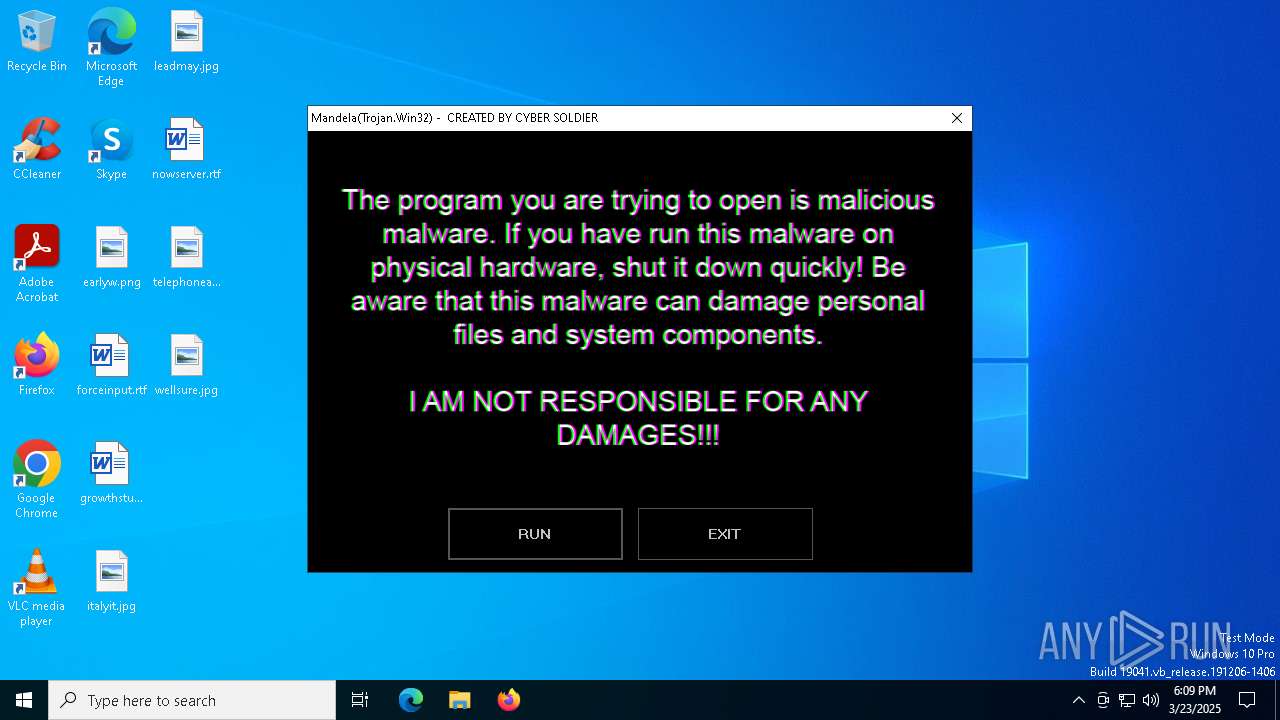
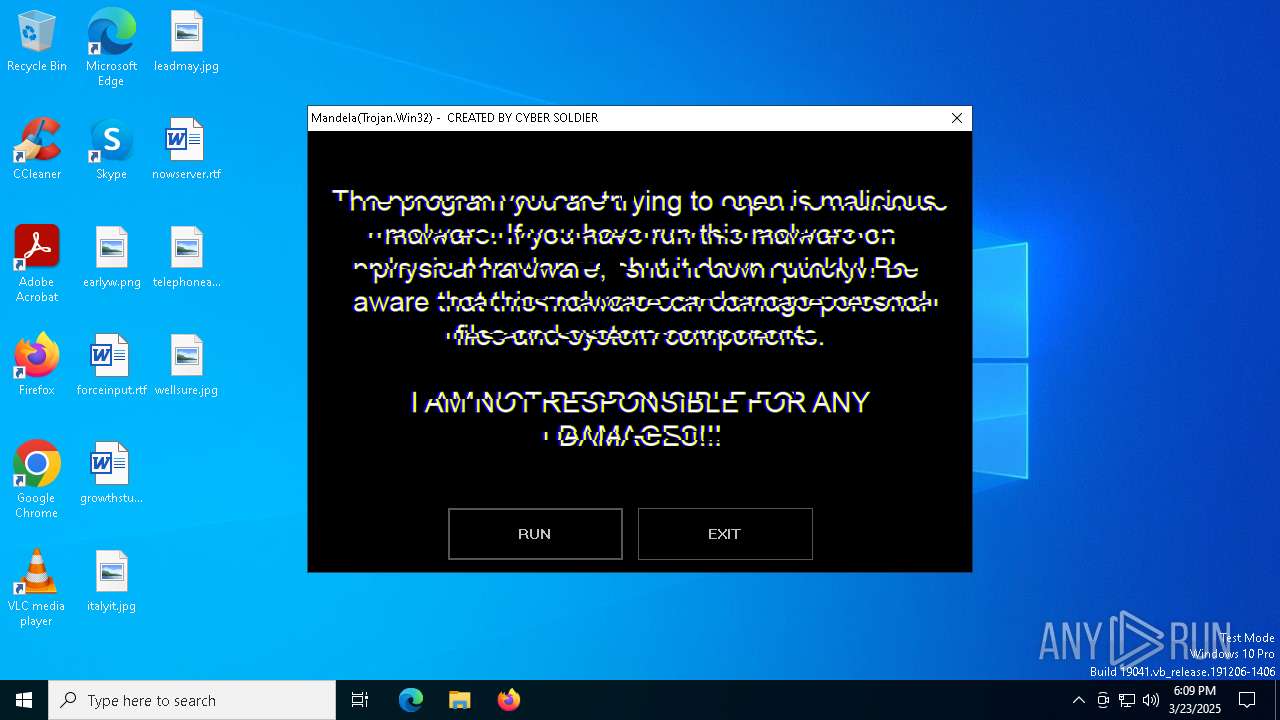
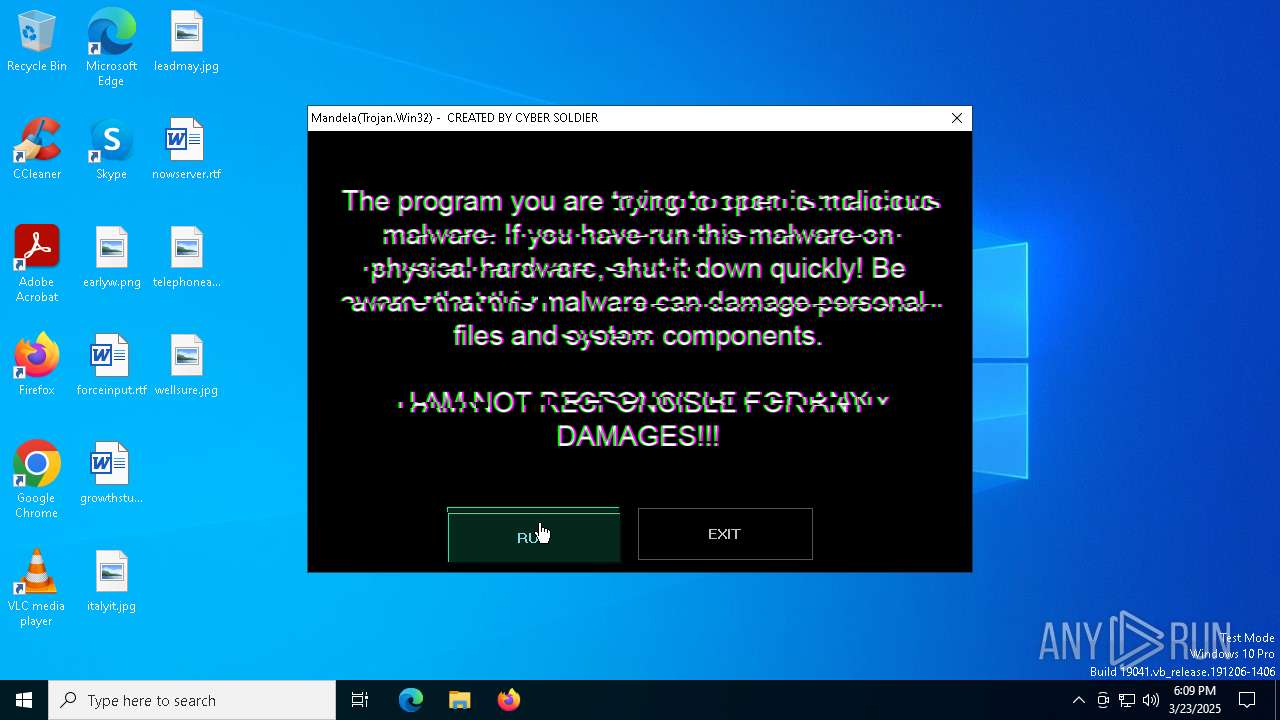
| File name: | Mandela.exe |
| Full analysis: | https://app.any.run/tasks/a0989046-bdb0-424d-bc53-068277ff8ea3 |
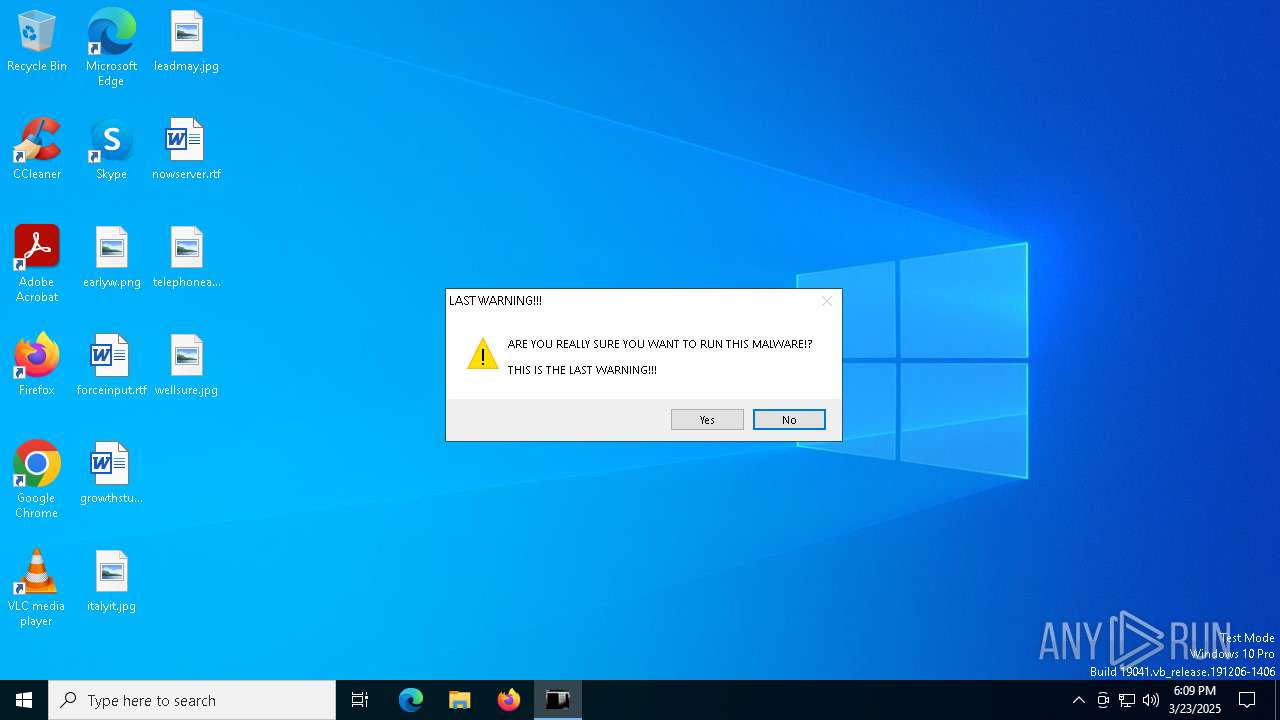
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2025, 18:09:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 68558A4A7DF242046A8A7345501ADCF7 |
| SHA1: | EAC84B6BC1BE332AF4BAFC1BDAC30B40041A1295 |
| SHA256: | C6818DA28A36A7ED628E5A86EDE3A642B609B34B2F61AE4DBA9A4814D6822D2F |
| SSDEEP: | 393216:3S2Jj2w9YgIrP/gHase3j3LINmWuwd6CZ/OK4jXo/jH599sl:Cm3YgIrXg6sELLIQWXsCZGKgY/jxa |
MALICIOUS
Changes the login/logoff helper path in the registry
- Mandela.exe (PID: 4180)
UAC/LUA settings modification
- Mandela.exe (PID: 4180)
Disables Windows Defender
- Mandela.exe (PID: 4180)
SUSPICIOUS
Executable content was dropped or overwritten
- Mandela.exe (PID: 4180)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 3332)
INFO
Process checks whether UAC notifications are on
- Mandela.exe (PID: 4180)
Creates files or folders in the user directory
- Mandela.exe (PID: 4180)
- BackgroundTransferHost.exe (PID: 6112)
Reads the computer name
- ShellExperienceHost.exe (PID: 3332)
Checks supported languages
- ShellExperienceHost.exe (PID: 3332)
.NET Reactor protector has been detected
- Mandela.exe (PID: 4180)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 6132)
- BackgroundTransferHost.exe (PID: 7288)
- BackgroundTransferHost.exe (PID: 6112)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 6112)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 6112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2054:04:04 15:20:39+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 15806976 |
| InitializedDataSize: | 110080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf151de |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | NOTHING IS WORTH THE RISK |
| CompanyName: | NOTHING IS WORTH THE RISK |
| FileDescription: | NOTHING IS WORTH THE RISK |
| FileVersion: | 1.0.0.0 |
| InternalName: | Mandela.exe |
| LegalCopyright: | NOTHING IS WORTH THE RISK |
| LegalTrademarks: | NOTHING IS WORTH THE RISK |
| OriginalFileName: | Mandela.exe |
| ProductName: | NOTHING IS WORTH THE RISK |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
130
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3332 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "C:\Users\admin\Downloads\Mandela.exe" | C:\Users\admin\Downloads\Mandela.exe | explorer.exe | ||||||||||||
User: admin Company: NOTHING IS WORTH THE RISK Integrity Level: HIGH Description: NOTHING IS WORTH THE RISK Version: 1.0.0.0 Modules
| |||||||||||||||
| 6112 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6132 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6300 | "C:\Users\admin\Downloads\Mandela.exe" | C:\Users\admin\Downloads\Mandela.exe | — | explorer.exe | |||||||||||
User: admin Company: NOTHING IS WORTH THE RISK Integrity Level: MEDIUM Description: NOTHING IS WORTH THE RISK Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7288 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 147
Read events
2 396
Write events
751
Delete events
0
Modification events
| (PID) Process: | (4180) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Keyboard Layout |
| Operation: | write | Name: | Scancode Map |
Value: 00000000000000004A000000000021E000006CE000006DE0000011E000006BE0000050E000004BE000004DE0000048E0000040E0000042E000003BE000003EE000003CE000003FE0000058E0000007E0000041E0000057E0000043E0000023E000003DE0000008E052001E004F00300052002E004F002000520012004C0021004B0022004900230048001700510024004C002500280026004A0032003400310029001800270019001A001000370013000C001F007D0014005300160056E02F0035E011004A002D00520015004F002C0000001CE000005DE000000E00000046E000003A00000053E000004FE000001C0000000100000047E0000052E00000380000001D0000002A0000005BE00000450000005EE0000038E000001DE00000360000005CE000005FE00000390000000F0000000000 | |||
| (PID) Process: | (4180) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe, mandela.exe | |||
| (PID) Process: | (4180) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | FilterAdministratorToken |
Value: 1 | |||
| (PID) Process: | (4180) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (4180) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3332) ShellExperienceHost.exe | Key: | \REGISTRY\A\{123c1da8-8daa-cccb-1d72-98af649897e6}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D0000006B99B3B31E9CDB01 | |||
| (PID) Process: | (3332) ShellExperienceHost.exe | Key: | \REGISTRY\A\{123c1da8-8daa-cccb-1d72-98af649897e6}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D0000003BE8B3B31E9CDB01 | |||
| (PID) Process: | (6132) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6132) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6132) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
4
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4180 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\education.mp4 | — | |
MD5:— | SHA256:— | |||
| 6112 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | — | |
MD5:— | SHA256:— | |||
| 6112 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\4e9cb248-44d6-4e2a-81aa-e62c50adc10b.down_data | — | |
MD5:— | SHA256:— | |||
| 4180 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\watching.bmp | image | |
MD5:A0446D6B6A4B68F596ACFB5F39A3056B | SHA256:858BF072C6C1202874365ABF2C3B52BD6AAB50B8AE8A71DAAF4E8EC9B79F1039 | |||
| 4180 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\nosleep2.bmp | image | |
MD5:B9805B16E8F3BC852EB4CBFF59828D1E | SHA256:32934EBCAA300EF712736003E0504B96ED07F11F64404FBD25E1D535BBDEE0E0 | |||
| 4180 | Mandela.exe | C:\Windows\mandela.exe | executable | |
MD5:68558A4A7DF242046A8A7345501ADCF7 | SHA256:C6818DA28A36A7ED628E5A86EDE3A642B609B34B2F61AE4DBA9A4814D6822D2F | |||
| 4180 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\nosleep.bmp | image | |
MD5:065C5858DA1C8B5806BCC39BE71C0B91 | SHA256:EC9DD0C0E6DFE1FA66D51BC0C64AB28ADEF7BDF33E63978BD6F8DD27FF14ABAC | |||
| 4180 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\momo.bmp | image | |
MD5:CF6D2C56E76DD4F62FDC478F1EF952D7 | SHA256:6B4C497C22754112A387E0286179E28989740DF614CEEF96F745C3333D05DB6D | |||
| 4180 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\cybersoldier.bmp | image | |
MD5:165DC85FA00CF1F84F3466E56EE72997 | SHA256:7E62A53A08595E697544E5BA93945DEFC418D06271B0E1932D1B451F92919C3D | |||
| 4180 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\smile.bmp | image | |
MD5:DB86CF66FB6F3D33EB39059C166478F1 | SHA256:5837CBA8136104B4DE1D2BD10CA5BA01092DA933AD6D09F1A2D9AC7DEC1DB4DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2284 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1616 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2284 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2284 | backgroundTaskHost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |