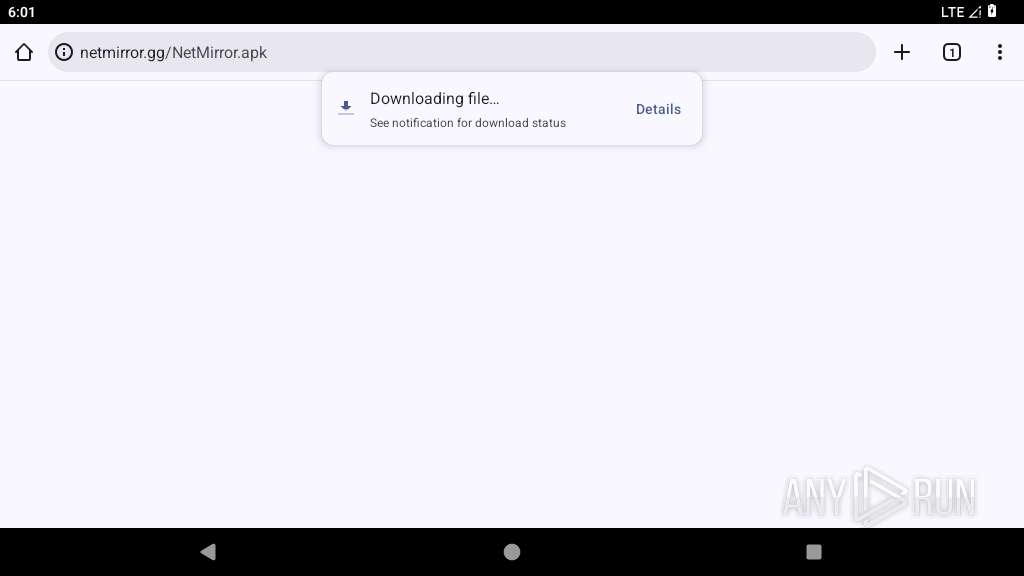
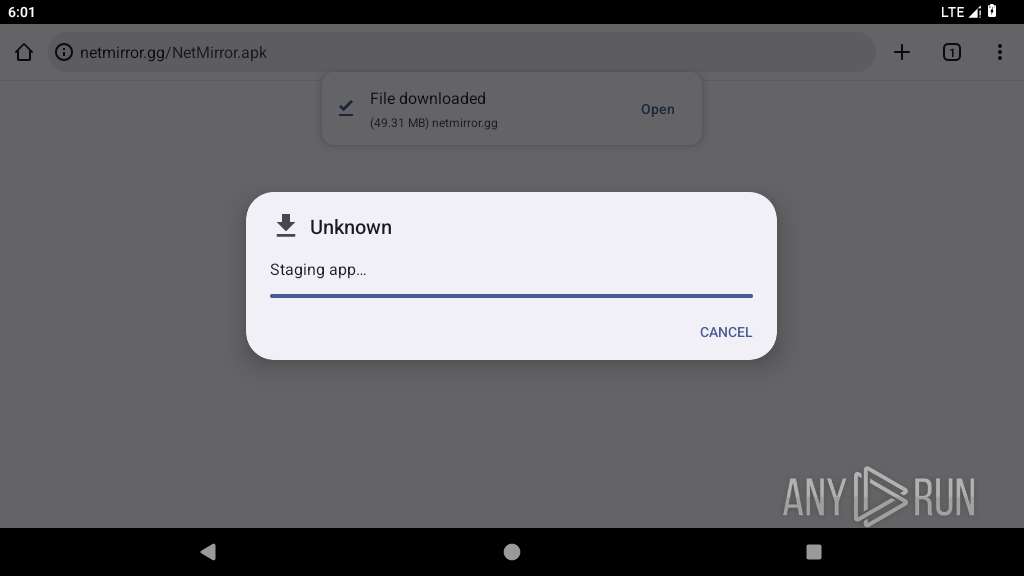
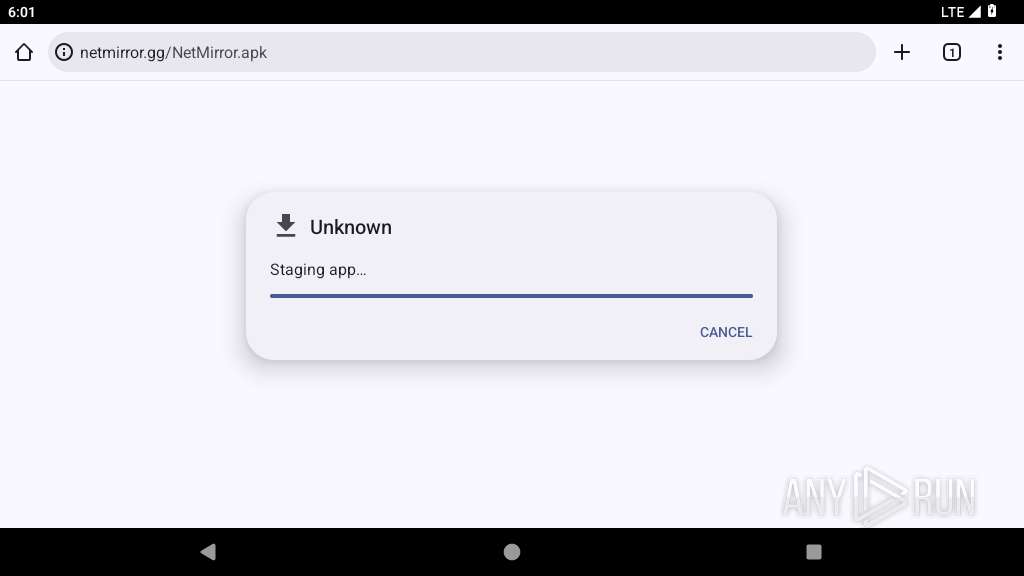
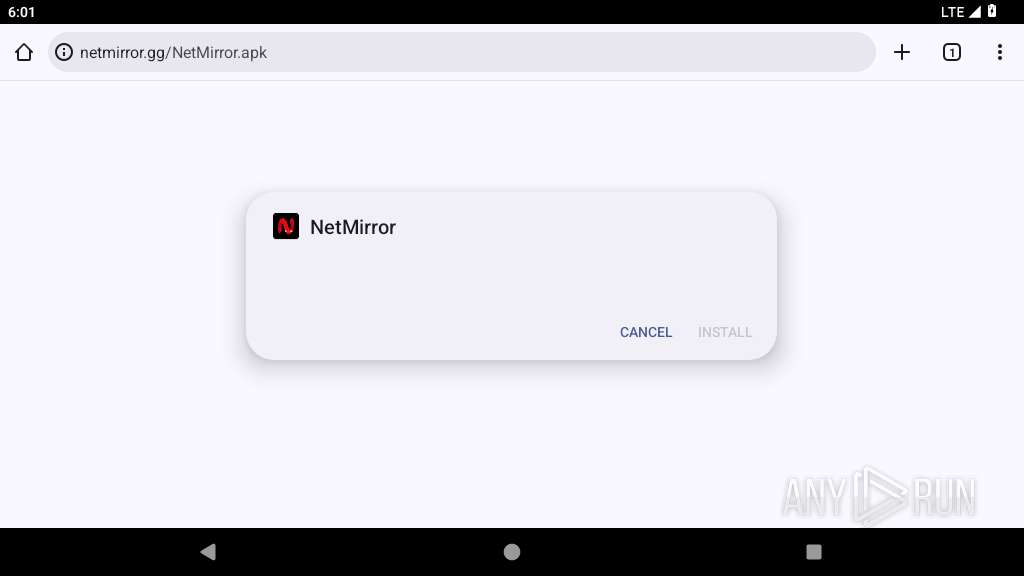
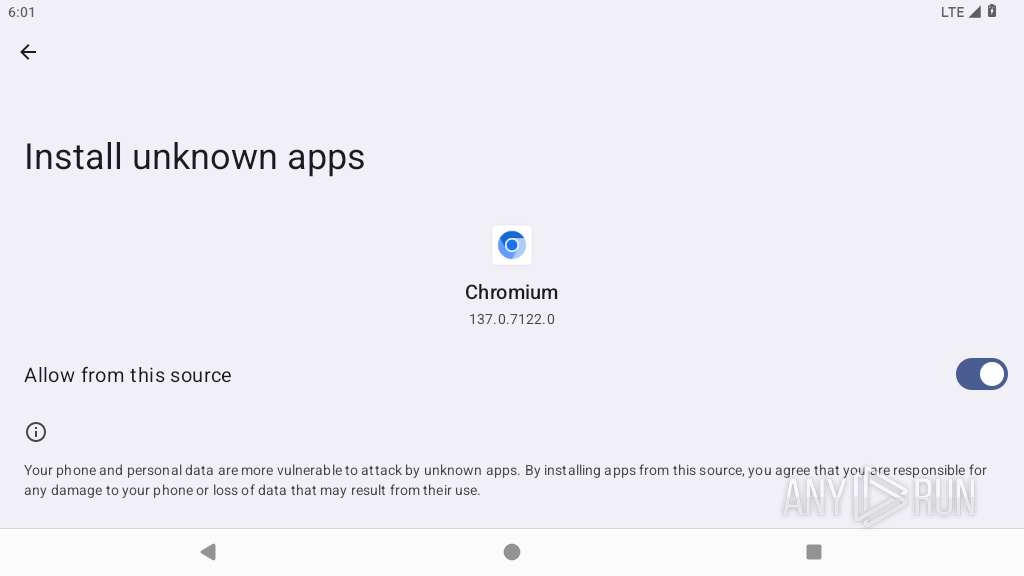
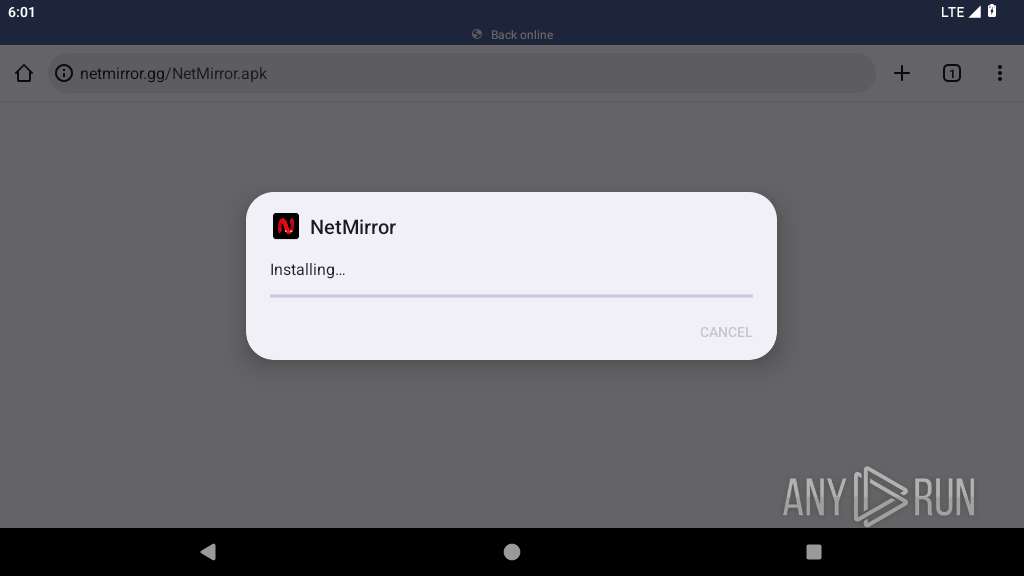
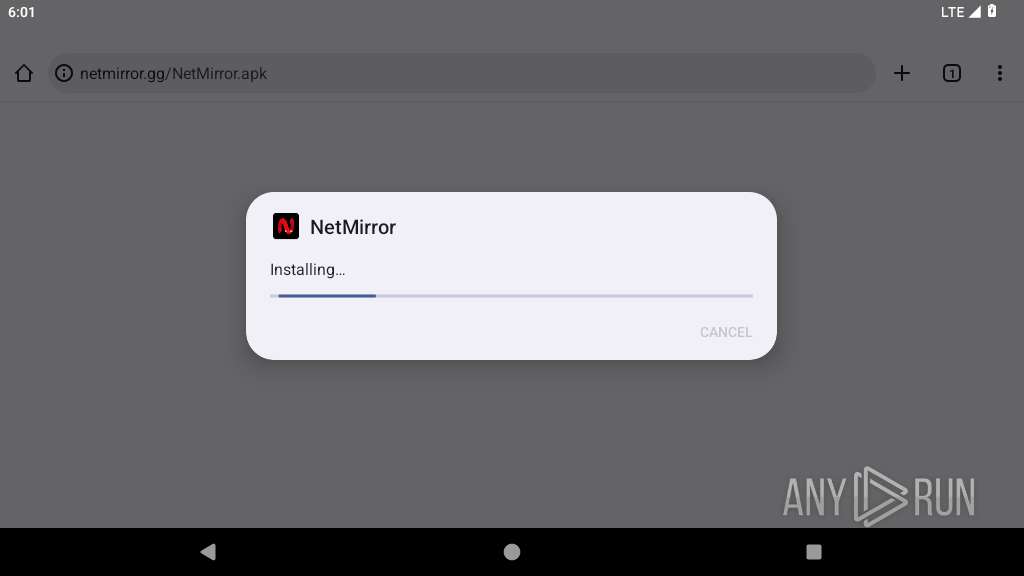
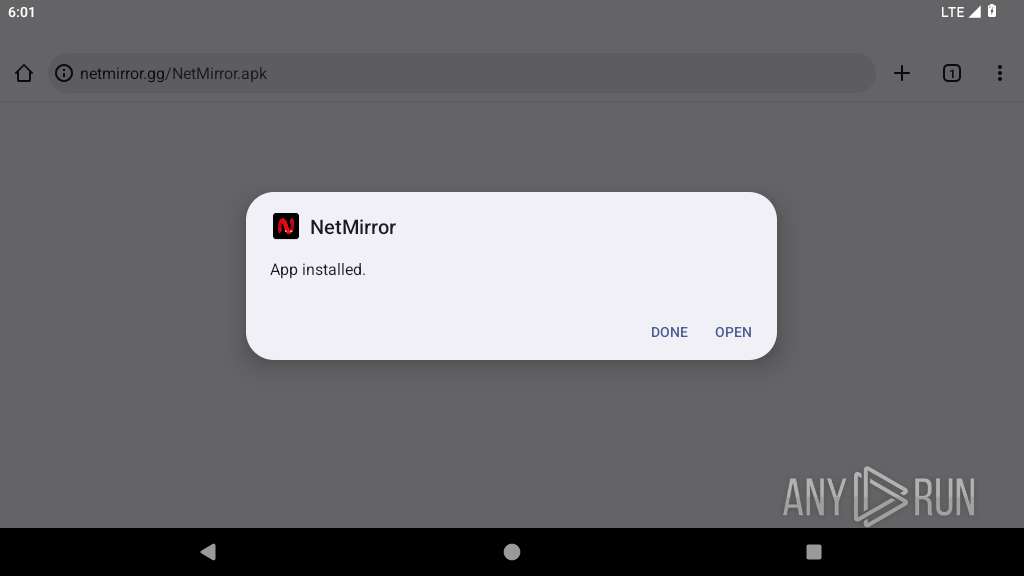
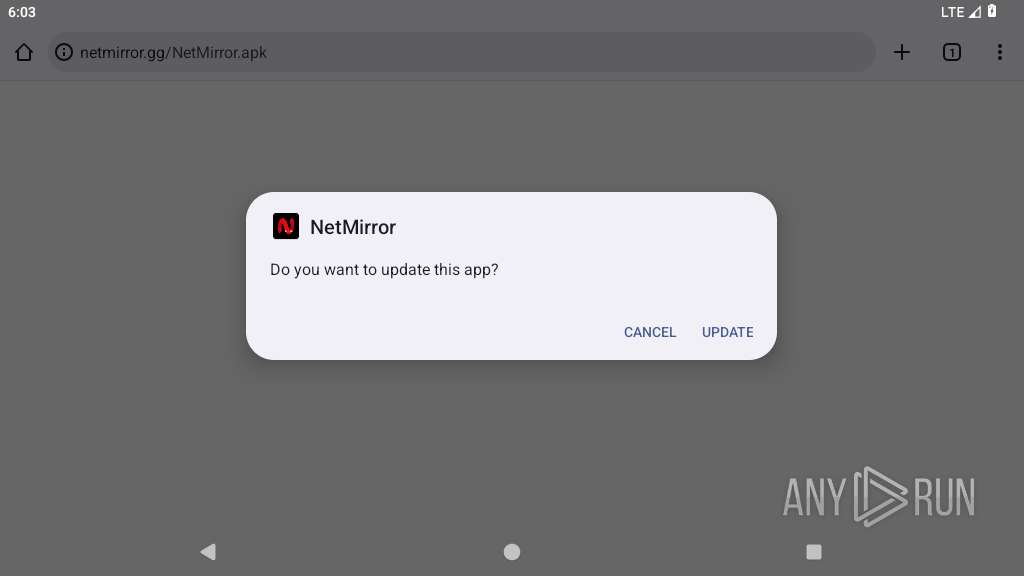
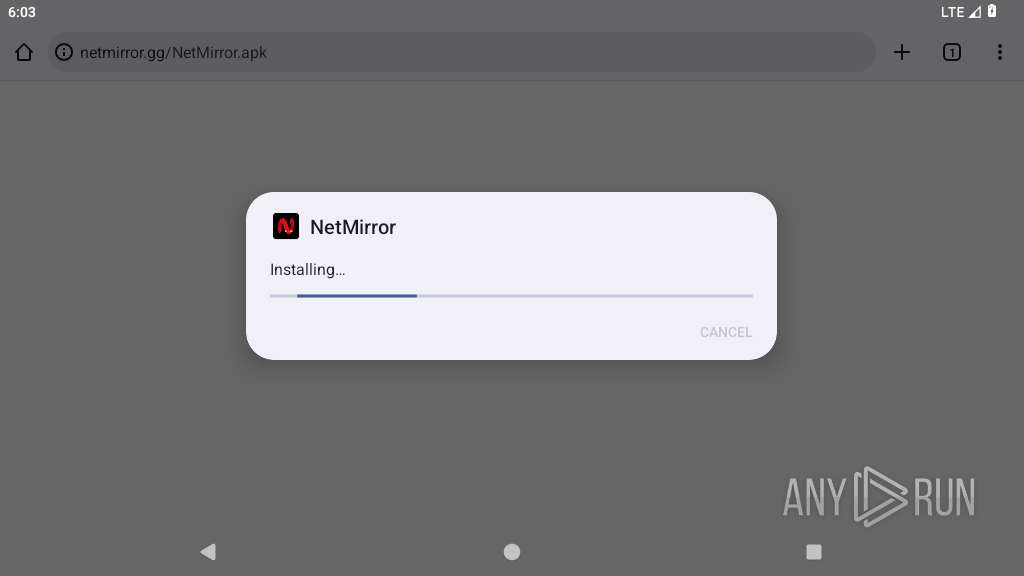
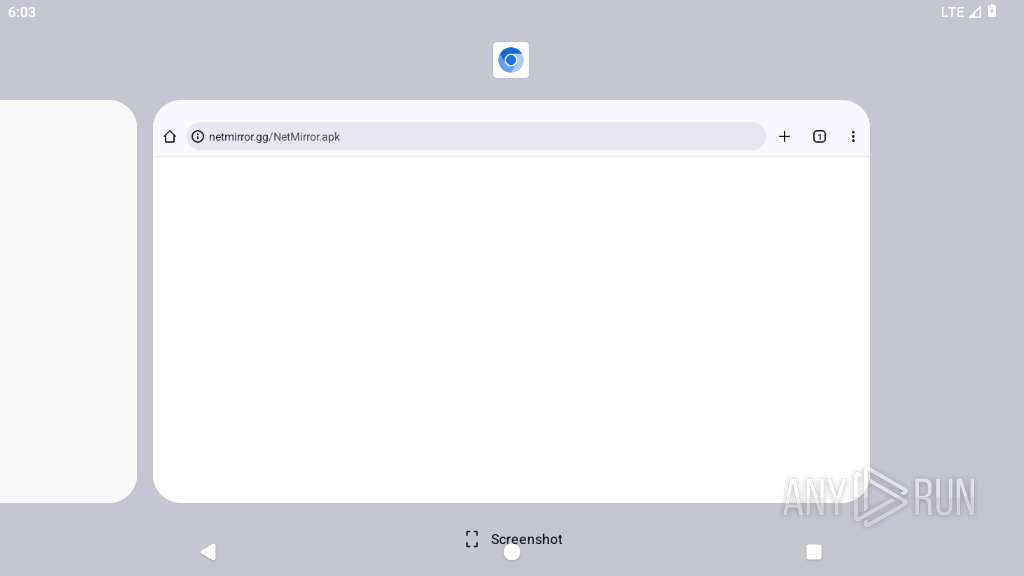
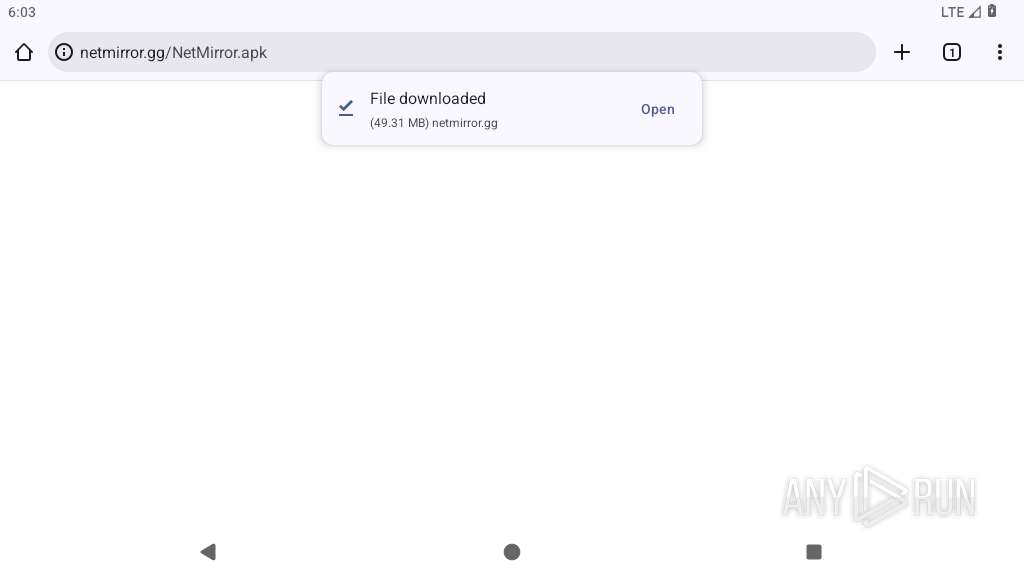
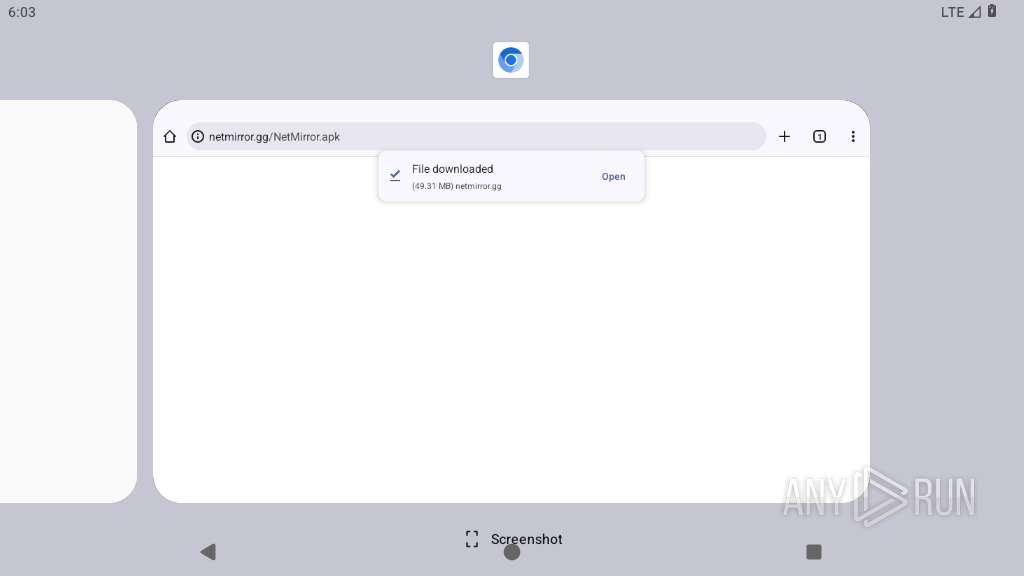
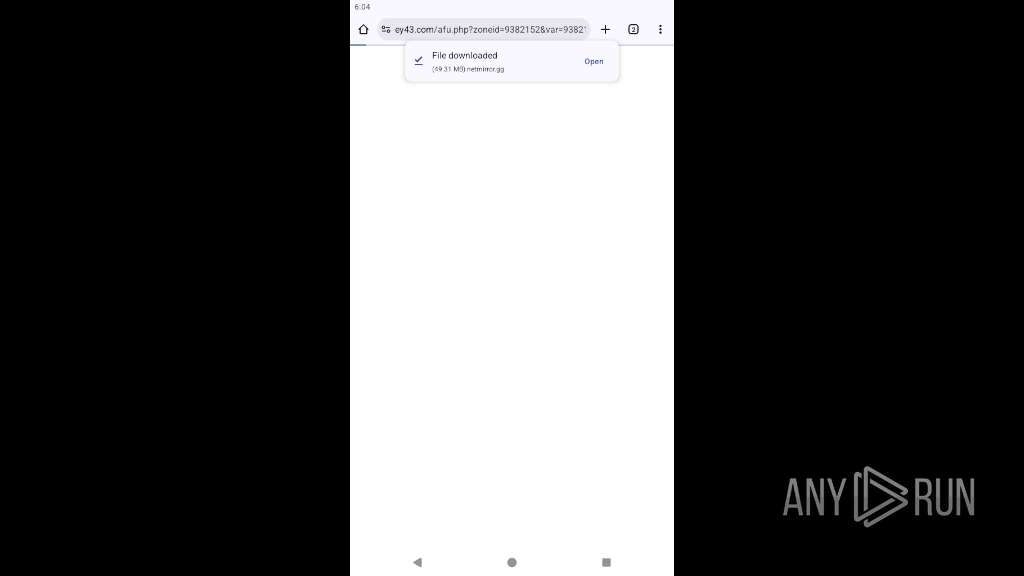
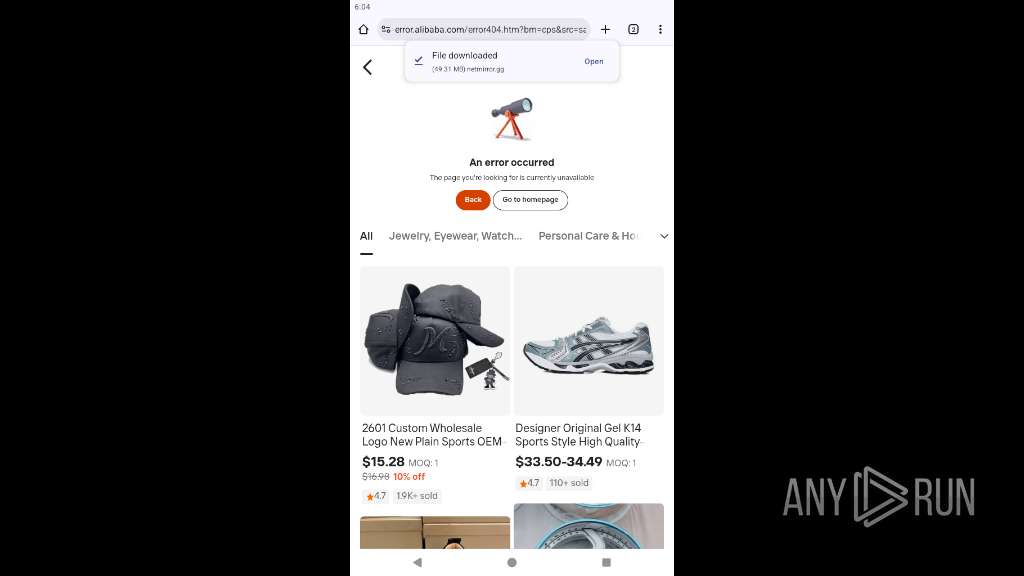
| URL: | https://netmirror.gg/NetMirror.apk |
| Full analysis: | https://app.any.run/tasks/f513d095-d160-4d05-a045-9923e8996f7e |
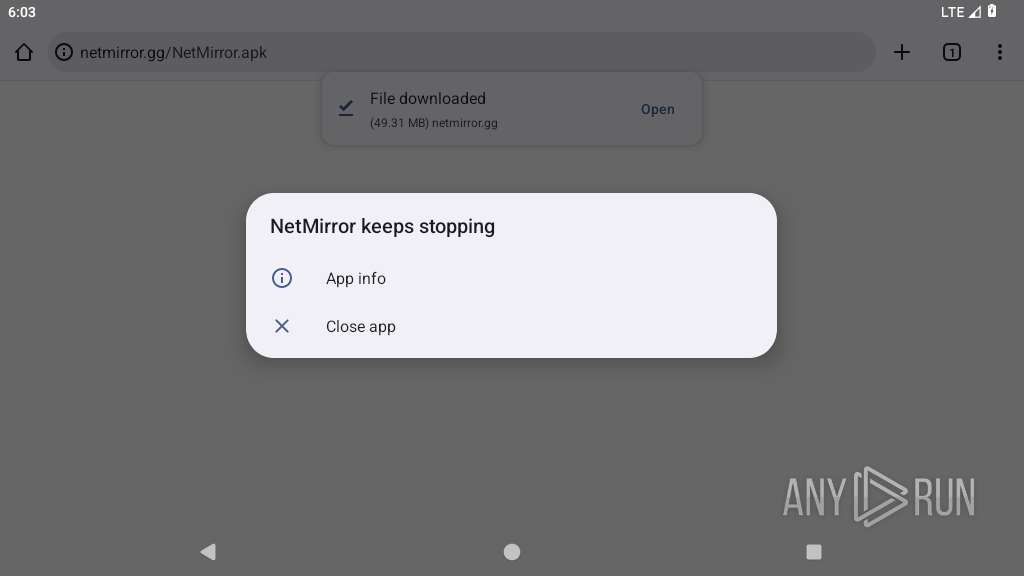
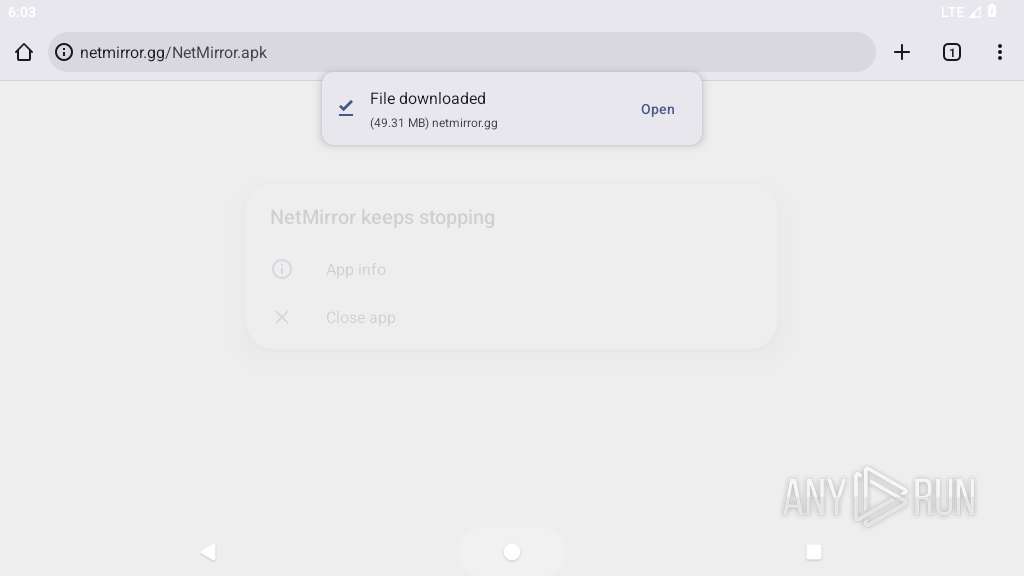
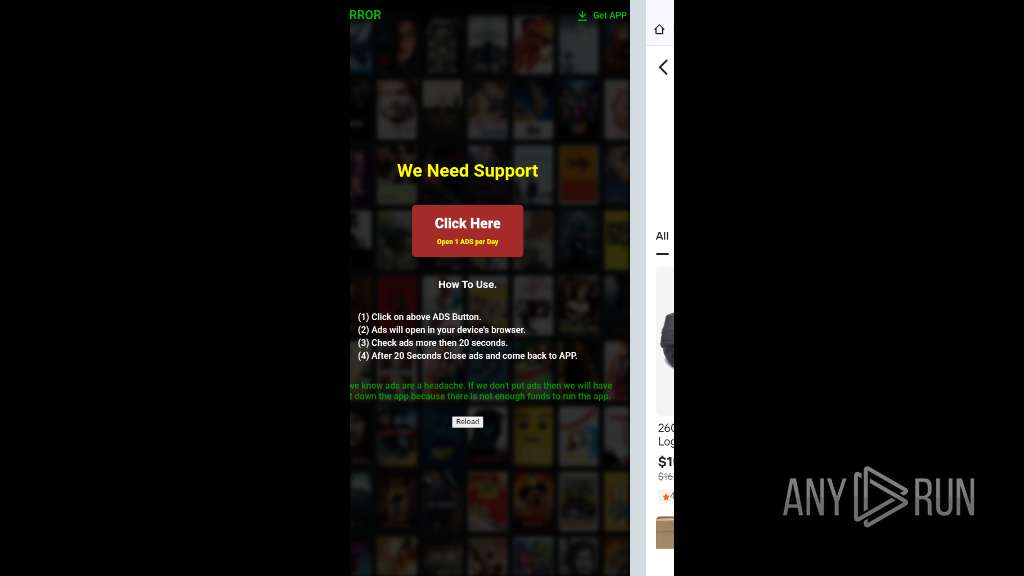
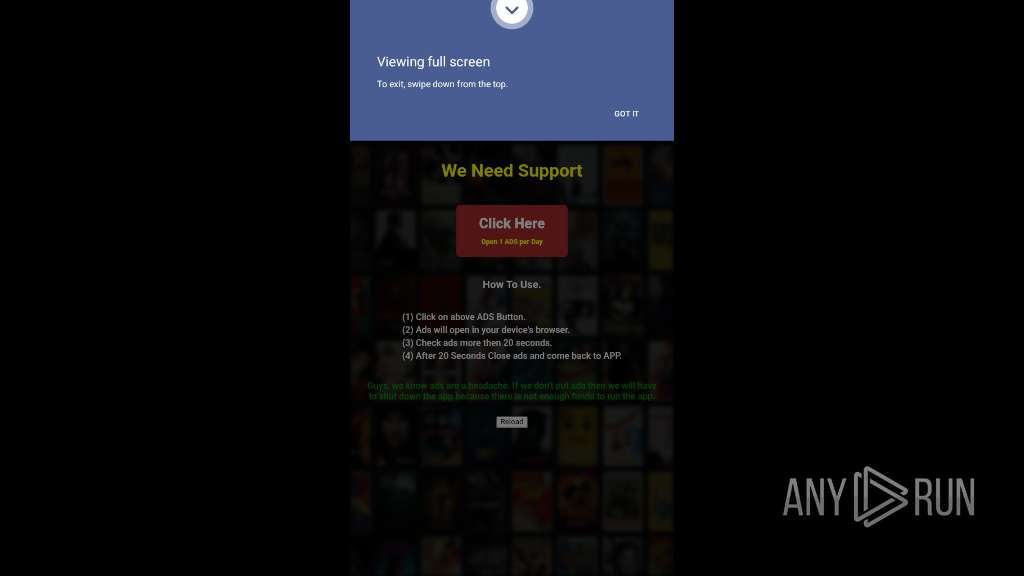
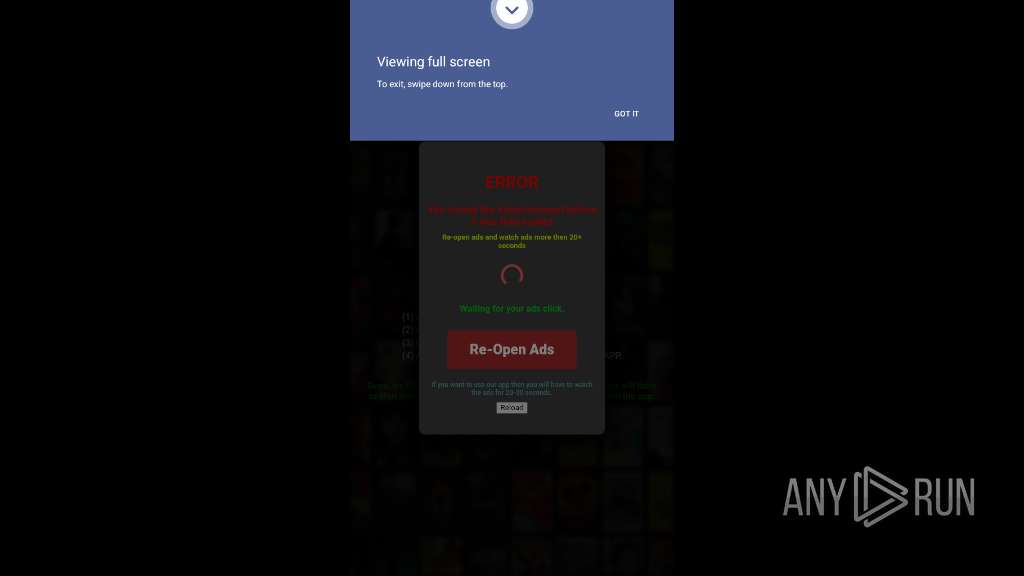
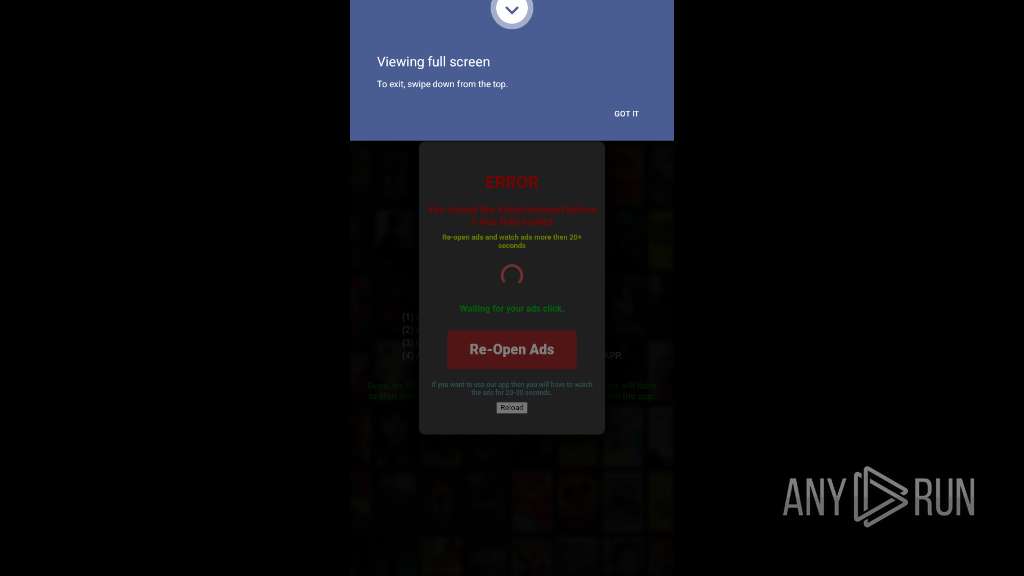
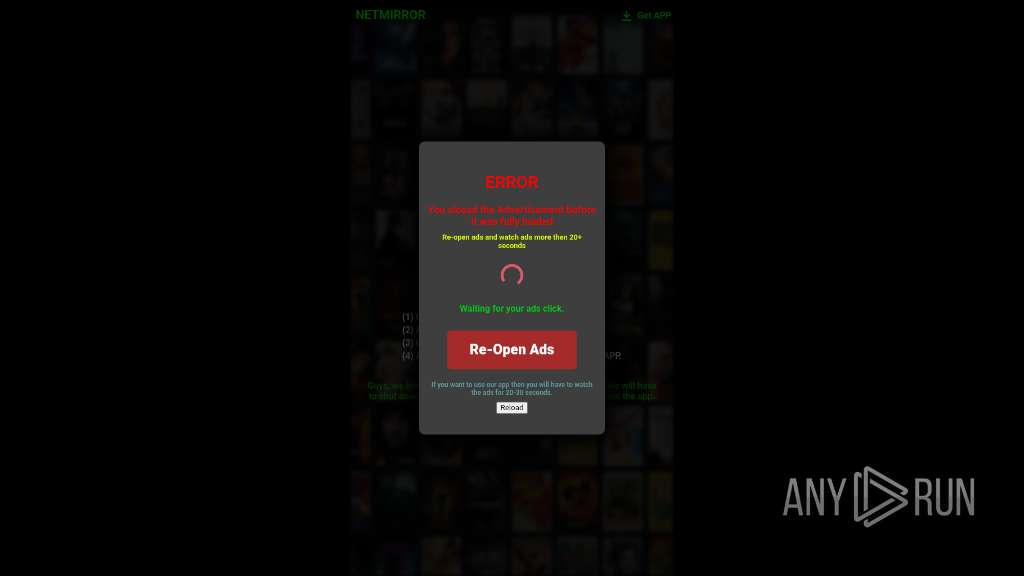
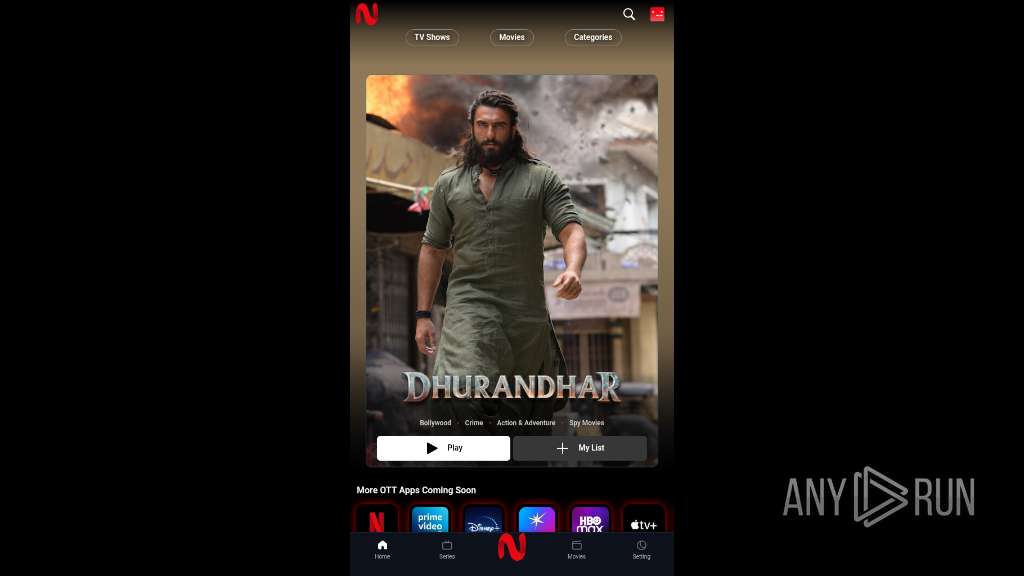
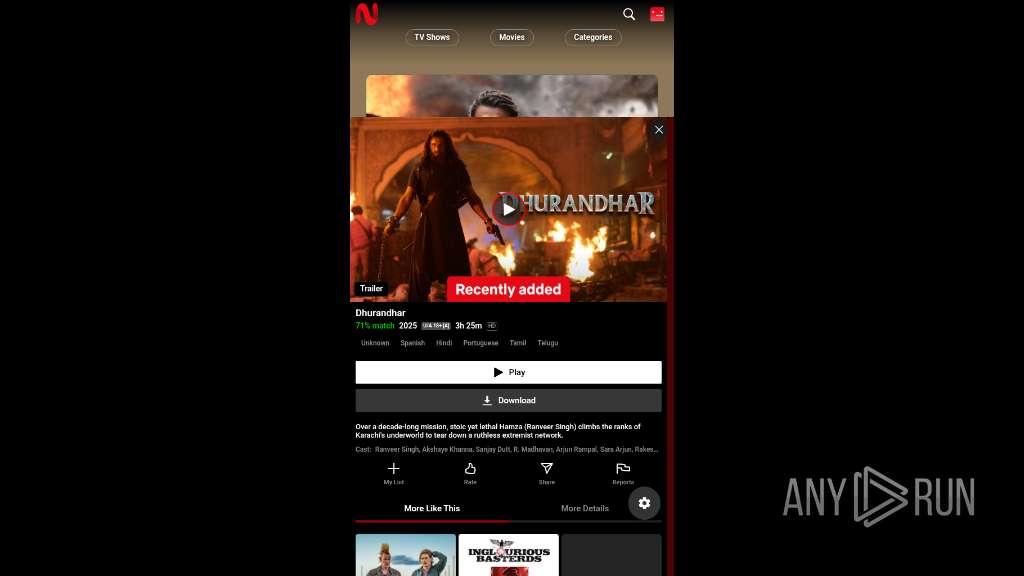
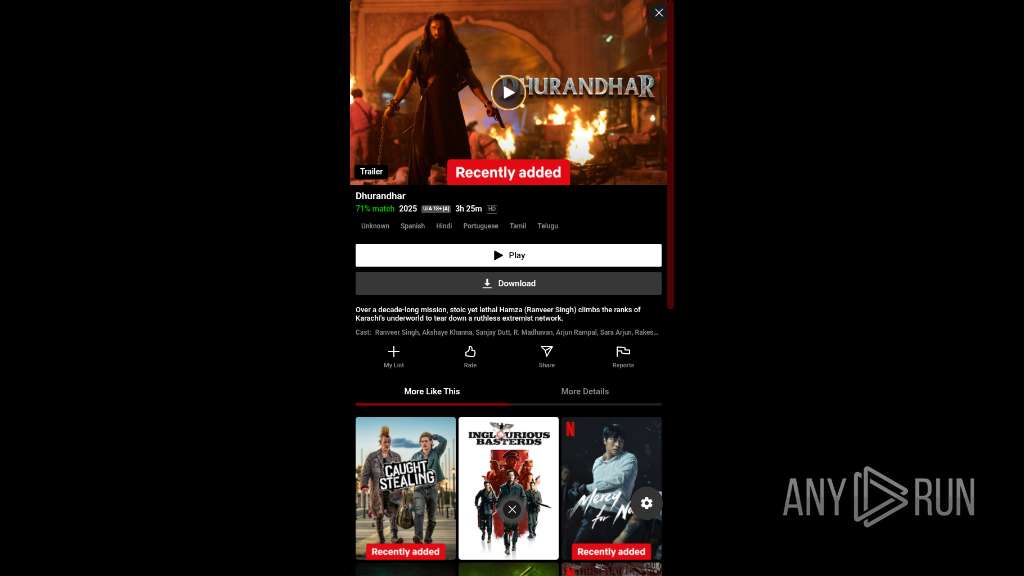
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2026, 18:01:16 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MD5: | F0DE6D3262A5C736A3B4D032759A2538 |
| SHA1: | ED7E75752B45AB7DDE7B9AA0A61B293D15E284BA |
| SHA256: | C622F6B533FF36A892BDC0C83B1D6BD20E927E42633C967B43030A15AC1E5E23 |
| SSDEEP: | 3:N8DMXX8w2KXLfn:2CZf |
MALICIOUS
PHISHING has been detected (SURICATA)
- app_process64 (PID: 2778)
SUSPICIOUS
Accesses memory information
- app_process64 (PID: 3255)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 3255)
- app_process64 (PID: 3359)
Accesses system-level resources
- app_process64 (PID: 3255)
Sets file permissions, owner, and group for a specified path
- app_process64 (PID: 3359)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 3119)
- app_process64 (PID: 3255)
- app_process64 (PID: 3359)
Verifies whether the device is connected to the internet
- app_process64 (PID: 3255)
Returns elapsed time since boot
- app_process64 (PID: 3359)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
20
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2778 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2839 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2857 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2882 | <pre-initialized> | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2899 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2947 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3105 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3108 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~lLAIuOmCFCICNtnKRO98Bg==/app.netmirror.netmirrornew-6wRPKImRIIuJpB7L26J07Q==/base.apk --oat-fd=7 --oat-location=/data/app/~~lLAIuOmCFCICNtnKRO98Bg==/app.netmirror.netmirrornew-6wRPKImRIIuJpB7L26J07Q==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context=PCL[] --classpath-dir=/data/app/~~lLAIuOmCFCICNtnKRO98Bg==/app.netmirror.netmirrornew-6wRPKImRIIuJpB7L26J07Q== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:35 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m --comments=app-version-name:3.0,app-version-code:1,art-version:340090000 | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3119 | <pre-initialized> | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 3193 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
162
Text files
28
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3255 | app_process64 | /data/data/app.netmirror.netmirrornew/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 3255 | app_process64 | /data/data/app.netmirror.netmirrornew/cache/http-cache/journal.tmp | text | |
MD5:— | SHA256:— | |||
| 3255 | app_process64 | /data/data/app.netmirror.netmirrornew/cache/http-cache/c357b8c48d7622e5b83c8ad4e4574a5d.0.tmp | text | |
MD5:— | SHA256:— | |||
| 3255 | app_process64 | /data/data/app.netmirror.netmirrornew/cache/http-cache/c357b8c48d7622e5b83c8ad4e4574a5d.1.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3255 | app_process64 | /data/data/app.netmirror.netmirrornew/cache/oat_primary/arm64/base.3255.tmp | binary | |
MD5:— | SHA256:— | |||
| 3359 | app_process64 | /data/data/app.netmirror.netmirrornew/cache/oat_primary/arm64/base.art | binary | |
MD5:— | SHA256:— | |||
| 3359 | app_process64 | /data/data/app.netmirror.netmirrornew/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 3359 | app_process64 | /data/data/app.netmirror.netmirrornew/cache/http-cache/journal | text | |
MD5:— | SHA256:— | |||
| 3359 | app_process64 | /data/data/app.netmirror.netmirrornew/cache/http-cache/c357b8c48d7622e5b83c8ad4e4574a5d.0 | text | |
MD5:— | SHA256:— | |||
| 3359 | app_process64 | /data/data/app.netmirror.netmirrornew/cache/http-cache/c357b8c48d7622e5b83c8ad4e4574a5d.1 | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
252
TCP/UDP connections
75
DNS requests
79
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2778 | app_process64 | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=0nby%2BeSf8ws7M7aYdXrUfb2ih%2FVTwnUokAf5ORRg23rhqqOIwsJli%2FnjSEX%2BeEoLHaJzC6HdghwogGqNb1zLE6kowiGnVoGKPKU%3D | US | — | — | unknown |
822 | app_process64 | GET | 204 | 142.251.141.68:443 | https://www.google.com/generate_204 | US | — | — | whitelisted |
2778 | app_process64 | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=0nby%2BeSf8ws7M7aYdXrUfb2ih%2FVTwnUokAf5ORRg23rhqqOIwsJli%2FnjSEX%2BeEoLHaJzC6HdghwogGqNb1zLE6kowiGnVoGKPKU%3D | US | — | — | unknown |
822 | app_process64 | GET | 204 | 142.251.141.68:80 | http://www.google.com/gen_204 | US | — | — | whitelisted |
2778 | app_process64 | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&laf=b64bin&json=standard | US | — | — | whitelisted |
2778 | app_process64 | GET | 200 | 216.58.206.46:80 | http://clients2.google.com/time/1/current?cup2key=9:qykG3WysQcpyQISLVs4fDz9p-Jxnp2Br9lyLE8-duwM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
822 | app_process64 | GET | 204 | 172.217.16.163:80 | http://connectivitycheck.gstatic.com/generate_204 | US | — | — | whitelisted |
2778 | app_process64 | POST | 400 | 142.251.141.138:443 | https://androidchromeprotect.pa.googleapis.com/v1/download | US | text | 586 b | whitelisted |
2778 | app_process64 | POST | — | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=0nby%2BeSf8ws7M7aYdXrUfb2ih%2FVTwnUokAf5ORRg23rhqqOIwsJli%2FnjSEX%2BeEoLHaJzC6HdghwogGqNb1zLE6kowiGnVoGKPKU%3D | US | — | — | unknown |
1756 | app_process64 | POST | 200 | 64.233.167.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | US | binary | 778 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
443 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.251.141.68:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 172.217.16.163:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
822 | app_process64 | 142.251.141.68:80 | www.google.com | GOOGLE | US | whitelisted |
2778 | app_process64 | 216.58.206.46:80 | clients2.google.com | GOOGLE | US | whitelisted |
2778 | app_process64 | 172.67.155.16:443 | netmirror.gg | CLOUDFLARENET | US | whitelisted |
2778 | app_process64 | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2778 | app_process64 | 142.251.141.68:443 | www.google.com | GOOGLE | US | whitelisted |
2778 | app_process64 | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
2778 | app_process64 | 142.251.141.138:443 | androidchromeprotect.pa.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
netmirror.gg |
| whitelisted |
accounts.google.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
androidchromeprotect.pa.googleapis.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2778 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2778 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
822 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
339 | netd | Misc activity | INFO [ANY.RUN] .cc TLD domain request |
339 | netd | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
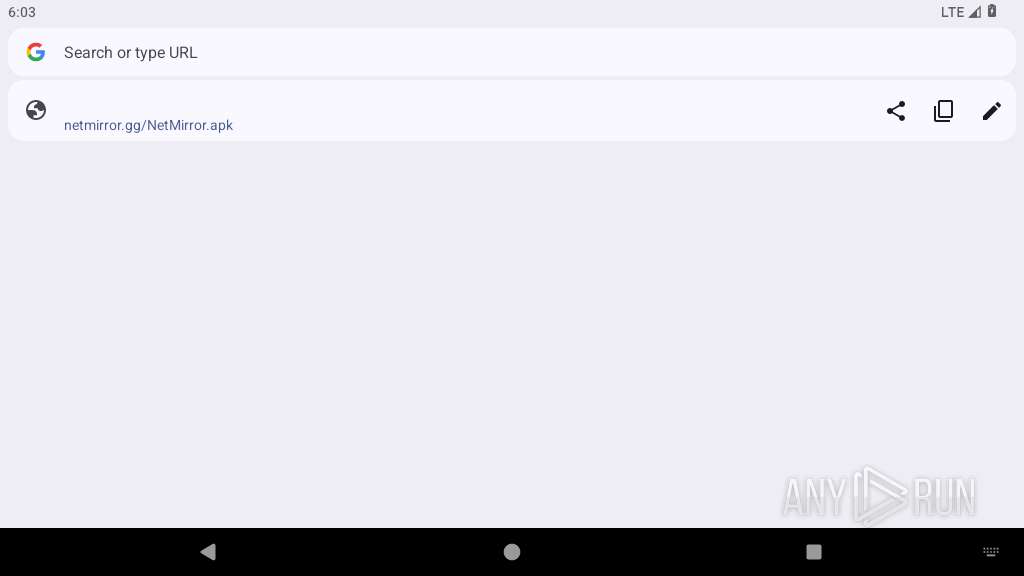
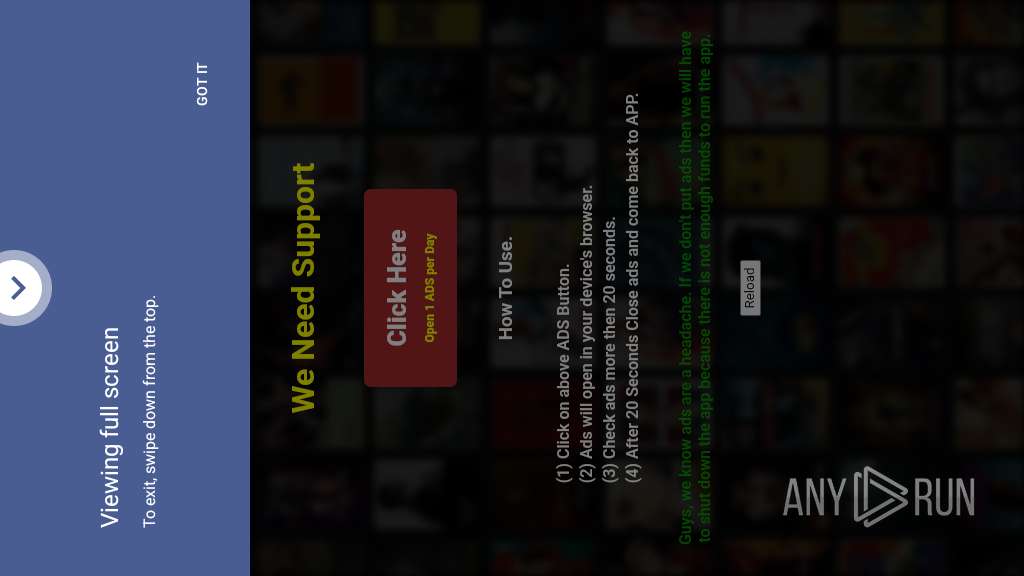
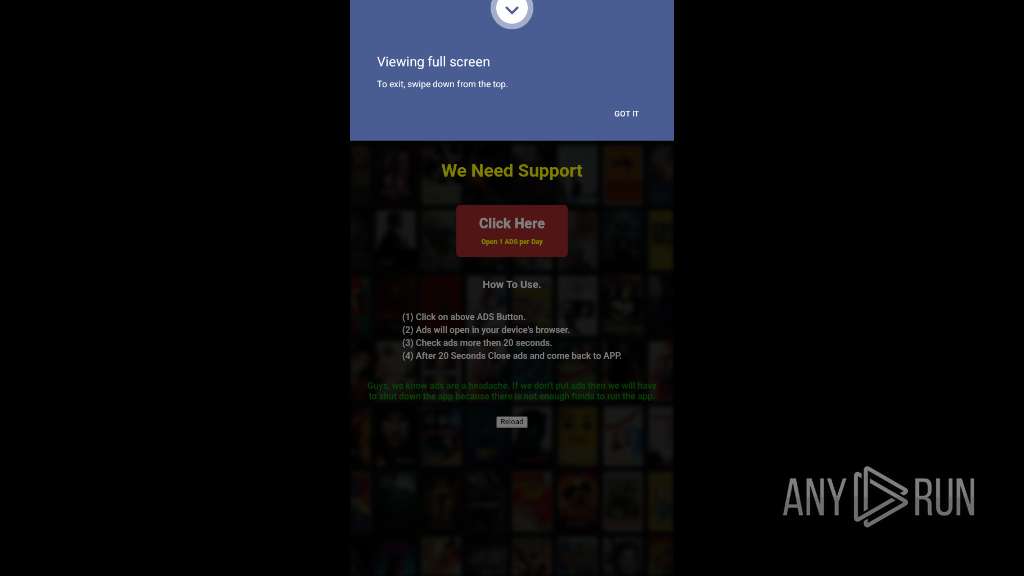
2778 | app_process64 | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (ey43 .com) |
2778 | app_process64 | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (ey43 .com) |
339 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
339 | netd | Misc activity | ET TA_ABUSED_SERVICES Observed DNS Query to Real-time Web Stats Domain (whos .amung .us) |