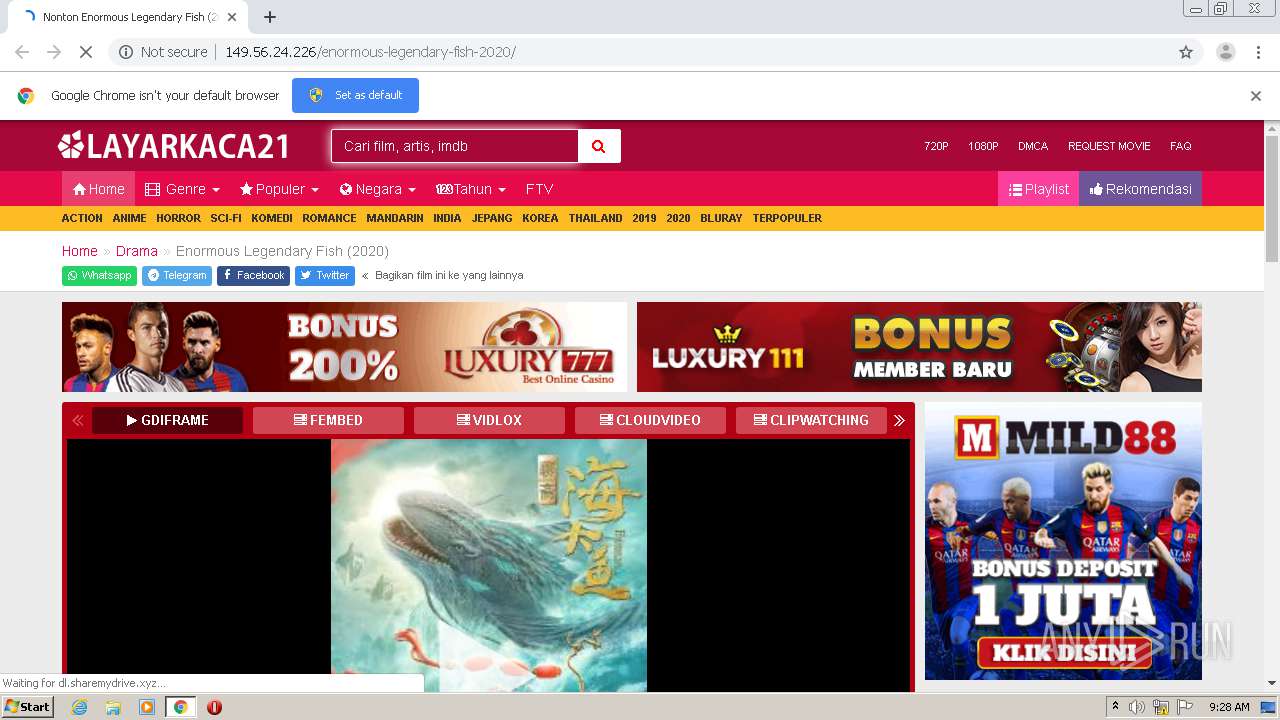
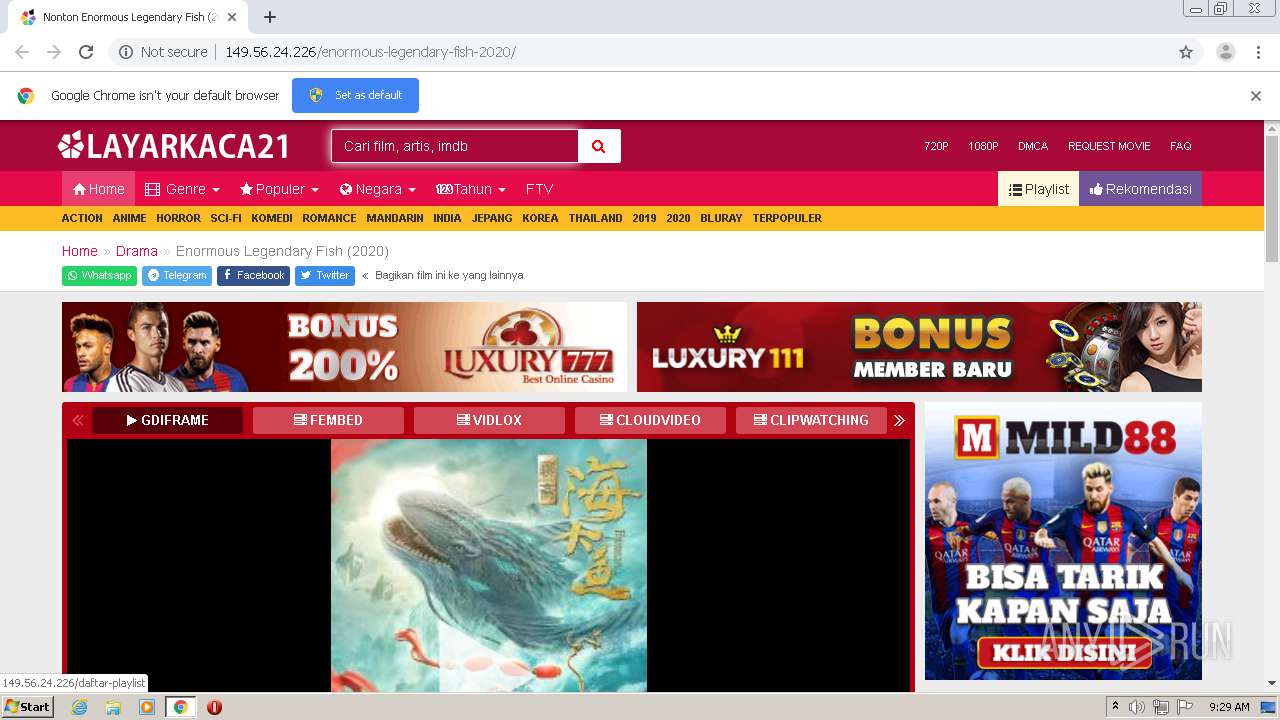
| URL: | http://149.56.24.226/enormous-legendary-fish-2020/ |
| Full analysis: | https://app.any.run/tasks/9b6e35ea-a02e-42ca-ac4c-81e47a38ad88 |
| Verdict: | Malicious activity |
| Analysis date: | January 04, 2021, 09:28:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 14F90E58D96838492FDA80350FF50FEF |
| SHA1: | 0B816EDBFFFB06BBD120B01D8143736F4D97C87C |
| SHA256: | C5F9F6A101D84193A1BD28A962812CD0F9224503DC34075AE07CB23F10508C60 |
| SSDEEP: | 3:N1Kpb1WhQxtDNIFw:CO2tDaFw |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2180)
- chrome.exe (PID: 1848)
Application launched itself
- chrome.exe (PID: 2180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17702580620707085879 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15617532298831163230 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13291633292147153316 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1136 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16921180396497047751 --mojo-platform-channel-handle=1544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8295496205173220027 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4729955857069893409 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13065331152315312990 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://149.56.24.226/enormous-legendary-fish-2020/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16834966201560440741 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
590
Read events
533
Write events
54
Delete events
3
Modification events
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2180-13254226116355375 |
Value: 259 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
42
Text files
63
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FF2DFC4-884.pma | — | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF154223.TMP | — | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\558e463a-212c-4394-8113-a61d33cb8218.tmp | — | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1541d5.TMP | text | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1543b9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
115
DNS requests
83
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1848 | chrome.exe | GET | 302 | 172.64.167.8:80 | http://redirector.gdriveplayer.to/drive/index.php?id=ug8v1ojkNKnYP%2BEnGoShCwevZBghXpiuJkN6121fofr5iFMs0xtIMz64QonQXPiutiy6MmQc0h04tDUO6Jywlv7IcC%2BYqJMZlQ43UNvtLnQ99R3r%2BgiZOdxrlw6bfedJxGqcG16fYtlm%2B4puoDJQSnq1lZahsQfHPq14vVmZ%2FUjZ%2BReDwvH4PLco3Jn9n%2FGfpyK6z1S4bDNDtErZZirpoJ6Hm8BjY9ImBhRs5eNwyvwGsPK6ydxXu1Ezoq1y0Yse0%3D&ref=http%3A%2F%2F149.56.24.226%2Fenormous-legendary-fish-2020%2F&sandbox=&ref=http://149.56.24.226/enormous-legendary-fish-2020/&res=360 | US | — | — | suspicious |
1848 | chrome.exe | GET | 200 | 149.56.24.226:80 | http://149.56.24.226/xjs.php?x=d21x | CA | html | 1.33 Kb | unknown |
1848 | chrome.exe | GET | 200 | 149.56.24.226:80 | http://149.56.24.226/enormous-legendary-fish-2020/ | CA | html | 14.9 Kb | unknown |
1848 | chrome.exe | GET | 200 | 172.64.195.30:80 | http://s1.sharemydrive.xyz/wp-content/uploads/2020/07/film-ayyappanum-koshiyum-2020-lk21.jpg | US | image | 16.9 Kb | suspicious |
1848 | chrome.exe | POST | 200 | 149.56.24.226:80 | http://149.56.24.226/ajax/movie.php | CA | html | 584 b | unknown |
1848 | chrome.exe | GET | 200 | 139.45.195.46:80 | http://toglooman.com/1?z=3524072 | US | text | 3.02 Kb | suspicious |
1848 | chrome.exe | GET | 200 | 149.56.24.226:80 | http://149.56.24.226/ajax/counter.php?slug=enormous-legendary-fish-2020 | CA | text | 33 b | unknown |
1848 | chrome.exe | GET | 200 | 139.45.195.81:80 | http://graizoah.com/tag.min.js | US | text | 24.3 Kb | suspicious |
1848 | chrome.exe | GET | 200 | 151.101.194.114:80 | http://ssl.p.jwpcdn.com/player/v/8.8.2/jwplayer.core.controls.html5.js | US | text | 74.3 Kb | whitelisted |
1848 | chrome.exe | GET | 200 | 139.45.197.9:80 | http://inpagepush.com/400/3521780 | US | text | 27.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1848 | chrome.exe | 172.64.195.30:80 | s8.sharemydrive.xyz | Cloudflare Inc | US | suspicious |
1848 | chrome.exe | 149.56.24.226:80 | — | OVH SAS | CA | unknown |
1848 | chrome.exe | 151.101.66.109:443 | cdn.jsdelivr.net | Fastly | US | unknown |
1848 | chrome.exe | 172.64.194.30:80 | s8.sharemydrive.xyz | Cloudflare Inc | US | malicious |
1848 | chrome.exe | 216.58.212.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1848 | chrome.exe | 172.217.16.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1848 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1848 | chrome.exe | 172.217.18.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
1848 | chrome.exe | 142.250.103.84:443 | accounts.google.com | Google Inc. | US | unknown |
1848 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
s8.sharemydrive.xyz |
| suspicious |
www.gstatic.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
s4.sharemydrive.xyz |
| suspicious |
safebrowsing.googleapis.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
s6.sharemydrive.xyz |
| suspicious |
s2.sharemydrive.xyz |
| suspicious |
s1.sharemydrive.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1848 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |