| File name: | SystemEater.exe |
| Full analysis: | https://app.any.run/tasks/8fa43e08-b7a7-4d30-bd45-0b775c458803 |
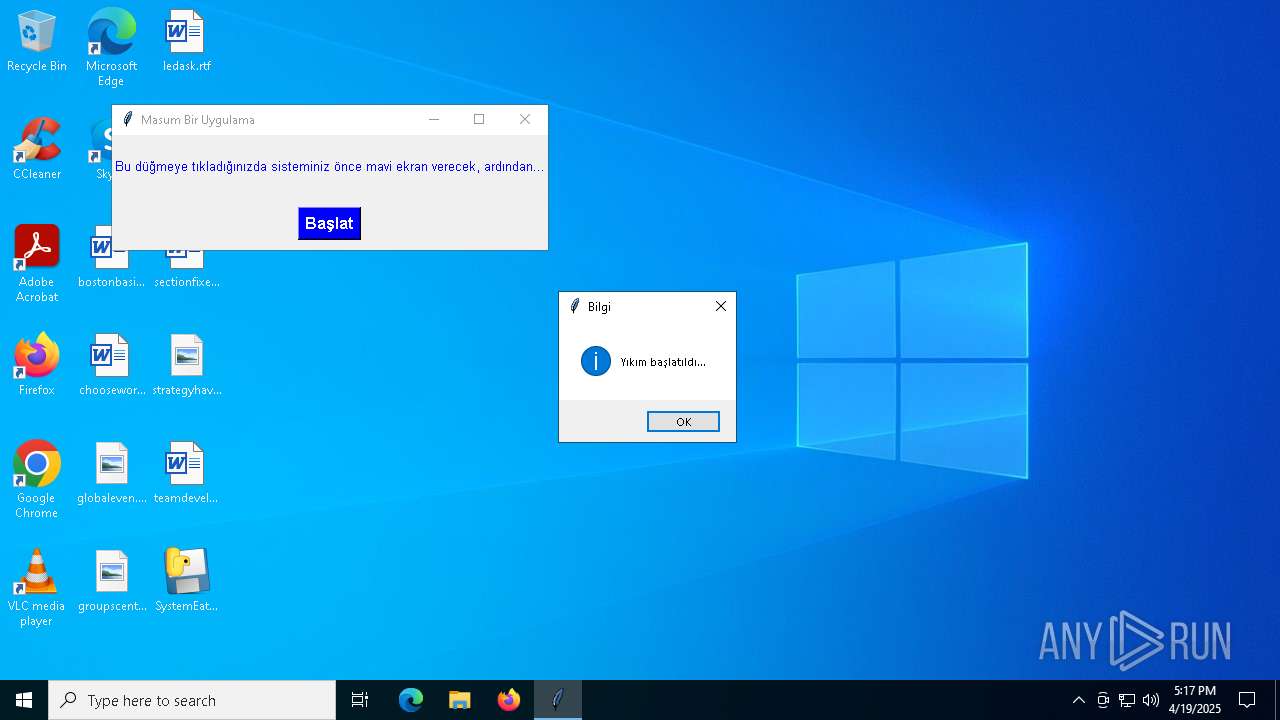
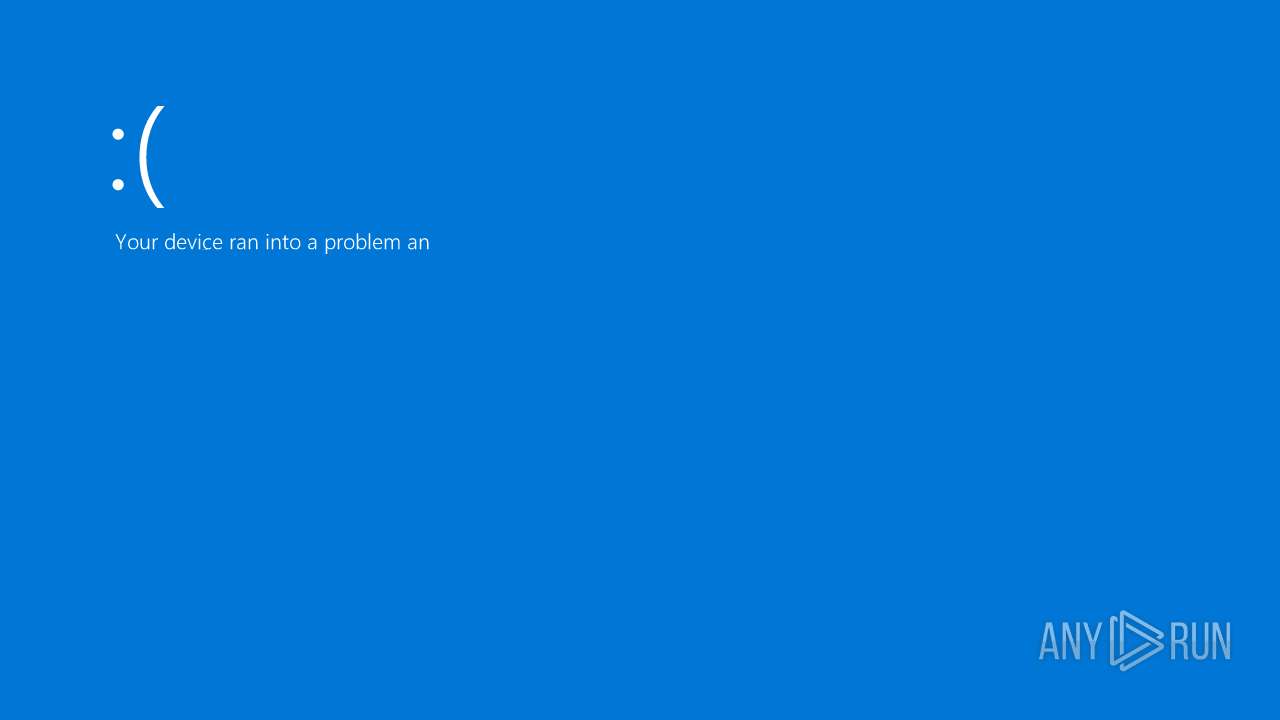
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 17:16:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 4FE046D90E31203A02A889092EDAD301 |
| SHA1: | FD57379DDC3E6C029E8D04101461AA3702655436 |
| SHA256: | C69A4601D2C6A3E328CA10C6514857DA96B89BD73C388B688EFFAD824D73686E |
| SSDEEP: | 98304:A1T2Q6TZP2bx5J1bSNAnYRO4Y6ZhkDQet54nHZU7mgyvOYVAYwVf9TtYw9pk9dbE:V9Tb2TaMLo881mwd/ki+LS3V |
MALICIOUS
No malicious indicators.SUSPICIOUS
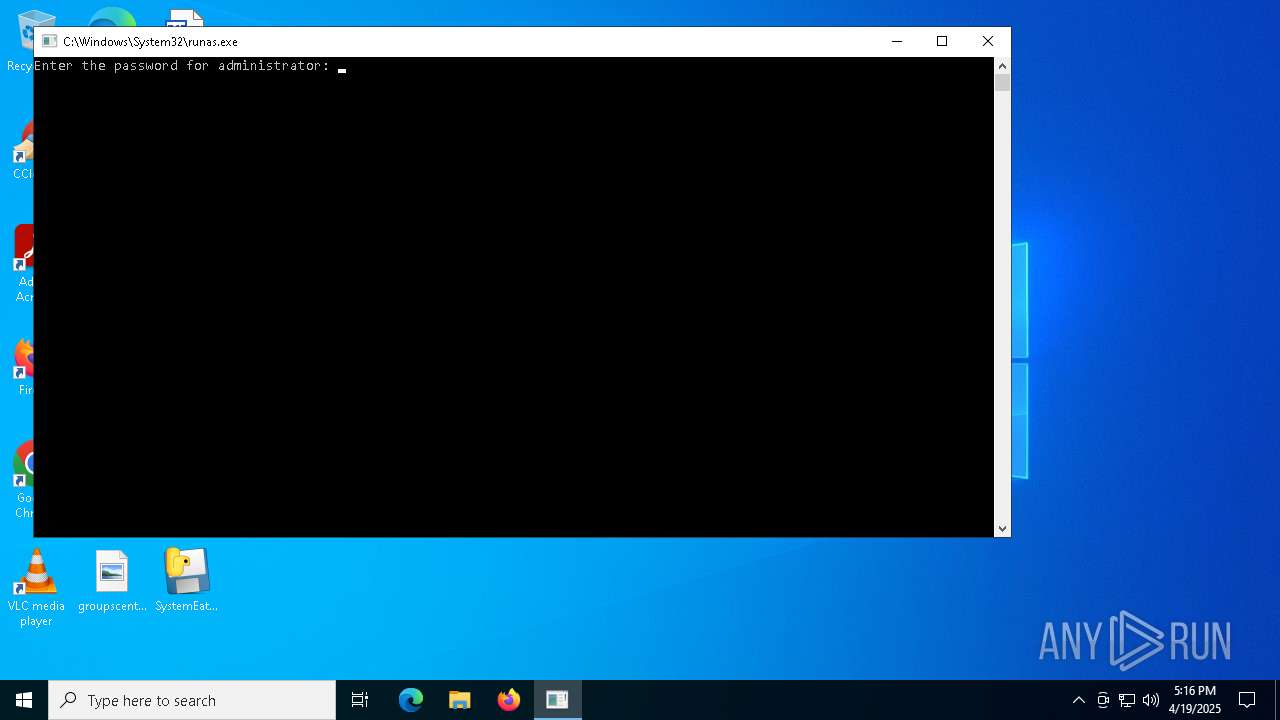
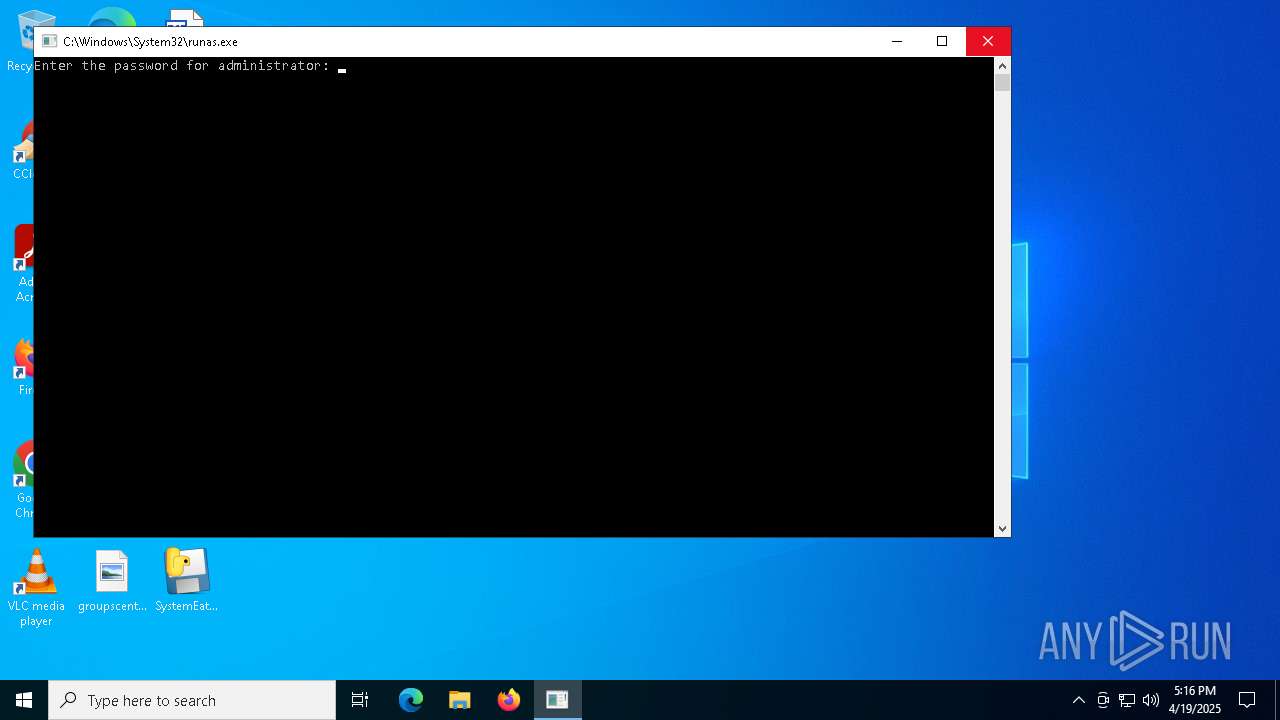
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 1348)
Process drops python dynamic module
- SystemEater.exe (PID: 7748)
Application launched itself
- SystemEater.exe (PID: 7748)
Process drops legitimate windows executable
- SystemEater.exe (PID: 7748)
Executable content was dropped or overwritten
- SystemEater.exe (PID: 7748)
Loads Python modules
- SystemEater.exe (PID: 8088)
The process drops C-runtime libraries
- SystemEater.exe (PID: 7748)
There is functionality for taking screenshot (YARA)
- SystemEater.exe (PID: 7748)
Detected use of alternative data streams (AltDS)
- svchost.exe (PID: 2480)
- svchost.exe (PID: 1760)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3644)
Creates file in the systems drive root
- svchost.exe (PID: 1760)
Searches for installed software
- svchost.exe (PID: 5636)
INFO
Reads the computer name
- SystemEater.exe (PID: 7748)
- SystemEater.exe (PID: 8088)
- OfficeClickToRun.exe (PID: 2948)
- TrustedInstaller.exe (PID: 5040)
- PLUGScheduler.exe (PID: 3644)
- uhssvc.exe (PID: 6328)
Create files in a temporary directory
- SystemEater.exe (PID: 7748)
Checks supported languages
- SystemEater.exe (PID: 7748)
- SystemEater.exe (PID: 8088)
- OfficeClickToRun.exe (PID: 2948)
- PLUGScheduler.exe (PID: 3644)
- TrustedInstaller.exe (PID: 5040)
- uhssvc.exe (PID: 6328)
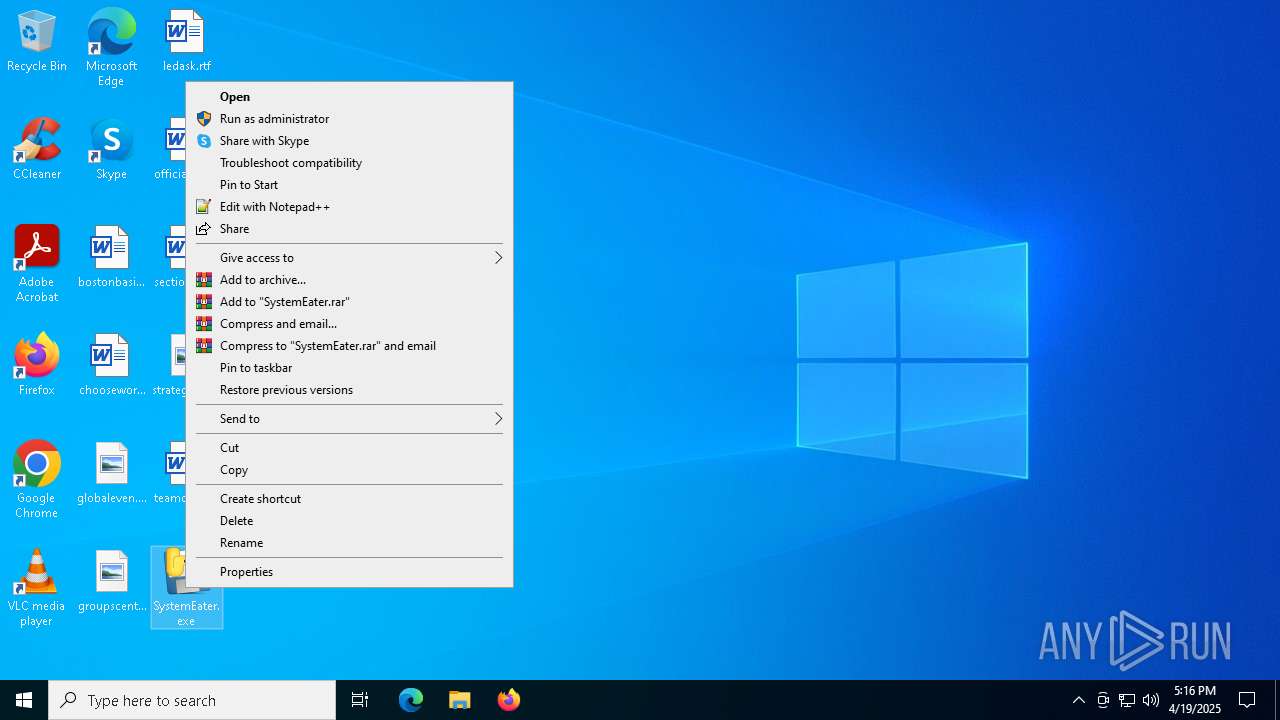
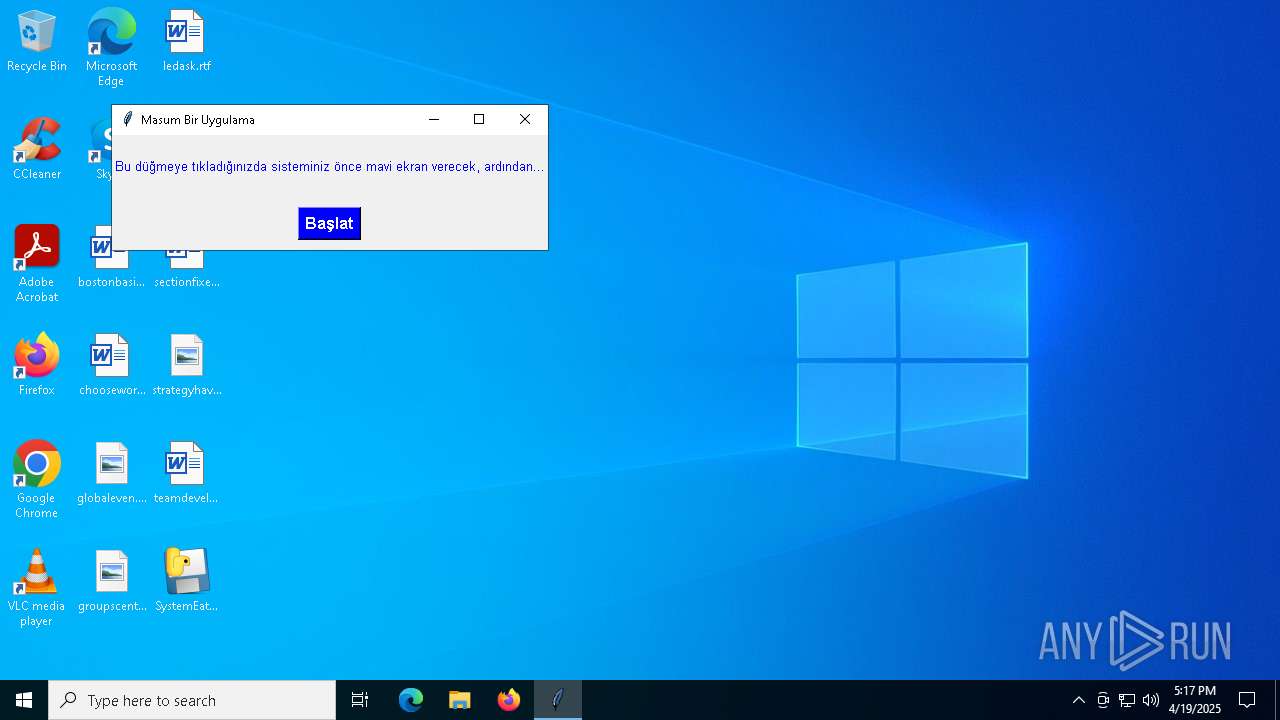
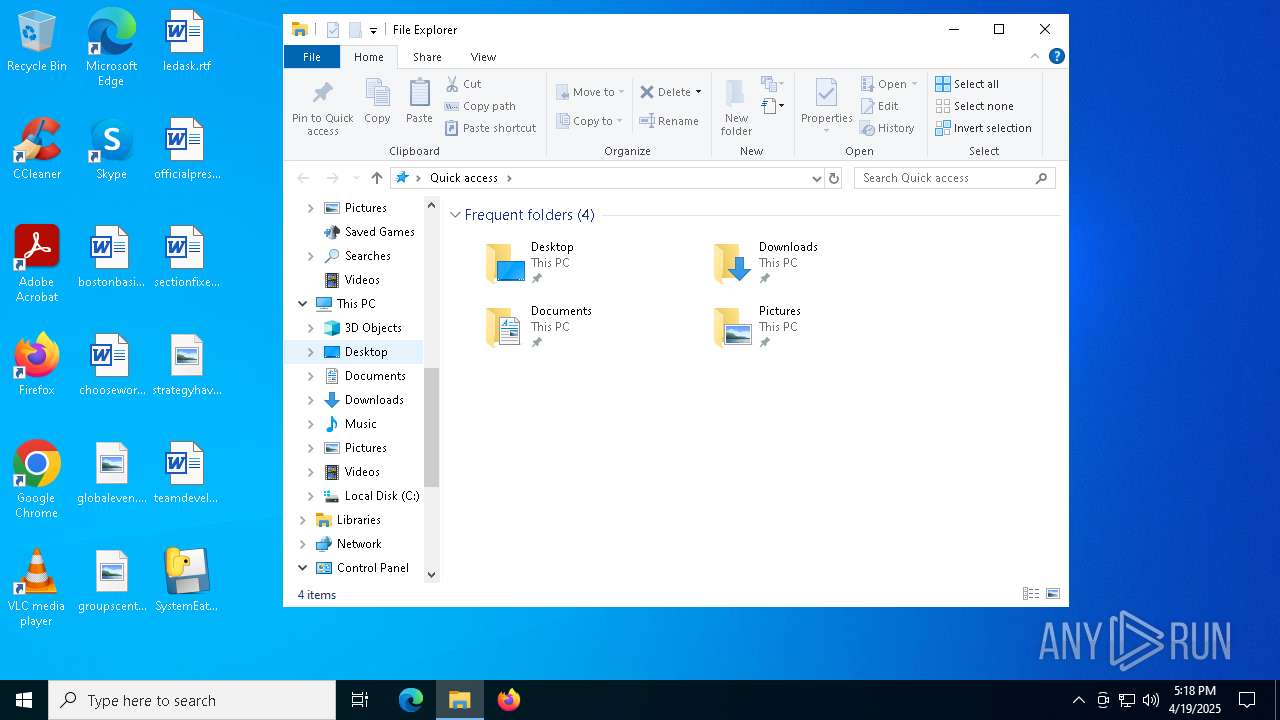
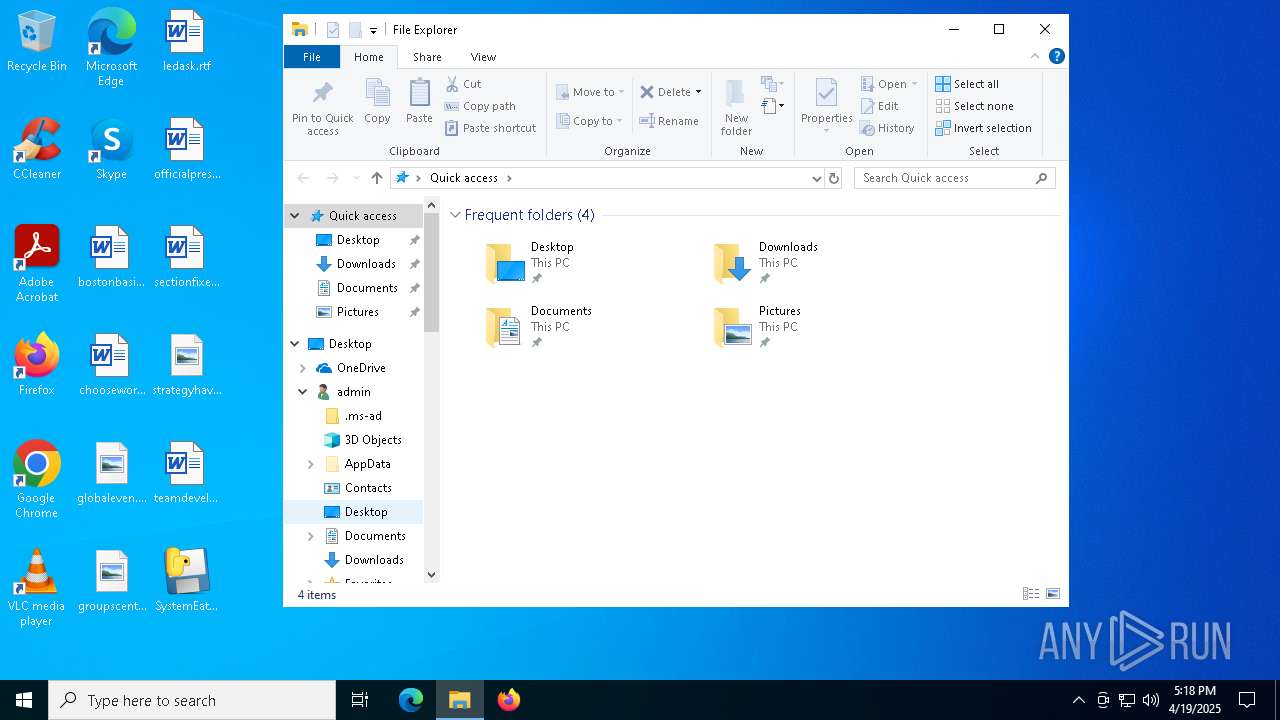
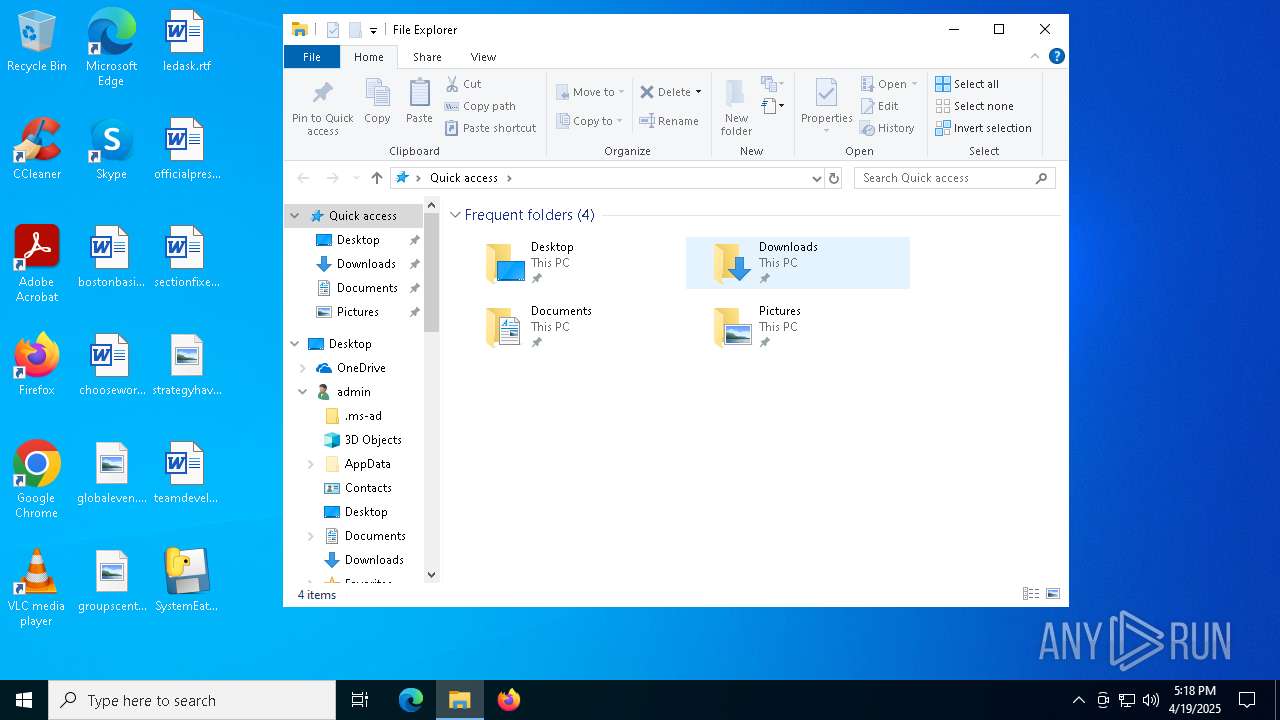
Manual execution by a user
- SystemEater.exe (PID: 7748)
- svchost.exe (PID: 1324)
- svchost.exe (PID: 1472)
- svchost.exe (PID: 1520)
- svchost.exe (PID: 1548)
- svchost.exe (PID: 1600)
- svchost.exe (PID: 1700)
- upfc.exe (PID: 1668)
- svchost.exe (PID: 1740)
- svchost.exe (PID: 1980)
- svchost.exe (PID: 1748)
- svchost.exe (PID: 1760)
- svchost.exe (PID: 1780)
- svchost.exe (PID: 1936)
- svchost.exe (PID: 2000)
- svchost.exe (PID: 2176)
- svchost.exe (PID: 2016)
- svchost.exe (PID: 2096)
- svchost.exe (PID: 2376)
- svchost.exe (PID: 2924)
- svchost.exe (PID: 2380)
- spoolsv.exe (PID: 2448)
- svchost.exe (PID: 2456)
- svchost.exe (PID: 2620)
- svchost.exe (PID: 2864)
- svchost.exe (PID: 2940)
- svchost.exe (PID: 2964)
- svchost.exe (PID: 2956)
- svchost.exe (PID: 2972)
- svchost.exe (PID: 2184)
- svchost.exe (PID: 2192)
- svchost.exe (PID: 2208)
- svchost.exe (PID: 2280)
- svchost.exe (PID: 2360)
- svchost.exe (PID: 2368)
- OfficeClickToRun.exe (PID: 2948)
- svchost.exe (PID: 2124)
- svchost.exe (PID: 2480)
- svchost.exe (PID: 2572)
- svchost.exe (PID: 3080)
- svchost.exe (PID: 3280)
- svchost.exe (PID: 2984)
- svchost.exe (PID: 2472)
- svchost.exe (PID: 3772)
- svchost.exe (PID: 3788)
- svchost.exe (PID: 3856)
- sppsvc.exe (PID: 3900)
- svchost.exe (PID: 3968)
- svchost.exe (PID: 4372)
- svchost.exe (PID: 4544)
- svchost.exe (PID: 4148)
- svchost.exe (PID: 4256)
- TrustedInstaller.exe (PID: 5040)
- svchost.exe (PID: 4816)
- svchost.exe (PID: 5084)
- svchost.exe (PID: 4760)
- svchost.exe (PID: 5756)
- svchost.exe (PID: 6416)
- svchost.exe (PID: 6556)
- svchost.exe (PID: 6964)
- svchost.exe (PID: 5636)
- svchost.exe (PID: 908)
- svchost.exe (PID: 5412)
- svchost.exe (PID: 5896)
- uhssvc.exe (PID: 6328)
- svchost.exe (PID: 6708)
- svchost.exe (PID: 4144)
- svchost.exe (PID: 5652)
- svchost.exe (PID: 6620)
- svchost.exe (PID: 2388)
- svchost.exe (PID: 4824)
- svchost.exe (PID: 5852)
PyInstaller has been detected (YARA)
- SystemEater.exe (PID: 7748)
The sample compiled with english language support
- SystemEater.exe (PID: 7748)
Reads the time zone
- svchost.exe (PID: 1324)
- svchost.exe (PID: 2376)
- svchost.exe (PID: 2956)
- svchost.exe (PID: 5852)
Creates files in the program directory
- svchost.exe (PID: 2208)
- svchost.exe (PID: 4760)
- svchost.exe (PID: 5852)
- PLUGScheduler.exe (PID: 3644)
- svchost.exe (PID: 6964)
- uhssvc.exe (PID: 6328)
- svchost.exe (PID: 908)
Reads security settings of Internet Explorer
- svchost.exe (PID: 2984)
- svchost.exe (PID: 2472)
- svchost.exe (PID: 4148)
- sihost.exe (PID: 1120)
- svchost.exe (PID: 5652)
- svchost.exe (PID: 2376)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 2948)
Reads the machine GUID from the registry
- OfficeClickToRun.exe (PID: 2948)
Checks proxy server information
- OfficeClickToRun.exe (PID: 2948)
- svchost.exe (PID: 2984)
Disables trace logs
- svchost.exe (PID: 3280)
Reads the software policy settings
- OfficeClickToRun.exe (PID: 2948)
Application launched itself
- msedge.exe (PID: 5992)
- msedge.exe (PID: 5668)
Reads Environment values
- uhssvc.exe (PID: 6328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:19 17:09:53+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 173568 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
286
Monitored processes
85
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 908 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s DsmSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | sihost.exe | C:\Windows\System32\sihost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Shell Infrastructure Host Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\System32\svchost.exe -k LocalServiceNetworkRestricted -p -s EventLog | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\Desktop\SystemEater.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s ProfSvc | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | C:\WINDOWS\system32\svchost.exe -k LocalService -p -s DispBrokerDesktopSvc | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s UserManager | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1548 | C:\WINDOWS\system32\svchost.exe -k LocalService -p -s nsi | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1600 | C:\WINDOWS\system32\svchost.exe -k LocalServiceNetworkRestricted -p -s Dhcp | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | C:\WINDOWS\System32\Upfc.exe /launchtype boot /cv FILrwQqCb0GJkQFA4r4X8g.0 | C:\Windows\System32\upfc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Updateability From SCM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
98 963
Read events
81 760
Write events
17 104
Delete events
99
Modification events
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\State |
| Operation: | delete value | Name: | LastRestoreId |
Value: | |||
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Reliability |
| Operation: | write | Name: | DirtyShutdown |
Value: 1 | |||
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Reliability |
| Operation: | write | Name: | DirtyShutdownTime |
Value: E907010005001F000900360023007E00 | |||
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\State |
| Operation: | write | Name: | 6005BT |
Value: C0A9C6054FB1DB01 | |||
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Reliability |
| Operation: | write | Name: | LastAliveStamp |
Value: D0BAAD0B | |||
| (PID) Process: | (1668) upfc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\WaaS\Upfc |
| Operation: | write | Name: | InstanceInProgress |
Value: 1 | |||
| (PID) Process: | (1668) upfc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\WaaS\Upfc |
| Operation: | write | Name: | InstanceInProgress |
Value: 0 | |||
| (PID) Process: | (1600) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\mpssvc\Parameters\PortKeywords\DHCP |
| Operation: | write | Name: | Collection |
Value: | |||
| (PID) Process: | (1600) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{d950ca8d-448e-4ca2-89de-a65a1ac2b2a6} |
| Operation: | delete value | Name: | DhcpClassIdBin |
Value: | |||
| (PID) Process: | (1600) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip\Parameters |
| Operation: | delete value | Name: | DhcpNameServer |
Value: | |||
Executable files
17
Suspicious files
231
Text files
932
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\SysDel.exe | executable | |
MD5:75672EDBA5C156AE3D83EF35EBF43053 | SHA256:BE70DD74FD603BD3D3DFAE6499AEA92BF8F985DDAC43FC52139384748363A0FA | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\VCRUNTIME140.dll | executable | |
MD5:32DA96115C9D783A0769312C0482A62D | SHA256:8B10C53241726B0ACC9F513157E67FCB01C166FEC69E5E38CA6AADA8F9A3619F | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\_ctypes.pyd | executable | |
MD5:29873384E13B0A78EE9857604161514B | SHA256:3CC8500A958CC125809B0467930EBCCE88A09DCC0CEDD7A45FACF3E332F7DB33 | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\_decimal.pyd | executable | |
MD5:21FCB8E3D4310346A5DC1A216E7E23CA | SHA256:9A0E05274CAD8D90F6BA6BC594261B36BFBDDF4F5CA6846B6367FE6A4E2FDCE4 | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\_bz2.pyd | executable | |
MD5:684D656AADA9F7D74F5A5BDCF16D0EDB | SHA256:A5DFB4A663DEF3D2276B88866F6D220F6D30CC777B5D841CF6DBB15C6858017C | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\_hashlib.pyd | executable | |
MD5:3E540EF568215561590DF215801B0F59 | SHA256:0ED7A6ED080499BC6C29D7113485A8A61BDBA93087B010FCA67D9B8289CBE6FA | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\_lzma.pyd | executable | |
MD5:D63E2E743EA103626D33B3C1D882F419 | SHA256:7C2D2030D5D246739C5D85F087FCF404BC36E1815E69A8AC7C9541267734FC28 | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\_socket.pyd | executable | |
MD5:566CB4D39B700C19DBD7175BD4F2B649 | SHA256:77EBA293FE03253396D7BB6E575187CD026C80766D7A345EB72AD92F0BBBC3AA | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\_tcl_data\encoding\big5.enc | text | |
MD5:41A874778111CC218BD421CF9C795EC2 | SHA256:AD1ED201B69855BFD353BF969DFC55576DA35A963ABF1BF7FC6D8B5142A61A61 | |||
| 7748 | SystemEater.exe | C:\Users\admin\AppData\Local\Temp\_MEI77482\_tcl_data\auto.tcl | text | |
MD5:97EFA9EBE840EA051F9706504C8BD783 | SHA256:08113823951619D659EB03A1F6ACD2F9500E1264795219125A5DF7B83CABCB99 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
60
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7924 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7924 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5484 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1028 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1144 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6456 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7924 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |