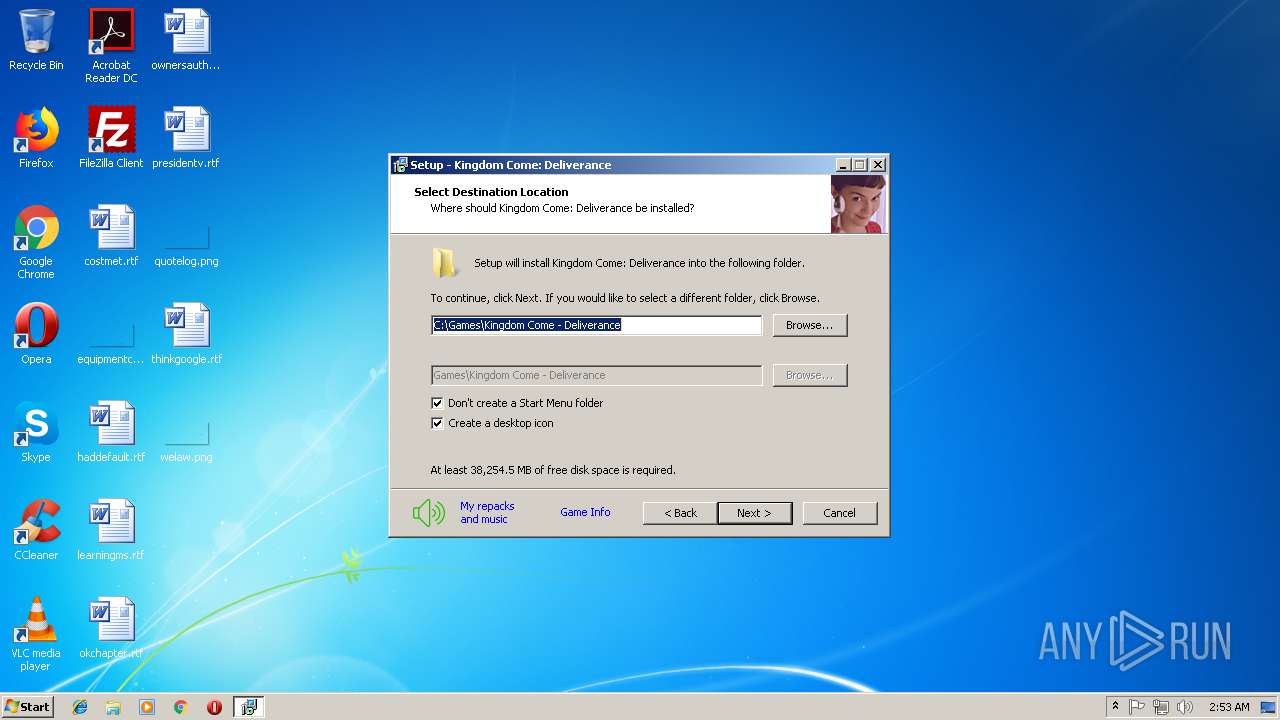
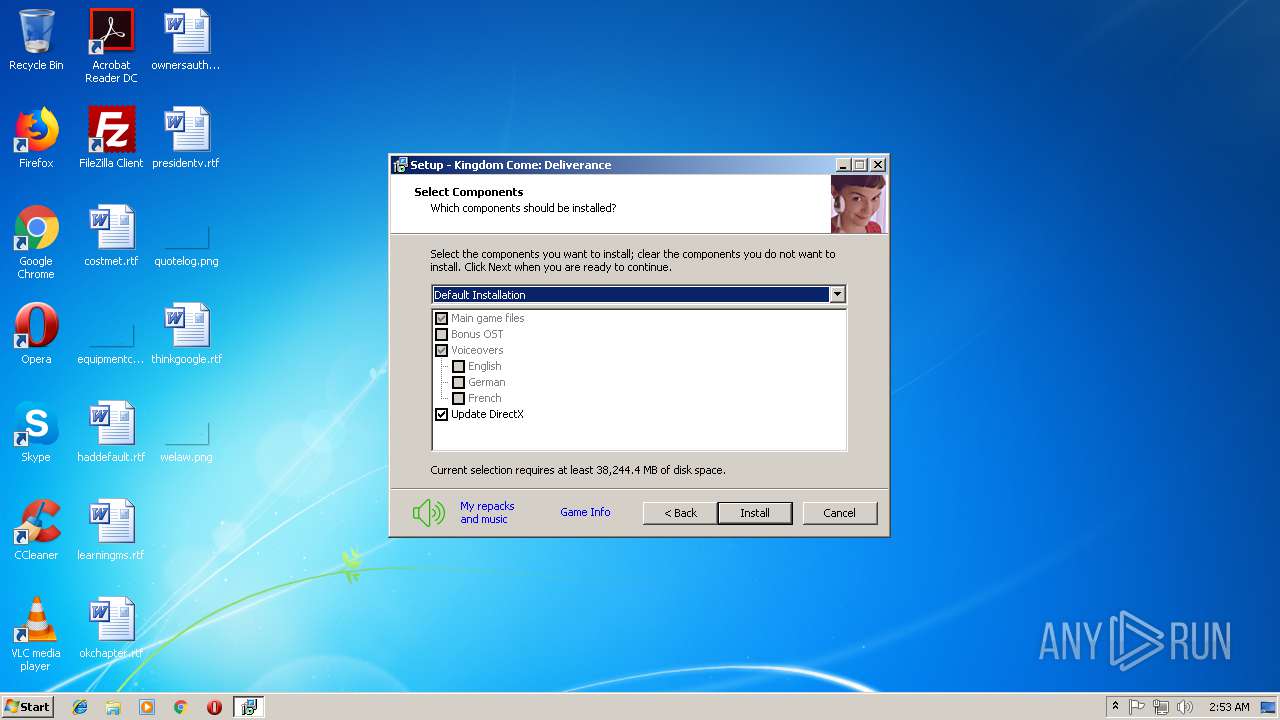
| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/9c3e0946-98c0-40ae-b1c3-b7bf1ef1dc9e |
| Verdict: | Malicious activity |
| Analysis date: | October 06, 2018, 01:52:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 094C2BB9894525FA62194F946F4494E1 |
| SHA1: | ECBBF7F6C5A5C5B4D1032C89499DEF1D7EA4C0A0 |
| SHA256: | C6BA5BA9095A4E30253AC1740459FBF5463300E4142B00EAC10D411E73F8D88E |
| SSDEEP: | 98304:Gf7wCQInrje/CAVMJhk7qDoWDMM574yZegyhOhuKADjjzN:Gfn6/VSwqDZDb74LgmOhul |
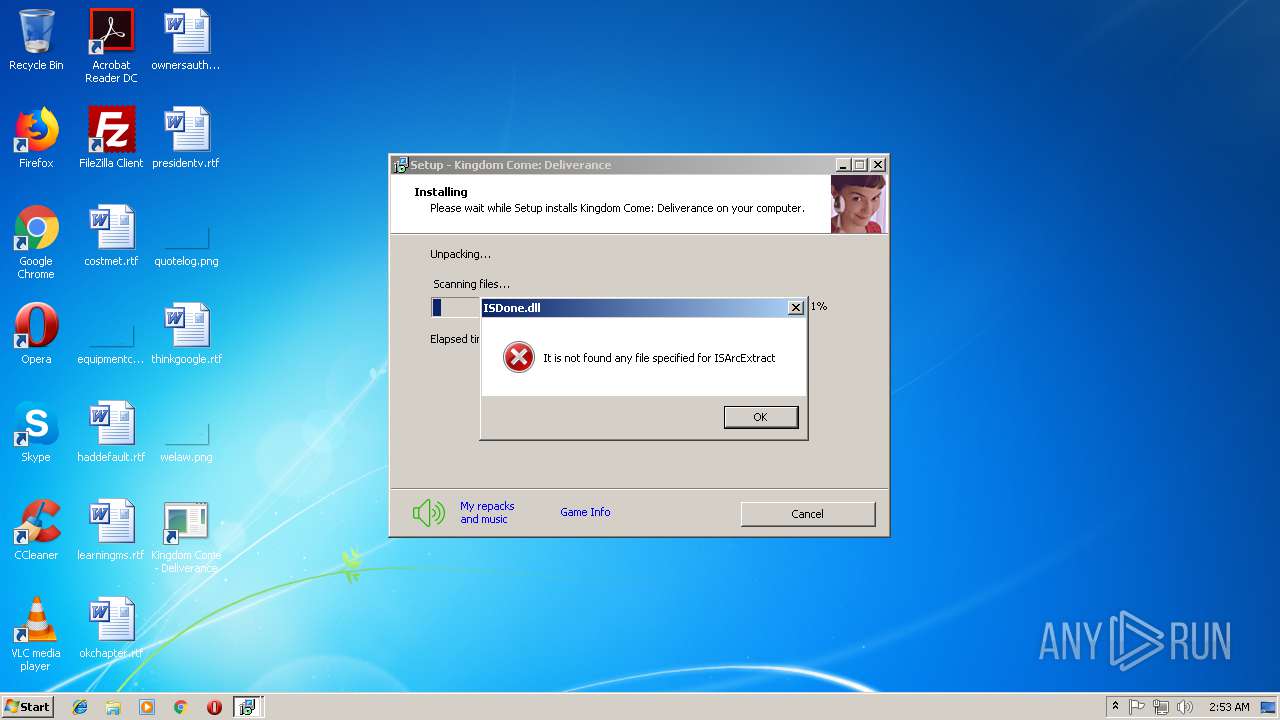
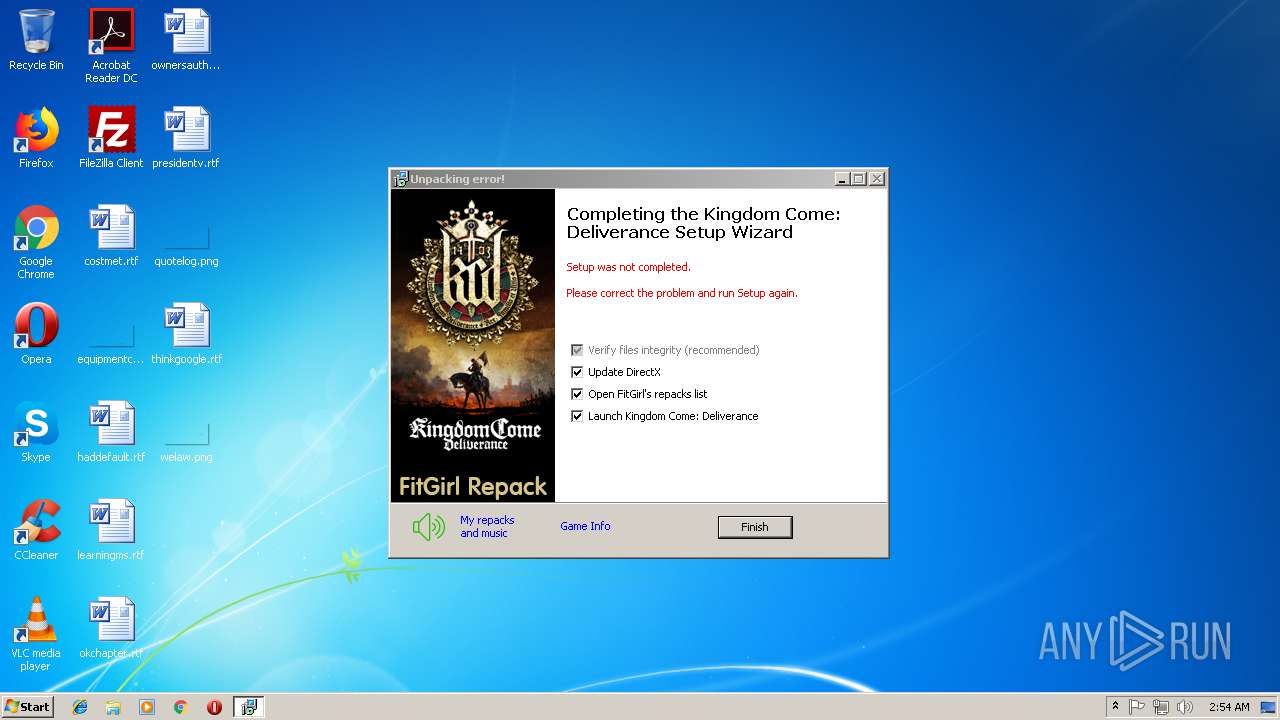
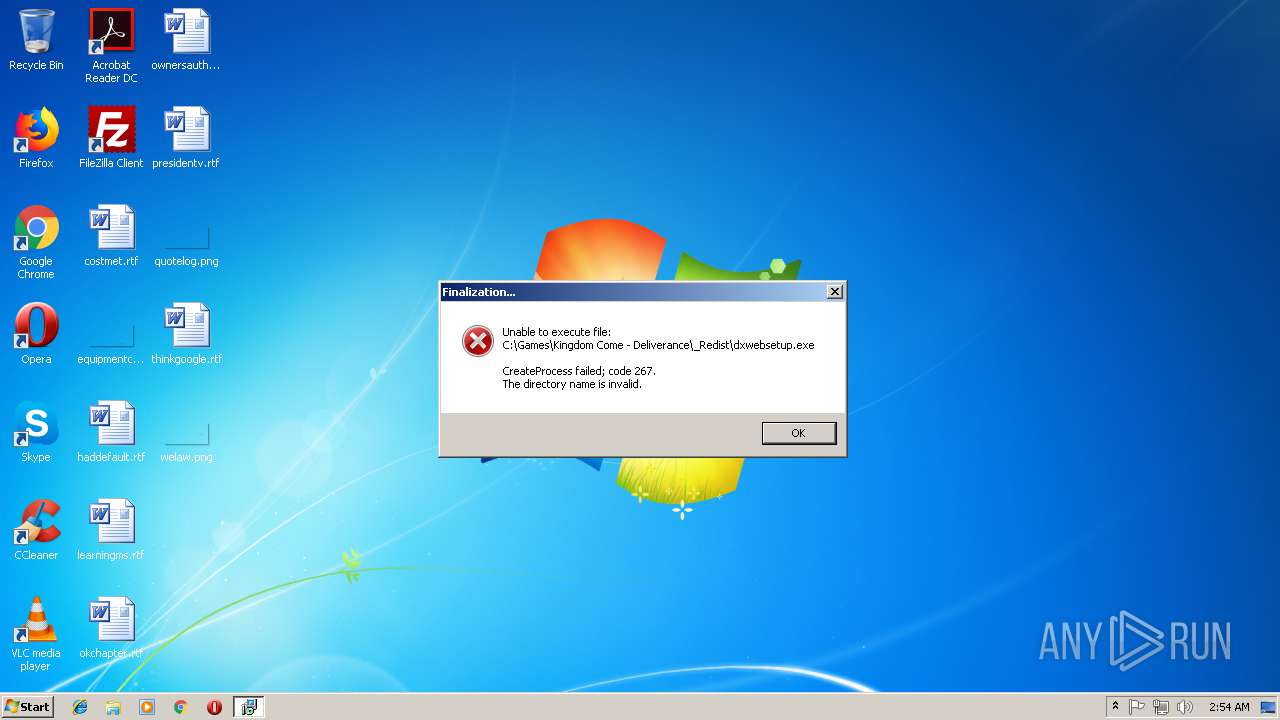
MALICIOUS
Application was dropped or rewritten from another process
- unins000.exe (PID: 120)
- _iu14D2N.tmp (PID: 1088)
Loads dropped or rewritten executable
- _iu14D2N.tmp (PID: 1088)
SUSPICIOUS
Reads the Windows organization settings
- setup.tmp (PID: 3096)
- _iu14D2N.tmp (PID: 1088)
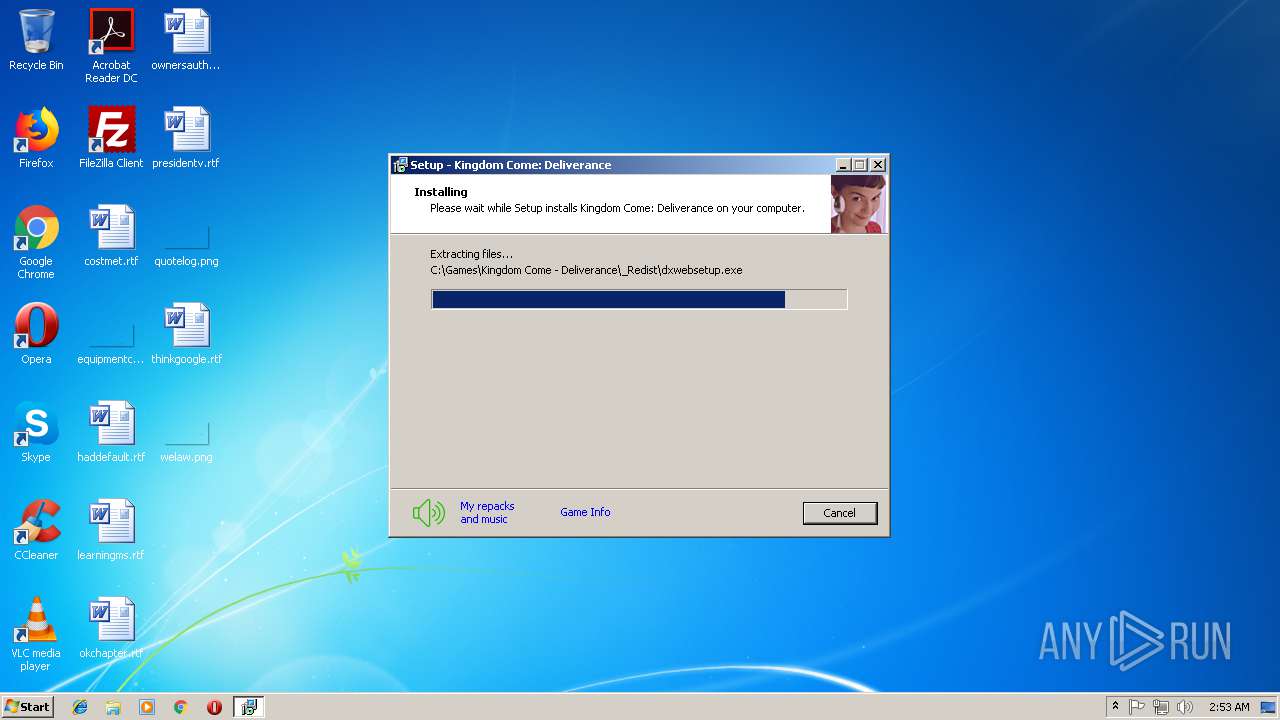
Executable content was dropped or overwritten
- setup.exe (PID: 384)
- setup.tmp (PID: 3096)
- unins000.exe (PID: 120)
- _iu14D2N.tmp (PID: 1088)
Reads Windows owner settings
- setup.tmp (PID: 3096)
- _iu14D2N.tmp (PID: 1088)
Starts application with an unusual extension
- unins000.exe (PID: 120)
Starts Internet Explorer
- setup.tmp (PID: 3096)
Creates files in the program directory
- iexplore.exe (PID: 3792)
Creates files in the user directory
- setup.tmp (PID: 3096)
INFO
Loads dropped or rewritten executable
- setup.tmp (PID: 3096)
Application was dropped or rewritten from another process
- setup.tmp (PID: 3096)
- FlushFileCache.exe (PID: 3760)
Creates a software uninstall entry
- setup.tmp (PID: 3096)
Changes internet zones settings
- iexplore.exe (PID: 896)
Creates files in the user directory
- iexplore.exe (PID: 3792)
Reads internet explorer settings
- iexplore.exe (PID: 3792)
Reads Internet Cache Settings
- iexplore.exe (PID: 3792)
Changes settings of System certificates
- iexplore.exe (PID: 3792)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 07:04:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
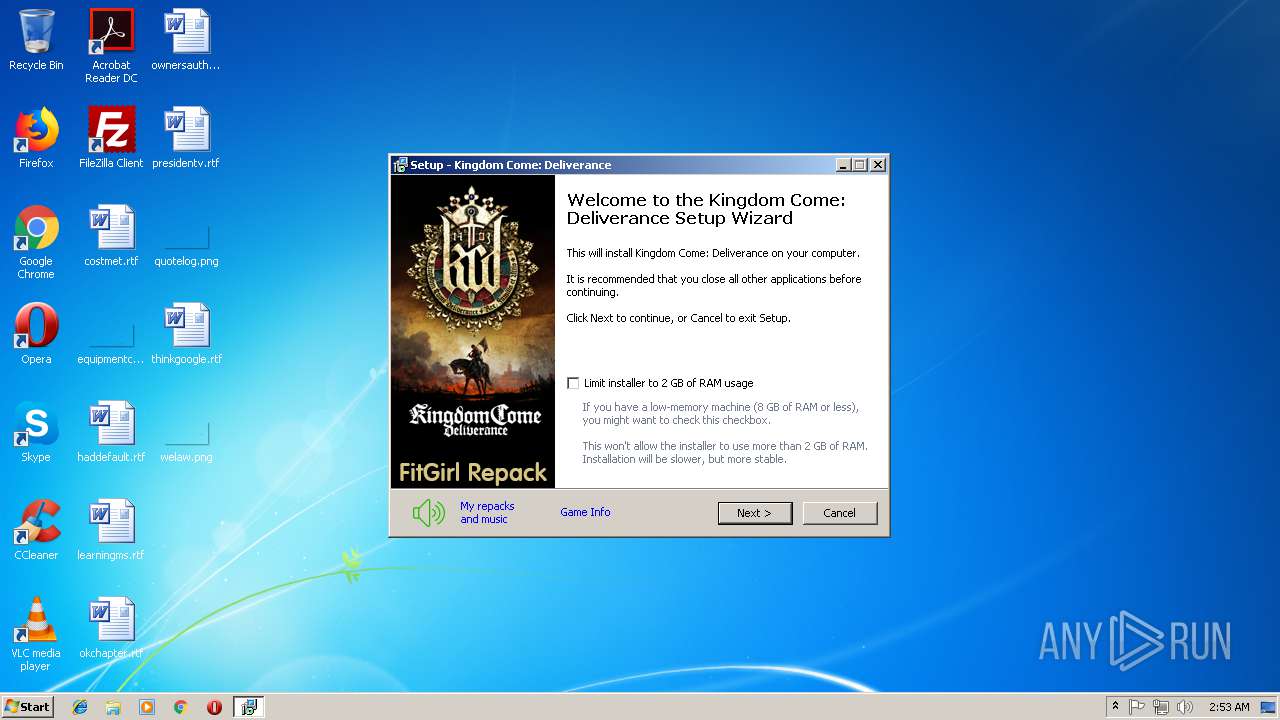
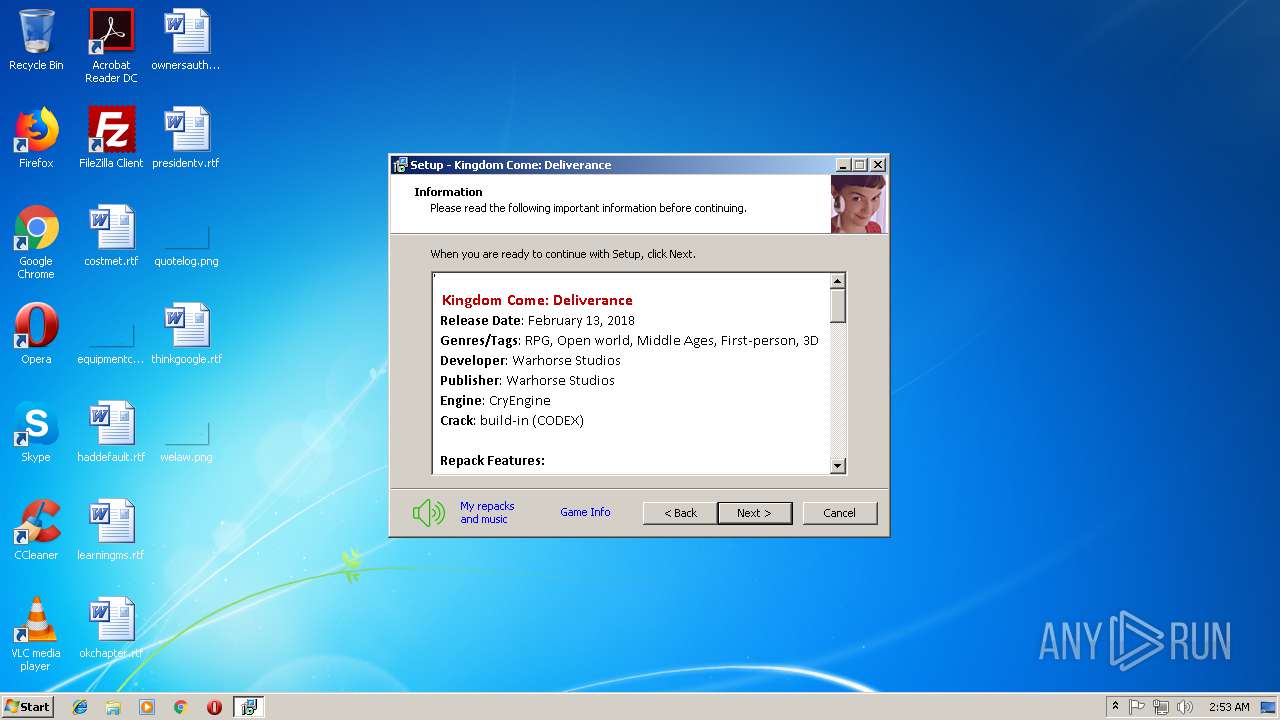
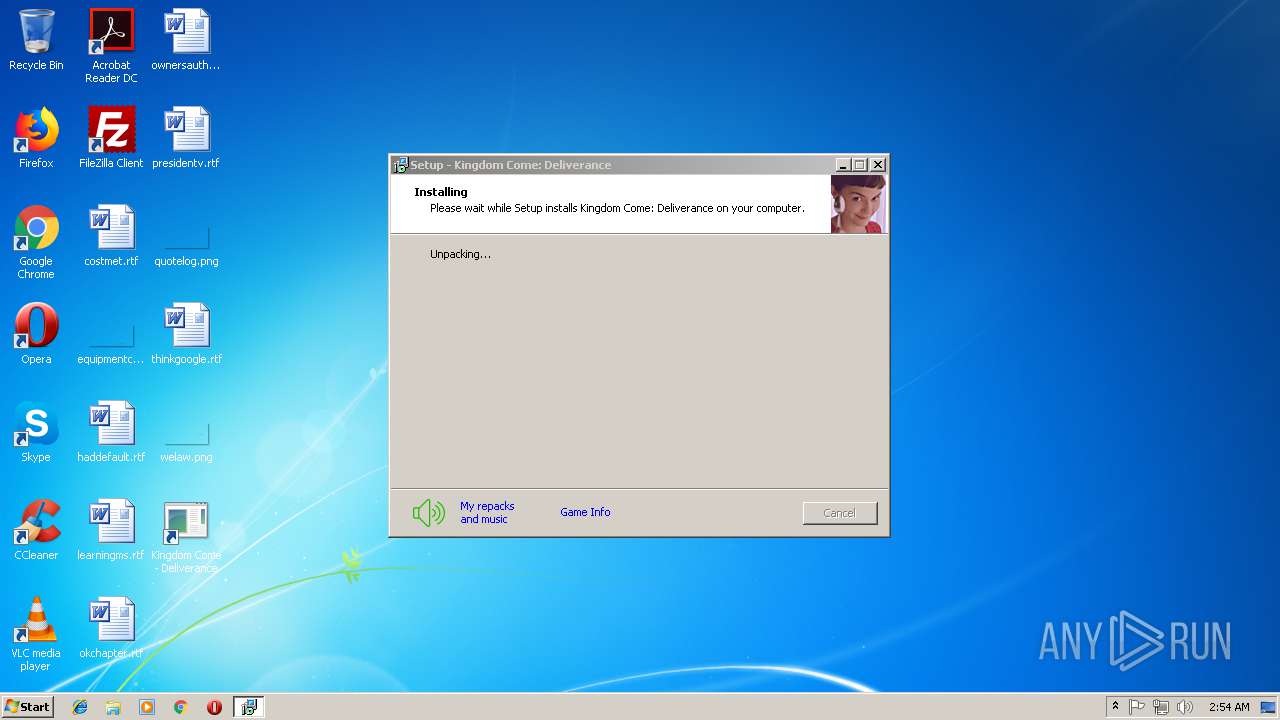
| FileDescription: | Kingdom Come: Deliverance Setup |
| FileVersion: | |
| LegalCopyright: | FitGirl |
| ProductName: | Kingdom Come: Deliverance |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2012 05:04:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Kingdom Come: Deliverance Setup |
| FileVersion: | - |
| LegalCopyright: | FitGirl |
| ProductName: | Kingdom Come: Deliverance |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 02-Oct-2012 05:04:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000143F8 | 0x00014400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4822 |
.itext | 0x00016000 | 0x00000BE8 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.01516 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.66929 |
.bss | 0x00018000 | 0x00005750 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.rsrc | 0x00021000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.15852 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06505 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
4091 | 3.13038 | 196 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.36196 | 204 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.34841 | 372 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.29351 | 924 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
46
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
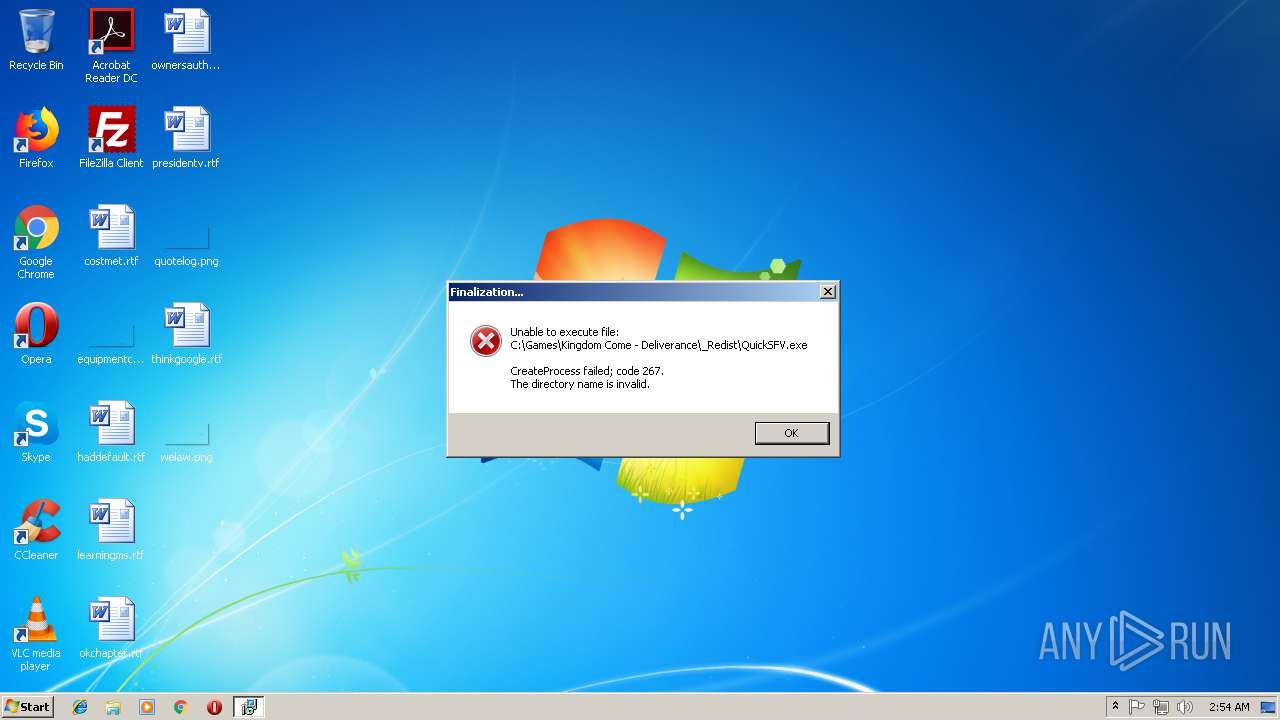
| 120 | "C:\Games\Kingdom Come - Deliverance\unins000.exe" /VERYSILENT | C:\Games\Kingdom Come - Deliverance\unins000.exe | setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 384 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Kingdom Come: Deliverance Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 896 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | setup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Games\Kingdom Come - Deliverance\unins000.exe" /FIRSTPHASEWND=$80548 /VERYSILENT | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3096 | "C:\Users\admin\AppData\Local\Temp\is-C201I.tmp\setup.tmp" /SL5="$2E0202,4767637,140800,C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-C201I.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\FlushFileCache.exe" | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\FlushFileCache.exe | — | setup.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:896 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Kingdom Come: Deliverance Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
Total events
866
Read events
597
Write events
262
Delete events
7
Modification events
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 180C000088786D60175DD401 | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: BA7DAAA000416DE11478CD87F9838D8A5EA035560B534F15B234BFB7CF10AA8C | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Games\Kingdom Come - Deliverance\_Redist\dxwebsetup.exe | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 3C7511CF186BC1096B1973851D8C8192633CC0F9ED91B01F85EF28EE3891F255 | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Games\Kingdom Come - Deliverance\Bin\Win64\KingdomCome.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Games\Kingdom Come - Deliverance\Bin\Win64\KingdomCome.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Kingdom Come: Deliverance_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1.ee2 (u) | |||
| (PID) Process: | (3096) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Kingdom Come: Deliverance_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Games\Kingdom Come - Deliverance | |||
Executable files
49
Suspicious files
1
Text files
110
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\ISDone.dll | executable | |
MD5:4FEAFA8B5E8CDB349125C8AF0AC43974 | SHA256:BB8A0245DCC5C10A1C7181BAD509B65959855009A8105863EF14F2BB5B38AC71 | |||
| 384 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-C201I.tmp\setup.tmp | executable | |
MD5:AE9890548F2FCAB56A4E9AE446F55B3F | SHA256:09AF8004B85478E1ECA09FA4CB5E3081DDDCB2F68A353F3EF6849D92BE47B449 | |||
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\BASS.dll | executable | |
MD5:8005750EC63EB5292884AD6183AE2E77 | SHA256:DF9F56C4DA160101567B0526845228EE481EE7D2F98391696FA27FE41F8ACF15 | |||
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\cls-lolzi_x86.exe | executable | |
MD5:2A108C93DFCF6B488880D0423D1F0EC7 | SHA256:CBC1D8A42AC2FF81C1F0D817312867D86A4EC2A7058D56E56C282F062113B9E0 | |||
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\wintb.dll | executable | |
MD5:9436DF49E08C83BAD8DDC906478C2041 | SHA256:1910537AA95684142250CA0C7426A0B5F082E39F6FBDBDBA649AECB179541435 | |||
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\cls-lolly_x64.exe | executable | |
MD5:816E95C6BFE26A139B0E628954D191DA | SHA256:A6C62FC3C84D2701BC21BC916DAB3B0B079E7E56890A075D66CB0F20459CBCD3 | |||
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\cls-lolzx.dll | executable | |
MD5:A67AF01BF2FE22DA108A7714B369D33F | SHA256:7429467F7A2B73F0AAF609F34F4E3385EDADC7F7014D97986ACC31F5293D171C | |||
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\cls-lolly.dll | executable | |
MD5:0EF04BC15FD1B28975AFF2951B857F03 | SHA256:F84677643D9977AA1E8A4AA8C85A12665D29A4E8292485A0B4DF846DD161F824 | |||
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\cls-lolzx_x64.exe | executable | |
MD5:1AA4F56CFD9D0685B03807626E12DF9A | SHA256:4CB2243D60B3C84683F88F97394DD020BE455196AA61A414A358A77D67BF902E | |||
| 3096 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GPM13.tmp\cls-lollypop_x86.exe | executable | |
MD5:3527C6739C46F4EE1CFB6B48E1407883 | SHA256:724C6E07180E321298B4EA4405C3F7536C524D9826D24F5D6FC50BCB0EF8F723 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
92
TCP/UDP connections
37
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
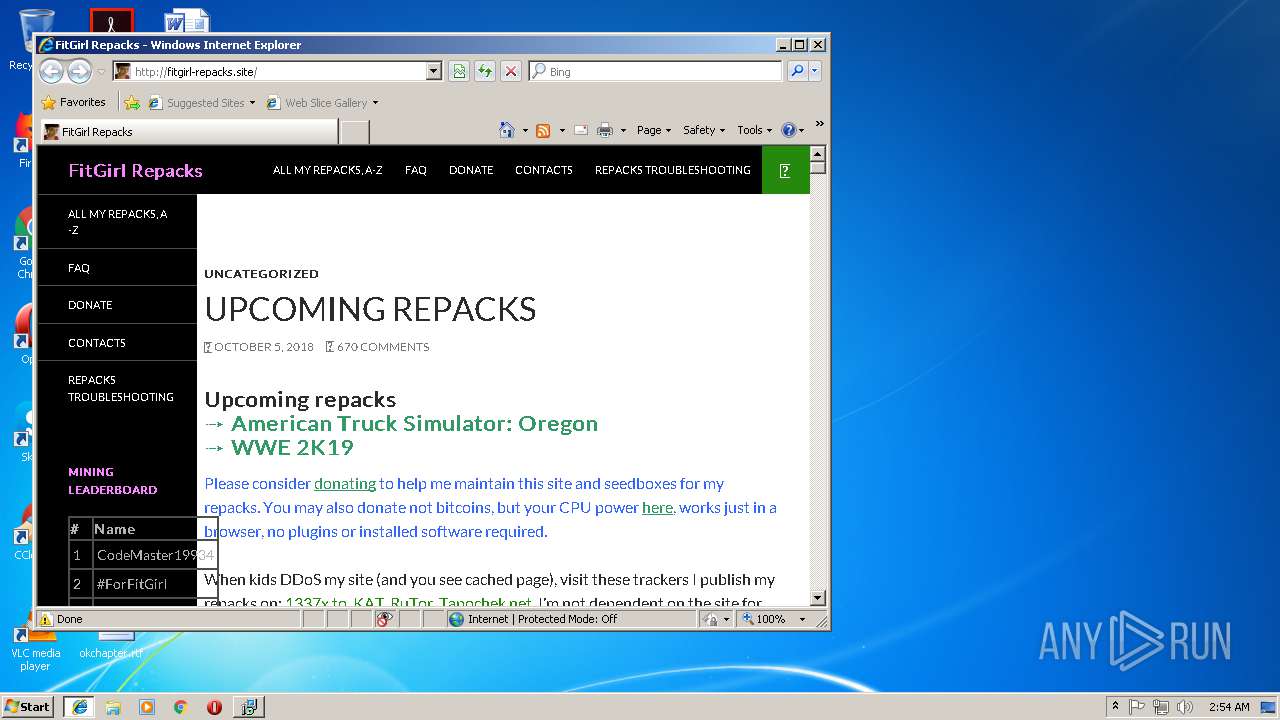
3792 | iexplore.exe | GET | 302 | 104.27.141.168:80 | http://fitgirl-repacks.site/cdn-cgi/l/chk_jschl?jschl_vc=f78b11f024447c03f55feaacb2b1b826&pass=1538790866.505-J2hRxCJYzm&jschl_answer=12.6263744287 | US | html | 159 b | suspicious |
3792 | iexplore.exe | GET | 503 | 104.27.141.168:80 | http://fitgirl-repacks.site/ | US | html | 9.02 Kb | suspicious |
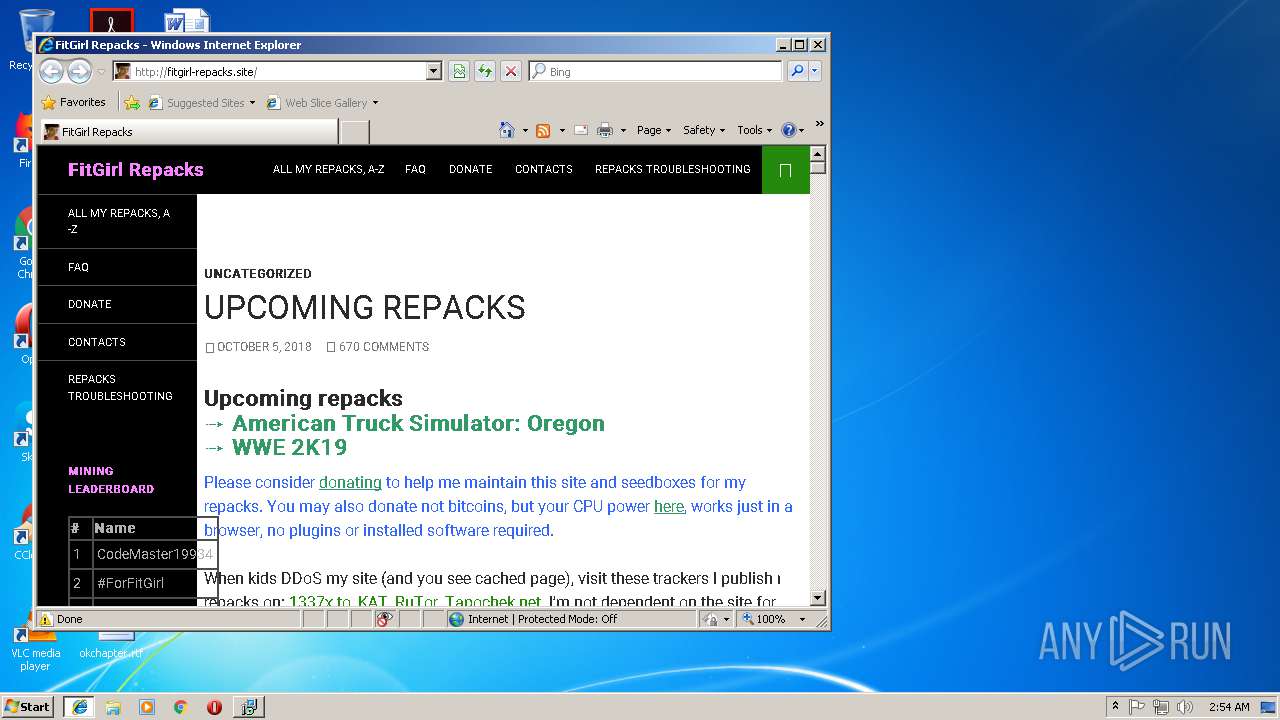
3792 | iexplore.exe | GET | 200 | 104.27.141.168:80 | http://fitgirl-repacks.site/ | US | html | 21.7 Kb | suspicious |
3792 | iexplore.exe | GET | 200 | 104.27.141.168:80 | http://fitgirl-repacks.site/wp-content/themes/twentyfourteen/style.css?ver=4.9.8 | US | text | 14.4 Kb | suspicious |
3792 | iexplore.exe | GET | 403 | 104.27.141.168:80 | http://fitgirl-repacks.site/wp-content/plugins/jetpack/_inc/genericons/genericons/Genericons.eot?)%20format("embedded-opentype" | US | html | 224 b | suspicious |
3792 | iexplore.exe | GET | 200 | 172.64.174.22:80 | http://s01.riotpixels.net/data/5f/00/5f006138-3399-46ad-9191-36ea145fba3d.jpg.240p.jpg | US | image | 18.7 Kb | suspicious |
3792 | iexplore.exe | GET | 200 | 194.36.150.42:80 | http://i91.fastpic.ru/big/2018/1005/7f/5e6ff5be7aaf210a58a0079039ddad7f.jpg | unknown | image | 63.6 Kb | unknown |
3792 | iexplore.exe | GET | 200 | 104.27.141.168:80 | http://fitgirl-repacks.site/wp-content/themes/twentyfourteen/js/html5.js | US | html | 1.22 Kb | suspicious |
3792 | iexplore.exe | GET | 301 | 67.199.248.10:80 | http://bit.ly/fitgirl-repacks-site | US | html | 115 b | shared |
3792 | iexplore.exe | GET | 200 | 104.27.141.168:80 | http://fitgirl-repacks.site/favicon.ico | US | image | 964 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | iexplore.exe | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
3792 | iexplore.exe | 104.27.141.168:80 | fitgirl-repacks.site | Cloudflare Inc | US | shared |
896 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3792 | iexplore.exe | 192.0.78.17:443 | wordpress.com | Automattic, Inc | US | unknown |
3792 | iexplore.exe | 194.36.150.42:80 | i91.fastpic.ru | — | — | unknown |
3792 | iexplore.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3792 | iexplore.exe | 172.64.174.22:80 | s01.riotpixels.net | Cloudflare Inc | US | shared |
3792 | iexplore.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
3792 | iexplore.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
3792 | iexplore.exe | 151.101.120.134:80 | fitgirl-repacks-site.disqus.com | Fastly | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
www.bing.com |
| whitelisted |
fitgirl-repacks.site |
| suspicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
wordpress.com |
| whitelisted |
i91.fastpic.ru |
| unknown |
s01.riotpixels.net |
| suspicious |
i89.fastpic.ru |
| unknown |
netdna.bootstrapcdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3792 | iexplore.exe | Potentially Bad Traffic | SC BAD_UNKNOWN Malicious interaction with hacking site (undentified malware) |