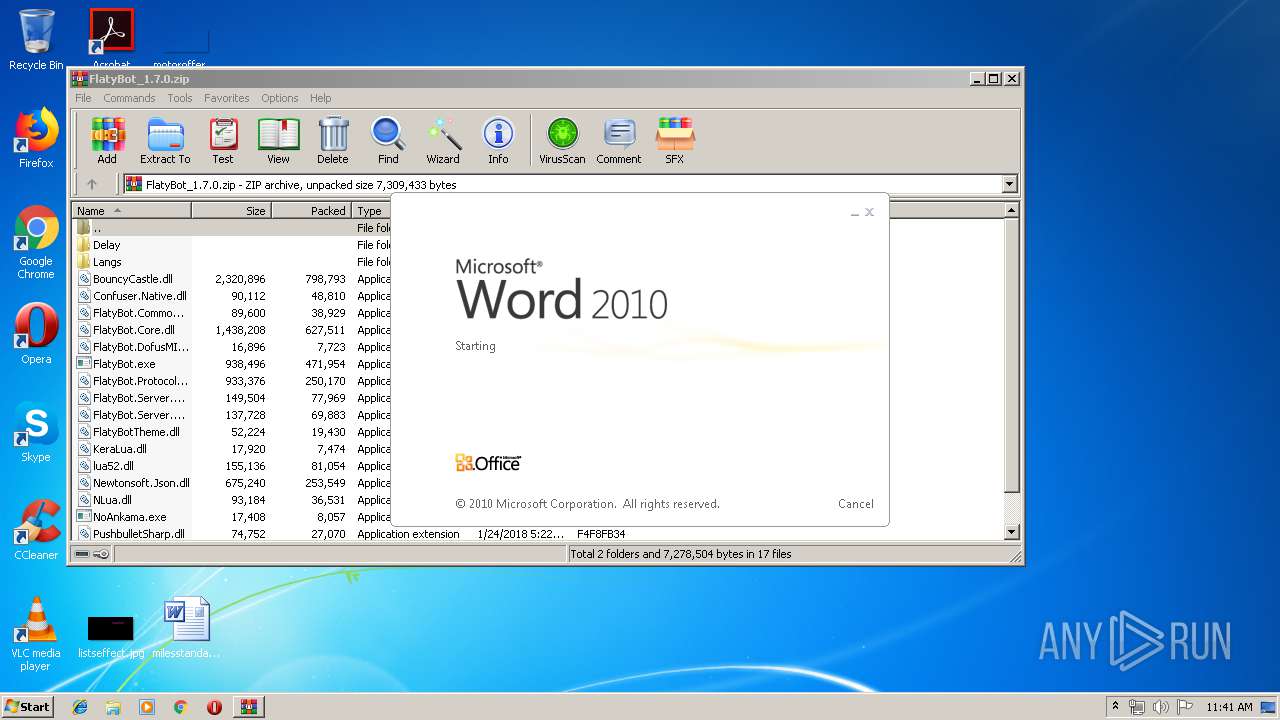
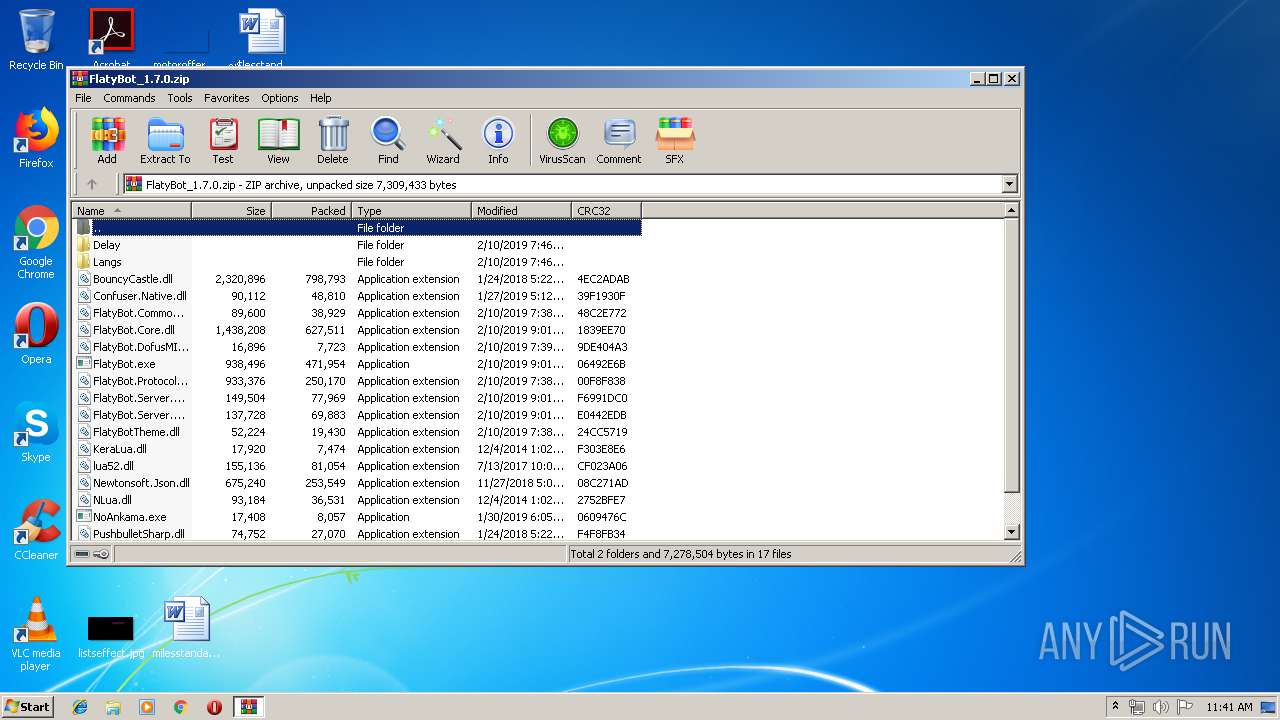
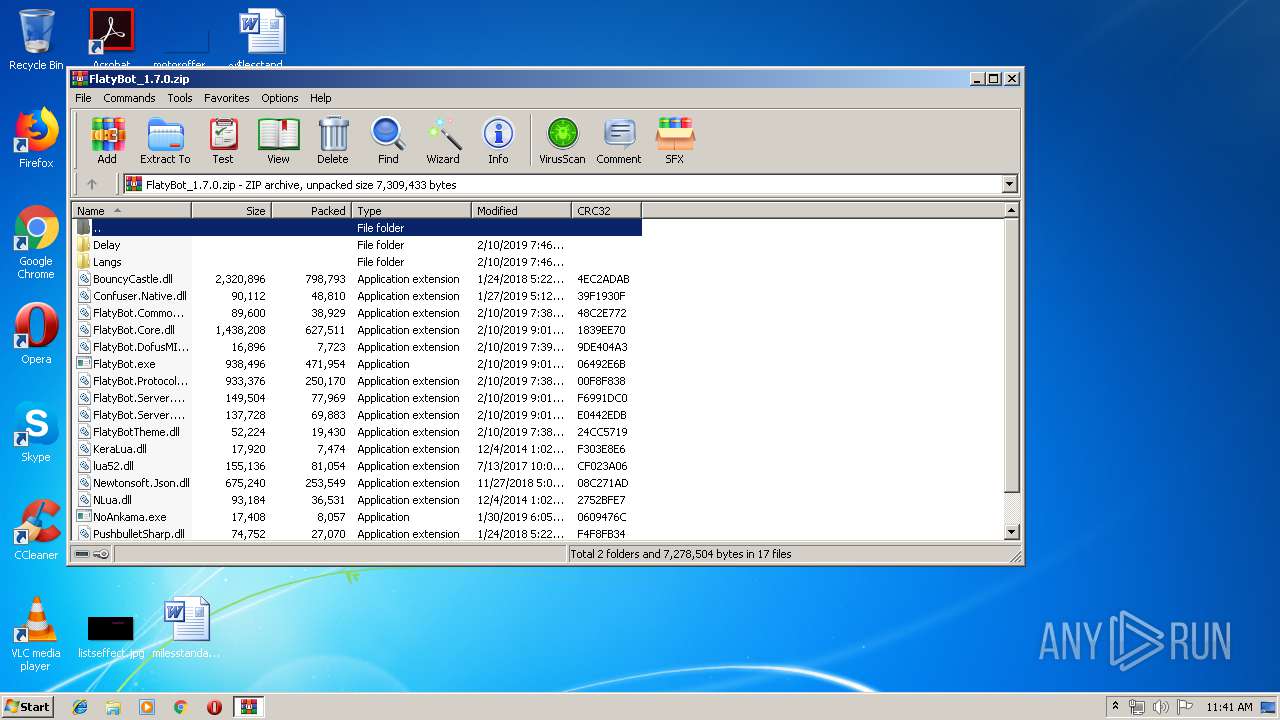
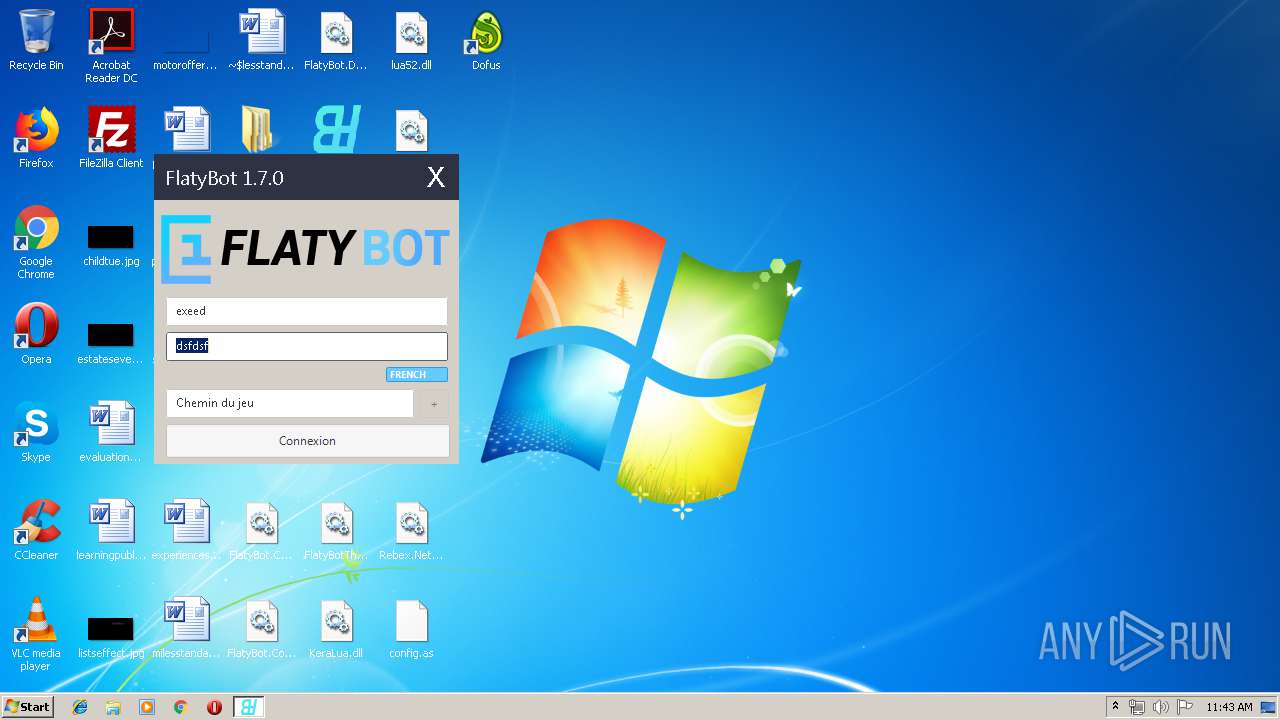
| File name: | FlatyBot_1.7.0.zip |
| Full analysis: | https://app.any.run/tasks/b7f03ac1-c91b-4662-ae8a-547d96325d9b |
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2019, 10:40:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | EF9B5DFE0543111A500D7EC66788A25E |
| SHA1: | A34FCFA8824695097AA1E807A94108F07991455C |
| SHA256: | C5F99F034B241E880D021DC7AE72FC20F3666454A95EA6B4267828E8A0CBCABB |
| SSDEEP: | 49152:VRuPkY6VGWDz9bVebj8j3h1UdOG8/pYQW8Sc/2SkRc2tP+j8l/ORt:zafqG8hbljwdOG8ZW8L/1SxtP+ga |
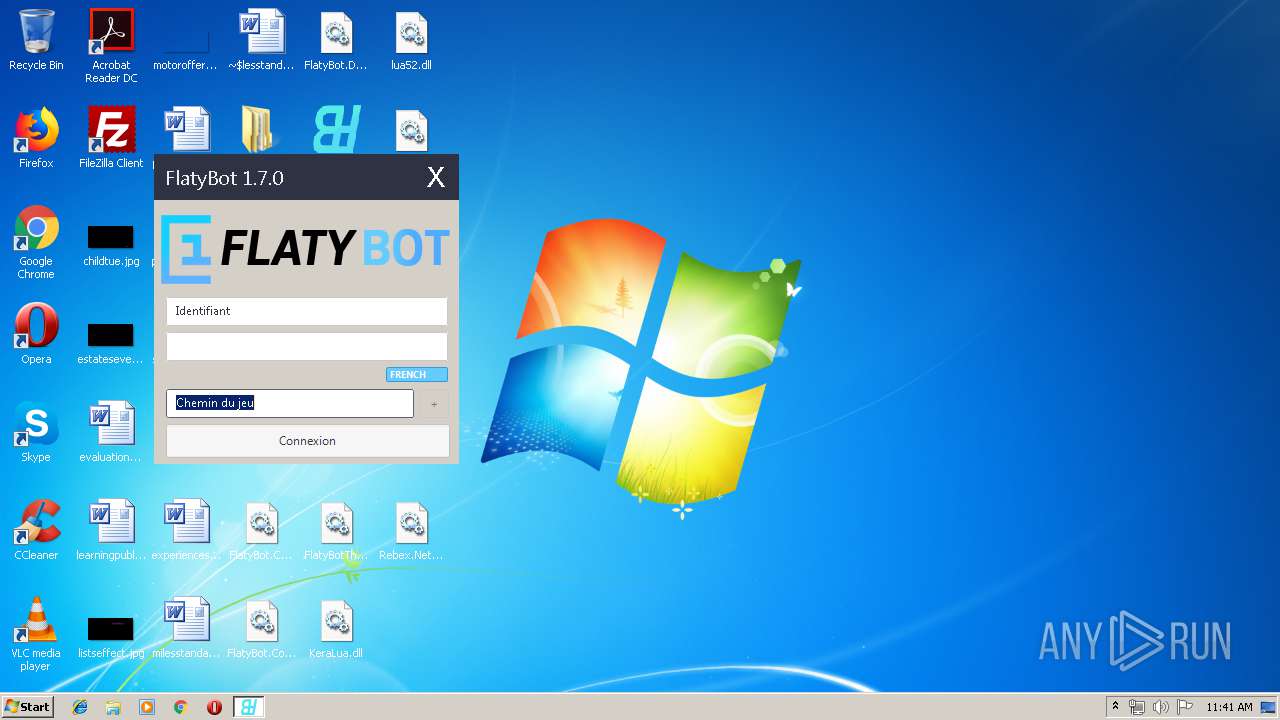
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3092)
- FlatyBot.exe (PID: 2676)
- transition.exe (PID: 1648)
- transition-service.exe (PID: 2136)
- transition.exe (PID: 2868)
- transition-service.exe (PID: 2948)
Application was dropped or rewritten from another process
- FlatyBot.exe (PID: 2676)
- dofus.exe (PID: 680)
- transition.exe (PID: 1648)
- transition-service.exe (PID: 2136)
- Dofus.exe (PID: 3536)
- transition.exe (PID: 2868)
- transition-service.exe (PID: 2948)
SUSPICIOUS
Connects to unusual port
- FlatyBot.exe (PID: 2676)
Executable content was dropped or overwritten
- chrome.exe (PID: 2200)
- chrome.exe (PID: 2808)
- WinRAR.exe (PID: 4000)
- dofus.exe (PID: 680)
- transition.exe (PID: 1648)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2200)
Creates files in the user directory
- transition.exe (PID: 1648)
Check for Java to be installed
- transition.exe (PID: 2868)
Executes JAVA applets
- transition.exe (PID: 2868)
Creates a software uninstall entry
- transition.exe (PID: 1648)
INFO
Application launched itself
- chrome.exe (PID: 2200)
- chrome.exe (PID: 2316)
Creates files in the user directory
- WINWORD.EXE (PID: 768)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 768)
Reads settings of System Certificates
- chrome.exe (PID: 1572)
- chrome.exe (PID: 2808)
Changes settings of System certificates
- chrome.exe (PID: 2808)
Reads Internet Cache Settings
- chrome.exe (PID: 2200)
Dropped object may contain Bitcoin addresses
- dofus.exe (PID: 680)
- transition.exe (PID: 2868)
- transition.exe (PID: 1648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:02:10 20:39:00 |
| ZipCRC: | 0x9de404a3 |
| ZipCompressedSize: | 7723 |
| ZipUncompressedSize: | 16896 |
| ZipFileName: | FlatyBot.DofusMITM.dll |
Total processes
93
Monitored processes
48
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
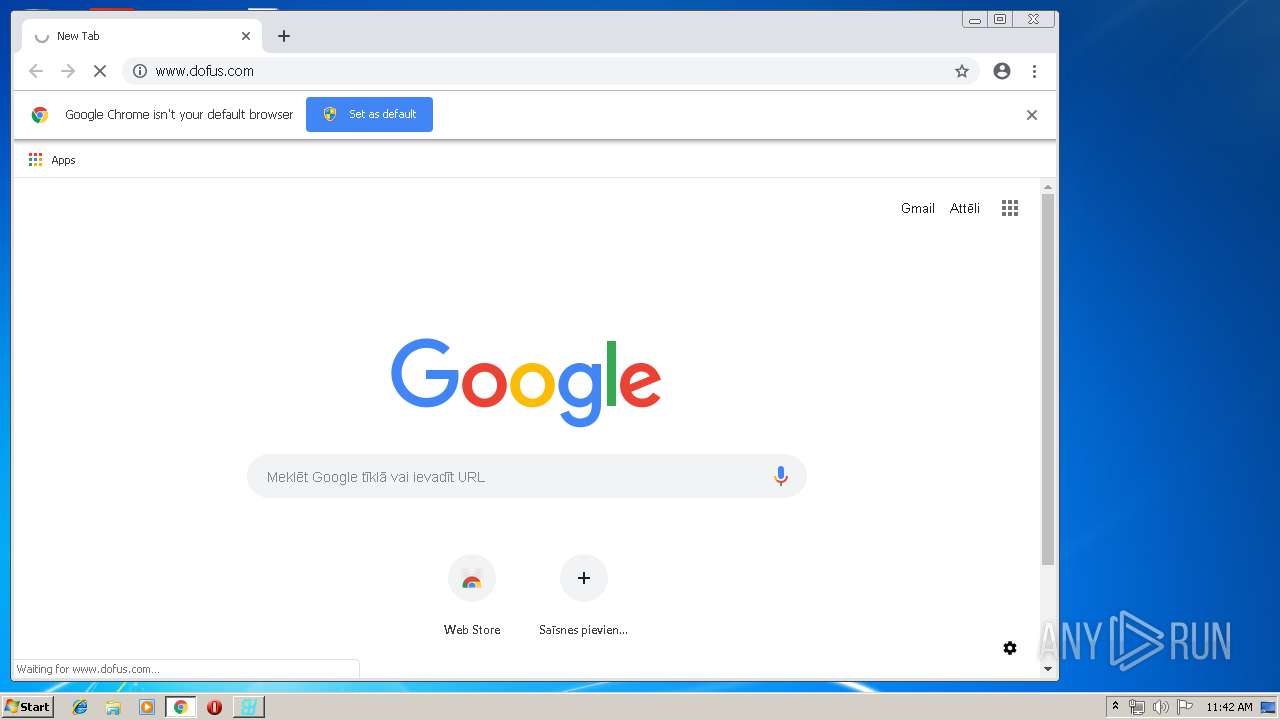
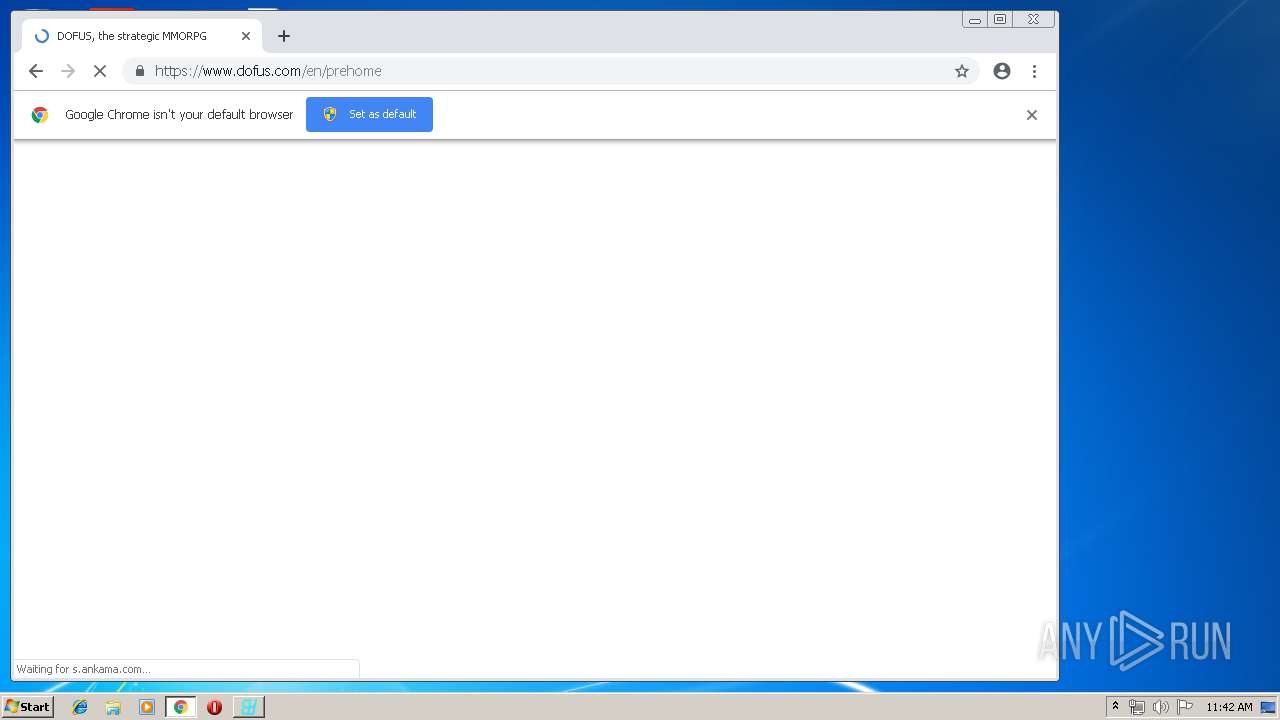
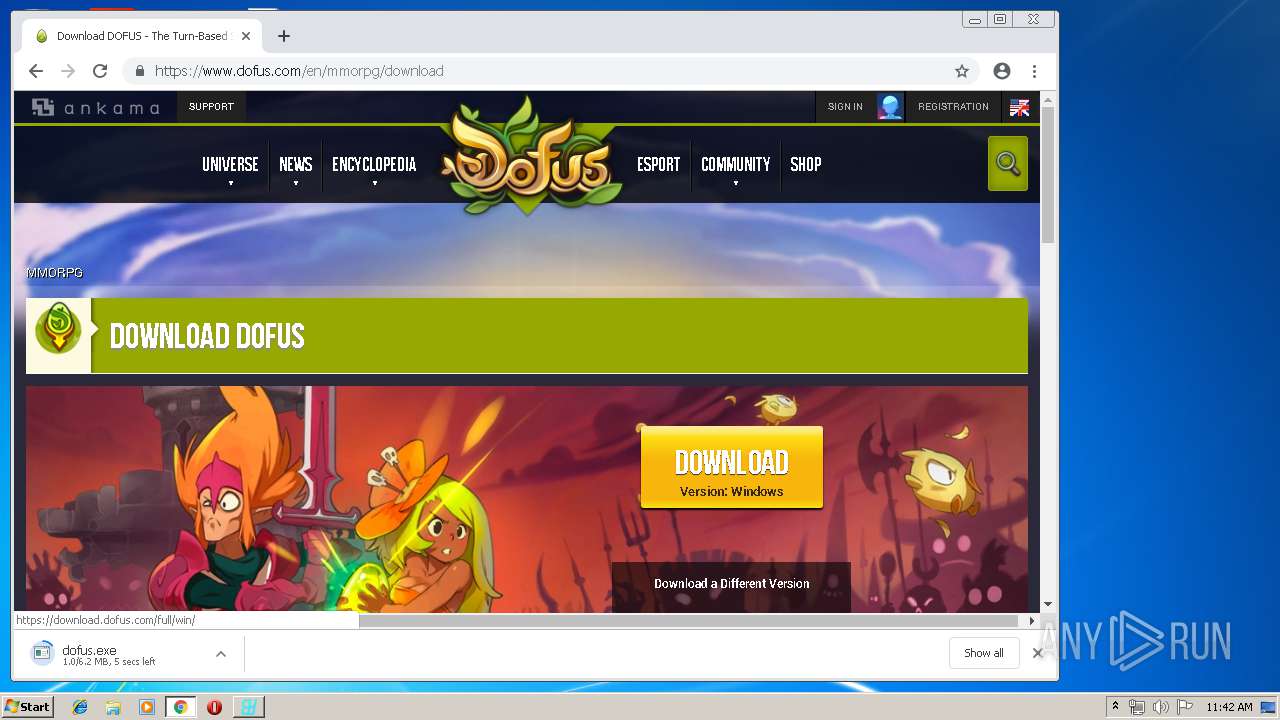
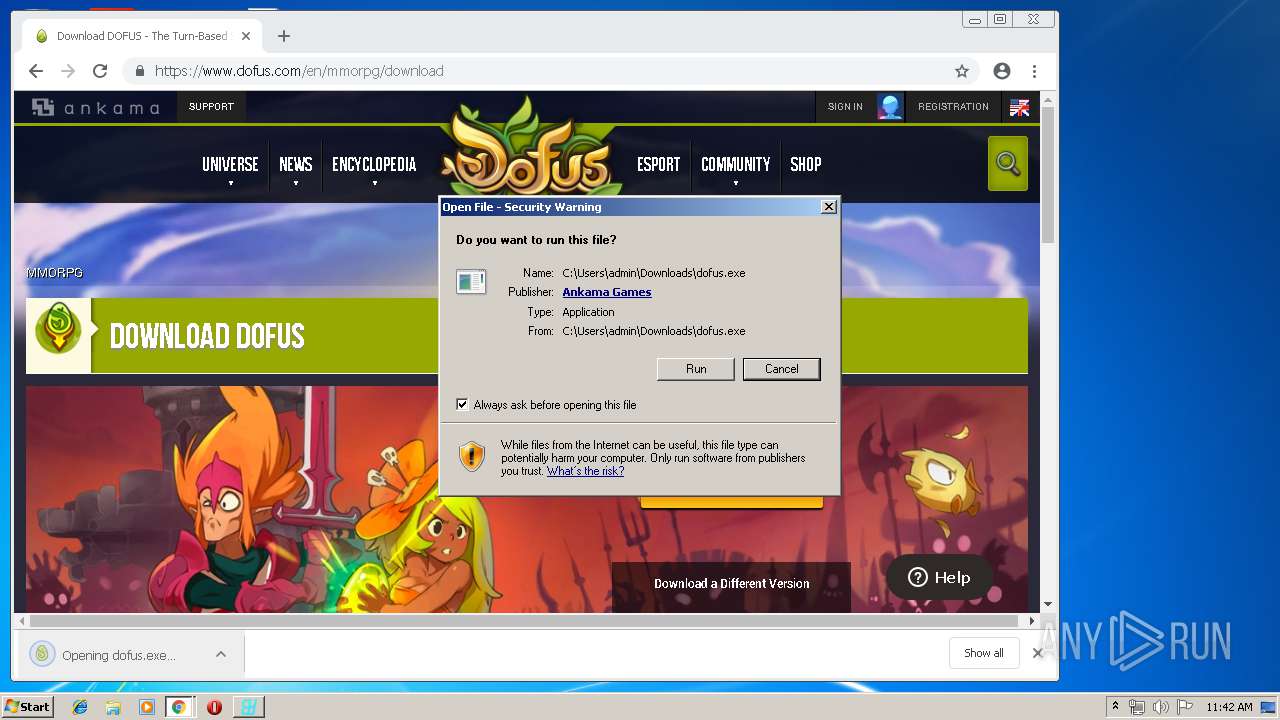
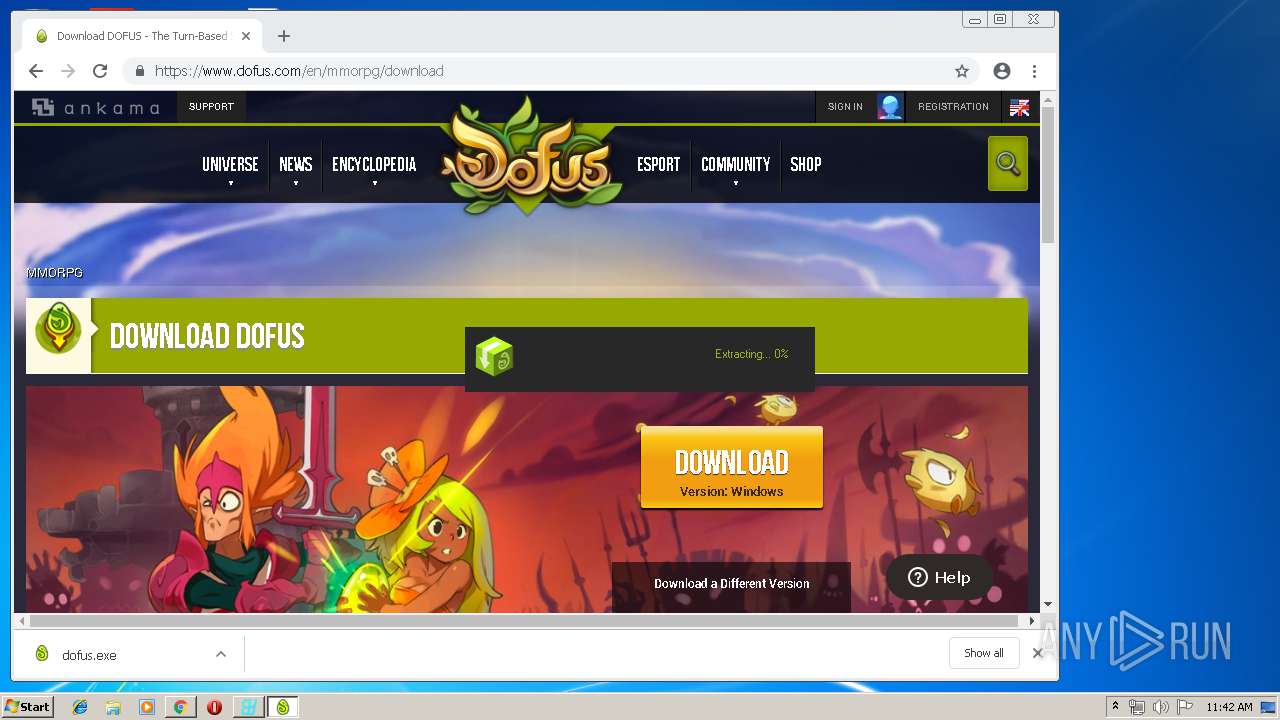
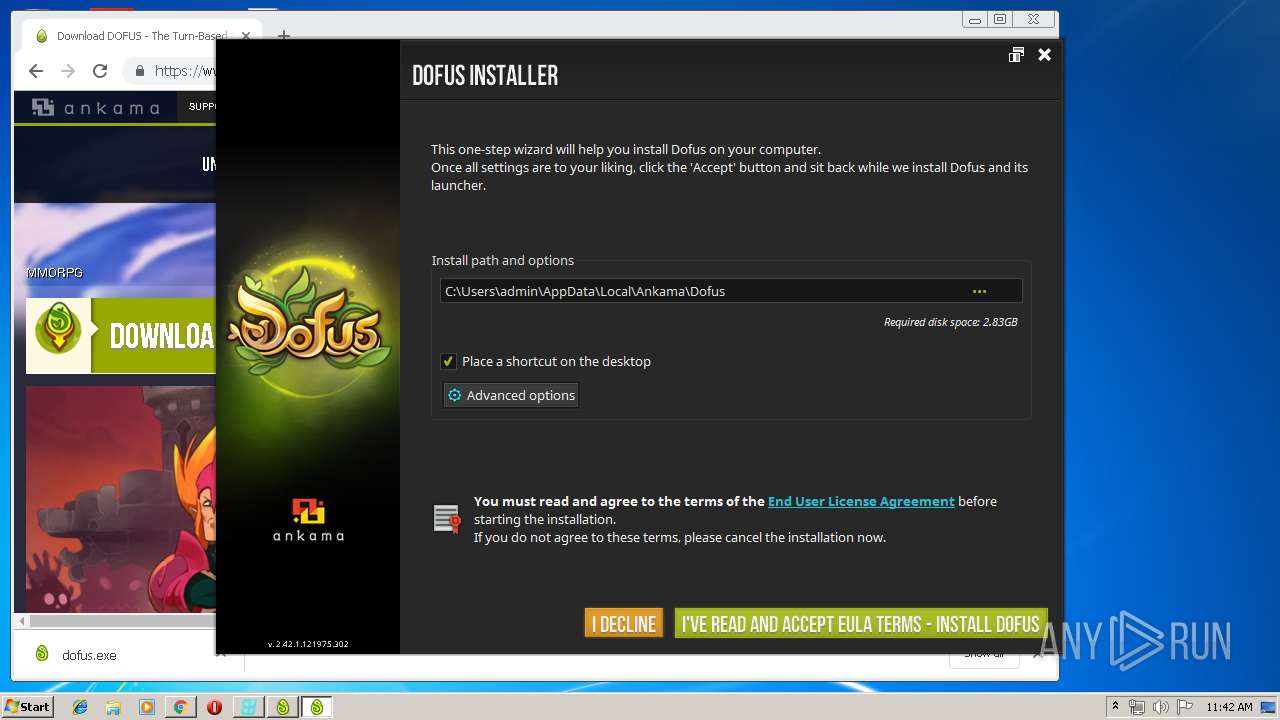
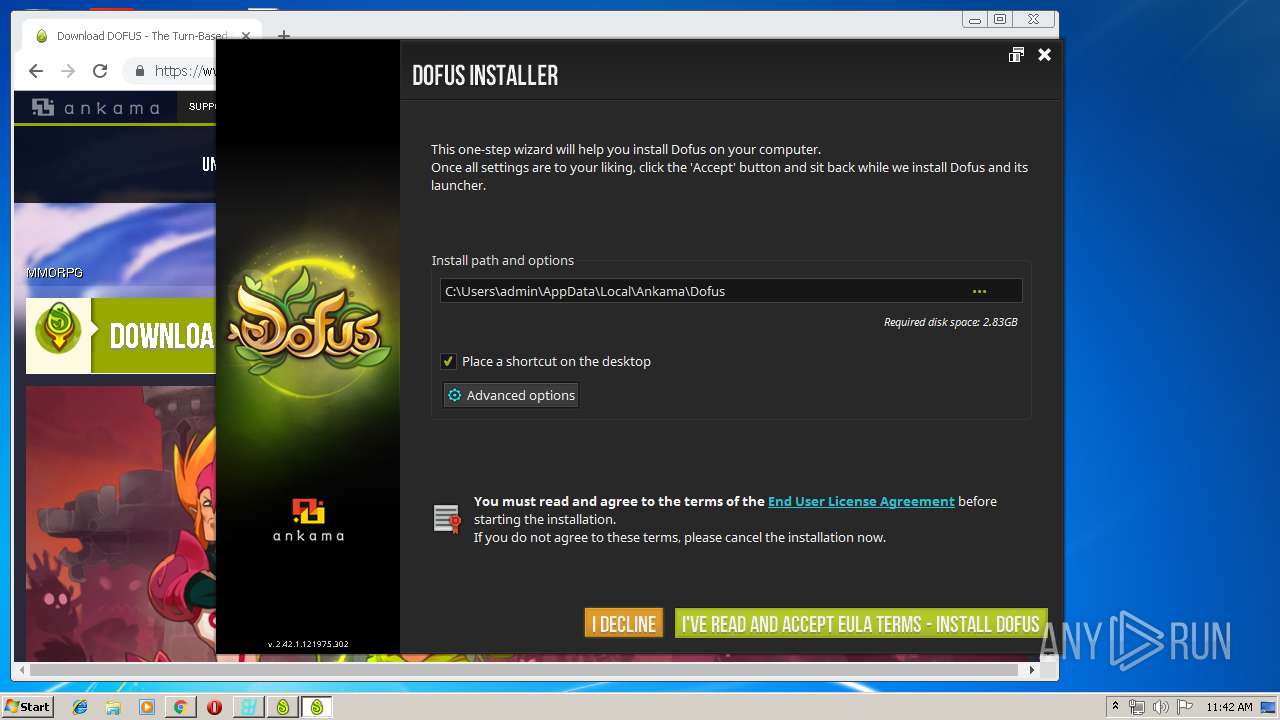
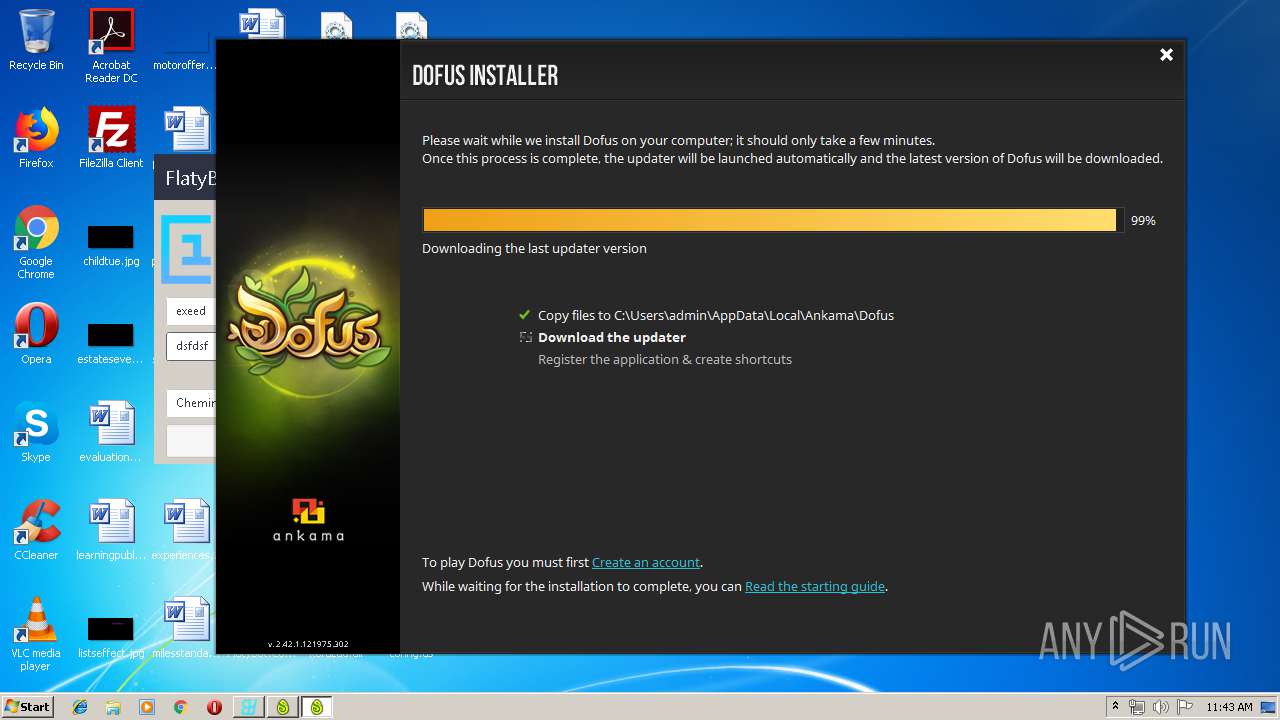
| 680 | "C:\Users\admin\Downloads\dofus.exe" | C:\Users\admin\Downloads\dofus.exe | chrome.exe | ||||||||||||
User: admin Company: Ankama Studio Integrity Level: MEDIUM Description: Launcher Dofus Exit code: 0 Version: 3.11.1 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\milesstandard.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,6137307180270770229,5528392947846488574,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10508489376903475127 --mojo-platform-channel-handle=2784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,8141810199613671770,9778469275299466564,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16538401679517005464 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16538401679517005464 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,6137307180270770229,5528392947846488574,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1410249767161896663 --mojo-platform-channel-handle=1476 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
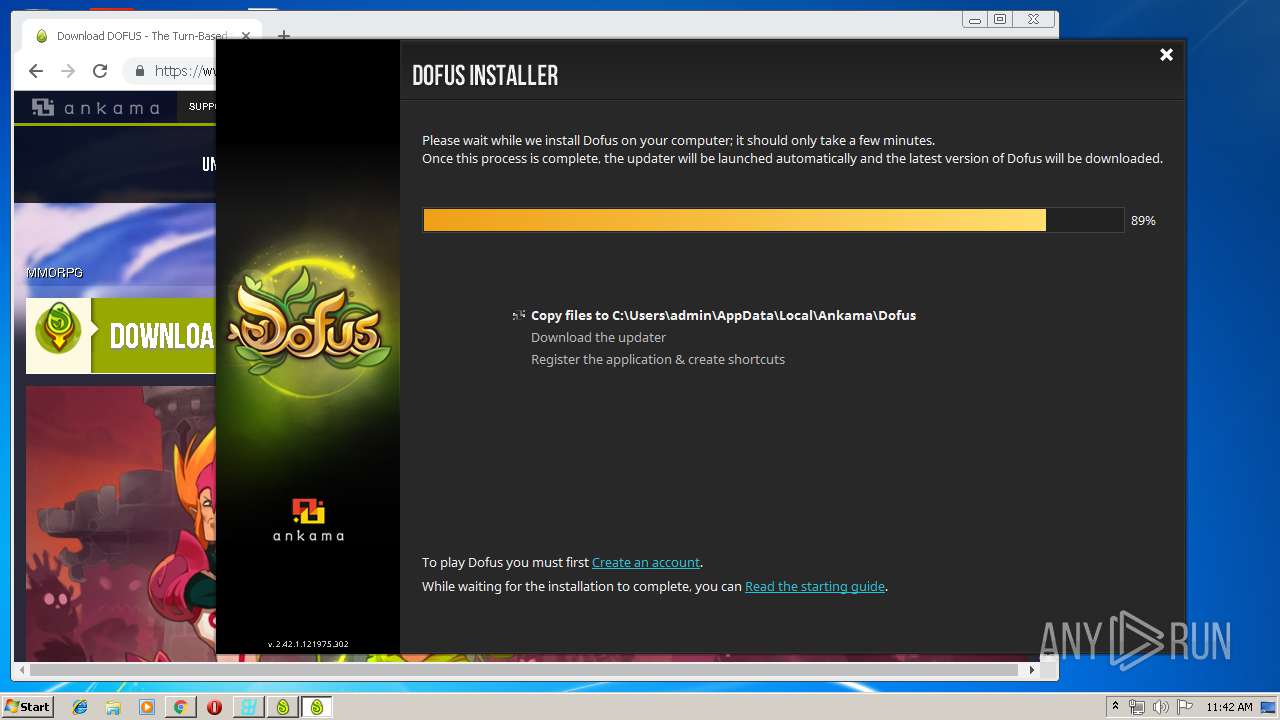
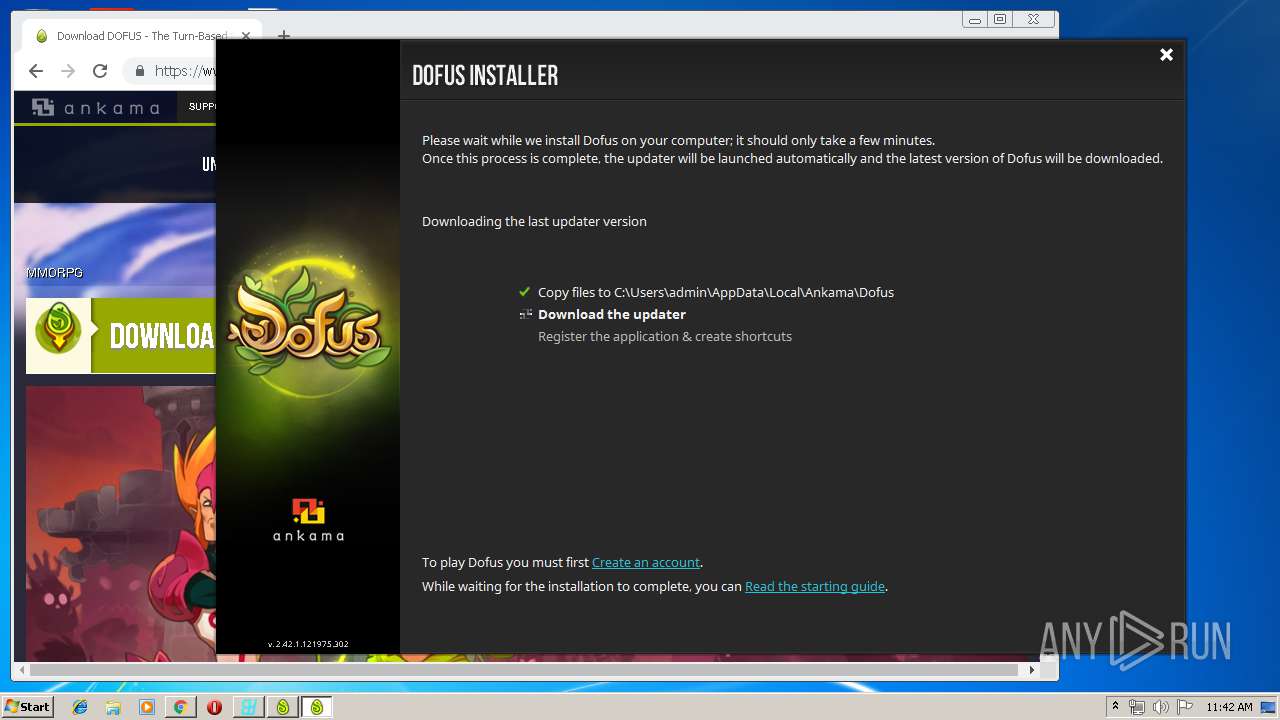
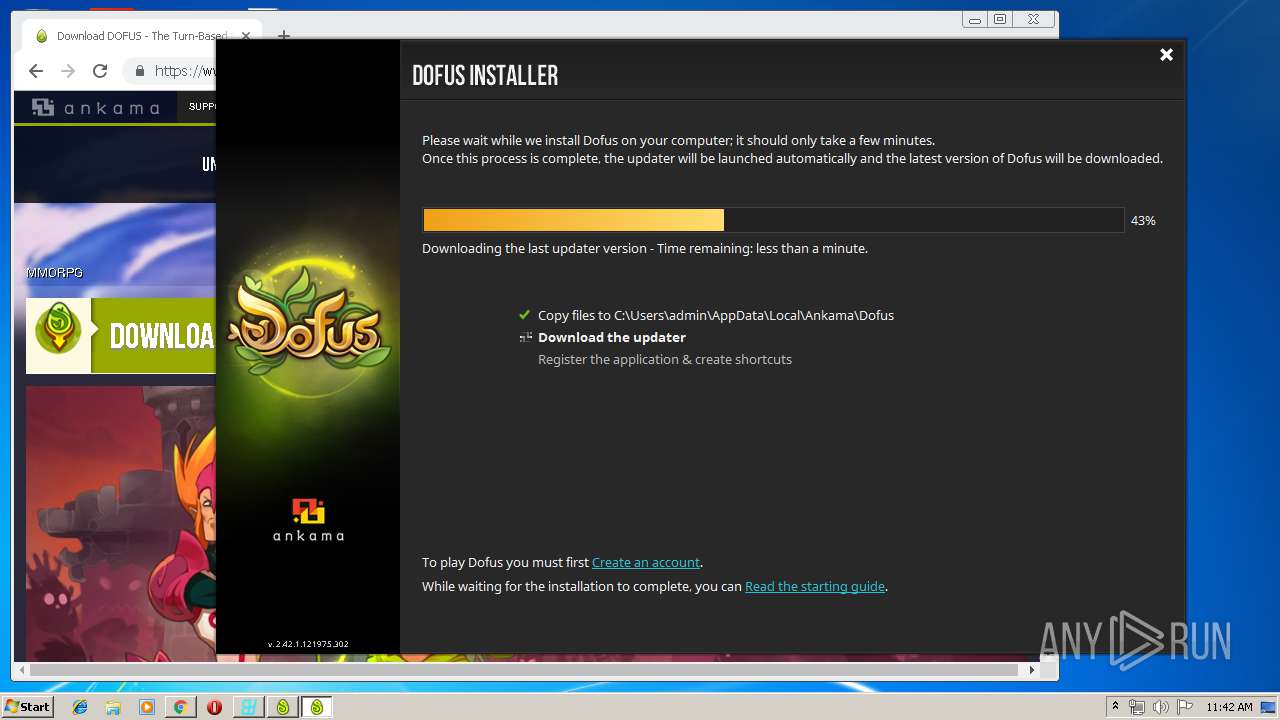
| 1648 | "transition.exe" "--no-footprint" "--no-restart" "--bootstrap-path=C:\Users\admin\Downloads\dofus.exe" "--launched-from=C:\Users\admin\Downloads" | C:\Users\admin\AppData\Local\Temp\akma00664\transition.exe | dofus.exe | ||||||||||||
User: admin Company: Ankama Integrity Level: MEDIUM Description: Updater Ankama Exit code: 0 Version: 3.2.0.0 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d500f18,0x6d500f28,0x6d500f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,8141810199613671770,9778469275299466564,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7774977326000305359 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7774977326000305359 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1748 | C:\ProgramData\Oracle\Java\javapath\java.exe -version | C:\ProgramData\Oracle\Java\javapath\java.exe | — | transition.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,8141810199613671770,9778469275299466564,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4981018817515701787 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4981018817515701787 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 129
Read events
2 801
Write events
308
Delete events
20
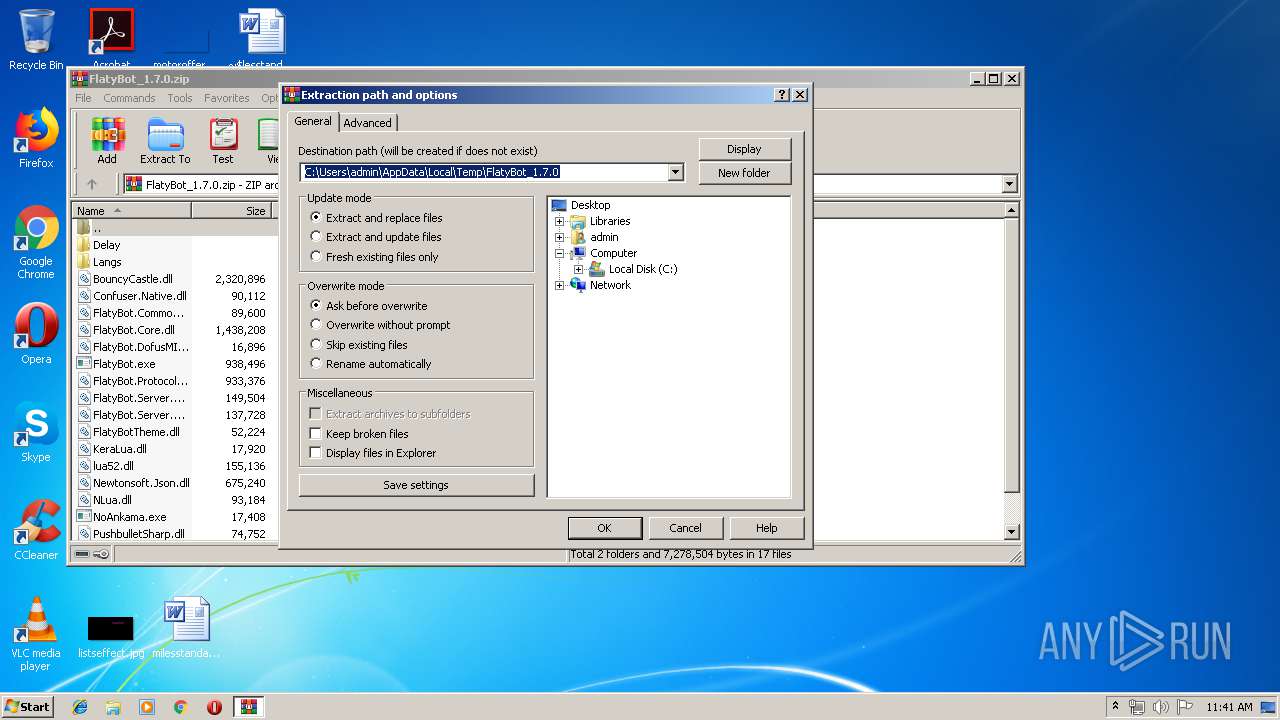
Modification events
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\FlatyBot_1.7.0.zip | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4000) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (768) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <c8 |
Value: 3C63380000030000010000000000000000000000 | |||
| (PID) Process: | (768) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
170
Suspicious files
699
Text files
338
Unknown types
70
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4BBC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B9862E12-F3AE-4405-B2E5-27D73FF29222}.tmp | — | |
MD5:— | SHA256:— | |||
| 768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{70F71873-43A3-4790-B555-0F357E4B41E0}.tmp | — | |
MD5:— | SHA256:— | |||
| 768 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 4000 | WinRAR.exe | C:\Users\admin\Desktop\lua52.dll | executable | |
MD5:— | SHA256:— | |||
| 4000 | WinRAR.exe | C:\Users\admin\Desktop\Langs\en.json | text | |
MD5:— | SHA256:— | |||
| 4000 | WinRAR.exe | C:\Users\admin\Desktop\Langs\fr.json | text | |
MD5:— | SHA256:— | |||
| 768 | WINWORD.EXE | C:\Users\admin\Desktop\~$lesstandard.rtf | pgc | |
MD5:— | SHA256:— | |||
| 4000 | WinRAR.exe | C:\Users\admin\Desktop\FlatyBot.Protocol.dll | executable | |
MD5:— | SHA256:— | |||
| 4000 | WinRAR.exe | C:\Users\admin\Desktop\FlatyBotTheme.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
118
TCP/UDP connections
92
DNS requests
47
Threats
107
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
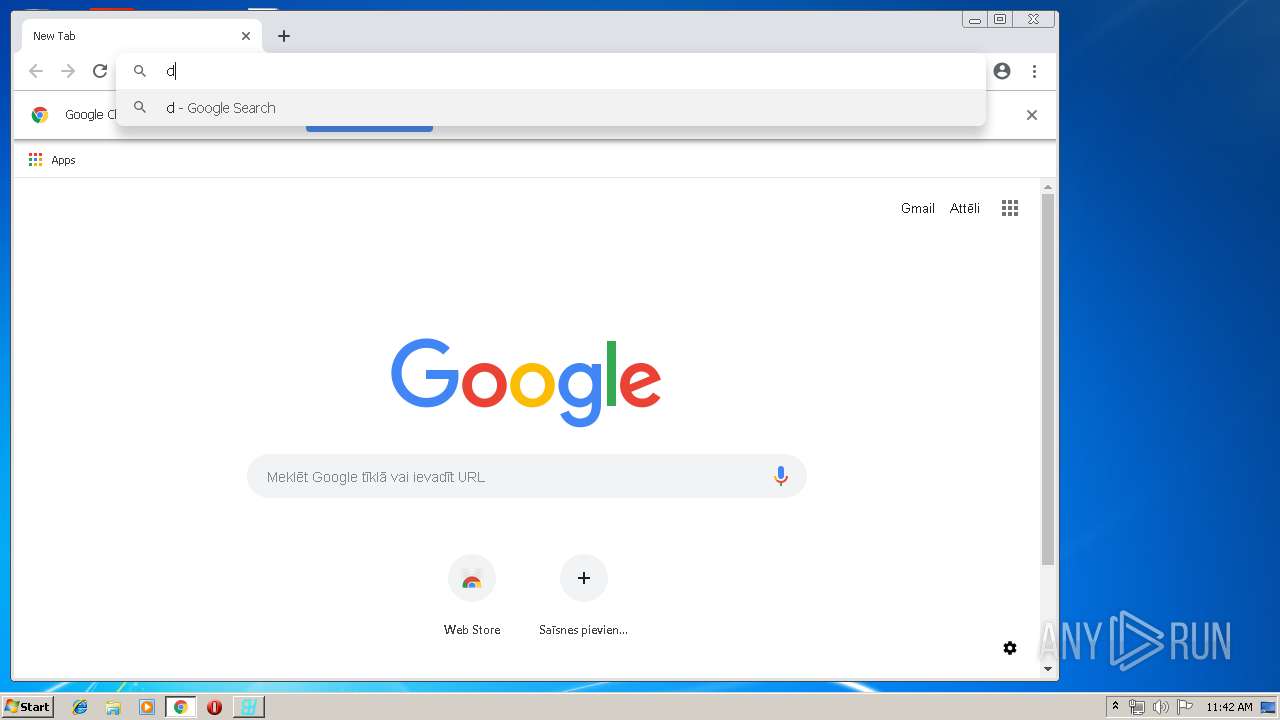
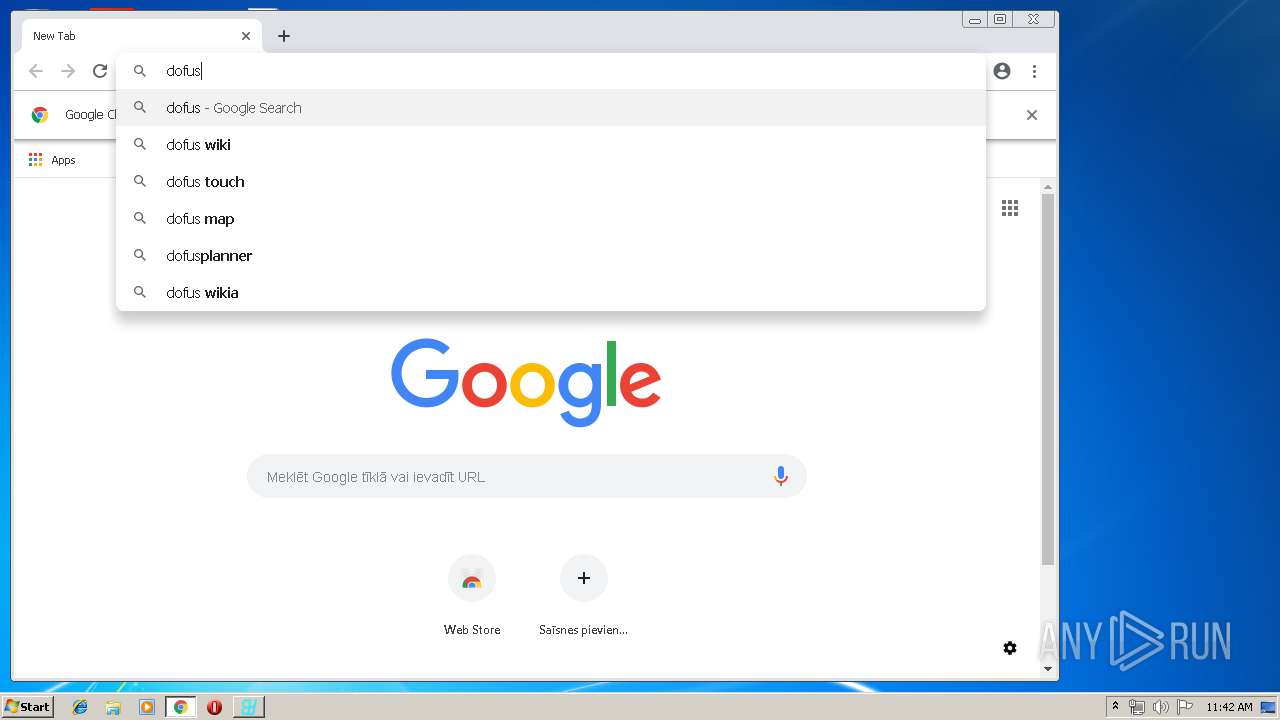
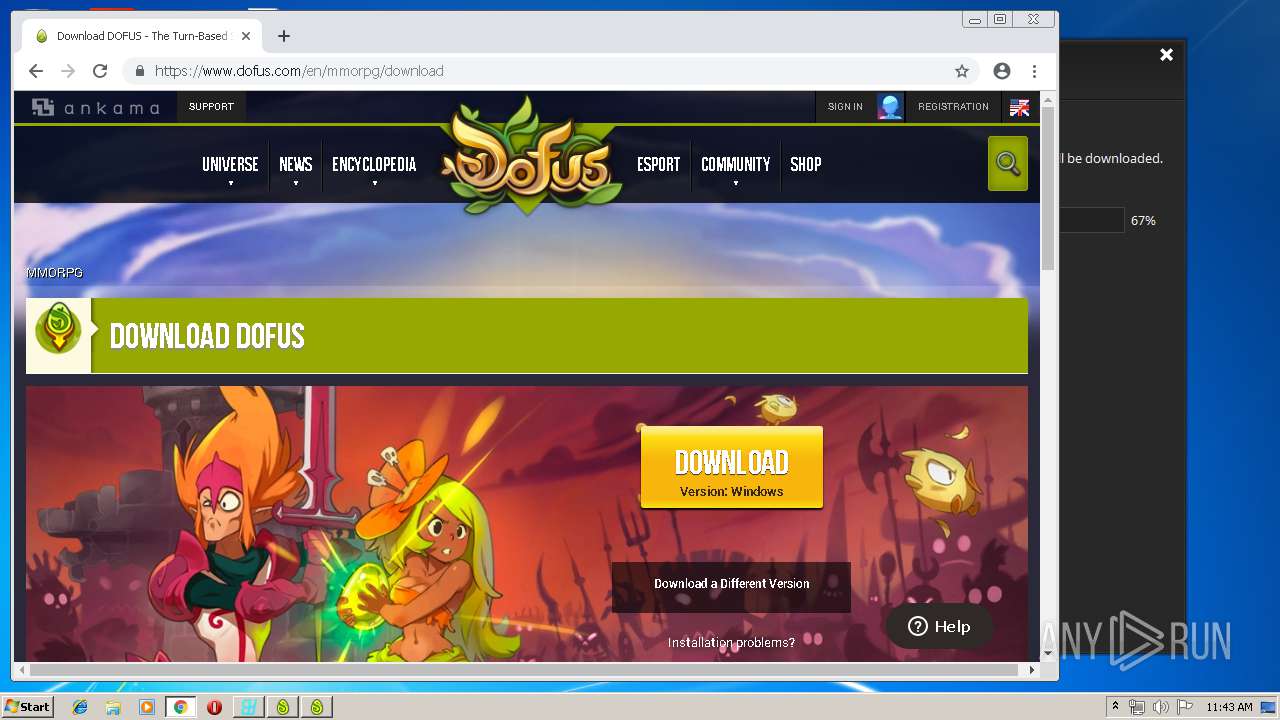
2808 | chrome.exe | GET | 301 | 104.16.168.239:80 | http://www.dofus.com/ | US | — | — | shared |
2808 | chrome.exe | GET | 301 | 104.16.168.239:80 | http://www.dofus.com/en/mmorpg/download | US | — | — | shared |
1648 | transition.exe | GET | — | 2.16.186.9:80 | http://dl.ak.ankama.com/updates/uc1/projects/transition-win32/updates/mesh | unknown | — | — | whitelisted |
1648 | transition.exe | GET | 200 | 2.16.186.9:80 | http://dl.ak.ankama.com/updates/uc1/repositories.json | unknown | text | 143 b | whitelisted |
1572 | chrome.exe | GET | 200 | 80.233.168.206:80 | http://r3---sn-uxap5a8-gpml.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=159.148.186.185&mm=28&mn=sn-uxap5a8-gpml&ms=nvh&mt=1554287807&mv=u&pl=24&shardbypass=yes | LV | crx | 842 Kb | whitelisted |
2808 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2808 | chrome.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
1572 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2808 | chrome.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
1648 | transition.exe | GET | 200 | 2.16.186.9:80 | http://dl.ak.ankama.com/updates/uc1/projects/transition-win32/updates/signature | unknown | binary | 256 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1572 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1572 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1572 | chrome.exe | 172.217.21.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
1572 | chrome.exe | 172.217.17.142:443 | apis.google.com | Google Inc. | US | whitelisted |
1572 | chrome.exe | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1572 | chrome.exe | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
1572 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 104.18.149.107:443 | account.ankama.com | Cloudflare Inc | US | shared |
2808 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-uxap5a8-gpml.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1648 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
Process | Message |
|---|---|
transition.exe | |
transition.exe | |
transition.exe | |
transition.exe |