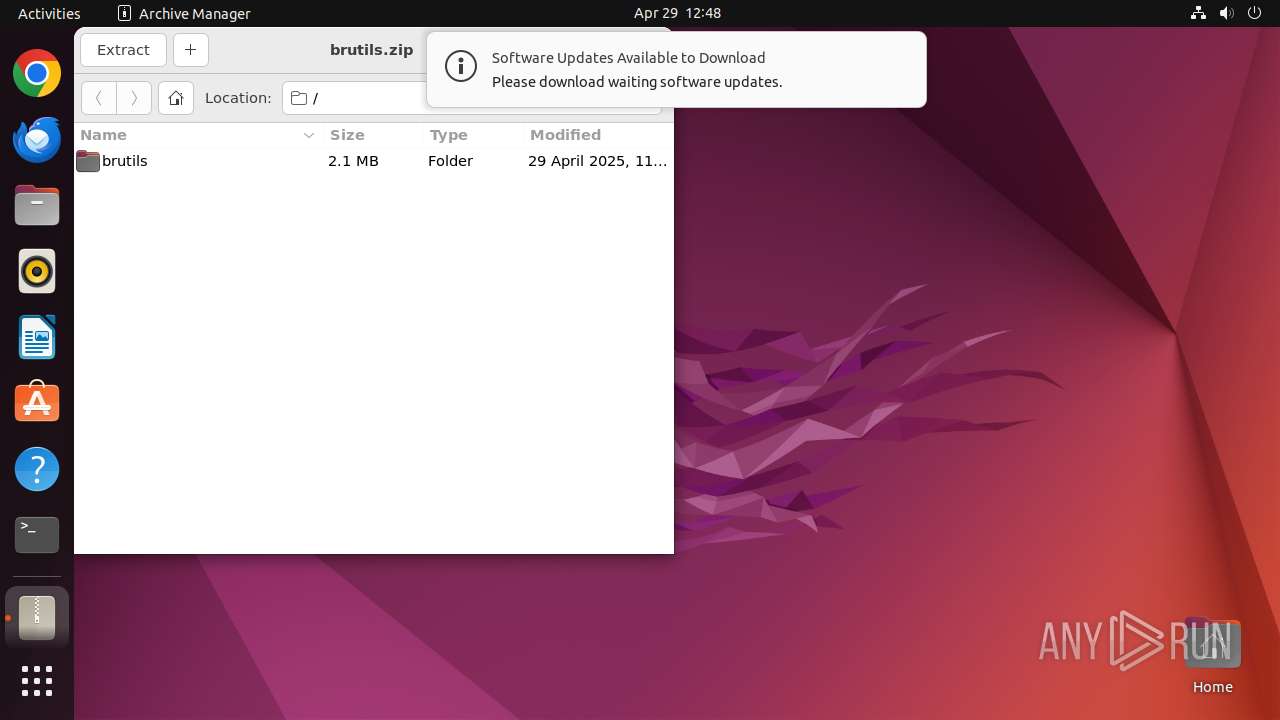
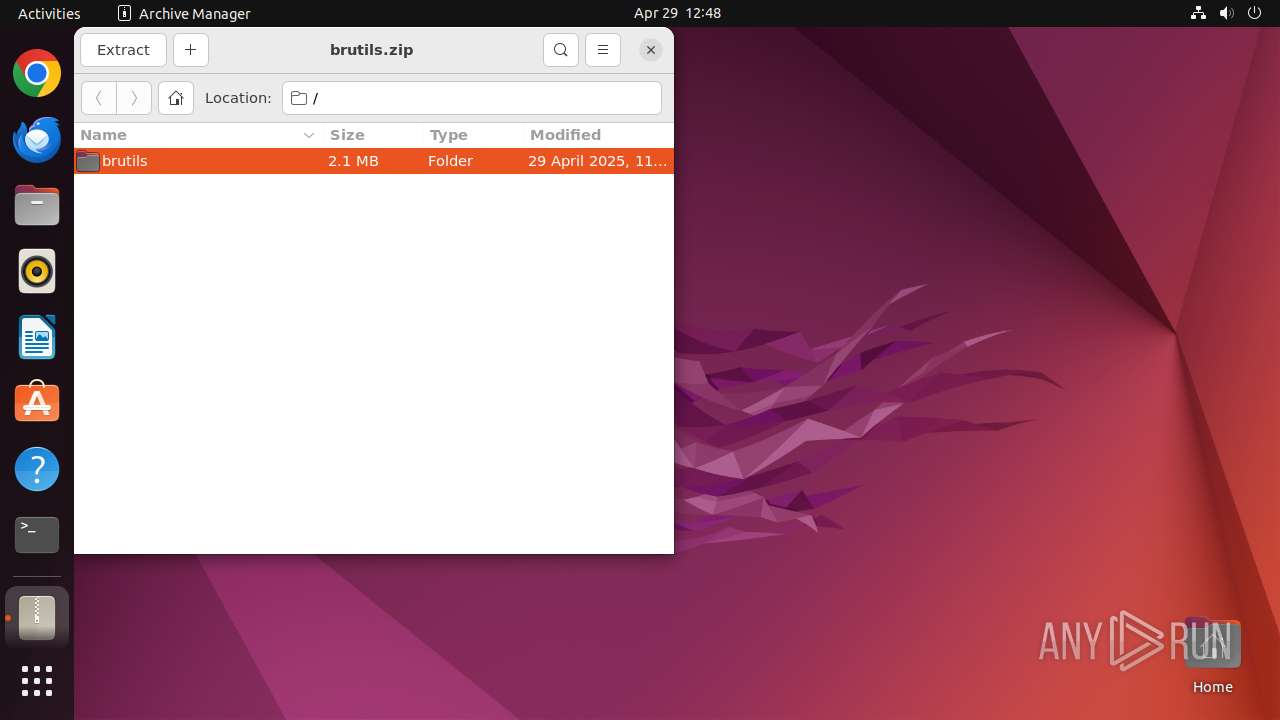
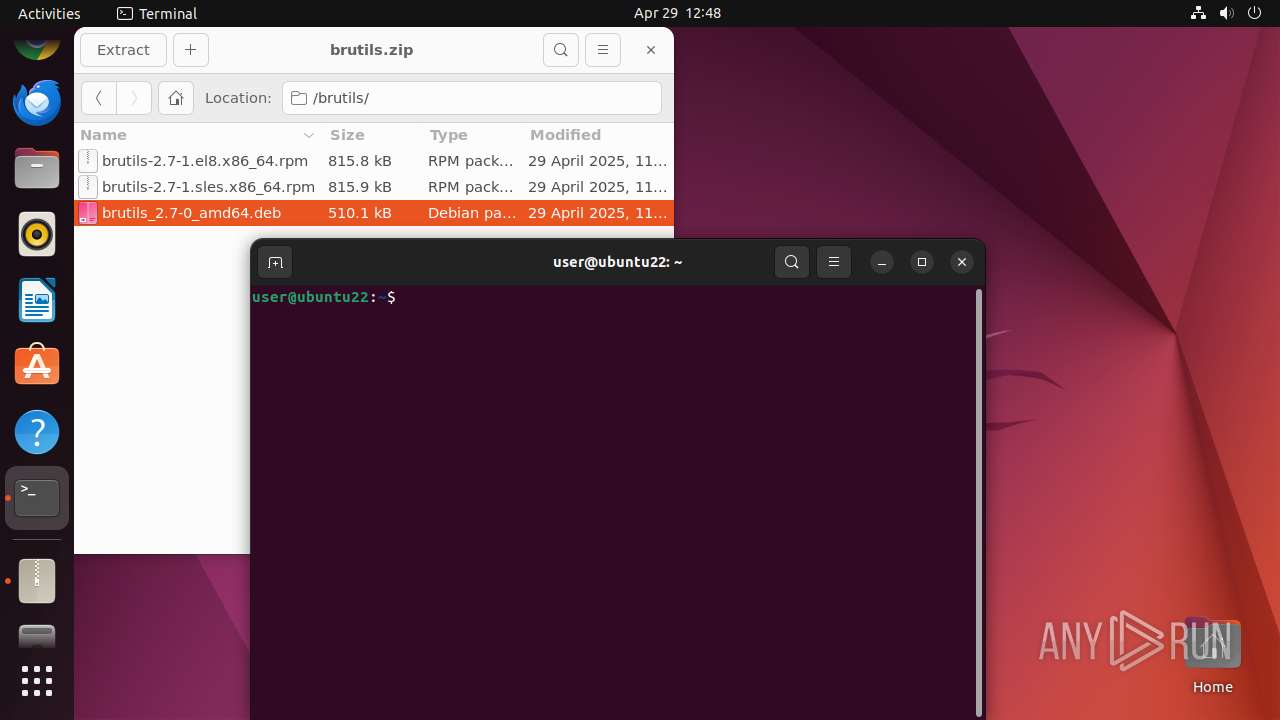
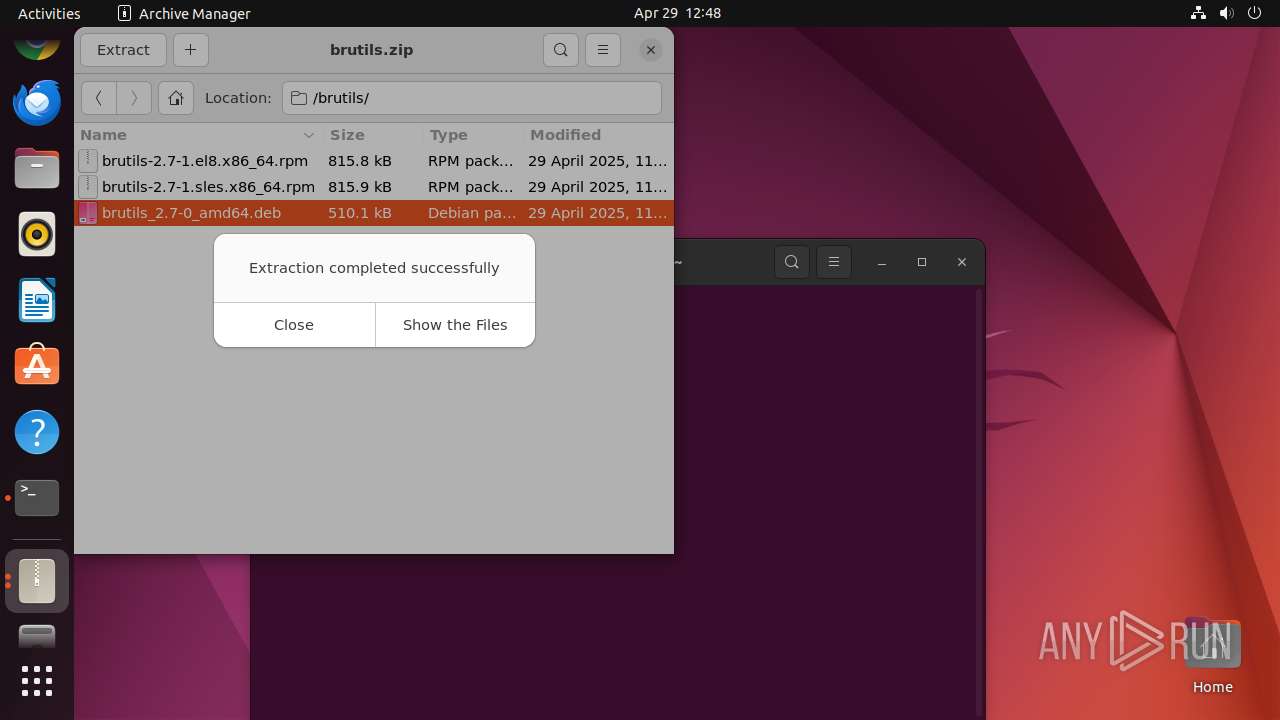
| File name: | brutils.zip |
| Full analysis: | https://app.any.run/tasks/22a5bd6b-0328-49ff-a53c-741601de2873 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 11:47:54 |
| OS: | Ubuntu 22.04.2 |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | FA774C452DD257B3AB75DBE9CEB1A659 |
| SHA1: | 212C9F35C2141C4D69BA0C89FAD4921497A6FC5D |
| SHA256: | C660D1208FDD5BC3CCE9C5AA868502B5E5E76DEE7688AC7D83A36E756B7C1DC6 |
| SSDEEP: | 98304:f276LhdHEs2C28e4xrkBQrLpa6k8Gah8NHgA0tCdPRArmV9mnf3jvu3VVP+DijT4:jH |
MALICIOUS
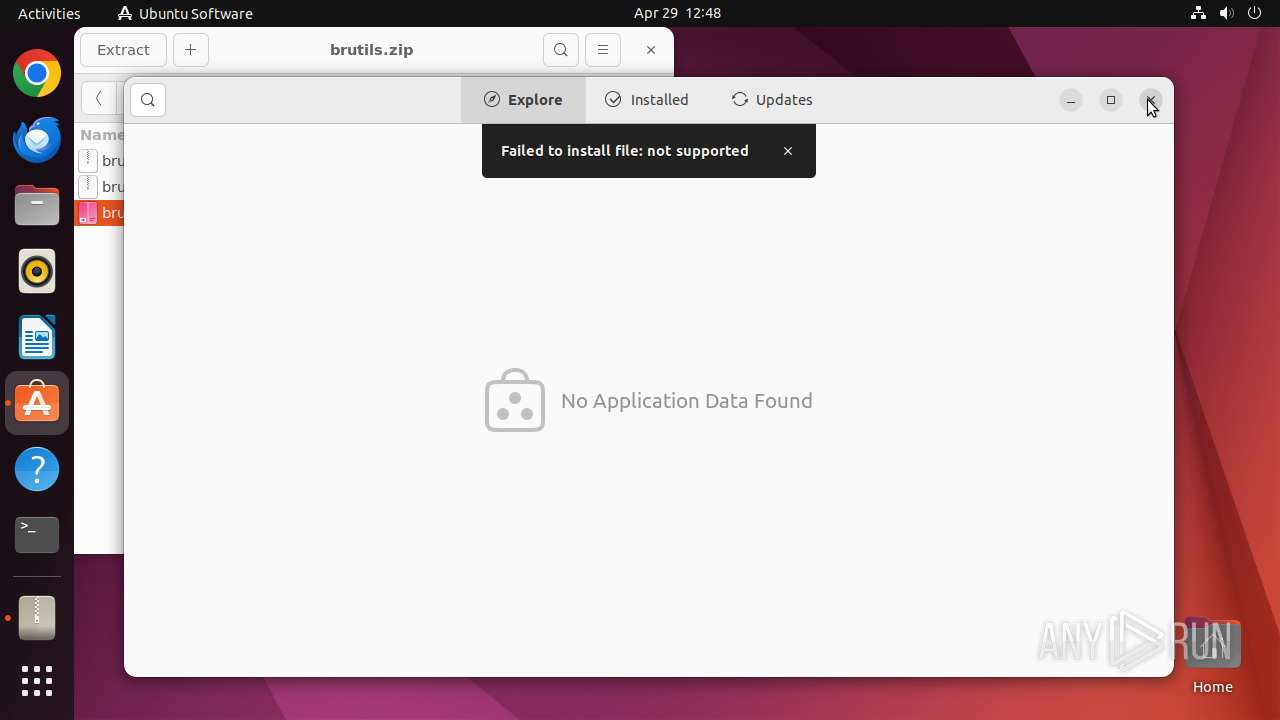
No malicious indicators.SUSPICIOUS
Reads profile file
- file-roller (PID: 39499)
Reads passwd file
- file-roller (PID: 39499)
Executes commands using command-line interpreter
- sudo (PID: 39498)
- file-roller (PID: 39526)
- gnome-terminal-server (PID: 39625)
Reads /proc/mounts (likely used to find writable filesystems)
- snap-store (PID: 39527)
Check the Environment Variables Related to System Identification (os-release)
- snapctl (PID: 39570)
- snapctl (PID: 39576)
- snap-store (PID: 39527)
Executes the "rm" command to delete files or directories
- file-roller (PID: 39499)
INFO
Checks timezone
- 7z (PID: 39515)
- file-roller (PID: 39499)
- python3.10 (PID: 39618)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:04:29 15:47:30 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | brutils/ |
Total processes
294
Monitored processes
69
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
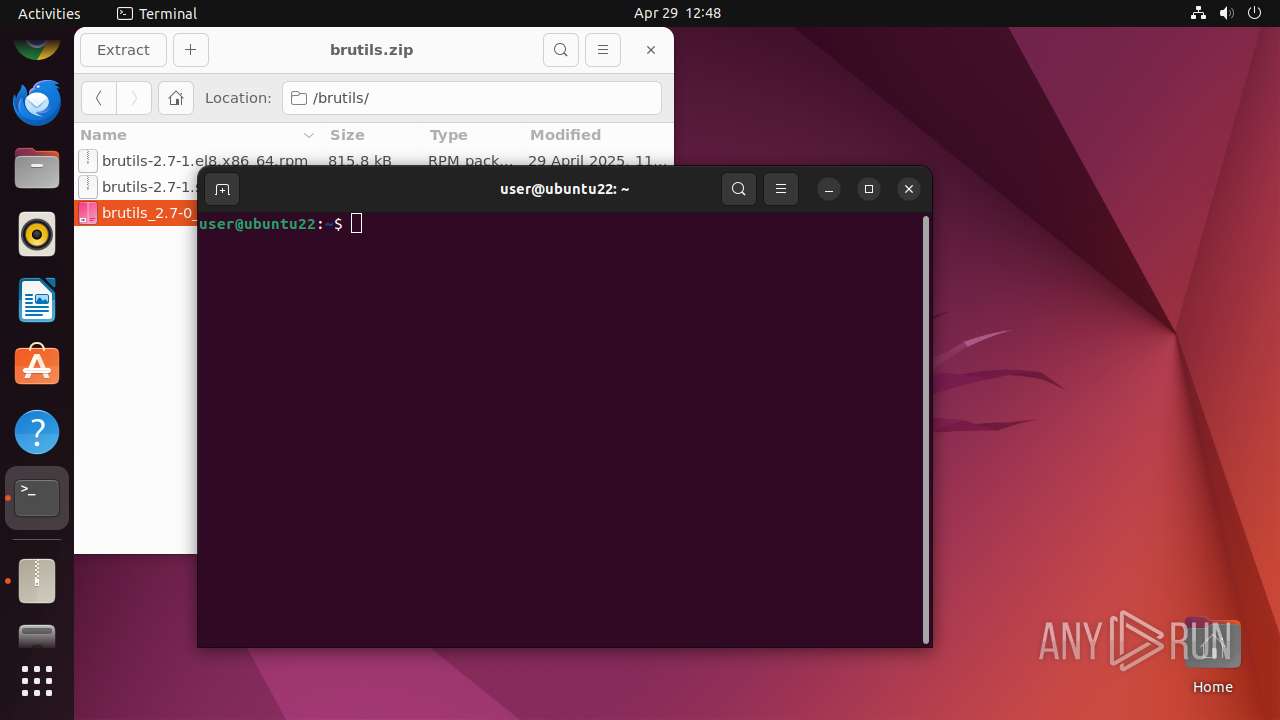
| 39497 | /bin/sh -c "DISPLAY=:0 sudo -iu user file-roller /tmp/brutils\.zip " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 39498 | sudo -iu user file-roller /tmp/brutils.zip | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 39499 | file-roller /tmp/brutils.zip | /usr/bin/file-roller | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 39500 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39510 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39515 | /usr/lib/p7zip/7z l -slt -bd -y -- /tmp/brutils.zip | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
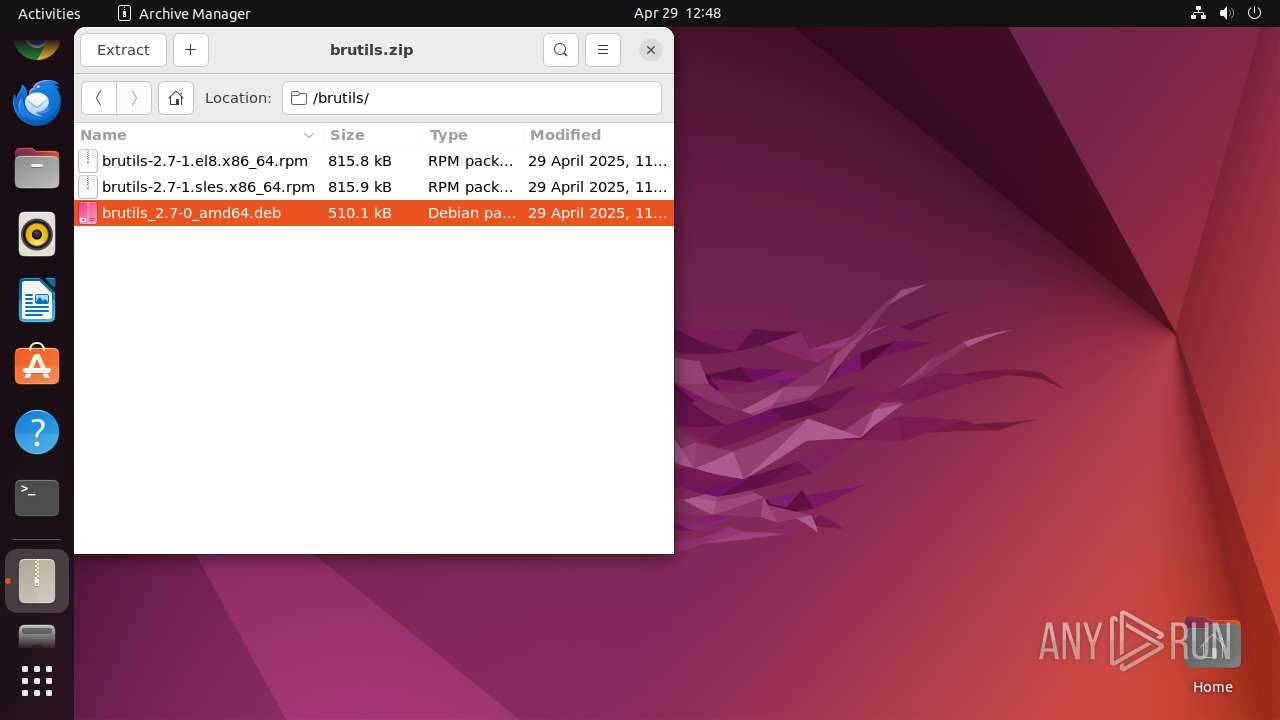
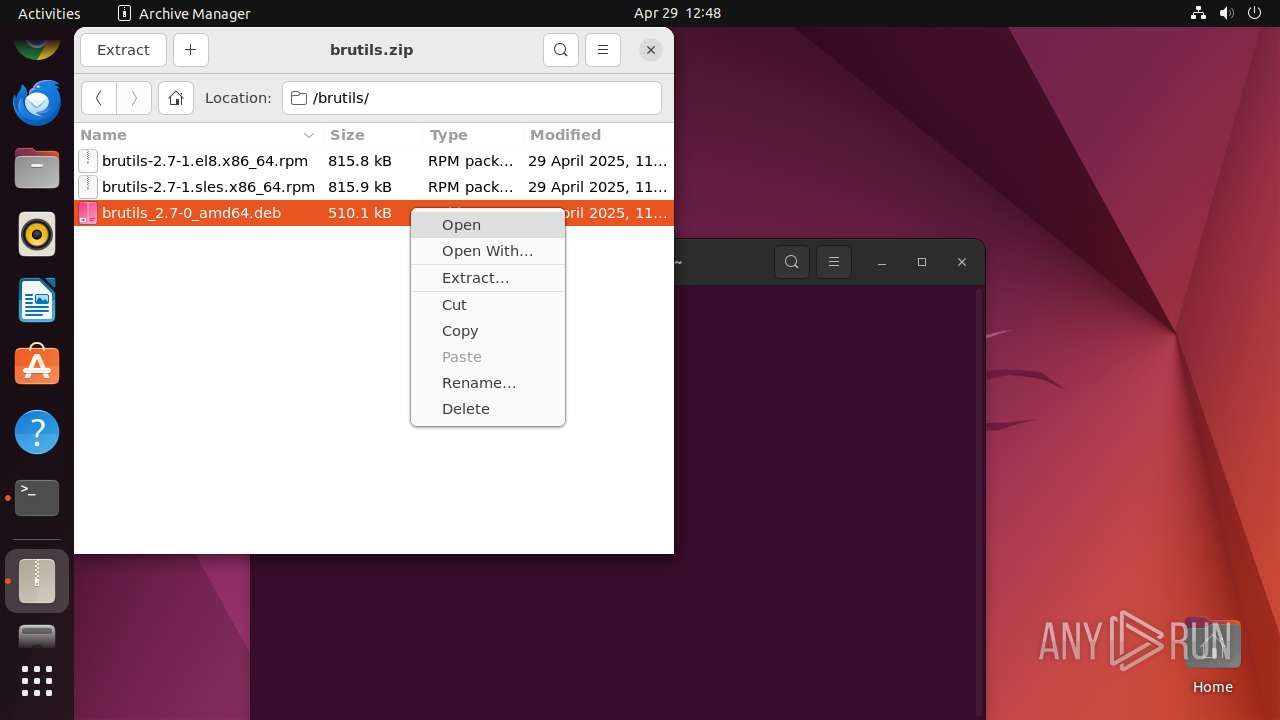
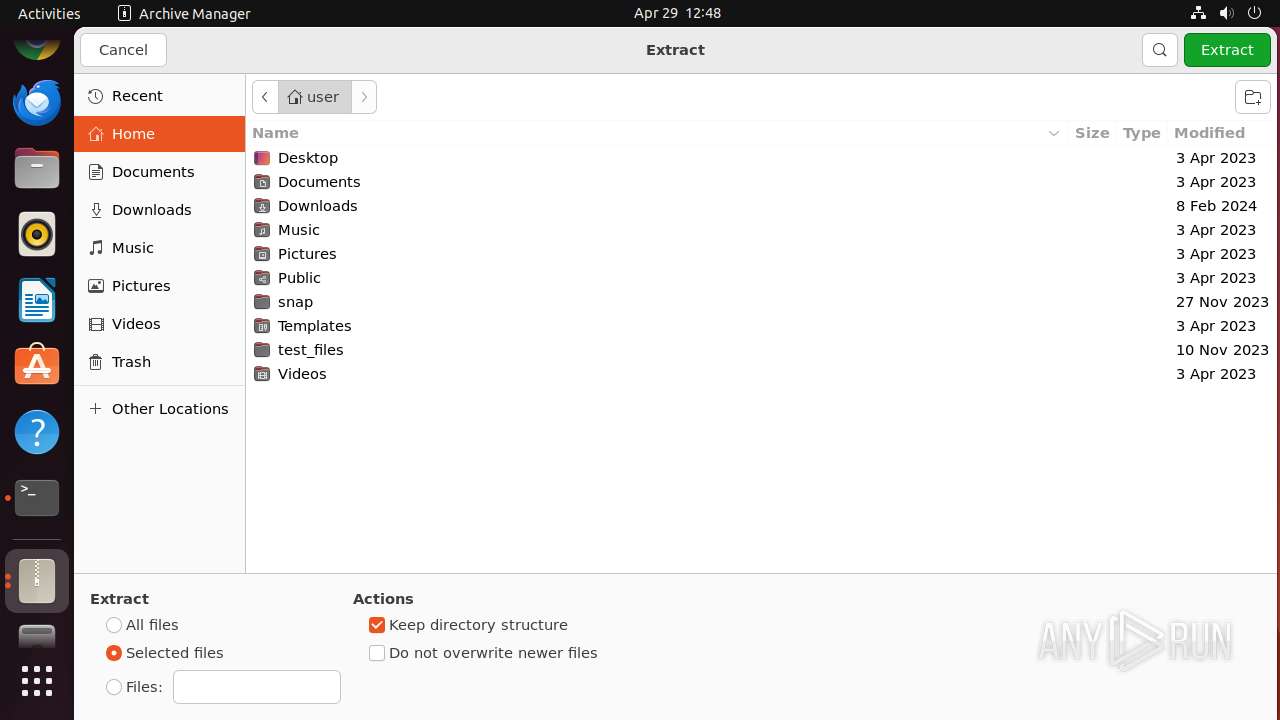
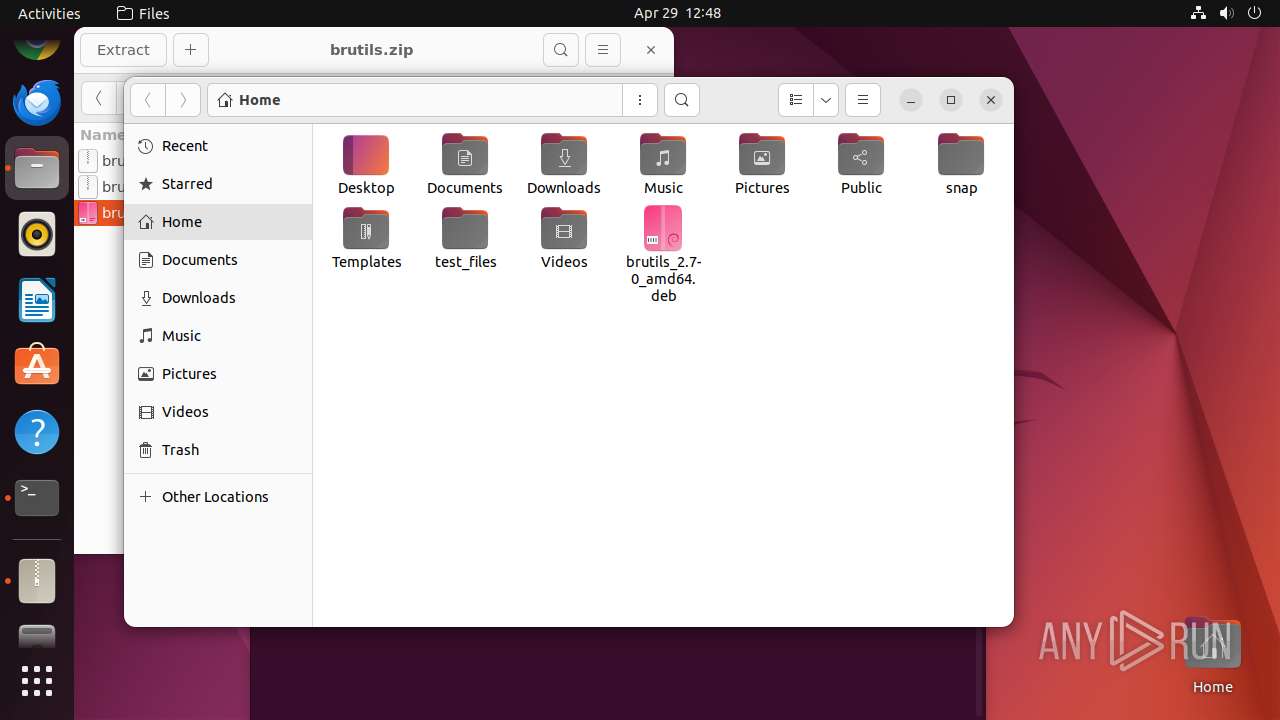
| 39525 | /usr/lib/p7zip/7z x -bd -bb1 -y -o/home/user/.cache/.fr-Y1P1g5 -- /tmp/brutils.zip brutils/brutils_2.7-0_amd64.deb | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
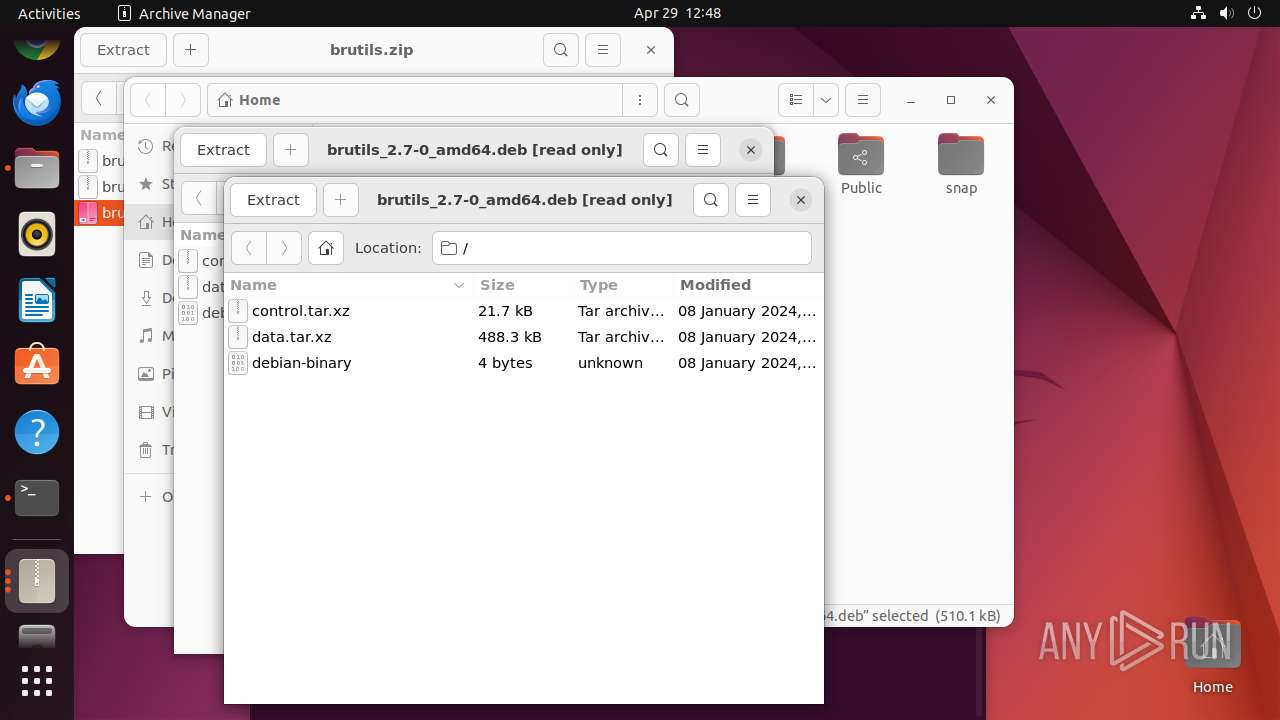
| 39526 | file-roller /tmp/brutils.zip | /usr/bin/file-roller | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
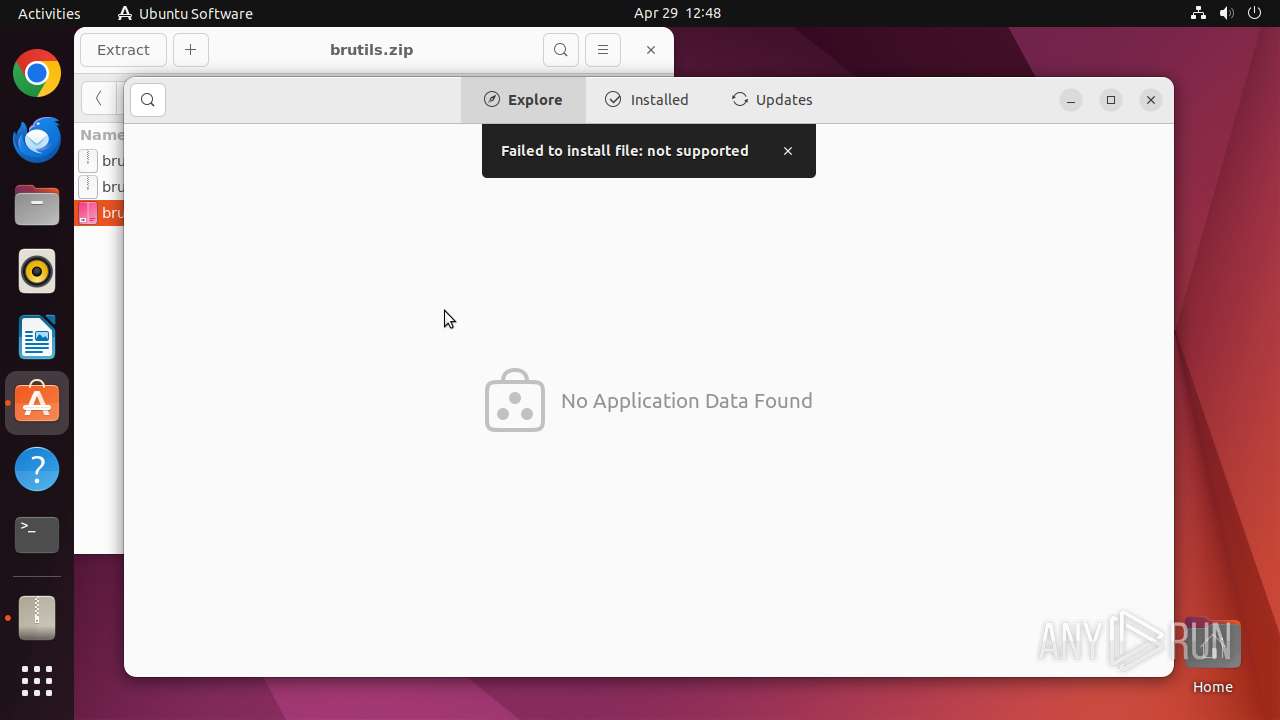
| 39527 | /snap/snap-store/959/usr/bin/snap-store --local-filename /home/user/.cache/.fr-Y1P1g5/brutils/brutils_2.7-0_amd64.deb | /snap/snap-store/959/usr/bin/snap-store | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39541 | /snap/snapd/20290/usr/lib/snapd/snap-seccomp version-info | /snap/snapd/20290/usr/lib/snapd/snap-seccomp | — | snap-store |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39525 | 7z | /home/user/.cache/.fr-Y1P1g5/brutils/brutils_2.7-0_amd64.deb | binary | |
MD5:— | SHA256:— | |||
| 39682 | 7z | /home/user/.fr-xMlNgq/brutils/brutils_2.7-0_amd64.deb | binary | |
MD5:— | SHA256:— | |||
| 39499 | file-roller | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 39694 | nautilus | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 39499 | file-roller | /home/user/.local/share/recently-used.xbel.OVY052 | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
13
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 195.181.175.40:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
39668 | gvfsd-smb-browse | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
14.100.168.192.in-addr.arpa |
| unknown |