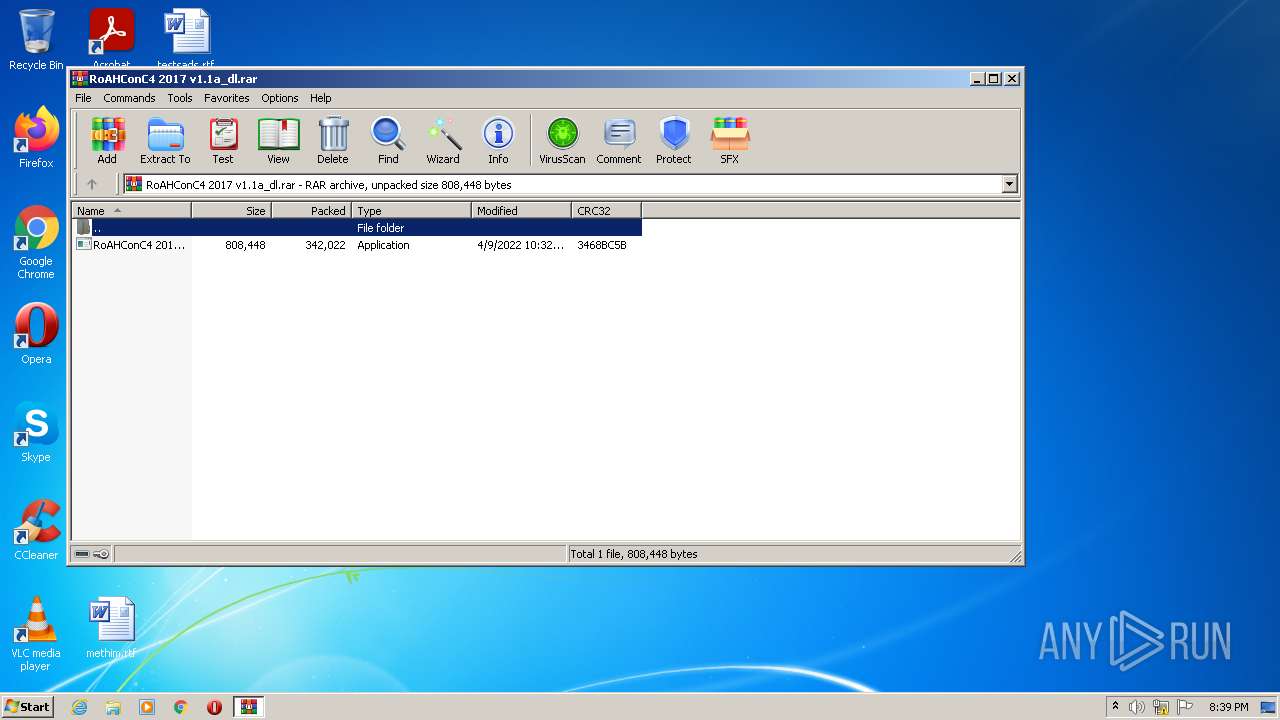
| File name: | RoAHConC4 2017 v1.1a_dl.rar |
| Full analysis: | https://app.any.run/tasks/d80091ae-ab32-472f-b49d-b4a33649b351 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 19:39:27 |
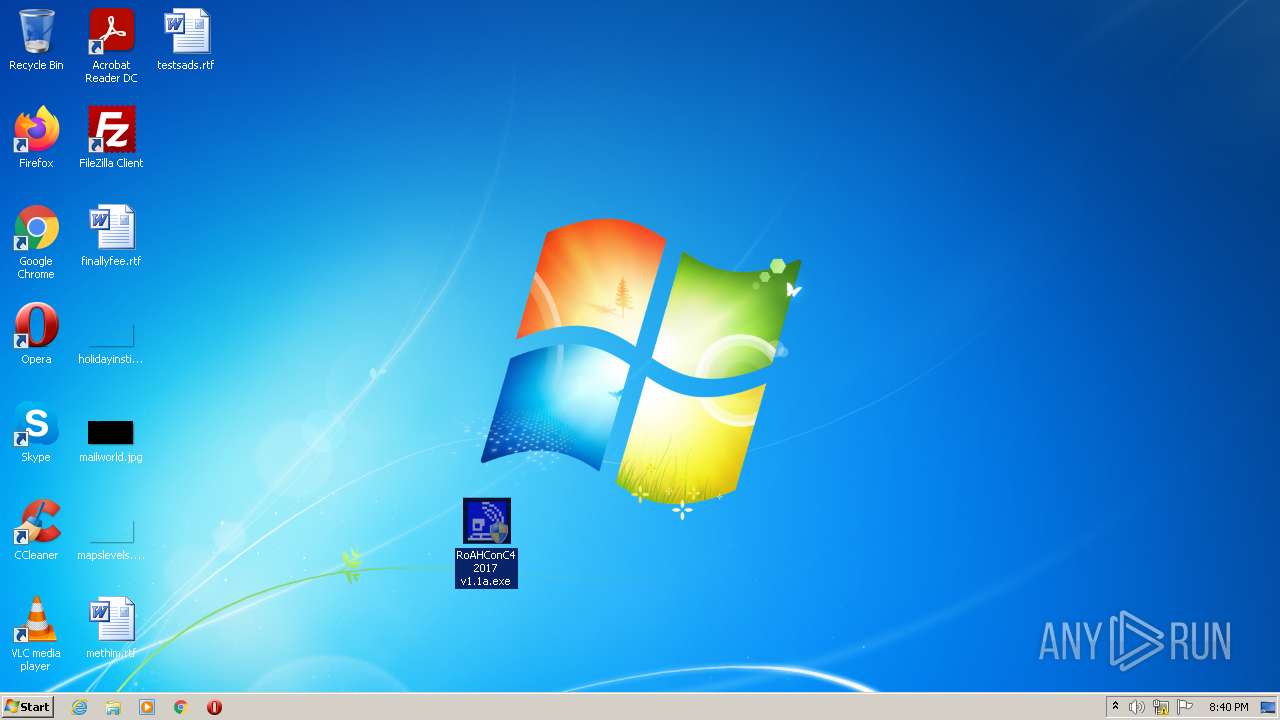
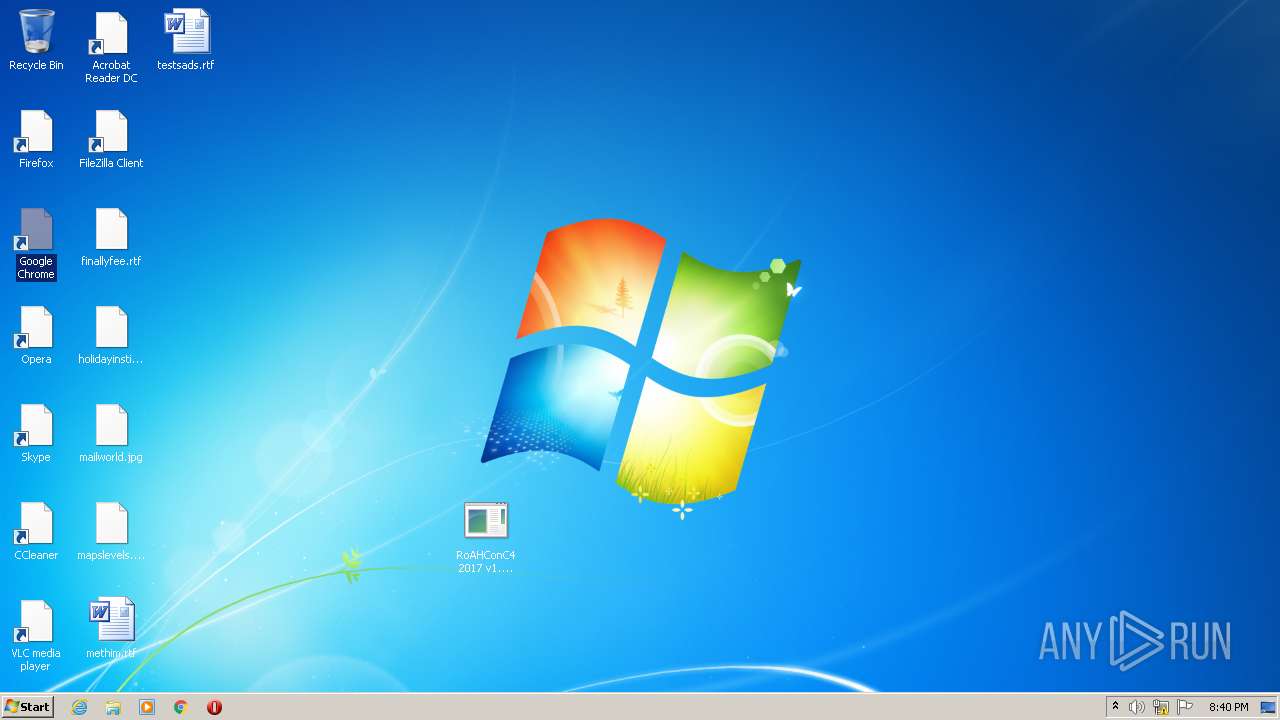
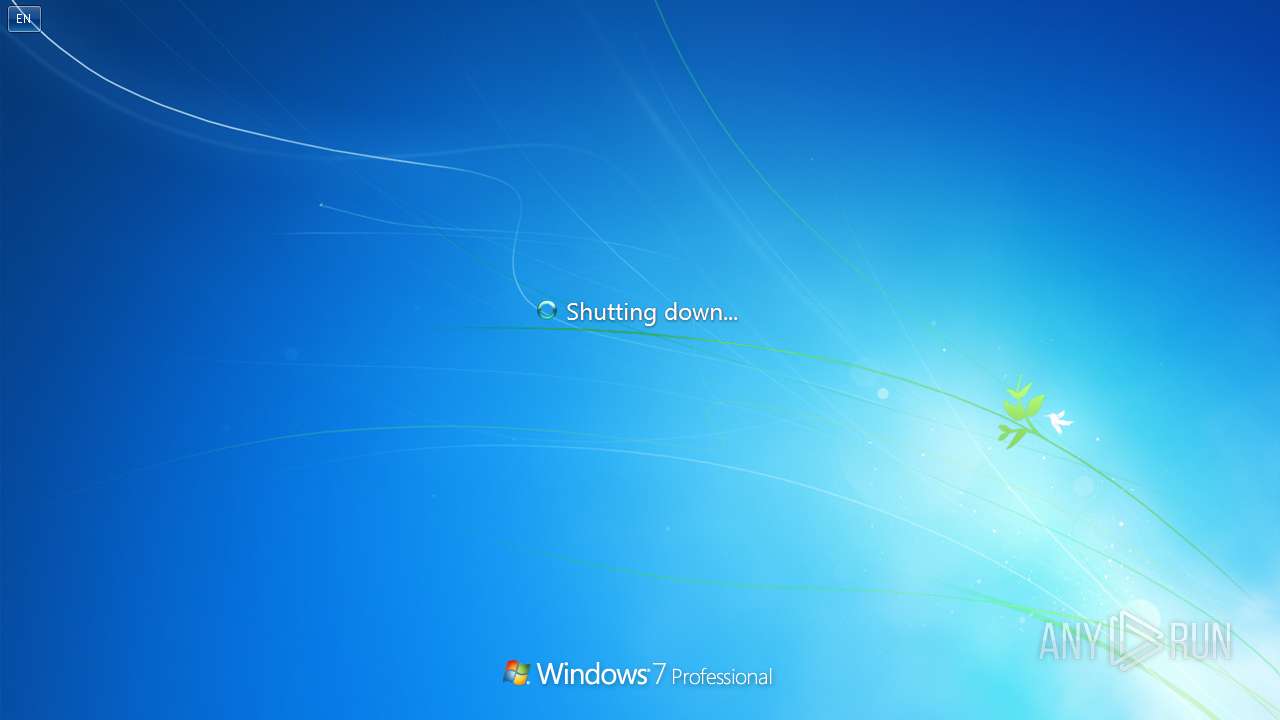
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 19A16D888B606025B01E842B88EB09A0 |
| SHA1: | 6F91675A53F6546E0E7E3B7FDEBCC96F257B1EDE |
| SHA256: | C6B9E40558B0BBE5CC1CCDD605760FE3E86D0D0D3E8927ADD6A506E6CDA3160B |
| SSDEEP: | 6144:I8ENEH4emRLLW9FF2EmdQGBbm4gQ7/64NRwhi8ENn5TUTGLmC4duKhjNdvjtdAAR:cN5qF2aWxC4NRT8ENAGLmL/5ZaAqU |
MALICIOUS
Application was dropped or rewritten from another process
- RoAHConC4 2017 v1.1a.exe (PID: 2244)
- RoAHConC4 2017 v1.1a.exe (PID: 2440)
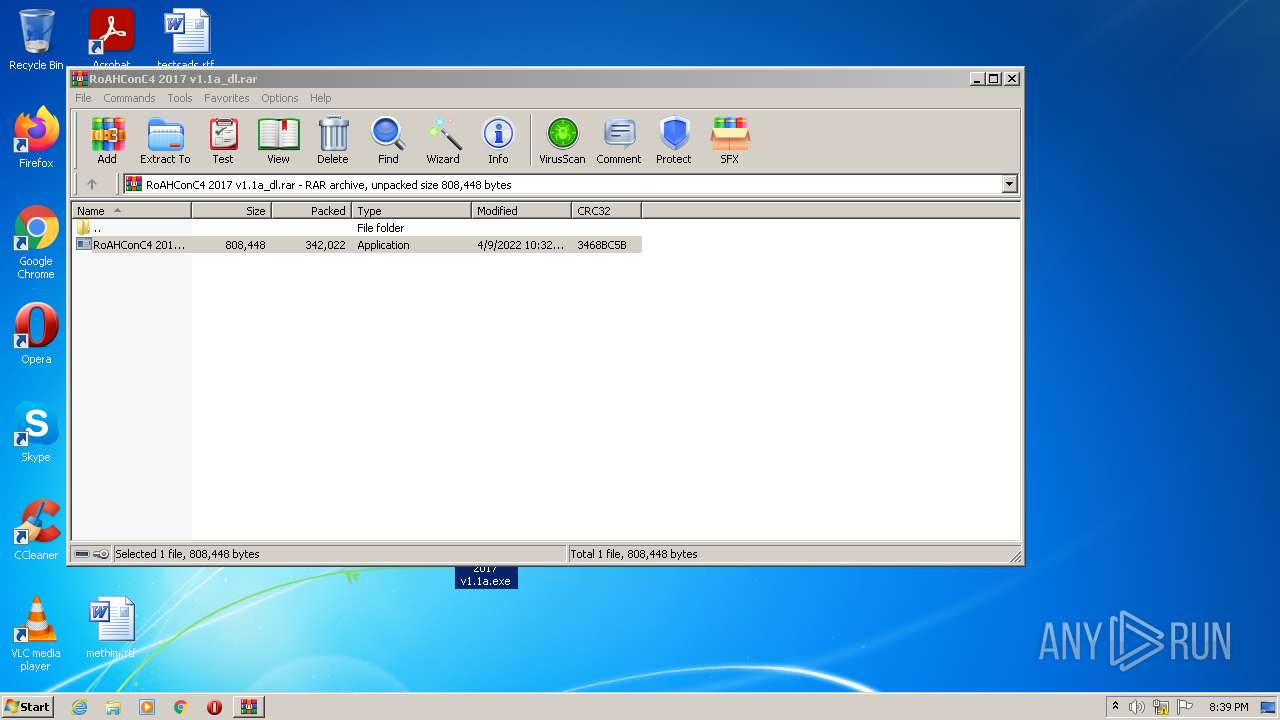
Drops executable file immediately after starts
- WinRAR.exe (PID: 2832)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2832)
- cmd.exe (PID: 1400)
- RoAHConC4 2017 v1.1a.exe (PID: 2440)
- cmd.exe (PID: 2988)
- cmd.exe (PID: 2820)
- cscript.exe (PID: 3932)
- cmd.exe (PID: 2328)
- cmd.exe (PID: 2584)
- cscript.exe (PID: 2640)
- cmd.exe (PID: 3136)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 1140)
- cscript.exe (PID: 3844)
Reads the computer name
- WinRAR.exe (PID: 2832)
- RoAHConC4 2017 v1.1a.exe (PID: 2440)
- cscript.exe (PID: 3932)
- cscript.exe (PID: 2640)
- cscript.exe (PID: 3844)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2832)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2832)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1400)
- cmd.exe (PID: 2988)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3136)
- cmd.exe (PID: 2328)
- cmd.exe (PID: 3116)
Starts CMD.EXE for commands execution
- RoAHConC4 2017 v1.1a.exe (PID: 2440)
- cmd.exe (PID: 1400)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3136)
Application launched itself
- cmd.exe (PID: 1400)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3136)
Executes scripts
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 1140)
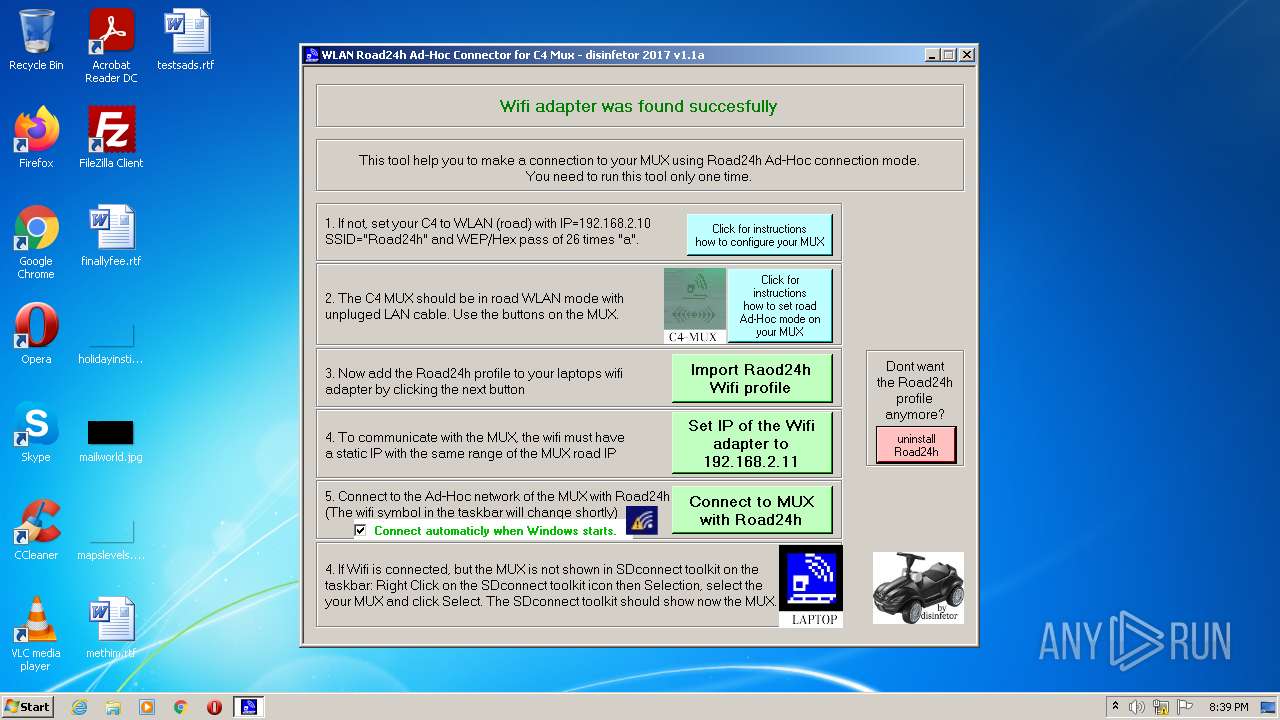
Uses NETSH.EXE for network configuration
- RoAHConC4 2017 v1.1a.exe (PID: 2440)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3136)
Reads Environment values
- netsh.exe (PID: 604)
- netsh.exe (PID: 4028)
- netsh.exe (PID: 2016)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4020)
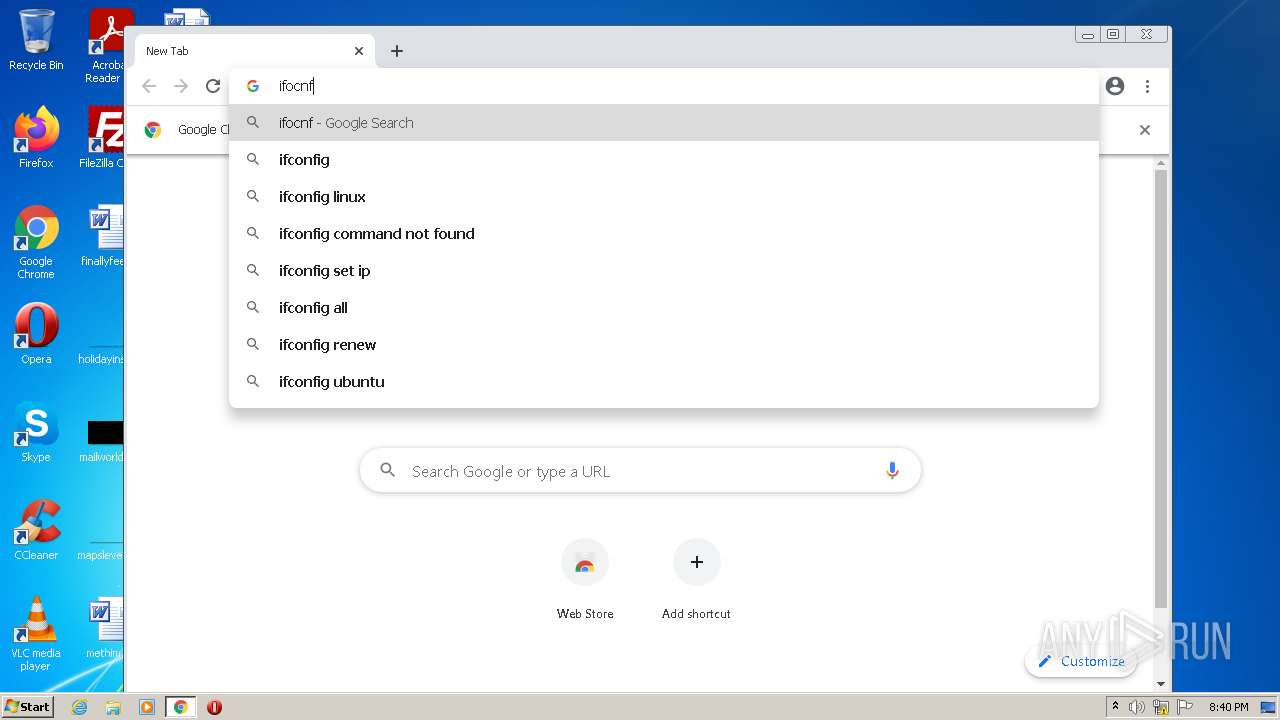
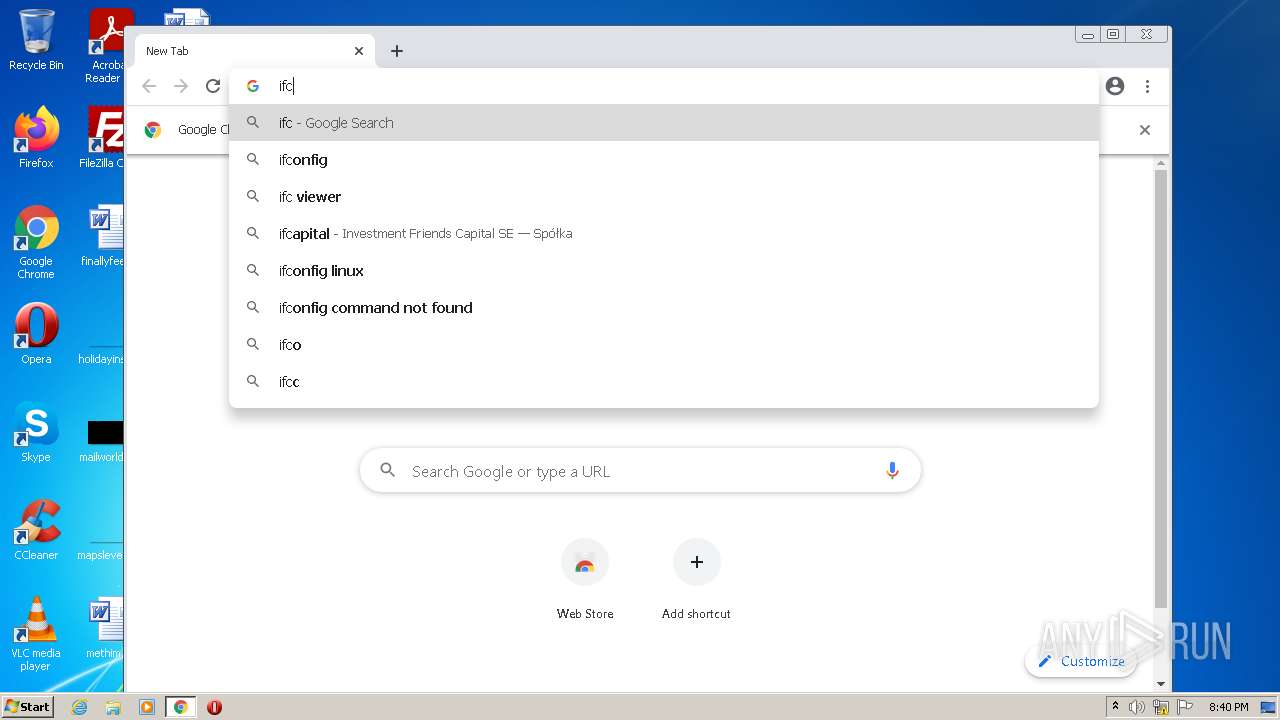
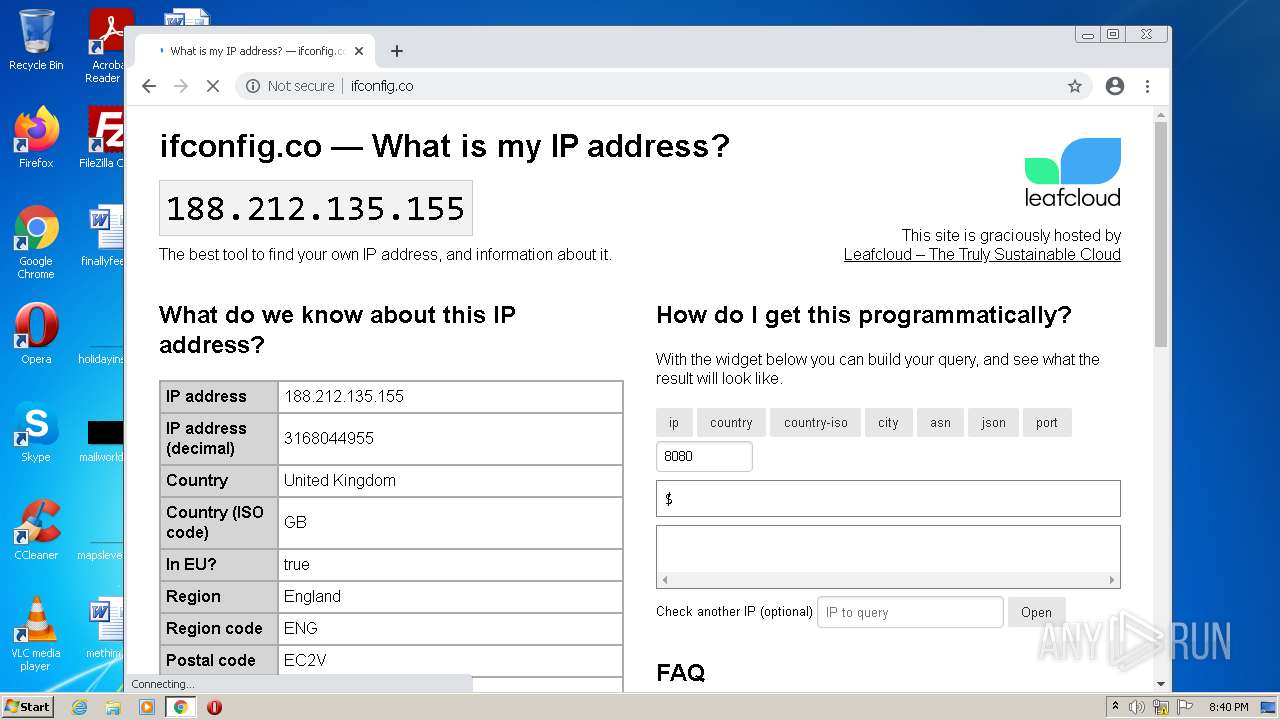
Checks for external IP
- chrome.exe (PID: 3440)
INFO
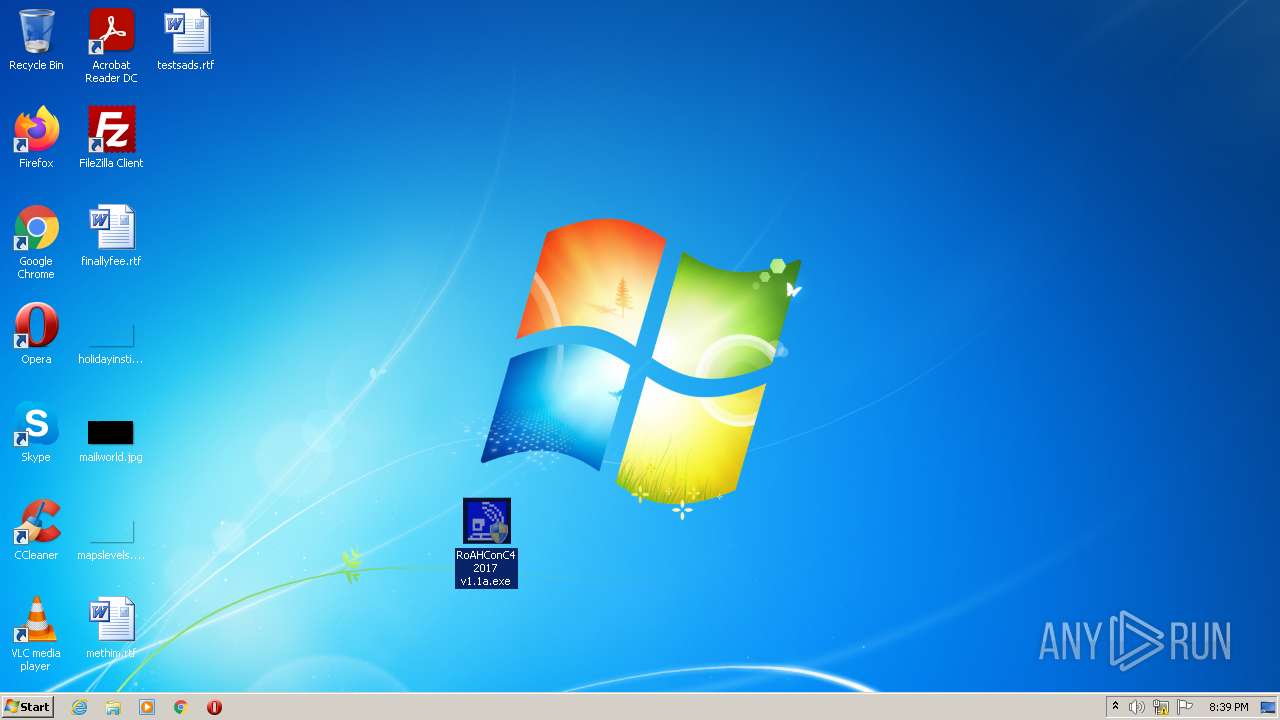
Manual execution by user
- RoAHConC4 2017 v1.1a.exe (PID: 2440)
- RoAHConC4 2017 v1.1a.exe (PID: 2244)
- chrome.exe (PID: 4020)
Checks supported languages
- find.exe (PID: 2604)
- reg.exe (PID: 4048)
- reg.exe (PID: 3080)
- netsh.exe (PID: 604)
- reg.exe (PID: 3880)
- find.exe (PID: 2132)
- reg.exe (PID: 2472)
- netsh.exe (PID: 4028)
- reg.exe (PID: 3568)
- find.exe (PID: 1576)
- reg.exe (PID: 2820)
- netsh.exe (PID: 2016)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 1980)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 2492)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 2344)
- chrome.exe (PID: 1544)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 1832)
- chrome.exe (PID: 2724)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 572)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 1048)
Checks Windows Trust Settings
- cscript.exe (PID: 3932)
- cscript.exe (PID: 2640)
- cscript.exe (PID: 3844)
Reads the computer name
- netsh.exe (PID: 604)
- netsh.exe (PID: 4028)
- netsh.exe (PID: 2016)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 1544)
Reads the hosts file
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3440)
Reads settings of System Certificates
- chrome.exe (PID: 3440)
Application launched itself
- chrome.exe (PID: 4020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
95
Monitored processes
53
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,16769685489511798591,693521267268965974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 604 | "netsh.exe" wlan show driver | C:\Windows\system32\netsh.exe | — | RoAHConC4 2017 v1.1a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,16769685489511798591,693521267268965974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,16769685489511798591,693521267268965974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1140 | C:\Windows\system32\cmd.exe /c cscript //NoLogo ".\detadmin.vbs" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1400 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\\start.bat"" | C:\Windows\system32\cmd.exe | — | RoAHConC4 2017 v1.1a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,16769685489511798591,693521267268965974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3192 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1556 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\\end.bat"" | C:\Windows\system32\cmd.exe | — | RoAHConC4 2017 v1.1a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1576 | find /i "0x1" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,16769685489511798591,693521267268965974,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3664 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 505
Read events
13 266
Write events
238
Delete events
1
Modification events
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\RoAHConC4 2017 v1.1a_dl.rar | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
119
Text files
112
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6287EE94-FB4.pma | — | |
MD5:— | SHA256:— | |||
| 2440 | RoAHConC4 2017 v1.1a.exe | C:\Users\admin\AppData\Local\Temp\start.bat | text | |
MD5:— | SHA256:— | |||
| 2440 | RoAHConC4 2017 v1.1a.exe | C:\Users\admin\AppData\Local\Temp\end.bat | text | |
MD5:— | SHA256:— | |||
| 3136 | cmd.exe | C:\Users\admin\Desktop\detadmin.vbs | text | |
MD5:— | SHA256:— | |||
| 2832 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2832.23021\RoAHConC4 2017 v1.1a.exe | executable | |
MD5:— | SHA256:— | |||
| 1556 | cmd.exe | C:\Users\admin\Desktop\detadmin.vbs | text | |
MD5:— | SHA256:— | |||
| 1400 | cmd.exe | C:\Users\admin\Desktop\detadmin.vbs | text | |
MD5:— | SHA256:— | |||
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ac35aad2-2962-4208-9246-c8d7ceb2ec1d.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
21
DNS requests
18
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3440 | chrome.exe | GET | 200 | 188.114.97.10:80 | http://ifconfig.co/ | US | html | 5.52 Kb | shared |
3440 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3440 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
3440 | chrome.exe | 188.114.97.10:80 | ifconfig.co | Cloudflare Inc | US | malicious |
3440 | chrome.exe | 142.250.185.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3440 | chrome.exe | 142.250.185.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3440 | chrome.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3440 | chrome.exe | 142.250.184.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3440 | chrome.exe | 142.250.74.195:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3440 | chrome.exe | 142.250.185.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 104.17.24.14:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3440 | chrome.exe | 142.250.185.238:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
ifconfig.co |
| shared |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3440 | chrome.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ifconfig. co) |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1 ETPRO signatures available at the full report