| File name: | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\~patchfile.tmp |
| Full analysis: | https://app.any.run/tasks/aab201a6-6e46-49c1-9b3a-59b628c0ed7b |
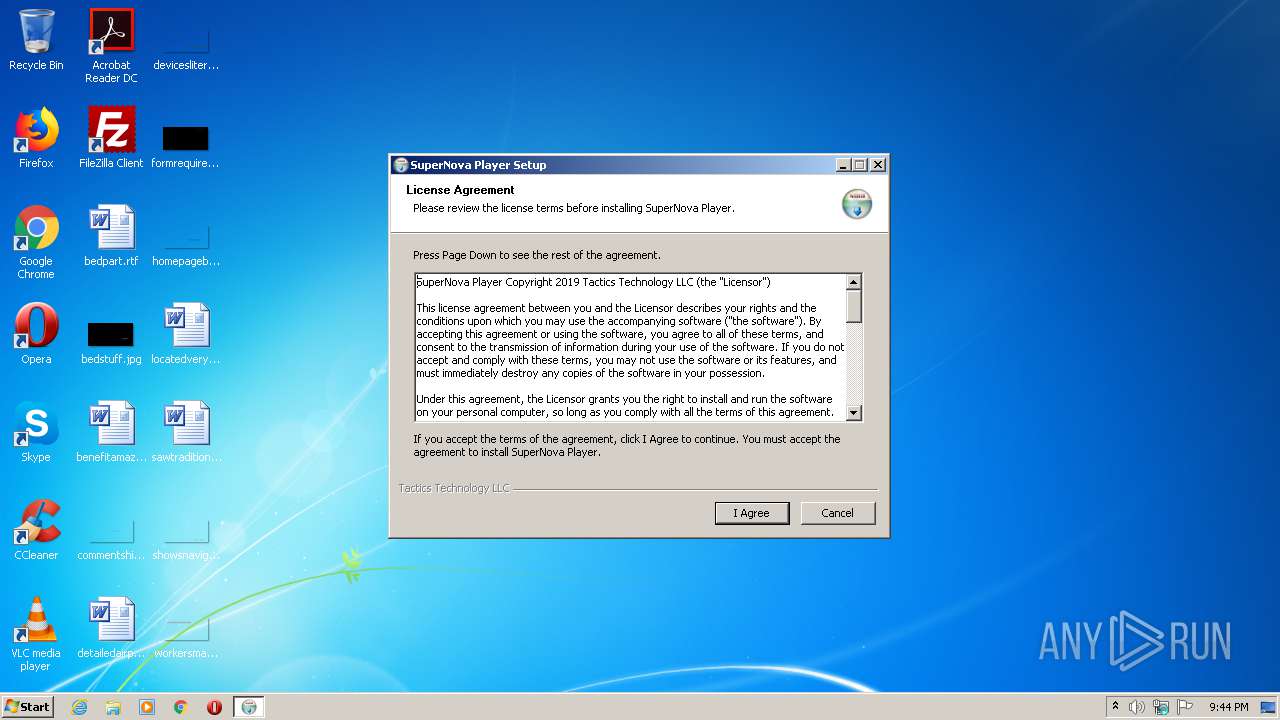
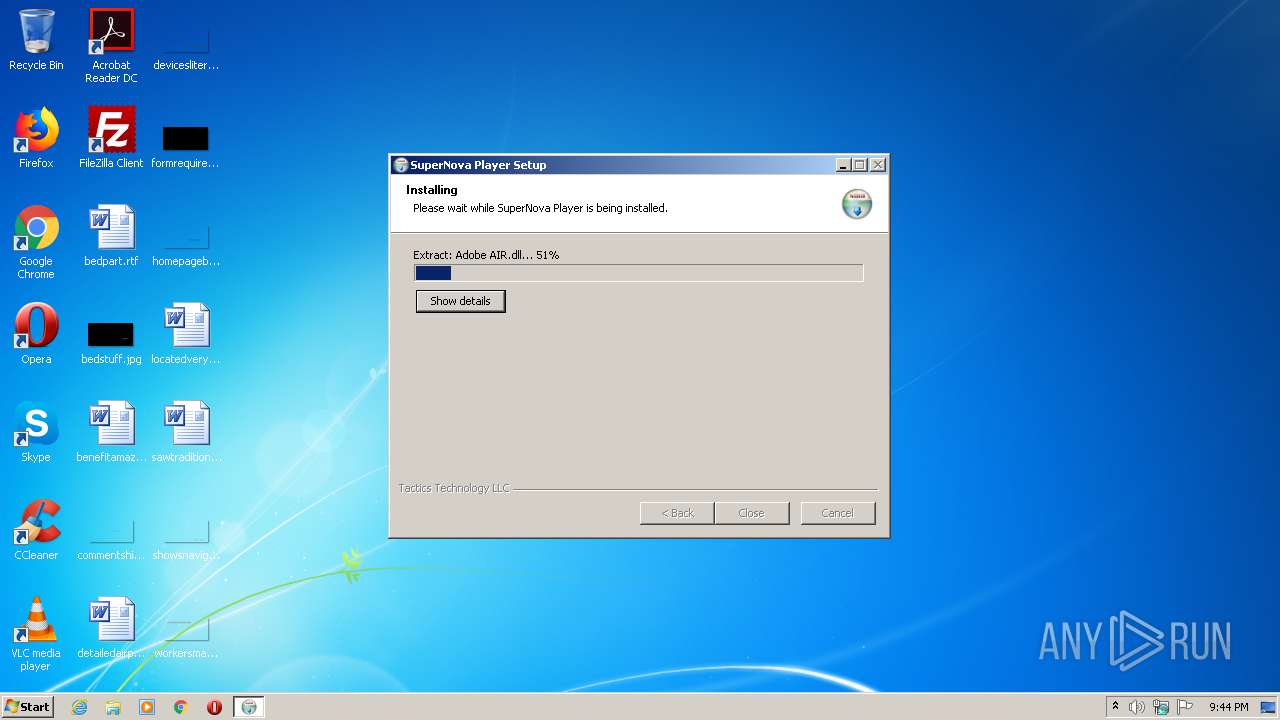
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2021, 20:43:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 056E0FA934F42E91E1E35A3F5B05169A |
| SHA1: | 369531A2652D9A63AAC75E4F3BFC427808EB9BFA |
| SHA256: | C693F1A8407CB117F41B97D4D9EEC8FAAD40FF9811384809941A43801B46A86E |
| SSDEEP: | 786432:dCBZNFV+3q3ImDw1aoOLaAw50D26BY4MCfQCW5P5vycG:sBZLVDw1ahLaA+03BYfB5vyX |
MALICIOUS
Application was dropped or rewritten from another process
- chginteg.exe (PID: 2064)
- chginteg.exe (PID: 1400)
- chginteg.exe (PID: 2380)
- chginteg.exe (PID: 3788)
- chginteg.exe (PID: 3388)
- chginteg.exe (PID: 2652)
- chginteg.exe (PID: 1252)
SUSPICIOUS
Executable content was dropped or overwritten
- ~patchfile.tmp.exe (PID: 2312)
Drops a file that was compiled in debug mode
- ~patchfile.tmp.exe (PID: 2312)
Creates a software uninstall entry
- ~patchfile.tmp.exe (PID: 2312)
Creates files in the user directory
- ~patchfile.tmp.exe (PID: 2312)
Changes default file association
- ~patchfile.tmp.exe (PID: 2312)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:32 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40386 |
.rdata | 0x00008000 | 0x00001250 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04481 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22445 |
.ndata | 0x00025000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00033000 | 0x000042C0 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.93302 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29611 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
44
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1252 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\www.macromedia.com" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe | — | ~patchfile.tmp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe | — | ~patchfile.tmp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sol" -med | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe | — | ~patchfile.tmp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3 Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\AppData\Local\Temp\~patchfile.tmp.exe" | C:\Users\admin\AppData\Local\Temp\~patchfile.tmp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\#SharedObjects" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe | — | ~patchfile.tmp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2652 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe | — | ~patchfile.tmp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\Logs" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe | — | ~patchfile.tmp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3788 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\openssl" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe | — | ~patchfile.tmp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
348
Read events
333
Write events
15
Delete events
0
Modification events
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CURRENT_USER\Software\TacticsTechnologySuperNova |
| Operation: | write | Name: | Install_Dir |
Value: C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CURRENT_USER\Software\TacticsTechnologySuperNova |
| Operation: | write | Name: | Version |
Value: 0.1.23 | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | DisplayName |
Value: SuperNova Player | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\uninstall.exe" | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\SuperNova Launcher.exe | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CLASSES_ROOT\supernova |
| Operation: | write | Name: | (default) |
Value: SuperNova Launcher | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CLASSES_ROOT\supernova |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (2312) ~patchfile.tmp.exe | Key: | HKEY_CLASSES_ROOT\supernova\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\SuperNova Launcher.exe",0 | |||
Executable files
16
Suspicious files
2
Text files
31
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\SuperNova Launcher.exe | executable | |
MD5:876EEF07CB24F6BE1D1F2018EFBA14EA | SHA256:94C007D27B644662DD9ABD3B63647C20176FF490DB6815EB833D417E1DA92683 | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\currentversion | text | |
MD5:F50B3648CB98EC69FF083BD113389E87 | SHA256:F3DDB4109C5AFDDAB1F3A7AD19FB9450B6629E4247DDFC8D88C8B6F70F04A27B | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\updater.cfg | text | |
MD5:EBBFE0DAE6078482CD4B29D870C1BE26 | SHA256:058B8EA5C883D189DB0B3B7BB0F6F2E8B2D0046A10FE9FC2169817627C84F395 | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\chginteg.exe | executable | |
MD5:7E86DBB05DF26824CE7D2C2F9A486D2C | SHA256:3341873244C2BA4C1E4B71A52992669150D269D93B6E9143E7171F52EF0B0464 | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\launcher\snlauncher.exe | executable | |
MD5:0C7C77194BFAAF9BAC5D1C721486A662 | SHA256:9E5245CE1FEEC92765E5435F6948769ABE82458B13F38AF55222CEF943E22FF5 | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\launcher\snlauncher.swf | swf | |
MD5:0C71FD6B531150CC1548128FBE780294 | SHA256:B230561DC9A071EB7E7A2675CB7ED100B27D255F1A29259AC0EA9A07703B3104 | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\launcher\Adobe AIR\Versions\1.0\Resources\NPSWF32.dll | executable | |
MD5:3938A41F662899C7DED7263C7D4CDEF7 | SHA256:AE786B1072ADFCD25C013B2F79D28163BFEA74D7D5E06F6C227ED73D7A32FE47 | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\launcher\Adobe AIR\Versions\1.0\Adobe AIR.dll | executable | |
MD5:9656DB174178623376CD257B9B5F0A04 | SHA256:3B96DF478E8C2B4C0C8E4CAF29212E9C1E92C4B76763ECBFFA92591B95322A11 | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\launcher\Adobe AIR\Versions\1.0\Resources\Adobe AIR.vch | cat | |
MD5:702DBEC7B3EAE73D19261376ABAD255D | SHA256:400ADE762A76F06472DF8CFFBF63C80CD6E65801B319C0DC916C623213C82581 | |||
| 2312 | ~patchfile.tmp.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.23\launcher\Adobe AIR\Versions\1.0\Resources\WebKit.dll | executable | |
MD5:92B06D7ED7A1C3A47AE7378CD727D1AE | SHA256:6277B7970E81C0B3C635D1D01668396493A96C906314E4D5206A8FF4A42CCC6F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report