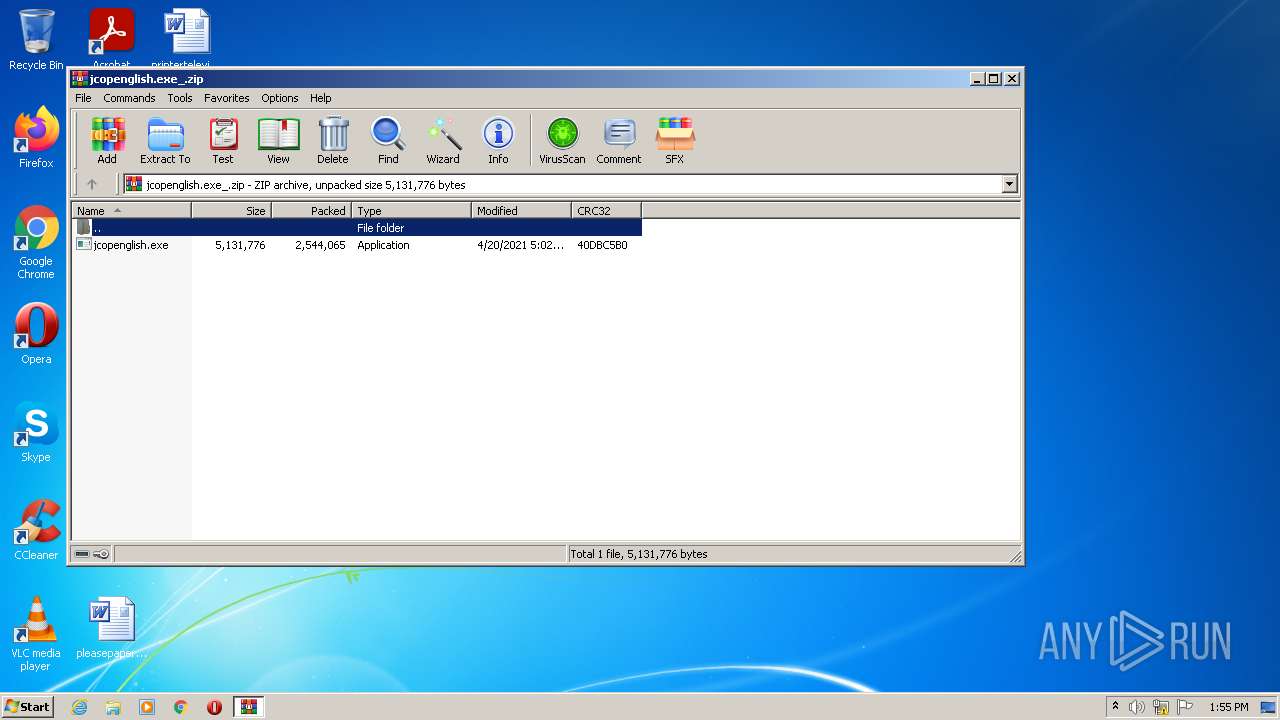
| File name: | jcopenglish.exe_.zip |
| Full analysis: | https://app.any.run/tasks/881107a7-8105-4b2d-85af-07c30880c1be |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2021, 13:55:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4F48F9F0BFBA90A09B26BFEA8929F2AA |
| SHA1: | 4EDEA29BF4E566D850303535AE03CF7C062235C1 |
| SHA256: | C640BB564D7FCE81EDAD9427C0A99C1092FE268D62079C1F3E42C4B63B74F2F5 |
| SSDEEP: | 49152:NM3X+iCk5T2flm+8cd7yUX2Fpdxb7RFx51TvR8cZ6lZ0Ng:N6XoeWX2/bNHvOrZ0g |
MALICIOUS
Application was dropped or rewritten from another process
- jcopenglish.exe (PID: 2204)
- GPShell.exe (PID: 404)
- GPShell.exe (PID: 3308)
- GPShell.exe (PID: 1780)
- GPShell.exe (PID: 3748)
- GPShell.exe (PID: 2444)
- GPShell.exe (PID: 2744)
- GPShell.exe (PID: 3076)
- GPShell.exe (PID: 3072)
- GPShell.exe (PID: 692)
- GPShell.exe (PID: 2232)
- GPShell.exe (PID: 1068)
- GPShell.exe (PID: 1516)
- GPShell.exe (PID: 3920)
- GPShell.exe (PID: 1988)
Drops executable file immediately after starts
- jcopenglish.exe (PID: 2204)
Loads dropped or rewritten executable
- GPShell.exe (PID: 404)
- GPShell.exe (PID: 3308)
- GPShell.exe (PID: 1780)
- GPShell.exe (PID: 2744)
- GPShell.exe (PID: 3748)
- GPShell.exe (PID: 2444)
- GPShell.exe (PID: 3076)
- GPShell.exe (PID: 2232)
- GPShell.exe (PID: 692)
- GPShell.exe (PID: 1068)
- GPShell.exe (PID: 1516)
- GPShell.exe (PID: 3072)
- GPShell.exe (PID: 3920)
- GPShell.exe (PID: 1988)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2896)
- jcopenglish.exe (PID: 2204)
- GPShell.exe (PID: 404)
- GPShell.exe (PID: 3308)
- GPShell.exe (PID: 1780)
- GPShell.exe (PID: 2444)
- GPShell.exe (PID: 2744)
- GPShell.exe (PID: 3920)
- GPShell.exe (PID: 692)
- GPShell.exe (PID: 1068)
- GPShell.exe (PID: 1988)
Checks supported languages
- WinRAR.exe (PID: 2896)
- jcopenglish.exe (PID: 2204)
- GPShell.exe (PID: 404)
- GPShell.exe (PID: 3308)
- GPShell.exe (PID: 3748)
- GPShell.exe (PID: 2444)
- GPShell.exe (PID: 2744)
- GPShell.exe (PID: 3076)
- GPShell.exe (PID: 1780)
- GPShell.exe (PID: 3920)
- GPShell.exe (PID: 2232)
- GPShell.exe (PID: 692)
- GPShell.exe (PID: 1068)
- GPShell.exe (PID: 3072)
- GPShell.exe (PID: 1988)
- GPShell.exe (PID: 1516)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2896)
- jcopenglish.exe (PID: 2204)
Drops a file with too old compile date
- jcopenglish.exe (PID: 2204)
INFO
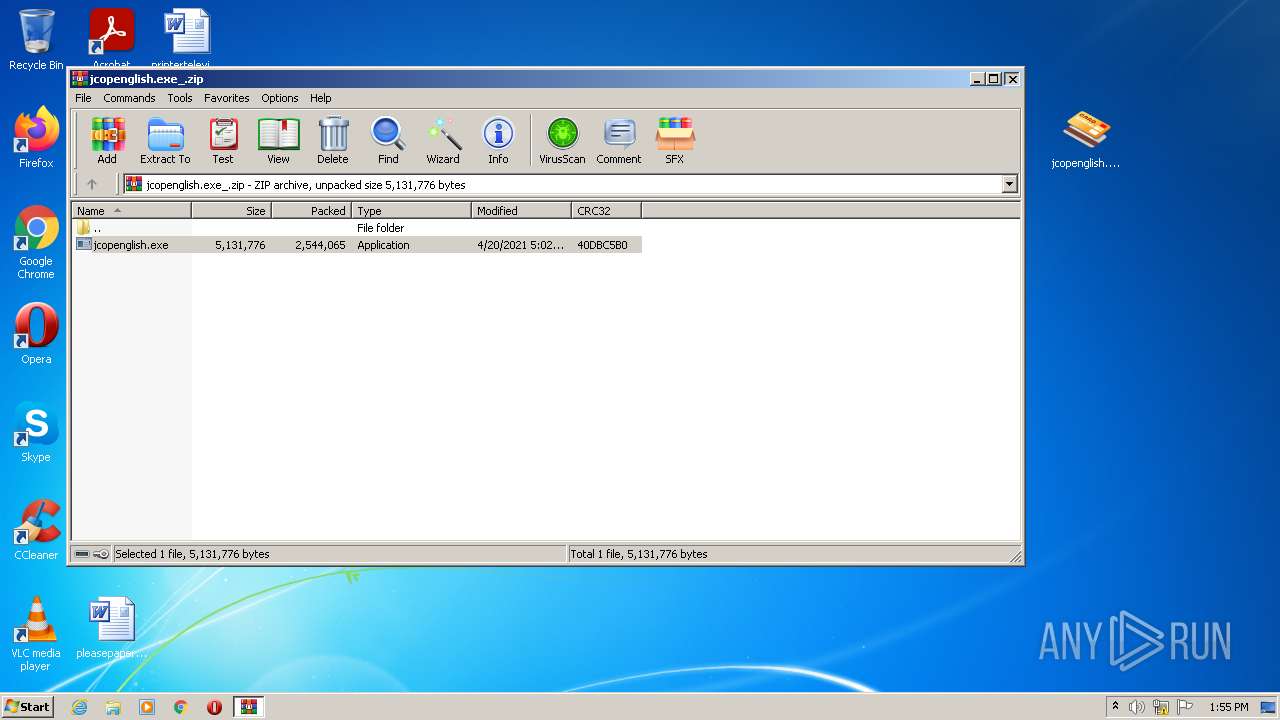
Manual execution by user
- jcopenglish.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | jcopenglish.exe |
|---|---|
| ZipUncompressedSize: | 5131776 |
| ZipCompressedSize: | 2544065 |
| ZipCRC: | 0x40dbc5b0 |
| ZipModifyDate: | 2021:04:20 12:02:06 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0008 |
| ZipRequiredVersion: | 20 |
Total processes
64
Monitored processes
16
Malicious processes
1
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
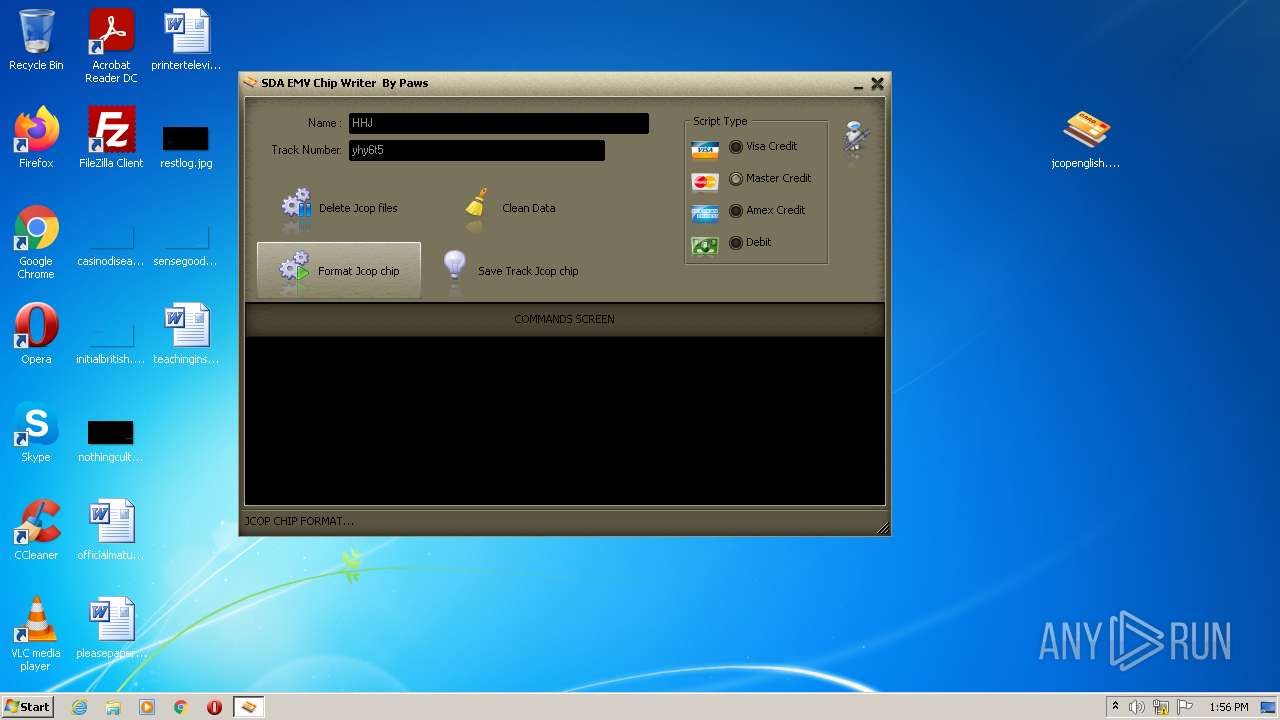
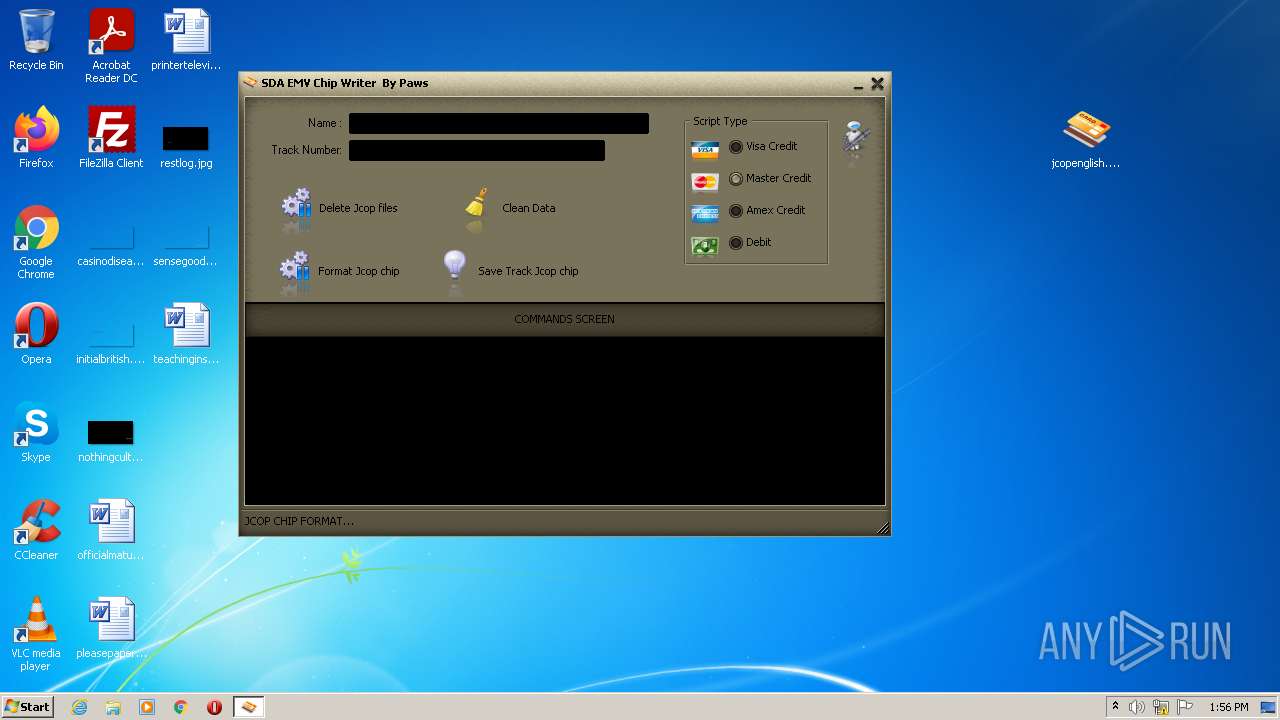
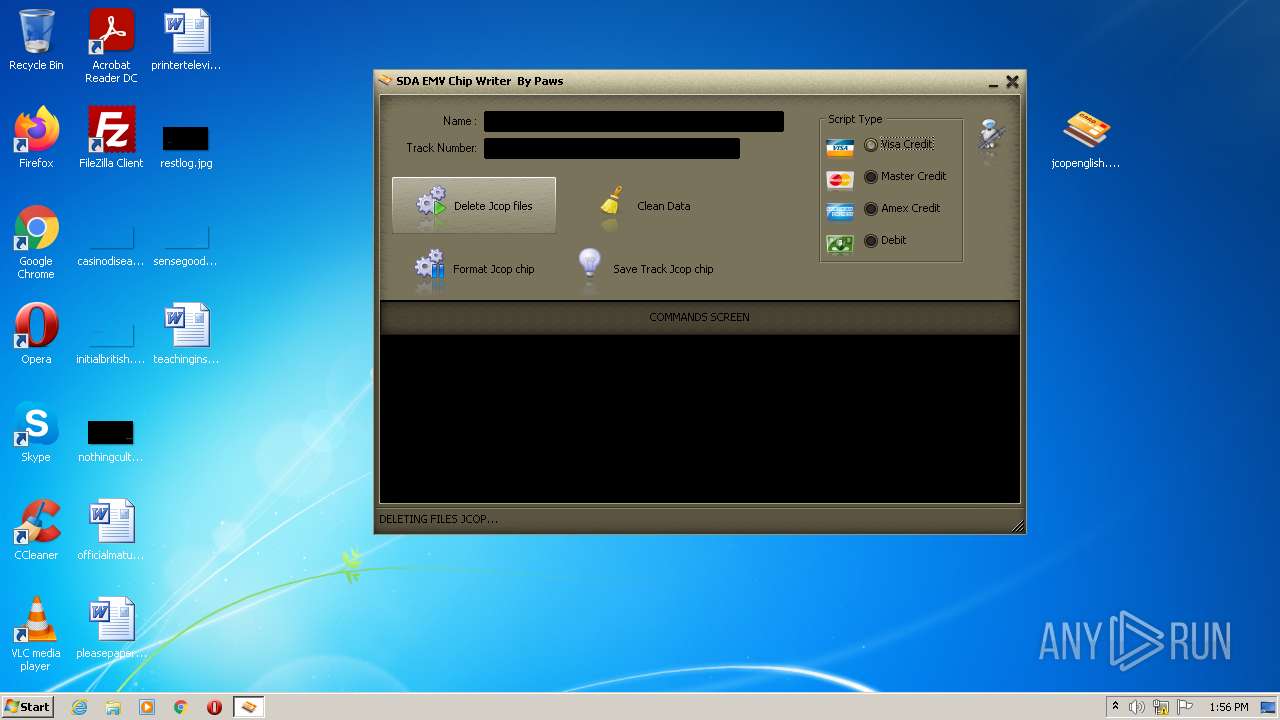
| 404 | "C:\Windowr\GPShell.exe" form.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 692 | "C:\Windowr\GPShell.exe" form.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
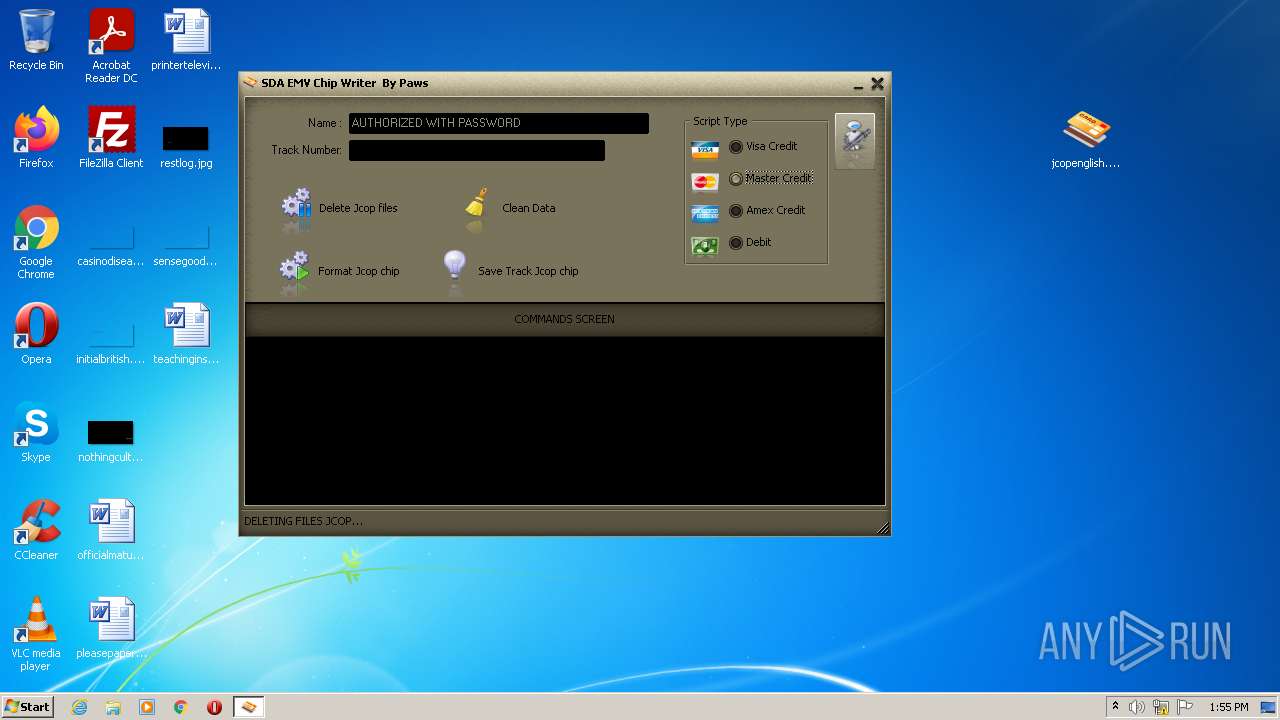
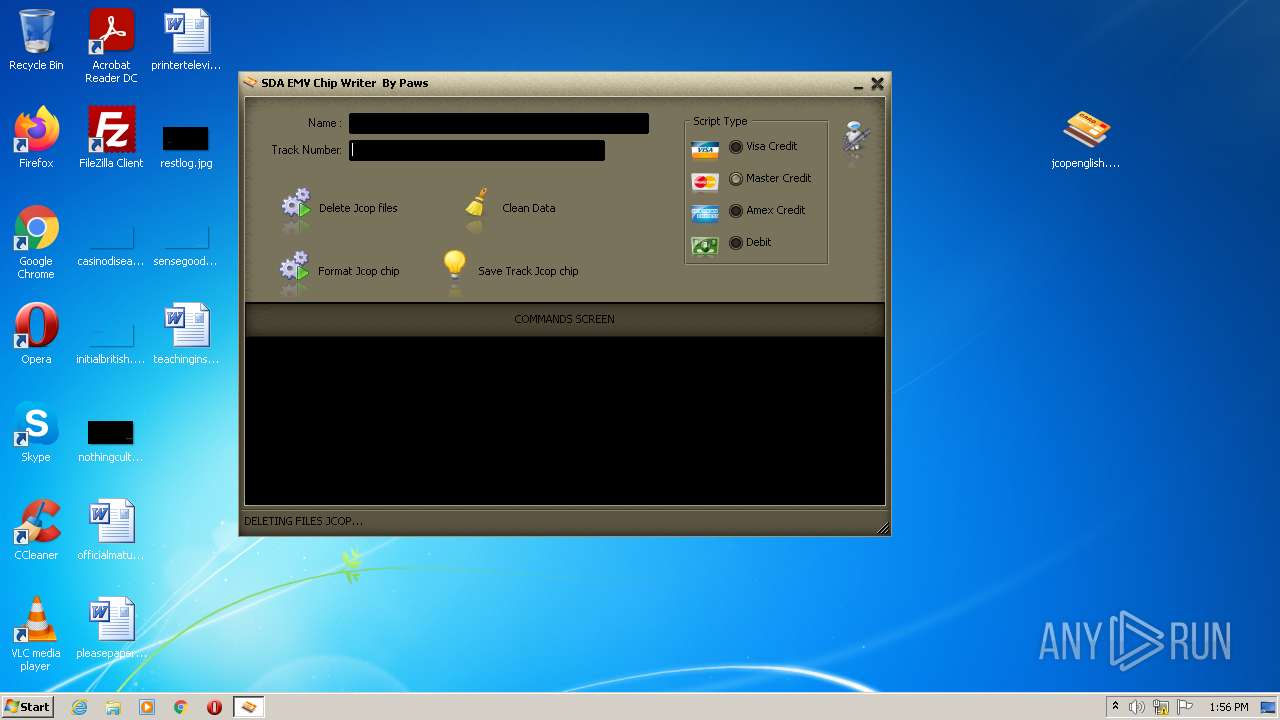
| 1068 | "C:\Windowr\GPShell.exe" del.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
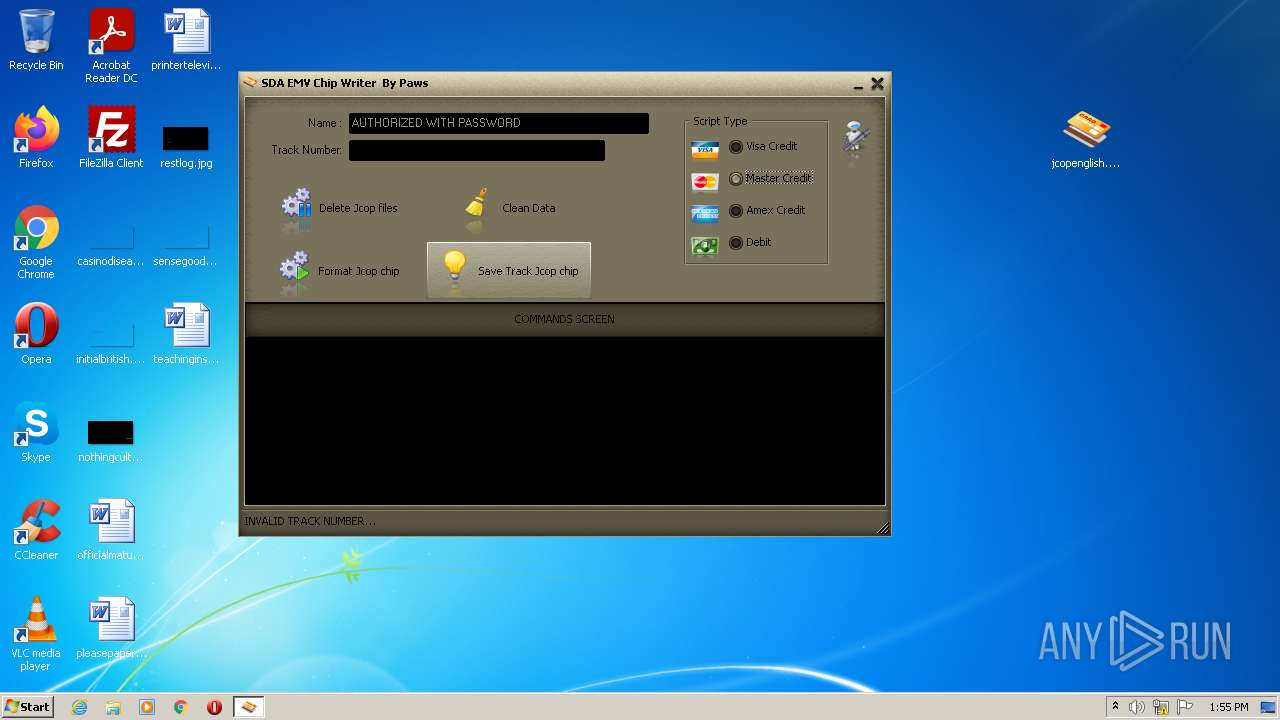
| 1516 | "C:\Windowr\GPShell.exe" apdu.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 1780 | "C:\Windowr\GPShell.exe" del.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 1988 | "C:\Windowr\GPShell.exe" del.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
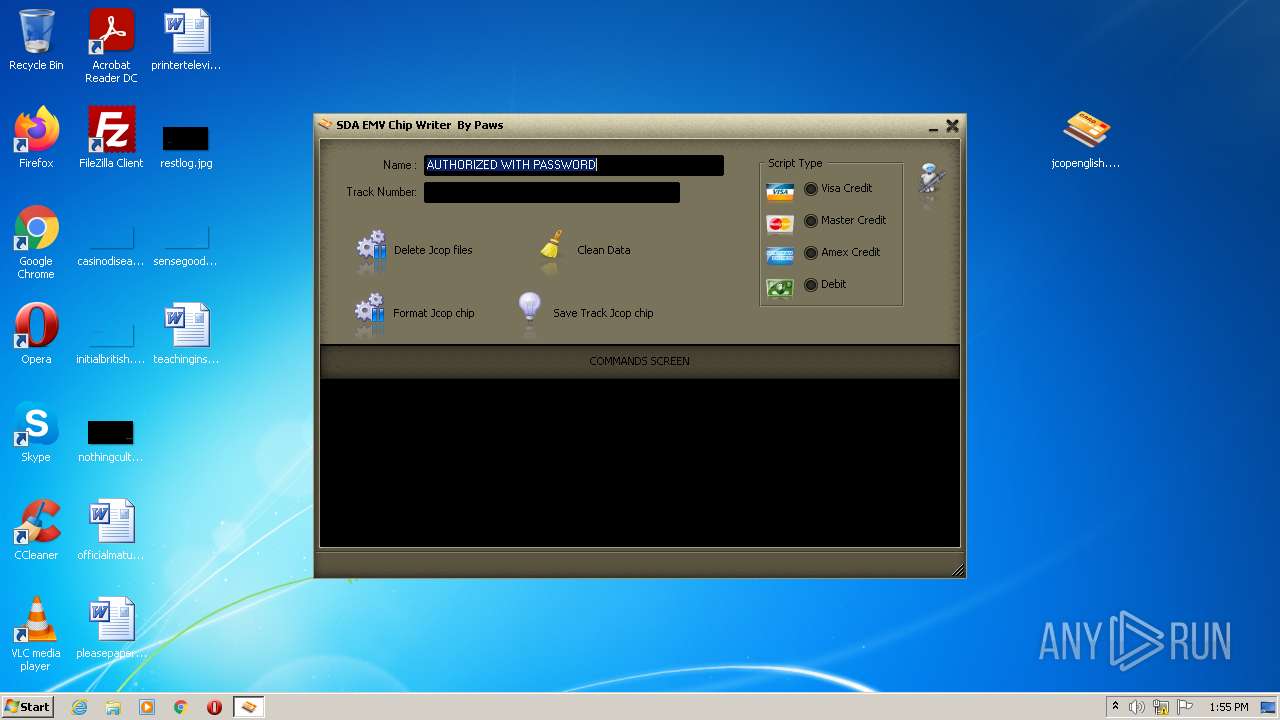
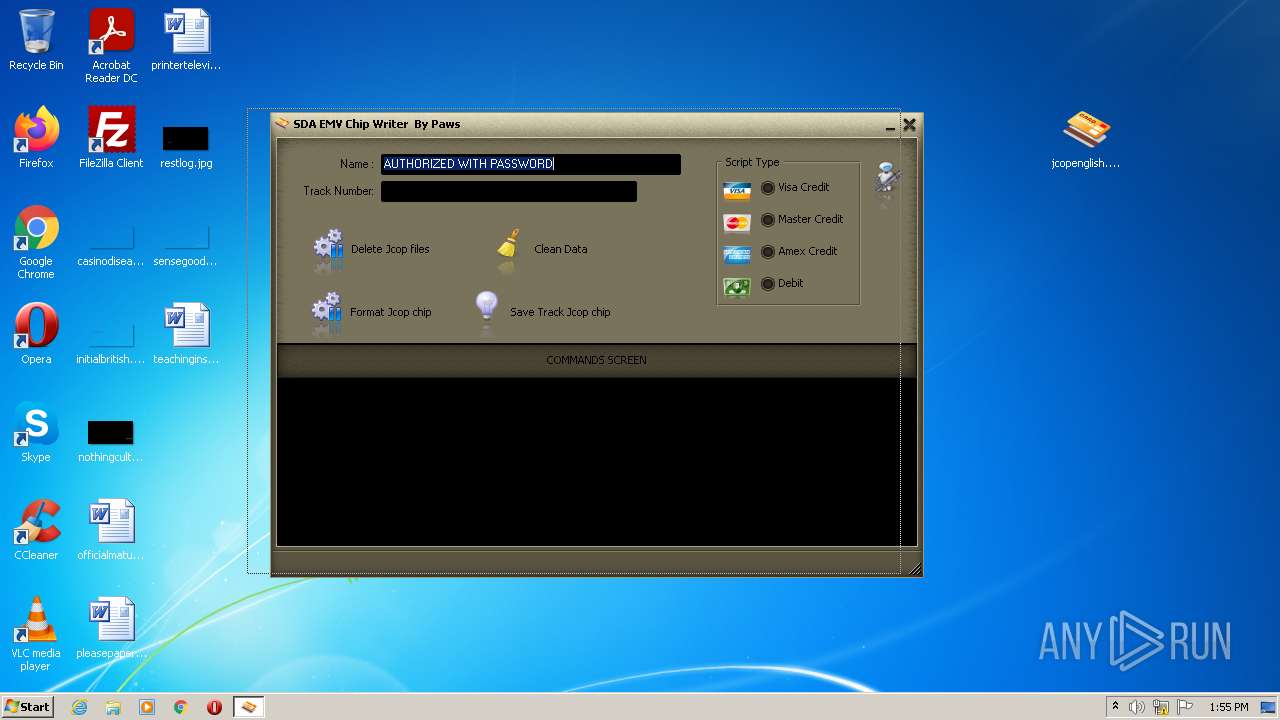
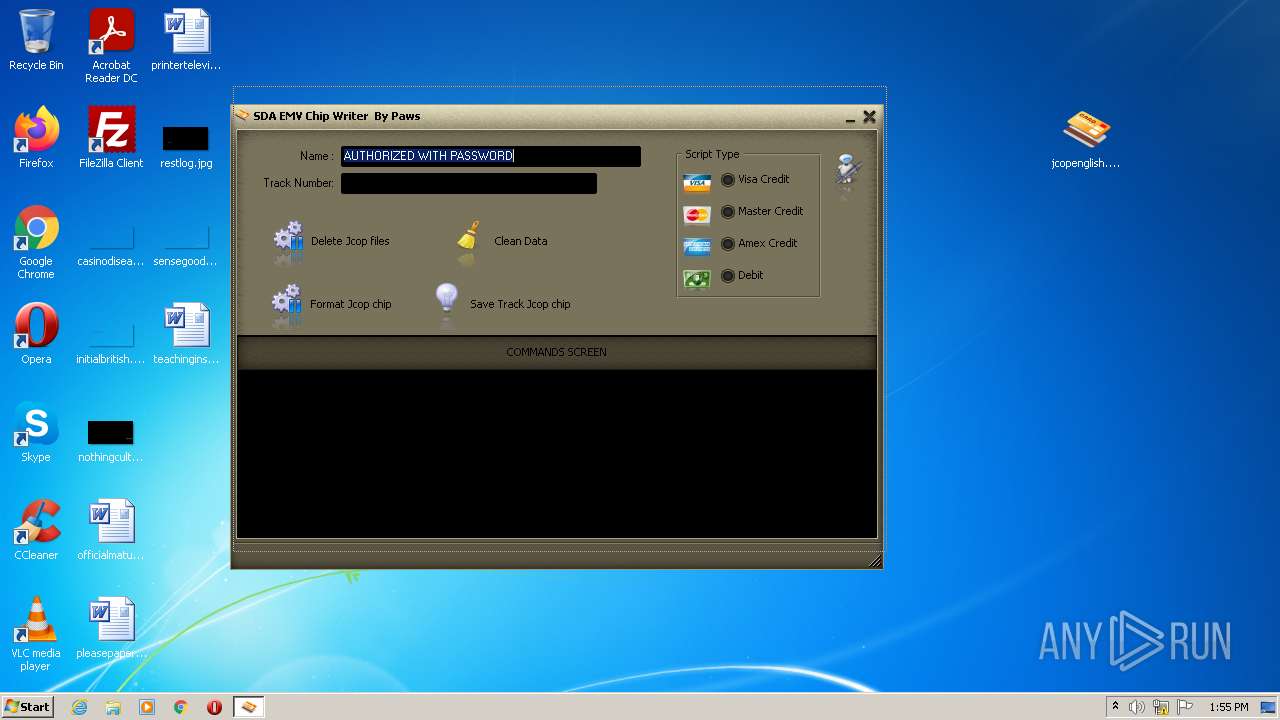
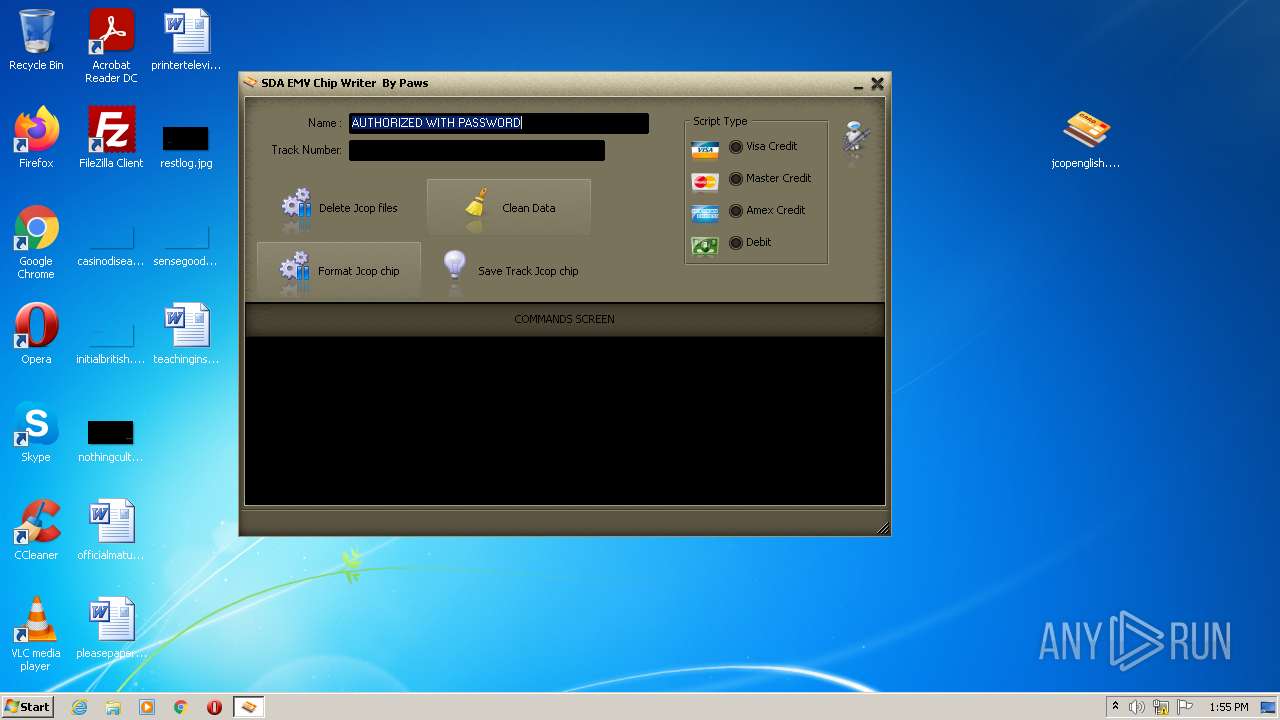
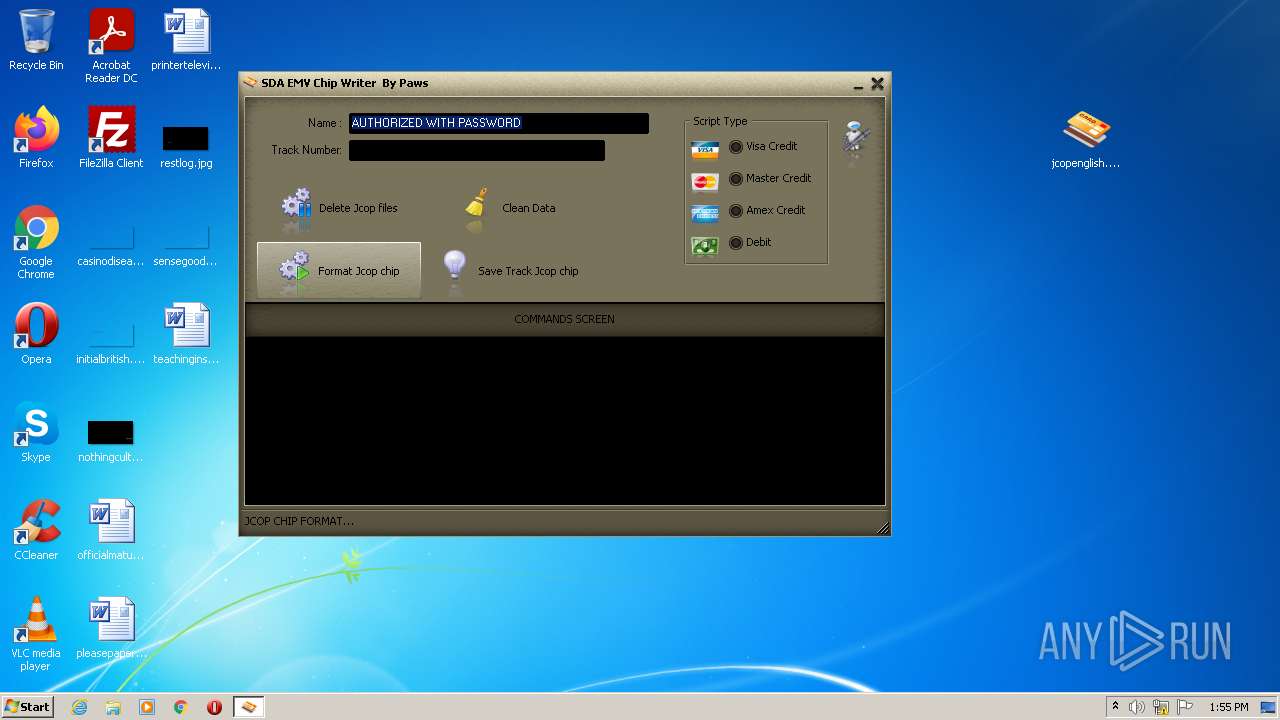
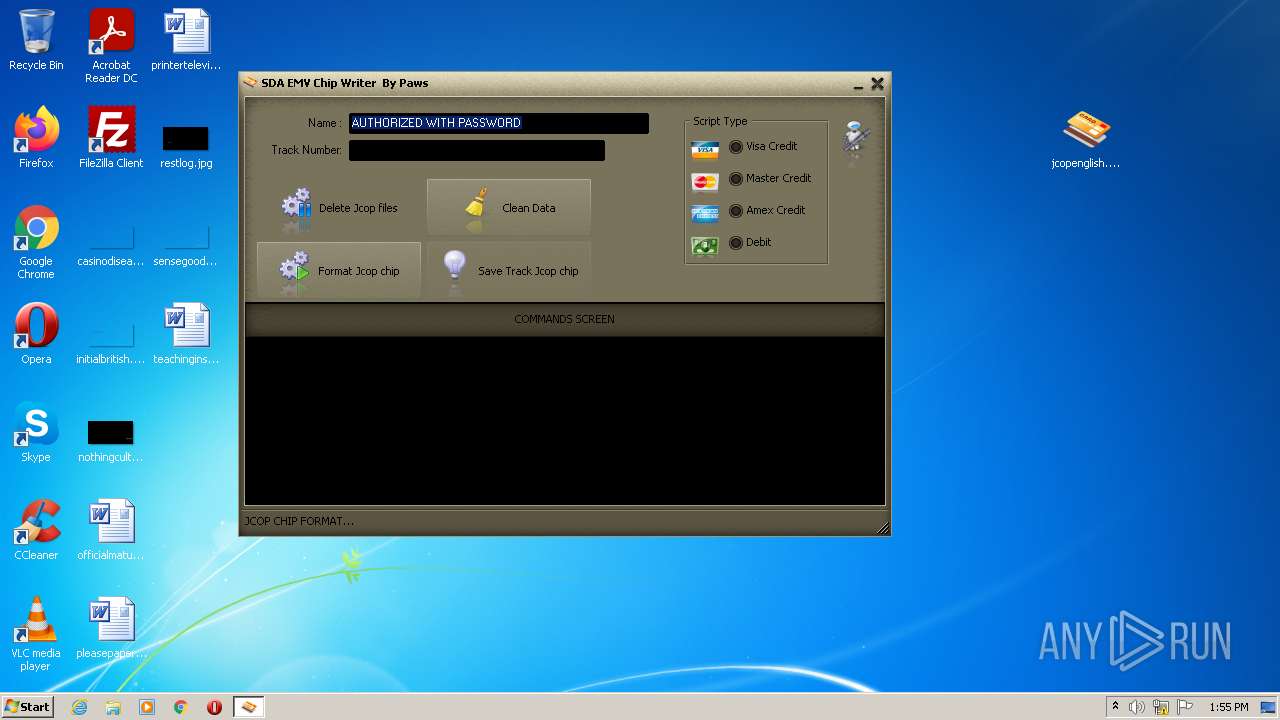
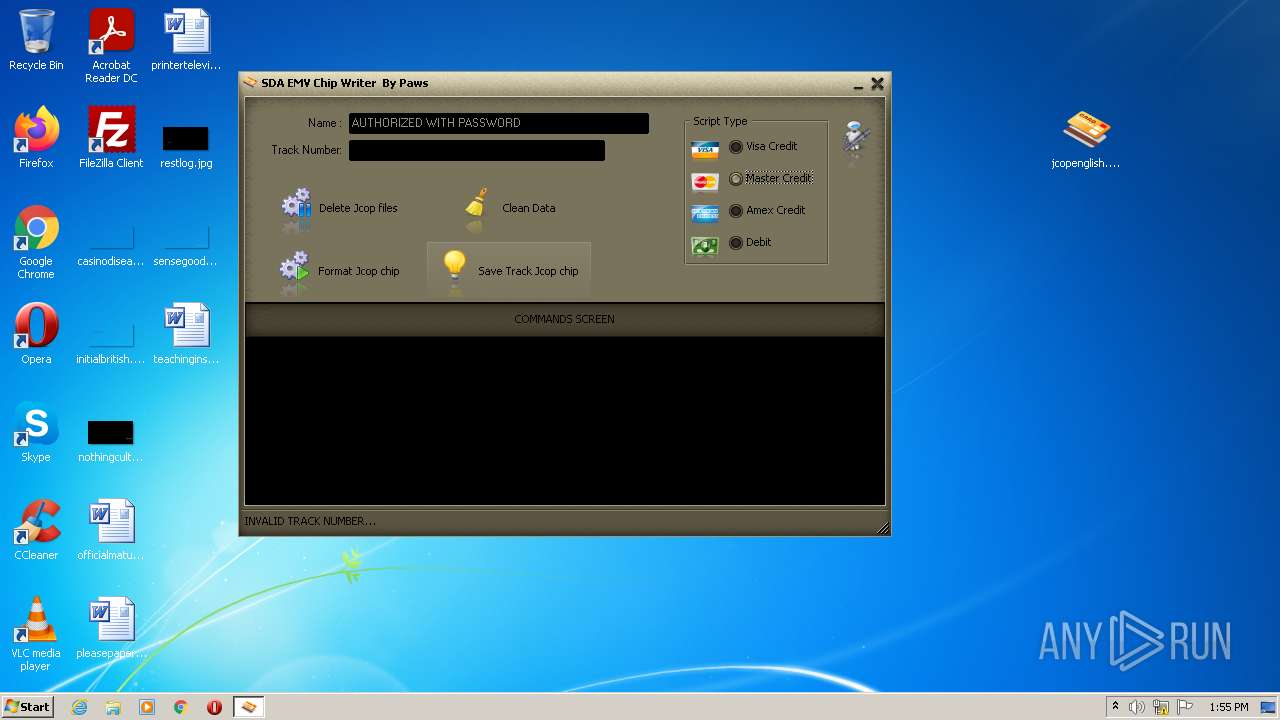
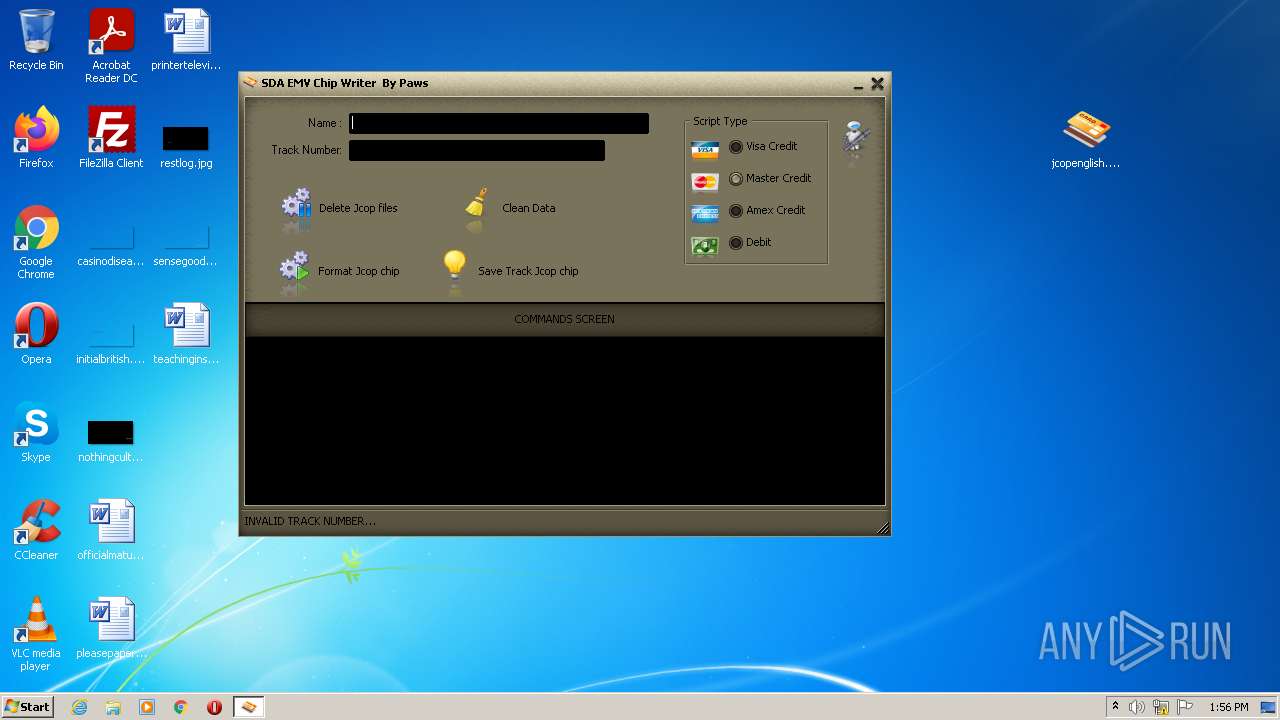
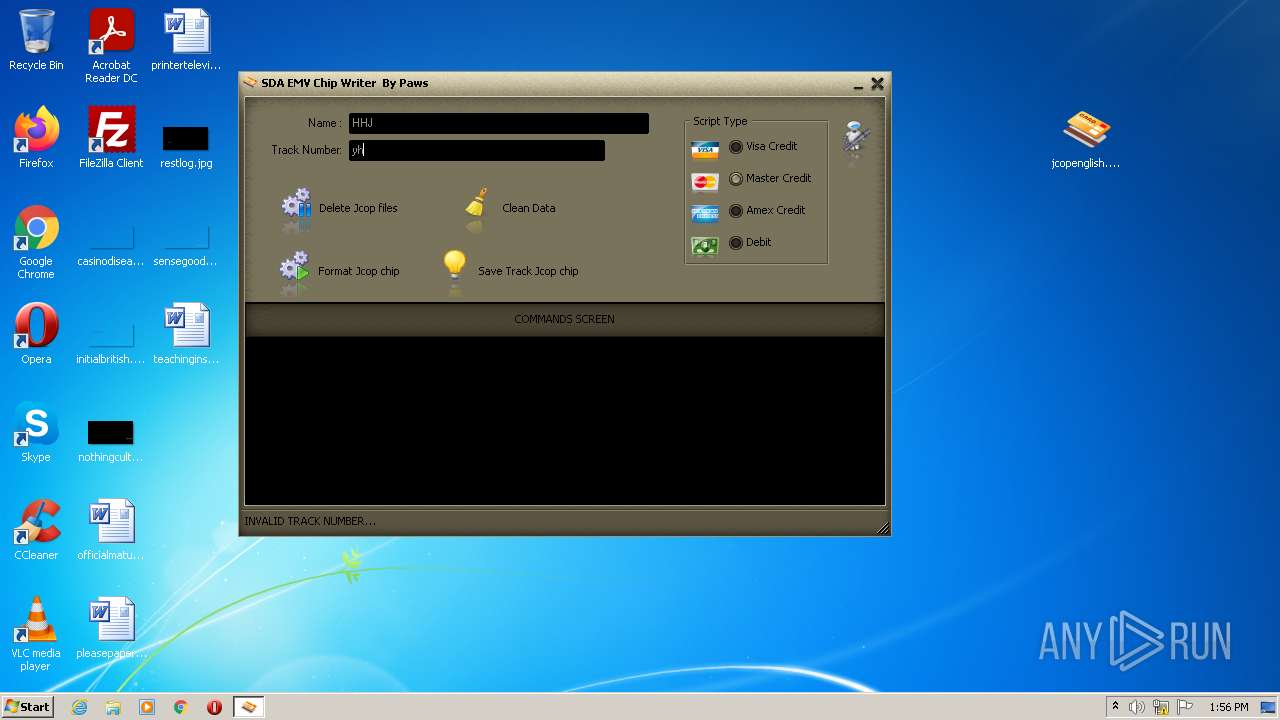
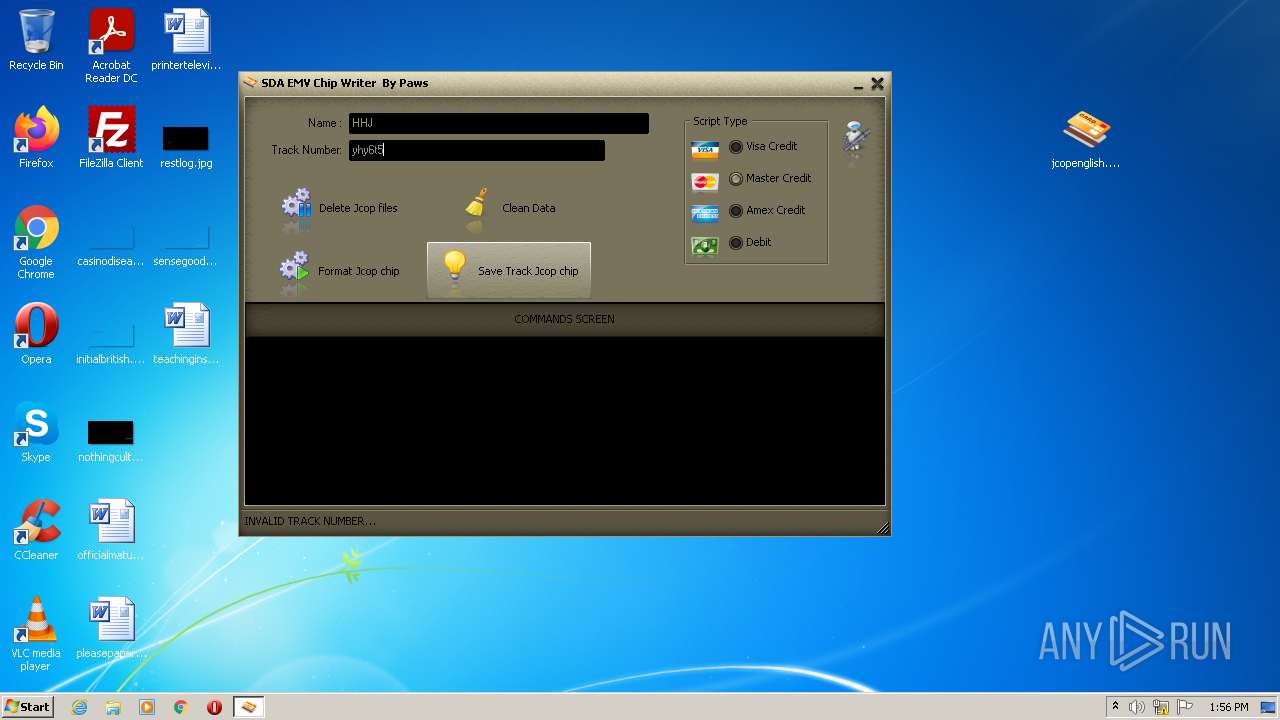
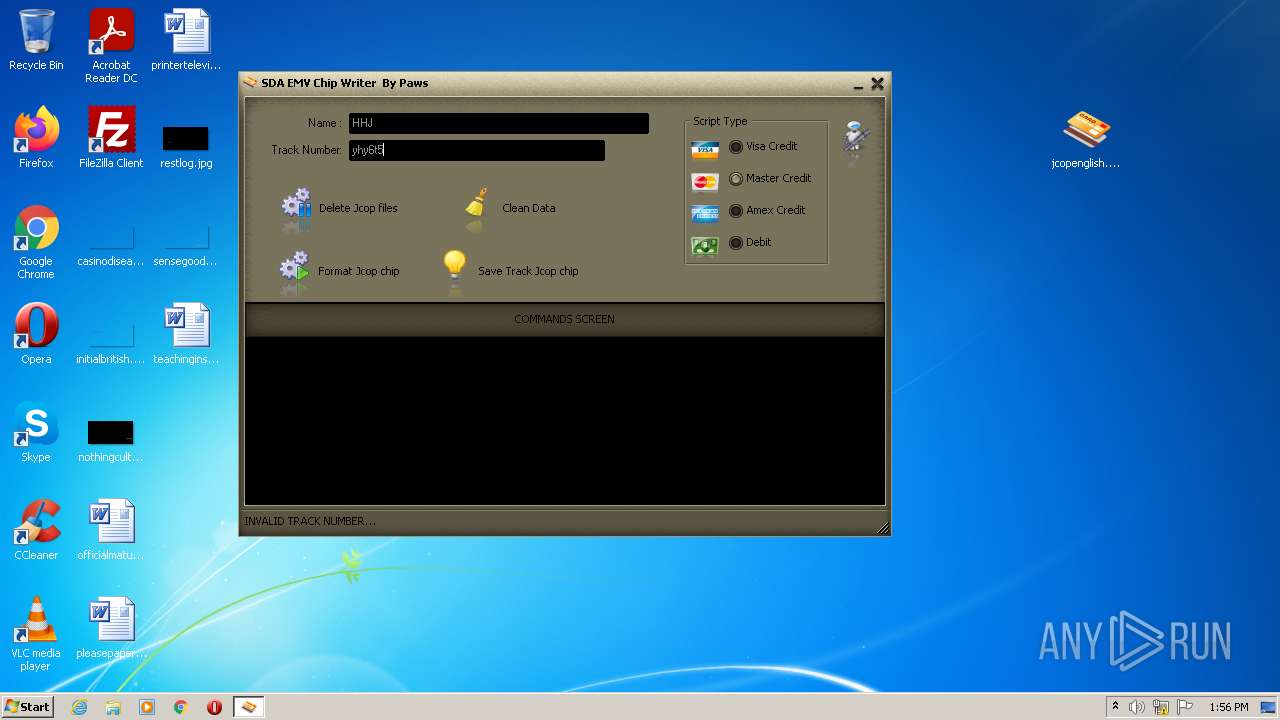
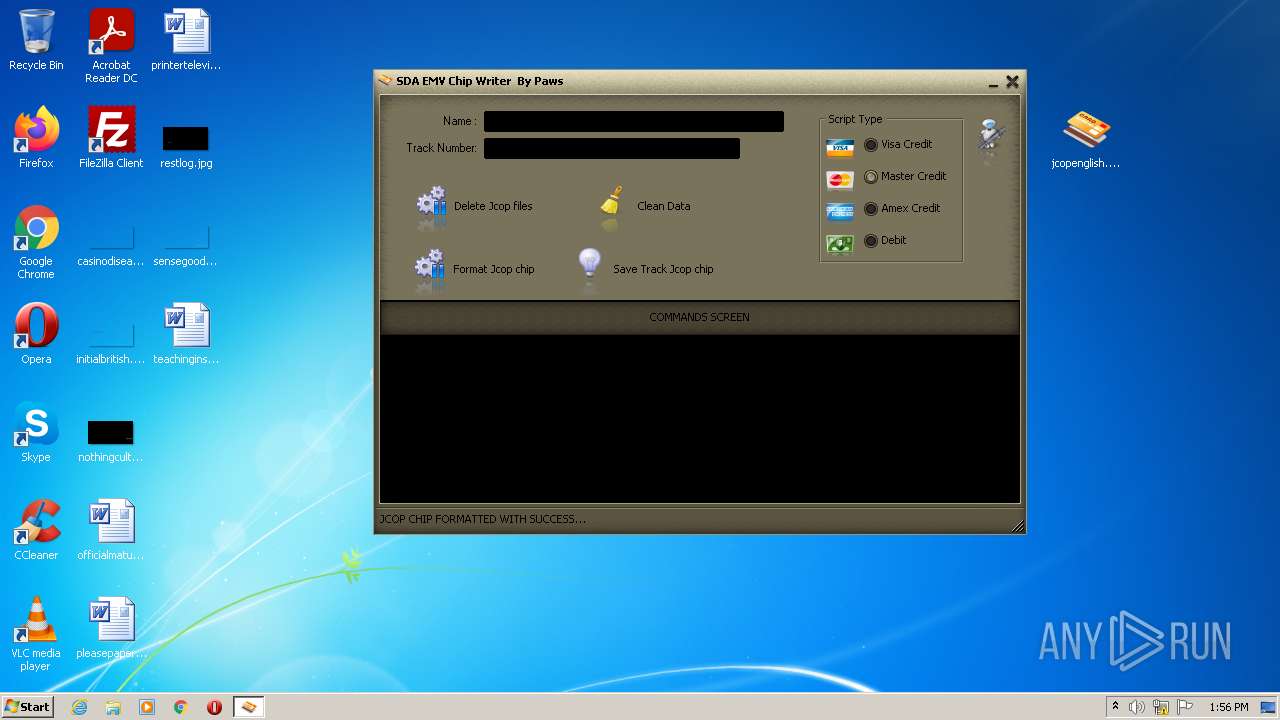
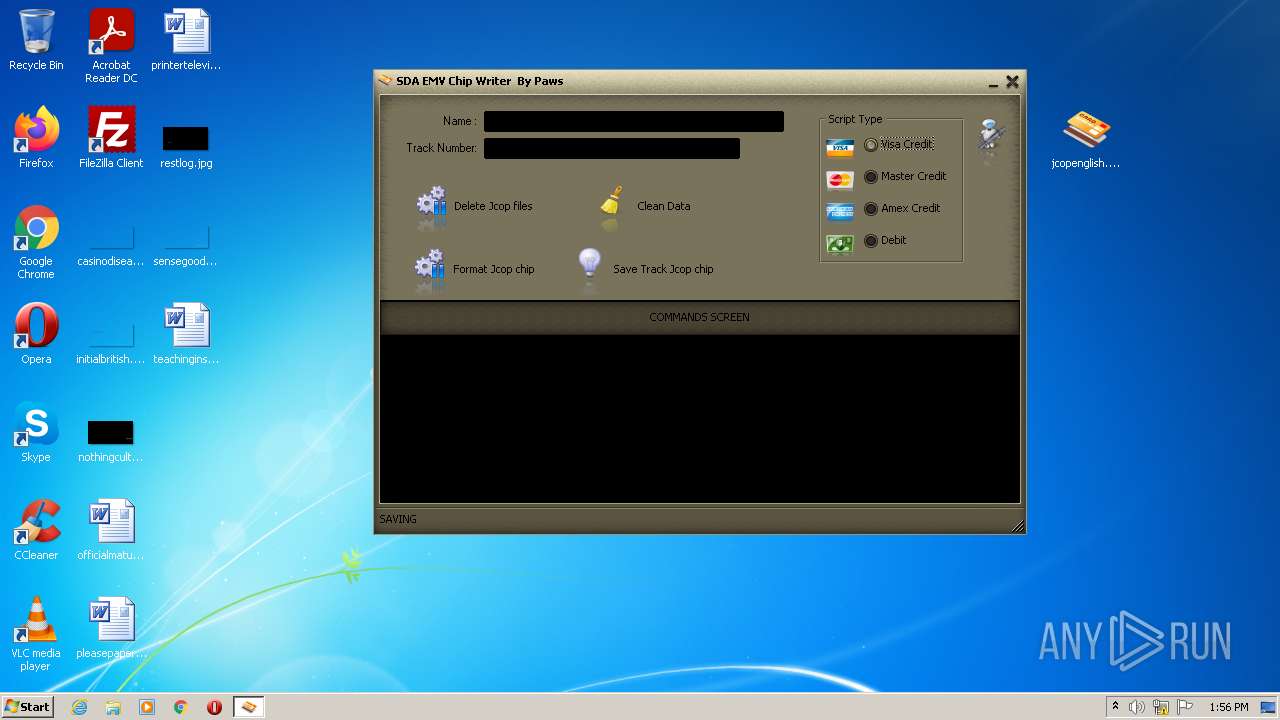
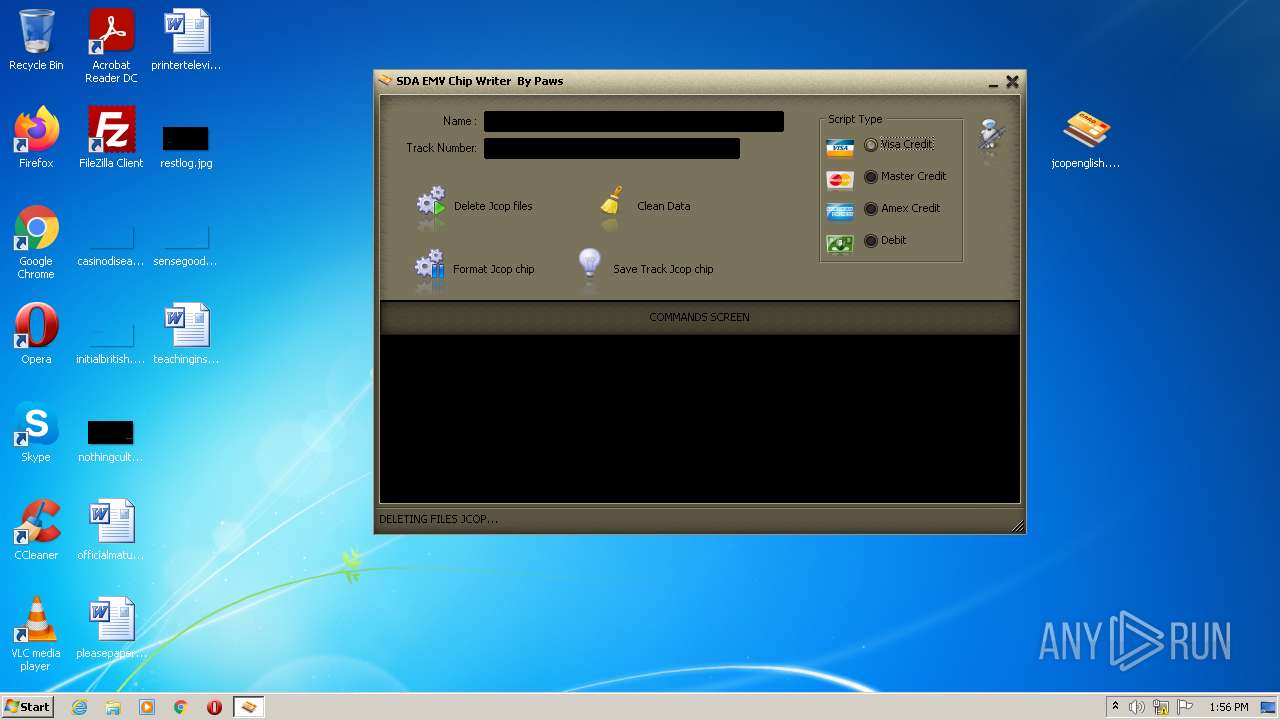
| 2204 | "C:\Users\admin\Desktop\jcopenglish.exe" | C:\Users\admin\Desktop\jcopenglish.exe | Explorer.EXE | ||||||||||||
User: admin Company: EMV Writer Software by Paws Integrity Level: MEDIUM Description: EMV Chip Writer Exit code: 0 Version: 10.0.0.0 Modules
| |||||||||||||||
| 2232 | "C:\Windowr\GPShell.exe" apdu.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 2444 | "C:\Windowr\GPShell.exe" form.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 2744 | "C:\Windowr\GPShell.exe" form.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
Total events
1 313
Read events
1 284
Write events
29
Delete events
0
Modification events
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\jcopenglish.exe_.zip | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
7
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | jcopenglish.exe | C:\Windowr\Global.drv | compressed | |
MD5:418F4F42405CEC3252F0B952ED9A642C | SHA256:148B8755D228F174F4DBD0B8454E3825F34E6D6E055341D4C3981C2BB7664C07 | |||
| 2896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2896.49783\jcopenglish.exe | executable | |
MD5:0828480F98ADB533104D42AD42601F80 | SHA256:1ECFD3755EBA578108363C0705C6EC205972080739ED0FBD17439F8139BA7E08 | |||
| 2204 | jcopenglish.exe | C:\Windowr\GPPcScConnectionPlugin.dll | executable | |
MD5:2F99E012379E8C950B0BDE761C5CCA0F | SHA256:5D84EC3F8DEE7438B0049D5DC201A68A99F3E471A4C9ACAC48DD7F67F89FD178 | |||
| 2204 | jcopenglish.exe | C:\Windowr\GPShell.exe | executable | |
MD5:50FCDD91AEE3EC8D7C54FEB63E324C03 | SHA256:BA5E9041668257393AE28413F5099DB5D12D7F48C239E8D19E9BEDA2036B31BE | |||
| 2204 | jcopenglish.exe | C:\Windowr\ssleay32.dll | executable | |
MD5:63D26ECAFCF3B2CEBD5E2F05BCAD553D | SHA256:4F1BAD1A6B9E00473D885BF4E7F3D9D0EC3D91CBDCE05B46F6C6CB2D1FCA8C2B | |||
| 2204 | jcopenglish.exe | C:\Windowr\del.dll | text | |
MD5:39F489355AC6CCC48A810E2C867475FD | SHA256:71E16A8C9540CBEB6AFC80045A21F7C5954F9E54B5EC731C93AFCA6D67A61646 | |||
| 2204 | jcopenglish.exe | C:\Windowr\GlobalPlatform.dll | executable | |
MD5:C035B189CCC0FA06E549CCABF7DFBA48 | SHA256:DAC5A4213654CAE1AA622877E7E156C0EFD77C0601440DF7CE9995E280DF8694 | |||
| 2204 | jcopenglish.exe | C:\Windowr\MacGyver.cap | compressed | |
MD5:3709E18B229E3DB113BF5C7863C59DB4 | SHA256:9DC70002E82C78EE34C813597925C6CF8AA8D68B7E9CE5BCC70EA9BCAB9DBF4A | |||
| 2204 | jcopenglish.exe | C:\Windowr\libeay32.dll | executable | |
MD5:A7EFD09E5B963AF88CE2FC5B8EB7127C | SHA256:FA4FB4F5A28BDE9C9CBC4BAA9E737C282799294C65E31D39CDF8E2C758969A70 | |||
| 2204 | jcopenglish.exe | C:\Windowr\zlib1.dll | executable | |
MD5:C7D4D685A0AF2A09CBC21CB474358595 | SHA256:E96B397B499D9EAA3F52EAF496CA8941E80C0AD1544879CCADF02BF2C6A1ECFC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report