| File name: | D0CE127F0027C56422F24AE00B604679.exe |
| Full analysis: | https://app.any.run/tasks/997b09fc-1081-4483-b710-f35e947d80c6 |
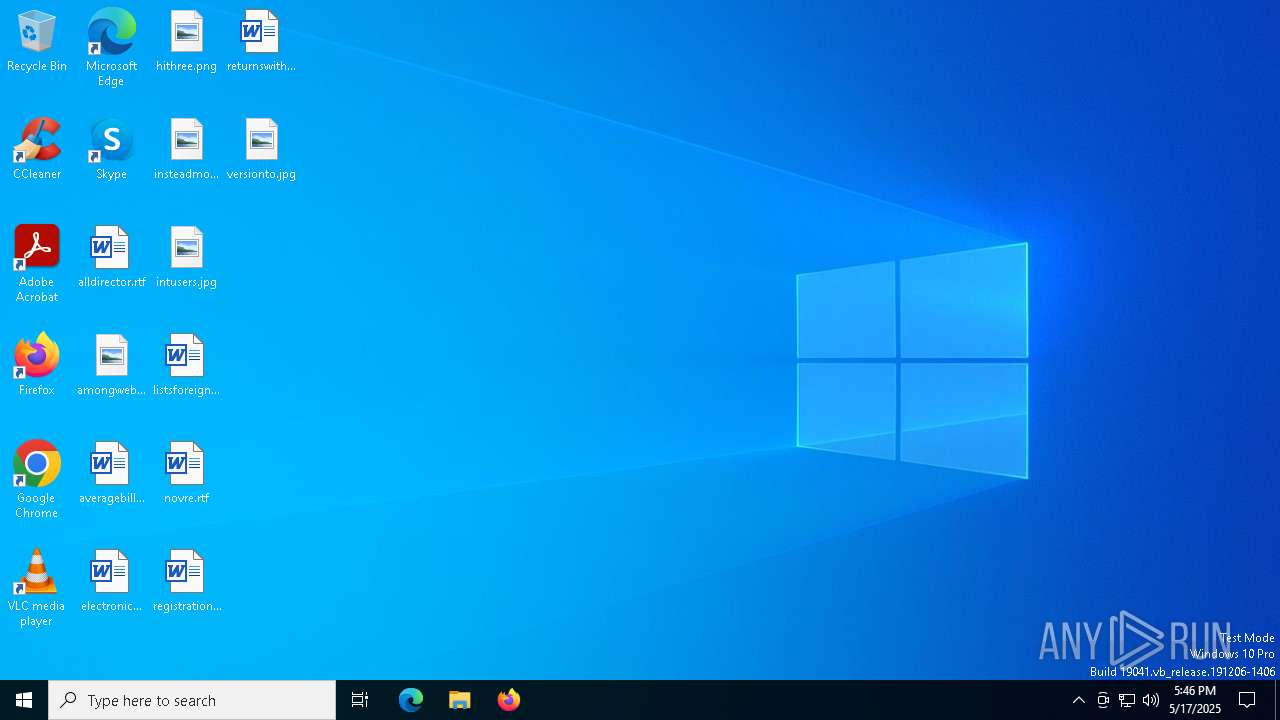
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | May 17, 2025, 17:46:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 4 sections |
| MD5: | D0CE127F0027C56422F24AE00B604679 |
| SHA1: | 16CB0B21705179DF2FDD960DFE4D5283A7C2EE45 |
| SHA256: | C67F1E457071A38BA1E32F9545A306BDA1EAAA2EA258BF742396EFEC23225B6E |
| SSDEEP: | 12288:ZsPAbeHno1MngLoOSIn5FXVF735/J7XRaf60hrarLI6KbwONe4N:ZsPAaoVVFj7XRw60hrarLIbkWdN |
MALICIOUS
DCRAT mutex has been found
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
- SystemSettings.exe (PID: 1812)
DCRAT has been detected (YARA)
- RuntimeBroker.exe (PID: 6620)
SUSPICIOUS
Executed via WMI
- schtasks.exe (PID: 2140)
- schtasks.exe (PID: 6572)
- schtasks.exe (PID: 6620)
- schtasks.exe (PID: 4428)
- schtasks.exe (PID: 1616)
- schtasks.exe (PID: 2432)
- schtasks.exe (PID: 5556)
- schtasks.exe (PID: 896)
- schtasks.exe (PID: 5176)
- schtasks.exe (PID: 516)
- schtasks.exe (PID: 4008)
- schtasks.exe (PID: 2152)
- schtasks.exe (PID: 4120)
- schtasks.exe (PID: 5332)
- schtasks.exe (PID: 2344)
- schtasks.exe (PID: 2384)
- schtasks.exe (PID: 5404)
- schtasks.exe (PID: 1660)
- schtasks.exe (PID: 6620)
- schtasks.exe (PID: 5552)
- schtasks.exe (PID: 1760)
- schtasks.exe (PID: 4428)
- schtasks.exe (PID: 6640)
- schtasks.exe (PID: 4380)
- schtasks.exe (PID: 1452)
- schtasks.exe (PID: 2152)
- schtasks.exe (PID: 780)
- schtasks.exe (PID: 1272)
- schtasks.exe (PID: 1056)
- schtasks.exe (PID: 2108)
- schtasks.exe (PID: 4208)
- schtasks.exe (PID: 2136)
- schtasks.exe (PID: 2344)
- schtasks.exe (PID: 896)
- schtasks.exe (PID: 5596)
- schtasks.exe (PID: 7000)
- schtasks.exe (PID: 6404)
- schtasks.exe (PID: 4408)
- schtasks.exe (PID: 1228)
- schtasks.exe (PID: 5552)
- schtasks.exe (PID: 516)
- schtasks.exe (PID: 4172)
The process creates files with name similar to system file names
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 5176)
- schtasks.exe (PID: 4008)
- schtasks.exe (PID: 4172)
- schtasks.exe (PID: 5332)
- schtasks.exe (PID: 2152)
- schtasks.exe (PID: 2384)
- schtasks.exe (PID: 6620)
- schtasks.exe (PID: 4120)
- backgroundTaskHost.exe (PID: 6244)
- backgroundTaskHost.exe (PID: 1244)
- schtasks.exe (PID: 5552)
- smss.exe (PID: 2236)
Executable content was dropped or overwritten
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Reads the date of Windows installation
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Starts CMD.EXE for commands execution
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Executing commands from a ".bat" file
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 5176)
Reads security settings of Internet Explorer
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
There is functionality for taking screenshot (YARA)
- RuntimeBroker.exe (PID: 6620)
INFO
Reads the computer name
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
- SystemSettings.exe (PID: 1812)
- services.exe (PID: 5936)
- backgroundTaskHost.exe (PID: 6244)
- backgroundTaskHost.exe (PID: 1244)
- Registry.exe (PID: 7148)
- Memory Compression.exe (PID: 3304)
- RuntimeBroker.exe (PID: 6620)
- smss.exe (PID: 2236)
- dllhost.exe (PID: 2340)
- TextInputHost.exe (PID: 7228)
- csrss.exe (PID: 7284)
- SystemSettings.exe (PID: 7340)
- backgroundTaskHost.exe (PID: 7172)
- ctfmon.exe (PID: 7420)
- Memory Compression.exe (PID: 7488)
Reads Environment values
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
- SystemSettings.exe (PID: 1812)
- services.exe (PID: 5936)
- backgroundTaskHost.exe (PID: 6244)
- backgroundTaskHost.exe (PID: 1244)
- Memory Compression.exe (PID: 3304)
- Registry.exe (PID: 7148)
- RuntimeBroker.exe (PID: 6620)
- smss.exe (PID: 2236)
- dllhost.exe (PID: 2340)
- TextInputHost.exe (PID: 7228)
- csrss.exe (PID: 7284)
- backgroundTaskHost.exe (PID: 7172)
- Memory Compression.exe (PID: 7488)
- ctfmon.exe (PID: 7420)
- SystemSettings.exe (PID: 7340)
The sample compiled with english language support
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Reads the machine GUID from the registry
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
- SystemSettings.exe (PID: 1812)
- services.exe (PID: 5936)
- backgroundTaskHost.exe (PID: 6244)
- backgroundTaskHost.exe (PID: 1244)
- Registry.exe (PID: 7148)
- Memory Compression.exe (PID: 3304)
- RuntimeBroker.exe (PID: 6620)
- smss.exe (PID: 2236)
- dllhost.exe (PID: 2340)
- backgroundTaskHost.exe (PID: 7172)
- TextInputHost.exe (PID: 7228)
- ctfmon.exe (PID: 7420)
- Memory Compression.exe (PID: 7488)
- csrss.exe (PID: 7284)
- SystemSettings.exe (PID: 7340)
Checks supported languages
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
- SystemSettings.exe (PID: 1812)
- services.exe (PID: 5936)
- backgroundTaskHost.exe (PID: 6244)
- backgroundTaskHost.exe (PID: 1244)
- Registry.exe (PID: 7148)
- Memory Compression.exe (PID: 3304)
- RuntimeBroker.exe (PID: 6620)
- smss.exe (PID: 2236)
- dllhost.exe (PID: 2340)
- csrss.exe (PID: 7284)
- SystemSettings.exe (PID: 7340)
- backgroundTaskHost.exe (PID: 7172)
- TextInputHost.exe (PID: 7228)
- Memory Compression.exe (PID: 7488)
- ctfmon.exe (PID: 7420)
Failed to create an executable file in Windows directory
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Creates files or folders in the user directory
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Creates files in the program directory
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Process checks computer location settings
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Create files in a temporary directory
- D0CE127F0027C56422F24AE00B604679.exe (PID: 5504)
Manual execution by a user
- services.exe (PID: 5936)
- backgroundTaskHost.exe (PID: 1244)
- Registry.exe (PID: 7148)
- backgroundTaskHost.exe (PID: 6244)
- RuntimeBroker.exe (PID: 6620)
- Memory Compression.exe (PID: 3304)
- smss.exe (PID: 2236)
- dllhost.exe (PID: 2340)
- TextInputHost.exe (PID: 7228)
- csrss.exe (PID: 7284)
- SystemSettings.exe (PID: 7340)
- backgroundTaskHost.exe (PID: 7172)
- ctfmon.exe (PID: 7420)
- Memory Compression.exe (PID: 7488)
Checks proxy server information
- SystemSettings.exe (PID: 1812)
Disables trace logs
- SystemSettings.exe (PID: 1812)
.NET Reactor protector has been detected
- RuntimeBroker.exe (PID: 6620)
Reads the software policy settings
- slui.exe (PID: 1056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(6620) RuntimeBroker.exe
C2 (1)http://f1127298.xsph.ru/0801894c
Options
MutexDCR_MUTEX-hy20F2jIr9vqqkjSGzxe
searchpath%UsersFolder% - Fast
Targetals
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (45.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (19.2) |
| .exe | | | Win64 Executable (generic) (17) |
| .scr | | | Windows screen saver (8) |
| .dll | | | Win32 Dynamic Link Library (generic) (4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:04 16:03:35+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 833024 |
| InitializedDataSize: | 13824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcd53e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.15.2.0 |
| ProductVersionNumber: | 5.15.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 5.15.2.0 |
| OriginalFileName: | libGLESv2.dll |
| ProductName: | libGLESv2 |
| ProductVersion: | 5.15.2.0 |
Total processes
192
Monitored processes
65
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | schtasks.exe /create /tn "Memory CompressionM" /sc MINUTE /mo 8 /tr "'C:\Users\Default\Cookies\Memory Compression.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | schtasks.exe /create /tn "SystemSettingsS" /sc MINUTE /mo 13 /tr "'C:\Users\Default\Saved Games\SystemSettings.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | schtasks.exe /create /tn "RegistryR" /sc MINUTE /mo 5 /tr "'C:\Users\admin\AppData\Roaming\Registry.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | schtasks.exe /create /tn "servicess" /sc MINUTE /mo 9 /tr "'C:\Users\Default\Favorites\services.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | schtasks.exe /create /tn "SystemSettings" /sc ONLOGON /tr "'C:\Users\Default\Saved Games\SystemSettings.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | schtasks.exe /create /tn "backgroundTaskHostb" /sc MINUTE /mo 13 /tr "'C:\Users\All Users\backgroundTaskHost.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | schtasks.exe /create /tn "ctfmonc" /sc MINUTE /mo 14 /tr "'C:\Users\All Users\ctfmon.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | C:\Users\Public\Pictures\backgroundTaskHost.exe | C:\Users\Public\Pictures\backgroundTaskHost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 1272 | schtasks.exe /create /tn "Registry" /sc ONLOGON /tr "'C:\Users\admin\AppData\Roaming\Registry.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 561
Read events
5 560
Write events
1
Delete events
0
Modification events
| (PID) Process: | (5504) D0CE127F0027C56422F24AE00B604679.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\aba673ef671cd544fd9879df1510cc195fe7d6b3 |
| Operation: | write | Name: | 4a283eaf3895b3bd425b6e43da905a7922815b75 |
Value: WyJDOlxcVXNlcnNcXGFkbWluXFxBcHBEYXRhXFxMb2NhbFxcVGVtcFxcRDBDRTEyN0YwMDI3QzU2NDIyRjI0QUUwMEI2MDQ2NzkuZXhlIiwiQzpcXFVzZXJzXFxEZWZhdWx0XFxGYXZvcml0ZXNcXFRleHRJbnB1dEhvc3QuZXhlIiwiQzpcXFVzZXJzXFxEZWZhdWx0XFxGYXZvcml0ZXNcXHNlcnZpY2VzLmV4ZSIsIkM6XFxVc2Vyc1xcRGVmYXVsdFxcQ29va2llc1xcTWVtb3J5IENvbXByZXNzaW9uLmV4ZSIsIkM6XFxVc2Vyc1xcUHVibGljXFxEb2N1bWVudHNcXE15IE11c2ljXFxiYWNrZ3JvdW5kVGFza0hvc3QuZXhlIiwiQzpcXFVzZXJzXFxQdWJsaWNcXFZpZGVvc1xcc21zcy5leGUiLCJDOlxcVXNlcnNcXEFsbCBVc2Vyc1xcQXBwbGljYXRpb24gRGF0YVxcY3Nyc3MuZXhlIiwiQzpcXFVzZXJzXFxQdWJsaWNcXFBpY3R1cmVzXFxiYWNrZ3JvdW5kVGFza0hvc3QuZXhlIiwiQzpcXFVzZXJzXFxEZWZhdWx0XFxWaWRlb3NcXFJ1bnRpbWVCcm9rZXIuZXhlIiwiQzpcXFVzZXJzXFxhZG1pblxcQXBwRGF0YVxcUm9hbWluZ1xcUmVnaXN0cnkuZXhlIiwiQzpcXFVzZXJzXFxBbGwgVXNlcnNcXGN0Zm1vbi5leGUiLCJDOlxcVXNlcnNcXEFsbCBVc2Vyc1xcYmFja2dyb3VuZFRhc2tIb3N0LmV4ZSIsIkM6XFxVc2Vyc1xcQWxsIFVzZXJzXFxQTFVHXFxMb2dzXFxNZW1vcnkgQ29tcHJlc3Npb24uZXhlIiwiQzpcXFVzZXJzXFxEZWZhdWx0XFxGYXZvcml0ZXNcXGRsbGhvc3QuZXhlIiwiQzpcXFVzZXJzXFxEZWZhdWx0XFxTYXZlZCBHYW1lc1xcU3lzdGVtU2V0dGluZ3MuZXhlIl0= | |||
Executable files
14
Suspicious files
0
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\ProgramData\26c12092da979c | text | |
MD5:56F49B6E4742A0A6BA11CC622F331F30 | SHA256:27FAD4B018930C2B8DD08C0D75C796BF2B227799444404B0EDDBC1E6AC781DFF | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\Users\admin\AppData\Roaming\ee2ad38f3d4382 | text | |
MD5:887ED6C7E43DBD254885BB03718418BA | SHA256:5B9DE6BD169C915E5C5B502A6B88BF75E5648D77BBC2B5729E445A665292E5A4 | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\Users\Default\Favorites\c5b4cb5e9653cc | text | |
MD5:D4E29F59C39A4A5A33D20C2C3586C66E | SHA256:EE63A6E7928B9DF02FB5EDA9771953A6A705FD01040472899E82247B134B9EE2 | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\ProgramData\ctfmon.exe | executable | |
MD5:D0CE127F0027C56422F24AE00B604679 | SHA256:C67F1E457071A38BA1E32F9545A306BDA1EAAA2EA258BF742396EFEC23225B6E | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\Users\Default\Favorites\22eafd247d37c3 | text | |
MD5:C79A1E8084F22D7157C363081EAE606E | SHA256:6D3588A9C16DD1230B7AF14D38088EFE98BADDEC2F9236A1CF0470EB6CD4E3D5 | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\Users\Default\AppData\Local\Microsoft\Windows\INetCookies\1a5d5b8dcee3d8 | text | |
MD5:36C0915D714FC1C31F48E736A9BDB804 | SHA256:3DC8CCA29D33DDEECE221D5C1AB407F34F08B025EC522E022DCA9CE8F310EFE3 | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\Users\Public\Videos\69ddcba757bf72 | text | |
MD5:932BDE4E3B3A3D420973ABAECEDF7353 | SHA256:0B94C7A0D0567262A65186F10CB9C4D65A398436CFAFF865151152E7E3480B61 | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\Users\Default\Favorites\services.exe | executable | |
MD5:D0CE127F0027C56422F24AE00B604679 | SHA256:C67F1E457071A38BA1E32F9545A306BDA1EAAA2EA258BF742396EFEC23225B6E | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\Users\Default\AppData\Local\Microsoft\Windows\INetCookies\Memory Compression.exe | executable | |
MD5:D0CE127F0027C56422F24AE00B604679 | SHA256:C67F1E457071A38BA1E32F9545A306BDA1EAAA2EA258BF742396EFEC23225B6E | |||
| 5504 | D0CE127F0027C56422F24AE00B604679.exe | C:\Users\Public\Music\backgroundTaskHost.exe | executable | |
MD5:D0CE127F0027C56422F24AE00B604679 | SHA256:C67F1E457071A38BA1E32F9545A306BDA1EAAA2EA258BF742396EFEC23225B6E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7708 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7708 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
f1127298.xsph.ru |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (xsph .ru) |
2196 | svchost.exe | Misc activity | ET INFO Observed DNS Query to xsph .ru Domain |