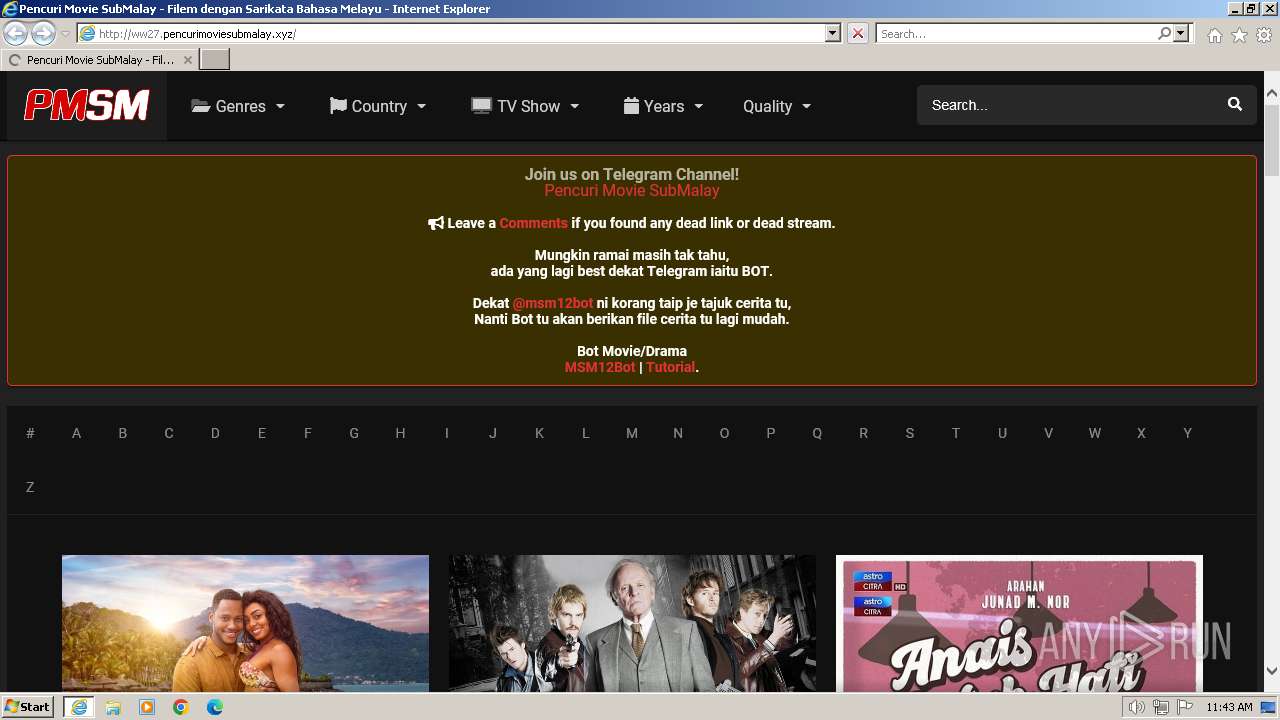
| URL: | ww27.pencurimoviesubmalay.xyz |
| Full analysis: | https://app.any.run/tasks/da1916d6-972b-4ed1-804c-b7608b2bbf36 |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2024, 11:43:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B154B36ABEBDF62EFC188C7DFECF8744 |
| SHA1: | 54398F3876DCF603A56FEB51CEAA17227965EA41 |
| SHA256: | C6A9B731A39B0A6D5EC4629C24C9FF2FA869743AE5F50F049E6DA9D2A265B7C9 |
| SSDEEP: | 3:khALZIMAWSbun:WALZIg9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3700 | "C:\Program Files\Internet Explorer\iexplore.exe" "ww27.pencurimoviesubmalay.xyz" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3952 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3700 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
74 511
Read events
74 385
Write events
91
Delete events
35
Modification events
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31090655 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31090655 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
33
Text files
170
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\MRB2XEJP.txt | text | |
MD5:F190BE43C1CCF8821402D5075C71D338 | SHA256:D88227DBF7E6CACB3EA7C65167D3A0A61AAAE83EEDB3F55703E9043FF3668F86 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\colors.dark.min[1].css | text | |
MD5:E7B7365D4FB0236B5DF80EC3B10A8502 | SHA256:9904853546D3D30611944FE53FF8A7E7CB02E77A5BE14923A347F6964A74E82E | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\front.crollbar.min[1].css | text | |
MD5:9E616D63CBABE72390EDB6A56B0542D5 | SHA256:6E12666BA88AAC25E0A52CB658950B878E5932F258D3D6BDE397542E338A021B | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\front.mobile.min[1].css | text | |
MD5:09DED5F0B08A22E680E6AAF72A4646E7 | SHA256:CDF69F171470ADC15B72F2604BE5440E6D8A8254B8095813596B45694CB51AB8 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\front.owl.min[1].css | text | |
MD5:D85BF9B7C512286B478726A6DE8E238B | SHA256:3B963D8C3B9B23F879654A20F996366D6E2427691C9F480EB78A08BF3F8E032F | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\SRZUCU66.htm | html | |
MD5:9C8310FCA9AFD3A4F12B3F629BB07F2C | SHA256:DD7B7DB792746B8992440E50C87DD0D5CD14440FE0517E11C60A11D562859A5F | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\front.style.min[1].css | text | |
MD5:C09B8D324EEA3E01AB0F0EB66ABA27E8 | SHA256:35A6C6B08117A7C8239667D8C72C17F7E92FBAEDE64B3491B515642C0B86E677 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jquery.min[1].js | text | |
MD5:826EB77E86B02AB7724FE3D0141FF87C | SHA256:CB6F2D32C49D1C2B25E9FFC9AAAFA3F83075346C01BCD4AE6EB187392A4292CF | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\isrepeater[1].js | text | |
MD5:6CEEB6D8B500945A6AAEA27F52F6F5E6 | SHA256:477F24A8AA73997EF9D469763C99D51A9A0E94826DB0525B45542D9D7219E214 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\all.min[1].css | text | |
MD5:95FE9653F2C45892B7E58090566F510F | SHA256:257418DE09101FF7791D410F420F9320141CE0436C264B076D46539B0EA0F830 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
76
DNS requests
24
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/wp-content/themes/dooplay/assets/css/front.owl.min.css?ver=2.5.5 | unknown | compressed | 721 b | unknown |
3952 | iexplore.exe | GET | 200 | 23.109.170.224:80 | http://waiwodemanila.com/rgp1fvw2NgRHdRB/11091 | unknown | binary | 20 b | unknown |
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/wp-content/themes/dooplay/assets/css/front.mobile.min.css?ver=2.5.5 | unknown | compressed | 2.18 Kb | unknown |
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/ | unknown | html | 55.1 Kb | unknown |
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/wp-includes/css/dist/block-library/style.min.css?ver=6.4.3 | unknown | compressed | 14.1 Kb | unknown |
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/wp-includes/js/jquery/jquery-migrate.min.js?ver=3.4.1 | unknown | compressed | 4.76 Kb | unknown |
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/wp-content/themes/dooplay/assets/js/lib/pwsscrollbar.js?ver=2.5.5 | unknown | compressed | 12.5 Kb | unknown |
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/wp-content/themes/dooplay/assets/js/lib/idtabs.js?ver=2.5.5 | unknown | compressed | 691 b | unknown |
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/wp-content/themes/dooplay/assets/js/lib/isrepeater.js?ver=2.5.5 | unknown | compressed | 2.94 Kb | unknown |
3952 | iexplore.exe | GET | 200 | 188.114.97.3:80 | http://ww27.pencurimoviesubmalay.xyz/wp-content/themes/dooplay/assets/img/no/dt_backdrop.png | unknown | image | 692 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3952 | iexplore.exe | 188.114.97.3:80 | ww27.pencurimoviesubmalay.xyz | CLOUDFLARENET | NL | unknown |
3952 | iexplore.exe | 216.58.212.170:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3952 | iexplore.exe | 142.250.186.104:443 | www.googletagmanager.com | GOOGLE | US | unknown |
3952 | iexplore.exe | 138.199.37.231:443 | image.tmdb.org | Datacamp Limited | DE | unknown |
3952 | iexplore.exe | 23.109.170.224:80 | waiwodemanila.com | SERVERS-COM | NL | unknown |
3952 | iexplore.exe | 193.108.153.6:443 | m.media-amazon.com | Akamai International B.V. | DE | unknown |
3952 | iexplore.exe | 188.114.97.3:443 | ww27.pencurimoviesubmalay.xyz | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ww27.pencurimoviesubmalay.xyz |
| unknown |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
waiwodemanila.com |
| unknown |
pl22194197.profitablegatecpm.com |
| unknown |
image.tmdb.org |
| whitelisted |
m.media-amazon.com |
| whitelisted |
telegra.ph |
| malicious |
a.ltrbxd.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3952 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |