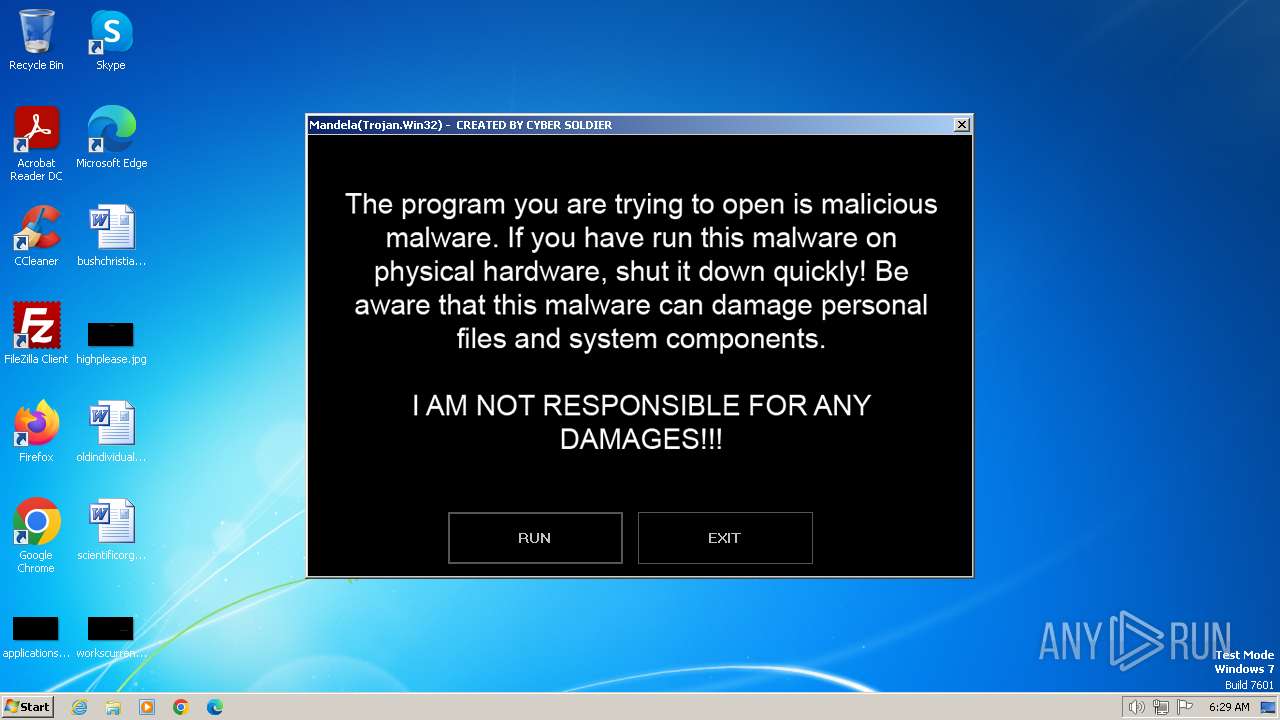
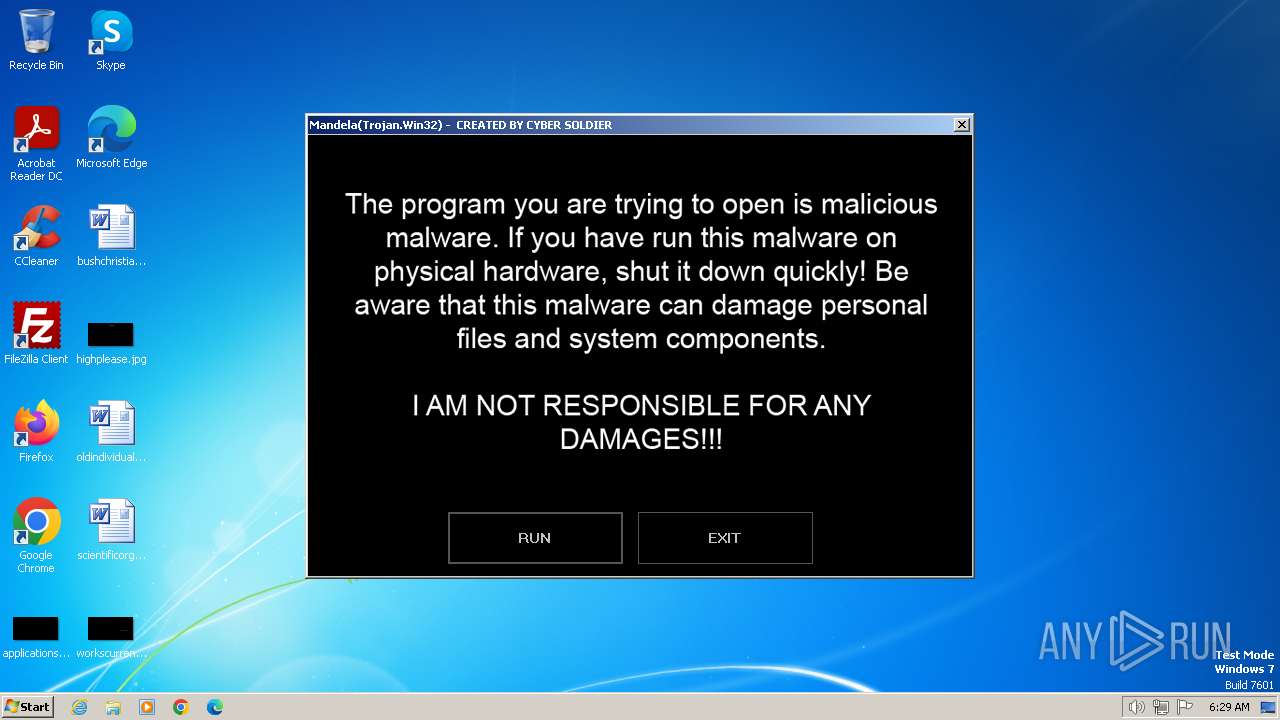
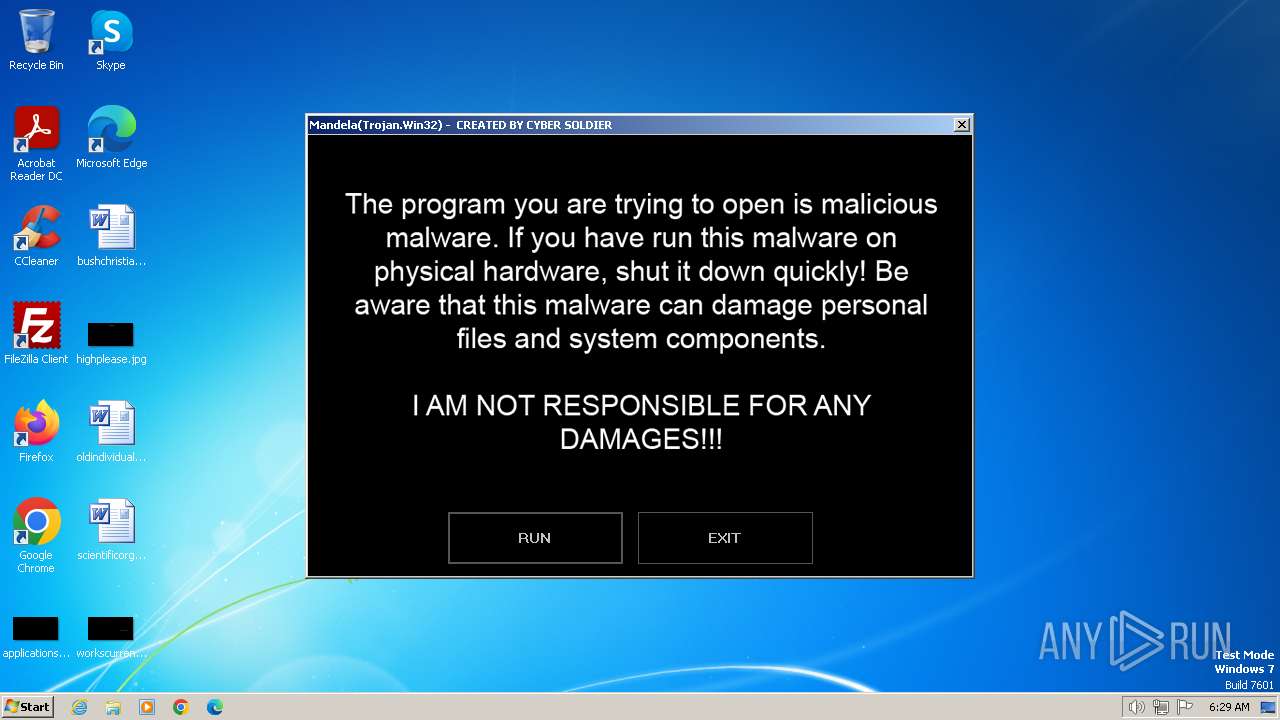
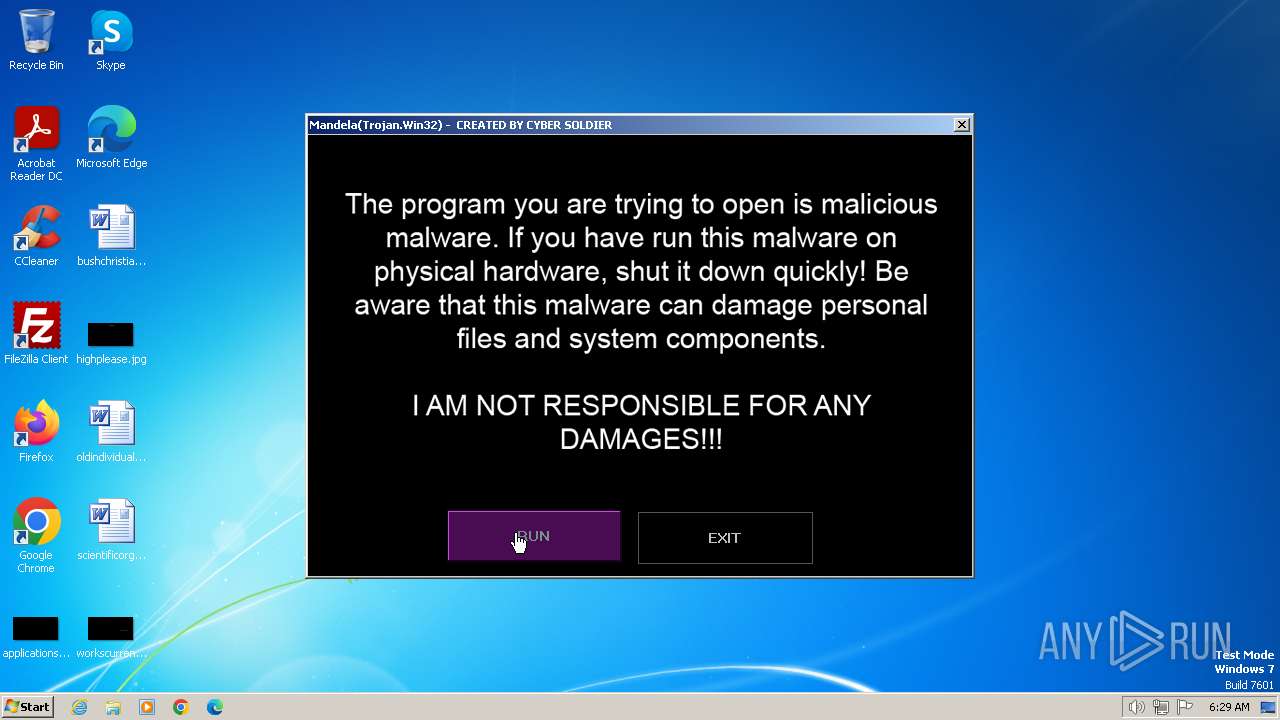
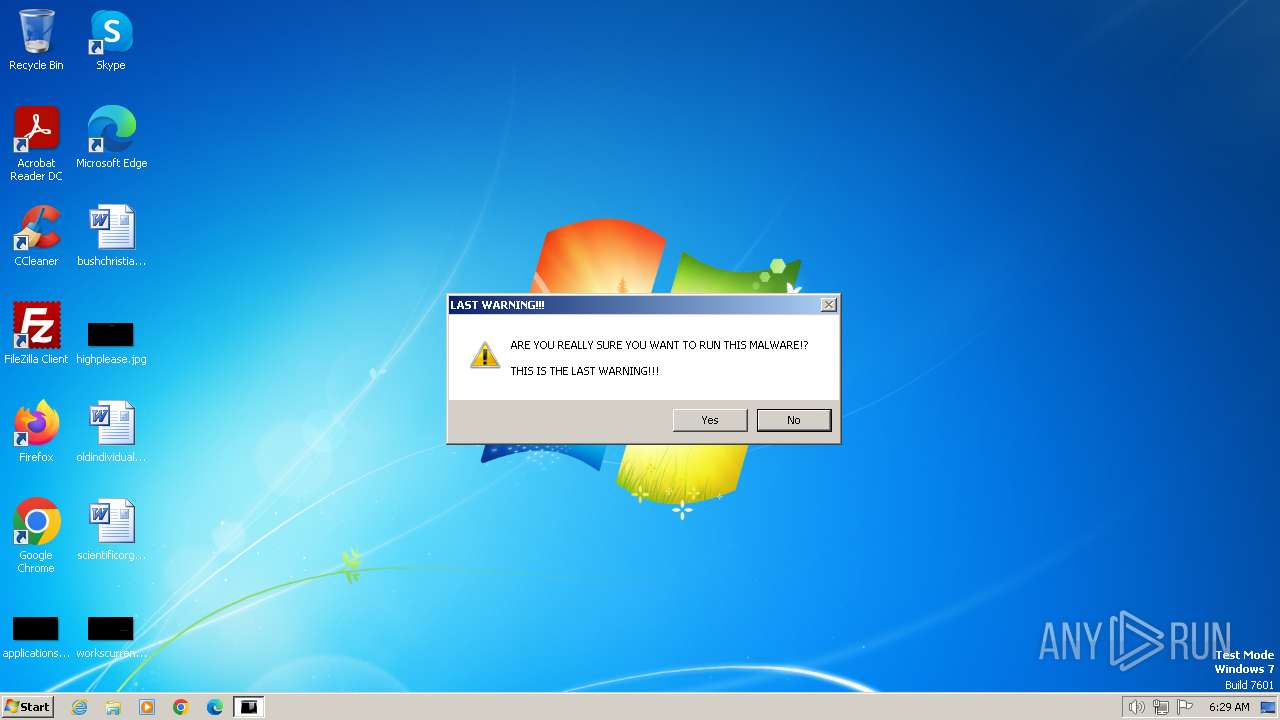
| File name: | Mandela.exe |
| Full analysis: | https://app.any.run/tasks/8d063e66-e9b8-49a5-8908-582b11406dd8 |
| Verdict: | Malicious activity |
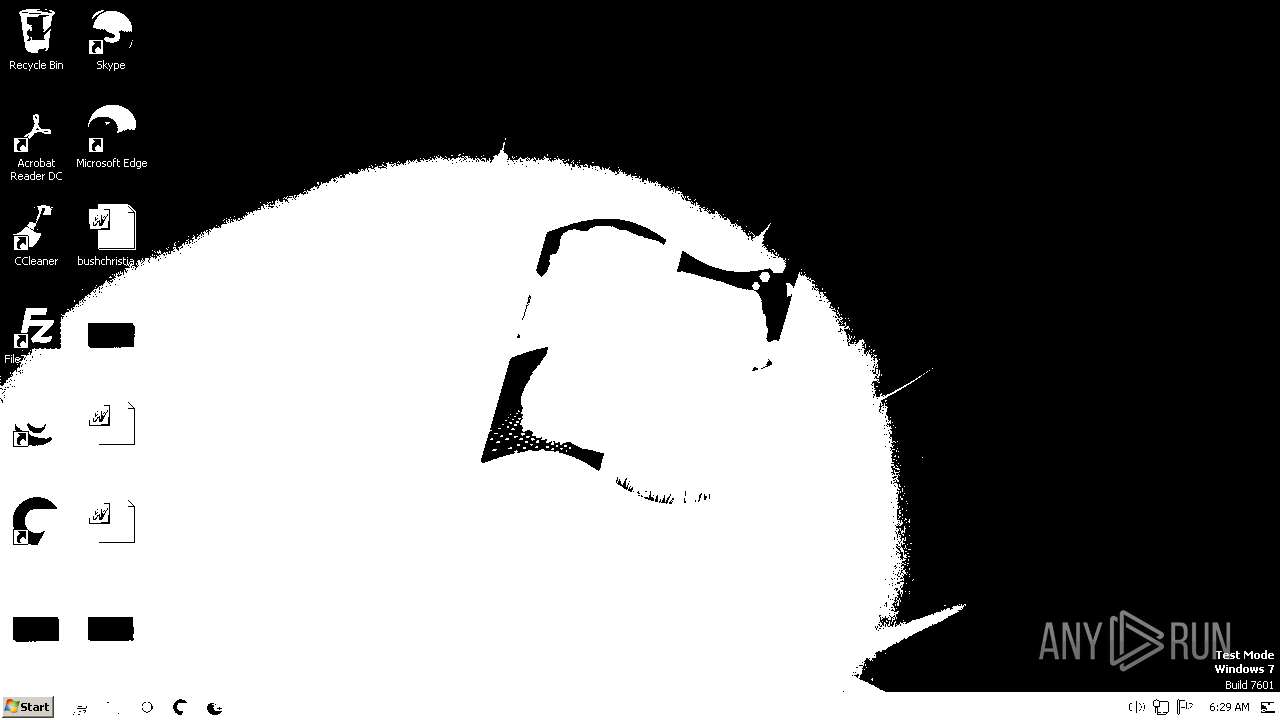
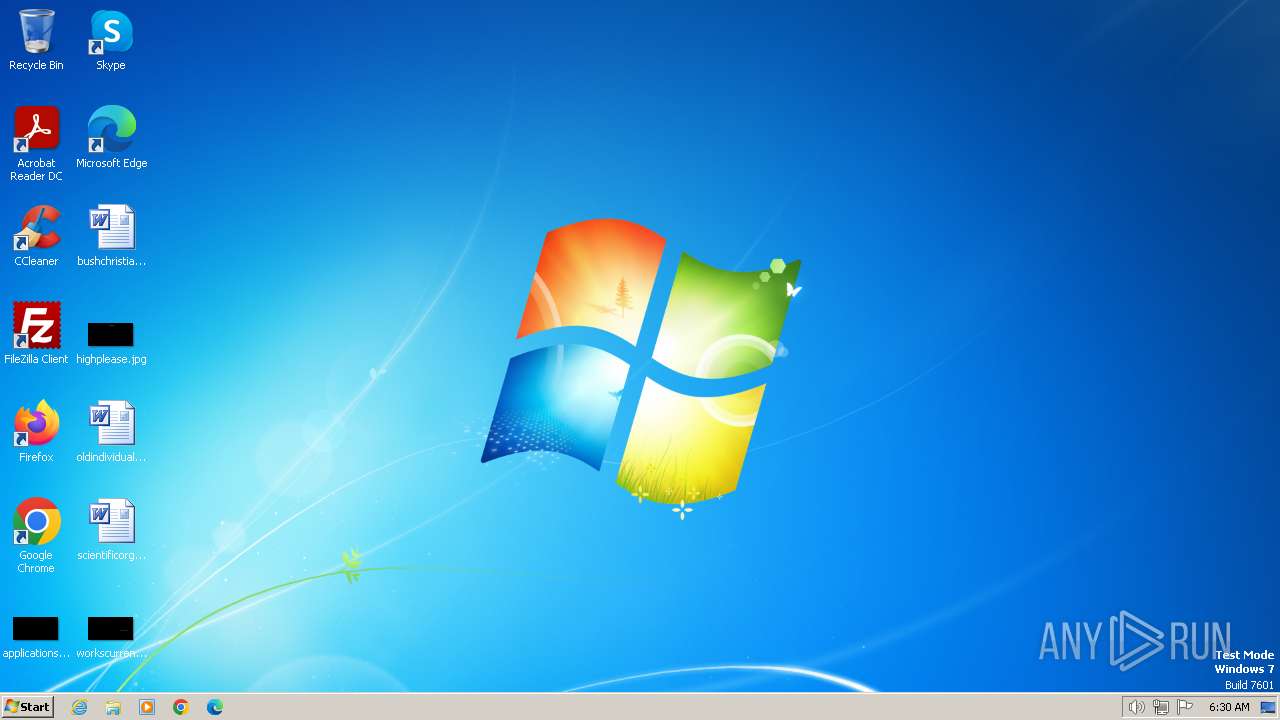
| Analysis date: | January 24, 2024, 06:29:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 68558A4A7DF242046A8A7345501ADCF7 |
| SHA1: | EAC84B6BC1BE332AF4BAFC1BDAC30B40041A1295 |
| SHA256: | C6818DA28A36A7ED628E5A86EDE3A642B609B34B2F61AE4DBA9A4814D6822D2F |
| SSDEEP: | 393216:3S2Jj2w9YgIrP/gHase3j3LINmWuwd6CZ/OK4jXo/jH599sl:Cm3YgIrXg6sELLIQWXsCZGKgY/jxa |
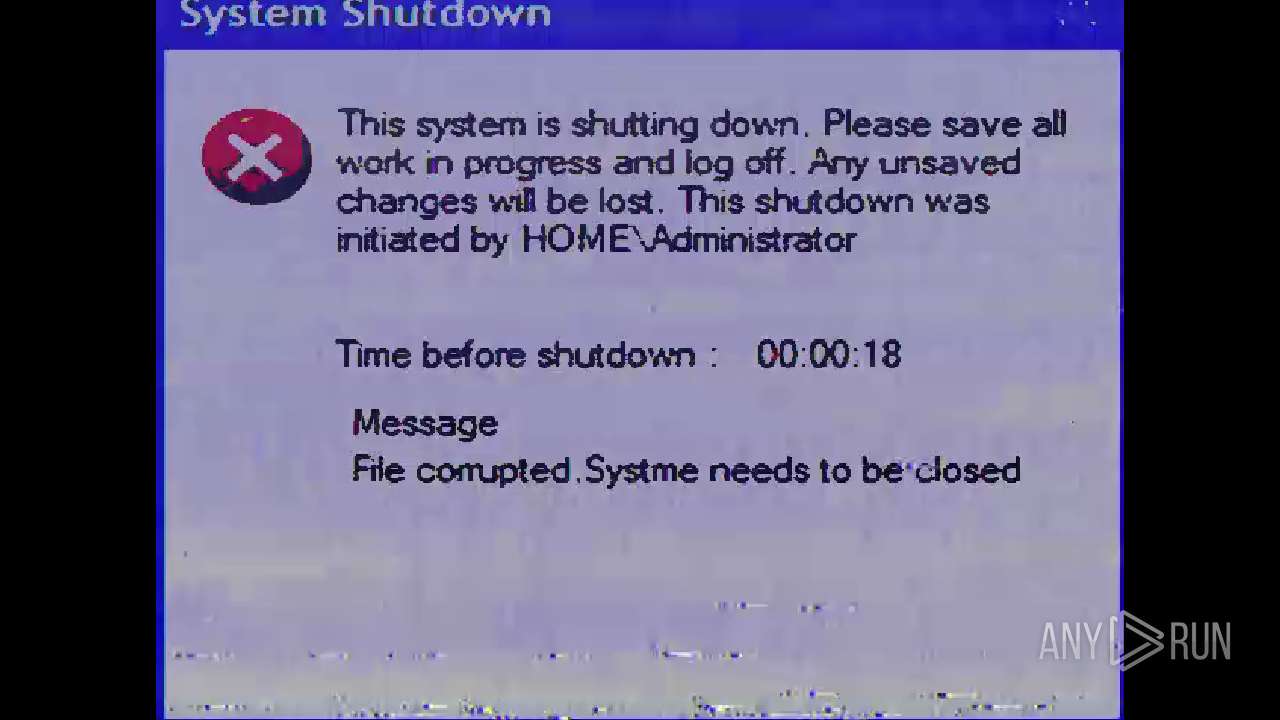
MALICIOUS
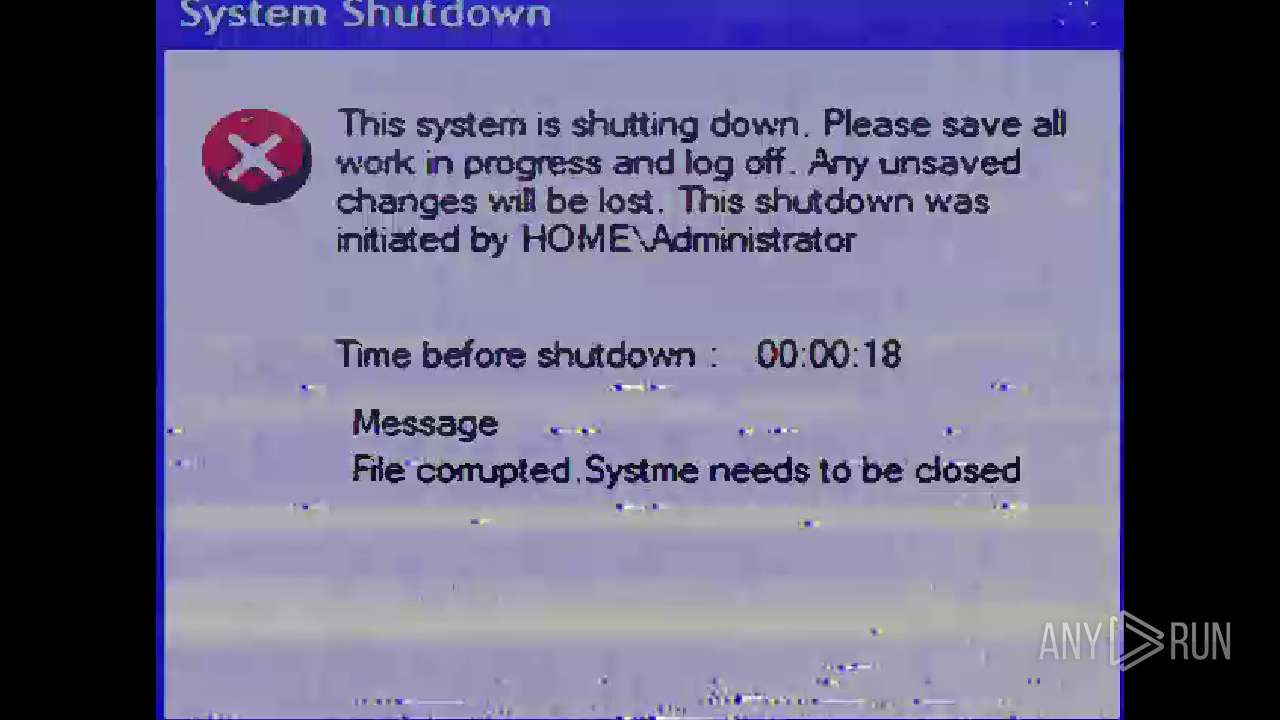
Drops the executable file immediately after the start
- Mandela.exe (PID: 2712)
Changes the login/logoff helper path in the registry
- Mandela.exe (PID: 2712)
Disables Windows Defender
- Mandela.exe (PID: 2712)
UAC/LUA settings modification
- Mandela.exe (PID: 2712)
SUSPICIOUS
Executable content was dropped or overwritten
- Mandela.exe (PID: 2712)
Starts CMD.EXE for commands execution
- Mandela.exe (PID: 2712)
Reads the Internet Settings
- Mandela.exe (PID: 2712)
- sipnotify.exe (PID: 1668)
- sipnotify.exe (PID: 1444)
The process executes via Task Scheduler
- sipnotify.exe (PID: 1668)
- ctfmon.exe (PID: 1444)
- ctfmon.exe (PID: 1504)
- sipnotify.exe (PID: 1444)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2892)
- cmd.exe (PID: 2244)
Reads settings of System Certificates
- sipnotify.exe (PID: 1668)
- sipnotify.exe (PID: 1444)
INFO
Checks supported languages
- Mandela.exe (PID: 2712)
- IMEKLMG.EXE (PID: 1900)
- IMEKLMG.EXE (PID: 1576)
- IMEKLMG.EXE (PID: 1864)
- IMEKLMG.EXE (PID: 340)
- wmpnscfg.exe (PID: 2336)
- wmpnscfg.exe (PID: 2408)
Process checks whether UAC notifications are on
- Mandela.exe (PID: 2712)
- IMEKLMG.EXE (PID: 340)
- IMEKLMG.EXE (PID: 1900)
- IMEKLMG.EXE (PID: 1864)
- IMEKLMG.EXE (PID: 1576)
Reads the computer name
- Mandela.exe (PID: 2712)
- IMEKLMG.EXE (PID: 340)
- IMEKLMG.EXE (PID: 1900)
- IMEKLMG.EXE (PID: 1864)
- IMEKLMG.EXE (PID: 1576)
- wmpnscfg.exe (PID: 2408)
- wmpnscfg.exe (PID: 2336)
Creates files or folders in the user directory
- Mandela.exe (PID: 2712)
Reads the machine GUID from the registry
- Mandela.exe (PID: 2712)
Manual execution by a user
- IMEKLMG.EXE (PID: 340)
- IMEKLMG.EXE (PID: 1900)
- IMEKLMG.EXE (PID: 1576)
- IMEKLMG.EXE (PID: 1864)
- wmpnscfg.exe (PID: 2336)
- wmpnscfg.exe (PID: 2408)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1668)
- sipnotify.exe (PID: 1444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2054:04:04 17:20:39+02:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 15806976 |
| InitializedDataSize: | 110080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf151de |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
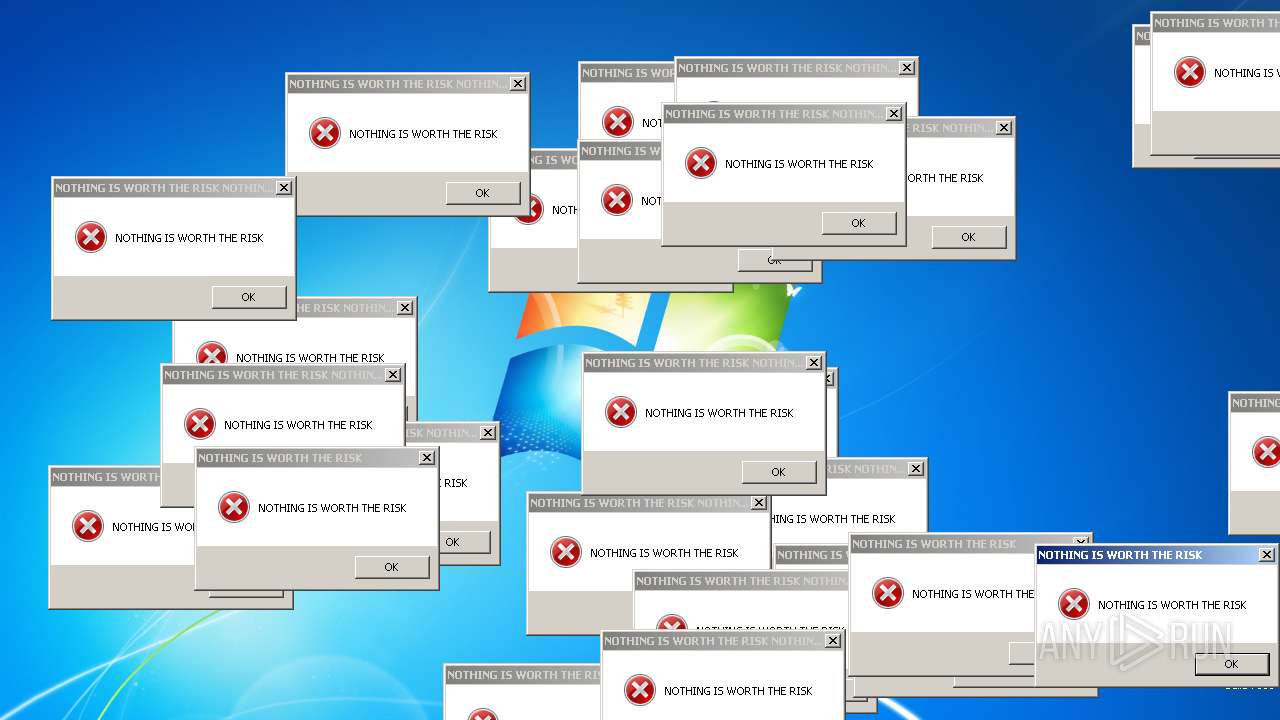
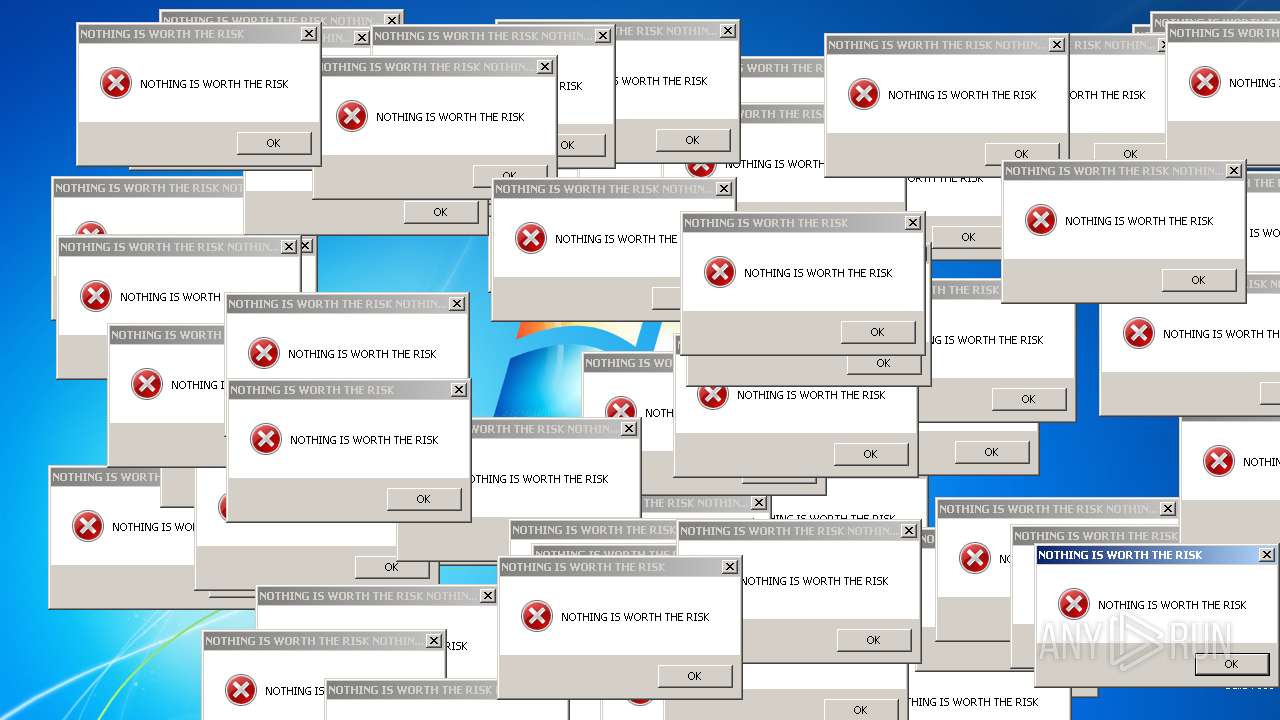
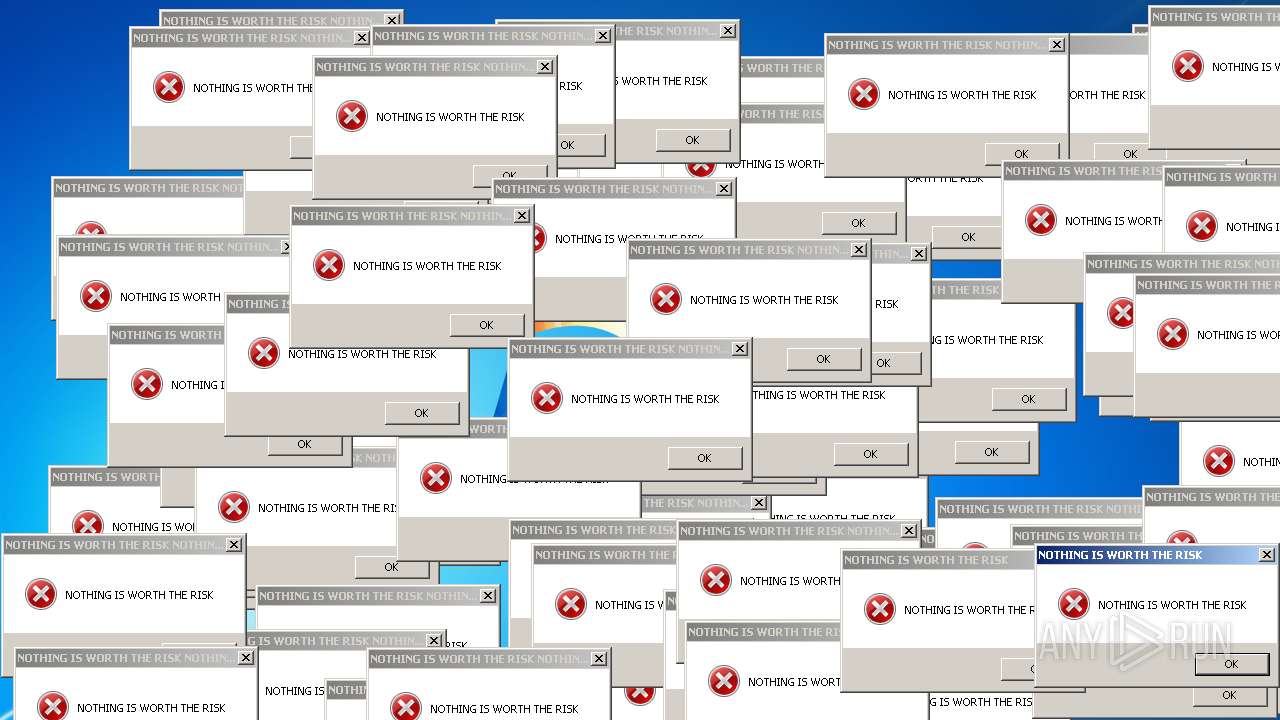
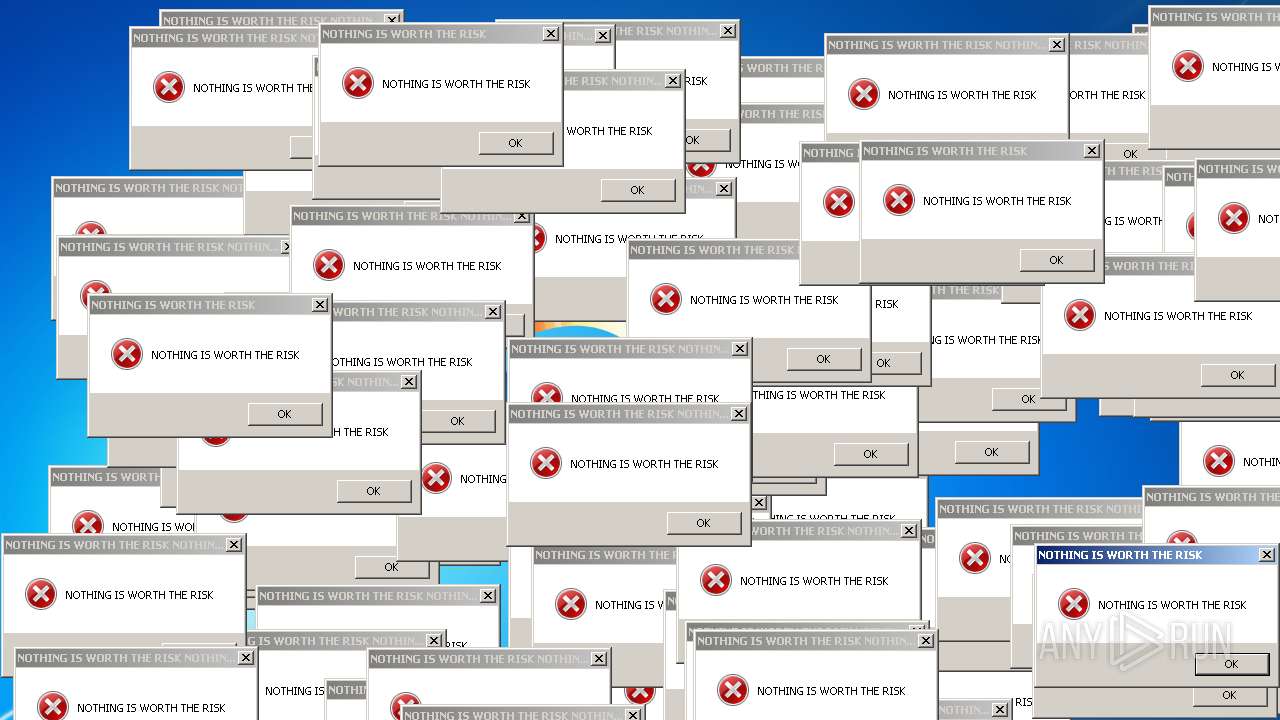
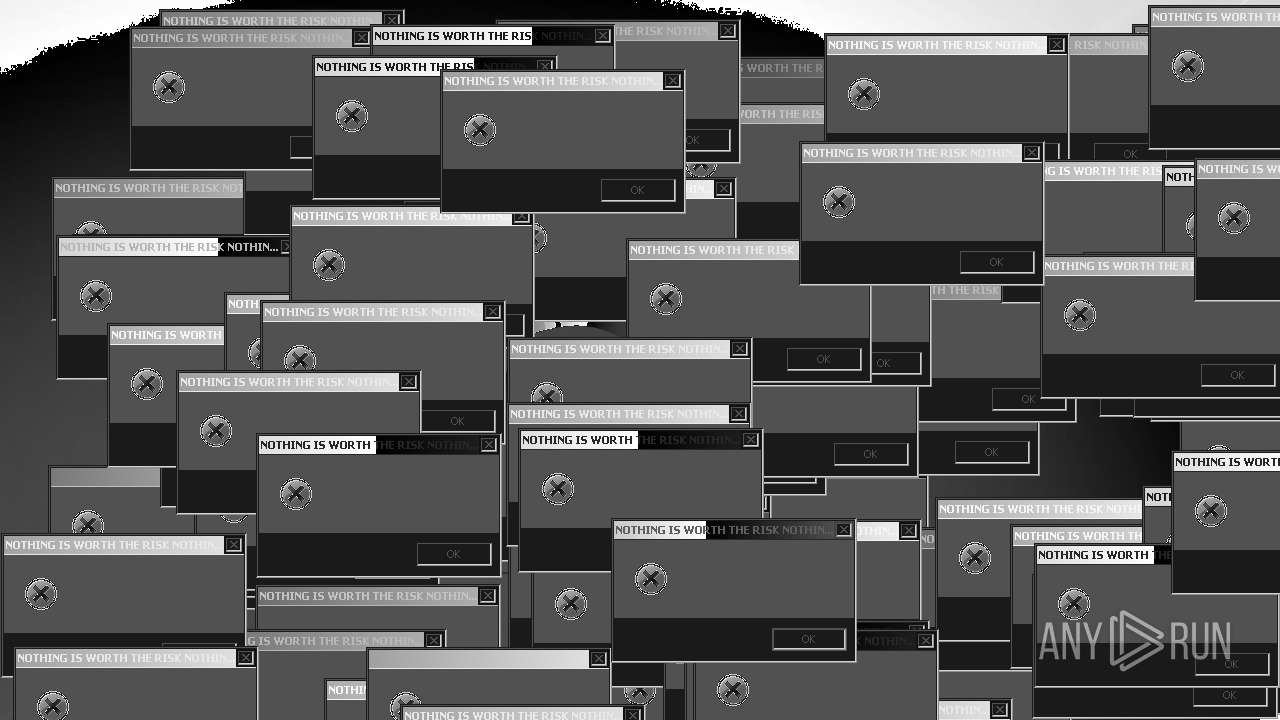
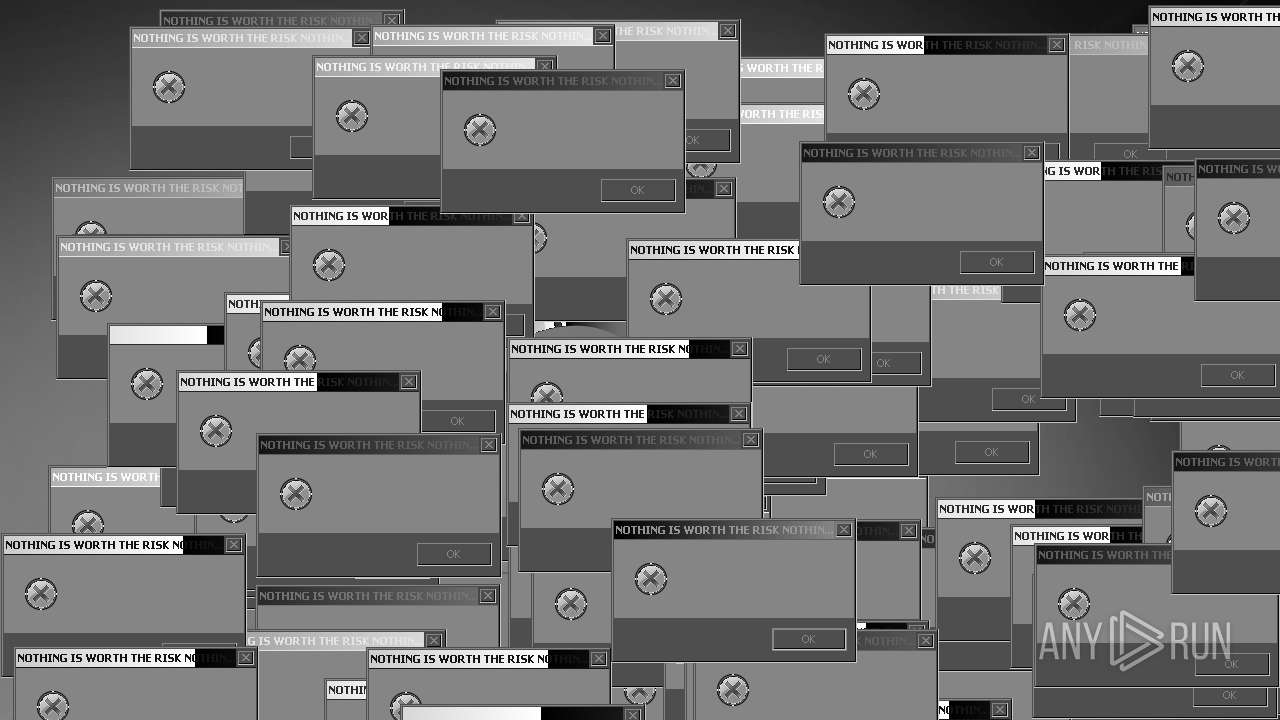
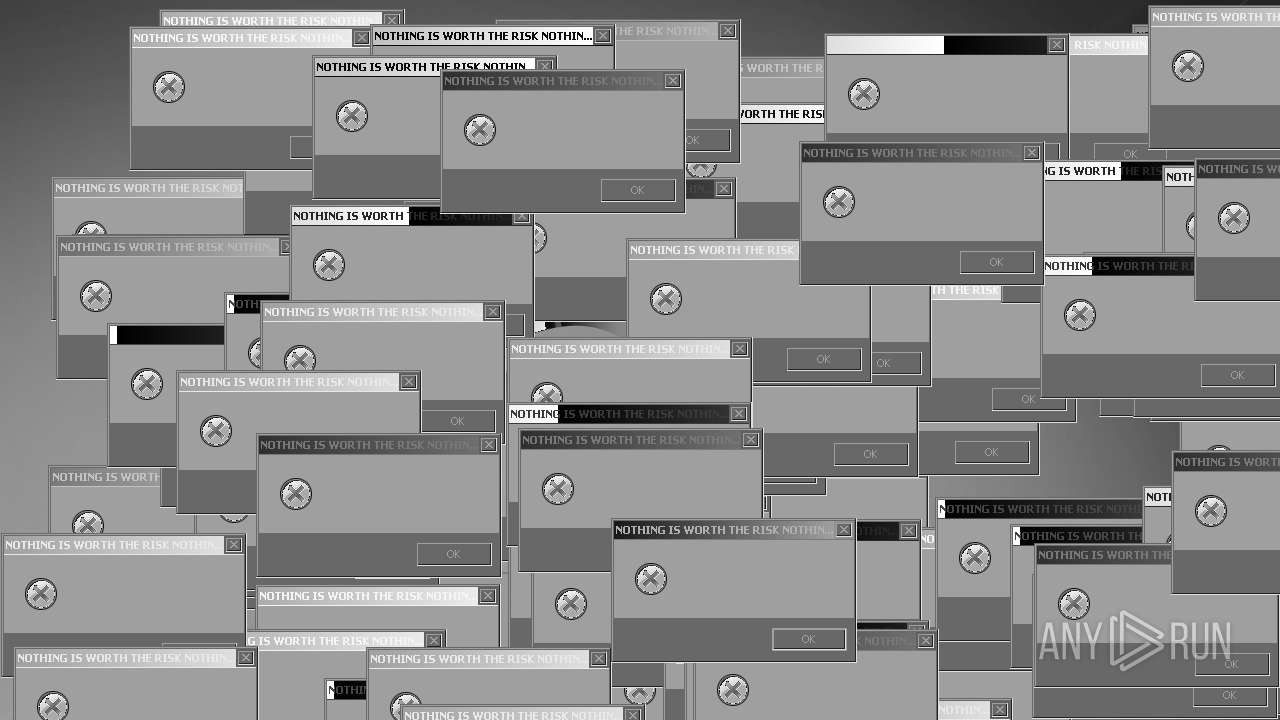
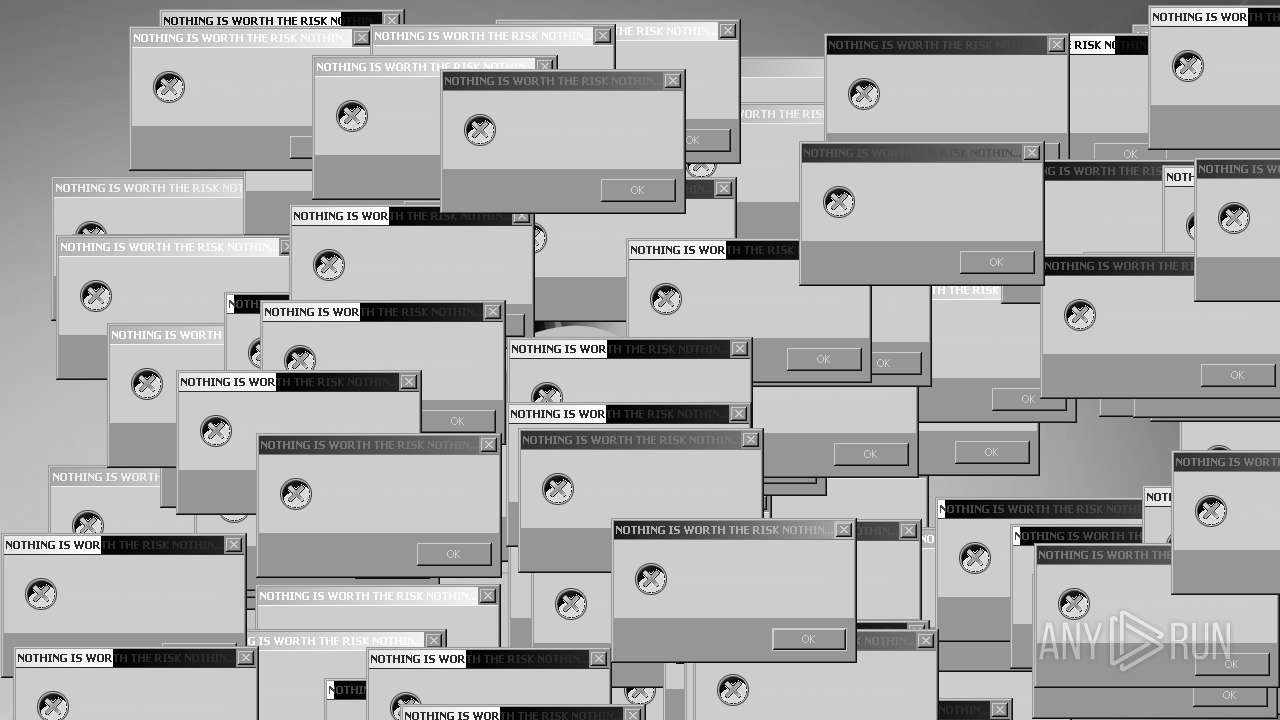
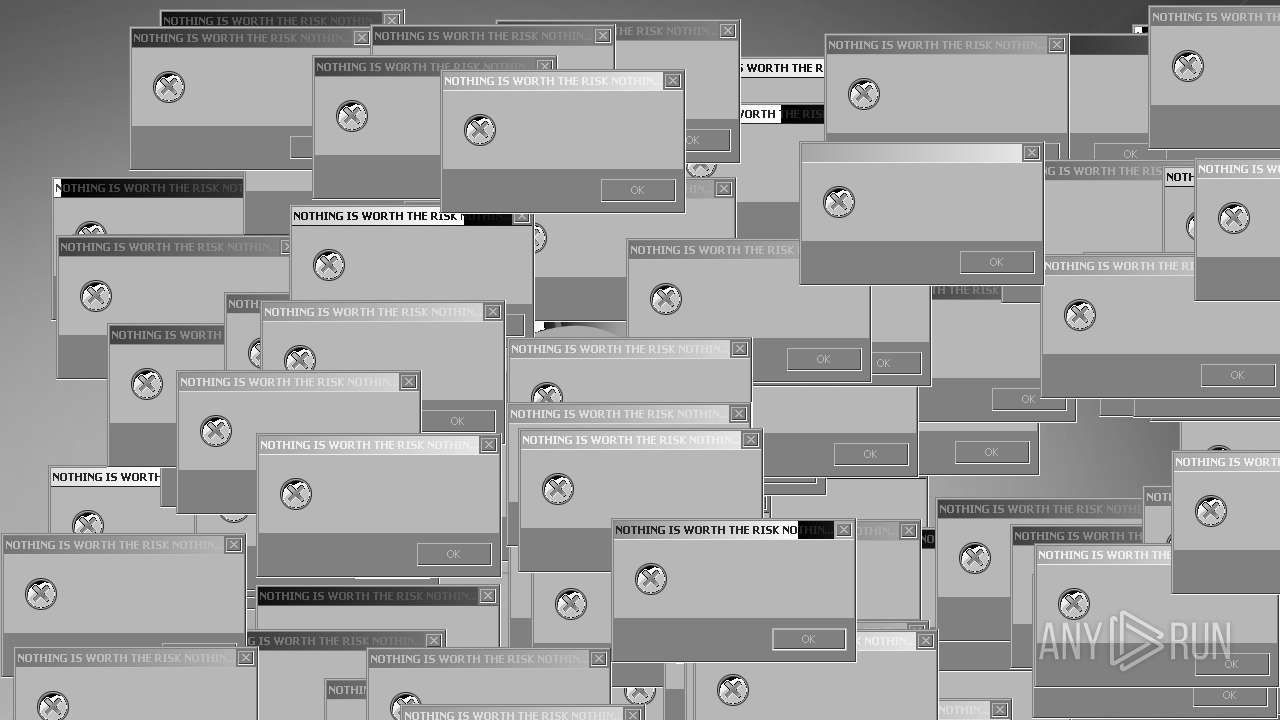
| Comments: | NOTHING IS WORTH THE RISK |
| CompanyName: | NOTHING IS WORTH THE RISK |
| FileDescription: | NOTHING IS WORTH THE RISK |
| FileVersion: | 1.0.0.0 |
| InternalName: | Mandela.exe |
| LegalCopyright: | NOTHING IS WORTH THE RISK |
| LegalTrademarks: | NOTHING IS WORTH THE RISK |
| OriginalFileName: | Mandela.exe |
| ProductName: | NOTHING IS WORTH THE RISK |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
138
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1444 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1444 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1504 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1668 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2244 | "C:\Windows\System32\cmd.exe" /k taskkill /f /im explorer.exe | C:\Windows\System32\cmd.exe | — | mandela.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2280 | taskkill /f /im explorer.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
144 835
Read events
75 972
Write events
68 863
Delete events
0
Modification events
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | FilterAdministratorToken |
Value: 0 | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 1 | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | FilterAdministratorToken |
Value: 1 | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2712) Mandela.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
1
Suspicious files
2
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2712 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\education.mp4 | — | |
MD5:— | SHA256:— | |||
| 2712 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\man.bmp | image | |
MD5:381B1BF27008F1CD9F1AD7C8F0138E31 | SHA256:DBCD6398FE3BE77EEEB580F400F9F08FF36F44BD80466446D111260195901FFB | |||
| 2712 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\momo.bmp | image | |
MD5:CF6D2C56E76DD4F62FDC478F1EF952D7 | SHA256:6B4C497C22754112A387E0286179E28989740DF614CEEF96F745C3333D05DB6D | |||
| 2712 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\intruder.bmp | image | |
MD5:87A4749241D4F5A7DBA948B689AEE8D9 | SHA256:E04C0E6680472C253DCD9D27BC07C0A6D7B915DD6F76DC1DD0BCFD05AE540AC5 | |||
| 2712 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\nosleep.bmp | image | |
MD5:065C5858DA1C8B5806BCC39BE71C0B91 | SHA256:EC9DD0C0E6DFE1FA66D51BC0C64AB28ADEF7BDF33E63978BD6F8DD27FF14ABAC | |||
| 2712 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\nosleep2.bmp | image | |
MD5:B9805B16E8F3BC852EB4CBFF59828D1E | SHA256:32934EBCAA300EF712736003E0504B96ED07F11F64404FBD25E1D535BBDEE0E0 | |||
| 2712 | Mandela.exe | C:\Windows\mandela.exe | executable | |
MD5:68558A4A7DF242046A8A7345501ADCF7 | SHA256:C6818DA28A36A7ED628E5A86EDE3A642B609B34B2F61AE4DBA9A4814D6822D2F | |||
| 2712 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\smile.bmp | image | |
MD5:DB86CF66FB6F3D33EB39059C166478F1 | SHA256:5837CBA8136104B4DE1D2BD10CA5BA01092DA933AD6D09F1A2D9AC7DEC1DB4DE | |||
| 1668 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\microsoft-logo.png | image | |
MD5:B7C73A0CFBA68CC70C35EF9C63703CE4 | SHA256:1D8B27A0266FF526CF95447F3701592A908848467D37C09A00A2516C1F29A013 | |||
| 2712 | Mandela.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\watching.bmp | image | |
MD5:A0446D6B6A4B68F596ACFB5F39A3056B | SHA256:858BF072C6C1202874365ABF2C3B52BD6AAB50B8AE8A71DAAF4E8EC9B79F1039 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
15
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1668 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133505514549530000 | unknown | — | — | unknown |
1668 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133505515786400000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1668 | sipnotify.exe | 23.197.138.118:80 | query.prod.cms.rt.microsoft.com | Akamai International B.V. | US | unknown |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |