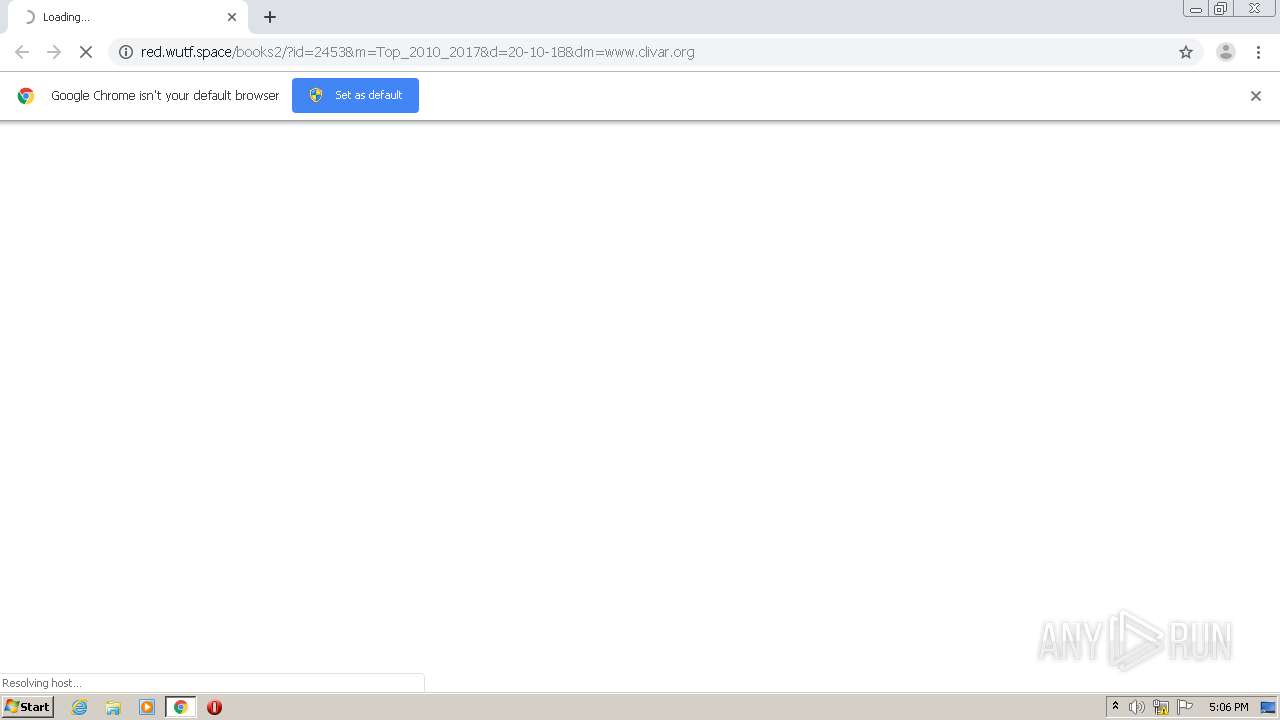
| URL: | http://red.wutf.space/books2/?id=2453&m=Top_2010_2017&d=20-10-18&dm=www.clivar.org |
| Full analysis: | https://app.any.run/tasks/dde81152-57dc-49cb-9f72-8558b35e0b6b |
| Verdict: | No threats detected |
| Analysis date: | December 08, 2020, 17:06:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6A23669892C38A78CEDD5A9E2A3EA469 |
| SHA1: | 065706B8ECB8049092E3401DF520BBBF35CED251 |
| SHA256: | C6336FD1E74CA1C589D8A317C37B3813AA30C7B68B7C6F13F79C3B376CE03177 |
| SSDEEP: | 3:N1KMRQwD1FVuV6Xx4ptdImMC:CMRF2VttGC |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2592)
- chrome.exe (PID: 2616)
Creates files in the user directory
- chrome.exe (PID: 2616)
Application launched itself
- chrome.exe (PID: 2616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,12707923133431722553,706226903478563278,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15819612811042721118 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2612 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,12707923133431722553,706226903478563278,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4703061488705512897 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,12707923133431722553,706226903478563278,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3186383097556583505 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,12707923133431722553,706226903478563278,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4362276608134623270 --mojo-platform-channel-handle=3412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,12707923133431722553,706226903478563278,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=290035011596313312 --mojo-platform-channel-handle=1328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://red.wutf.space/books2/?id=2453&m=Top_2010_2017&d=20-10-18&dm=www.clivar.org" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,12707923133431722553,706226903478563278,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11829610251388160296 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,12707923133431722553,706226903478563278,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11286876282952602957 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,12707923133431722553,706226903478563278,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4029520869202641588 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
598
Read events
537
Write events
58
Delete events
3
Modification events
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2616-13251920797956250 |
Value: 259 | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
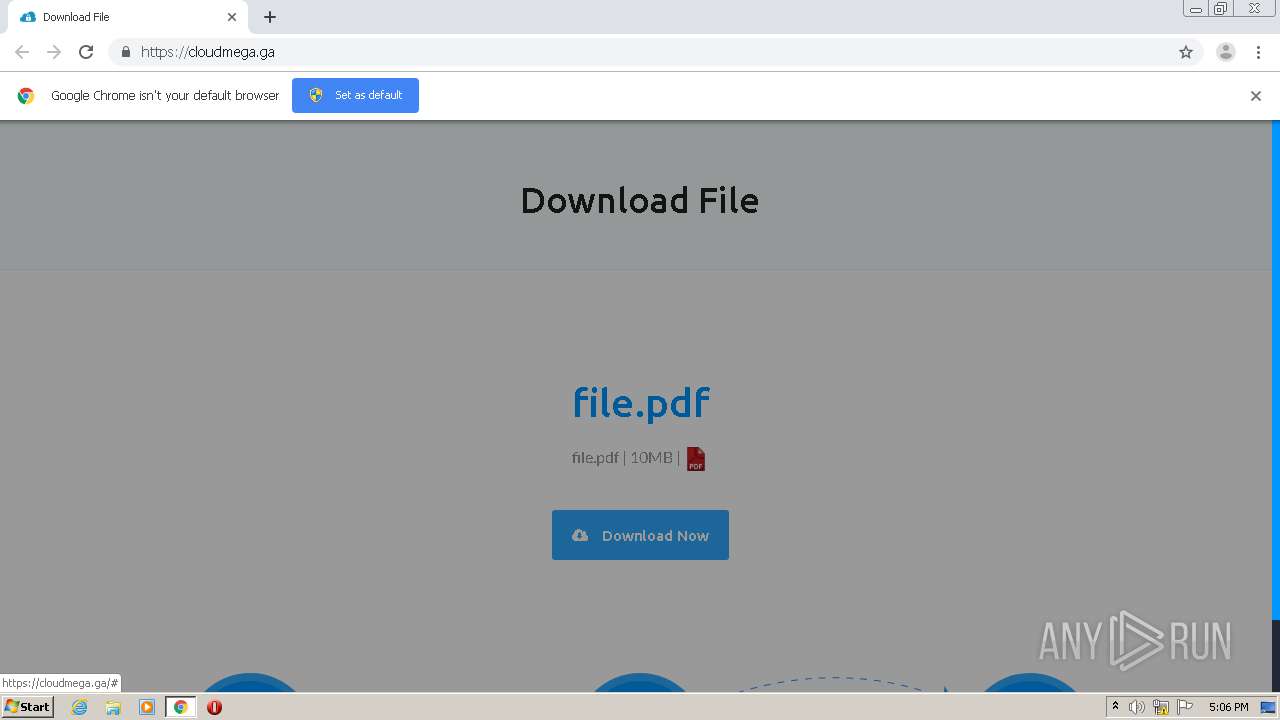
Suspicious files
28
Text files
74
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FCFB29E-A38.pma | — | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ecda5dbc-41f7-4f3e-b4f4-f98c379f6bcd.tmp | — | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF15ab7c.TMP | text | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF15ab4d.TMP | text | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15acf3.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
42
DNS requests
25
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
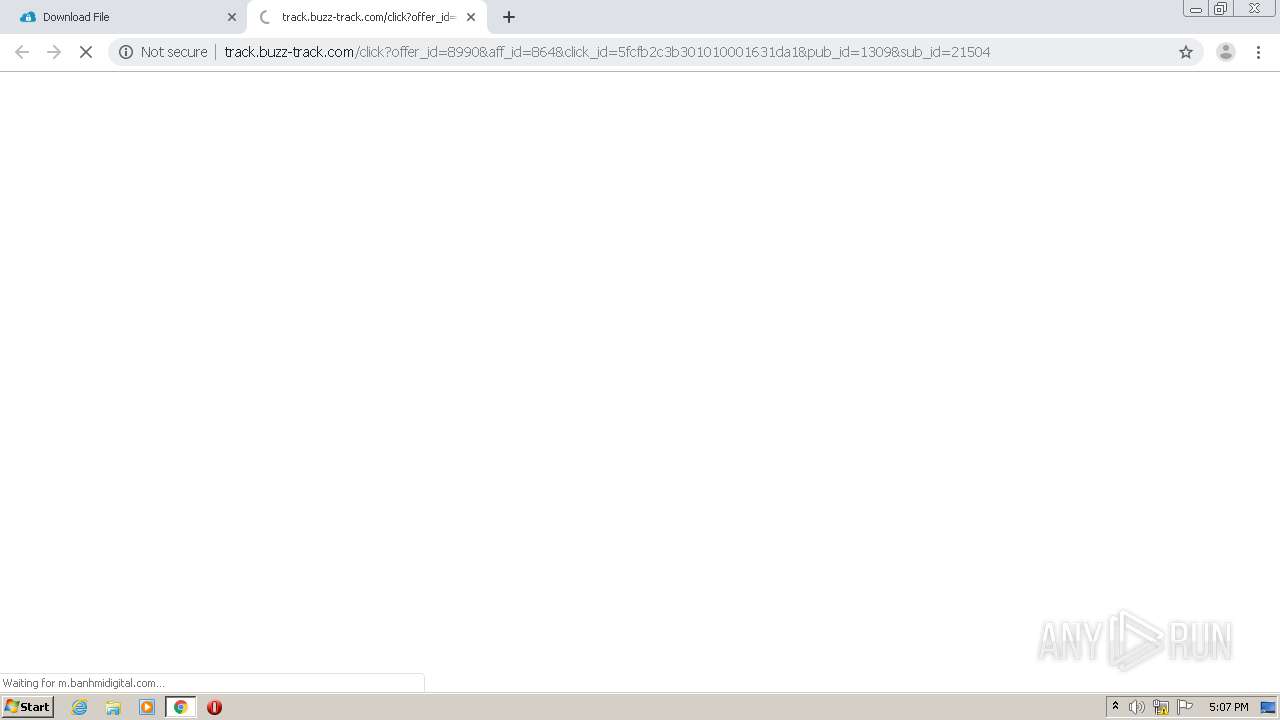
2592 | chrome.exe | GET | 302 | 104.27.163.122:80 | http://red.wutf.space/books2/?id=2453&m=Top_2010_2017&d=20-10-18&dm=www.clivar.org | US | — | — | suspicious |
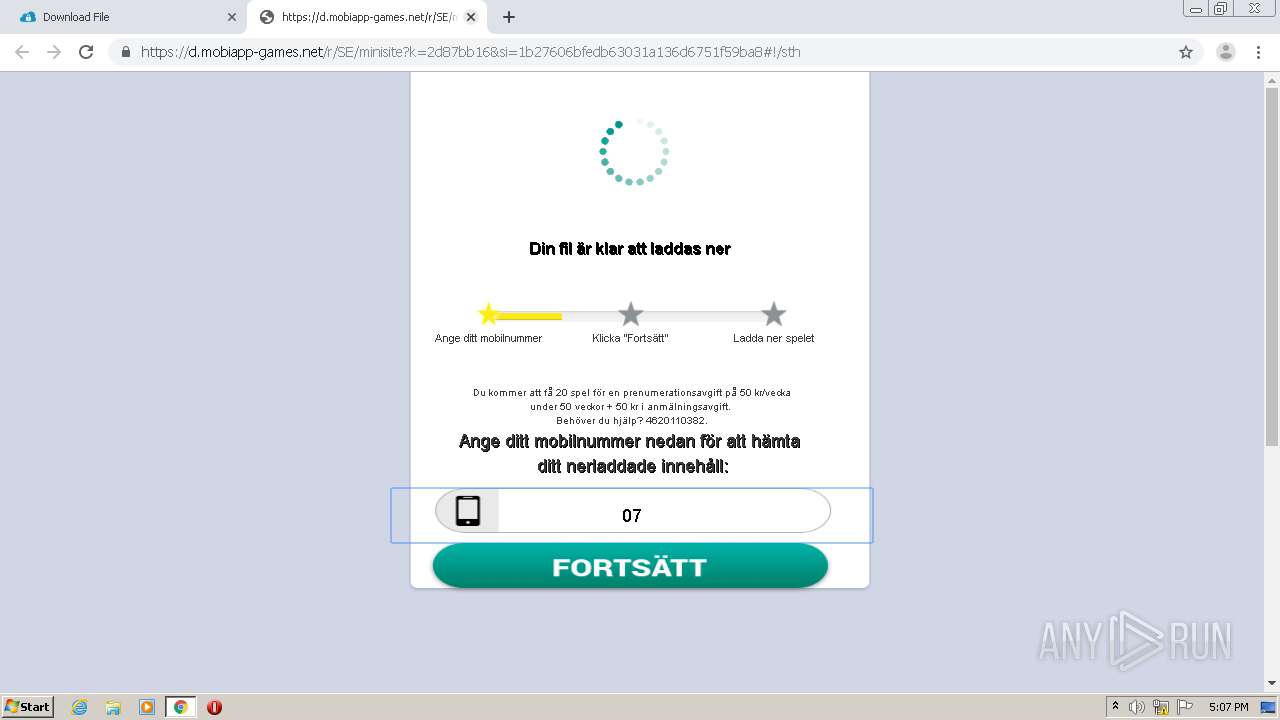
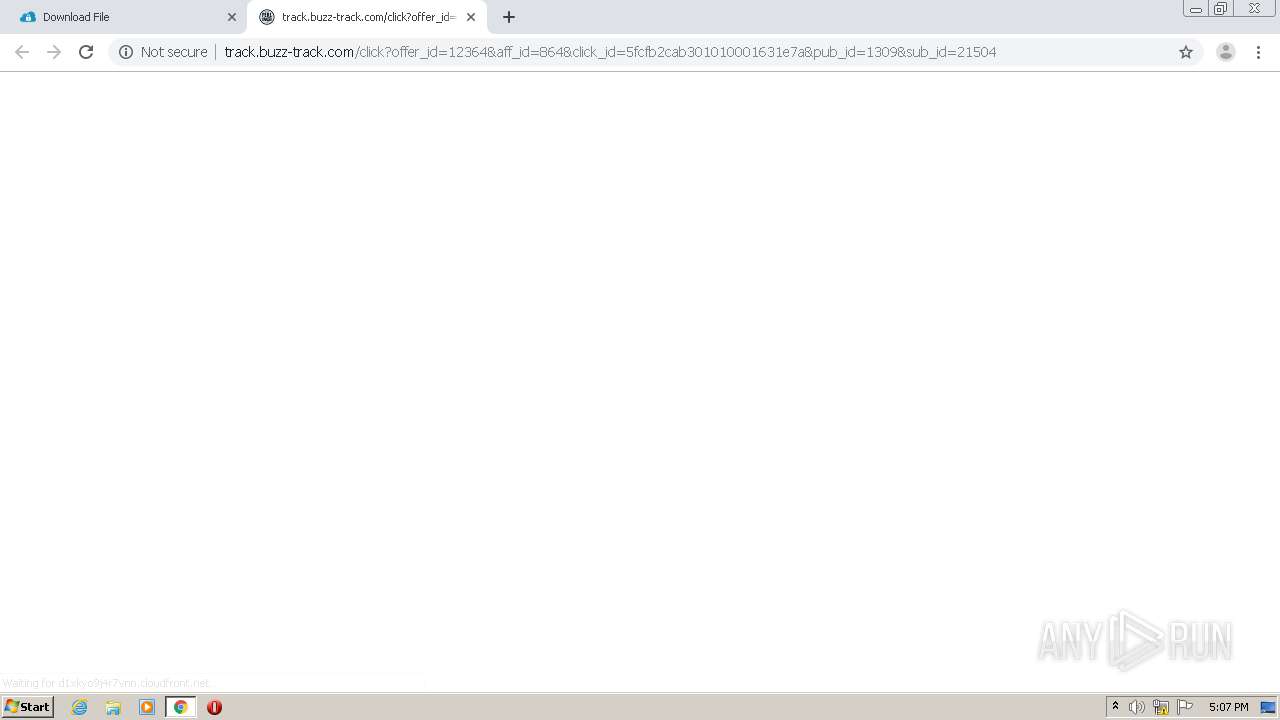
2592 | chrome.exe | GET | 200 | 104.27.161.37:80 | http://track.buzz-track.com/click?offer_id=8990&aff_id=864&click_id=5fcfb2c3b301010001631da1&pub_id=1309&sub_id=21504 | US | html | 214 b | suspicious |
2592 | chrome.exe | GET | 200 | 104.27.161.37:80 | http://track.buzz-track.com/click?offer_id=12364&aff_id=864&click_id=5fcfb2cab301010001631e7a&pub_id=1309&sub_id=21504 | US | binary | 20 b | suspicious |
2592 | chrome.exe | GET | 200 | 104.27.161.37:80 | http://track.buzz-track.com/favicon.ico | US | image | 1.02 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2592 | chrome.exe | 104.27.163.122:80 | red.wutf.space | Cloudflare Inc | US | shared |
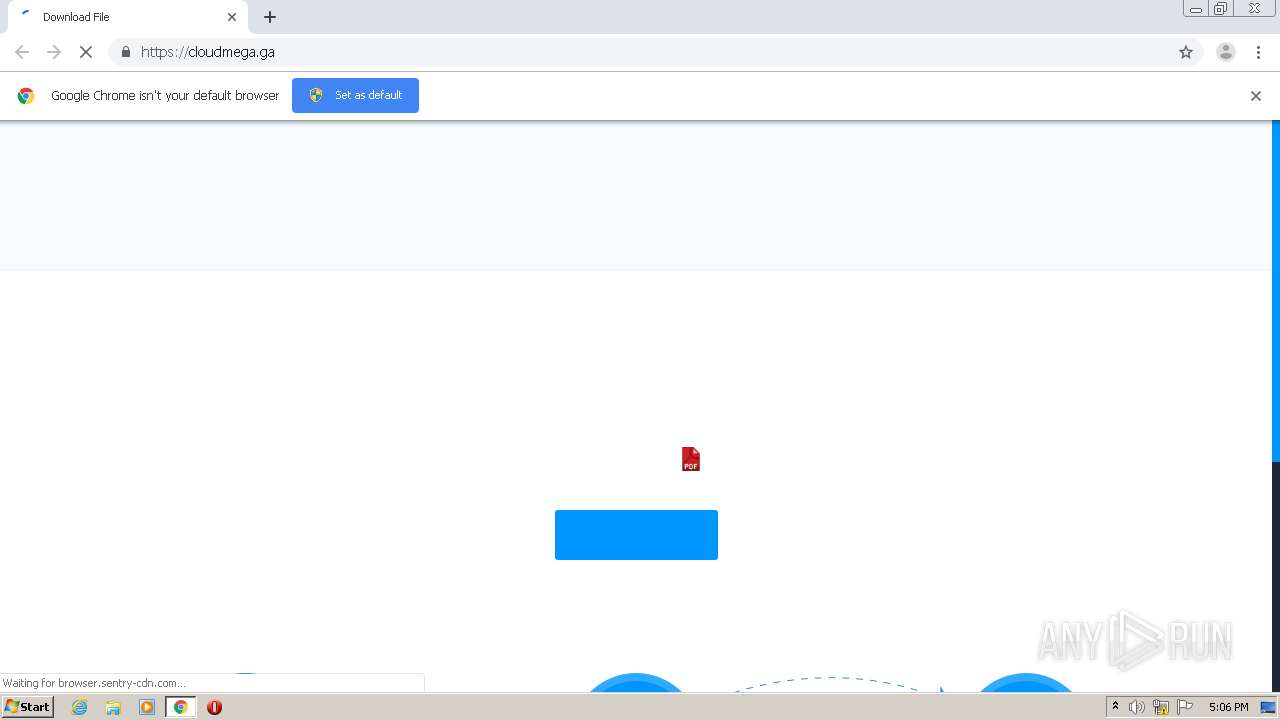
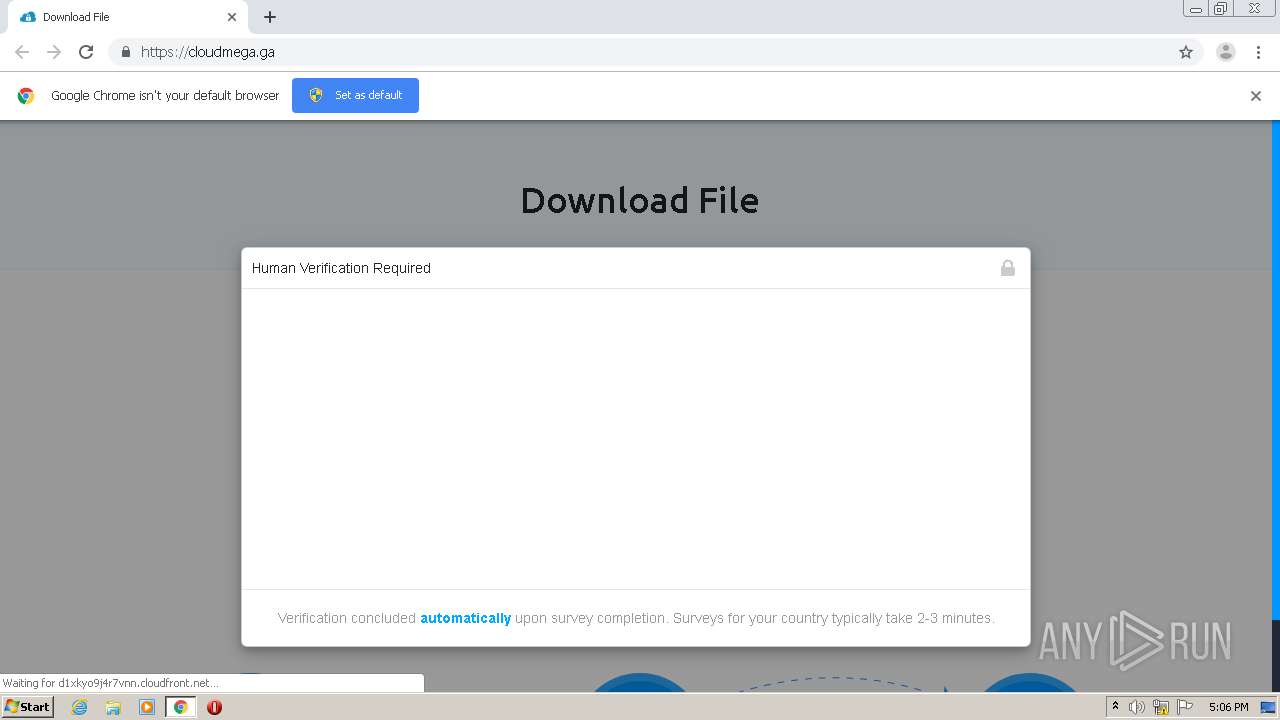
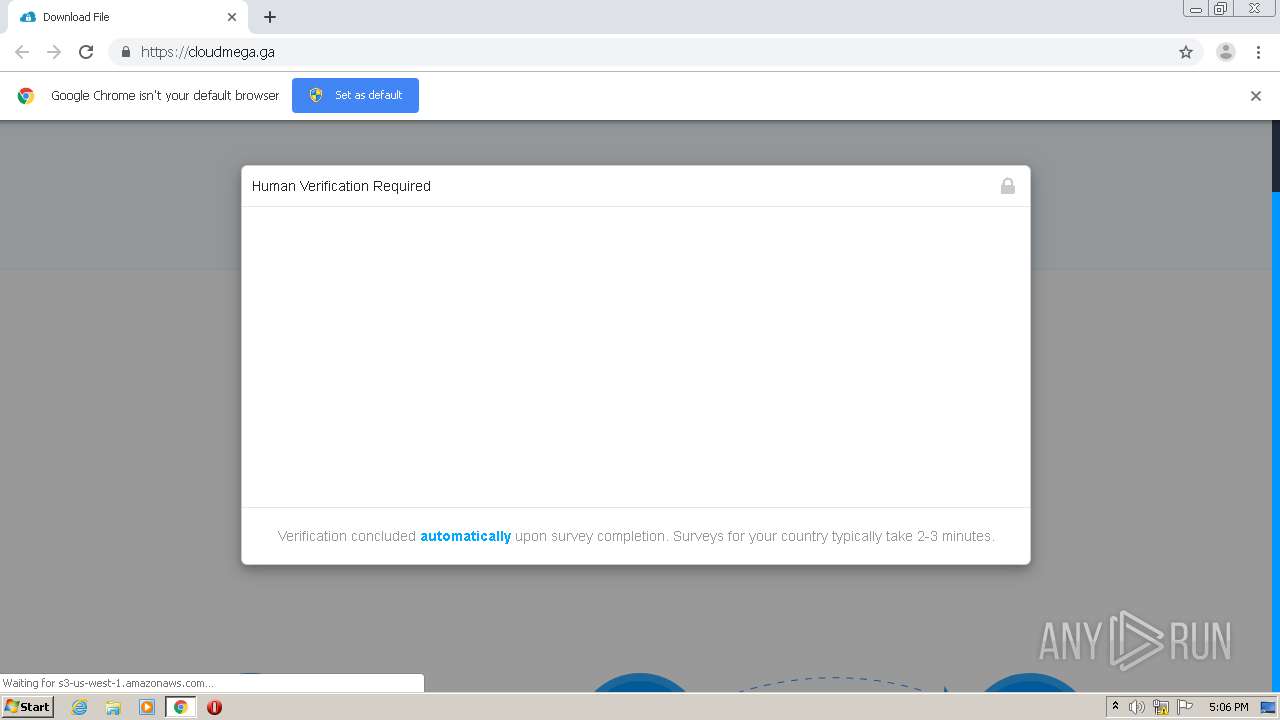
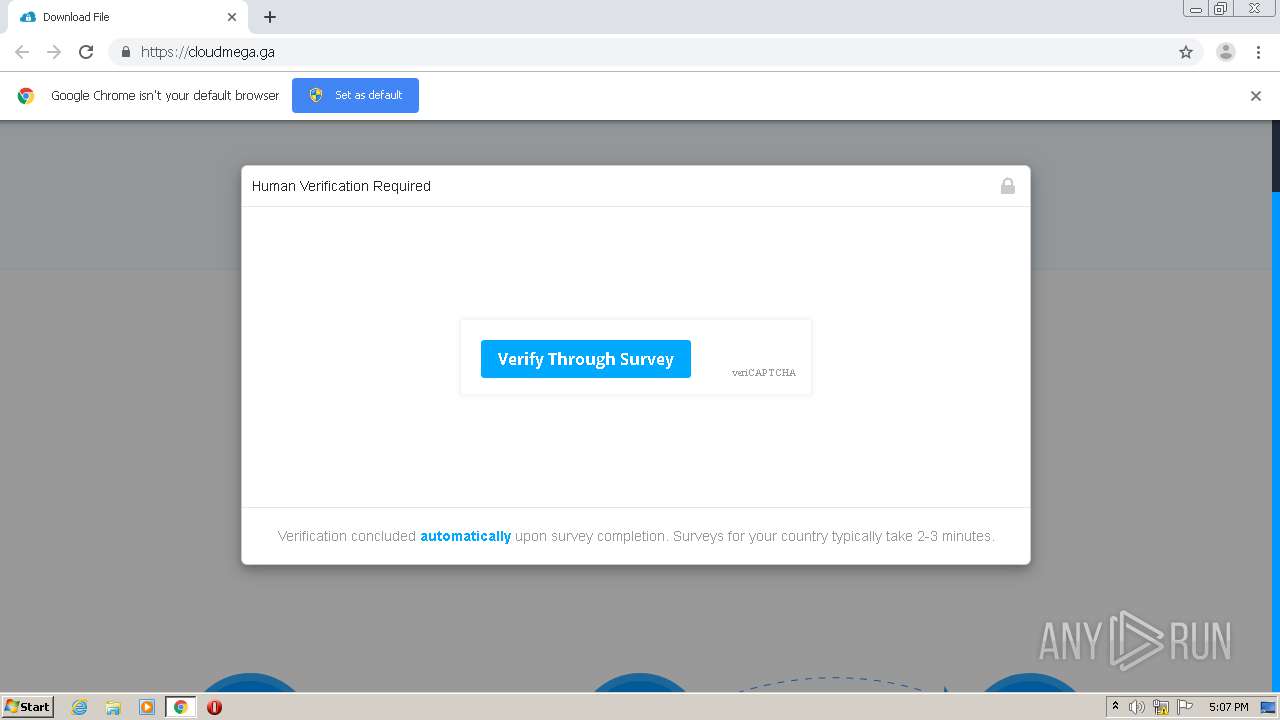
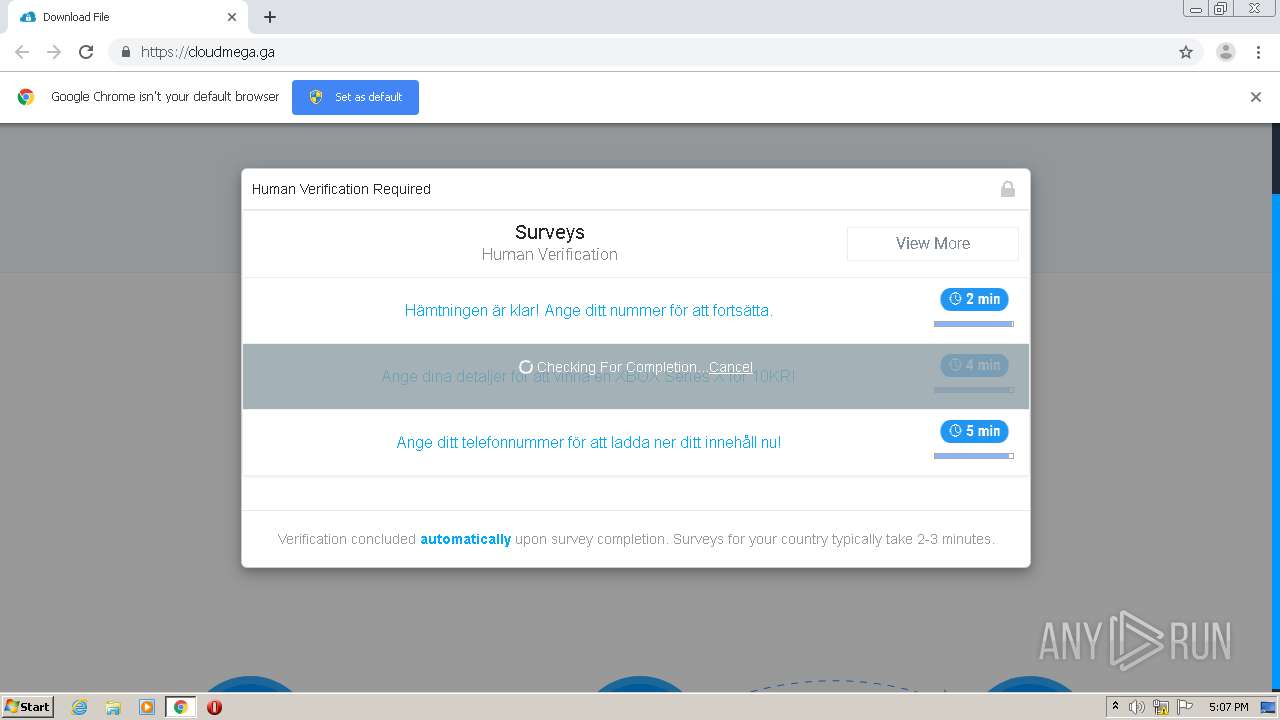
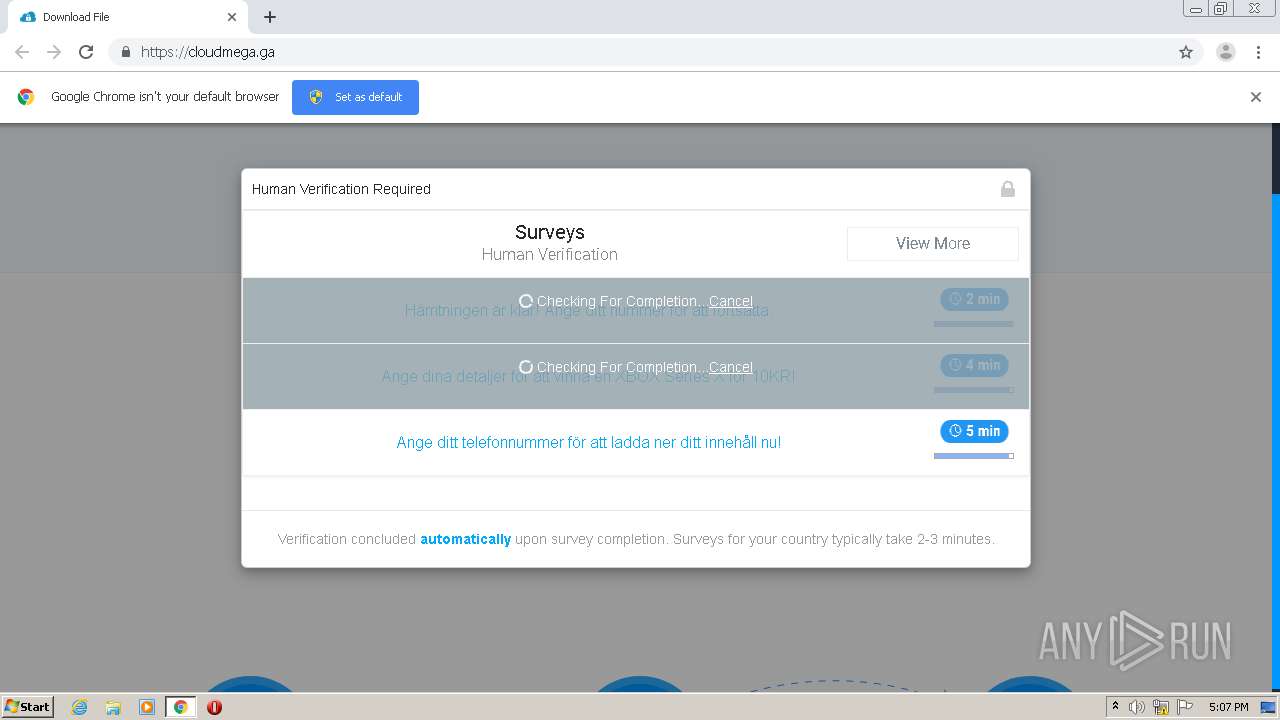
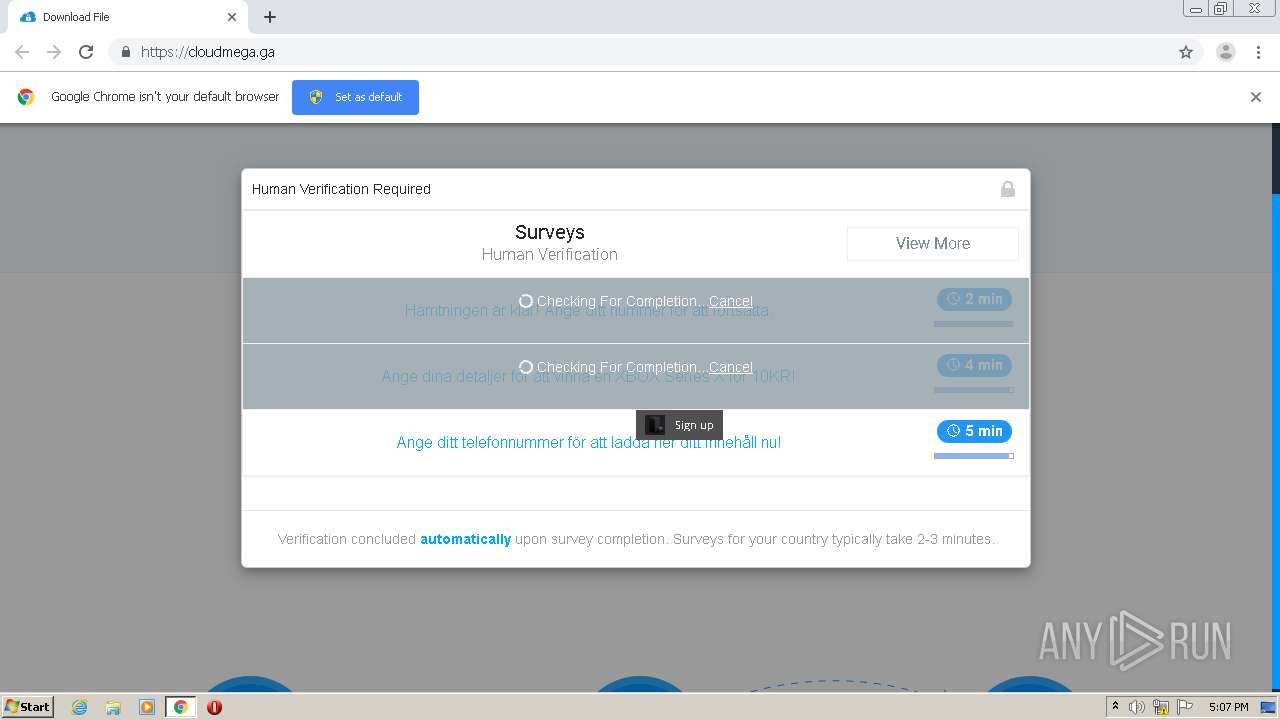
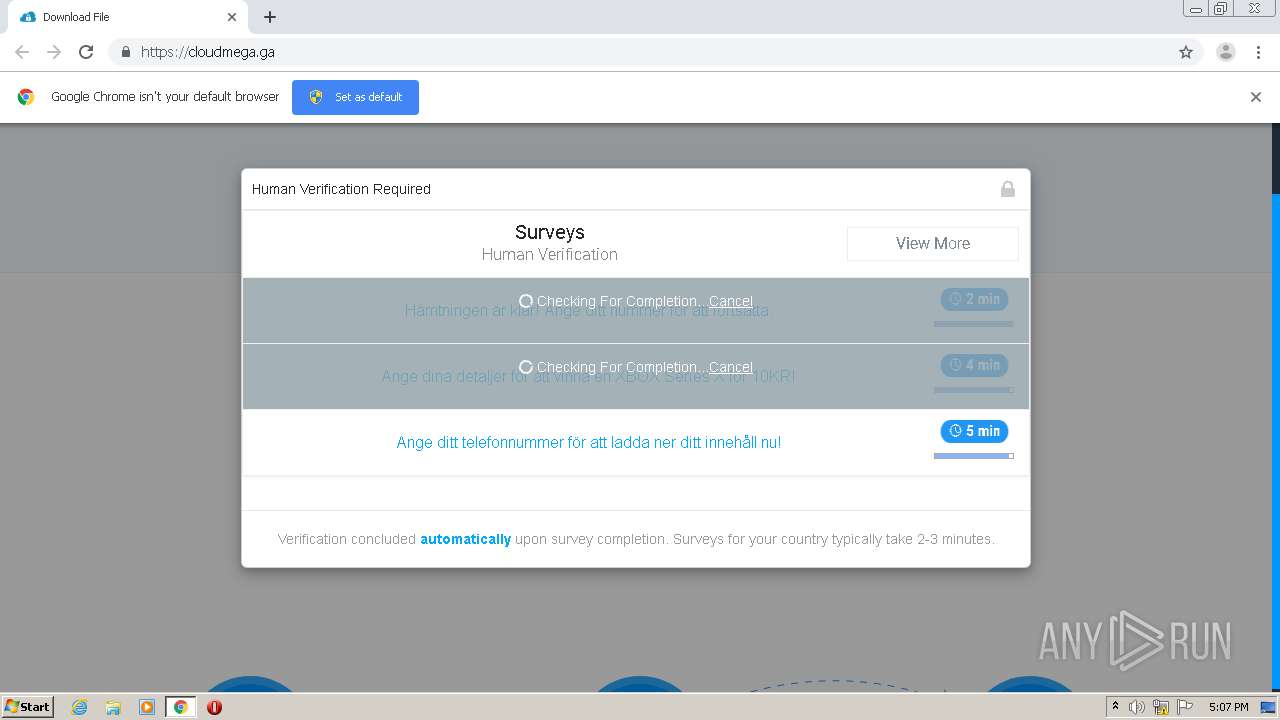
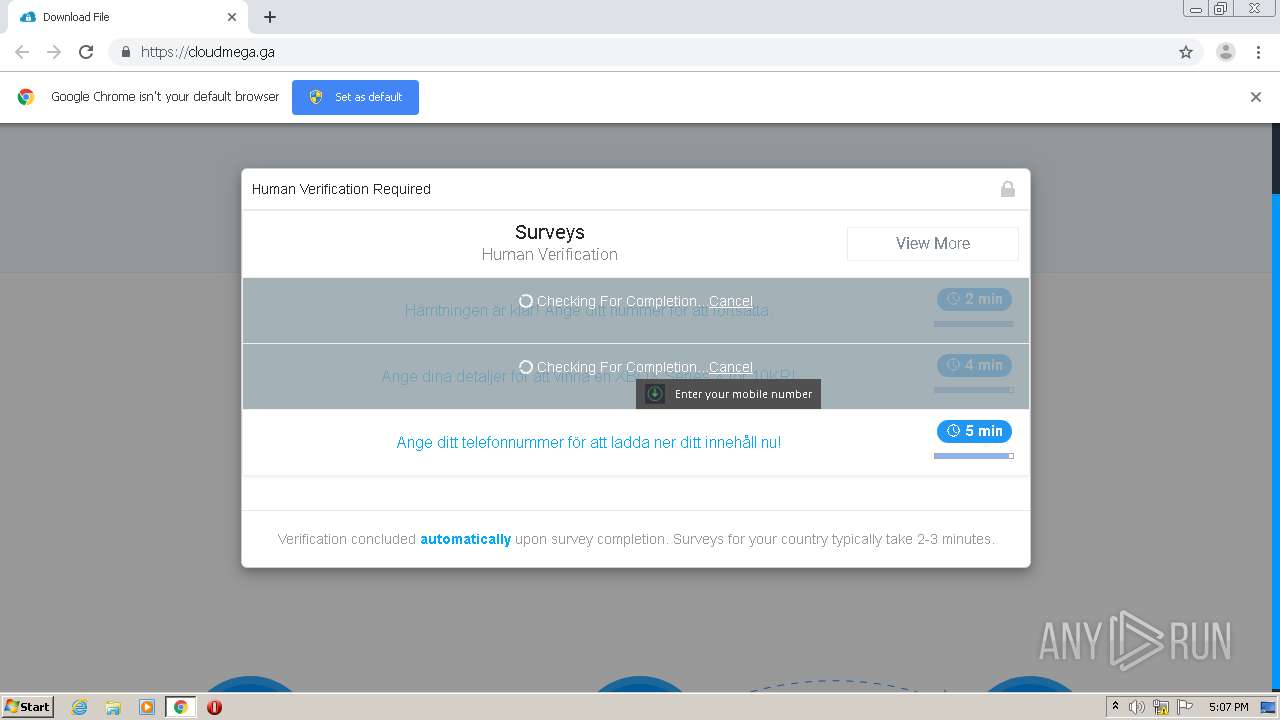
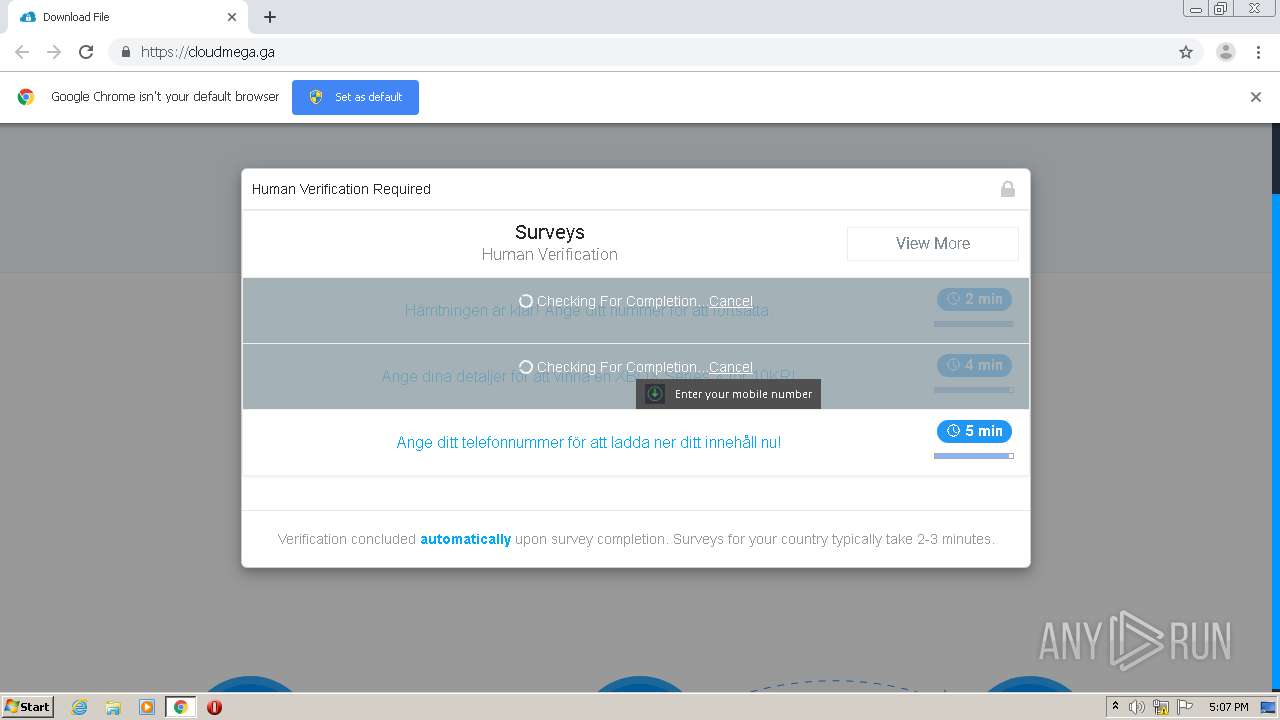
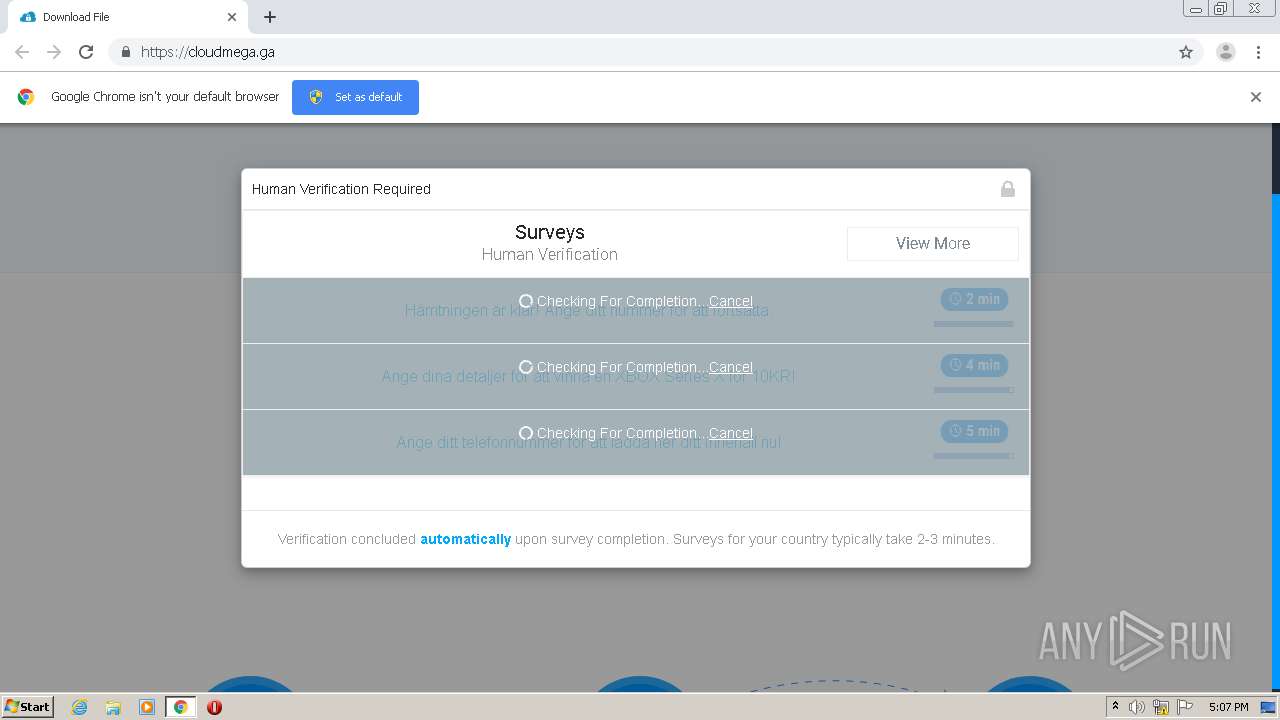
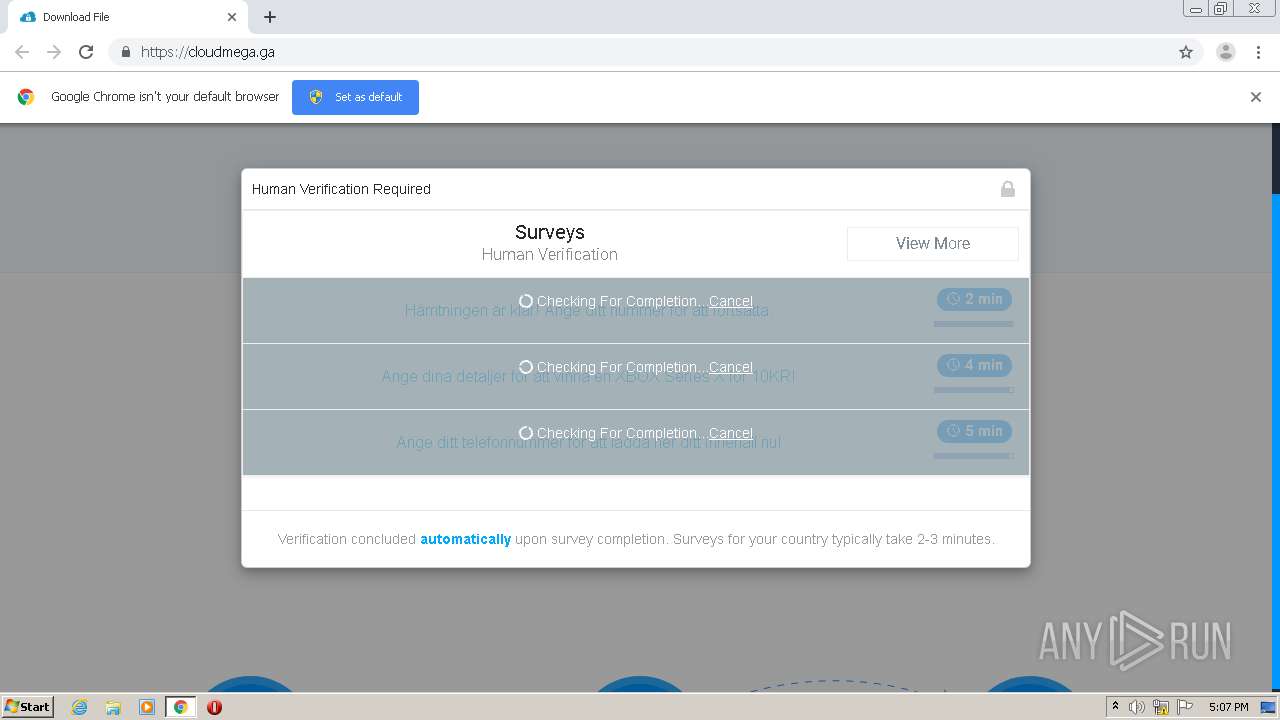
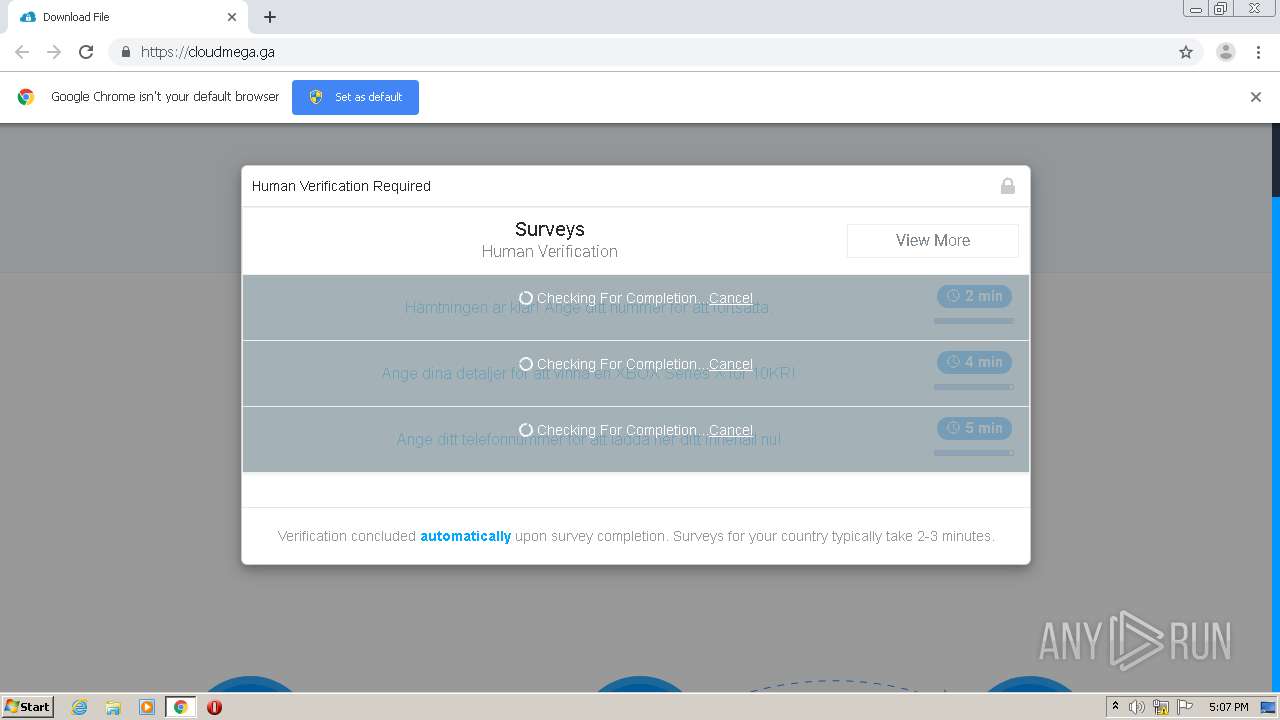
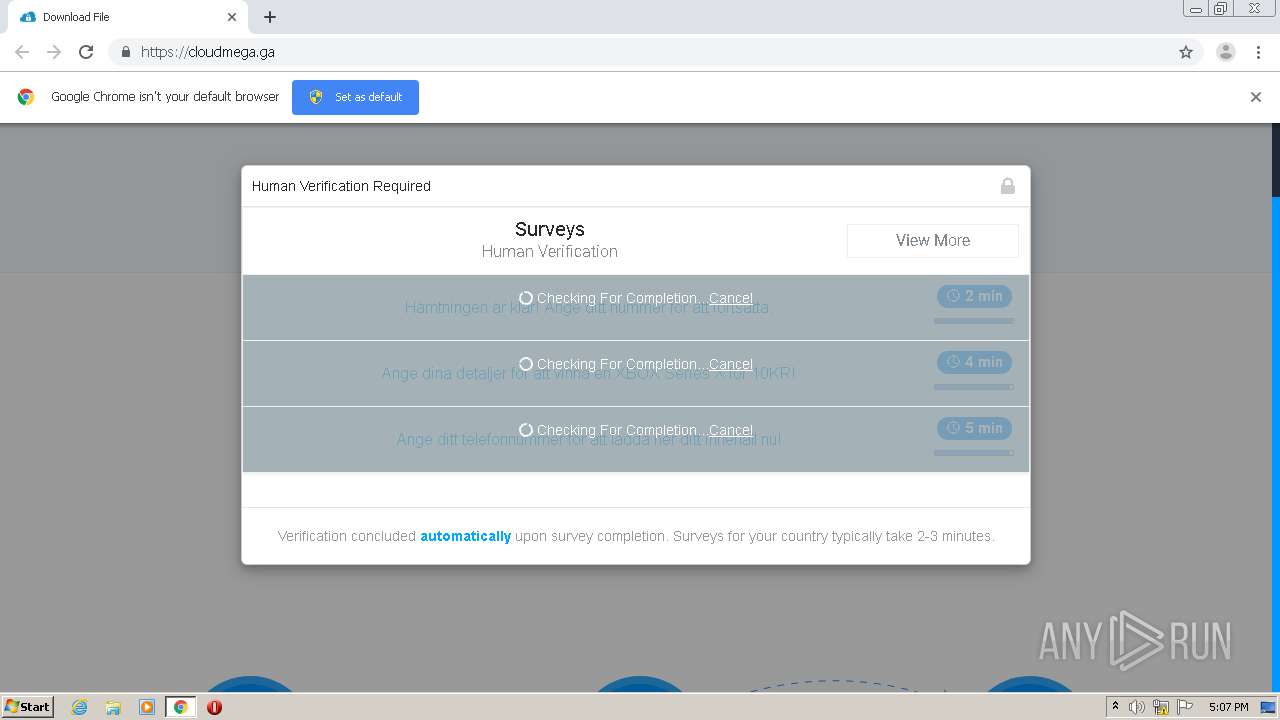
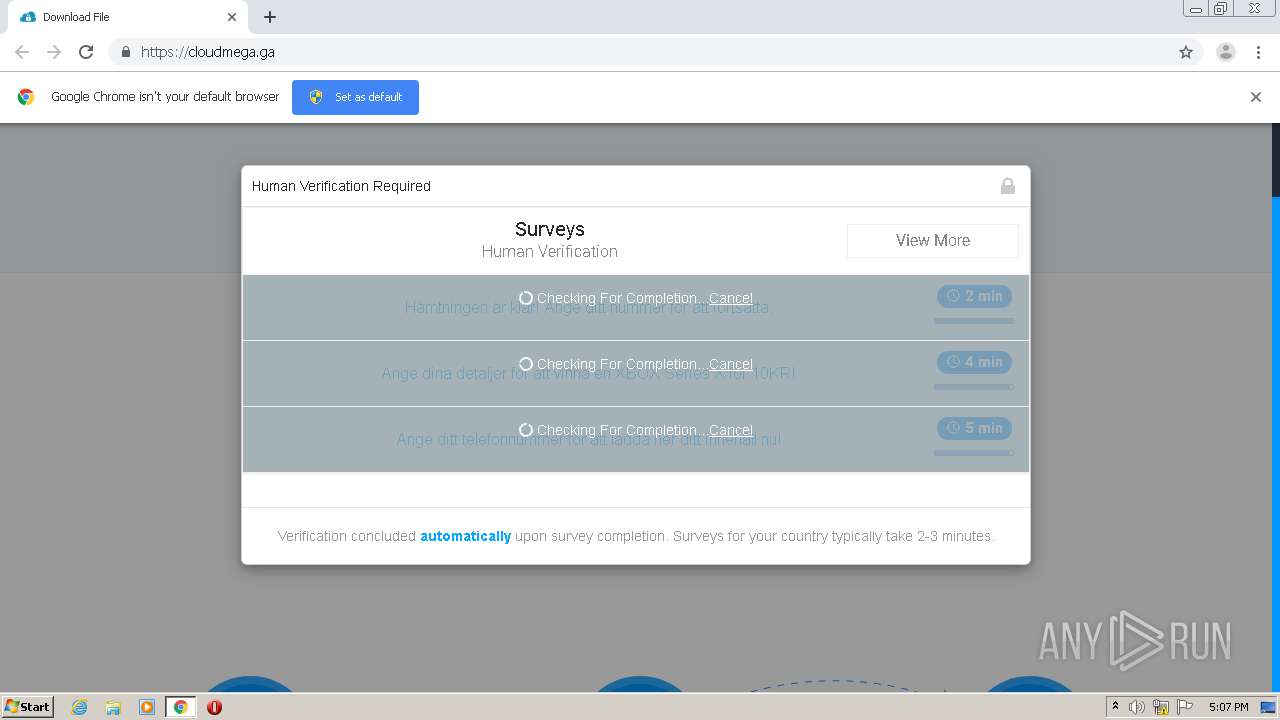
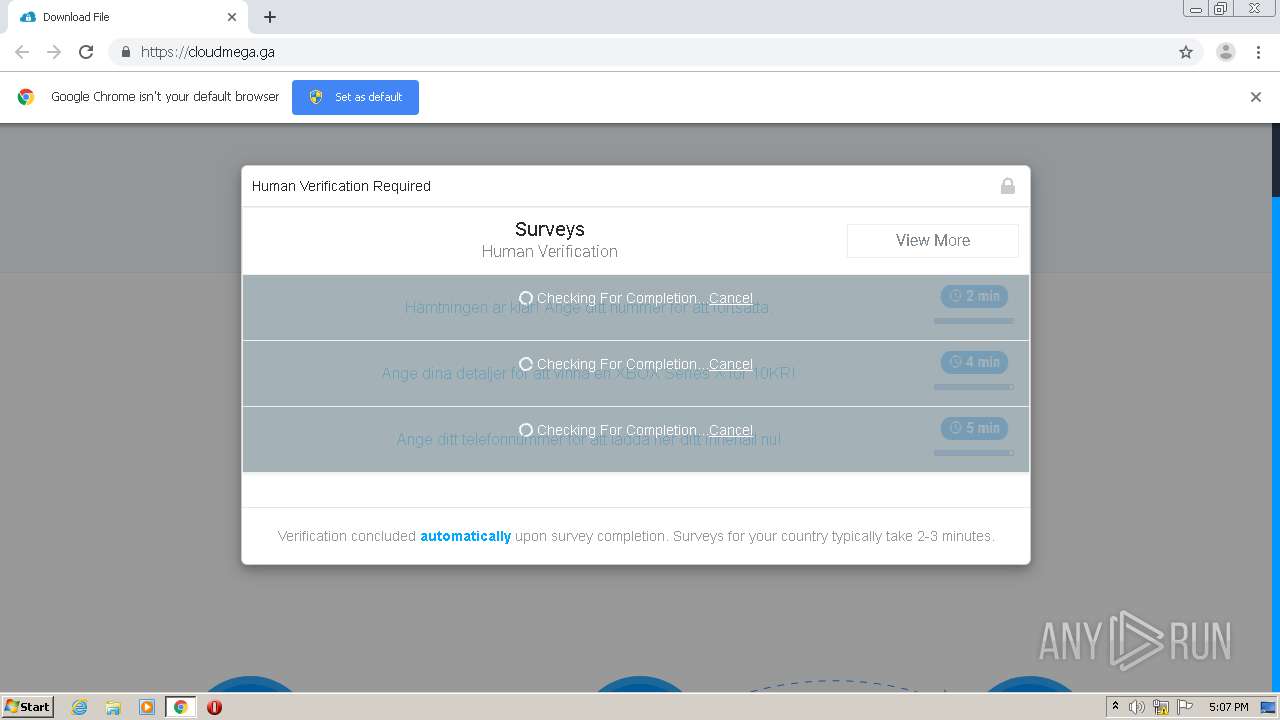
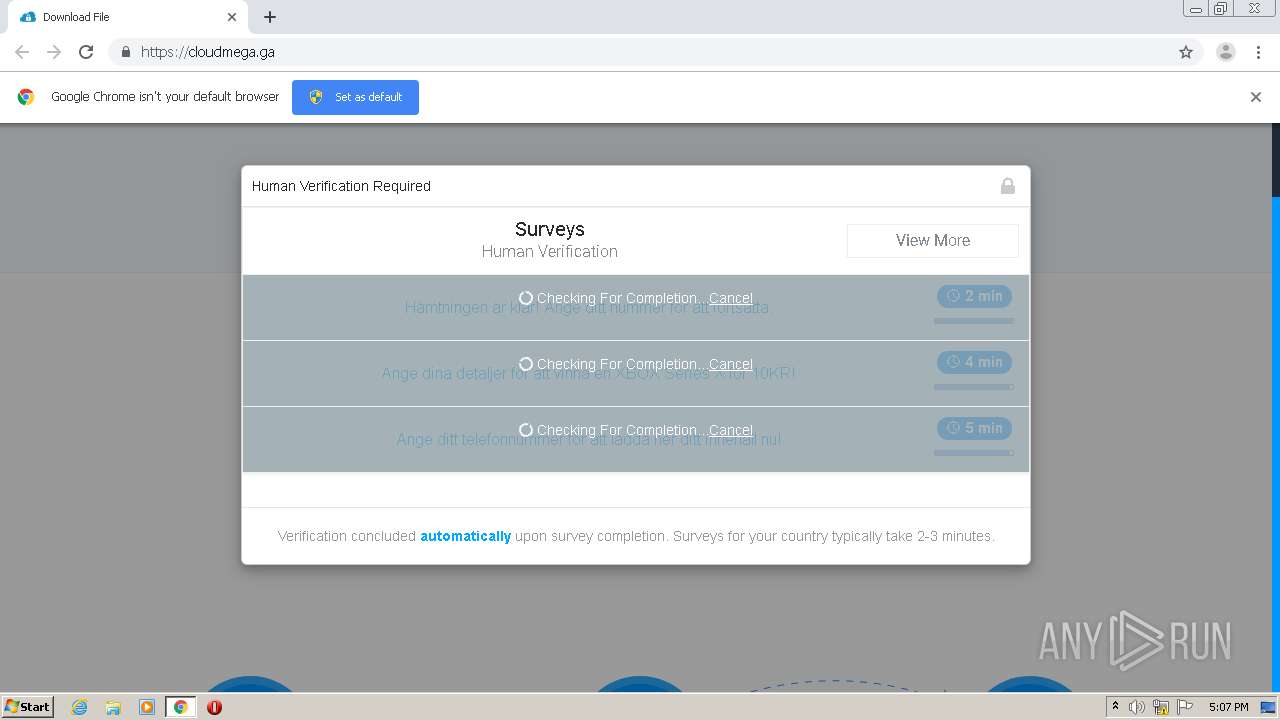
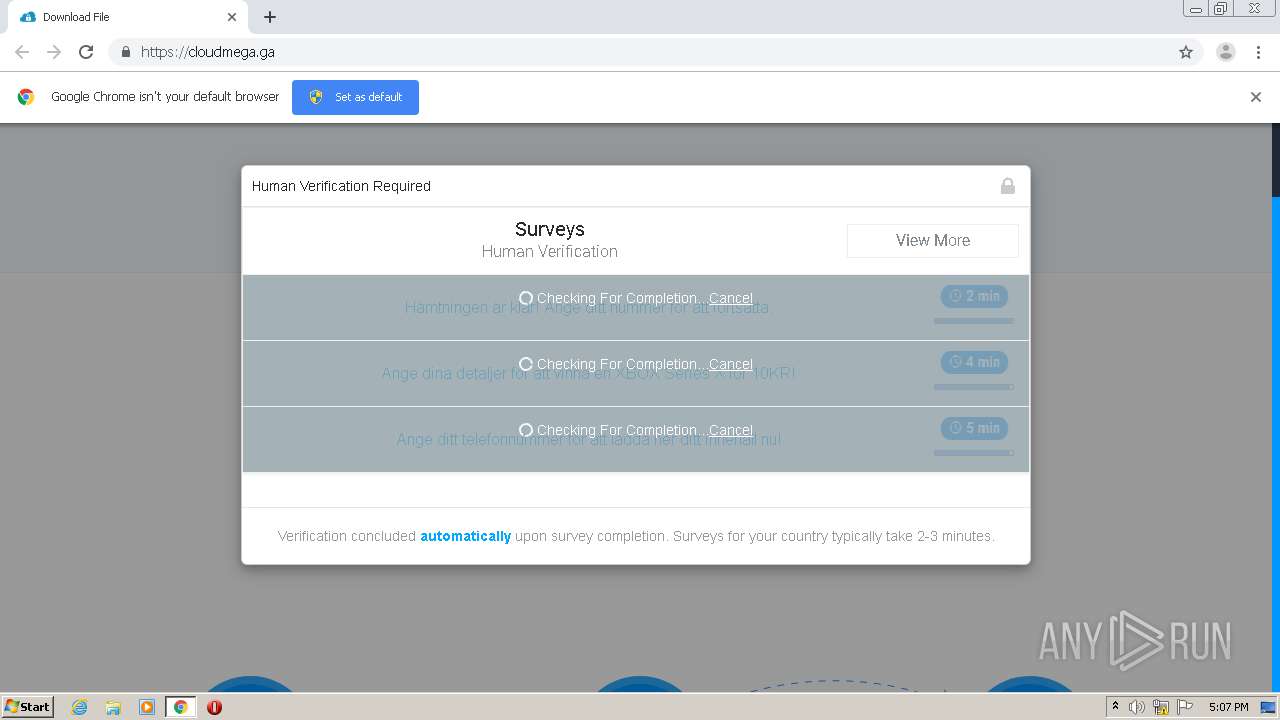
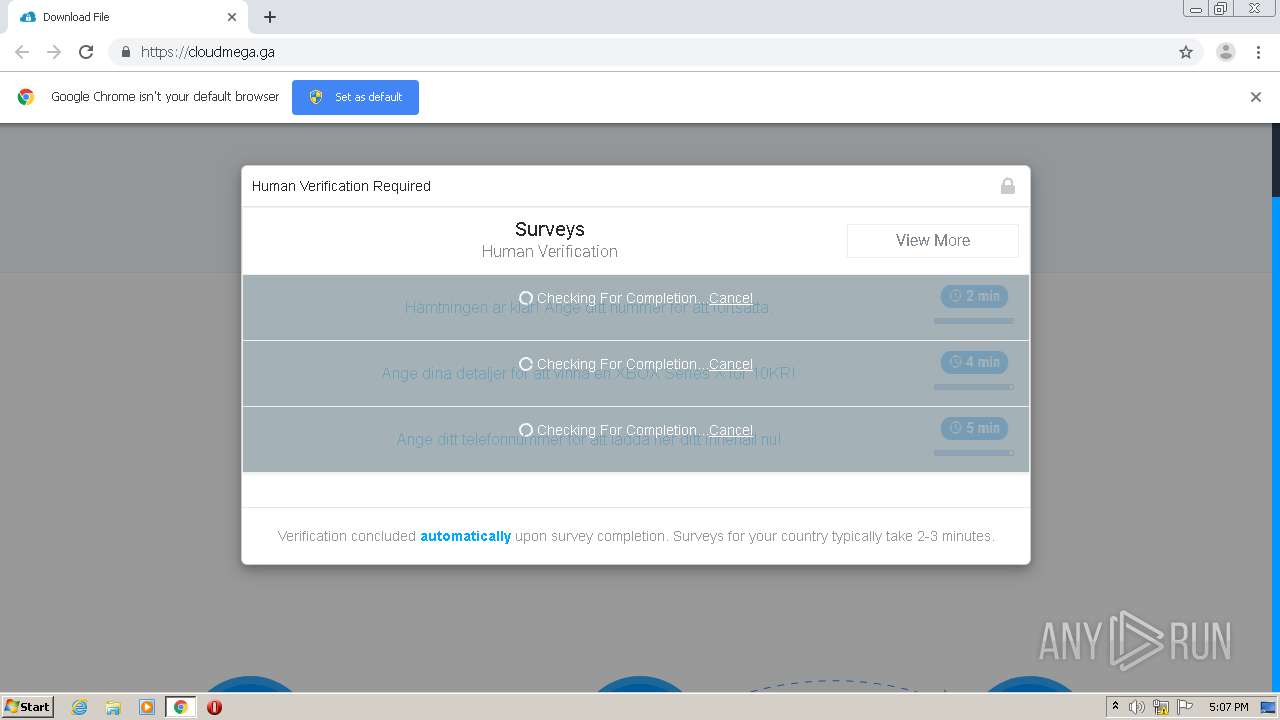
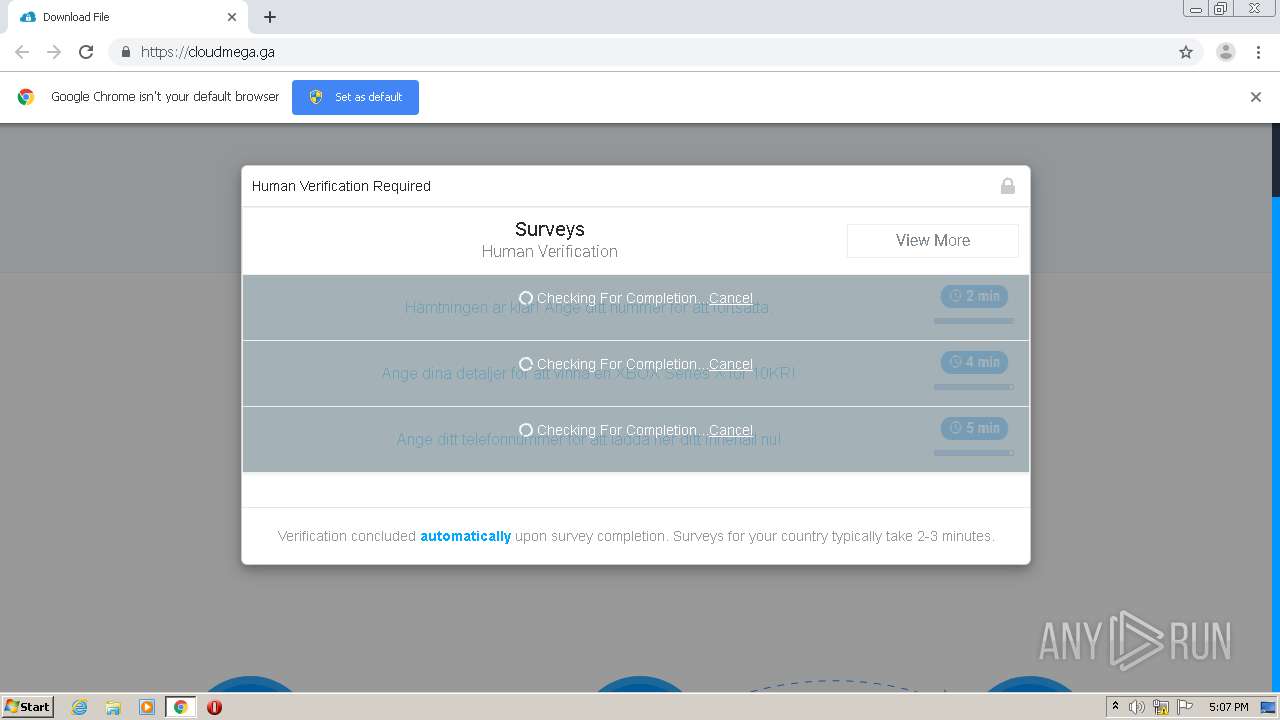
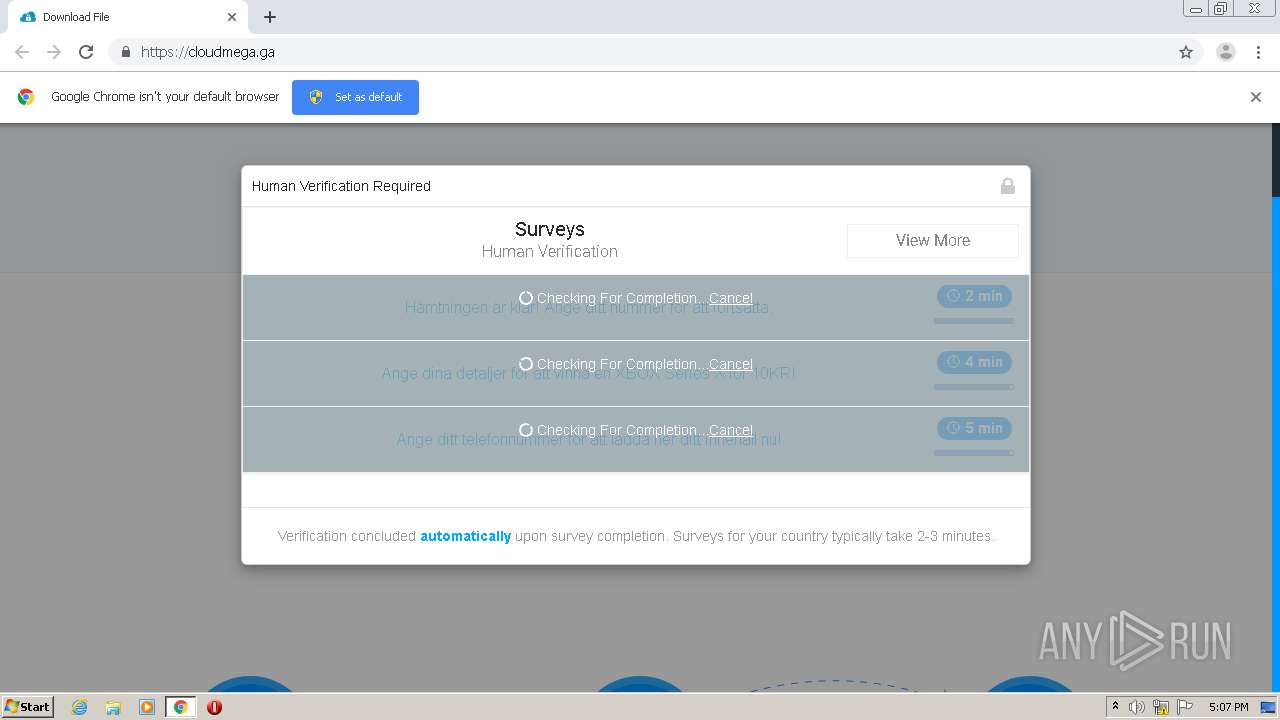
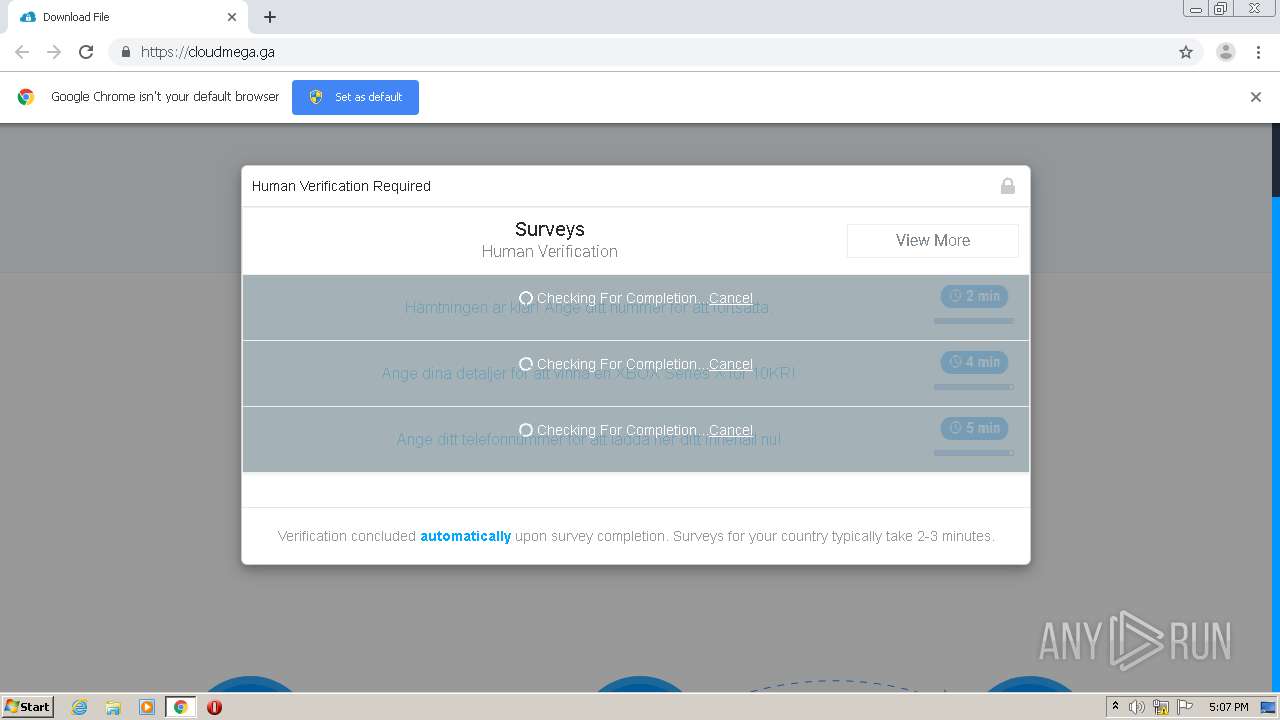
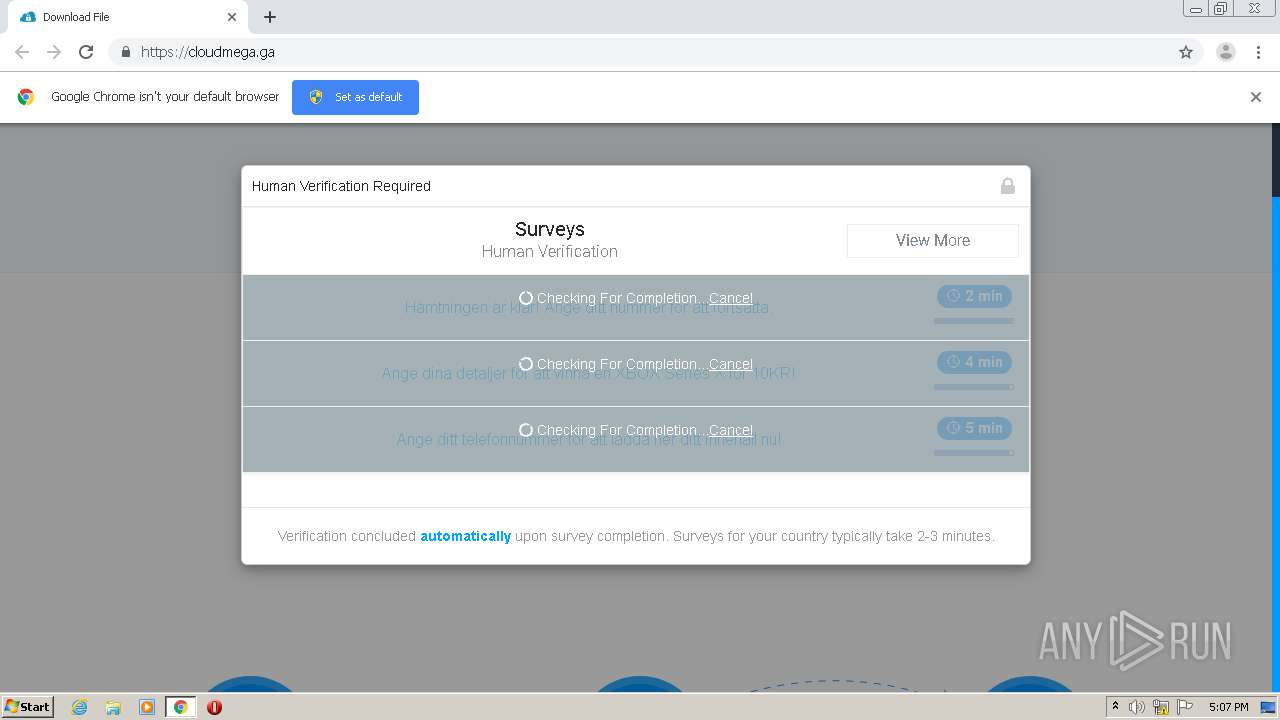
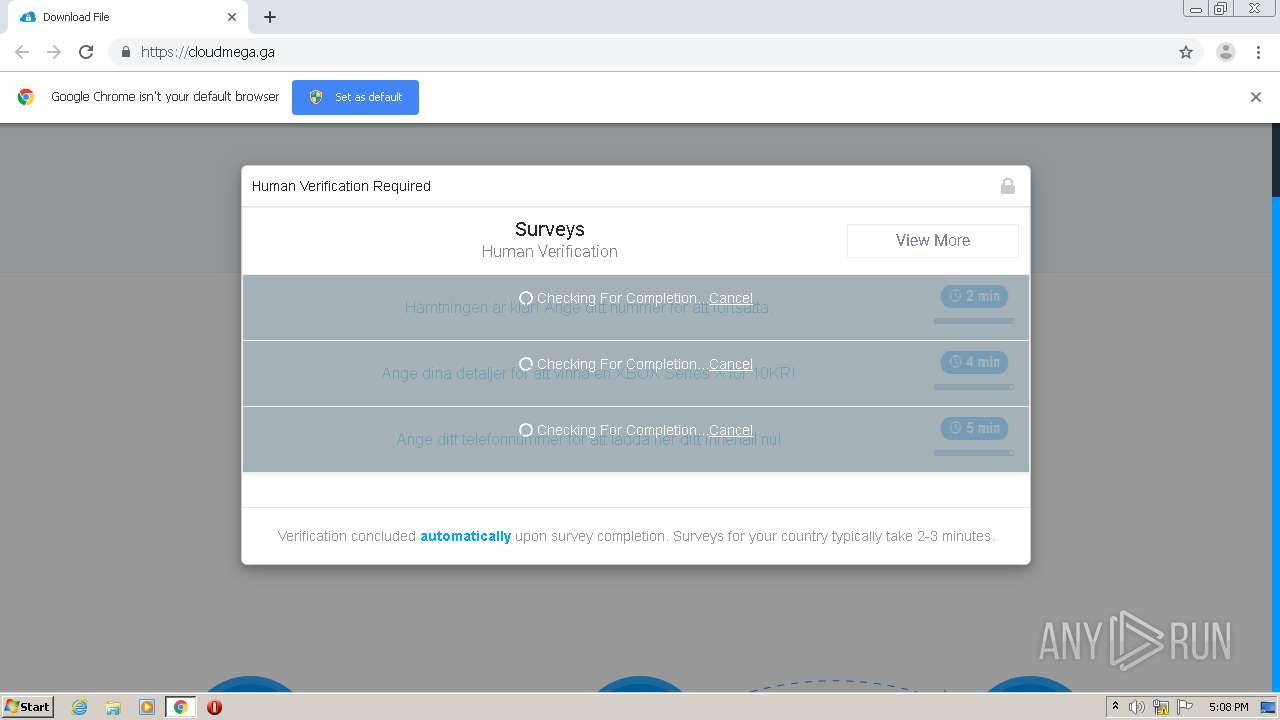
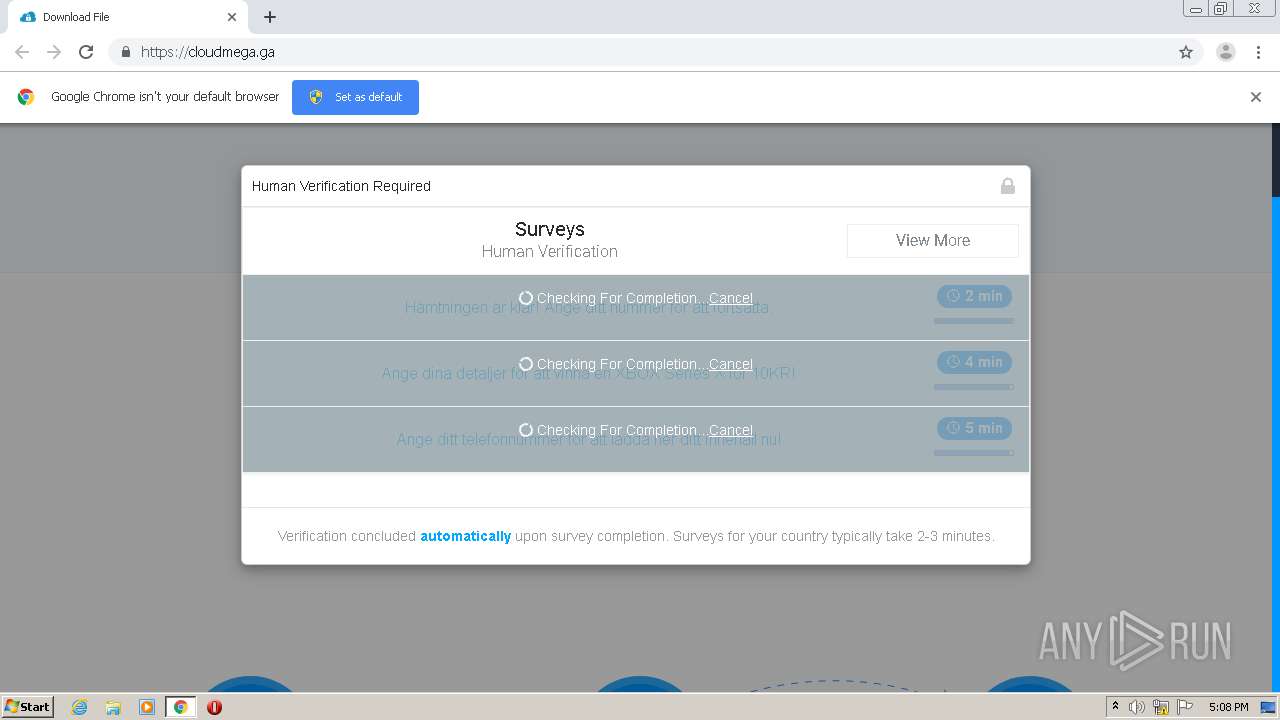
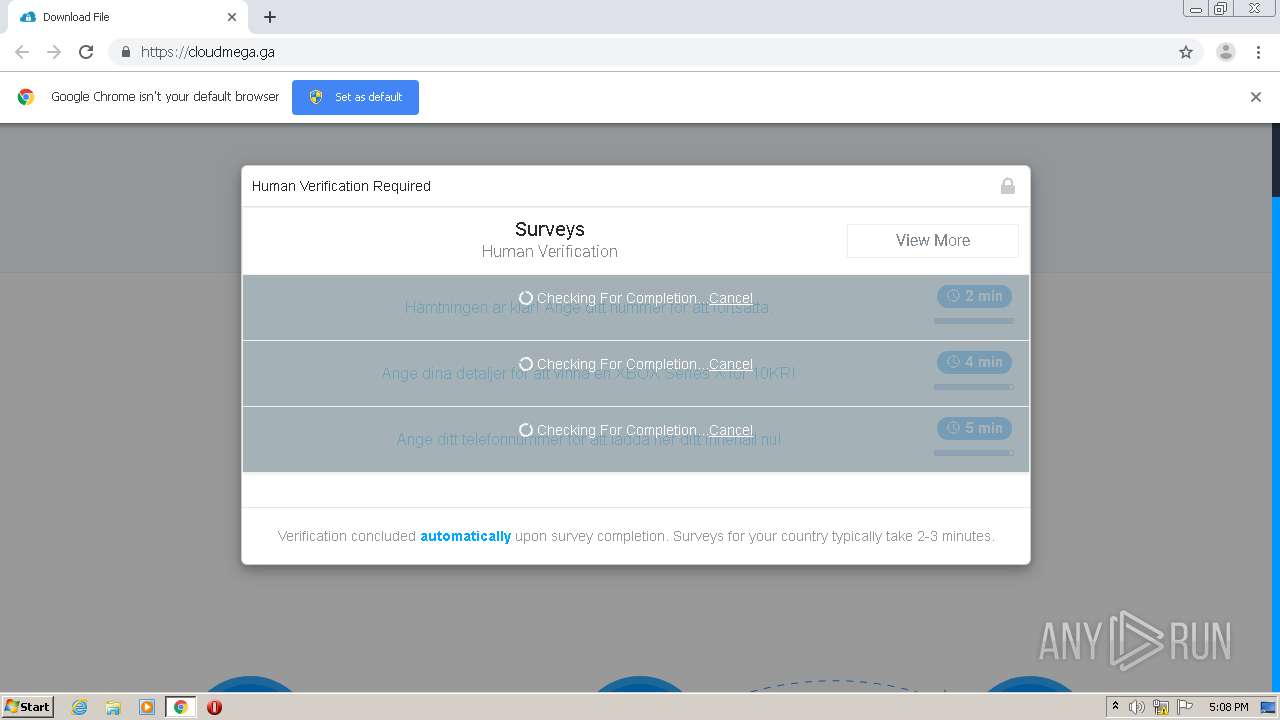
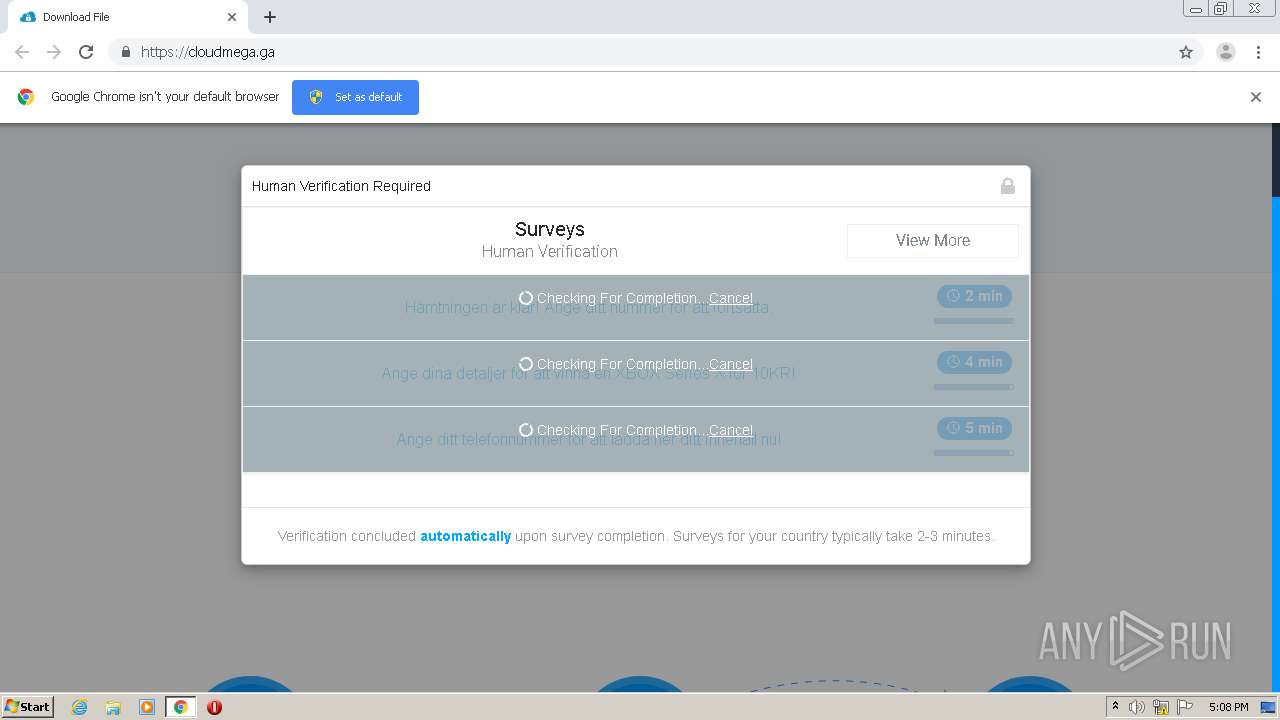
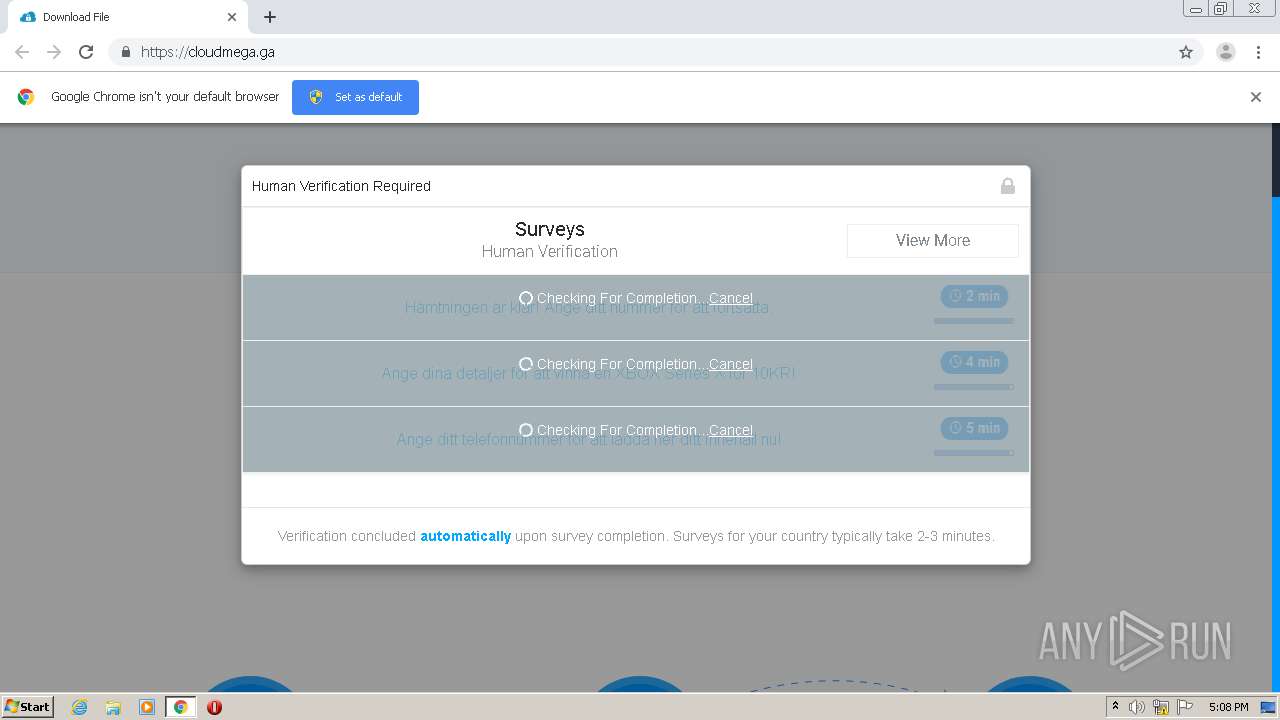
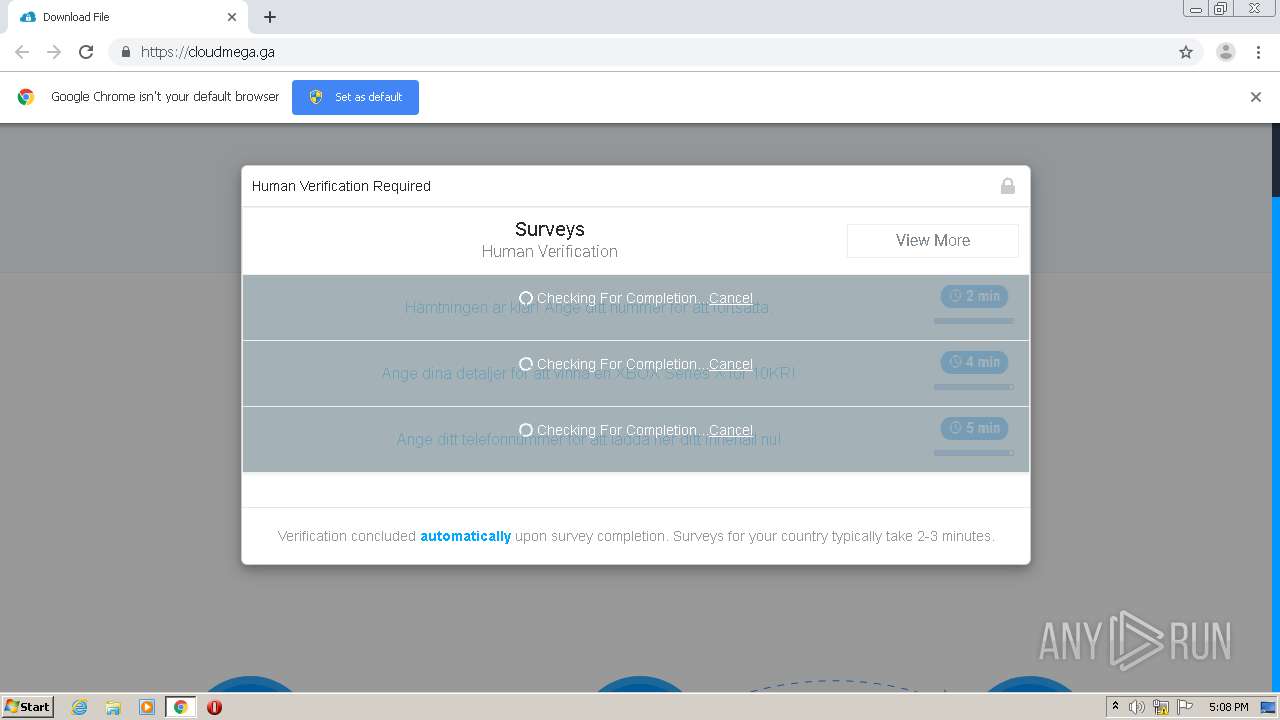
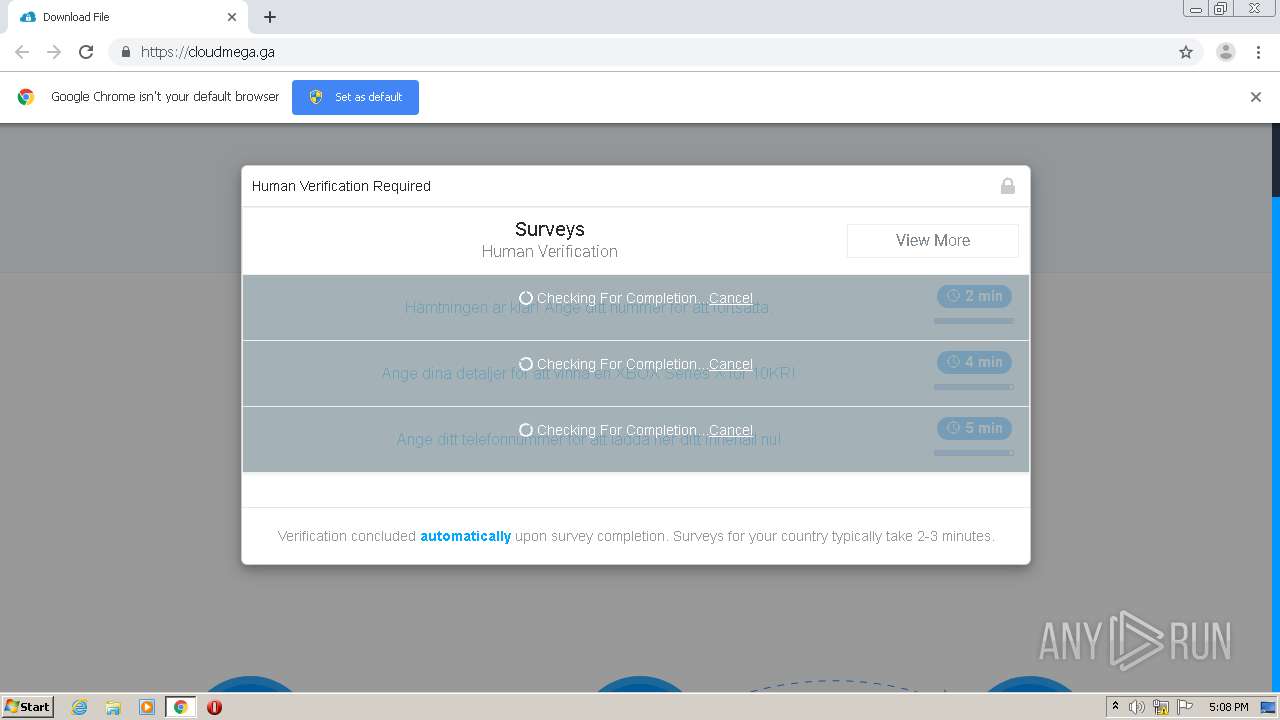
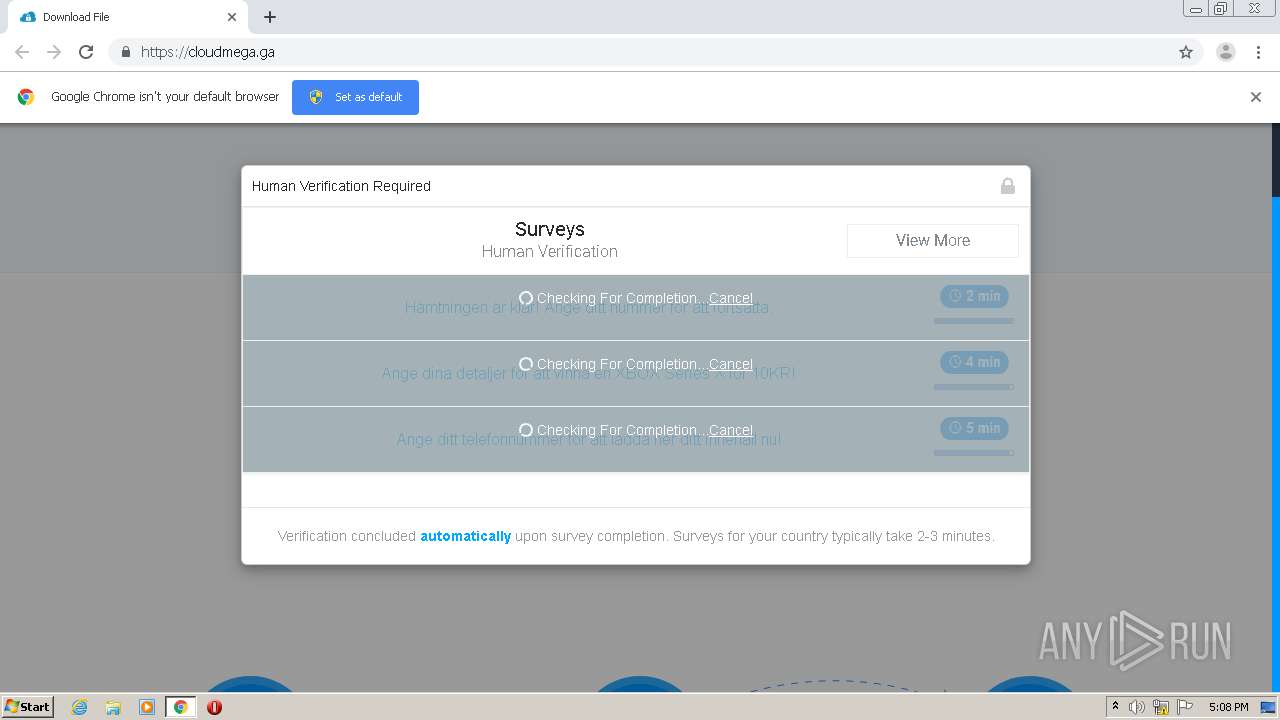
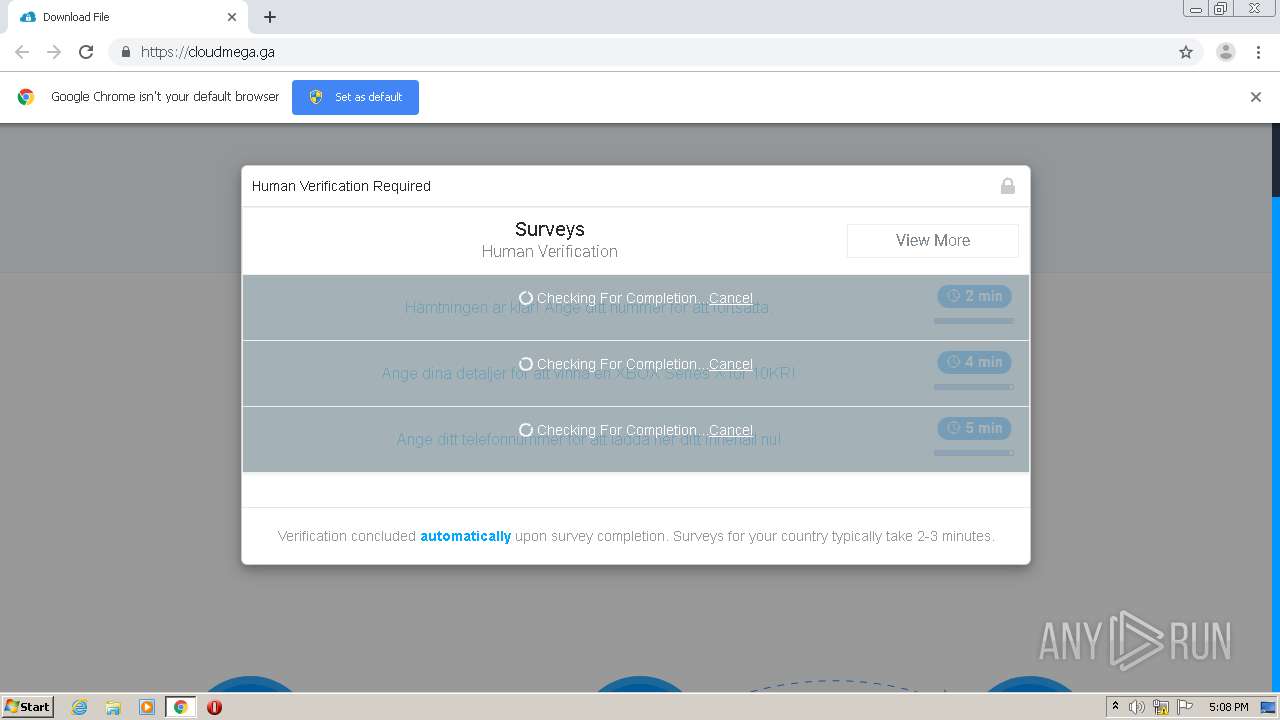
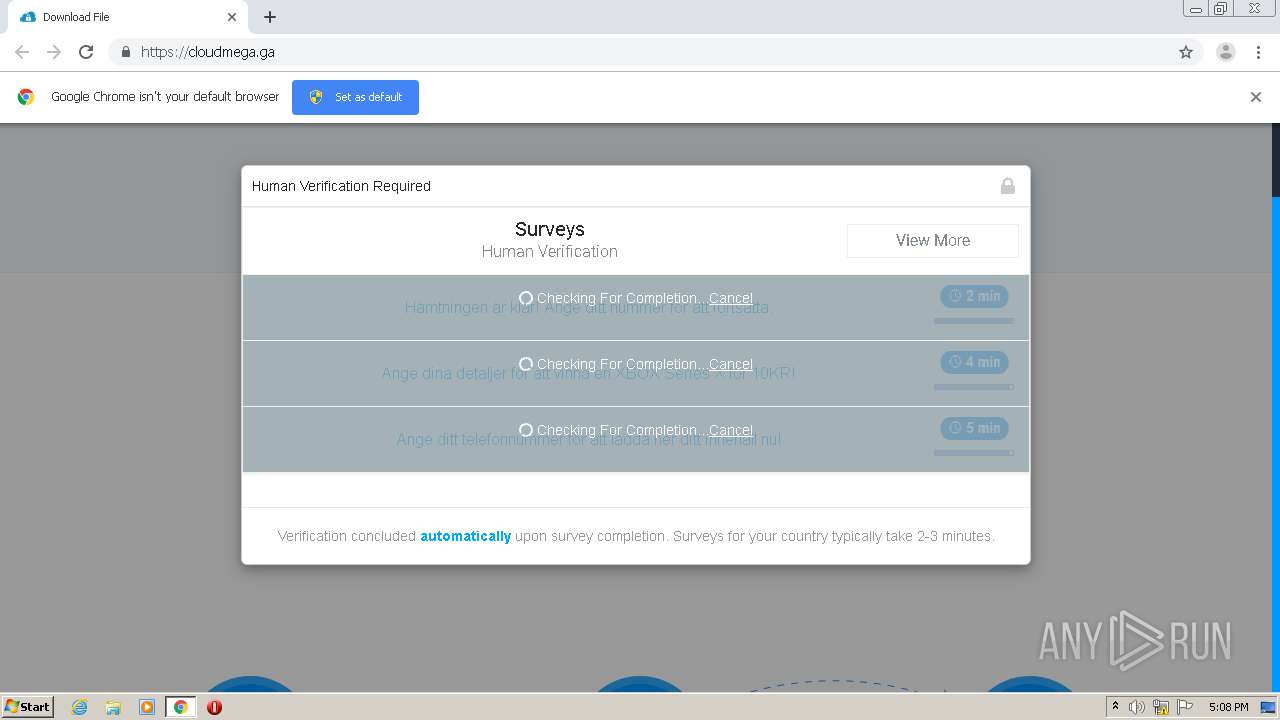
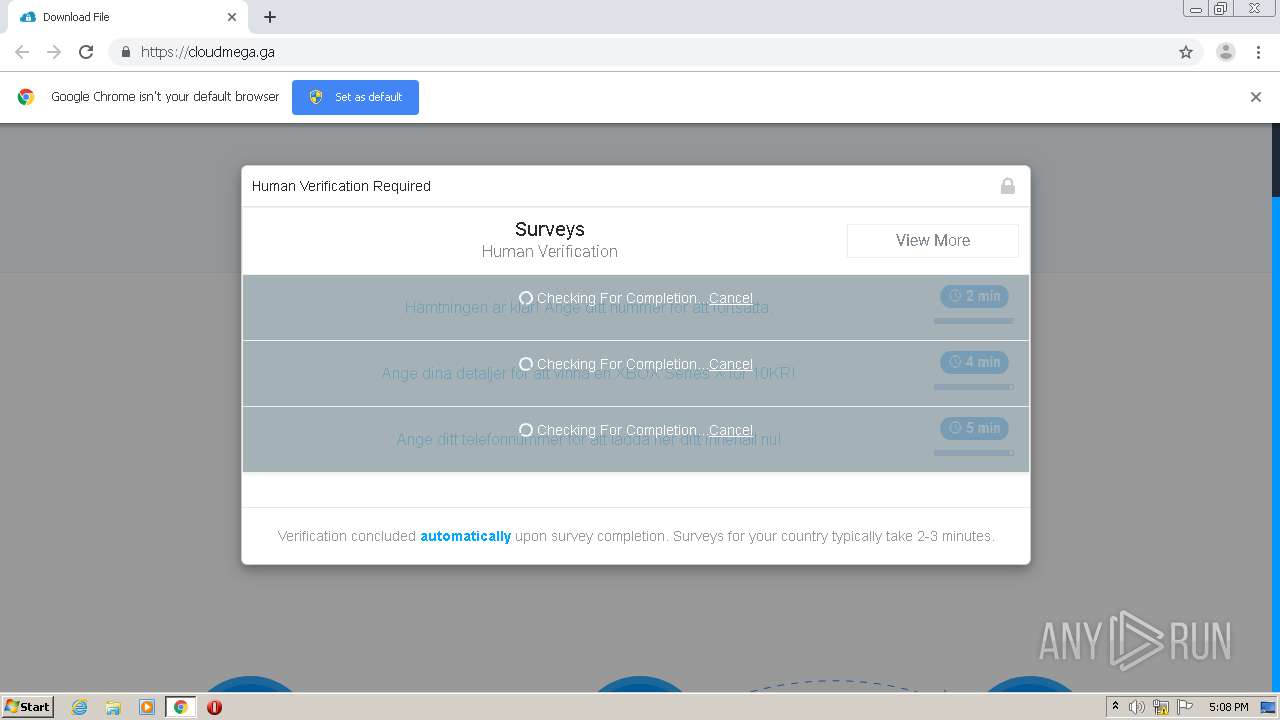
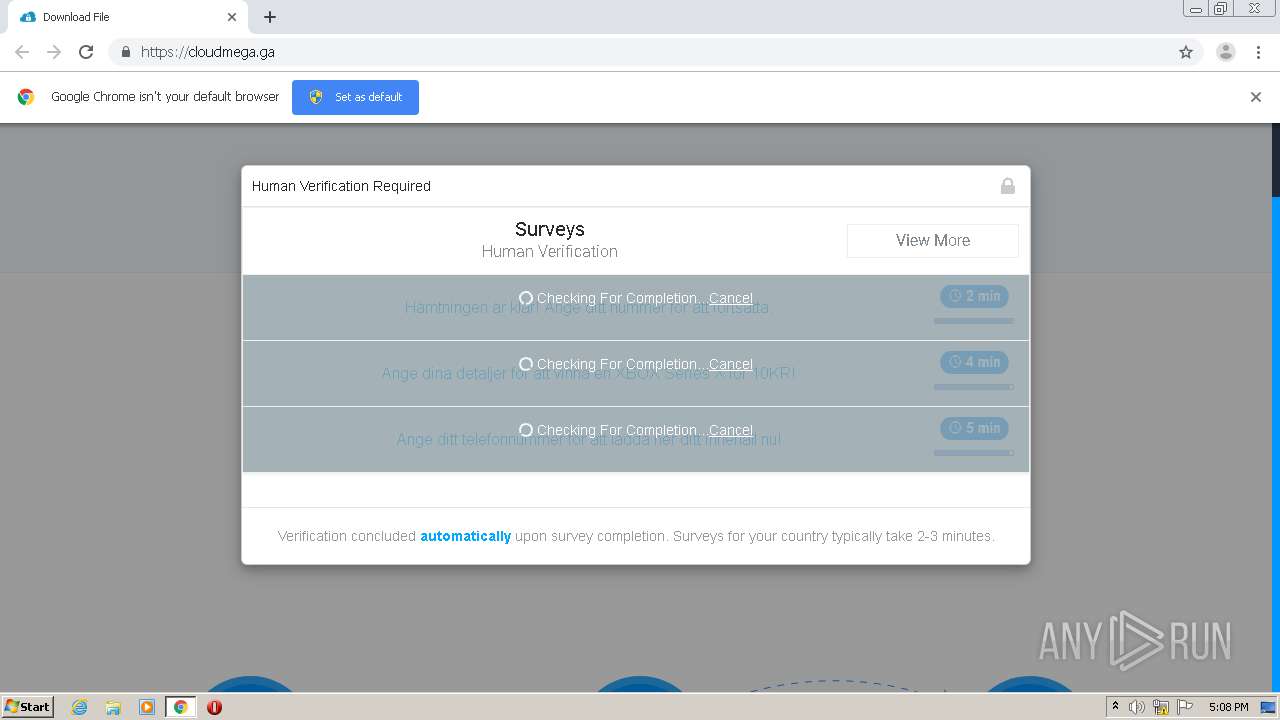
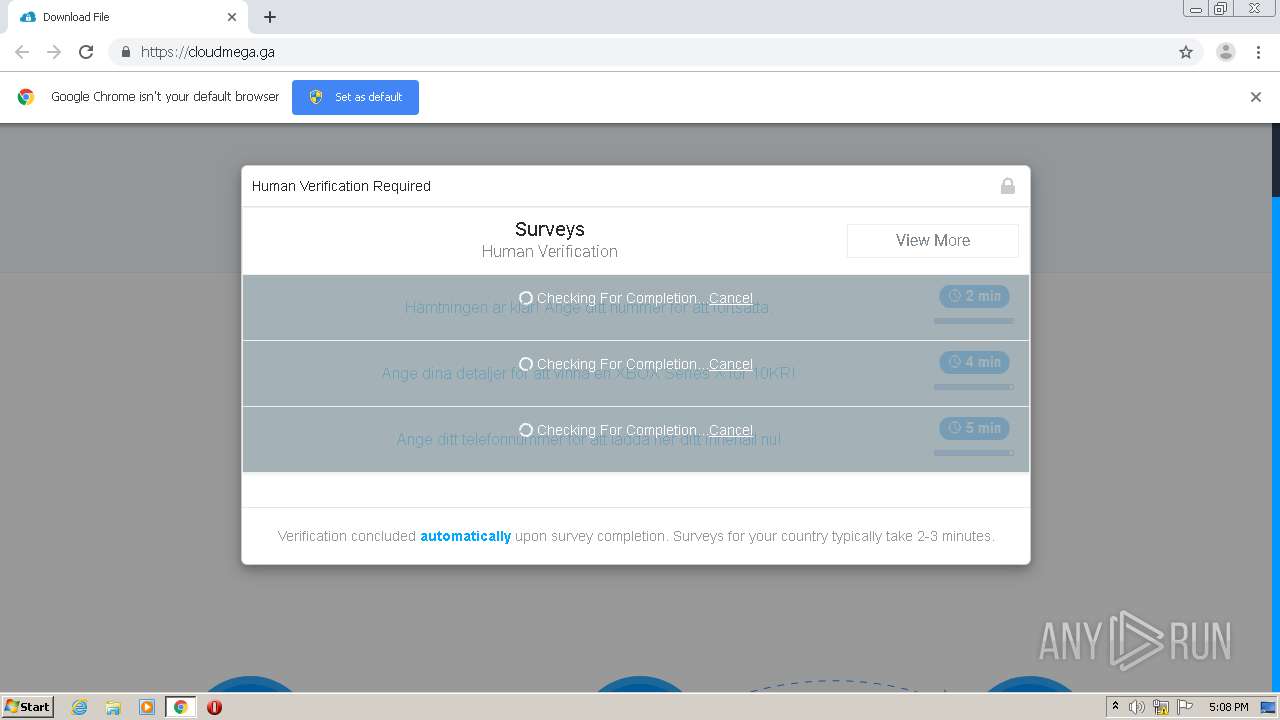
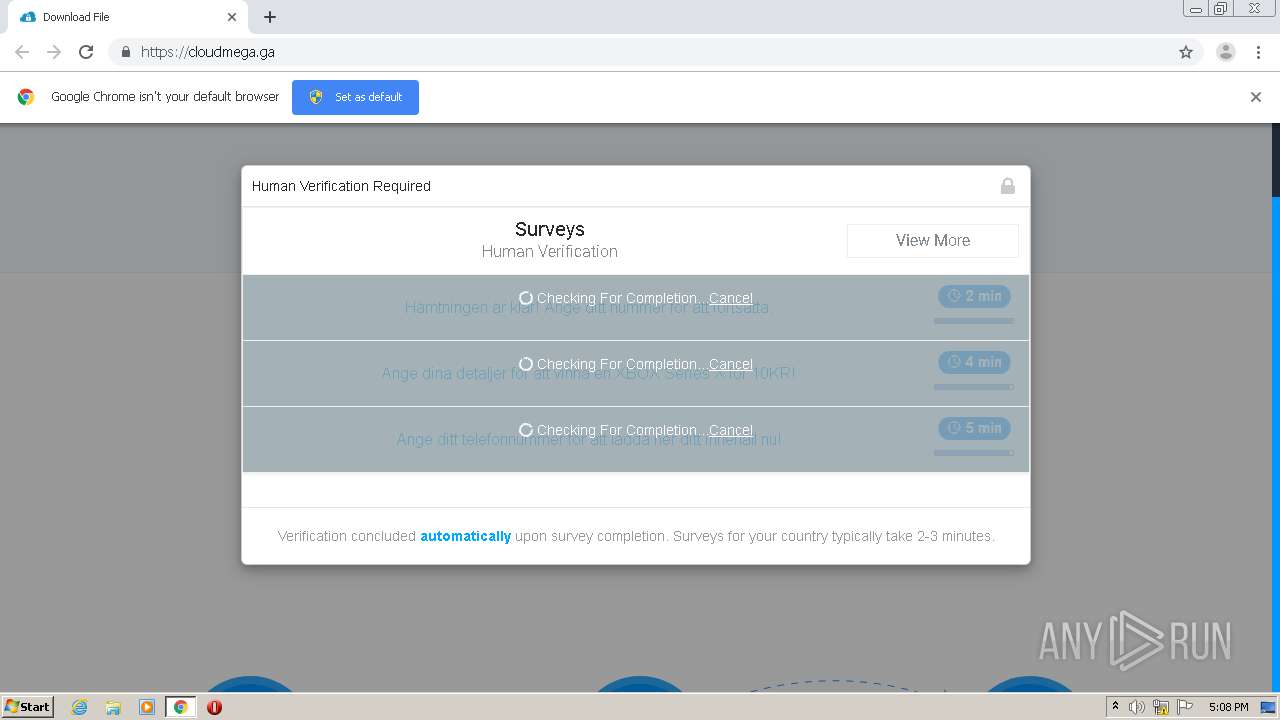
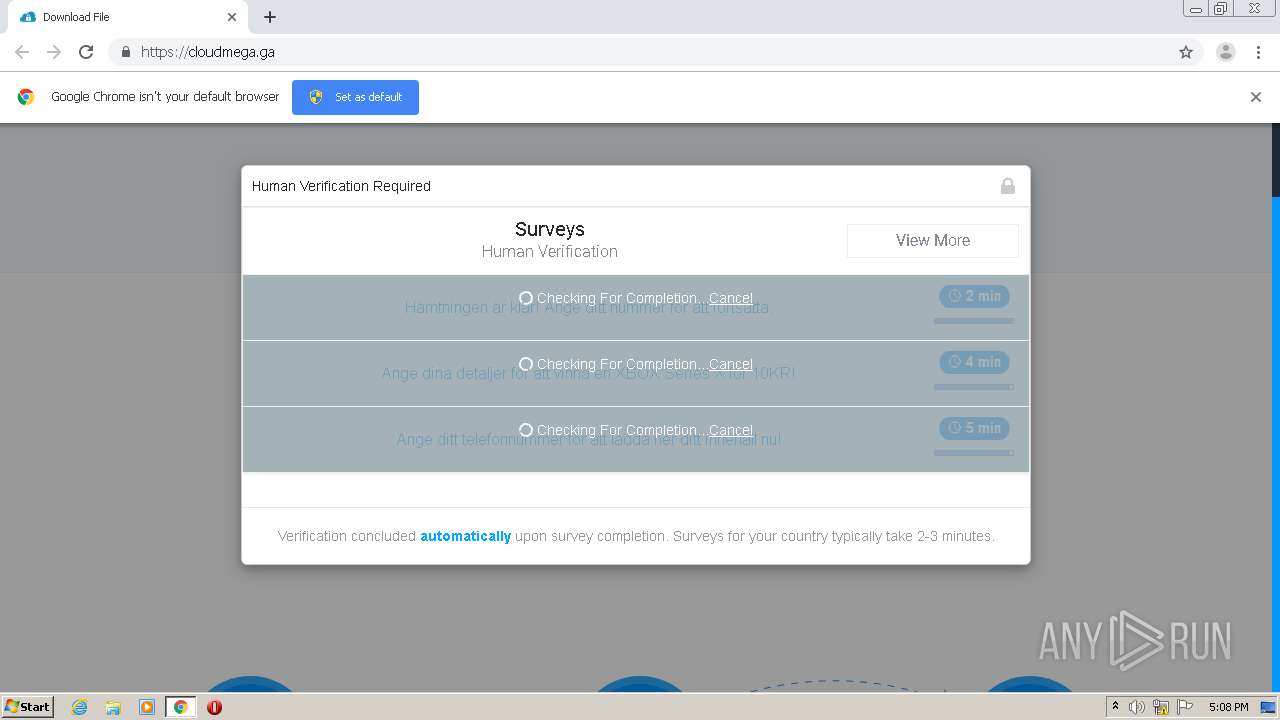
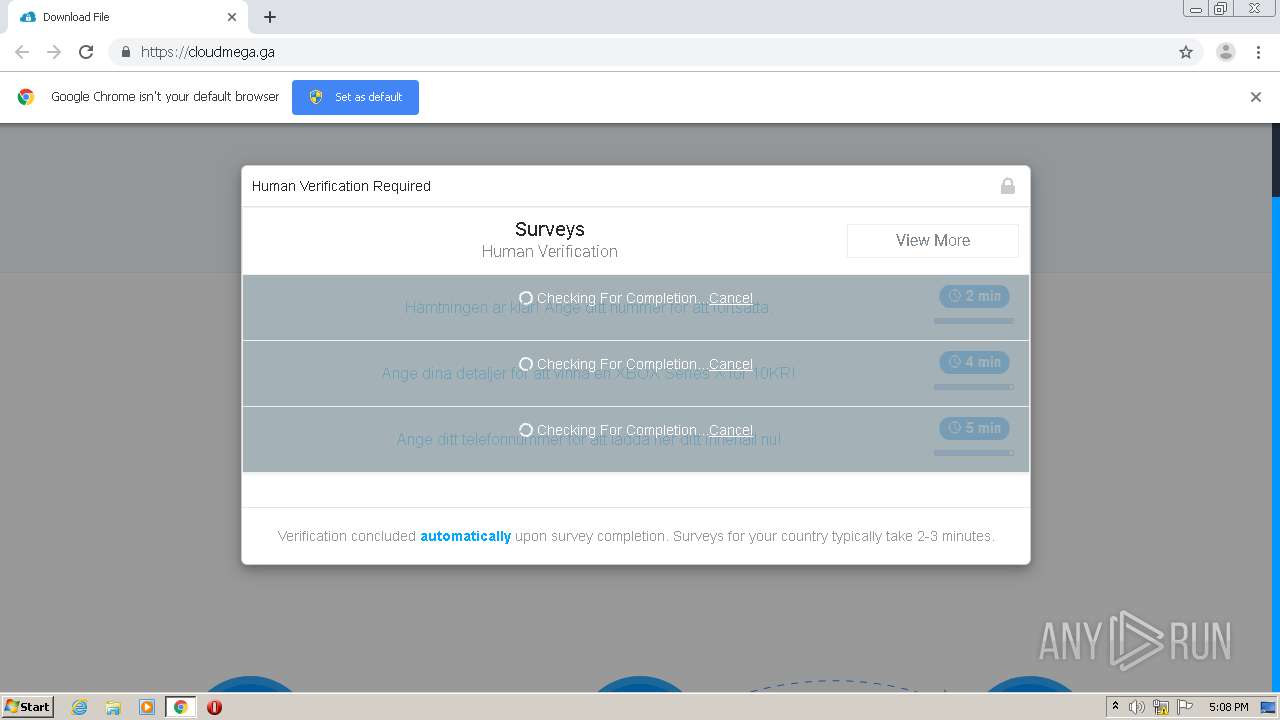
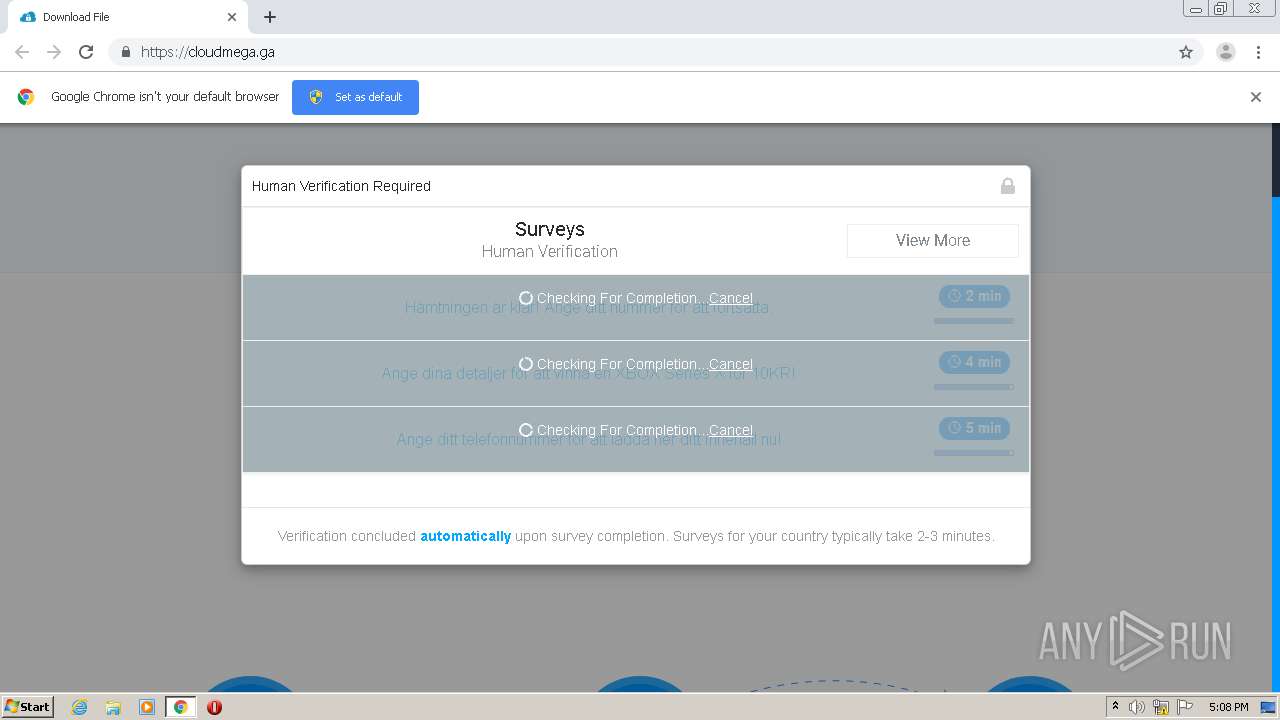
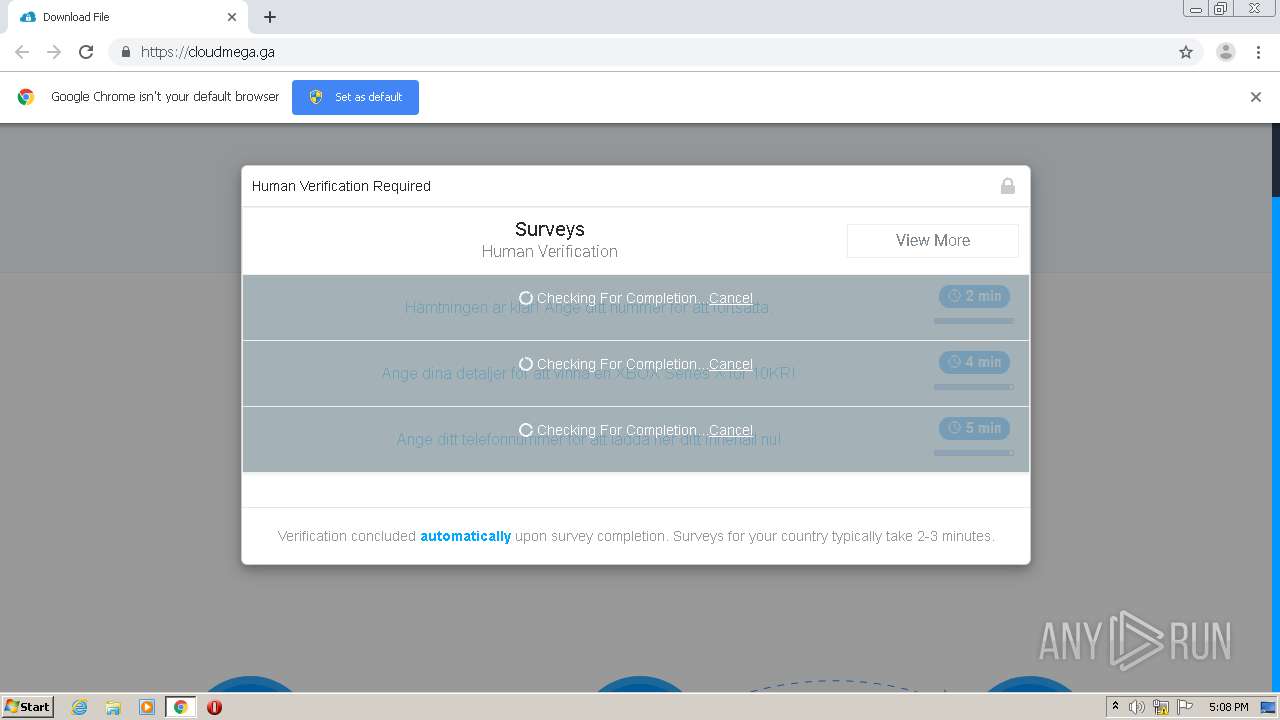
2592 | chrome.exe | 91.214.114.67:443 | cloudmega.ga | United Networks of Ukraine, Ltd | UA | suspicious |
2592 | chrome.exe | 172.67.215.243:443 | cldoffers.net | — | US | suspicious |
2592 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2592 | chrome.exe | 151.101.194.217:443 | browser.sentry-cdn.com | Fastly | US | suspicious |
2592 | chrome.exe | 65.9.70.215:443 | d13pxqgp3ixdbh.cloudfront.net | AT&T Services, Inc. | US | unknown |
2592 | chrome.exe | 65.9.70.37:443 | d13nu0oomnx5ti.cloudfront.net | AT&T Services, Inc. | US | unknown |
2592 | chrome.exe | 172.217.23.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2592 | chrome.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
red.wutf.space |
| suspicious |
accounts.google.com |
| shared |
cloudmega.ga |
| suspicious |
browser.sentry-cdn.com |
| whitelisted |
d13pxqgp3ixdbh.cloudfront.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
d13nu0oomnx5ti.cloudfront.net |
| whitelisted |
cldoffers.net |
| malicious |
www.google-analytics.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
2592 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.ga) in TLS SNI |
2592 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.ga) |