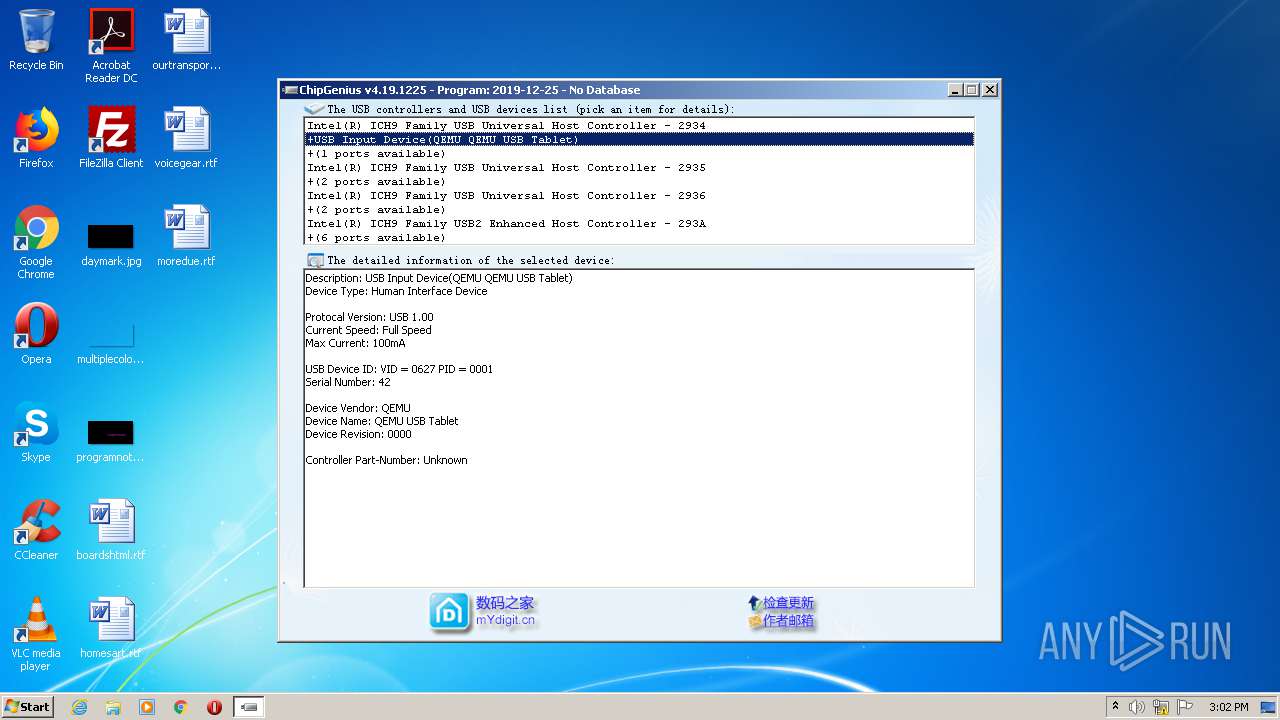
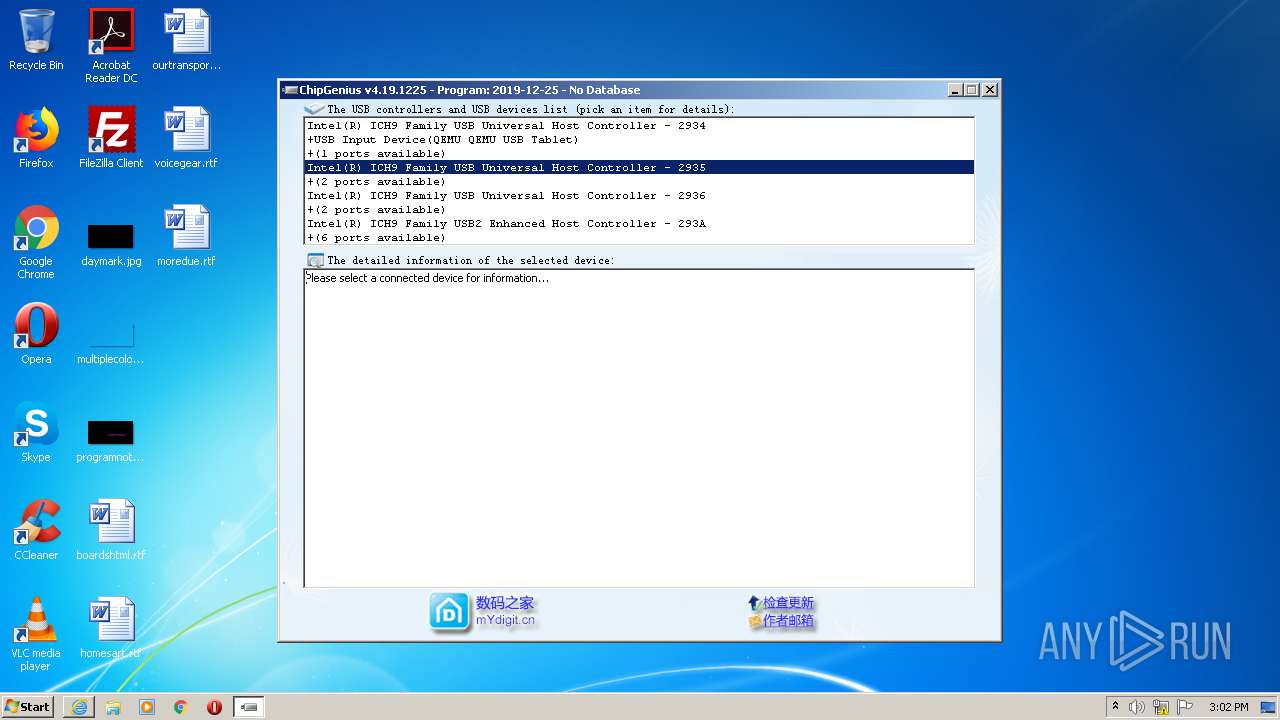
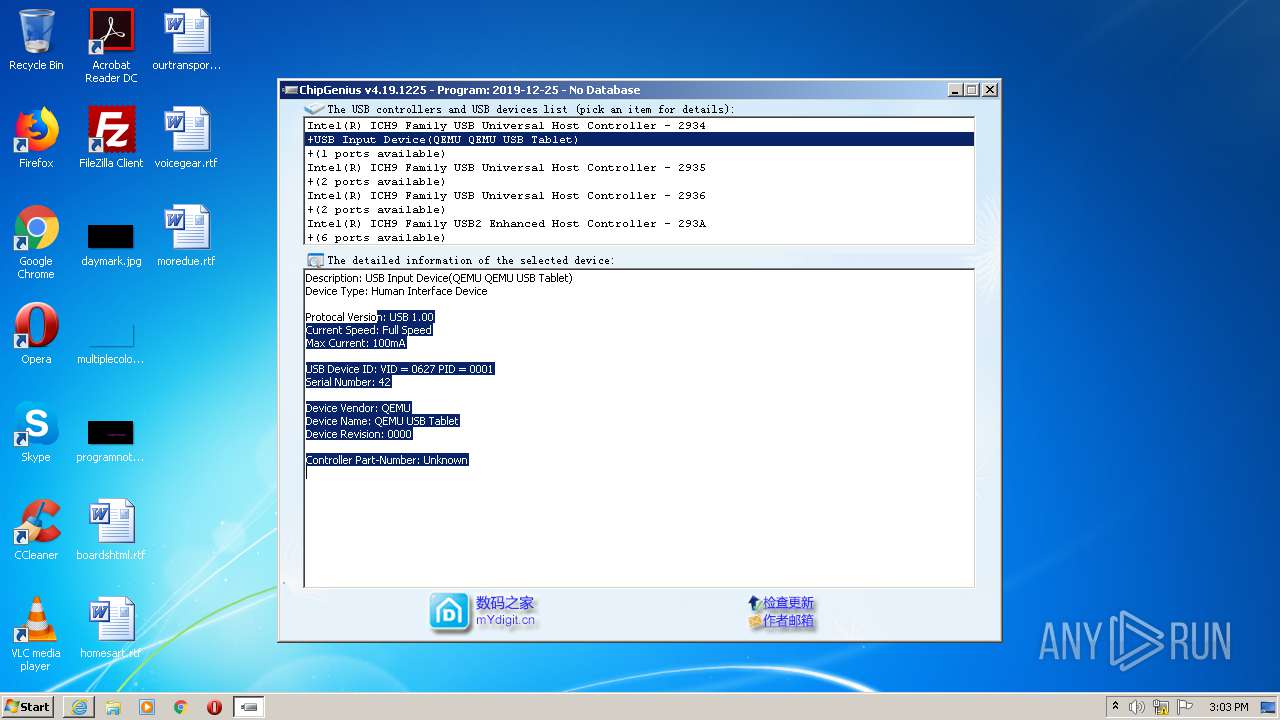
| File name: | ChipGenius.exe |
| Full analysis: | https://app.any.run/tasks/522808d1-dc64-445e-abd6-fe8b7a6b1e8a |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2020, 14:02:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3D9639303432104D35FDB18CC03AE127 |
| SHA1: | 918445EC87A7BB7732B000AFEAF30B5D092C88E2 |
| SHA256: | C6A942D31A6CA5C8F78E30DA41BD6147C0448A16481F3DAA7AA4B6E22E68FED8 |
| SSDEEP: | 3072:w7j8zQvguz7Ka7eupjRMklLez2Zg4LB5tr0j5LapisicWx9h1c5HU8szLS/eA9QM:O8zQbD8kJqchIsiP1D8si/4ioSzPOv |
MALICIOUS
No malicious indicators.SUSPICIOUS
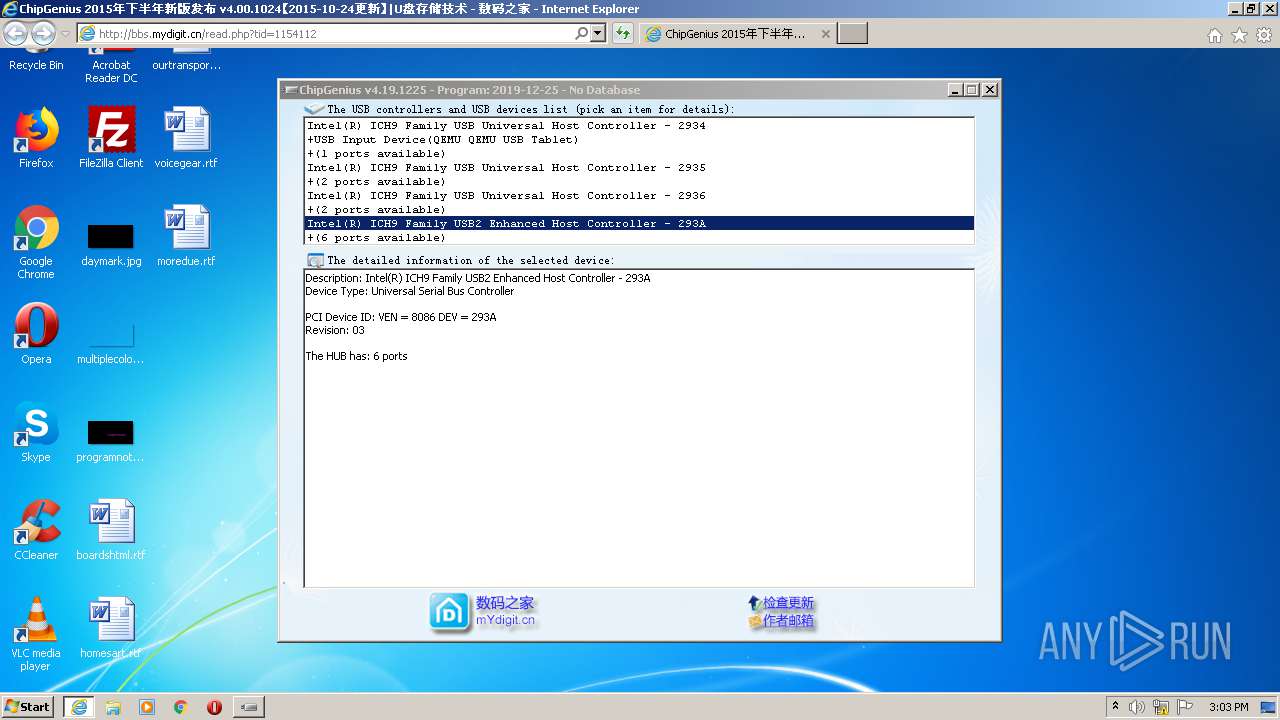
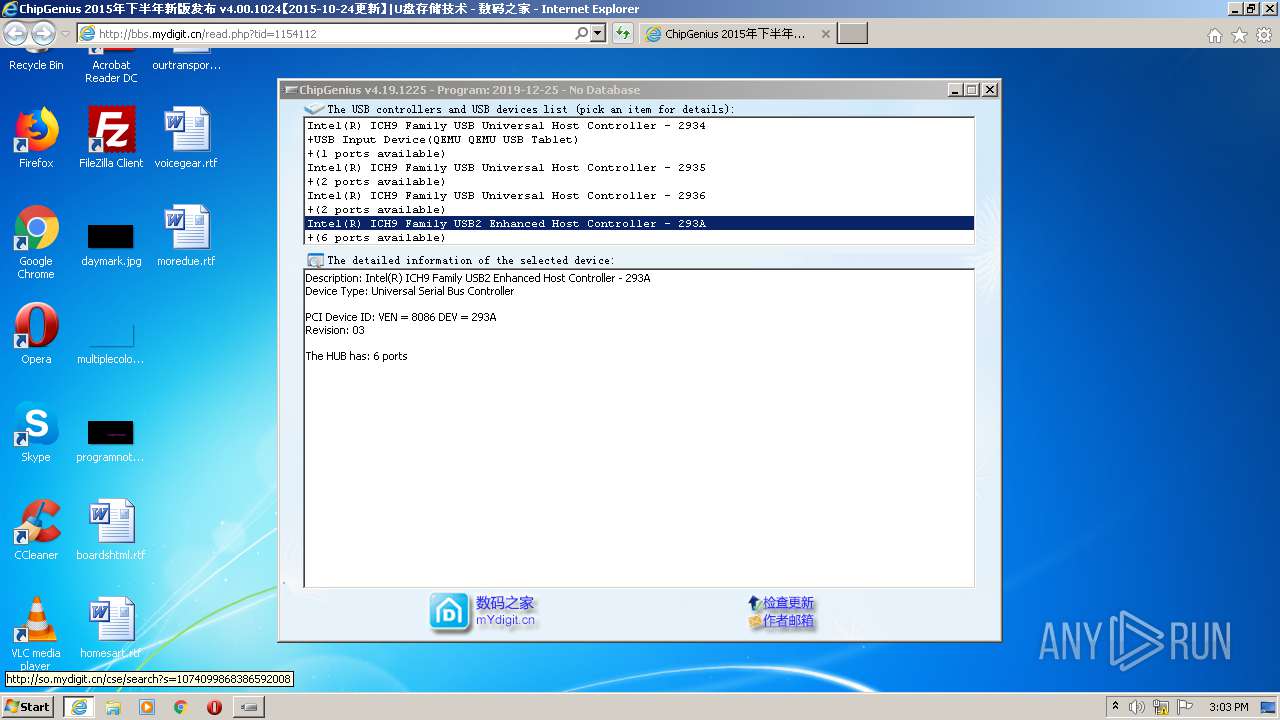
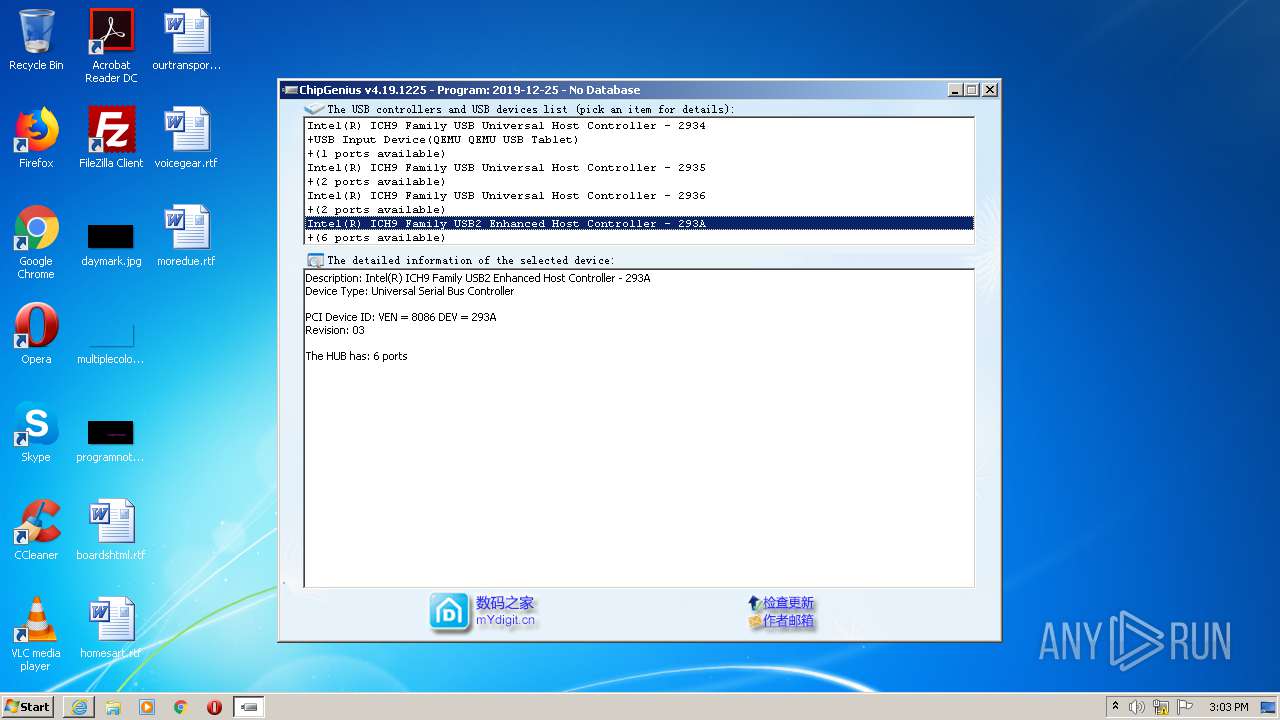
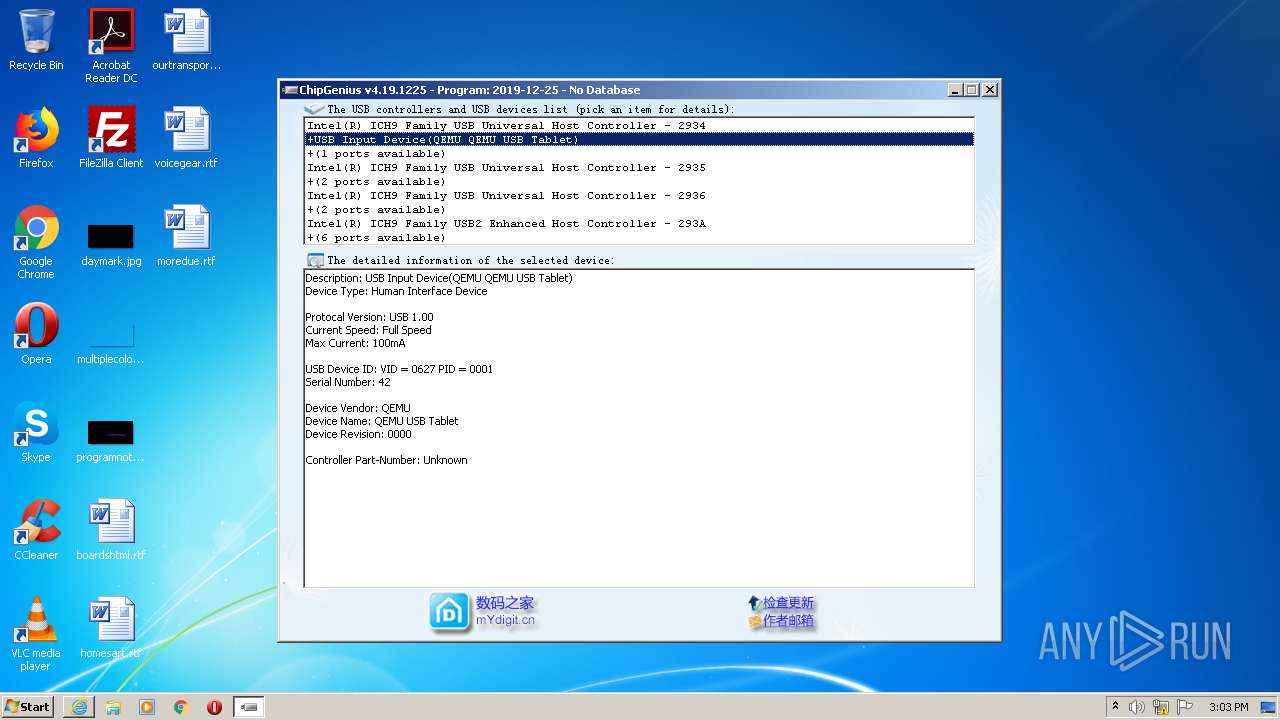
Starts Internet Explorer
- ChipGenius.exe (PID: 3268)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2176)
Reads Internet Cache Settings
- iexplore.exe (PID: 1200)
- iexplore.exe (PID: 2176)
Application launched itself
- iexplore.exe (PID: 2176)
Reads settings of System Certificates
- iexplore.exe (PID: 1200)
- iexplore.exe (PID: 2176)
Reads internet explorer settings
- iexplore.exe (PID: 1200)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1200)
Changes settings of System certificates
- iexplore.exe (PID: 1200)
Creates files in the user directory
- iexplore.exe (PID: 1200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:25 02:03:56+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 208896 |
| InitializedDataSize: | 86016 |
| UninitializedDataSize: | 884736 |
| EntryPoint: | 0x10a6e0 |
| OSVersion: | 4 |
| ImageVersion: | 4.19 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.19.0.1225 |
| ProductVersionNumber: | 4.19.0.1225 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | 方便实用的USB设备主控芯片识别工具 |
| CompanyName: | 数码之家 |
| FileDescription: | U盘/MP3主控芯片识别工具 |
| LegalCopyright: | ~~翁软在线 创意无限~~ |
| LegalTrademarks: | 哈尔滨工业大学研究生院 哈尔滨理工大学软件与微电子学院 |
| ProductName: | Chip Genius |
| FileVersion: | 4.19.1225 |
| ProductVersion: | 4.19.1225 |
| InternalName: | ChipGenius_v4_19_1225 |
| OriginalFileName: | ChipGenius_v4_19_1225.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2019 01:03:56 |
| Detected languages: |
|
| Comments: | 方便实用的USB设备主控芯片识别工具 |
| CompanyName: | 数码之家 |
| FileDescription: | U盘/MP3主控芯片识别工具 |
| LegalCopyright: | ~~翁软在线 创意无限~~ |
| LegalTrademarks: | 哈尔滨工业大学研究生院 哈尔滨理工大学软件与微电子学院 |
| ProductName: | Chip Genius |
| FileVersion: | 4.19.1225 |
| ProductVersion: | 4.19.1225 |
| InternalName: | ChipGenius_v4_19_1225 |
| OriginalFilename: | ChipGenius_v4_19_1225.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Dec-2019 01:03:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UBO0 | 0x00001000 | 0x000D8000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UBO1 | 0x000D9000 | 0x00033000 | 0x00032400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99683 |
.rsrc | 0x0010C000 | 0x00015000 | 0x00014E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.8728 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87973 | 388 | Unicode (UTF 16LE) | Chinese - PRC | RT_MANIFEST |
2 | 0 | 280 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
3 | 0 | 380 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
4 | 0 | 336 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
5 | 0 | 344 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
6 | 0 | 340 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
7 | 0 | 436 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
8 | 0 | 264 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
9 | 0 | 432 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
10 | 0 | 212 | Unicode (UTF 16LE) | Chinese - PRC | RT_STRING |
Imports
KERNEL32.DLL |
MSVBVM60.DLL |
Total processes
43
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1200 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2176 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Internet Explorer\iexplore.exe" http://bbs.mydigit.cn/read.php?tid=1154112 | C:\Program Files\Internet Explorer\iexplore.exe | ChipGenius.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\AppData\Local\Temp\ChipGenius.exe" | C:\Users\admin\AppData\Local\Temp\ChipGenius.exe | — | explorer.exe | |||||||||||
User: admin Company: 数码之家 Integrity Level: MEDIUM Description: U盘/MP3主控芯片识别工具 Exit code: 3221226540 Version: 4.19.1225 Modules
| |||||||||||||||
| 3268 | "C:\Users\admin\AppData\Local\Temp\ChipGenius.exe" | C:\Users\admin\AppData\Local\Temp\ChipGenius.exe | explorer.exe | ||||||||||||
User: admin Company: 数码之家 Integrity Level: HIGH Description: U盘/MP3主控芯片识别工具 Exit code: 0 Version: 4.19.1225 Modules
| |||||||||||||||
Total events
863
Read events
744
Write events
119
Delete events
0
Modification events
| (PID) Process: | (3268) ChipGenius.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 010000000000000084741C994372D601 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2869716384 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30831171 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
17
Text files
96
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1200 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\FZPLIXGG.txt | — | |
MD5:— | SHA256:— | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\3J3Y7CZQ.txt | — | |
MD5:— | SHA256:— | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\VAEYN051.txt | — | |
MD5:— | SHA256:— | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\I5FZV4WA.txt | — | |
MD5:— | SHA256:— | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\WZ4J80T4.txt | text | |
MD5:FB226BDD2C20688AFDAC14AEFC159DF2 | SHA256:323F8C1790005EA34CB62FB3CE225587CFB341B9F278797192CB89A7B17580B2 | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\read[1].htm | html | |
MD5:548166D9B88D4F83B021CA964D37A3D8 | SHA256:C0AC04AEAAC9960F21B9EECACDCCD1037A55AF209DC74BB6CBC135BB8DFA3173 | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\2B5J18N9.txt | text | |
MD5:02A825F0F13993B0A1F01BE348D492DB | SHA256:5F7EC4BD5C8A3710912B1978C9174B48EF54E533E85AFBA228AB4AC2352491C5 | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\d1[1].png | image | |
MD5:5AD960655D4E416BA01CE700CCA6435A | SHA256:04A349A4EA9F014B8C9A107DC777F61F18C4D21D16B08EAF134D95F2CC551E2F | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\home[1].gif | image | |
MD5:1DAB4DA2DA0FB02A4465F03ECF5E6EC4 | SHA256:608153B06D068F918AAA96C8BB0687B6159F2E5583C6865E40551B56F3C7984E | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
103
TCP/UDP connections
94
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1200 | iexplore.exe | GET | 200 | 125.77.197.109:80 | http://bbs.mydigit.cn/u/images/attest/alipay.gif | CN | image | 390 b | unknown |
1200 | iexplore.exe | GET | 200 | 125.77.197.109:80 | http://bbs.mydigit.cn/images/wind/level/18.gif | CN | image | 1.05 Kb | unknown |
1200 | iexplore.exe | GET | 200 | 125.77.197.109:80 | http://bbs.mydigit.cn/data/bbscache/wind_wind.css | CN | text | 6.06 Kb | unknown |
1200 | iexplore.exe | GET | 200 | 125.77.197.109:80 | http://bbs.mydigit.cn/js/pw_ajax.js | CN | text | 12.2 Kb | unknown |
1200 | iexplore.exe | GET | 200 | 125.77.197.109:80 | http://bbs.mydigit.cn/js/core/core.js | CN | html | 23.6 Kb | unknown |
1200 | iexplore.exe | GET | 200 | 125.77.197.109:80 | http://bbs.mydigit.cn/images/wind/logo.png | CN | image | 5.54 Kb | unknown |
1200 | iexplore.exe | GET | 200 | 218.85.137.20:80 | http://img.mydigit.net/upload/middle/87/862887.jpg | CN | image | 5.51 Kb | unknown |
1200 | iexplore.exe | GET | 200 | 218.85.137.20:80 | http://img.mydigit.net/upload/middle/82/20382.jpg | CN | image | 5.59 Kb | unknown |
1200 | iexplore.exe | GET | 200 | 125.77.197.109:80 | http://bbs.mydigit.cn/images/wind/thread/home.gif | CN | image | 1.01 Kb | unknown |
1200 | iexplore.exe | GET | 200 | 218.85.137.20:80 | http://img.mydigit.net/upload/middle/88/1365388.jpg | CN | image | 6.70 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1200 | iexplore.exe | 124.238.241.36:443 | t12.baidu.com | Changsha | CN | unknown |
1200 | iexplore.exe | 125.64.104.36:443 | t12.baidu.com | No.31,Jin-rong Street | CN | unknown |
1200 | iexplore.exe | 125.77.154.35:443 | lupic.cdn.bcebos.com | No.31,Jin-rong Street | CN | malicious |
1200 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1200 | iexplore.exe | 60.190.116.36:443 | t10.baidu.com | No.31,Jin-rong Street | CN | unknown |
1200 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1200 | iexplore.exe | 125.77.197.109:80 | bbs.mydigit.cn | Xiamen | CN | unknown |
1200 | iexplore.exe | 218.85.137.20:80 | img.mydigit.net | Xiamen | CN | unknown |
1200 | iexplore.exe | 113.105.172.35:80 | cpro.baidustatic.com | CHINANET Guangdong province network | CN | suspicious |
2176 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bbs.mydigit.cn |
| unknown |
img.mydigit.net |
| unknown |
cpro.baidustatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
pos.baidu.com |
| whitelisted |
hm.baidu.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
cm.pos.baidu.com |
| whitelisted |
wn.pos.baidu.com |
| whitelisted |