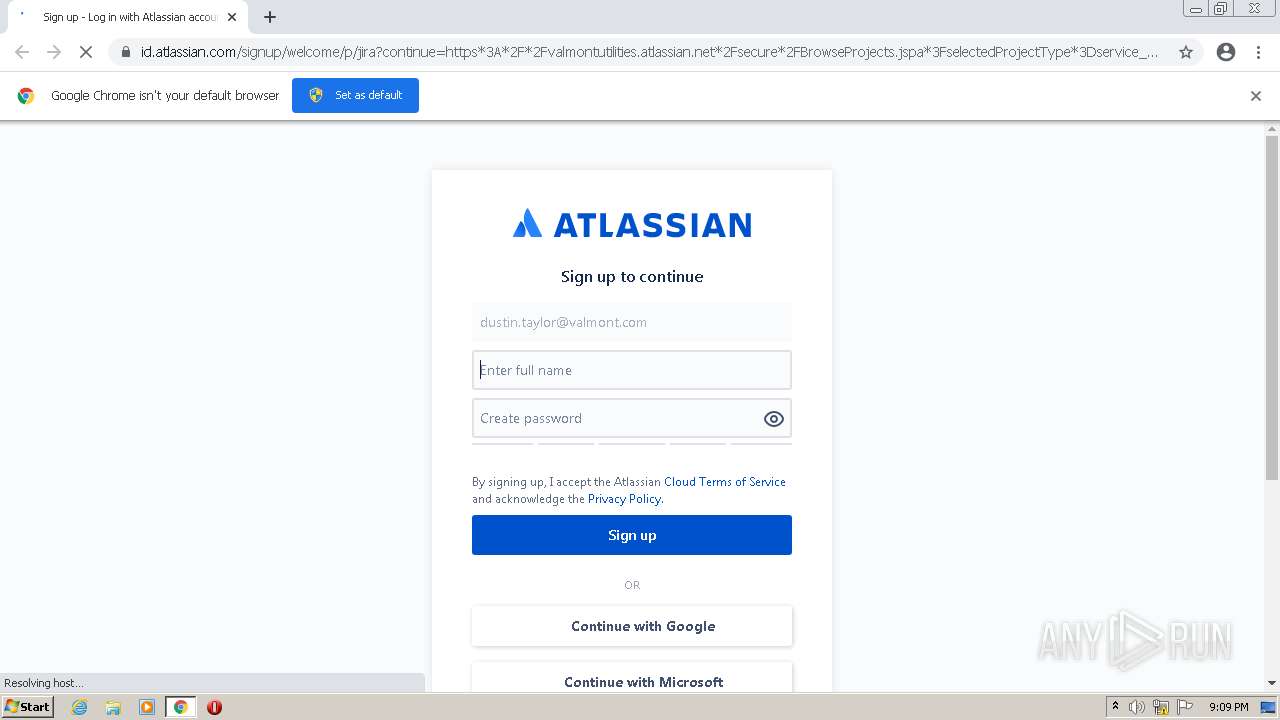
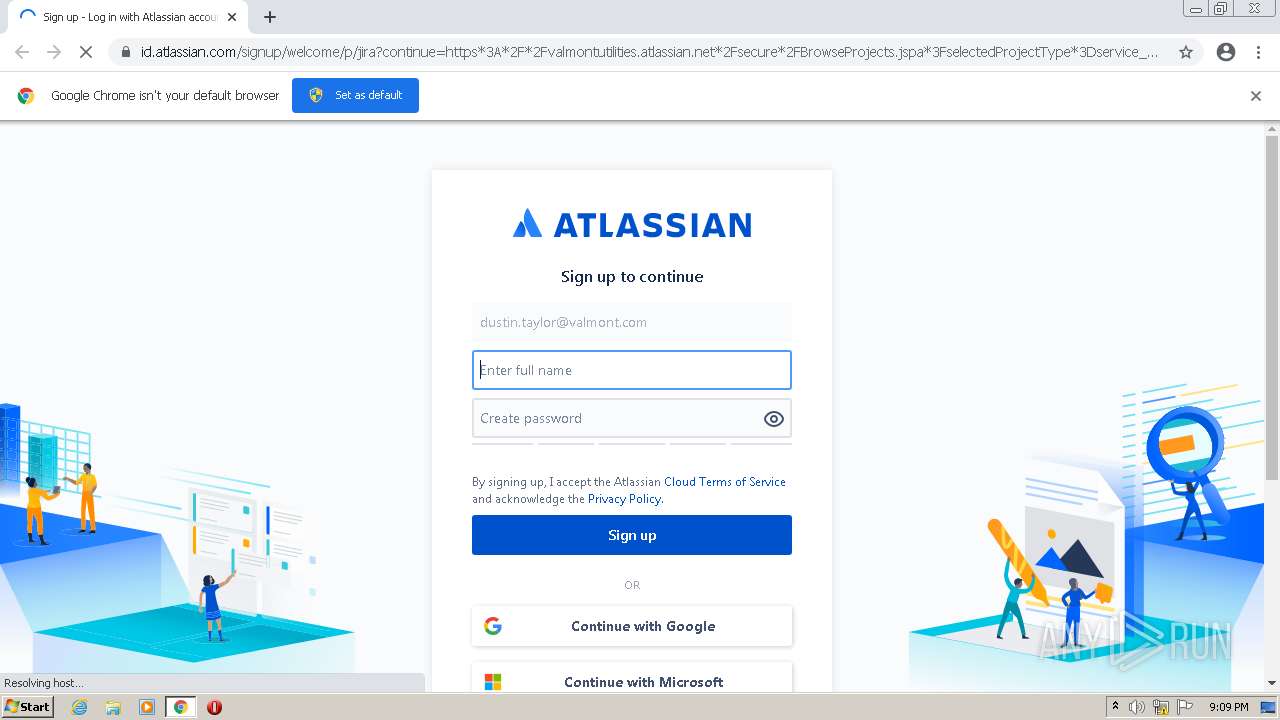
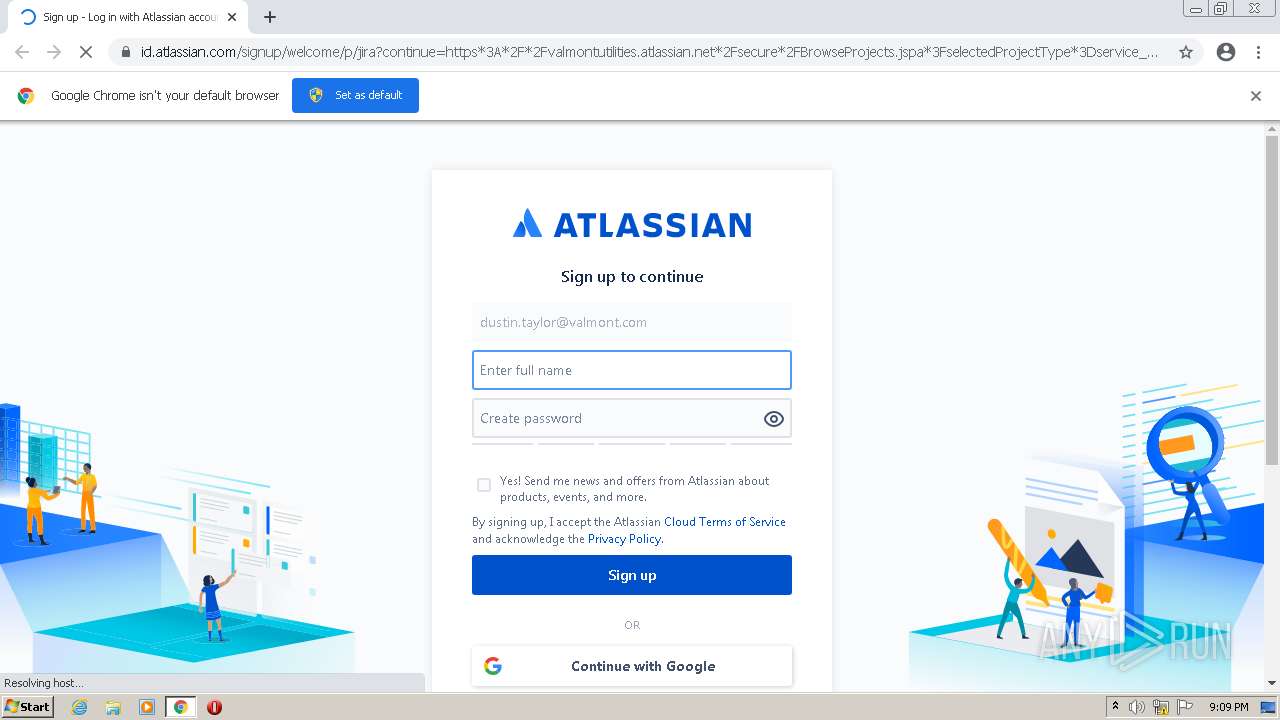
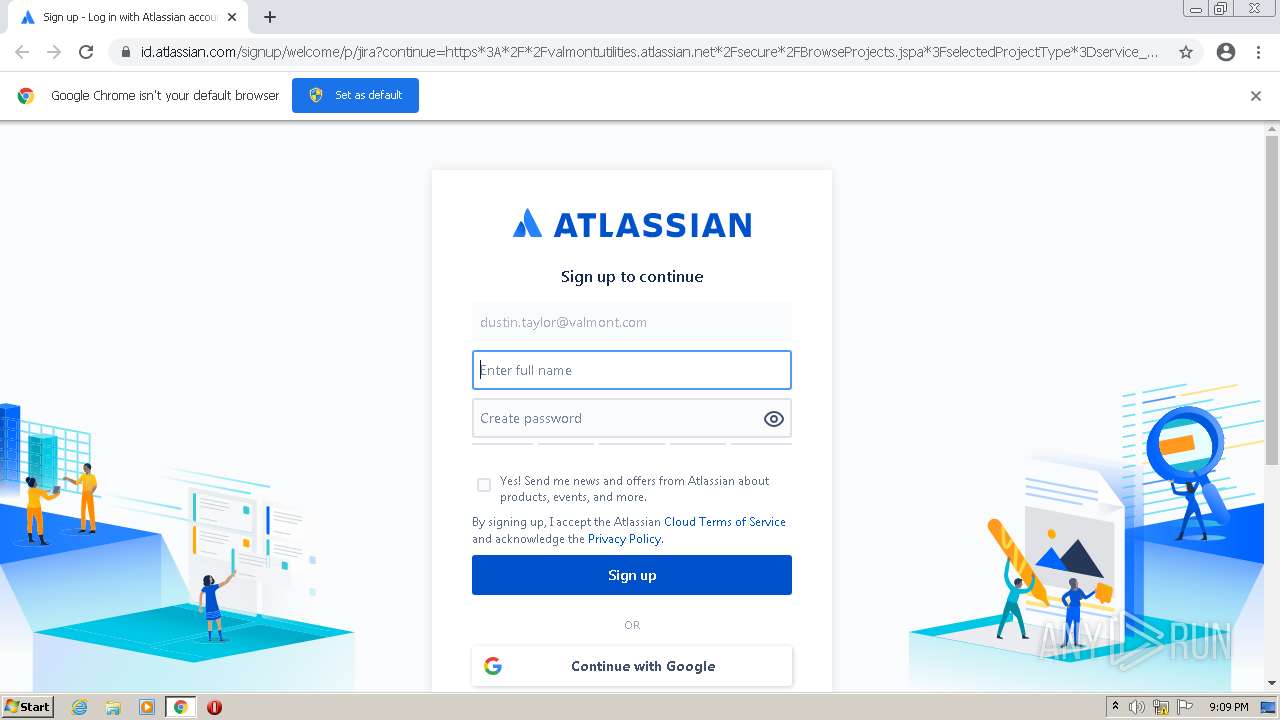
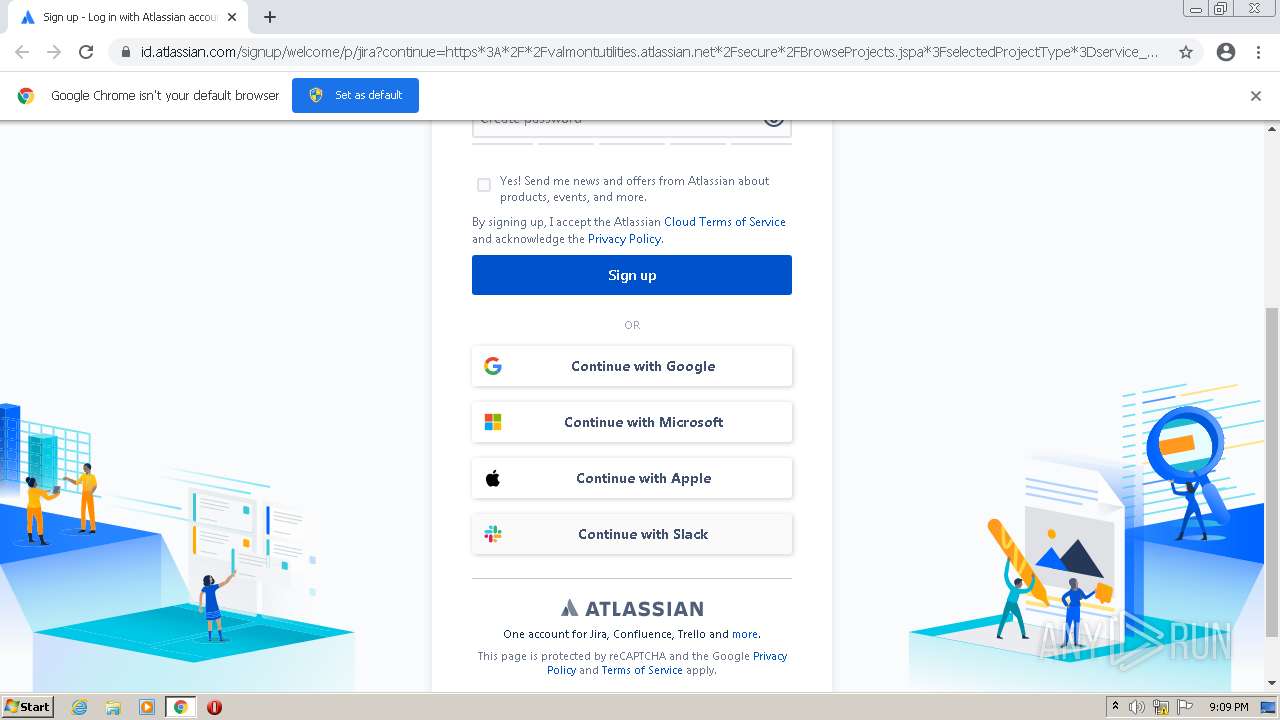
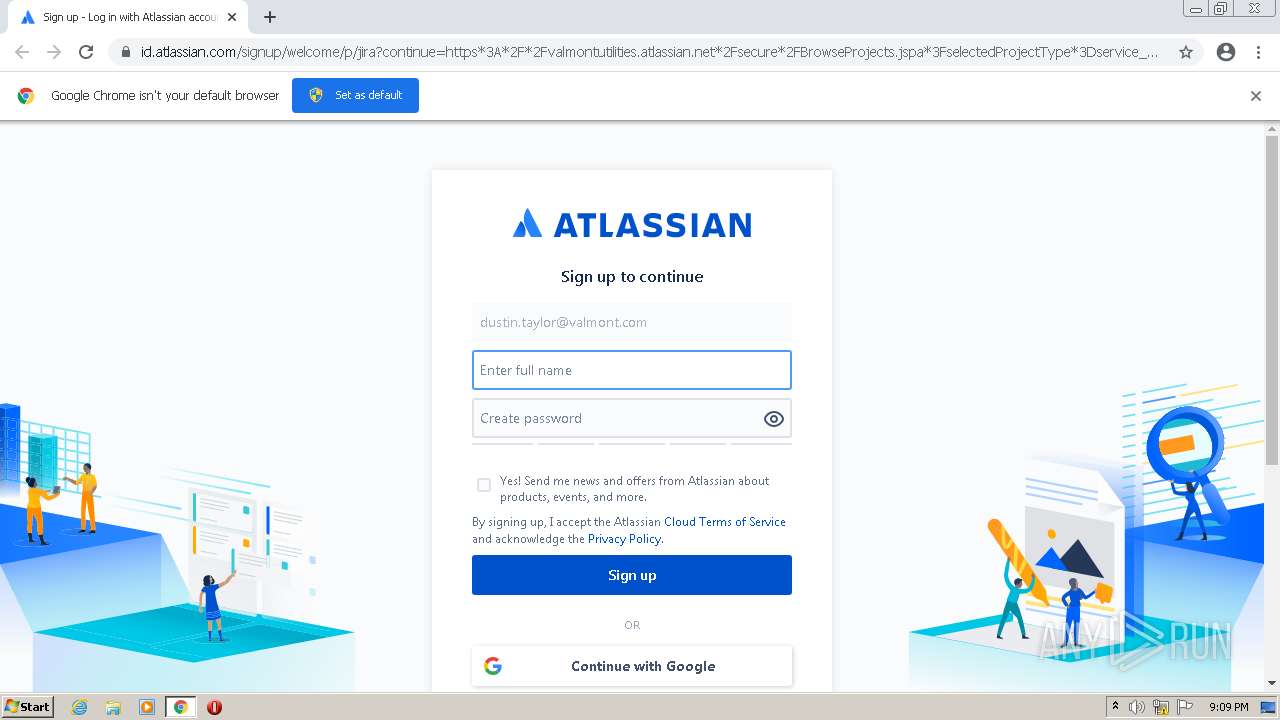
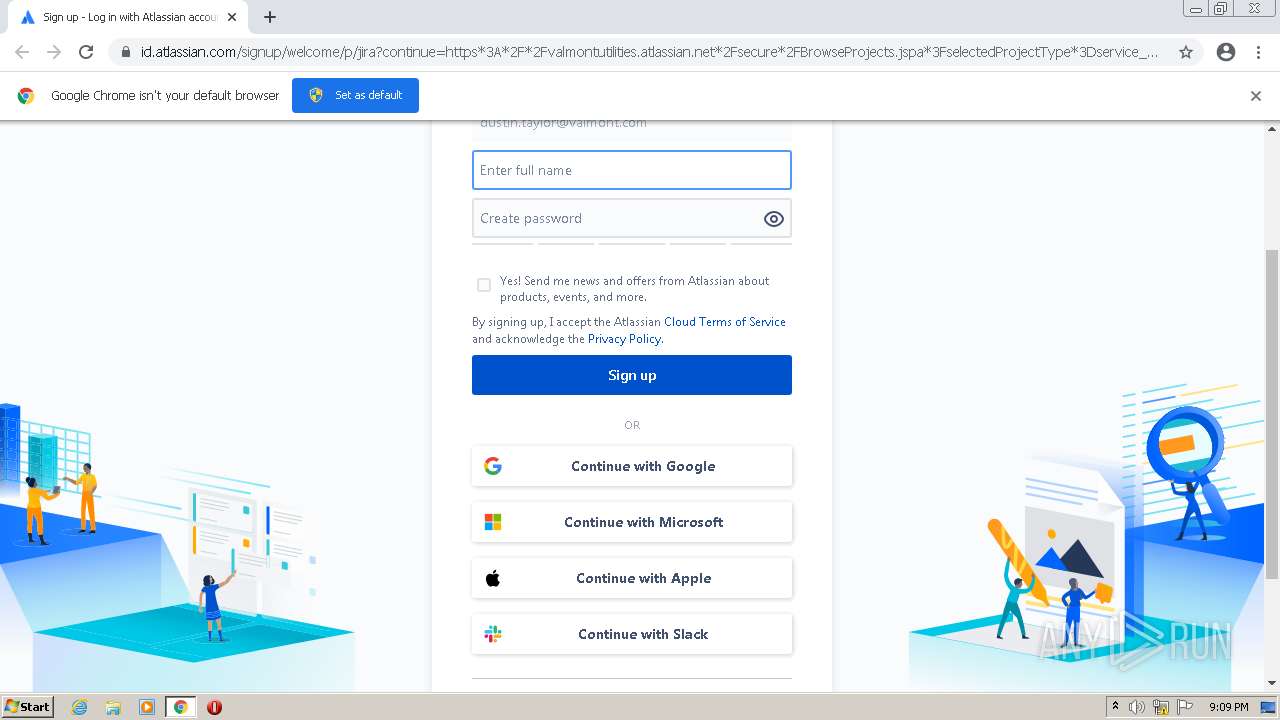
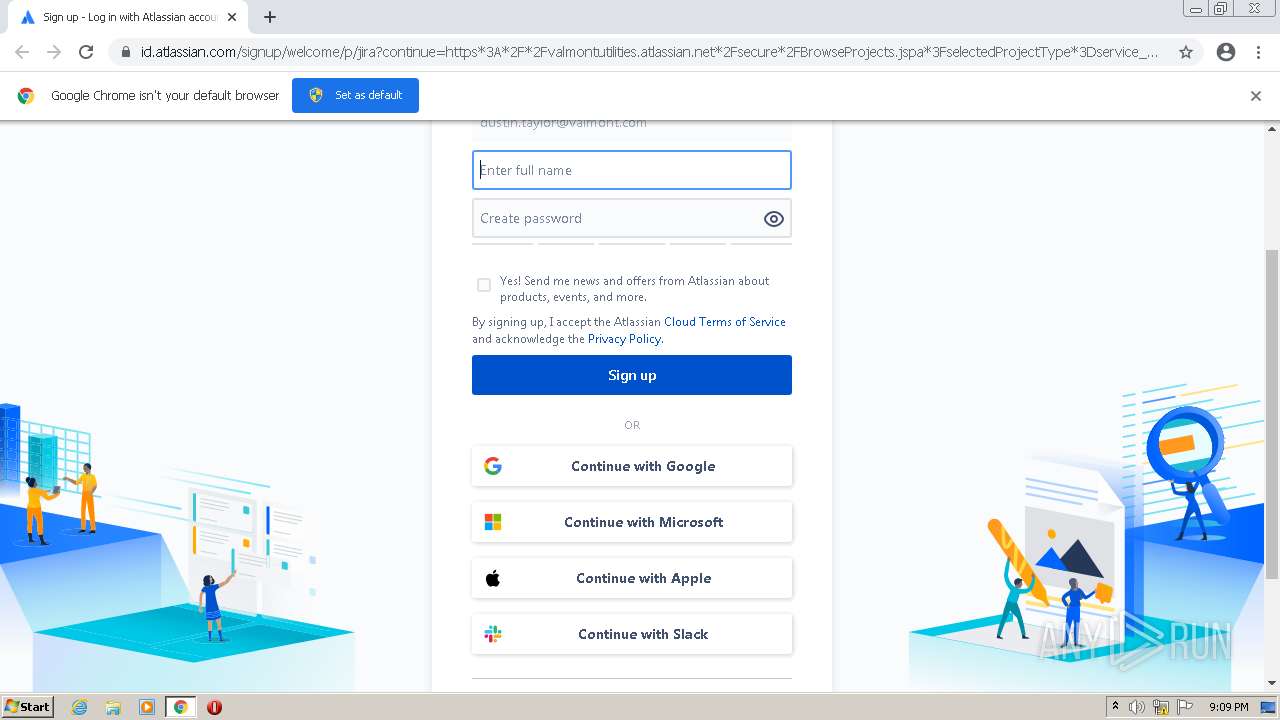
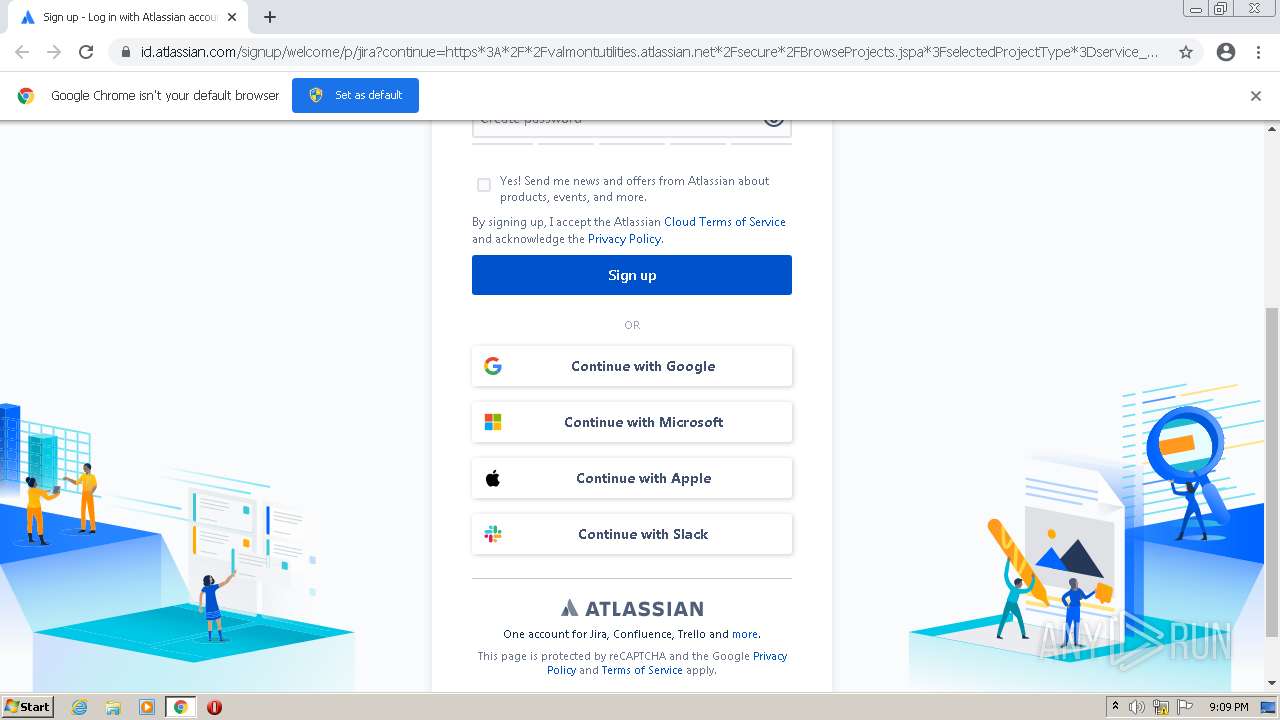
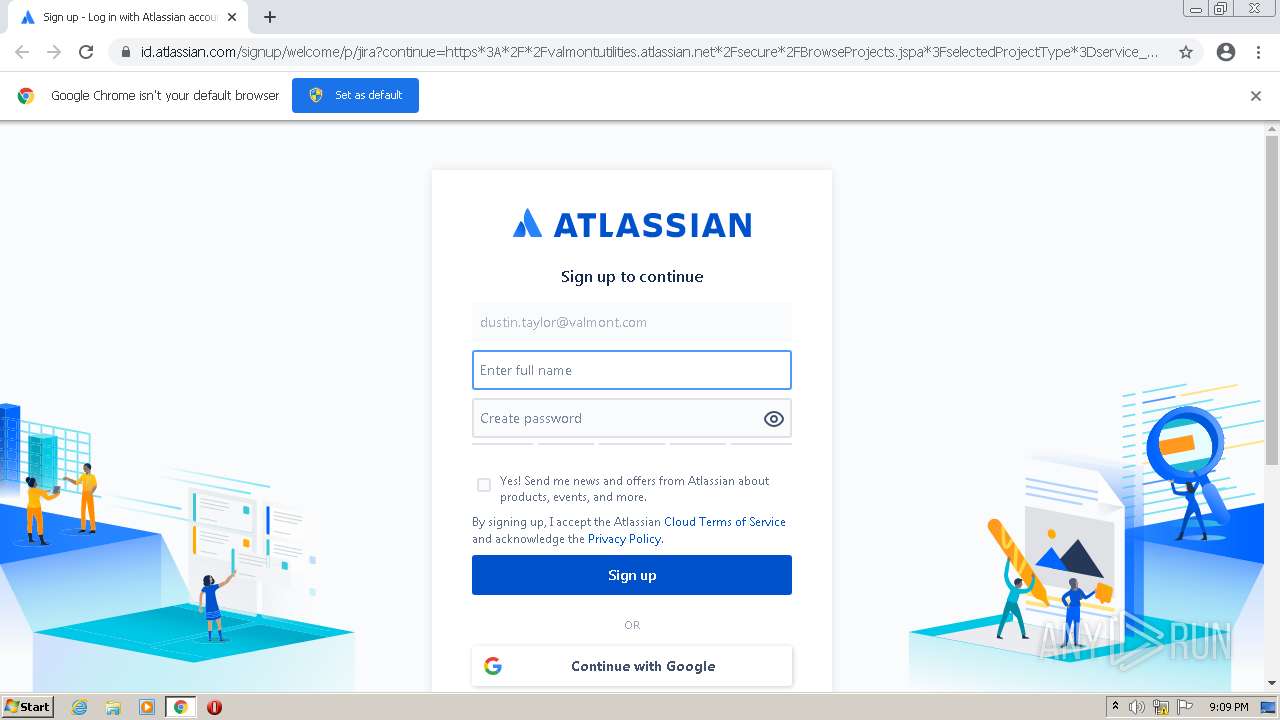
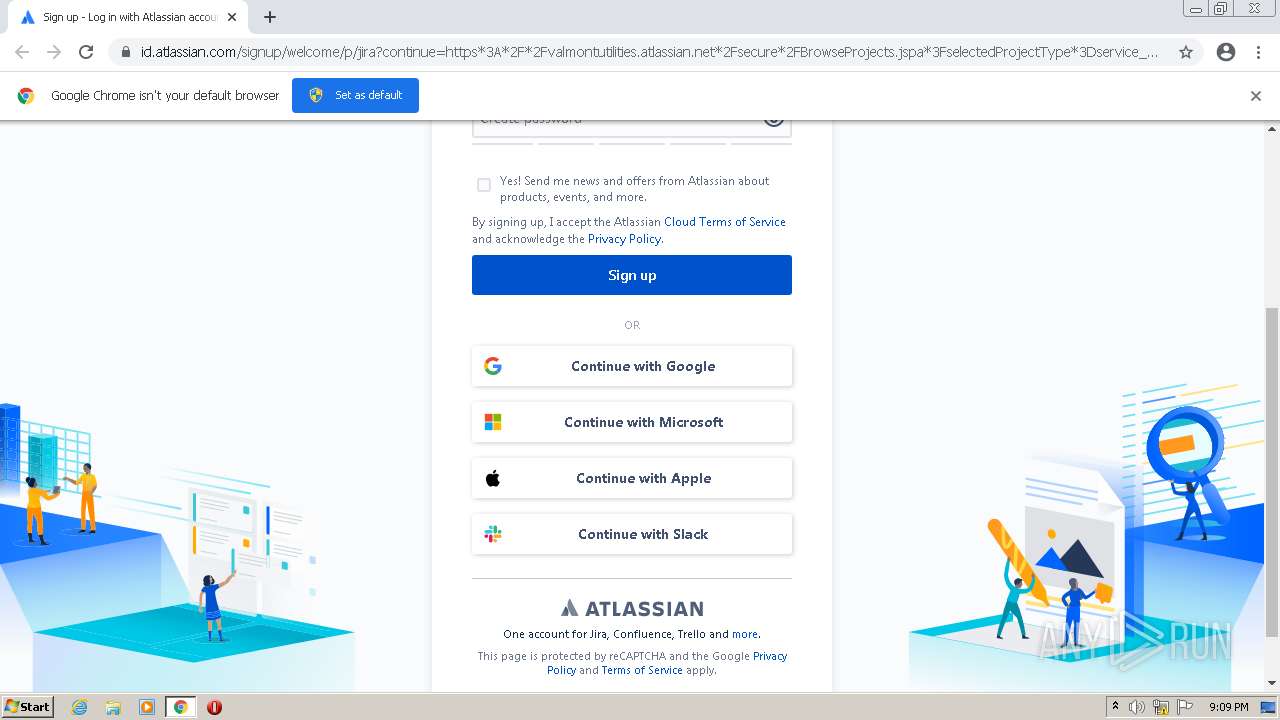
| URL: | https://id.atlassian.com/signup/welcome/p/jira?continue=https*3A*2F*2Fvalmontutilities.atlassian.net*2Fsecure*2FBrowseProjects.jspa*3FselectedProjectType*3Dservice_desk&token=eyJraWQiOiJtaWNyb3NcL3NpZ24taW4tc2VydmljZVwvOTJ1bjU4a2oycTJyYzViMiIsImFsZyI6IlJTMjU2In0.eyJhdWQiOiJsaW5rLXNpZ25hdHVyZS12YWxpZGF0b3IiLCJzdWIiOiJkdXN0aW4udGF5bG9yQHZhbG1vbnQuY29tIiwibmJmIjoxNjgwMjkyNjYwLCJzY29wZSI6IndlbGNvbWUiLCJpc3MiOiJtaWNyb3NcL3NpZ24taW4tc2VydmljZSIsInJlZGlyZWN0VHlwZSI6InJlc3VtZV9zaWdudXAiLCJleHAiOjE2ODA4OTc0NjAsImlhdCI6MTY4MDI5MjY2MCwianRpIjoiMmNiZGEwMDYtZTIyMi00YjU2LWJlOTgtNDU4ZTJkZjY5NGIzIn0.Alyl_KqlLeP9qI1RXcd0ZBezwFyRlbAbI0SbT9xXVvK5r2wfy6cS3IjjHRPcta_KUhSUQcg1i3gHljaZaFCIy3ksYNuXk7I2o3nIJTiaBzvXyFzlpaVZDbE4PhimqVCmFy-EJvleYAyfnNo3gke_RjNk2pihtlZEsAIw_Pf9WfsST7s_haZa6r8LsK7gBMrTsFLTD9bYlJm2vLe9t1sKXIoOSa7-bqg6IPXzR1aFB_FV5TBfImSGyq-_fMPrz94Z3dVPDjd_16a2ExbCNTTT8YQKaiQhoW_bFTYJwWrFRymqshDkRHRygamkR8CRl_wJMQwcx3FtEQkC8CE5hjSLsw&source=f27c2f50974749ac8ffe229ba04f9564__;JSUlJSUlJQ!!DfEmI9Yb!vVJChSfaOPwKzYpNR8UooOyjXVj8mamndEiuNy3RNXCg67ZQ3F547cyq2NH1xP5Sm1MiAb_sZPGqn3TiWCHm_kx2Kb4WwiKvYcFC$ |
| Full analysis: | https://app.any.run/tasks/e44ad765-44c2-4255-8167-e5699fa1465d |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2023, 20:08:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A5CD42A4C08119AD78A73E4CC555220E |
| SHA1: | 1C9A490D4A3D4ABE676CFB259CC3EA911B37BF0F |
| SHA256: | C63D318C0B9DC40CAA2C6FA6BD33EA30B93F55B9B449330C2C05E2292A9AFE3A |
| SSDEEP: | 24:2QWzWJSWmfaP3kqVrs2RQsPGn7+bx7AYDm07SrL38cg/kQP:tWq8n50DQs+nYDUL38R/L |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1016,4996106497170537729,15826102838741553815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=2780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,4996106497170537729,15826102838741553815,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f3dd988,0x6f3dd998,0x6f3dd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,4996106497170537729,15826102838741553815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,4996106497170537729,15826102838741553815,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://id.atlassian.com/signup/welcome/p/jira?continue=https*3A*2F*2Fvalmontutilities.atlassian.net*2Fsecure*2FBrowseProjects.jspa*3FselectedProjectType*3Dservice_desk&token=eyJraWQiOiJtaWNyb3NcL3NpZ24taW4tc2VydmljZVwvOTJ1bjU4a2oycTJyYzViMiIsImFsZyI6IlJTMjU2In0.eyJhdWQiOiJsaW5rLXNpZ25hdHVyZS12YWxpZGF0b3IiLCJzdWIiOiJkdXN0aW4udGF5bG9yQHZhbG1vbnQuY29tIiwibmJmIjoxNjgwMjkyNjYwLCJzY29wZSI6IndlbGNvbWUiLCJpc3MiOiJtaWNyb3NcL3NpZ24taW4tc2VydmljZSIsInJlZGlyZWN0VHlwZSI6InJlc3VtZV9zaWdudXAiLCJleHAiOjE2ODA4OTc0NjAsImlhdCI6MTY4MDI5MjY2MCwianRpIjoiMmNiZGEwMDYtZTIyMi00YjU2LWJlOTgtNDU4ZTJkZjY5NGIzIn0.Alyl_KqlLeP9qI1RXcd0ZBezwFyRlbAbI0SbT9xXVvK5r2wfy6cS3IjjHRPcta_KUhSUQcg1i3gHljaZaFCIy3ksYNuXk7I2o3nIJTiaBzvXyFzlpaVZDbE4PhimqVCmFy-EJvleYAyfnNo3gke_RjNk2pihtlZEsAIw_Pf9WfsST7s_haZa6r8LsK7gBMrTsFLTD9bYlJm2vLe9t1sKXIoOSa7-bqg6IPXzR1aFB_FV5TBfImSGyq-_fMPrz94Z3dVPDjd_16a2ExbCNTTT8YQKaiQhoW_bFTYJwWrFRymqshDkRHRygamkR8CRl_wJMQwcx3FtEQkC8CE5hjSLsw&source=f27c2f50974749ac8ffe229ba04f9564__;JSUlJSUlJQ!!DfEmI9Yb!vVJChSfaOPwKzYpNR8UooOyjXVj8mamndEiuNy3RNXCg67ZQ3F547cyq2NH1xP5Sm1MiAb_sZPGqn3TiWCHm_kx2Kb4WwiKvYcFCf7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,4996106497170537729,15826102838741553815,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1016,4996106497170537729,15826102838741553815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,4996106497170537729,15826102838741553815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,4996106497170537729,15826102838741553815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1664 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
24 388
Read events
24 230
Write events
158
Delete events
0
Modification events
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
0
Suspicious files
34
Text files
124
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-64273DD8-900.pma | — | |
MD5:— | SHA256:— | |||
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e3dbe50a-5a0e-4238-961b-17394794f551.tmp | text | |
MD5:— | SHA256:— | |||
| 1204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2506a3.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF25024d.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF25025d.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF2506a3.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
31
DNS requests
19
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3324 | chrome.exe | 216.58.212.174:443 | clients2.google.com | GOOGLE | US | whitelisted |
3324 | chrome.exe | 142.250.185.97:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3324 | chrome.exe | 142.250.186.131:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3324 | chrome.exe | 44.235.148.141:443 | api.segment.io | AMAZON-02 | US | unknown |
3324 | chrome.exe | 142.250.185.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3324 | chrome.exe | 18.66.147.45:443 | metal.prod.atl-paas.net | AMAZON-02 | US | suspicious |
3324 | chrome.exe | 35.188.42.15:443 | sentry.io | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3324 | chrome.exe | 34.193.138.129:443 | t.castle.io | AMAZON-AES | US | unknown |
3324 | chrome.exe | 142.250.185.131:443 | update.googleapis.com | GOOGLE | US | whitelisted |
3324 | chrome.exe | 185.166.143.26:443 | id.atlassian.com | AMAZON-02 | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
id.atlassian.com |
| shared |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
aid-frontend.prod.atl-paas.net |
| whitelisted |
t.castle.io |
| whitelisted |
metal.prod.atl-paas.net |
| whitelisted |
api.segment.io |
| whitelisted |
sentry.io |
| whitelisted |