| URL: | https://to.getnitropack.com |
| Full analysis: | https://app.any.run/tasks/7cbb8bec-07f7-4d6e-8985-9837946bbeee |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2021, 08:26:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8040064B8D521BD43B52272E0E0AAF29 |
| SHA1: | 6146C1DA8B9818C4F6910D4D7E5F67EF65C65E4D |
| SHA256: | C6771109143D0F0DB0D1C6B9949DFC71221FB05711F88A60DE8FA346AA1741C1 |
| SSDEEP: | 3:N8CRLbvOLKn:2CR3vkKn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2360)
INFO
Checks supported languages
- iexplore.exe (PID: 1372)
- iexplore.exe (PID: 2360)
Reads the computer name
- iexplore.exe (PID: 2360)
- iexplore.exe (PID: 1372)
Application launched itself
- iexplore.exe (PID: 1372)
Checks Windows Trust Settings
- iexplore.exe (PID: 2360)
- iexplore.exe (PID: 1372)
Reads internet explorer settings
- iexplore.exe (PID: 2360)
Changes internet zones settings
- iexplore.exe (PID: 1372)
Reads settings of System Certificates
- iexplore.exe (PID: 1372)
- iexplore.exe (PID: 2360)
Creates files in the user directory
- iexplore.exe (PID: 1372)
Changes settings of System certificates
- iexplore.exe (PID: 1372)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1372)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1372 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://to.getnitropack.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1372 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
11 662
Read events
11 494
Write events
166
Delete events
2
Modification events
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30916217 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30916217 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
12
Text files
18
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94C1B0DDEF2157A5817DB222794ED709 | binary | |
MD5:45666DCC9DDF11842B5492A371BC0DDB | SHA256:A7B5E7163E04975197C8C8751794EA615EAC76F6CDB65644C3E648F9C41DEA73 | |||
| 1372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:41B85F0ADFA6468BE25FB8DA8D7B90C4 | SHA256:FB1D497525779F9141E7E442C9A5561914A015F4D26FE5F9BD6625D21CF075F5 | |||
| 2360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94C1B0DDEF2157A5817DB222794ED709 | der | |
MD5:156055634B320EC63B7730CEF90EEE91 | SHA256:1F45AA07BCC6580BC16728A6E464D10CCC4EAABB4B032A8FC625E3C9ADB1158F | |||
| 2360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:8B70E257147F1E5D4FC944D6AD115A44 | SHA256:F4BE7CEF33E06CDBBC028AD9B99FF074377A29E947B4043C98F0E59A095D9C9C | |||
| 2360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:F278B68F03483AE74DF9A0C3EEDFD771 | SHA256:DAAE7166C9A8353FCCC546B63342B86049AC42C1CCCD0BB9FE63DDD9296A841E | |||
| 1372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:D90427449E8B0E3416F8293F08A04BDB | SHA256:C84164DCCCF212EBE1EE8A39F7BDAF3BD59F94942D670B87DEDC6B55DC5A3109 | |||
| 2360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:FBA084F5B935FE9DFD6BA8BE2F0AFFDB | SHA256:68D35B7305866AC34210FB8BF1E0F651D885AEA2AE13D10C42A1264565C3E433 | |||
| 2360 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:622A0D0E195E102F79364D0E0475C5DB | SHA256:E4AB7D6914EF121D451D992DCEA712890FAC197359D8F1FB2B2048CDBC05A858 | |||
| 1372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:5AF3CC2180A68A865E440F314F6F601E | SHA256:85C9493D3EBB57E5A7F0BF1F618DB63EA328CD545D66B27003D3CF8C505A4350 | |||
| 1372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
32
DNS requests
14
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2360 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a26ceaada84eb87f | US | compressed | 4.70 Kb | whitelisted |
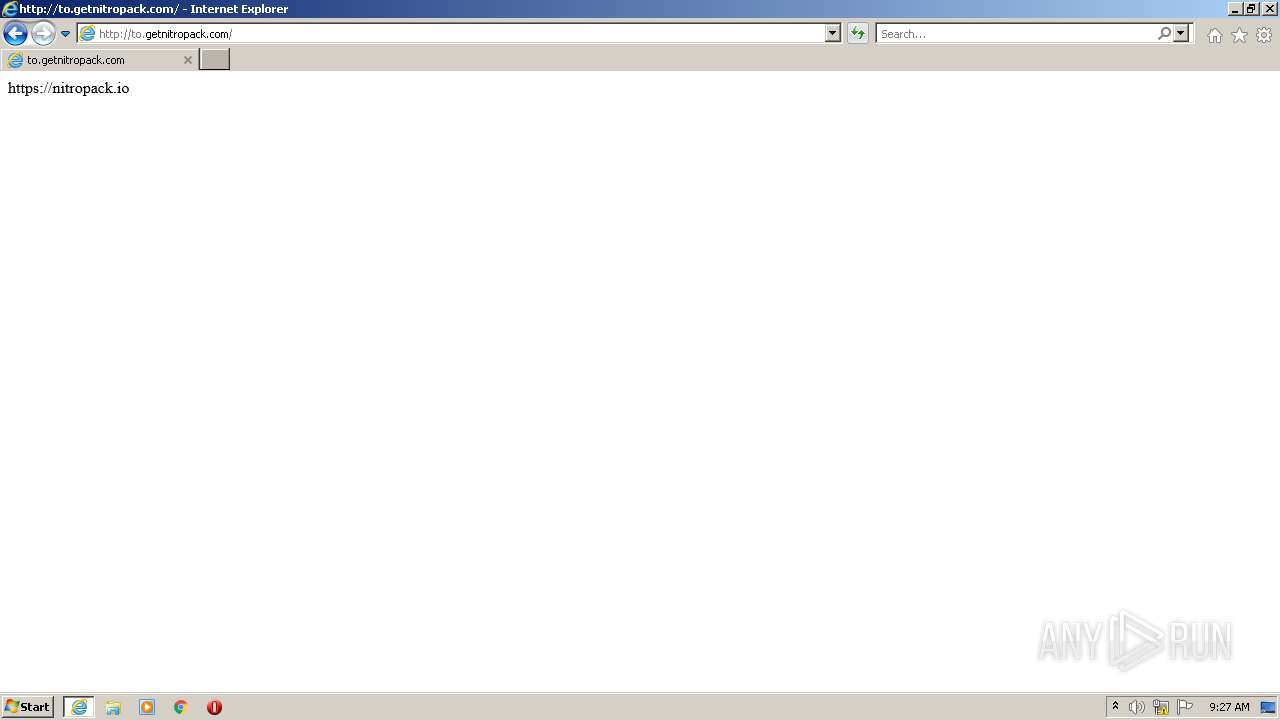
2360 | iexplore.exe | GET | 200 | 89.187.169.47:80 | http://to.getnitropack.com/ | CZ | text | 20 b | whitelisted |
2360 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2360 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEHu%2FEpRsirsd7%2BUKE%2BMwK0I%3D | US | der | 471 b | whitelisted |
2360 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1372 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1372 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1372 | iexplore.exe | GET | 404 | 89.187.169.47:80 | http://to.getnitropack.com/favicon.ico | CZ | text | 55 b | whitelisted |
1372 | iexplore.exe | GET | 304 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9584d6f882a7a42e | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2360 | iexplore.exe | 89.187.169.47:443 | to.getnitropack.com | — | CZ | malicious |
1372 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2360 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1372 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2360 | iexplore.exe | 89.187.169.47:80 | to.getnitropack.com | — | CZ | malicious |
1372 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1372 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
1372 | iexplore.exe | 89.187.169.47:80 | to.getnitropack.com | — | CZ | malicious |
1372 | iexplore.exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
1372 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
to.getnitropack.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2360 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |