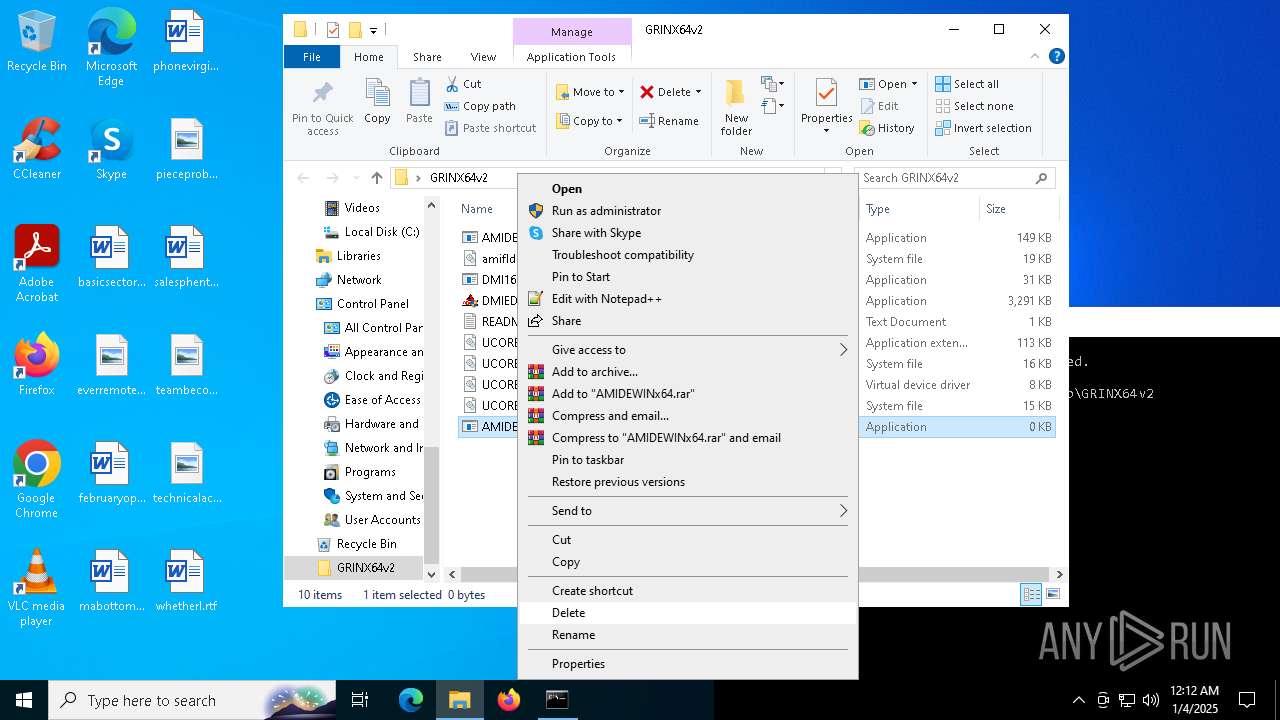
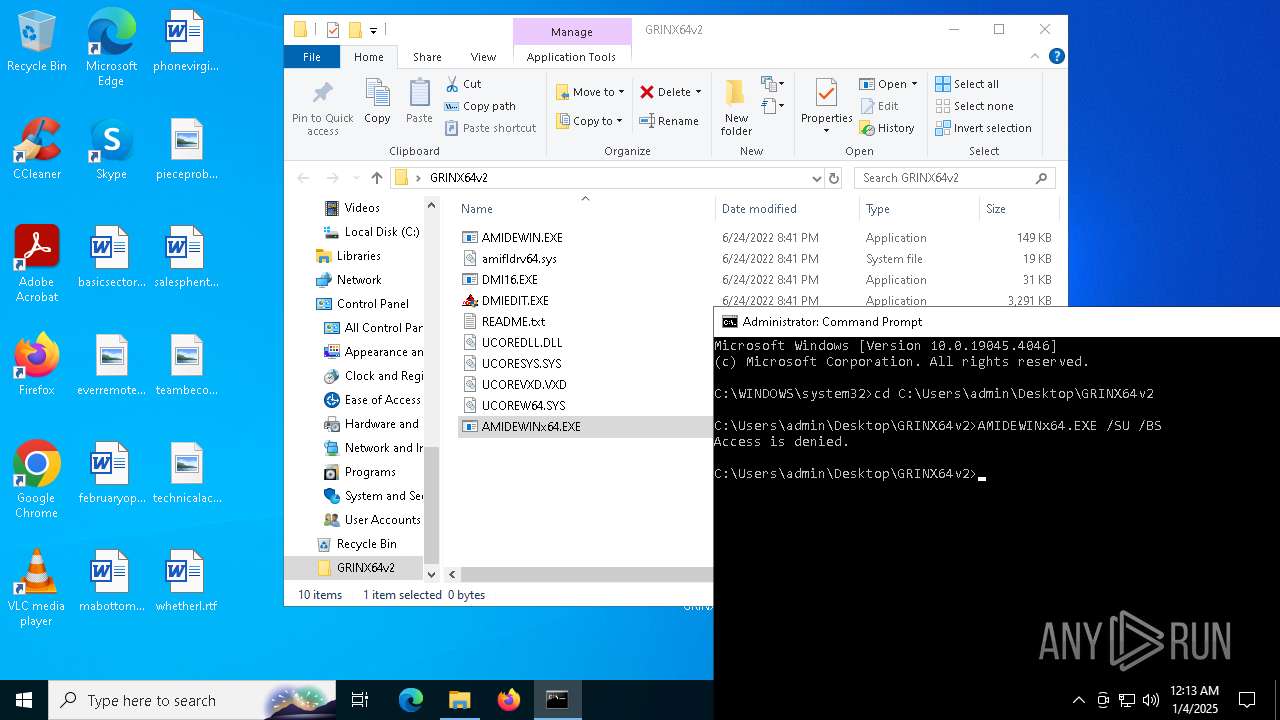
Reads the computer name
- AMIDEWINx64.EXE (PID: 5092)
The sample compiled with english language support
- WinRAR.exe (PID: 6380)
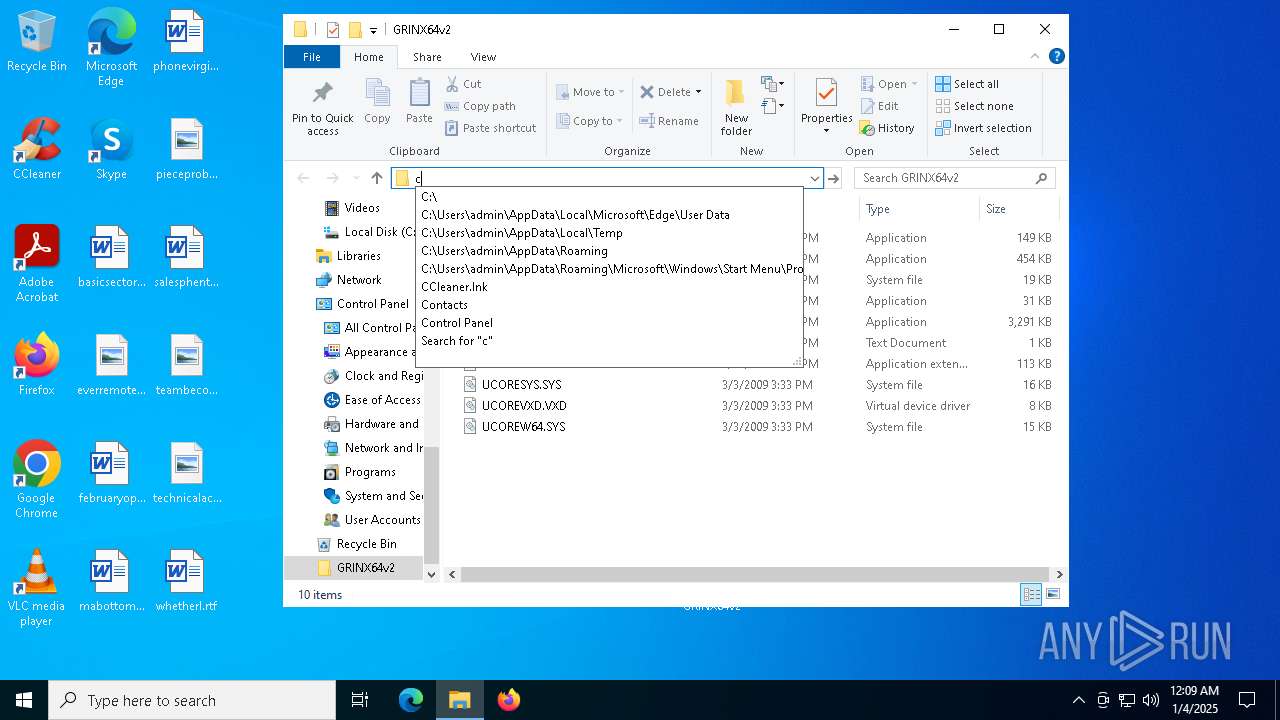
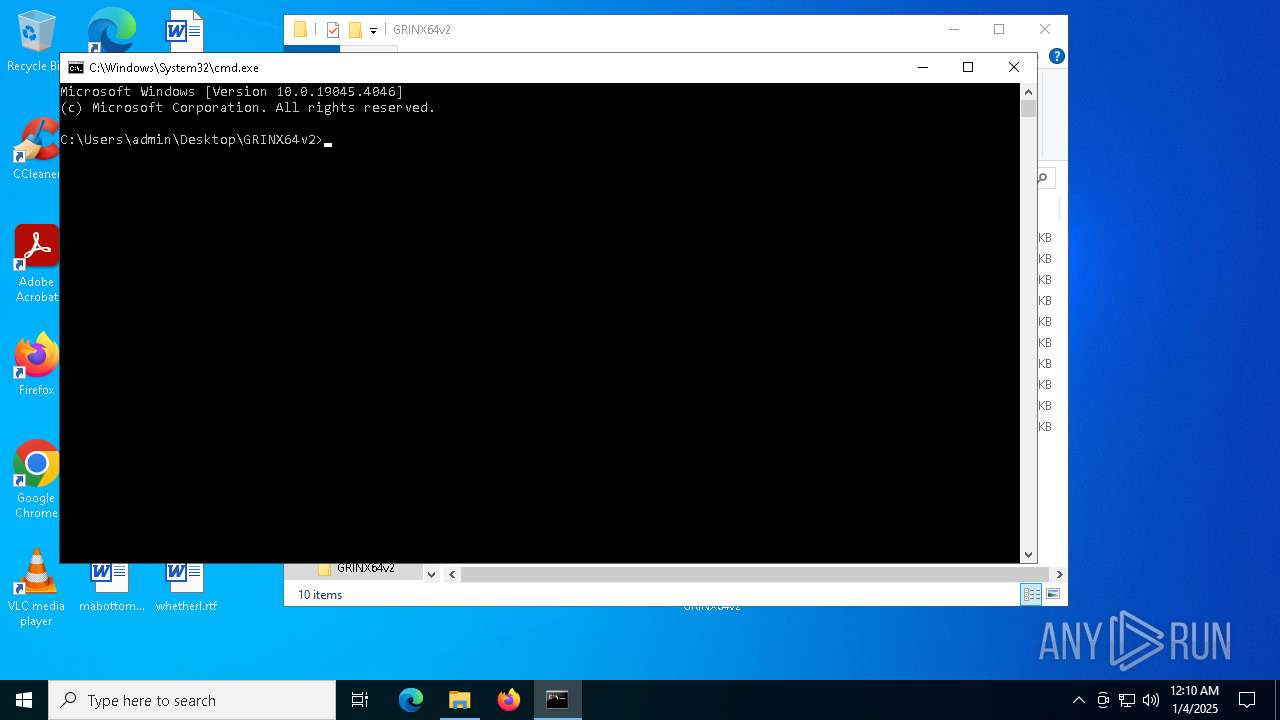
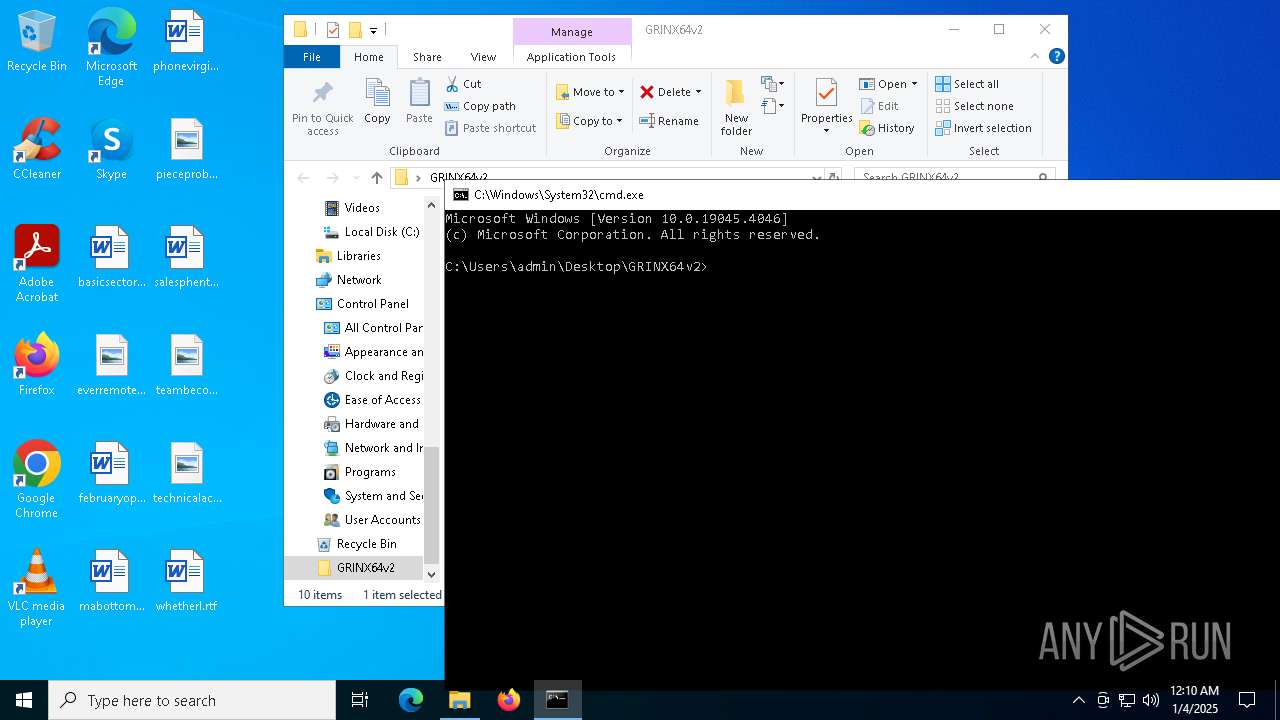
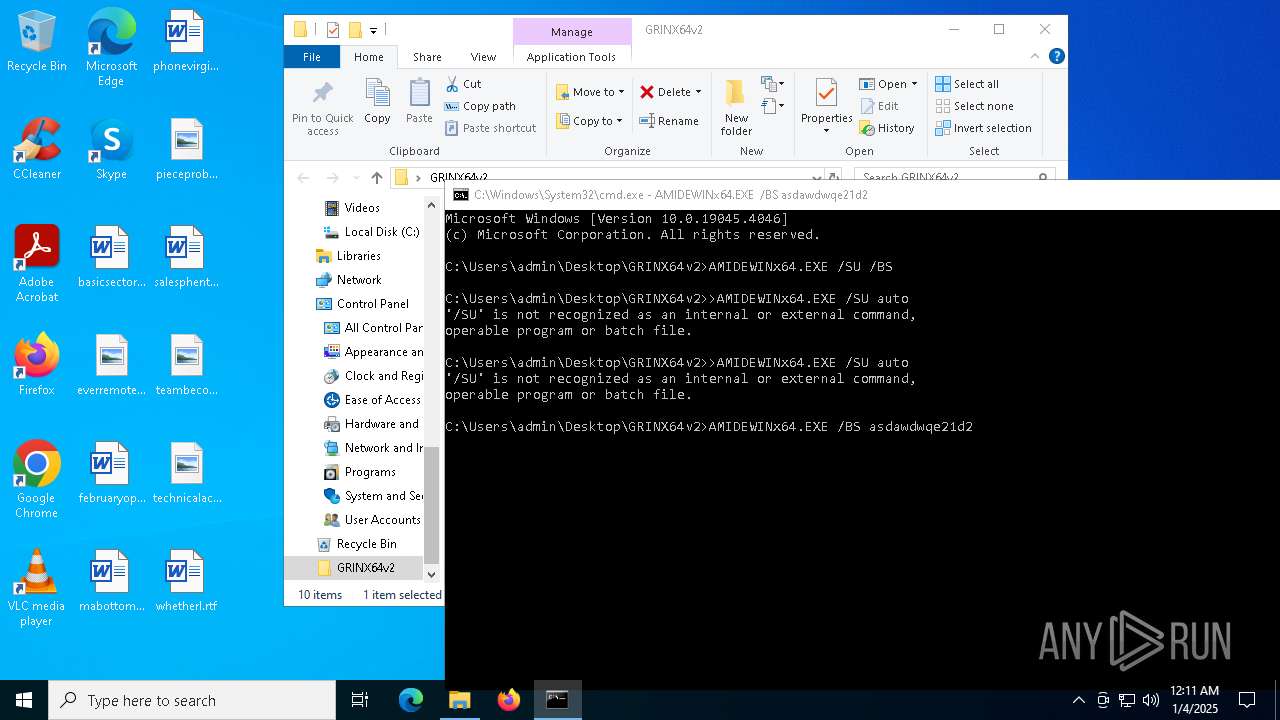
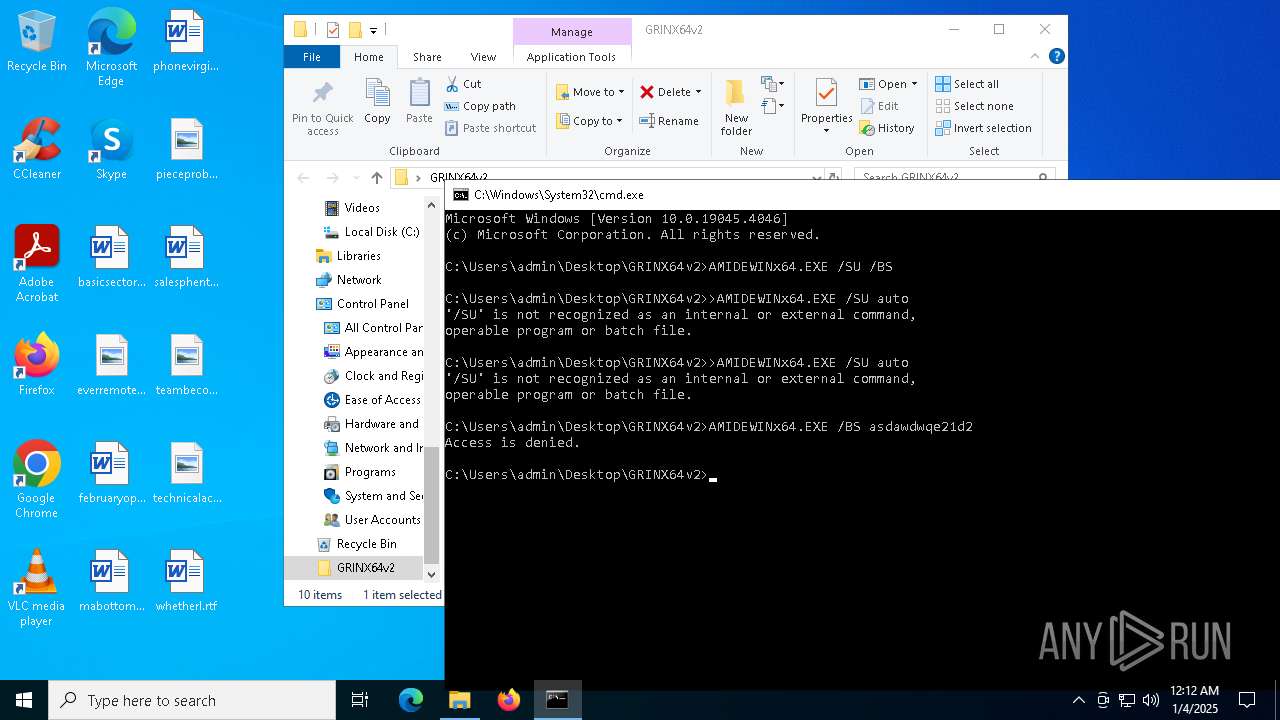
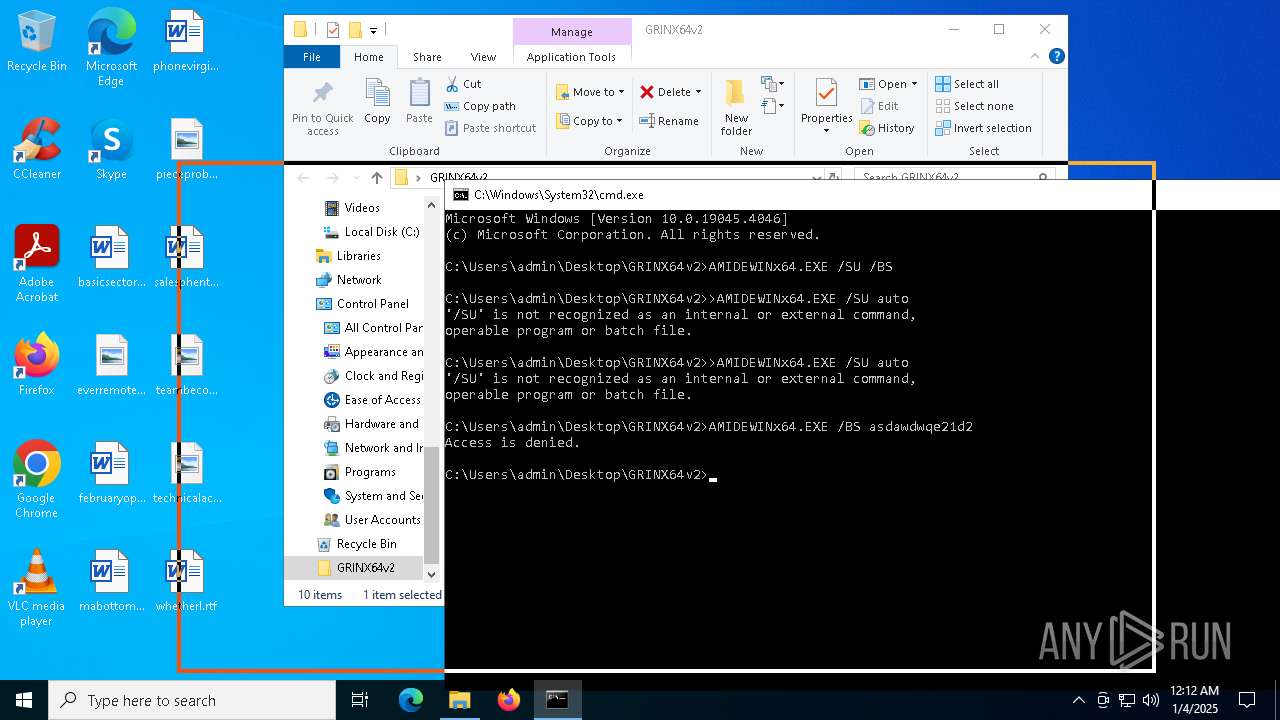
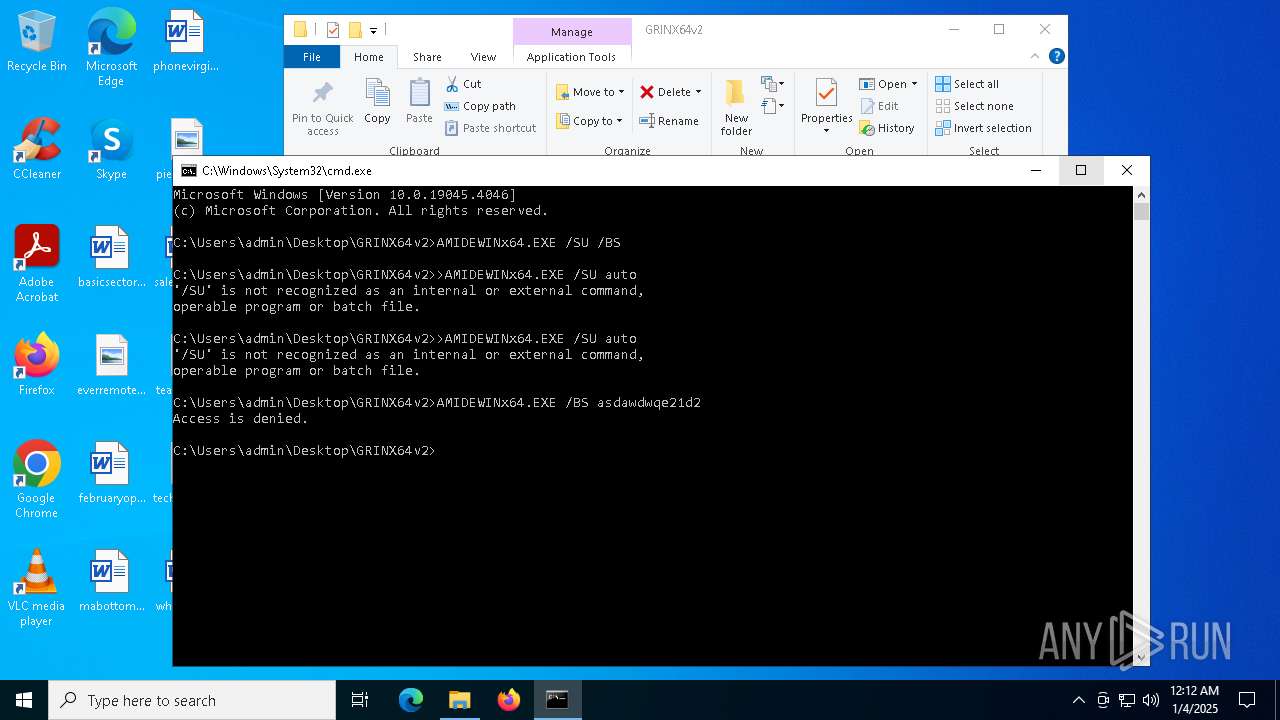
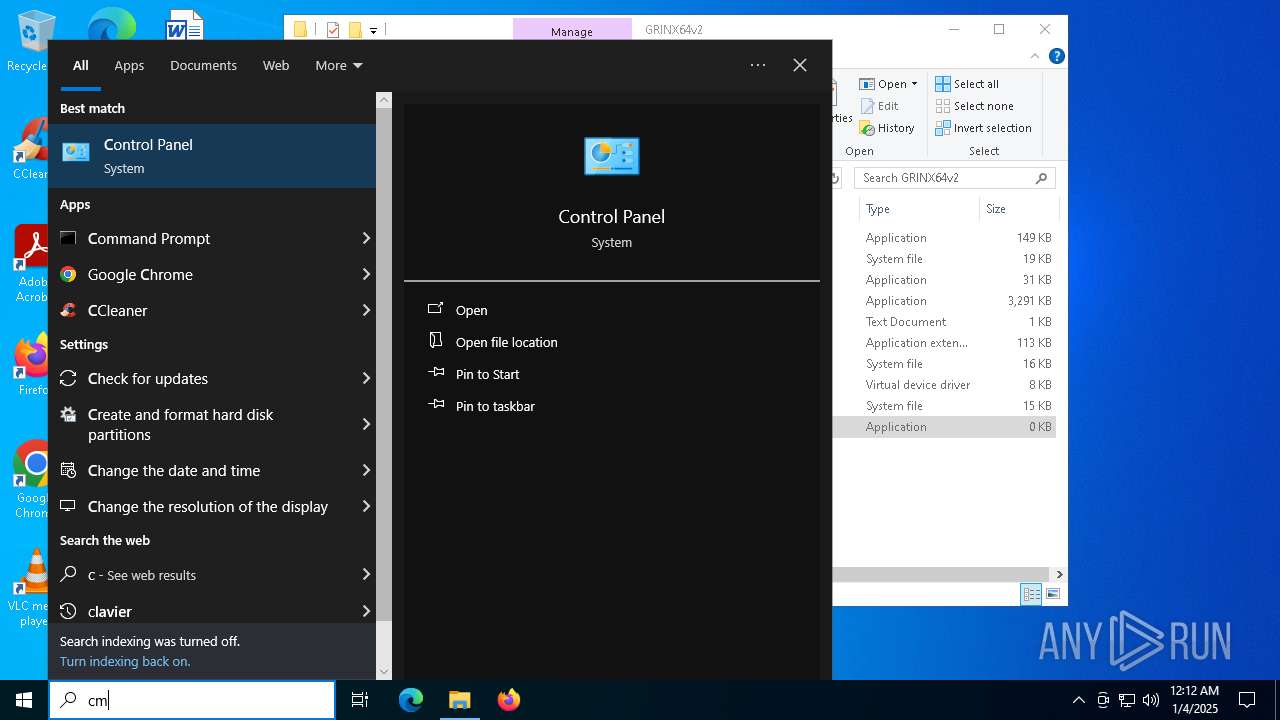
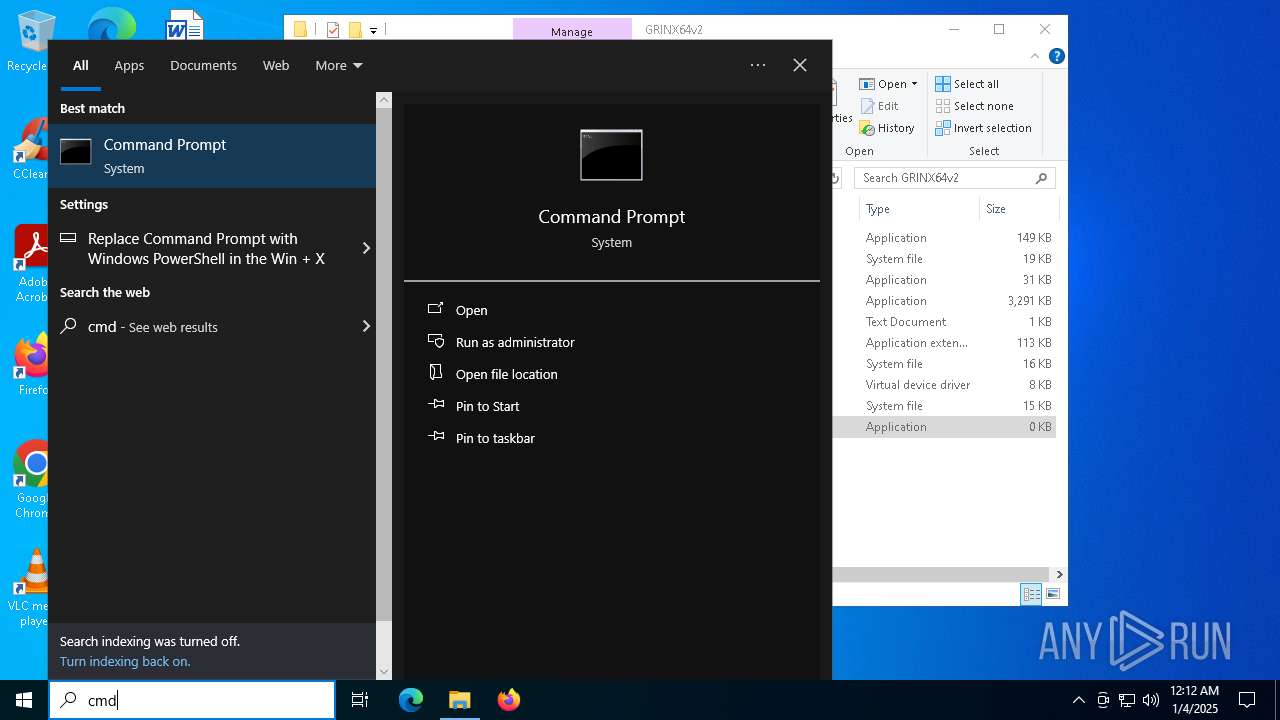
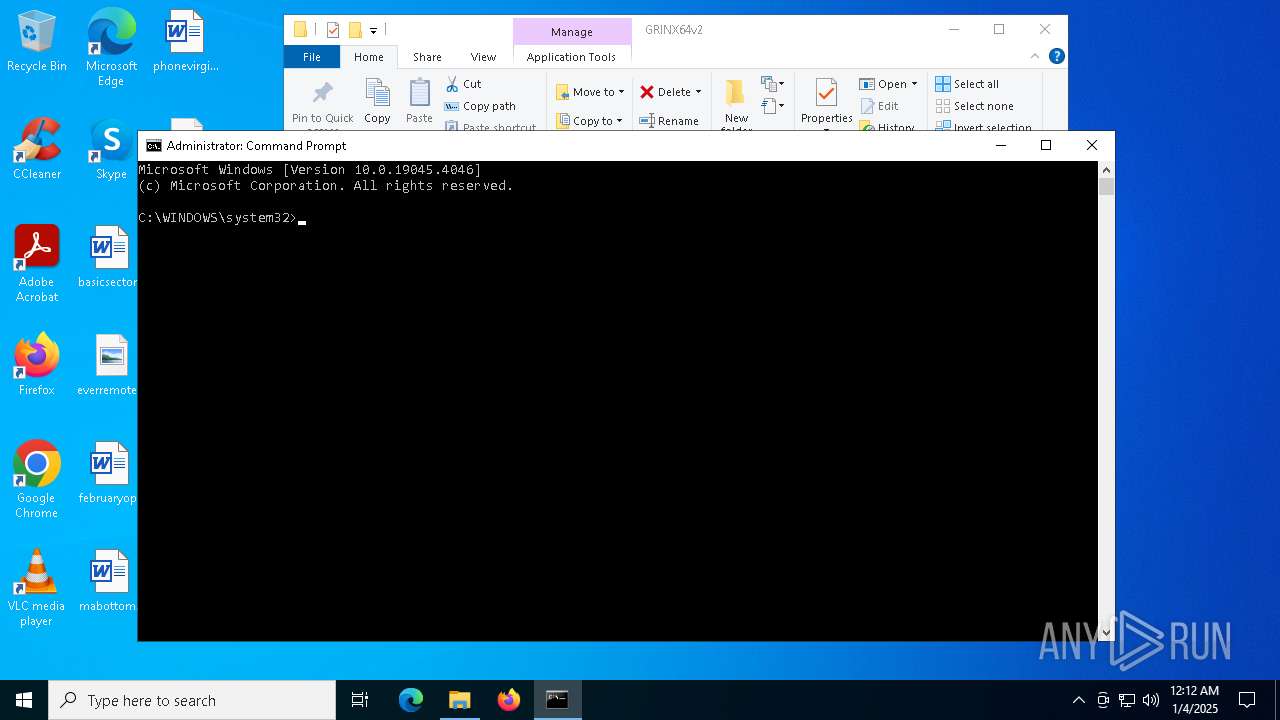
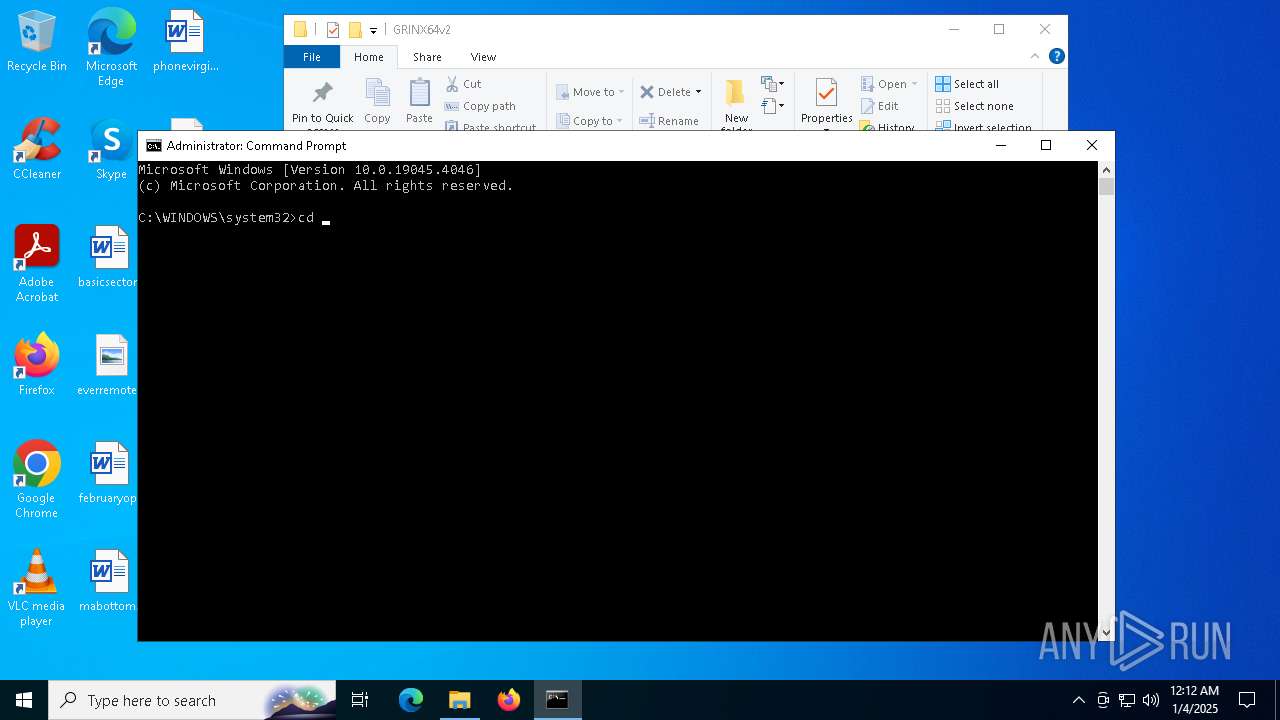
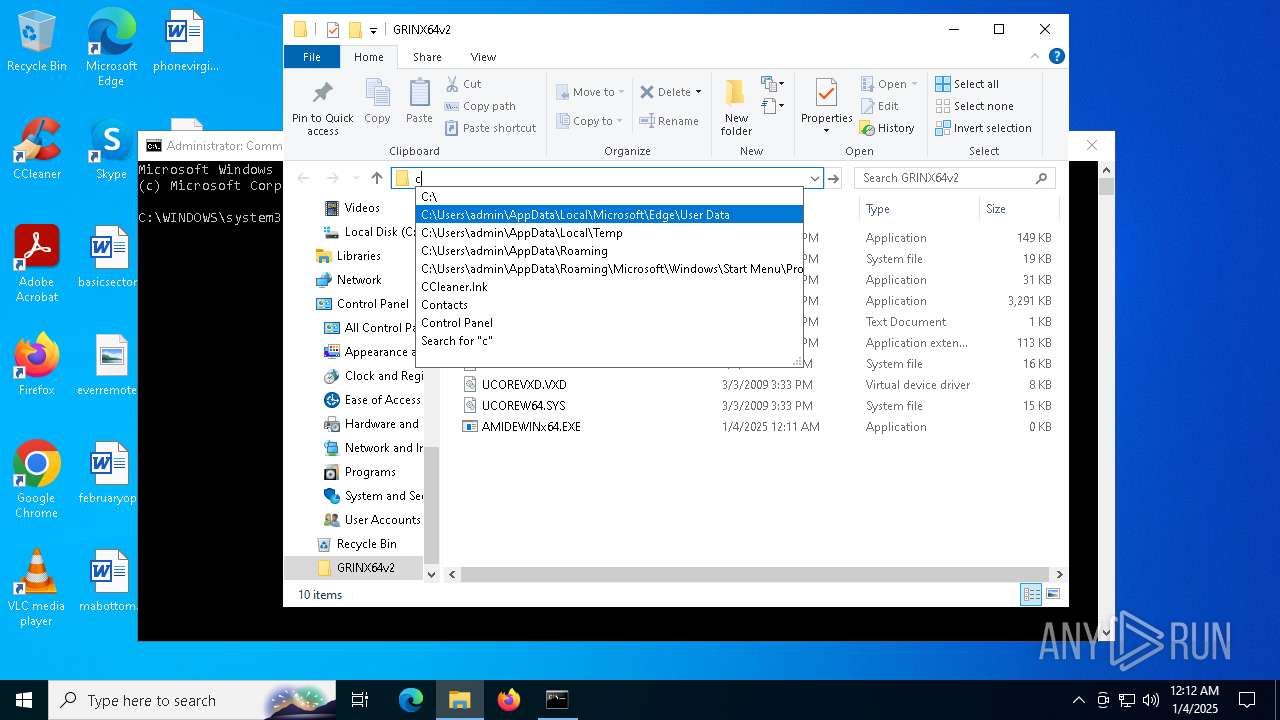
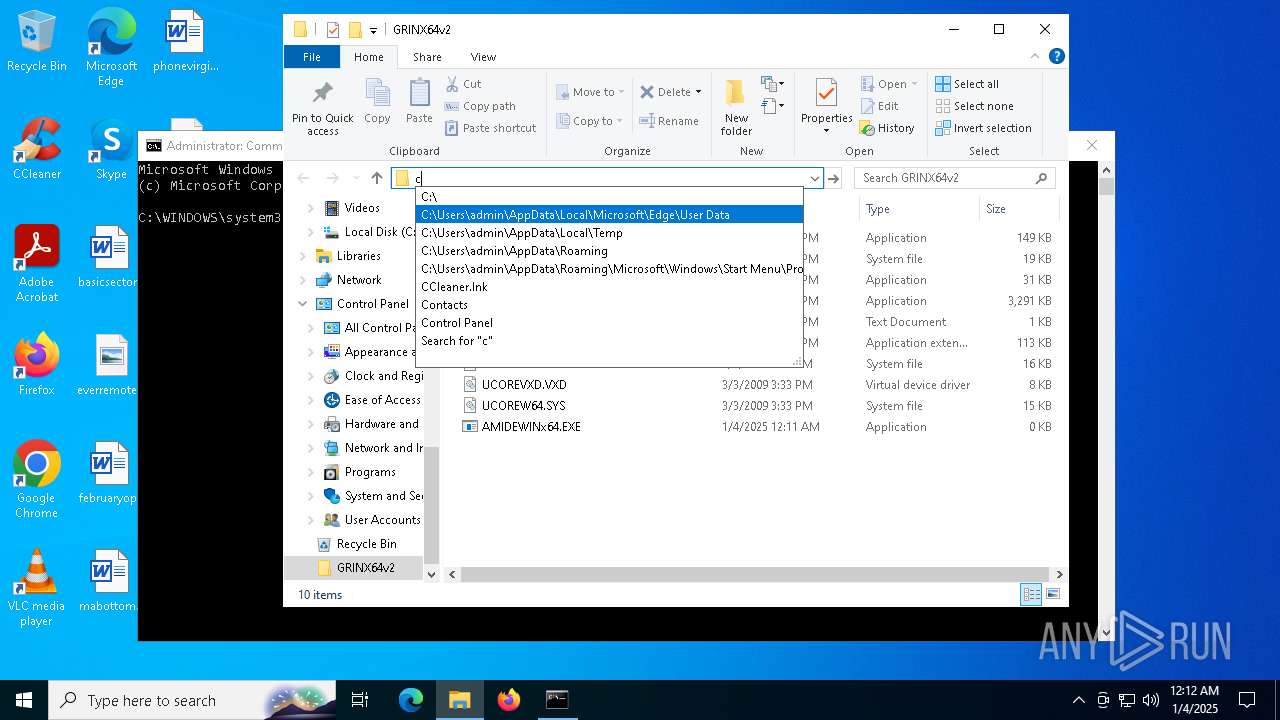
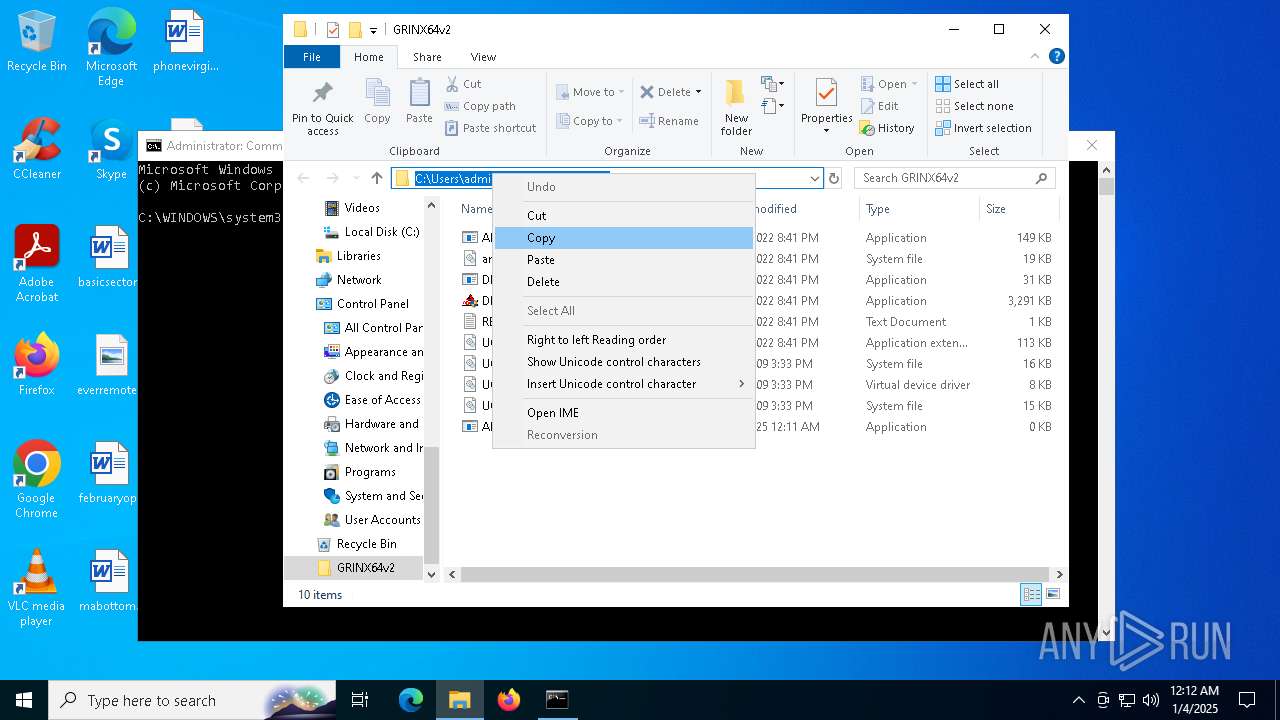
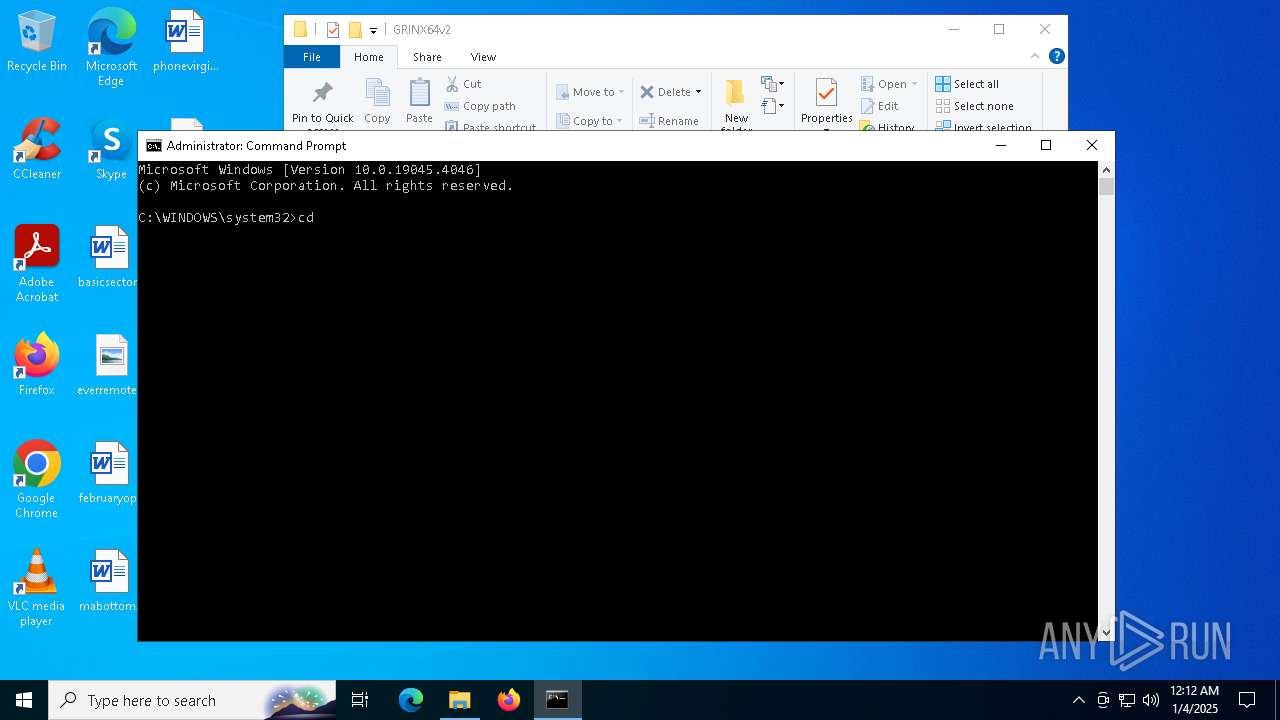
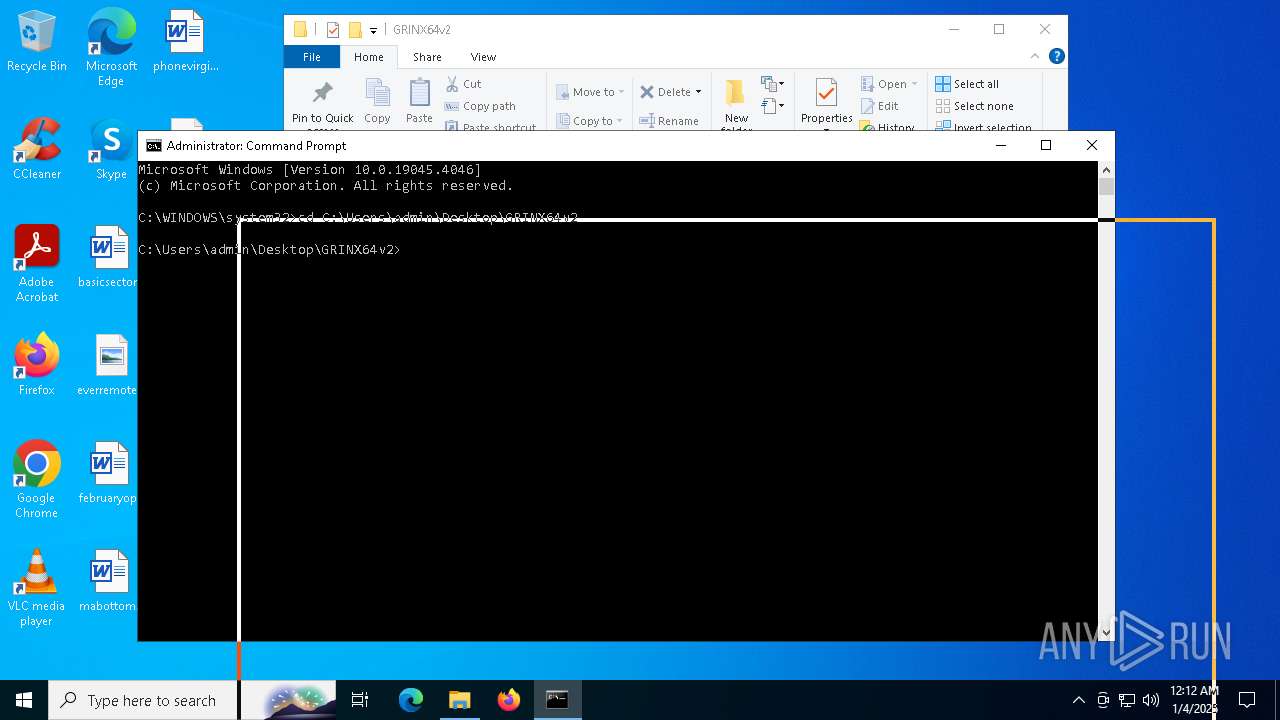
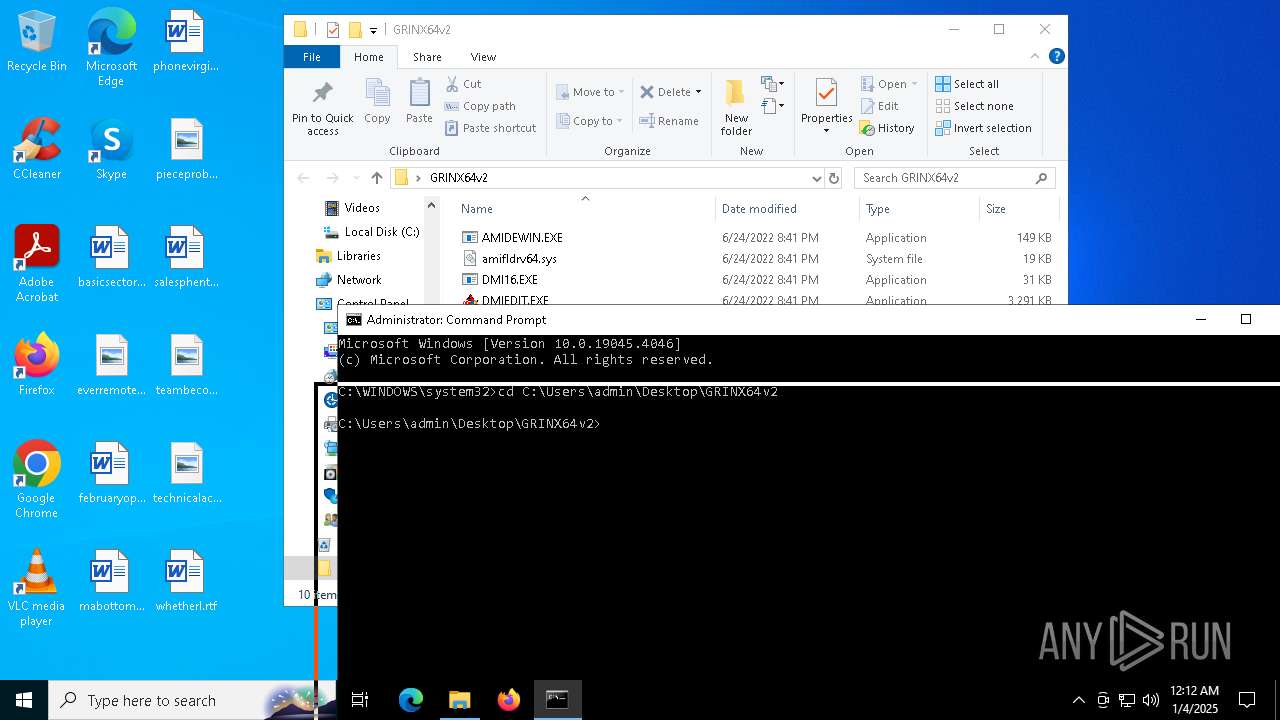
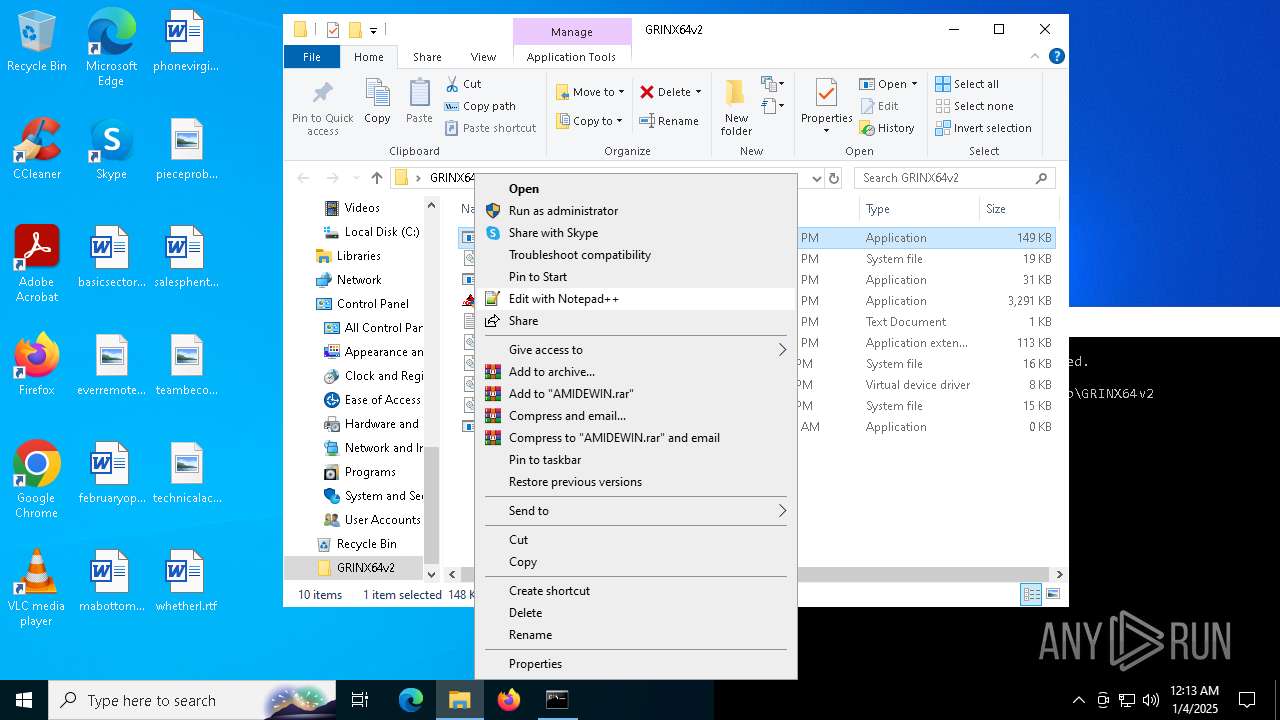
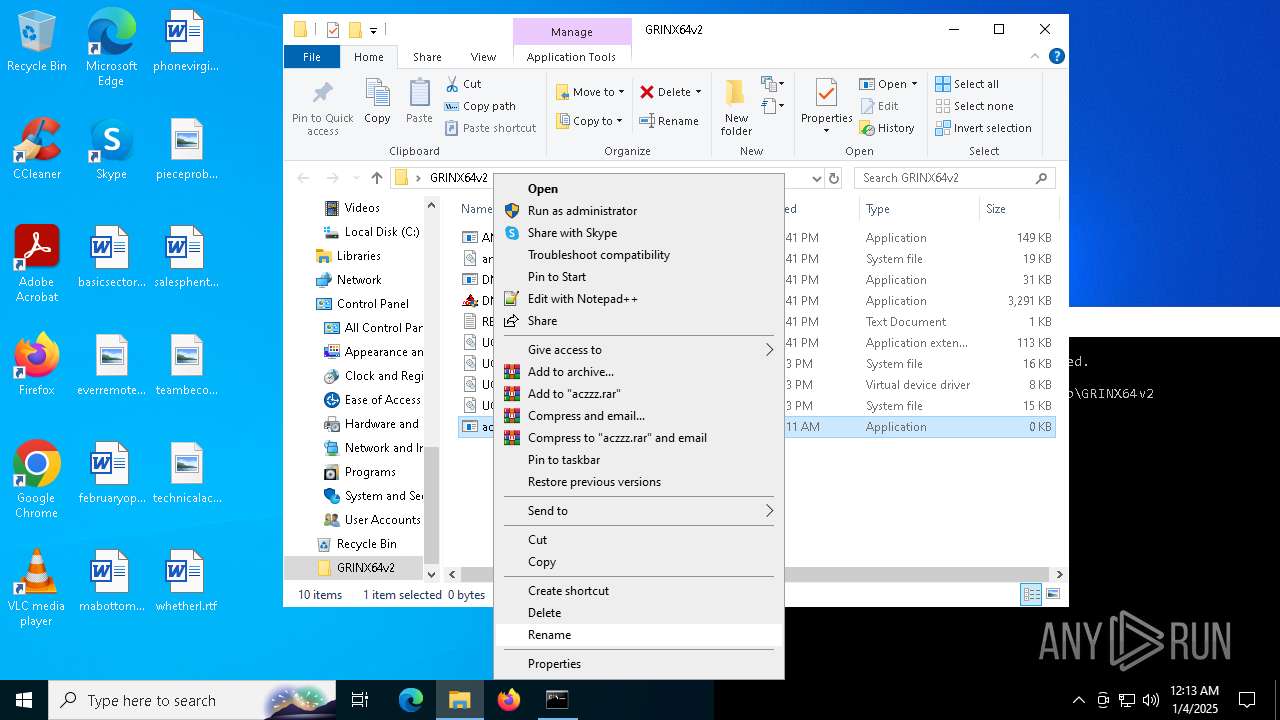
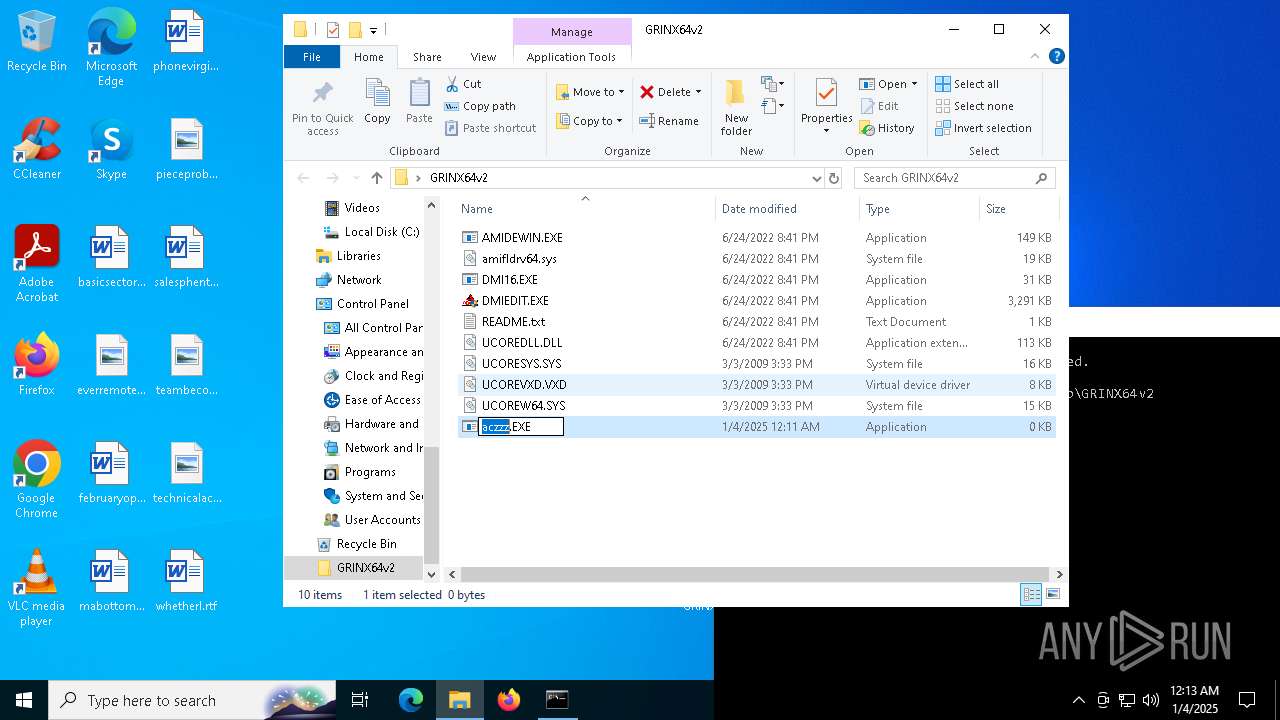
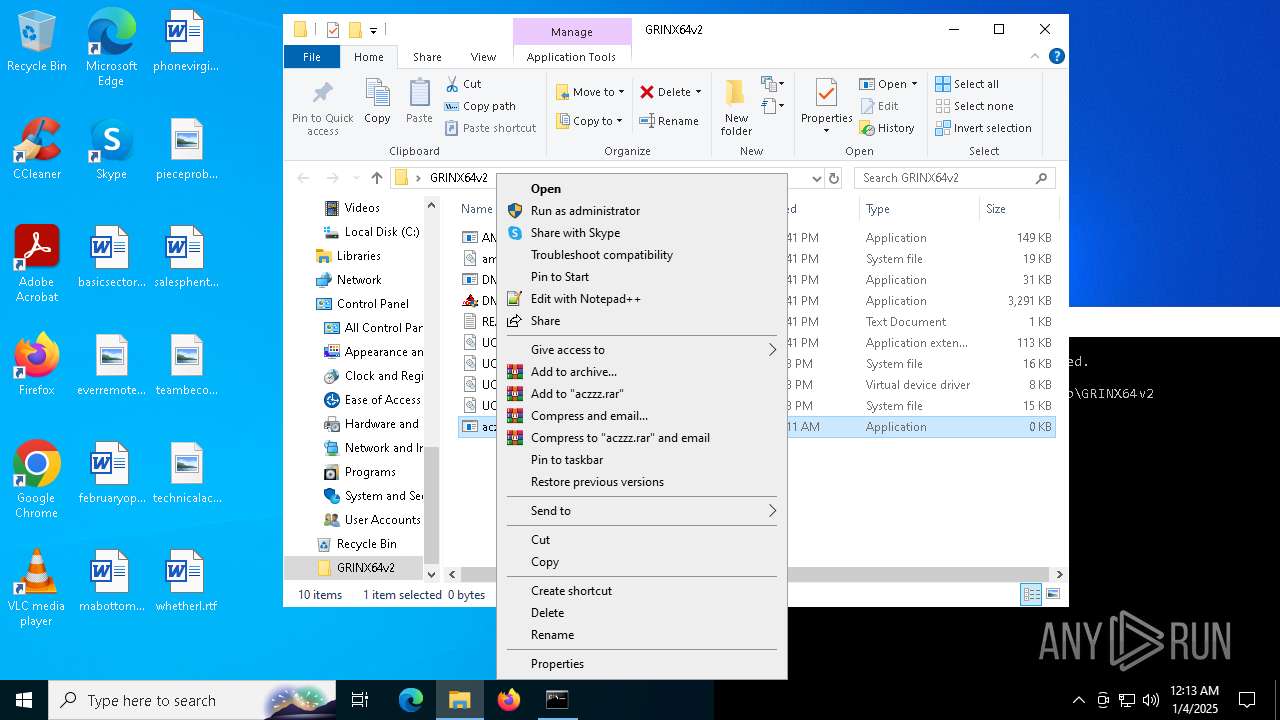
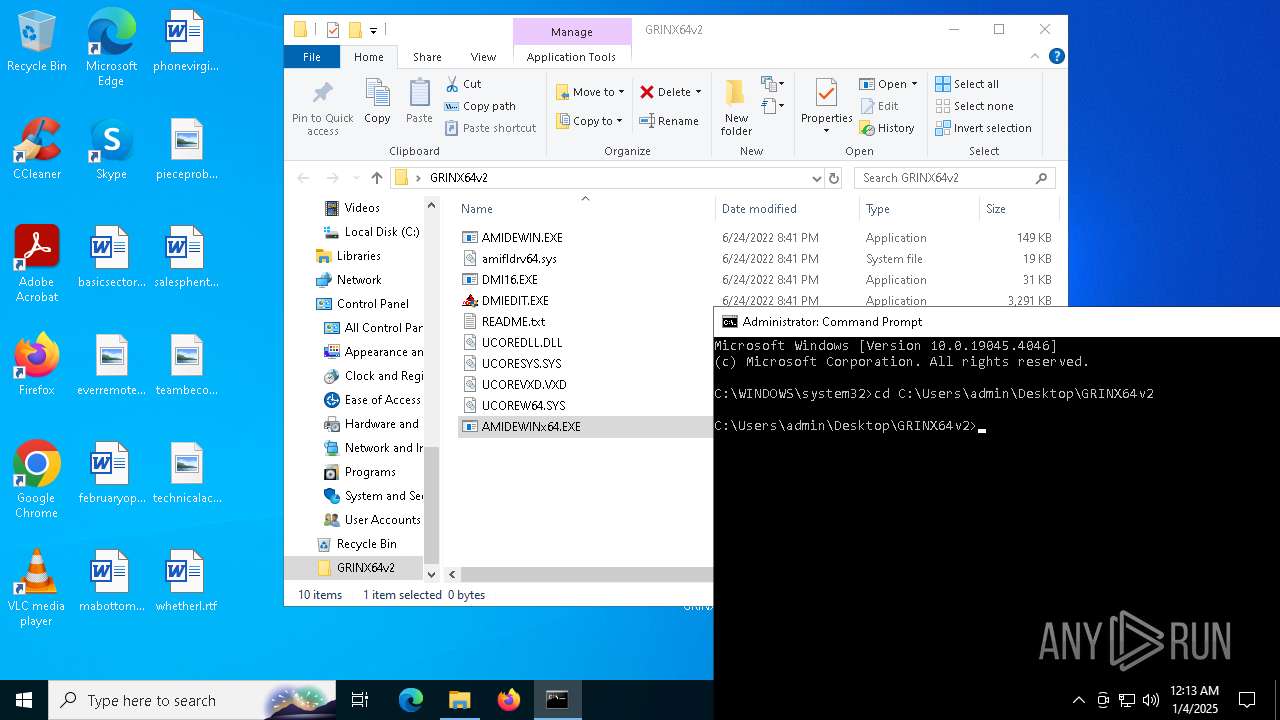
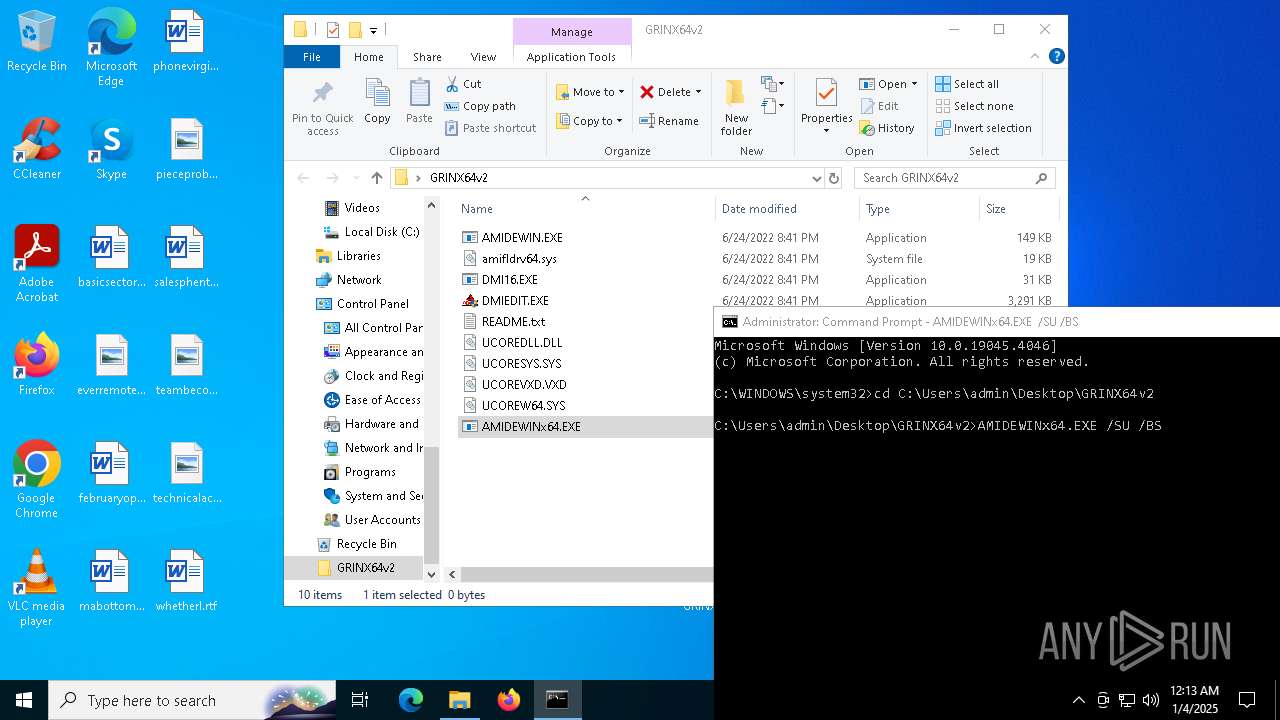
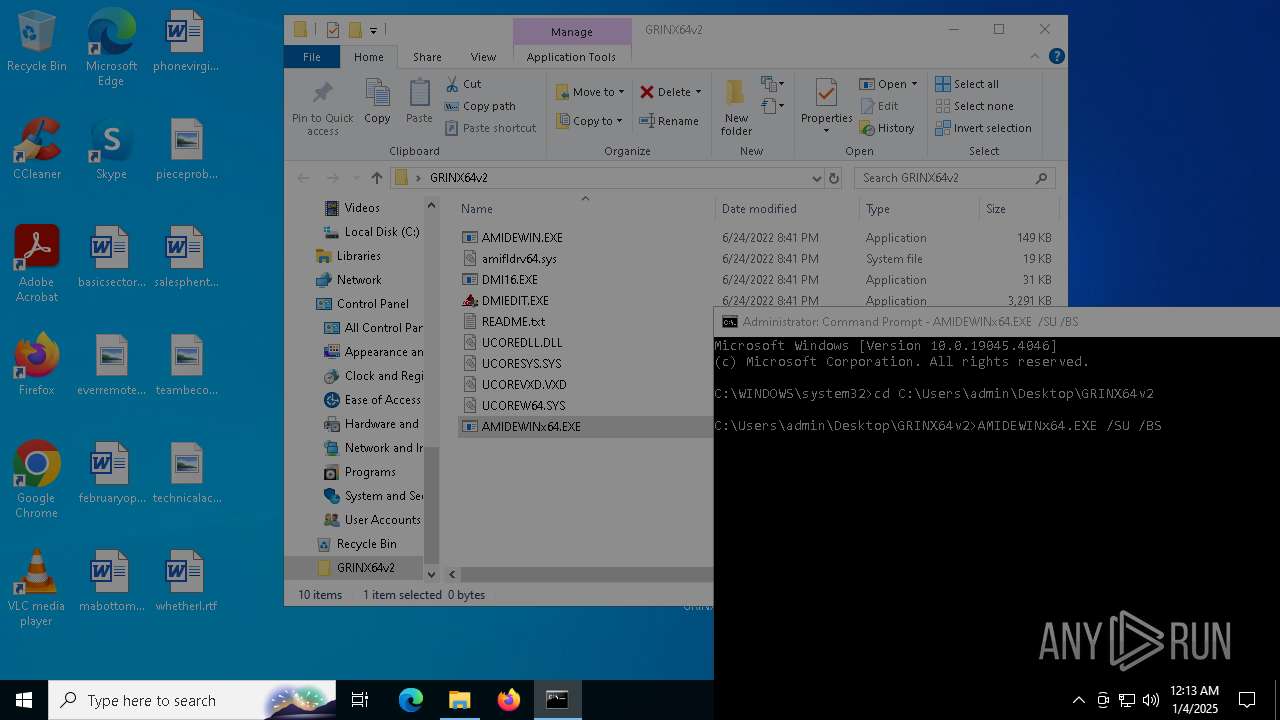
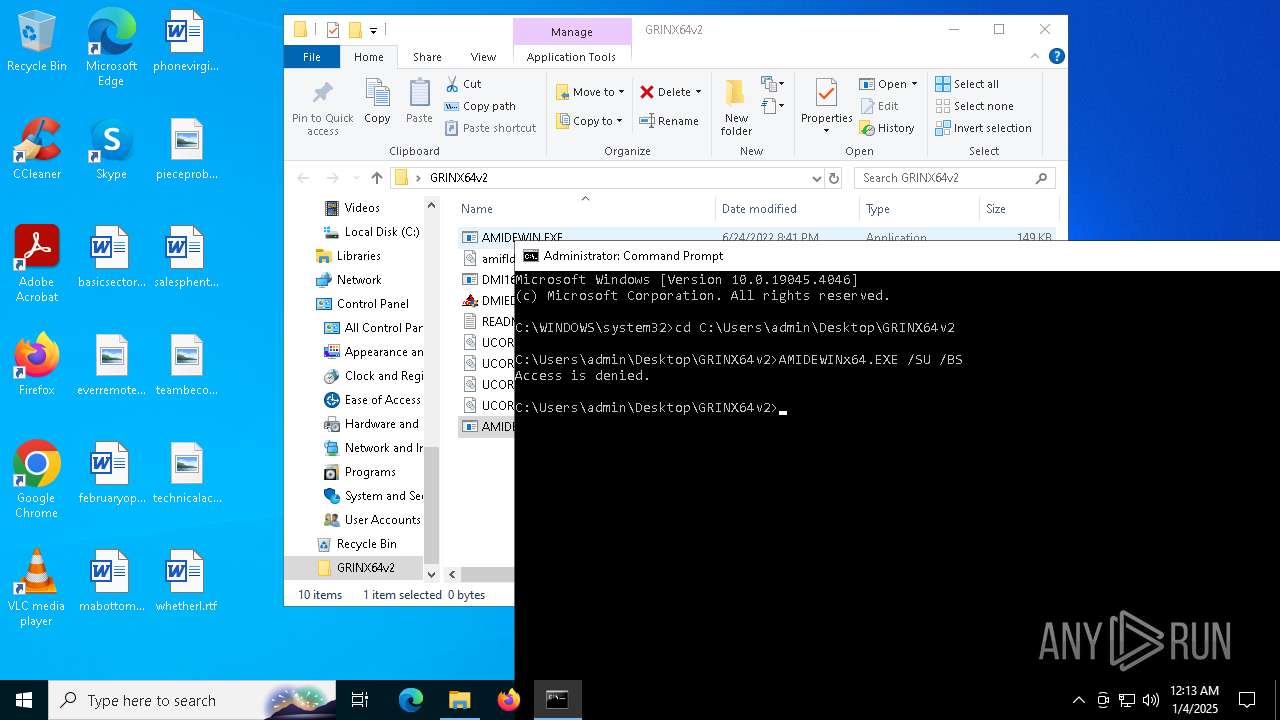
Manual execution by a user
- cmd.exe (PID: 6220)
- cmd.exe (PID: 2456)
The process uses the downloaded file
- WinRAR.exe (PID: 6380)
- cmd.exe (PID: 2456)
- cmd.exe (PID: 6220)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6380)
Checks supported languages
- AMIDEWINx64.EXE (PID: 5092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 51798 |
| UncompressedSize: | 151664 |
| OperatingSystem: | Win32 |
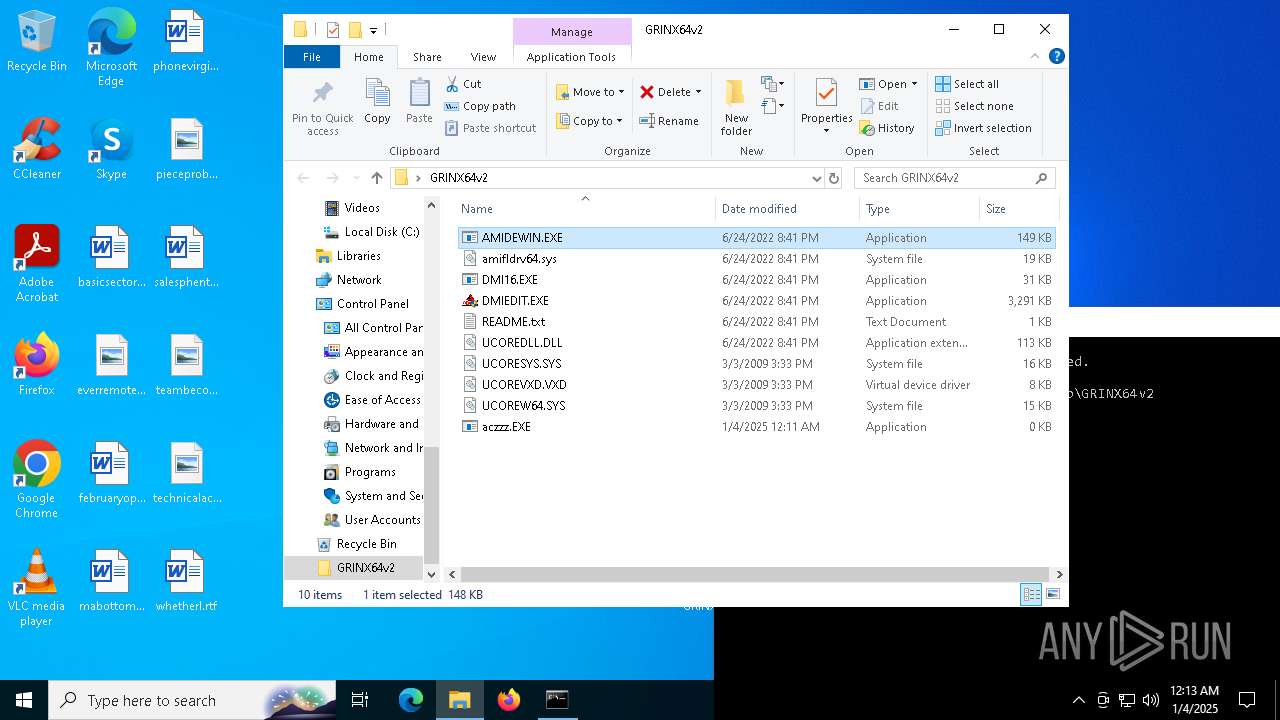
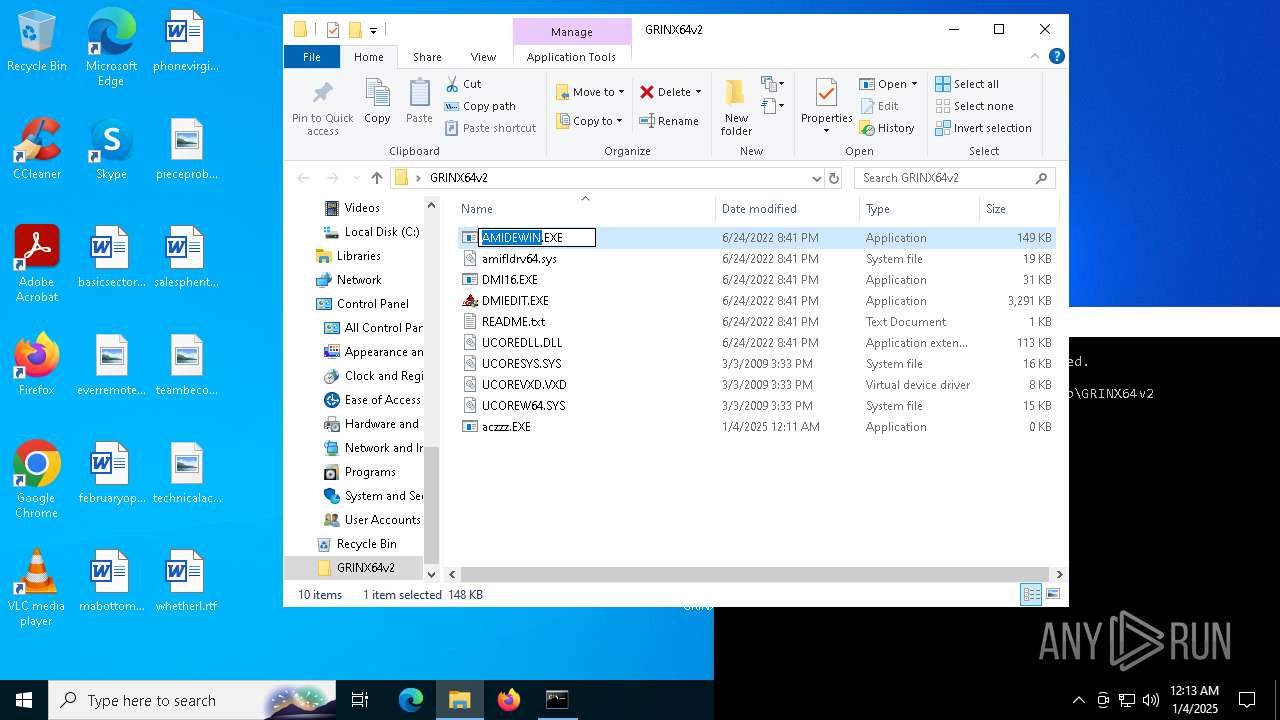
| ArchivedFileName: | GRINX64v2/AMIDEWIN.EXE |
Total processes
144
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
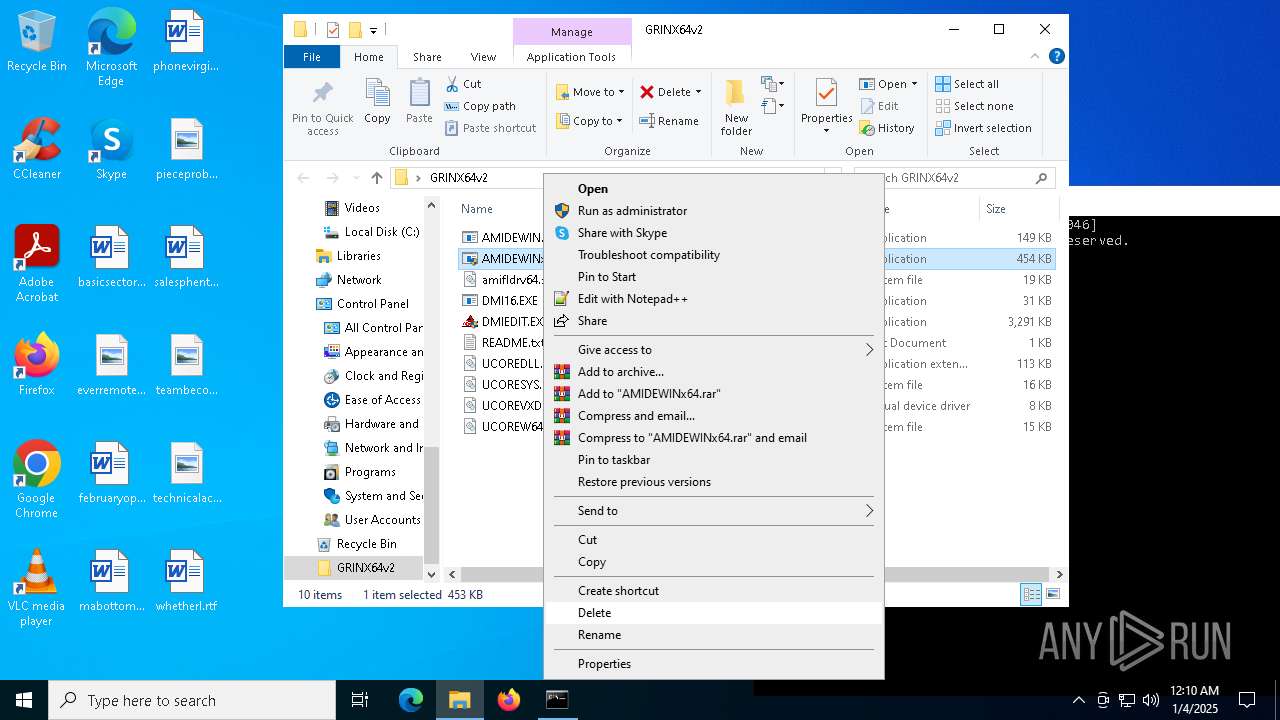
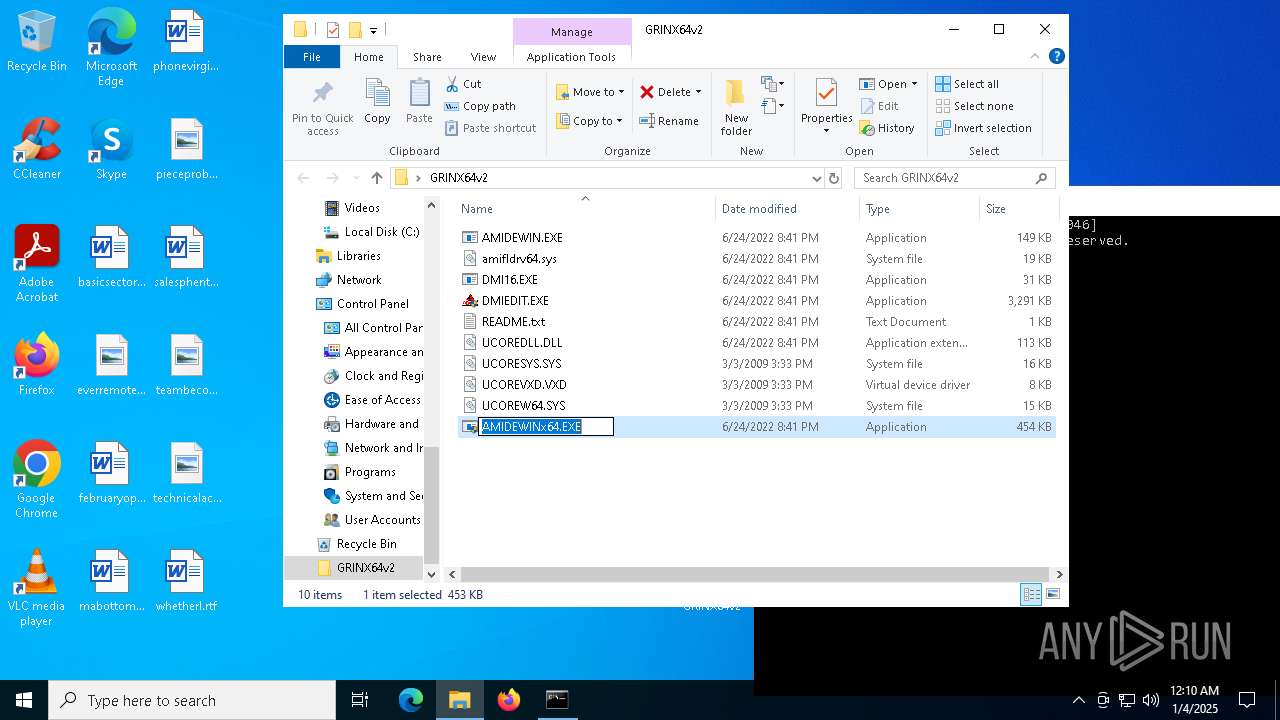
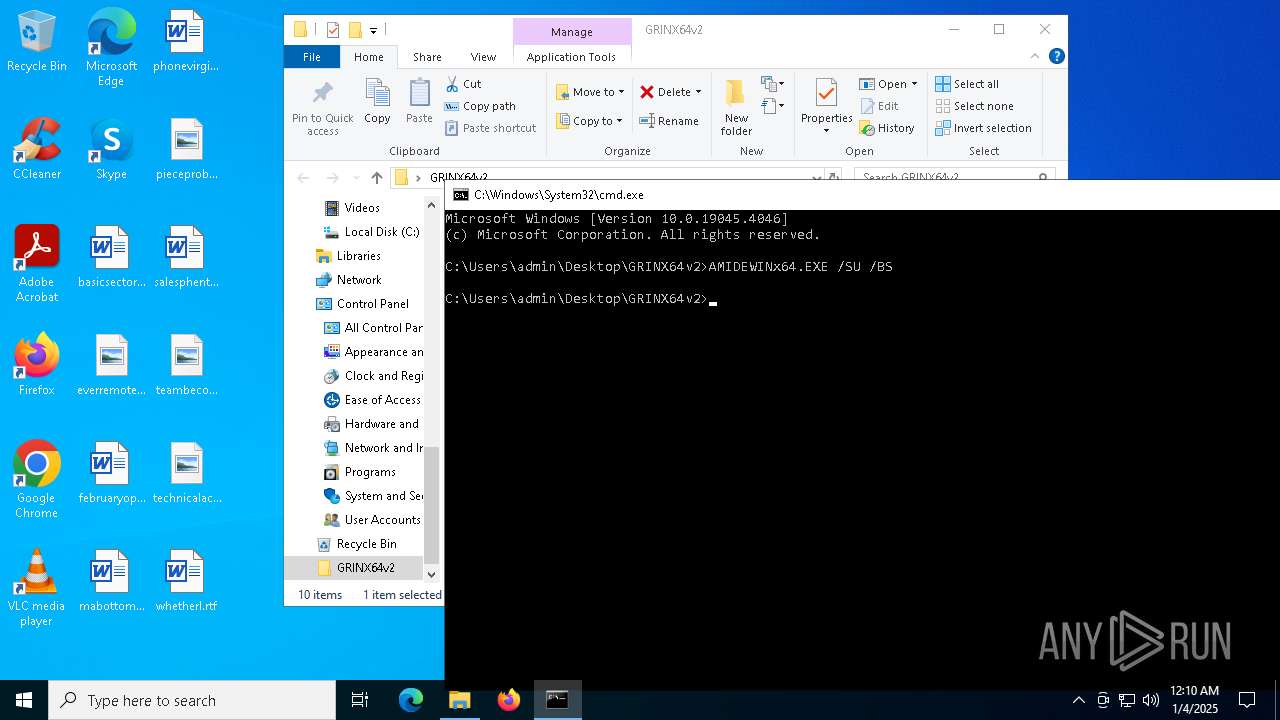
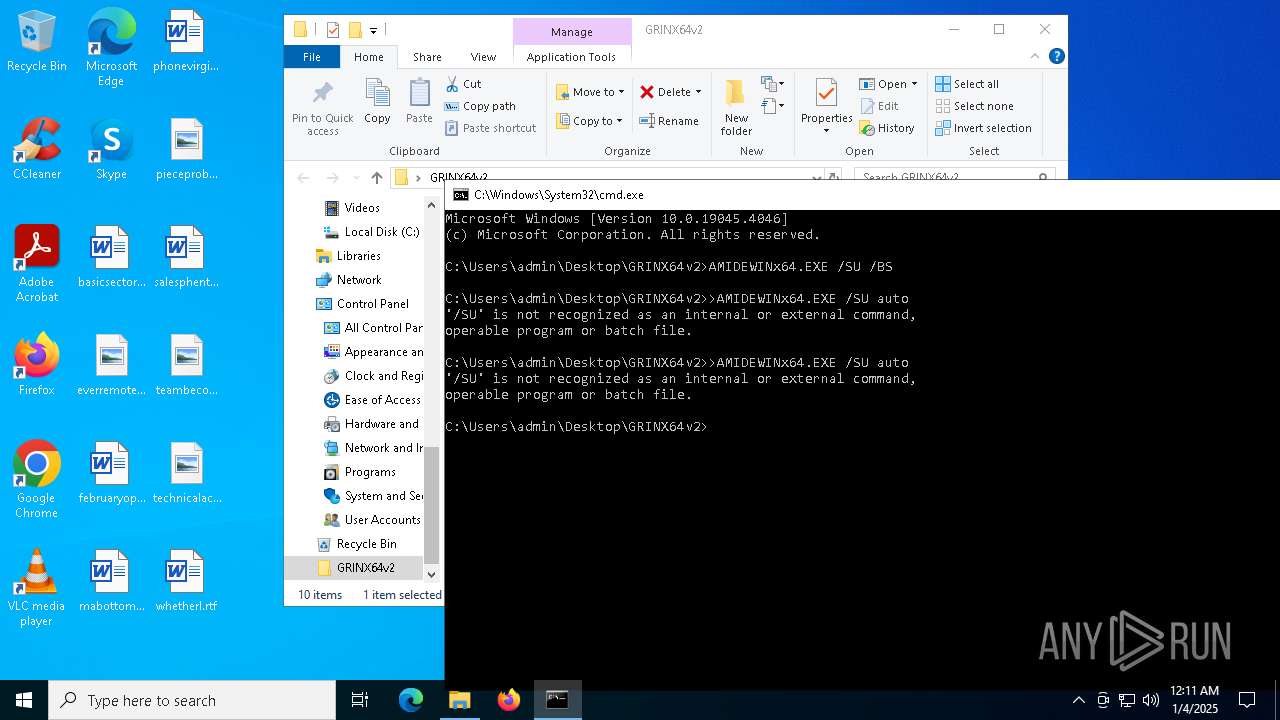
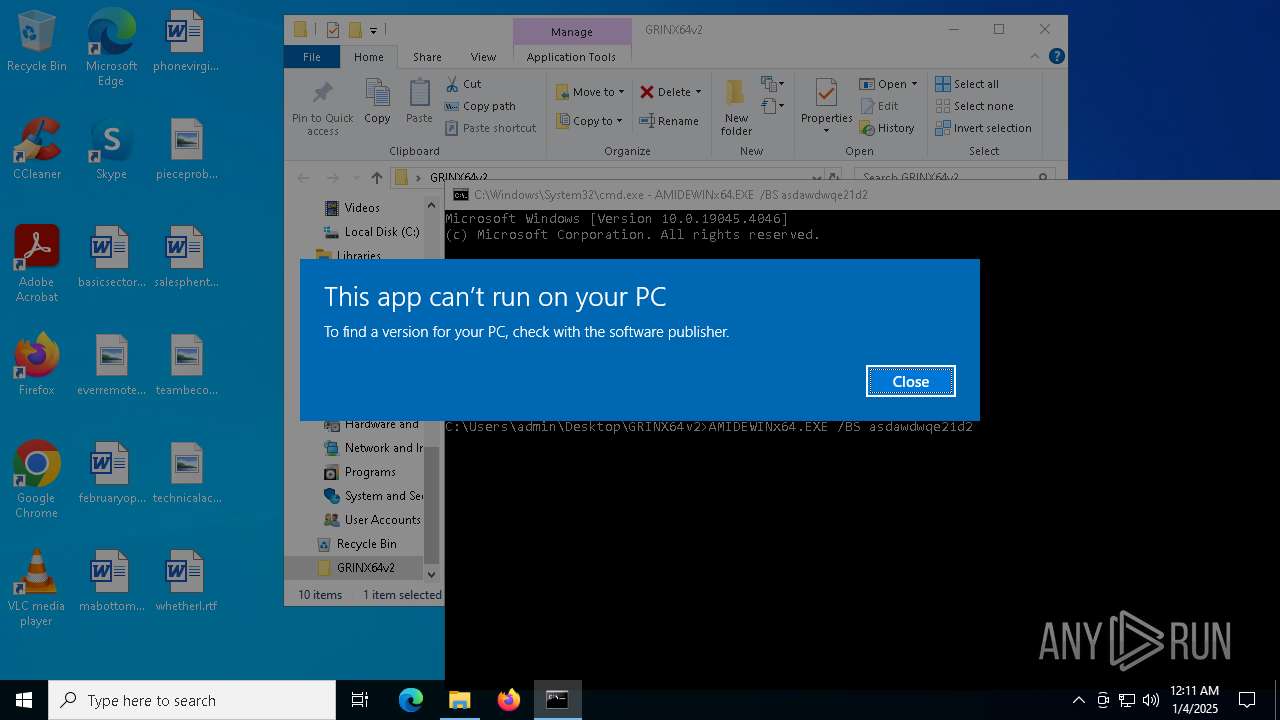
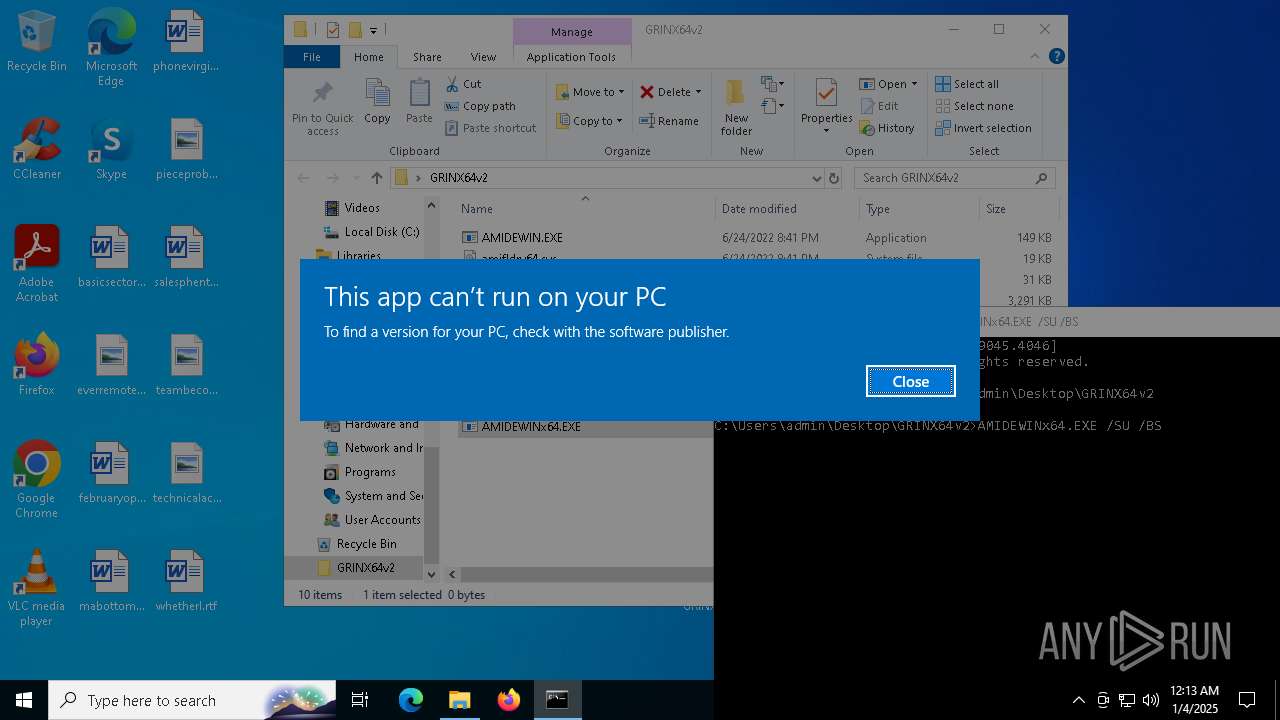
| 2440 | AMIDEWINx64.EXE /SU /BS | C:\Users\admin\Desktop\GRINX64v2\AMIDEWINx64.EXE | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2456 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AMIDEWINx64.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | "C:\Users\admin\Desktop\GRINX64v2\AMIDEWINx64.EXE" /SU /BS | C:\Users\admin\Desktop\GRINX64v2\AMIDEWINx64.EXE | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5092 | "C:\Users\admin\Desktop\GRINX64v2\AMIDEWINx64.EXE" /SU /BS | C:\Users\admin\Desktop\GRINX64v2\AMIDEWINx64.EXE | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 216 Modules
| |||||||||||||||
| 5556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6220 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6260 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6380 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\GRINX64v2.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7112 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 696
Read events
2 678
Write events
18
Delete events
0
Modification events
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GRINX64v2.rar | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
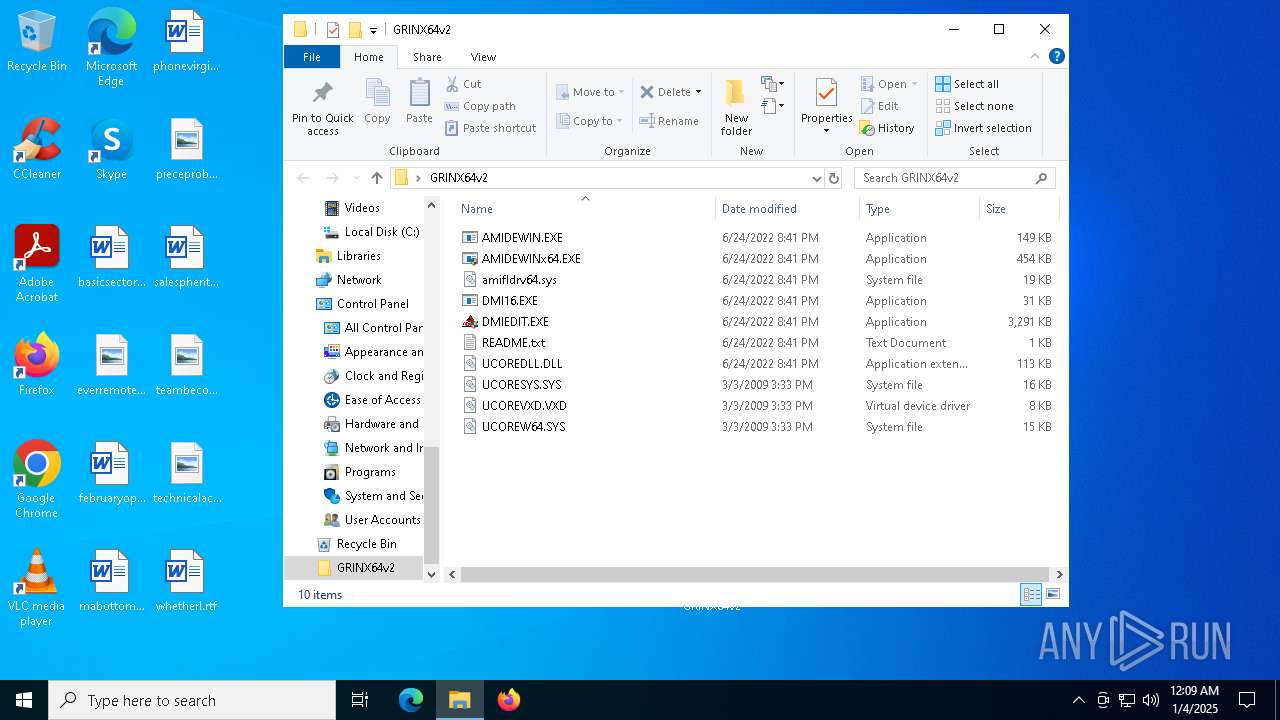
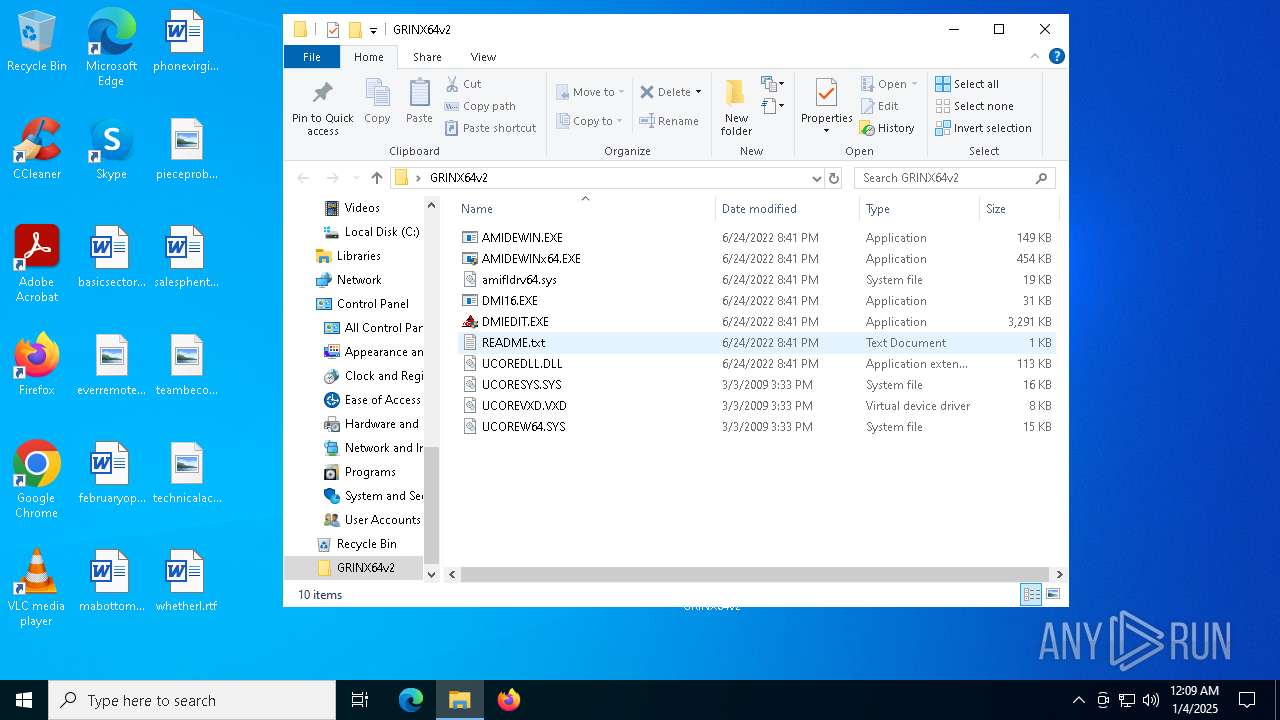
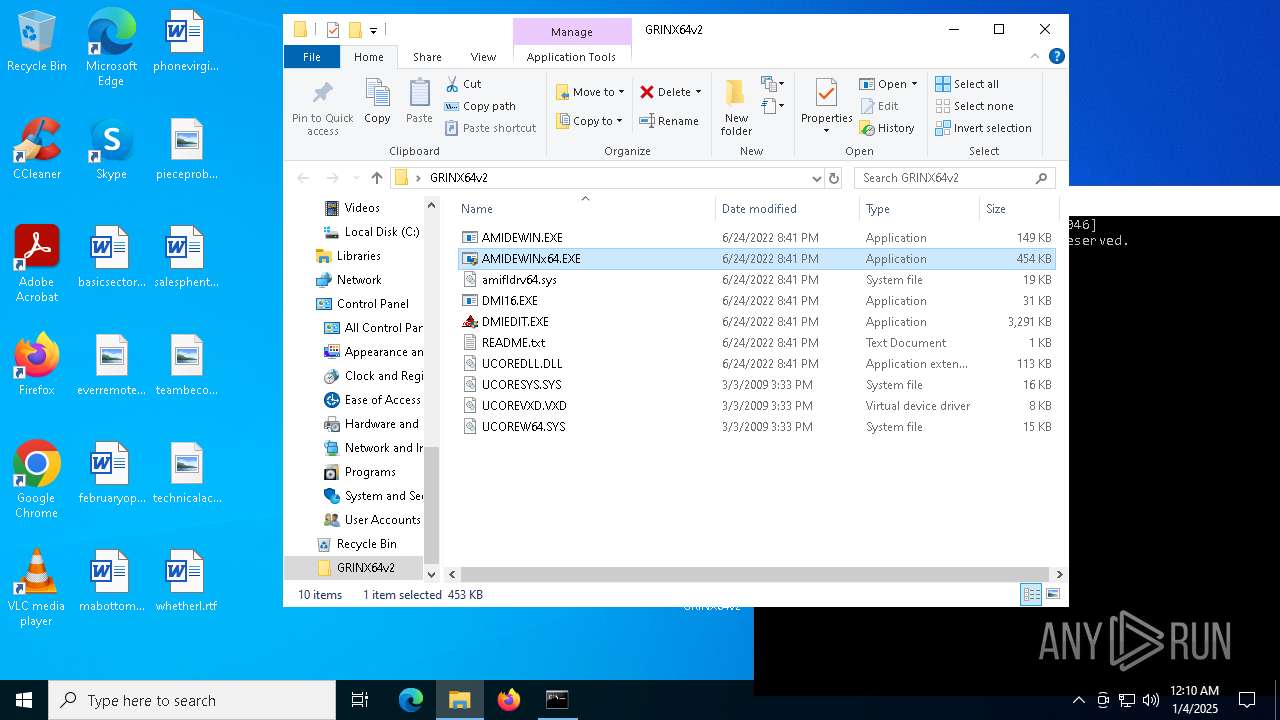
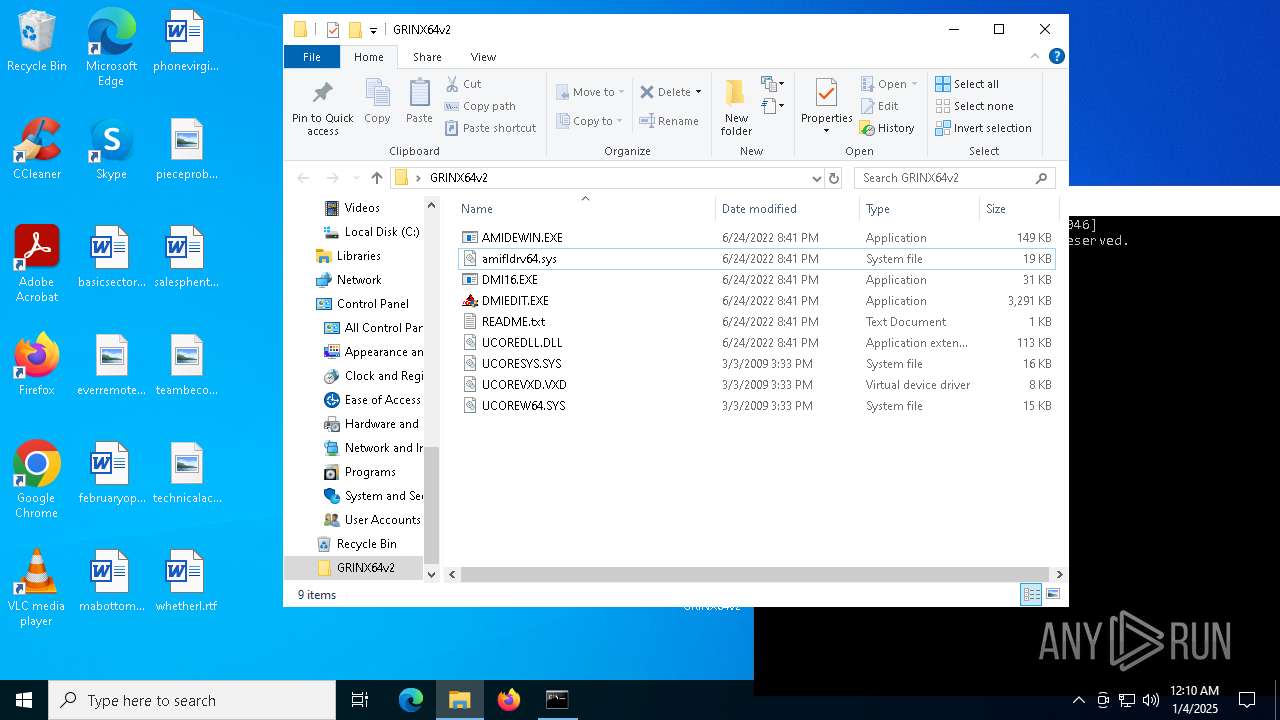
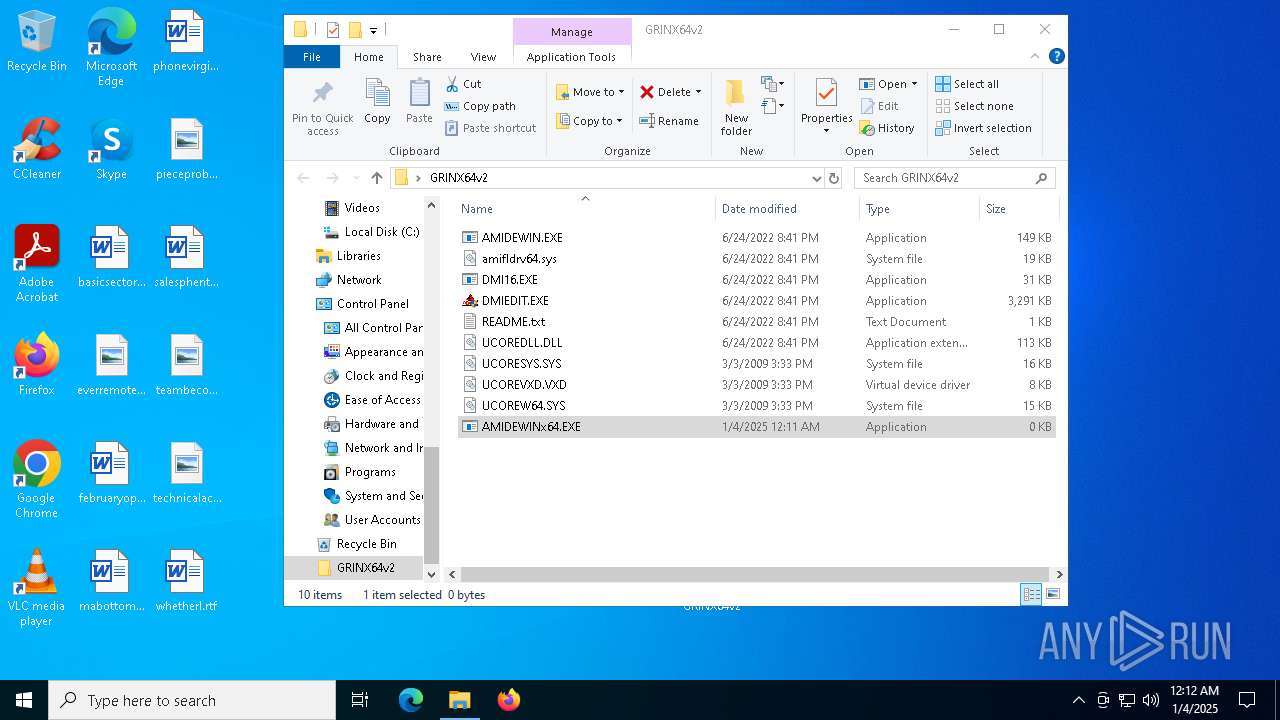
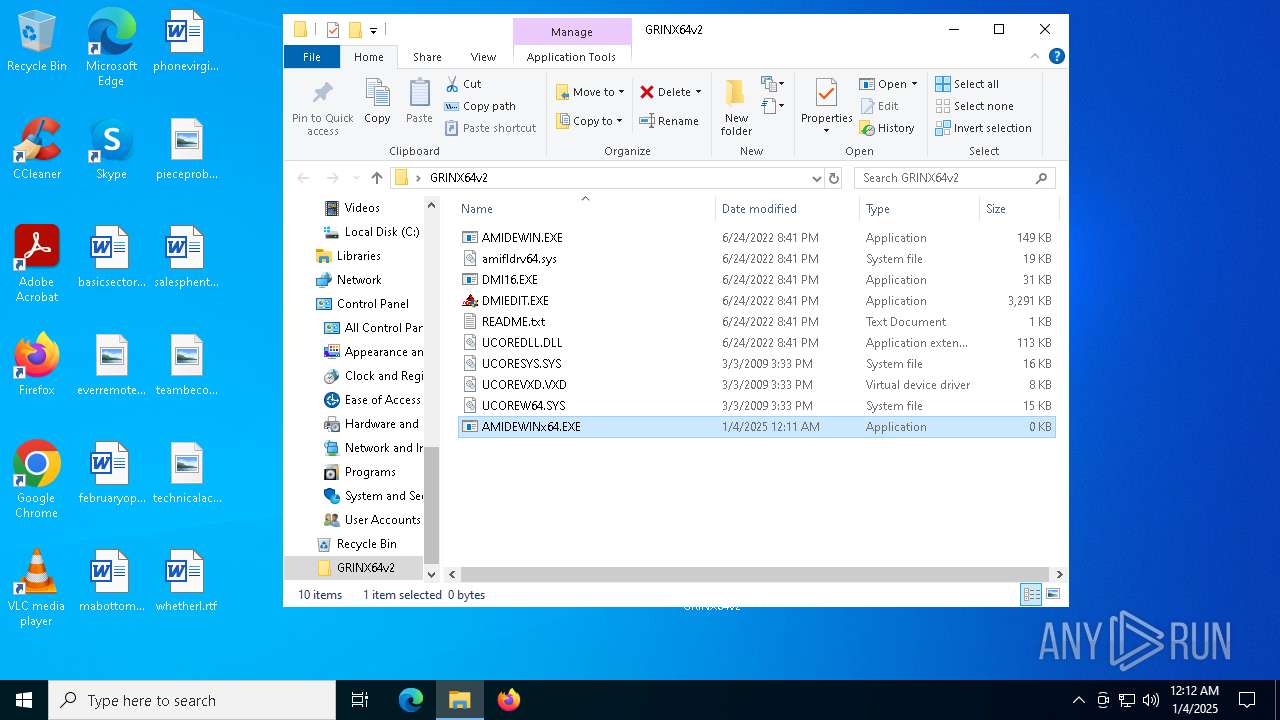
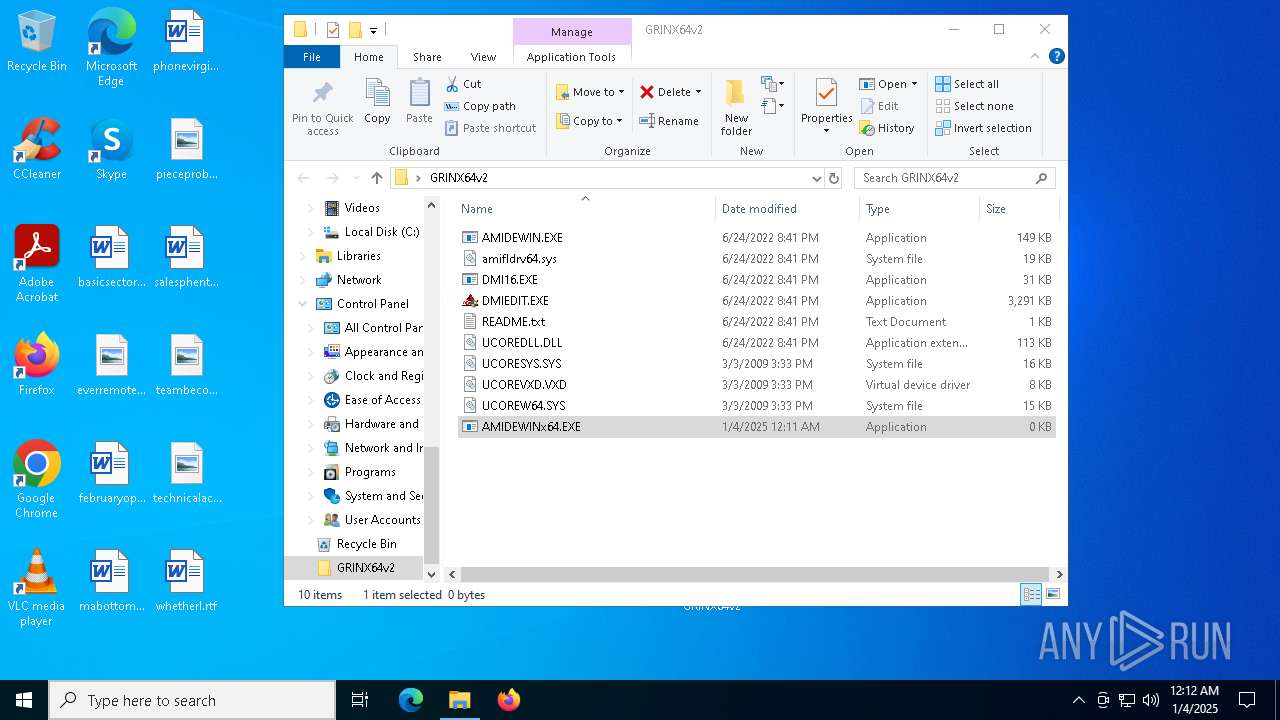
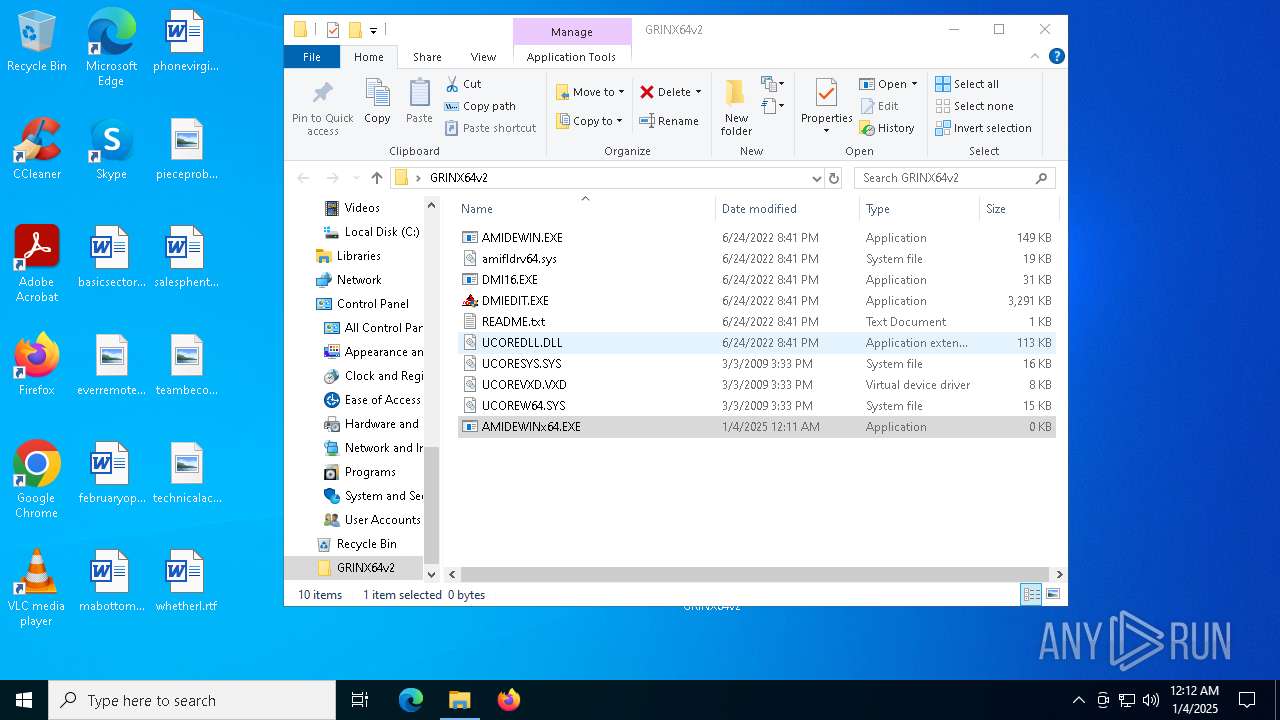
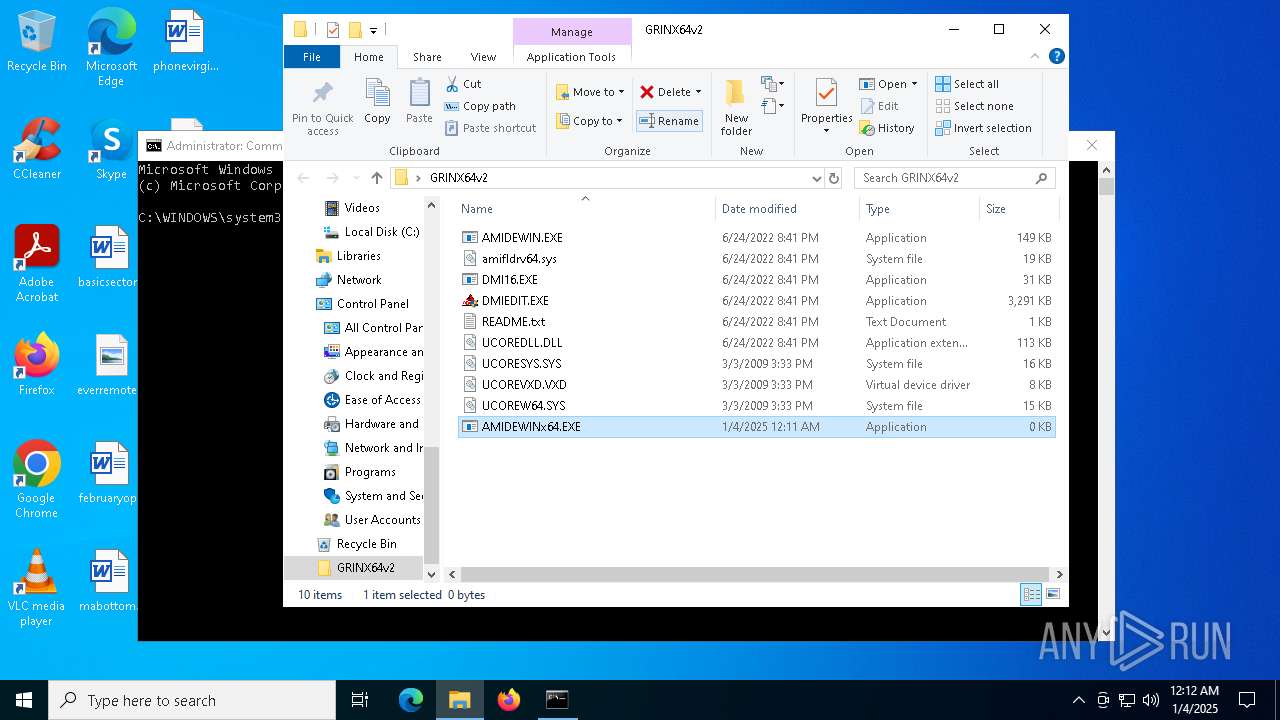
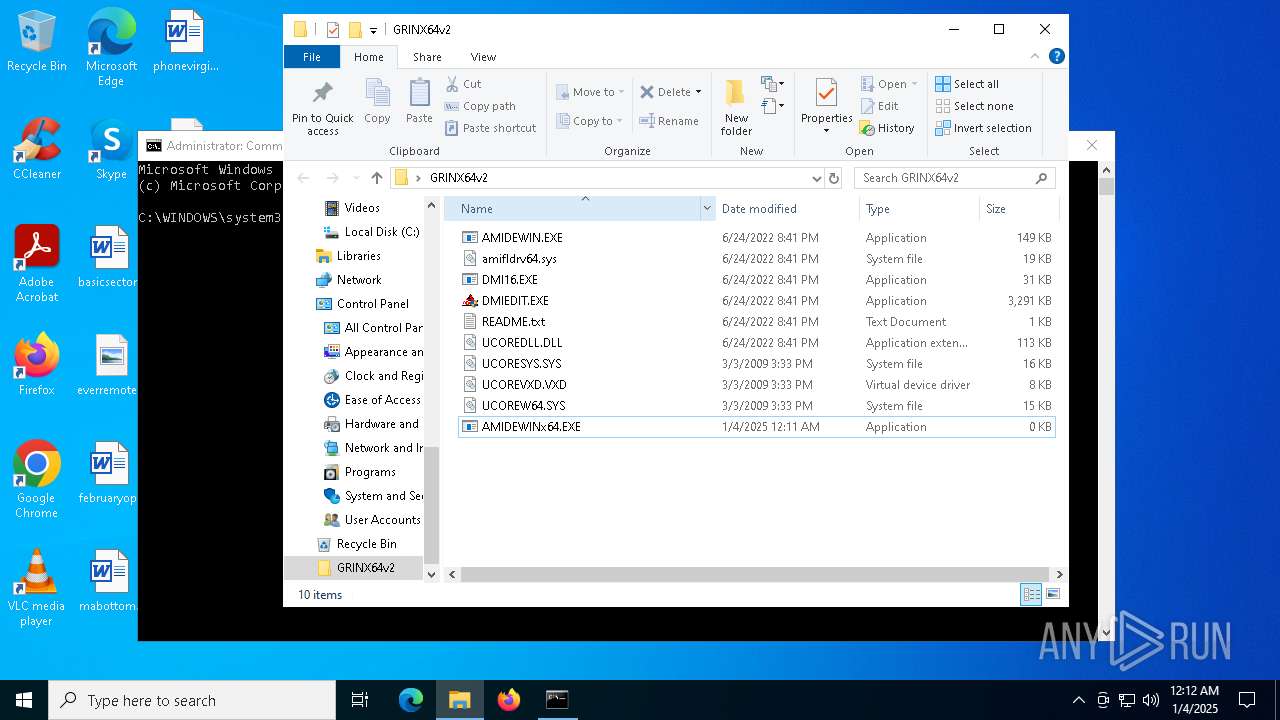
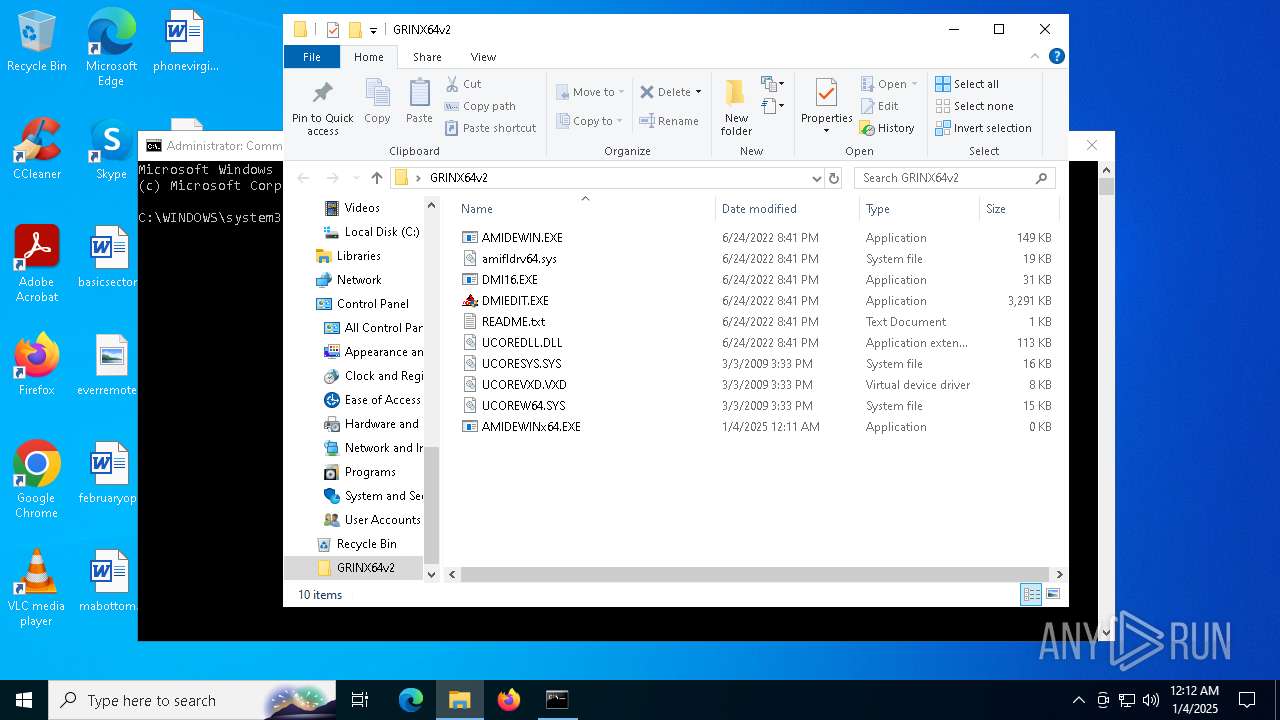
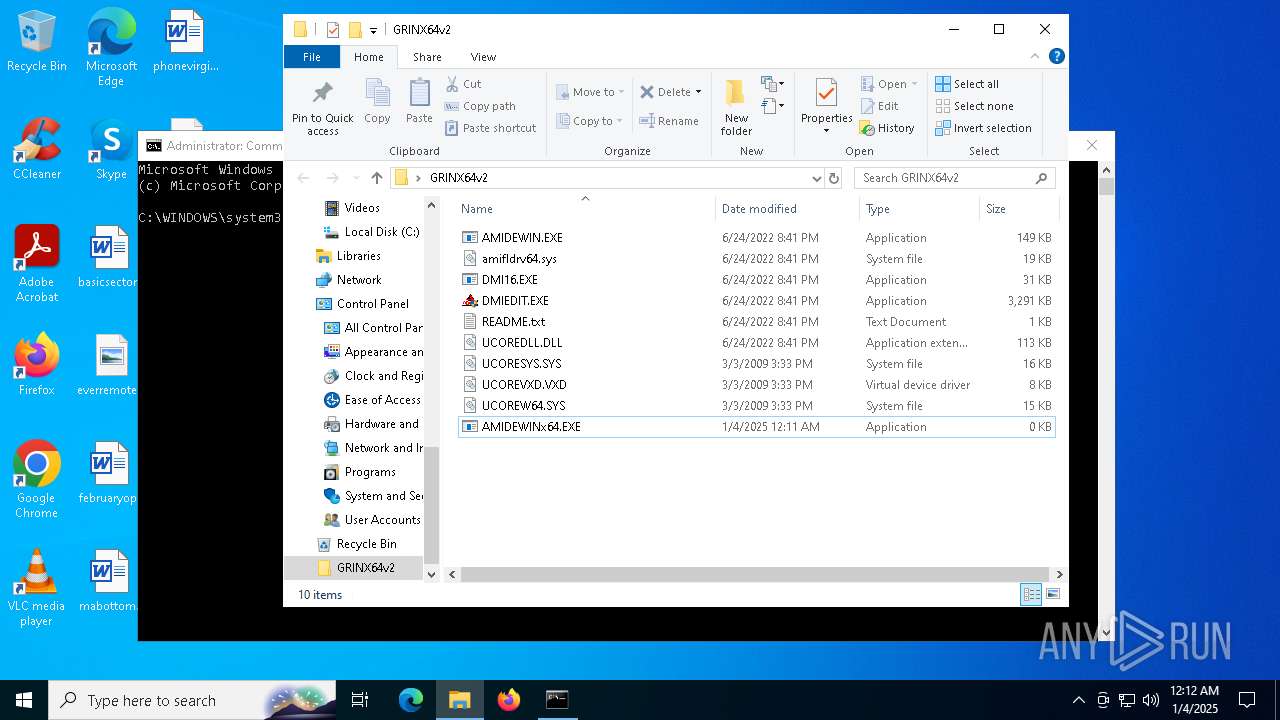
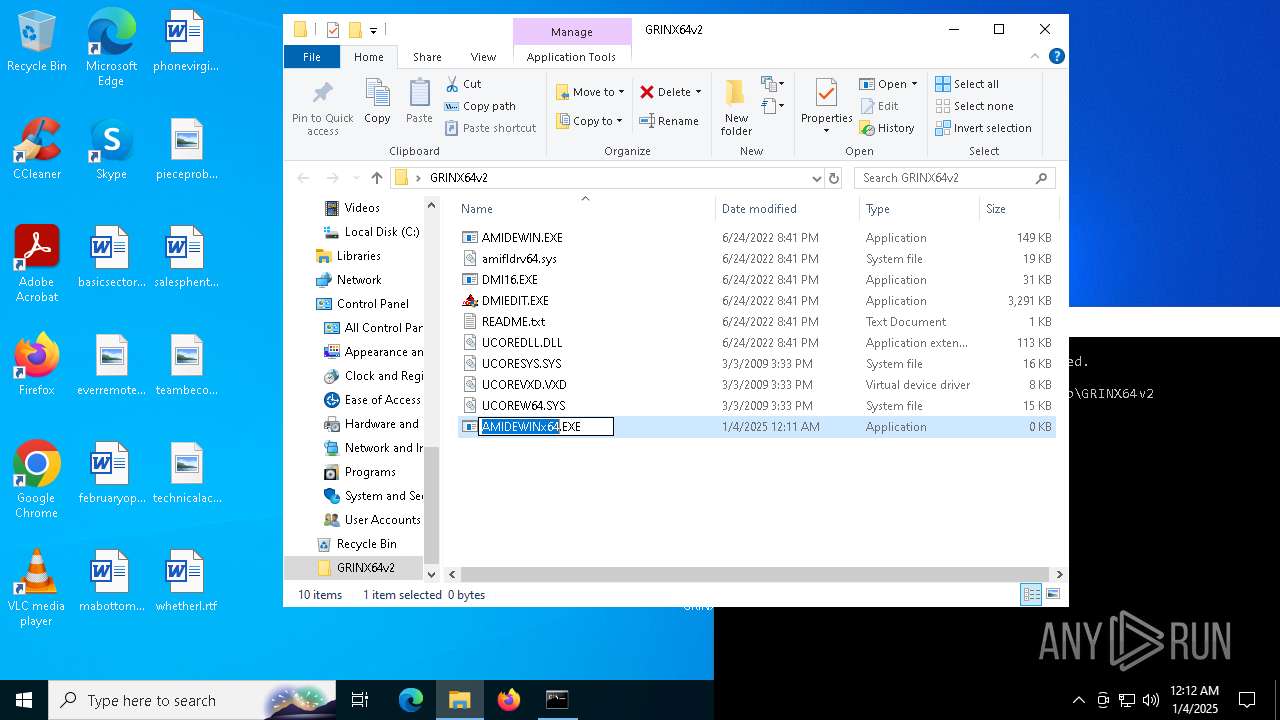
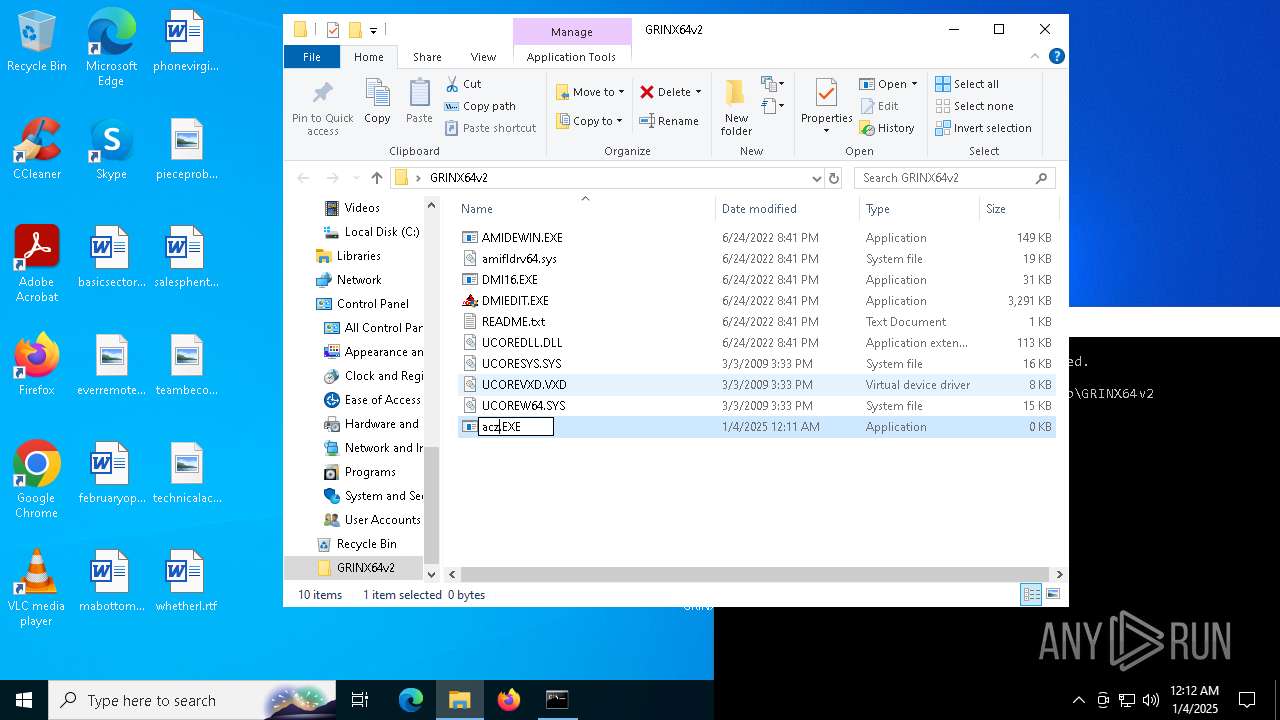
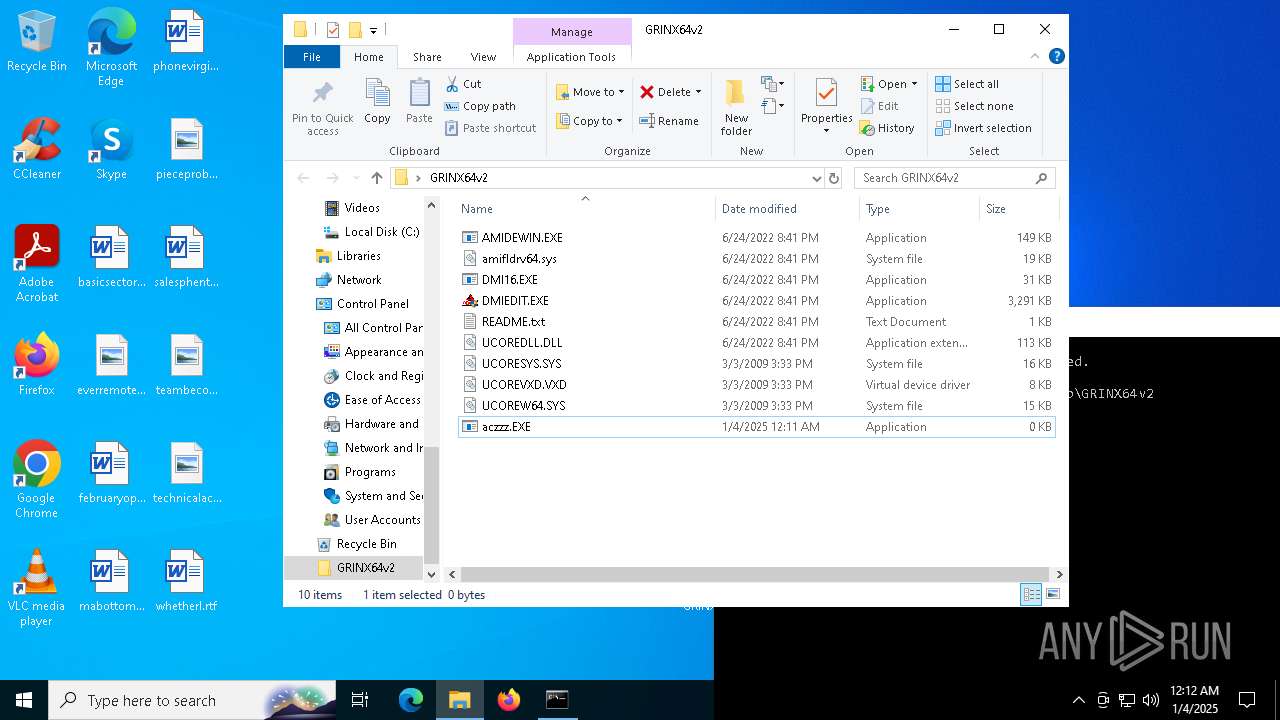
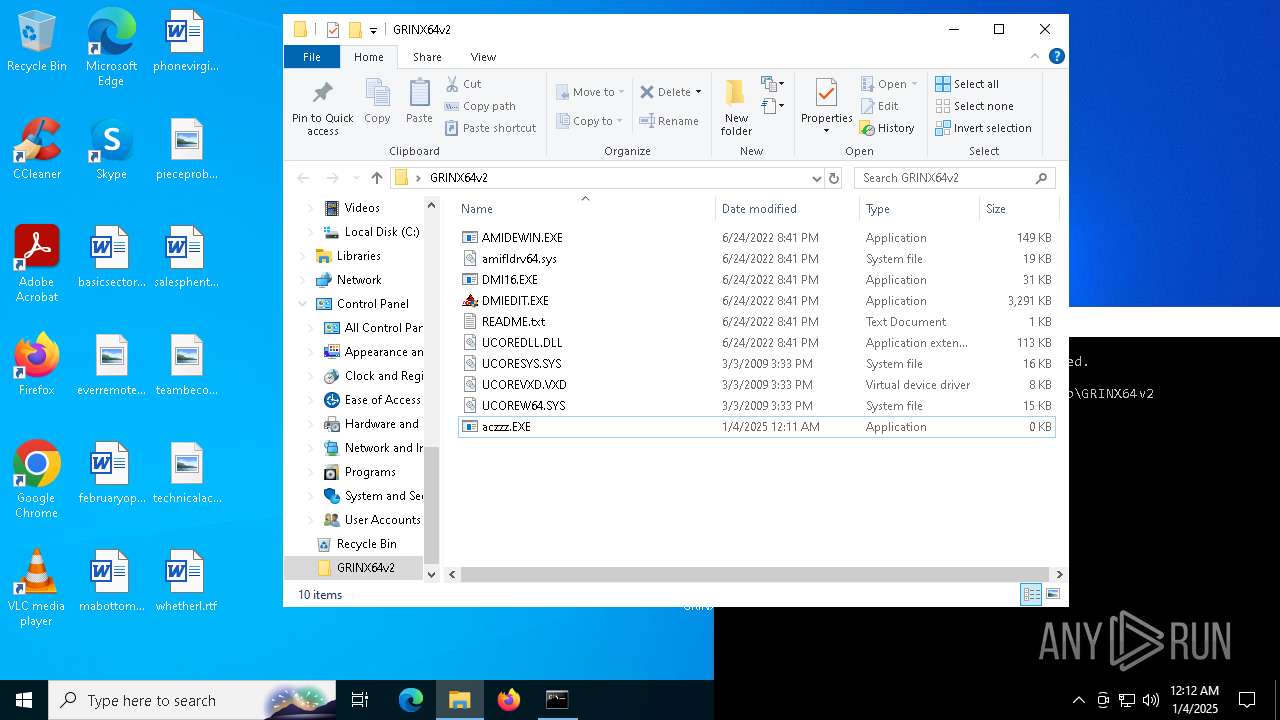
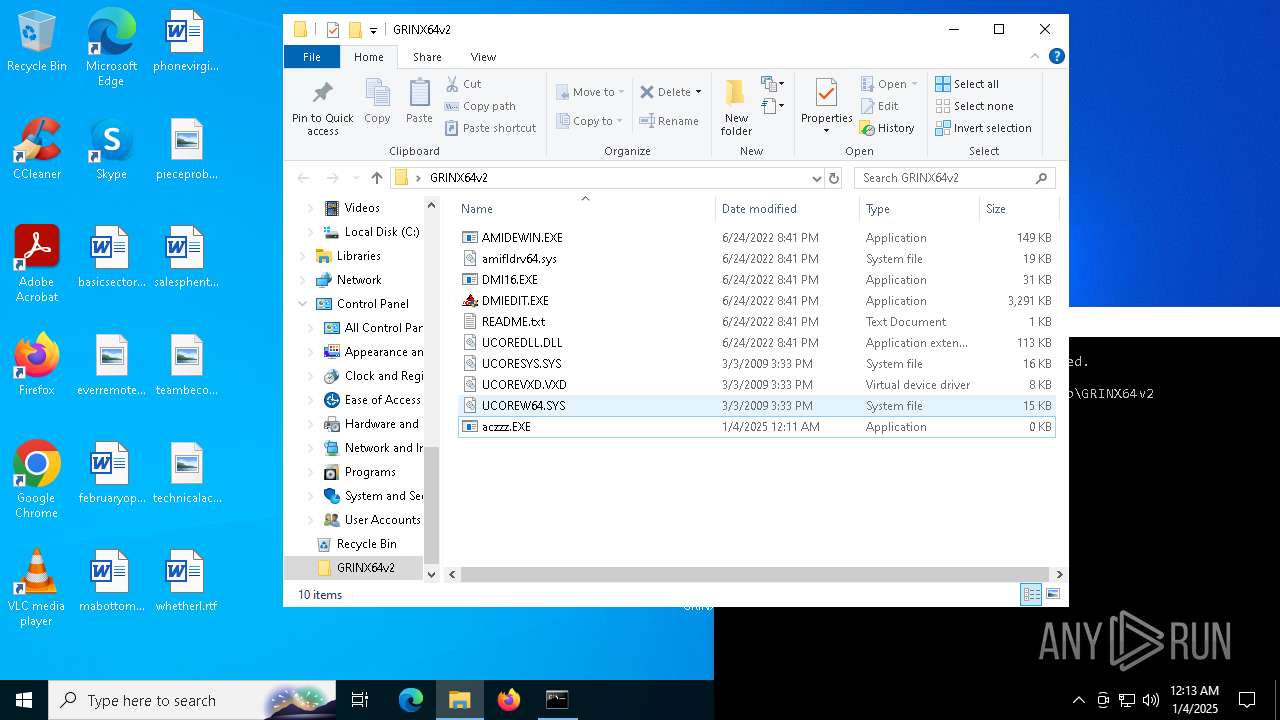
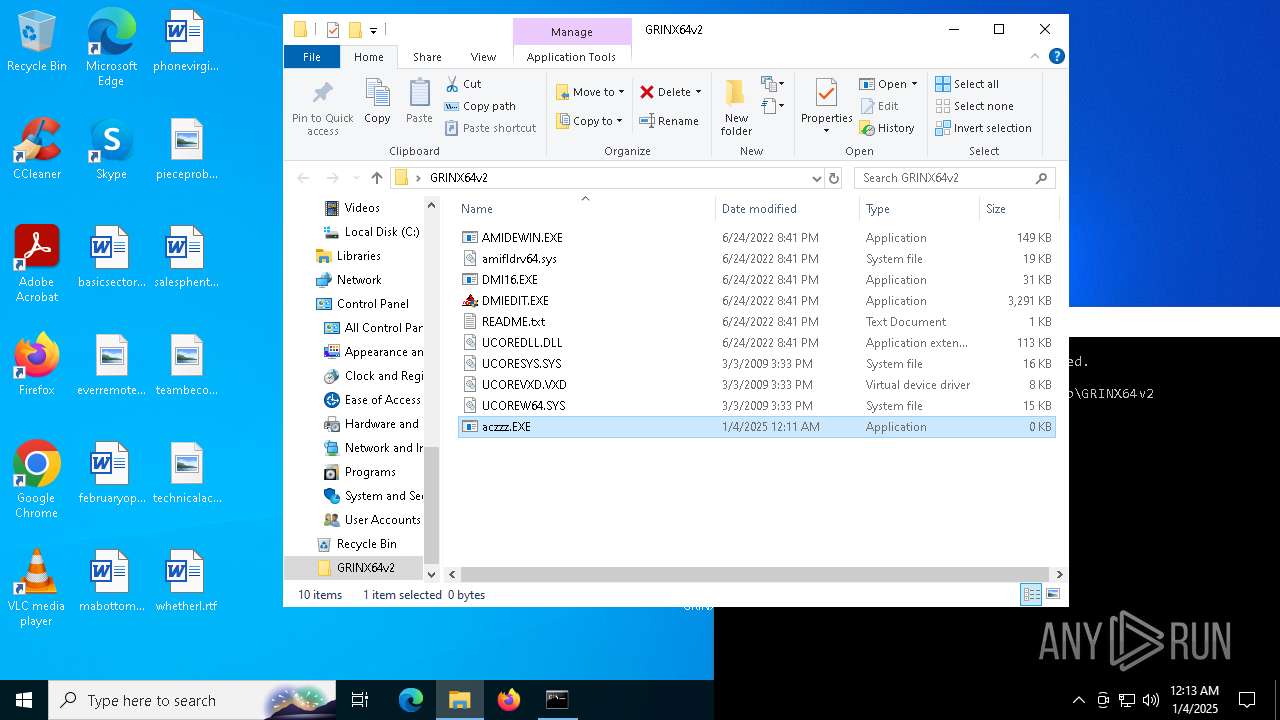
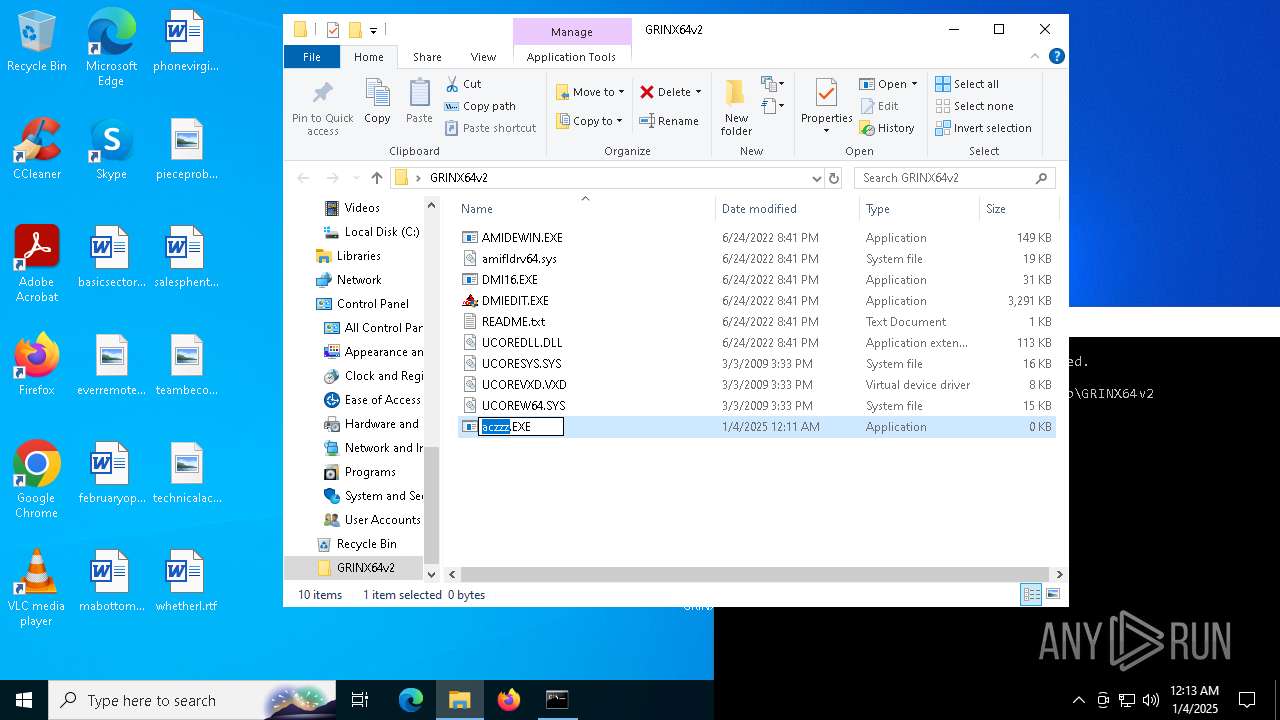
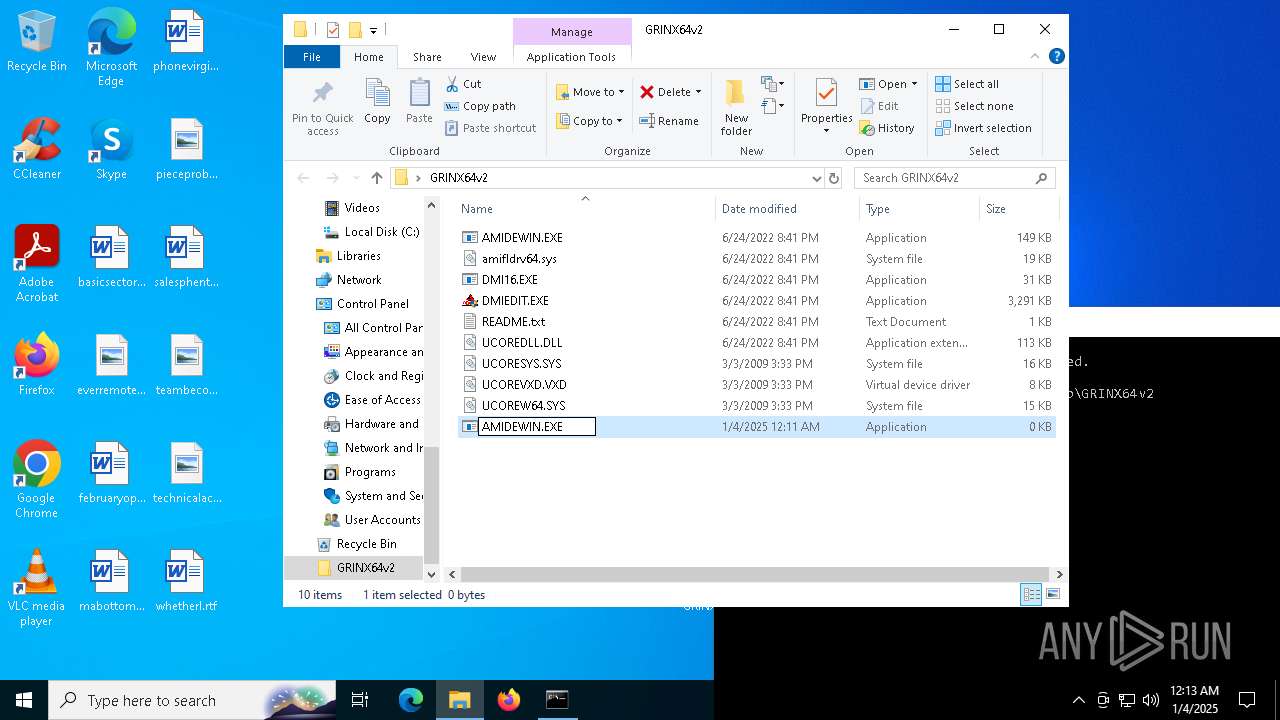
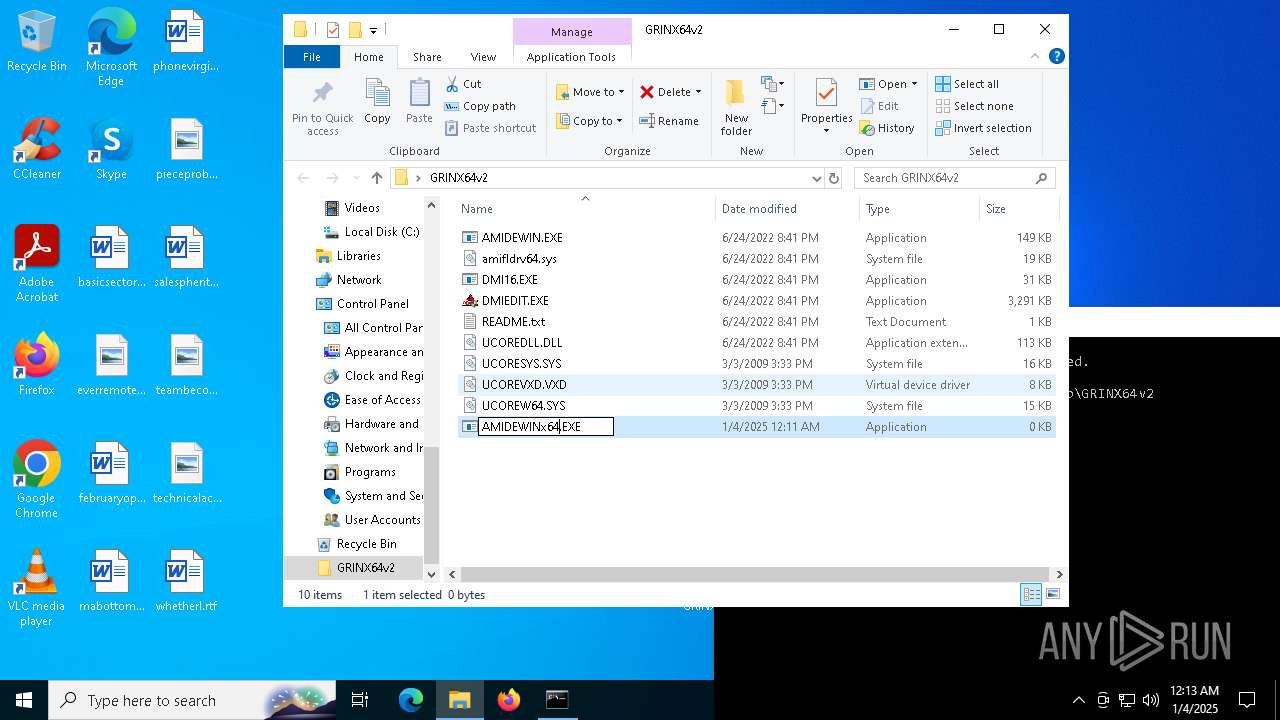
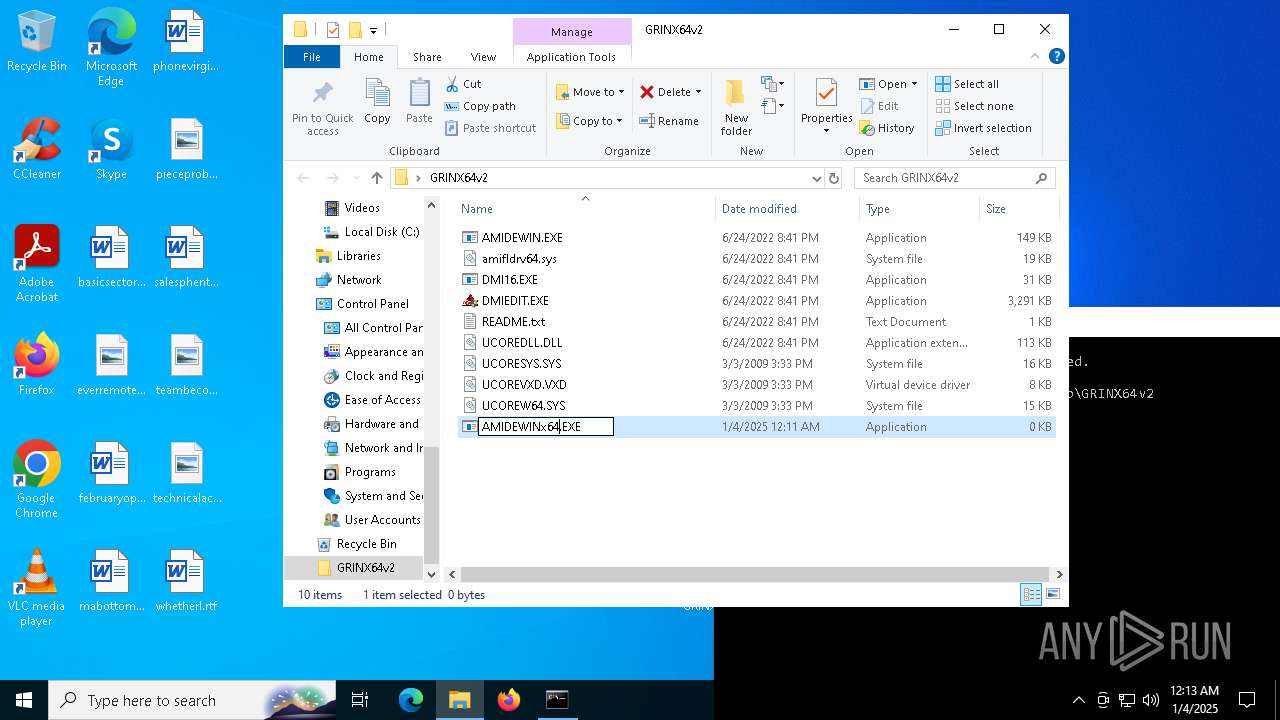
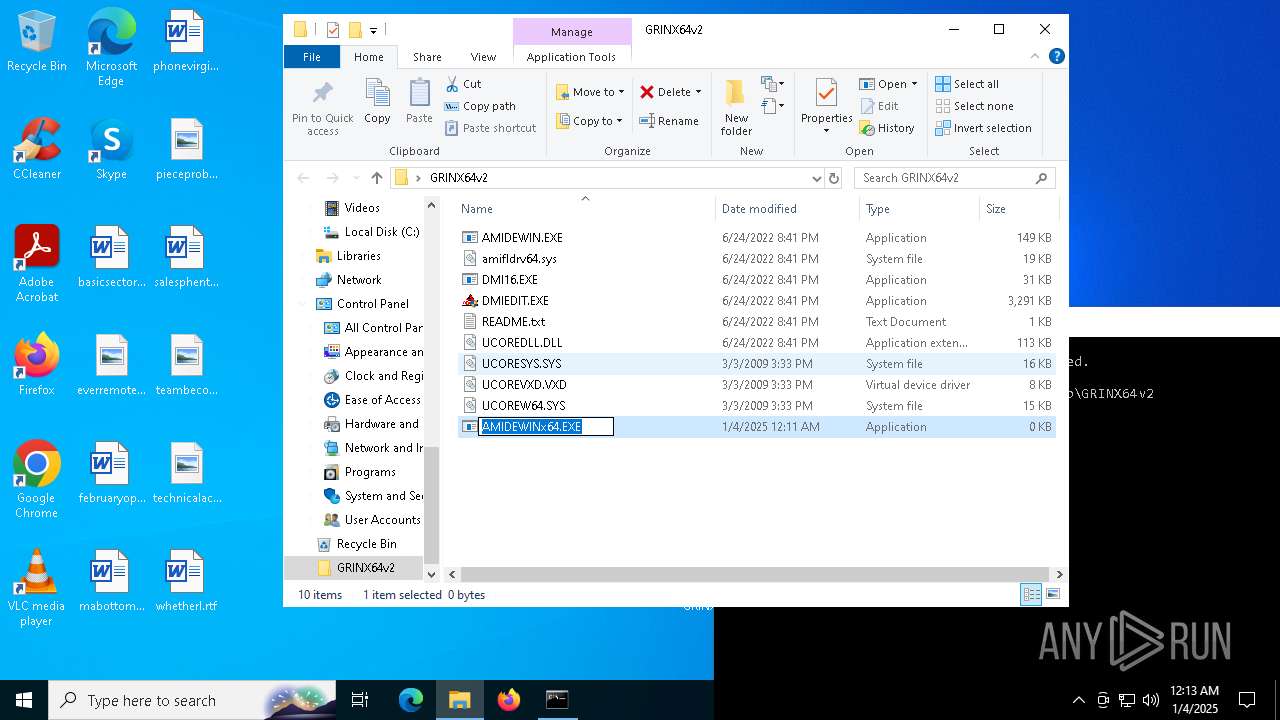
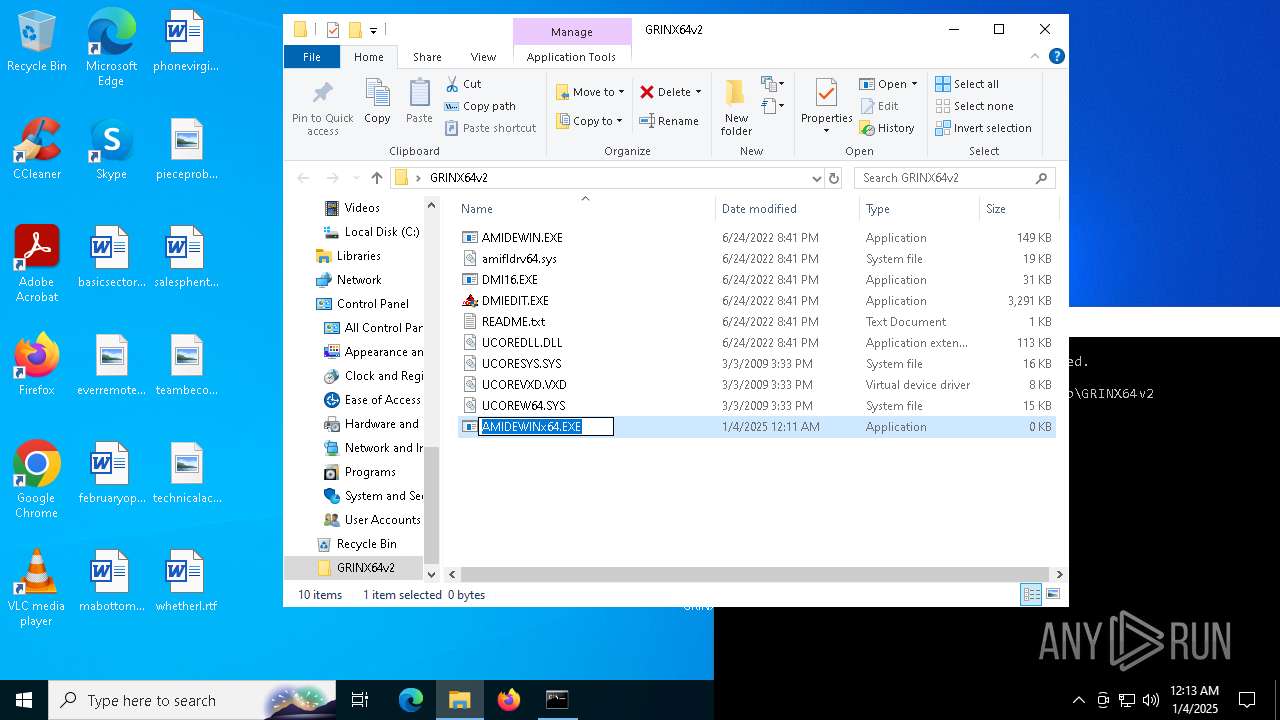
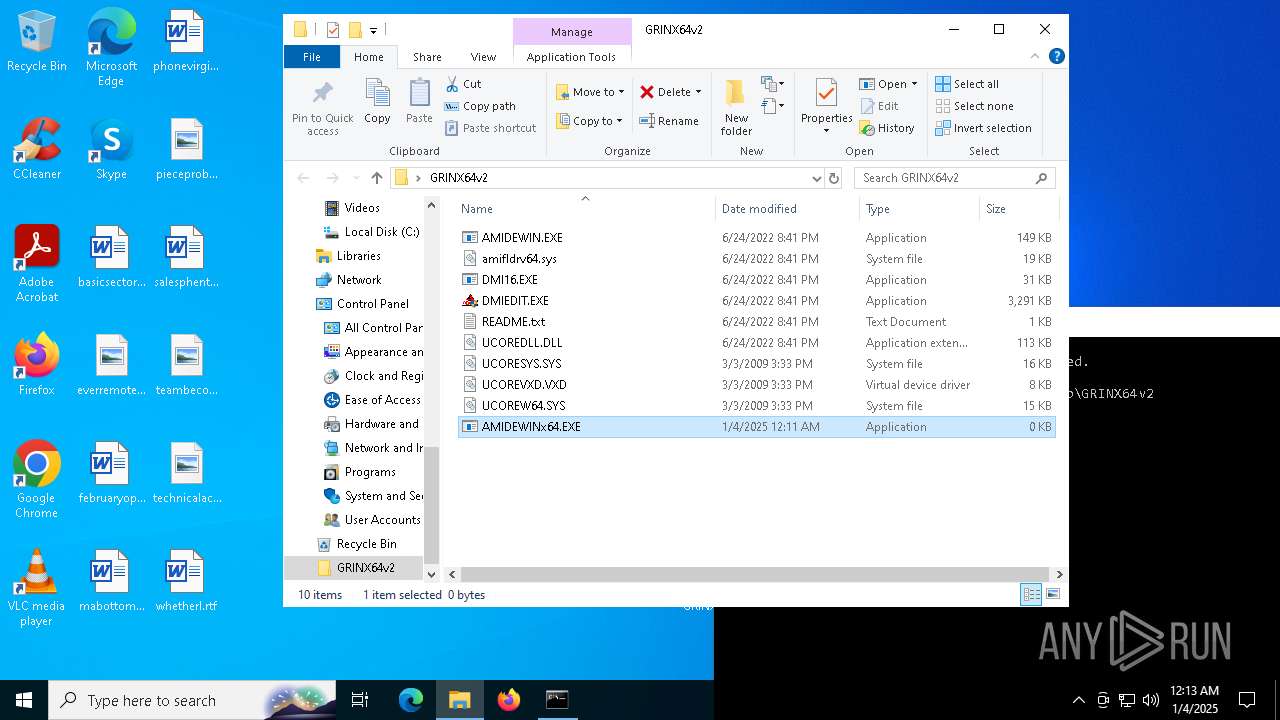
Executable files
9
Suspicious files
0
Text files
1
Unknown types
0
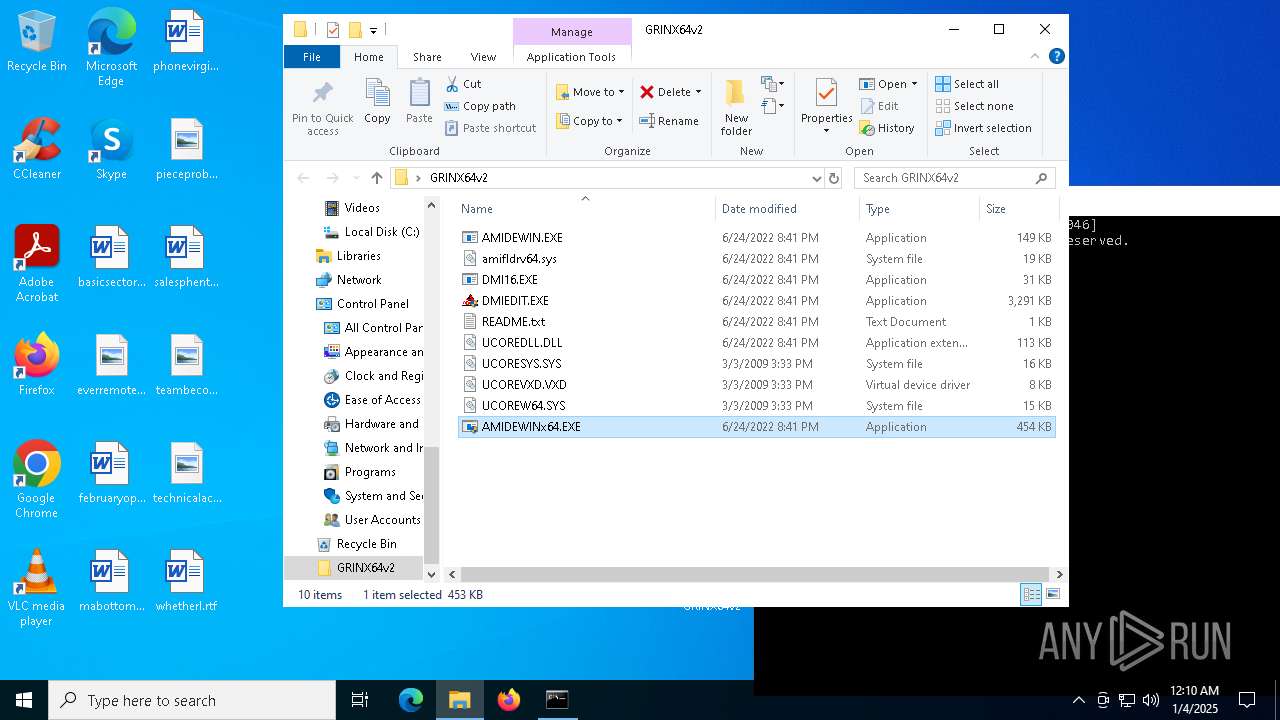
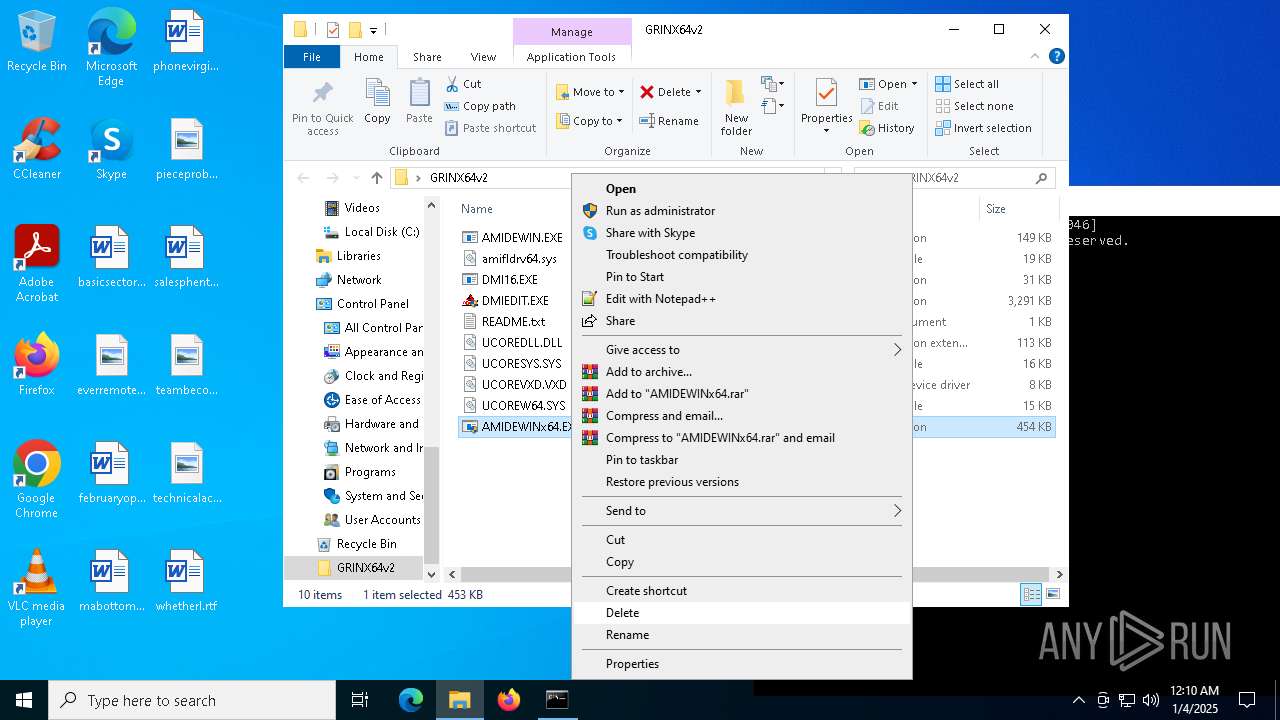
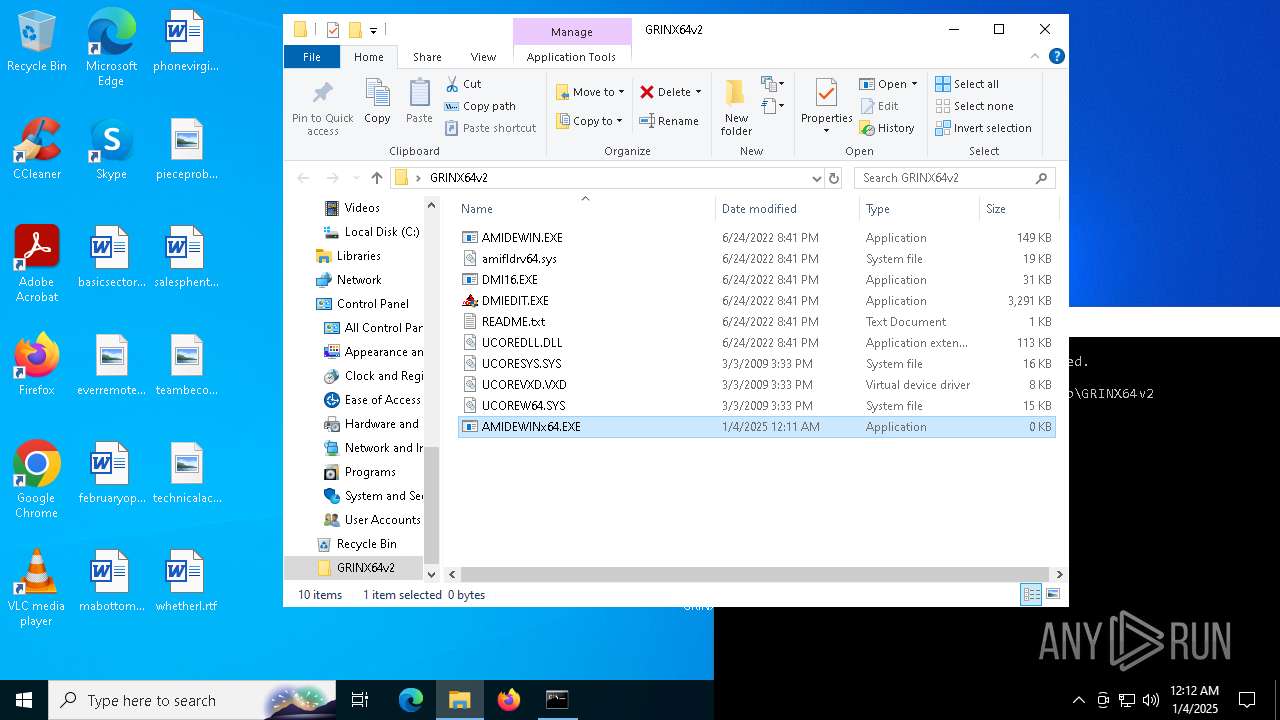
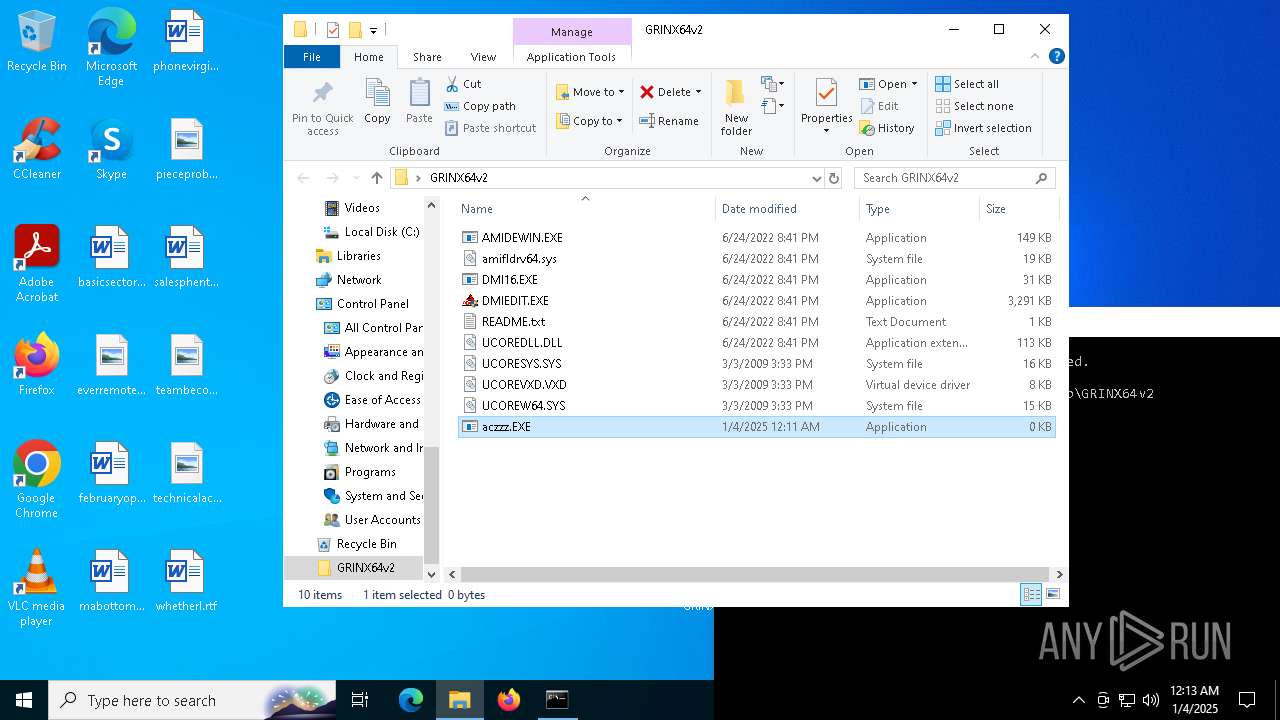
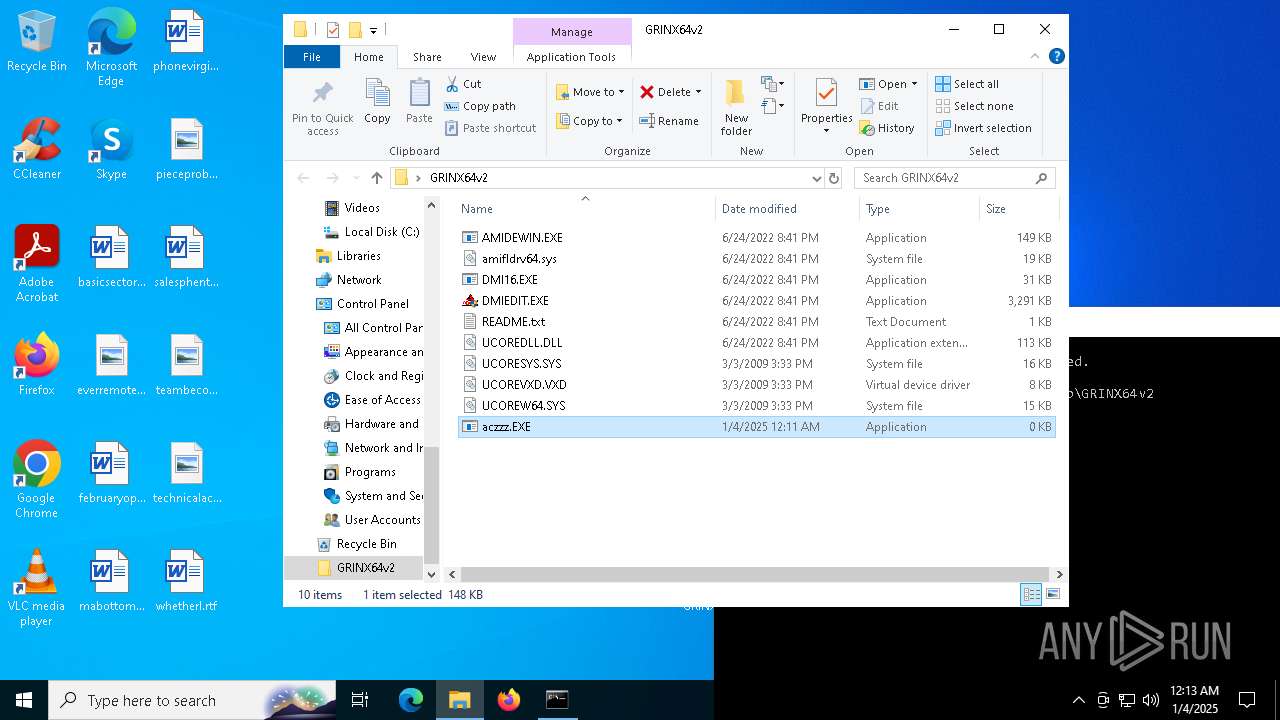
Dropped files
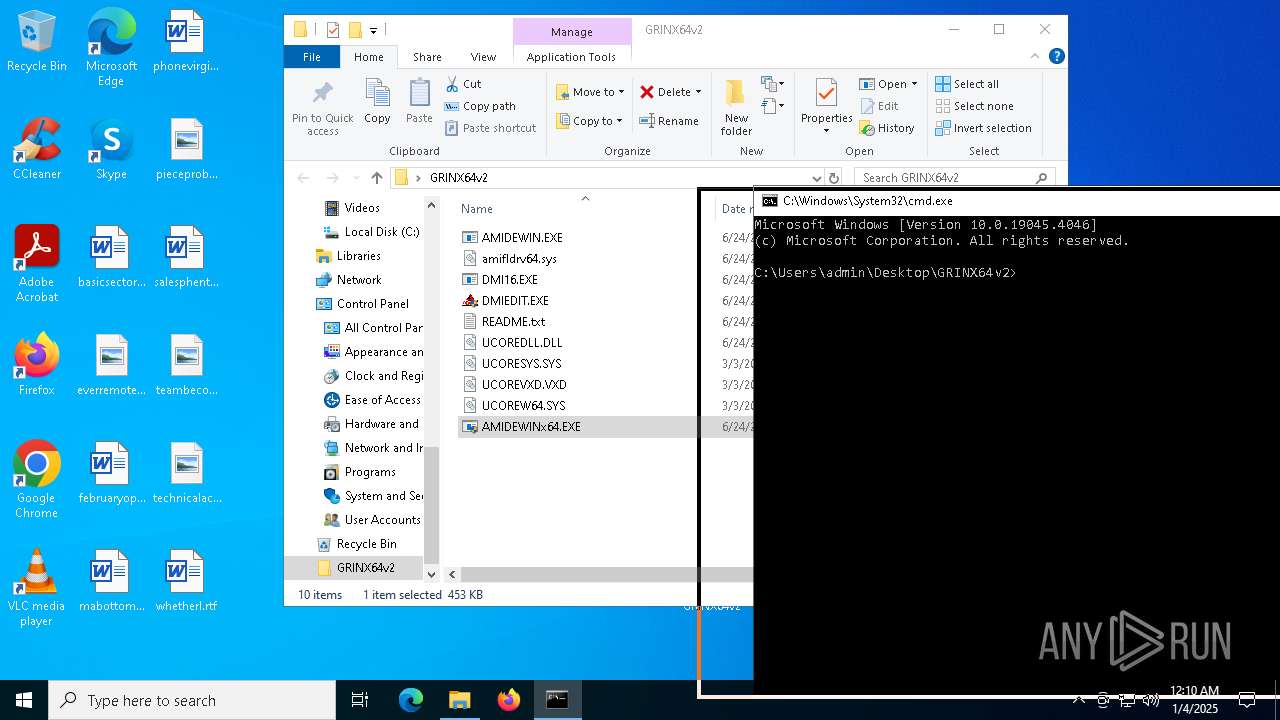
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\amifldrv64.sys | executable | |
MD5:785045F8B25CD2E937DDC6B09DEBE01A | SHA256:37073E42FFA0322500F90CD7E3C8D02C4CDD695D31C77E81560ABEC20BFB68BA | |||
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\README.txt | text | |
MD5:0E28E605E0988892043002E8D6FA719B | SHA256:1541F150F12295D926578FC8920F2F398D046BDDA66BC3026BF2533BBA07666B | |||
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\UCOREW64.SYS | executable | |
MD5:A17C58C0582EE560C72F60764ED63224 | SHA256:A7C8F4FAF3CBB088CAC7753D81F8EC4C38CCB97CD9DA817741F49272E8D01200 | |||
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\DMIEDIT.EXE | executable | |
MD5:FBAF6262FD84F9966338518D4DE46FDD | SHA256:5D37E5E7CE01549965BF2166ADCBA33D1E2C4BD2C90711032F3987B58452CE49 | |||
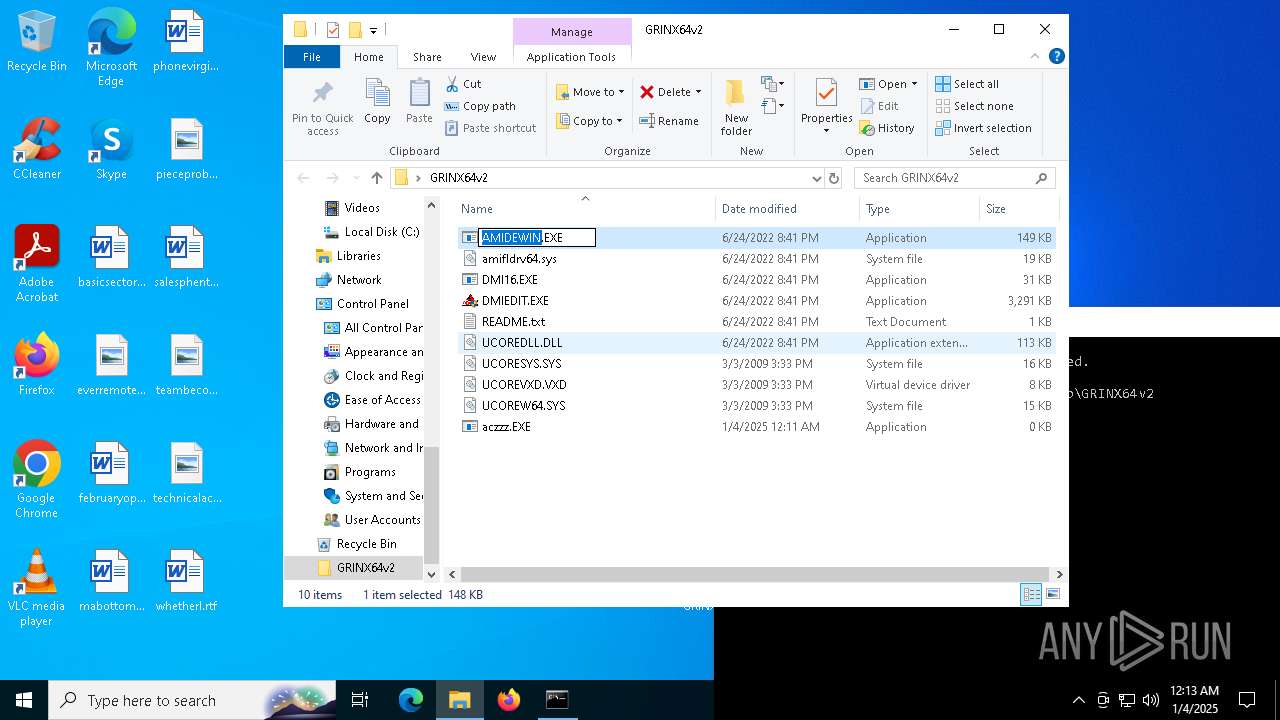
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\AMIDEWIN.EXE | executable | |
MD5:182EC3A59BD847FB1BC3E12A41D48FA6 | SHA256:948DBD2BC128F8DC08267E110020FEE3FF5DE17CF4AAEF89372DE29623AF96FA | |||
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\AMIDEWINx64.EXE | executable | |
MD5:6A6505B2413D2C7B16C6D059448DB9E5 | SHA256:53E3B72F8EB13ACF3CB69D4CB124E8DC64FC541555C3C95CC8003B8046853955 | |||
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\DMI16.EXE | executable | |
MD5:2A89D4E479351022AB8BD604030A76F3 | SHA256:28E6E1908F2996AF9B7A9930F13D4C770D6963425DF0869CE4BCDB1442A4A917 | |||
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\UCOREVXD.VXD | executable | |
MD5:211B3CDA6EE0F7A8C86FFC2E5177020D | SHA256:0C30287DEB78A25A4037FC3201062DDF880B06EA436550D83F47FB7FCAC7DCF4 | |||
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\UCOREDLL.DLL | executable | |
MD5:8370F3114924ED6C53741DE7A253625A | SHA256:78A4D8E5E8C33793E5A2020325D3A49E92E4826167742E93179BDACBF167B409 | |||
| 6380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6380.19977\GRINX64v2\UCORESYS.SYS | executable | |
MD5:9555D36FB21B993E5C4B98C2FC2B3671 | SHA256:FD6F56189CD723B32FC06392867FCD5128E63D8B5801E4F7A83523F820531981 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
43
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 92.123.53.223:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | BE | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 104.103.72.96:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | AT | binary | 1.01 Kb | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
6616 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
1580 | SIHClient.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 418 b | whitelisted |
1580 | SIHClient.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | US | binary | 408 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
440 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.103.72.96:80 | crl.microsoft.com | Akamai International B.V. | AT | whitelisted |
5064 | SearchApp.exe | 95.101.23.43:443 | www.bing.com | Akamai International B.V. | AT | whitelisted |
— | — | 92.123.53.223:80 | www.microsoft.com | AKAMAI-AS | BE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |